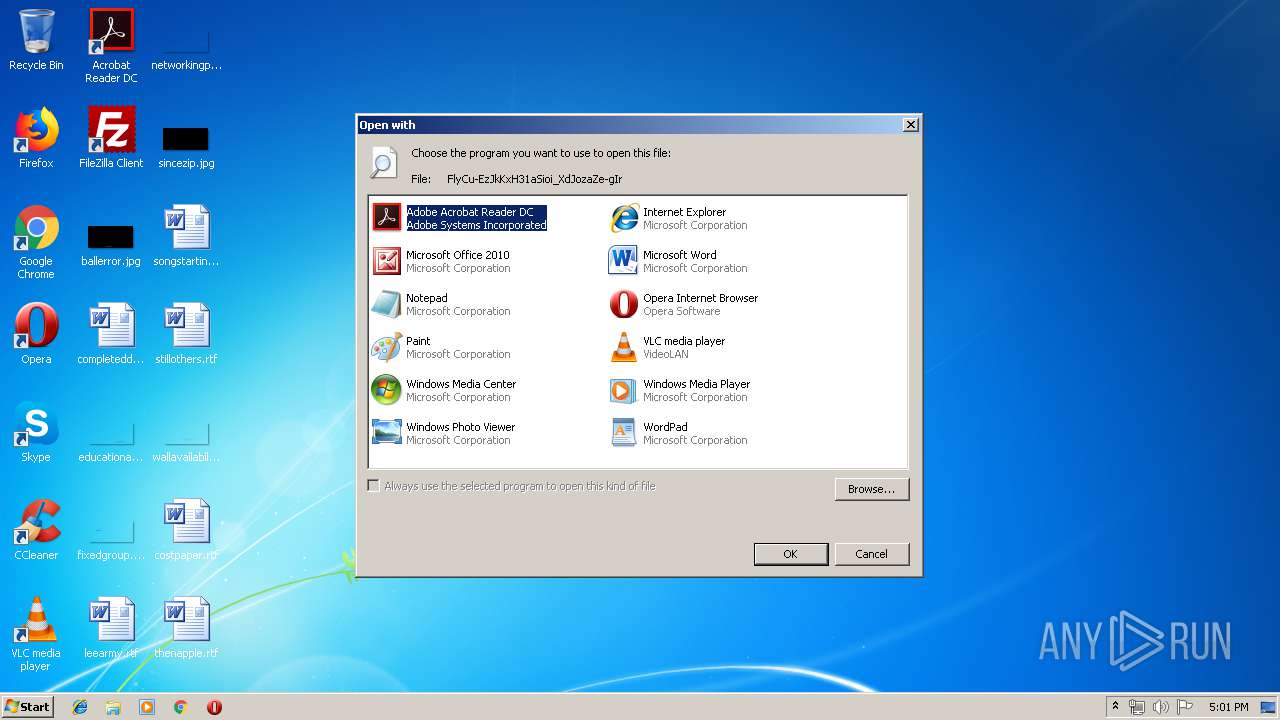
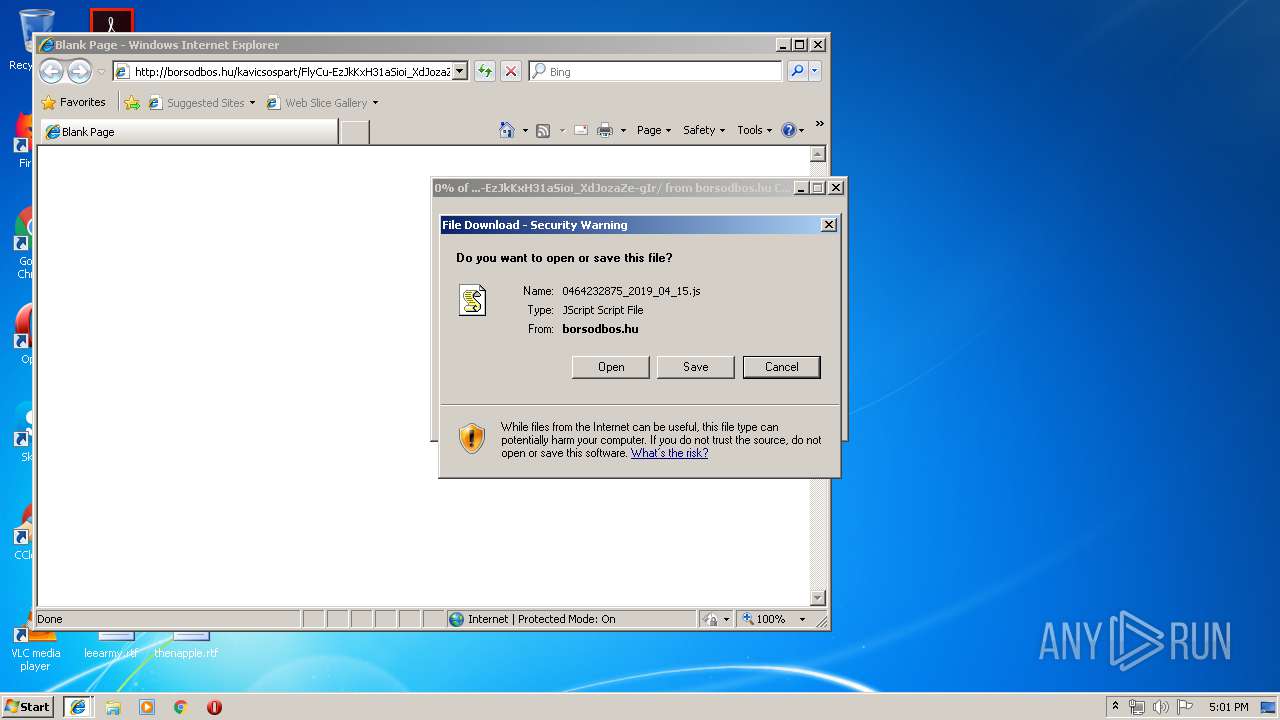
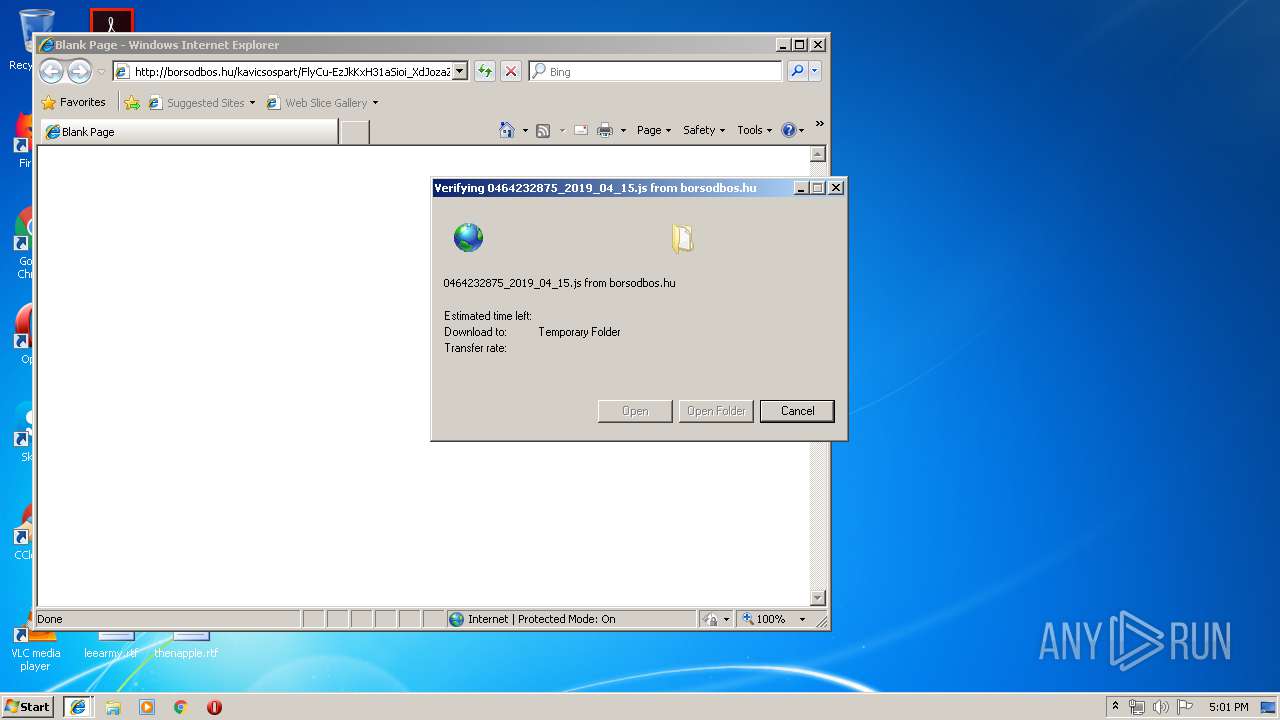
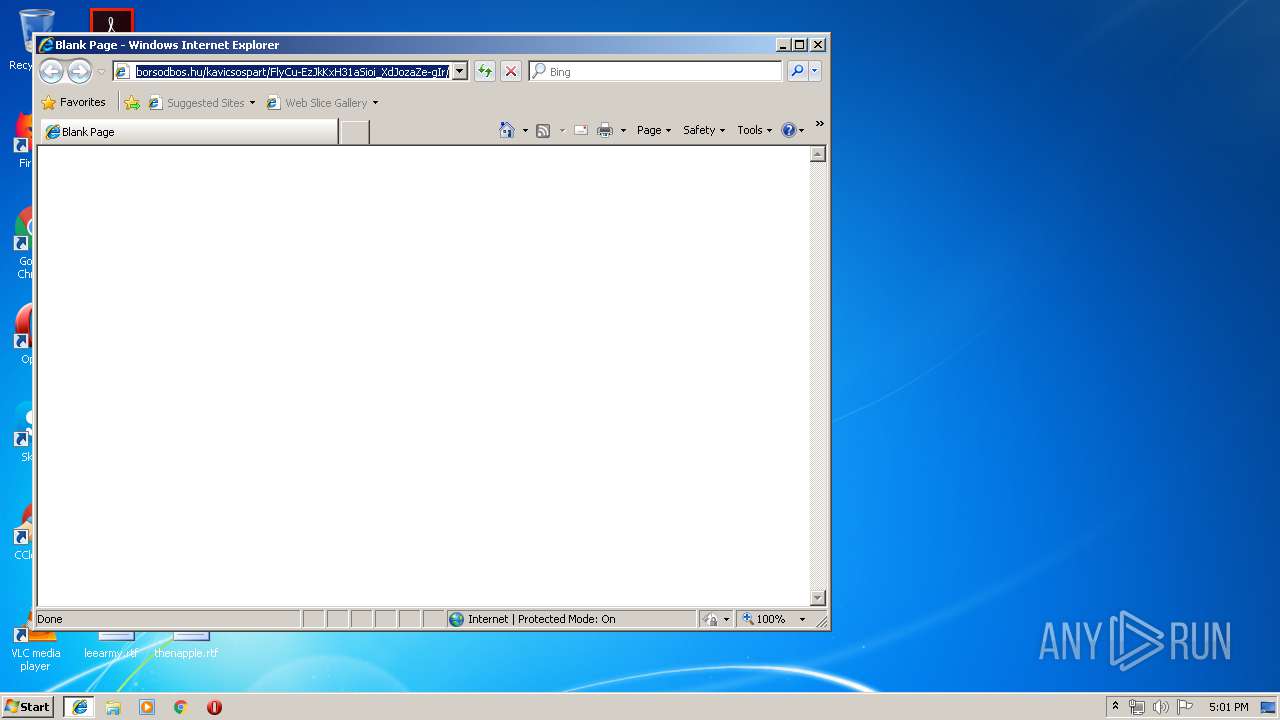
| download: | FlyCu-EzJkKxH31aSioi_XdJozaZe-gIr |
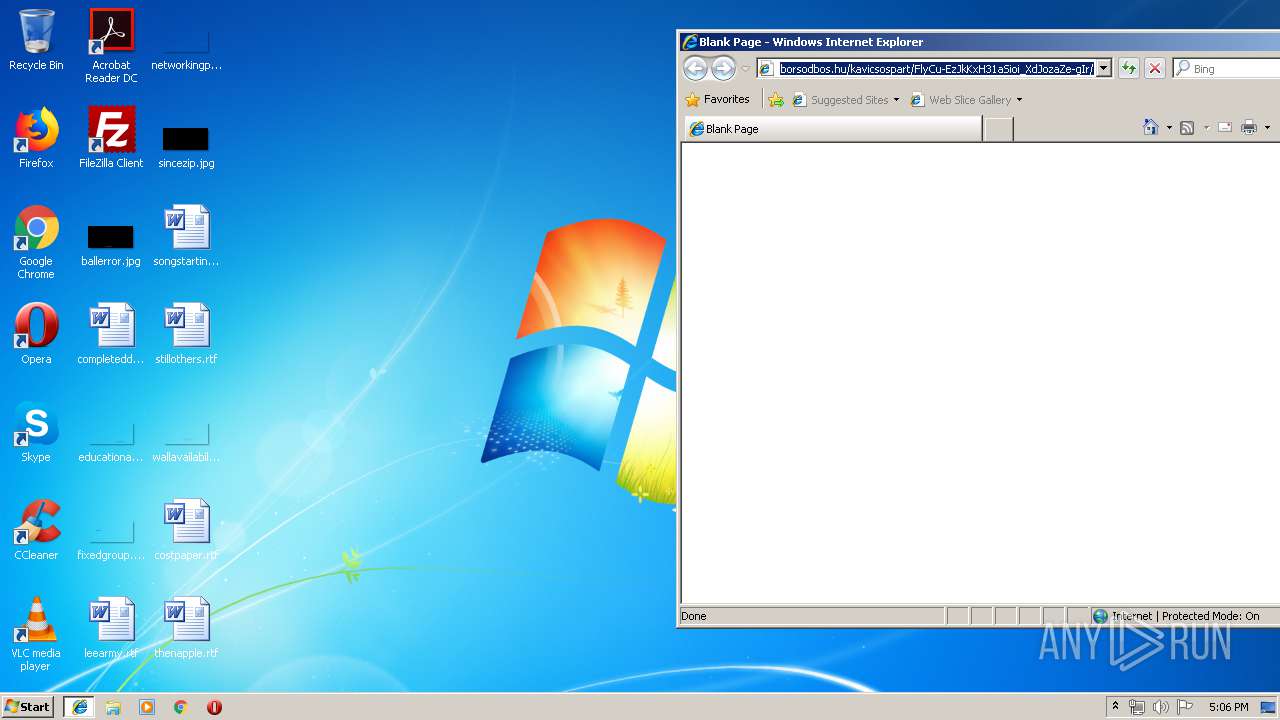
| Full analysis: | https://app.any.run/tasks/07ef2ab6-f029-495b-beef-60fe31371d39 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 15, 2019, 16:01:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with no line terminators |
| MD5: | 47B501D6DE8E3502F675D52C2592892D |
| SHA1: | 20914A0699D837FA8055E19328C6A026B872A64F |
| SHA256: | 268307363C224D65DA7370D6DA6CF518826F73A2D38CF8174037D4FCC5D18570 |
| SSDEEP: | 192:2bFHCHDUYuU/AzZ69rP4BYAjTykM+gCv0PH5t969YbmVg4bCBG1J3lpCt2oastyn:2blCjXcZ6OYOykM+gCv0PH5t9OYbmVgi |
MALICIOUS
Application was dropped or rewritten from another process
- dg822k5x2.exe (PID: 3276)
- soundser.exe (PID: 3568)
- dg822k5x2.exe (PID: 2404)
- soundser.exe (PID: 1256)
- R0usK2.exe (PID: 2696)
- R0usK2.exe (PID: 280)
- soundser.exe (PID: 1944)
- soundser.exe (PID: 2984)
Emotet process was detected
- soundser.exe (PID: 3568)
- soundser.exe (PID: 2984)
