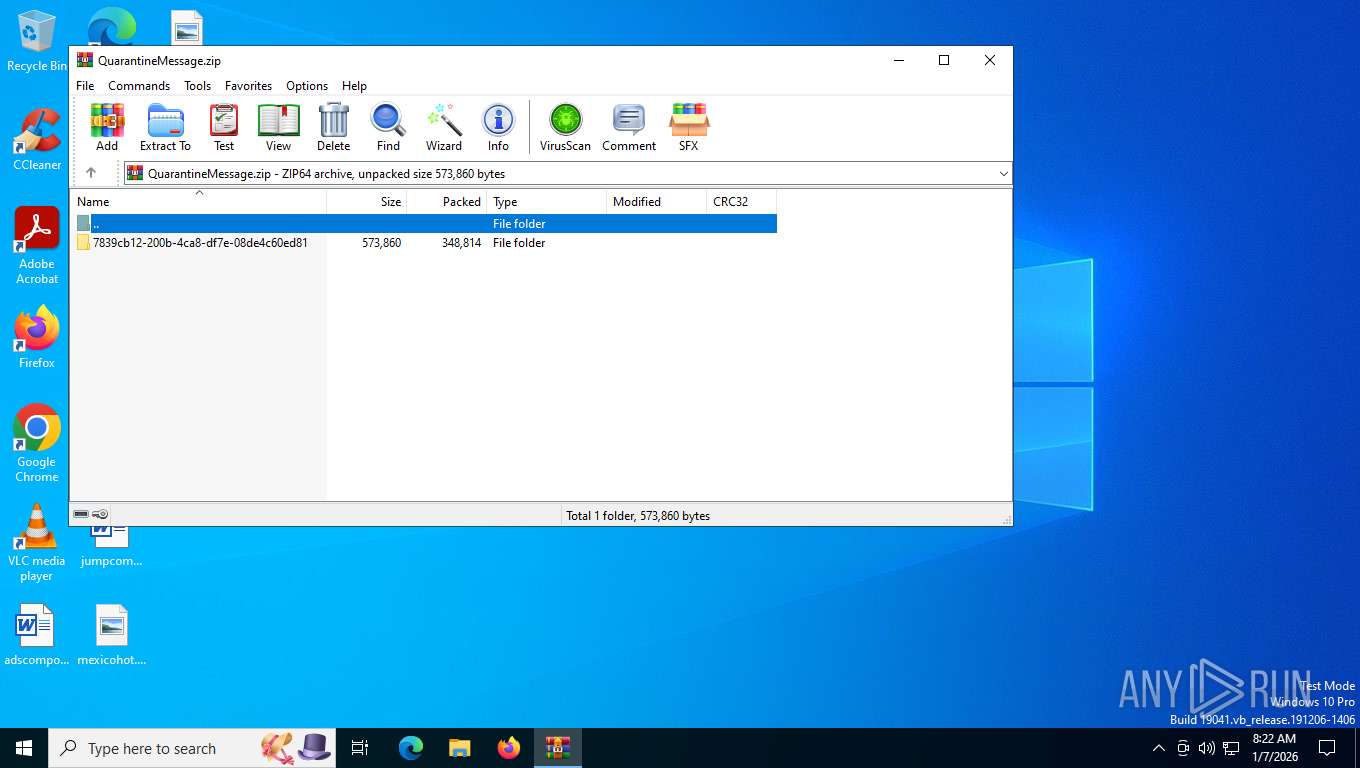
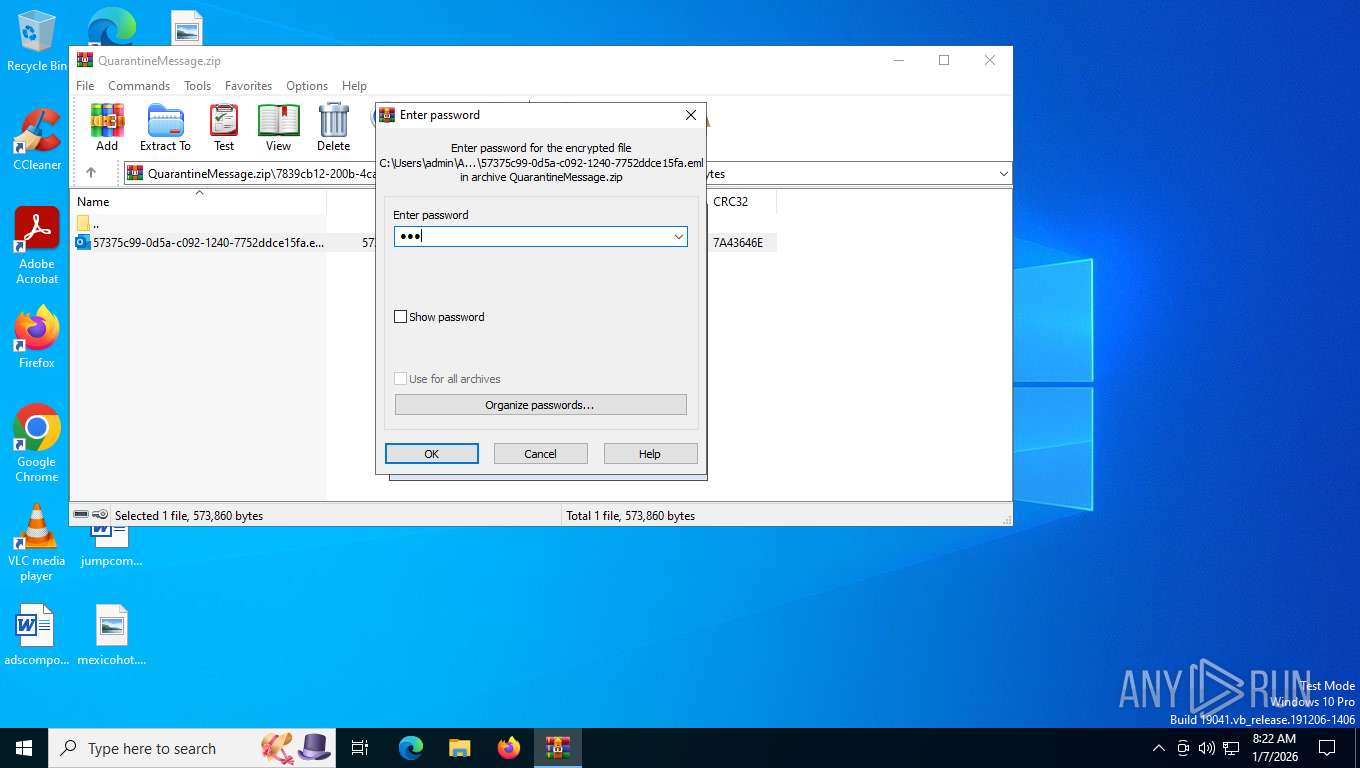