Downloads executable files from the Internet
- WScript.exe (PID: 3184)
EMOTET was detected
- soundser.exe (PID: 1256)
- soundser.exe (PID: 1944)
Connects to CnC server
- soundser.exe (PID: 1256)
- soundser.exe (PID: 1944)
Changes the autorun value in the registry
- soundser.exe (PID: 1256)
- soundser.exe (PID: 1944)
SUSPICIOUS
Executable content was dropped or overwritten
- WScript.exe (PID: 3184)
- dg822k5x2.exe (PID: 3276)
- soundser.exe (PID: 1256)
- R0usK2.exe (PID: 280)
Executes scripts
- iexplore.exe (PID: 1524)
Starts itself from another location
- dg822k5x2.exe (PID: 3276)
- R0usK2.exe (PID: 280)
Application launched itself
- soundser.exe (PID: 3568)
- dg822k5x2.exe (PID: 2404)
- soundser.exe (PID: 2984)
- R0usK2.exe (PID: 2696)
Connects to server without host name
- soundser.exe (PID: 1256)
- soundser.exe (PID: 1944)
INFO
Changes internet zones settings
- iexplore.exe (PID: 1524)
Reads Internet Cache Settings
- iexplore.exe (PID: 3372)
Creates files in the user directory
- iexplore.exe (PID: 1524)
- iexplore.exe (PID: 3372)
Reads internet explorer settings
- iexplore.exe (PID: 3372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
44
Monitored processes
13
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | --4bae5b6a | C:\Users\admin\AppData\Local\soundser\R0usK2.exe | R0usK2.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1256 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
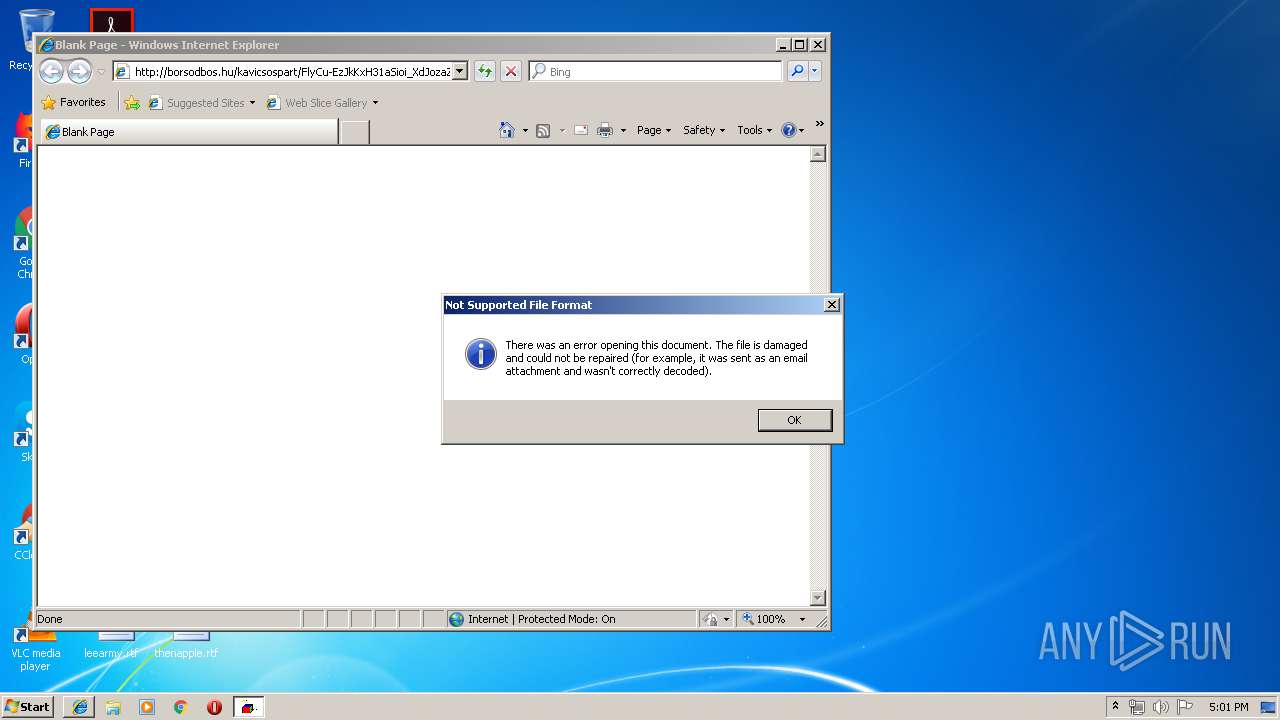
| 1740 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\FlyCu-EzJkKxH31aSioi_XdJozaZe-gIr | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1944 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2128 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2404 | "C:\Users\admin\AppData\Local\Temp\dg822k5x2.exe" | C:\Users\admin\AppData\Local\Temp\dg822k5x2.exe | — | WScript.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2696 | "C:\Users\admin\AppData\Local\soundser\R0usK2.exe" | C:\Users\admin\AppData\Local\soundser\R0usK2.exe | — | soundser.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2984 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | R0usK2.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3184 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\FlyCu-EzJkKxH31aSioi_XdJozaZe-gIr[1].js" | C:\Windows\System32\WScript.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
1 269
Read events
1 167
Write events
102
Delete events
0
Modification events
| (PID) Process: | (1740) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | LangID |
Value: 0904 | |||
| (PID) Process: | (1740) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (1740) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (1740) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Internet Explorer\iexplore.exe |
Value: Internet Explorer | |||
| (PID) Process: | (1740) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (1740) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (1740) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (1740) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (1740) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (1740) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
Executable files
4
Suspicious files
0
Text files
14
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1524 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1524 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@borsodbos[1].txt | text | |
MD5:— | SHA256:— | |||
| 1524 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OBX0MPW5\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\UXVZXVFN\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 1524 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\IGNXHO1E\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
11
DNS requests
7
Threats
41
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
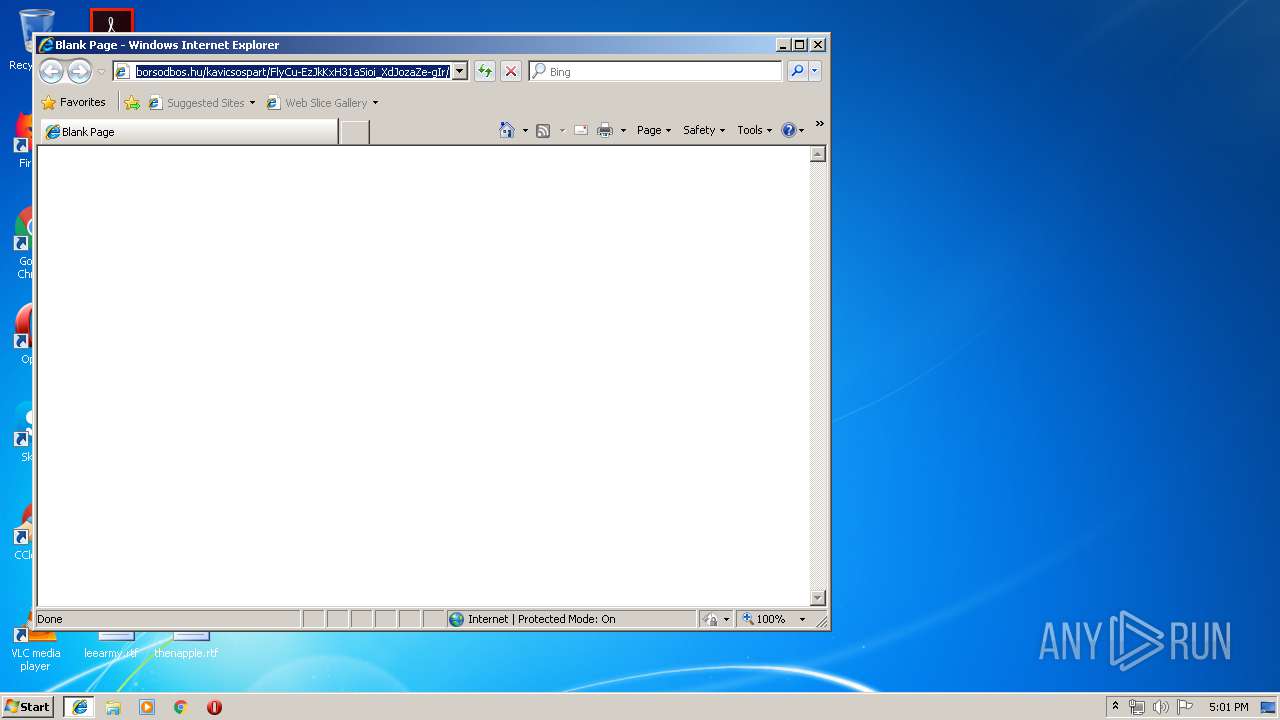
3372 | iexplore.exe | GET | 200 | 84.2.38.70:80 | http://borsodbos.hu/kavicsospart/FlyCu-EzJkKxH31aSioi_XdJozaZe-gIr/ | HU | text | 4.01 Kb | suspicious |
3184 | WScript.exe | GET | 200 | 104.248.52.157:80 | http://airtechscubaservices.com/wp-includes/PT8/ | US | executable | 131 Kb | suspicious |
1256 | soundser.exe | POST | — | 181.37.126.2:80 | http://181.37.126.2/health/ | DO | — | — | malicious |
3184 | WScript.exe | GET | 403 | 103.27.236.185:80 | http://canho-ezland.com/wp-content/T9L/ | VN | html | 199 b | unknown |
1256 | soundser.exe | POST | 200 | 181.30.126.66:80 | http://181.30.126.66/cookies/entries/ | AR | binary | 91.4 Kb | malicious |
1944 | soundser.exe | POST | — | 65.49.60.163:443 | http://65.49.60.163:443/stubs/raster/ | US | — | — | malicious |
1944 | soundser.exe | POST | — | 187.137.162.145:443 | http://187.137.162.145:443/rtm/dma/ | MX | — | — | malicious |
1944 | soundser.exe | POST | 502 | 88.215.2.29:80 | http://88.215.2.29/badge/mult/ringin/merge/ | GB | html | 552 b | malicious |
1944 | soundser.exe | POST | 200 | 45.33.35.103:8080 | http://45.33.35.103:8080/free/report/ringin/merge/ | US | binary | 148 b | malicious |
1944 | soundser.exe | POST | 200 | 45.33.35.103:8080 | http://45.33.35.103:8080/arizona/guids/ringin/ | US | binary | 66.3 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1524 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3372 | iexplore.exe | 84.2.38.70:80 | borsodbos.hu | Magyar Telekom plc. | HU | suspicious |
3184 | WScript.exe | 103.27.236.185:80 | canho-ezland.com | Long Van System Solution JSC | VN | unknown |
3184 | WScript.exe | 104.248.52.157:80 | airtechscubaservices.com | — | US | suspicious |
1944 | soundser.exe | 187.137.162.145:443 | — | Uninet S.A. de C.V. | MX | malicious |
1944 | soundser.exe | 65.49.60.163:443 | — | Linode, LLC | US | malicious |
1944 | soundser.exe | 45.33.35.103:8080 | — | Linode, LLC | US | malicious |
1944 | soundser.exe | 187.188.166.192:80 | — | TOTAL PLAY TELECOMUNICACIONES SA DE CV | MX | malicious |
1944 | soundser.exe | 88.215.2.29:80 | — | Gamma Telecom Holdings Ltd | GB | malicious |
1256 | soundser.exe | 181.30.126.66:80 | — | CABLEVISION S.A. | AR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
borsodbos.hu |
| unknown |
canho-ezland.com |
| unknown |
airtechscubaservices.com |
| suspicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3184 | WScript.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
3184 | WScript.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
3184 | WScript.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3184 | WScript.exe | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
3184 | WScript.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3184 | WScript.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
1256 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1256 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1944 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 8 |
1944 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 23 |
21 ETPRO signatures available at the full report