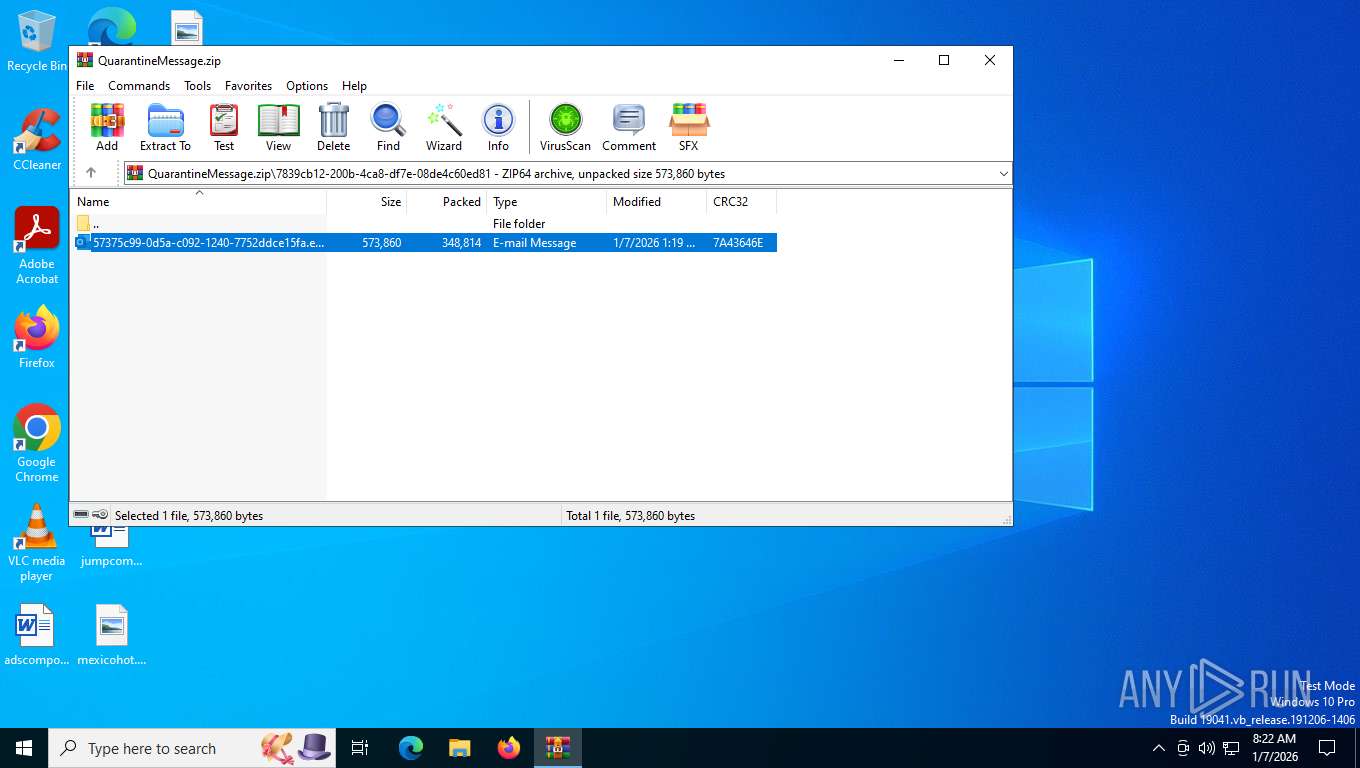
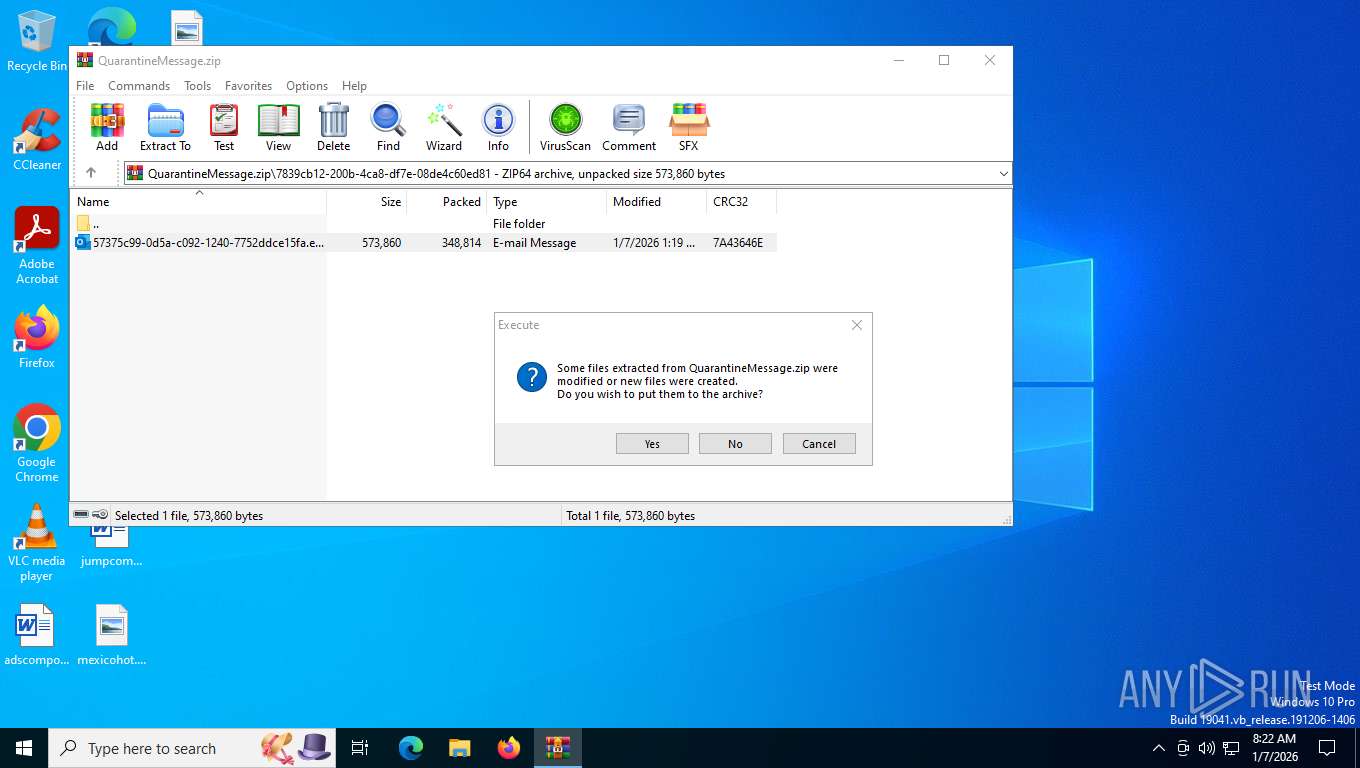
| File name: | QuarantineMessage.zip |
| Full analysis: | https://app.any.run/tasks/83552b82-9887-444d-b922-09b02d89dcb6 |
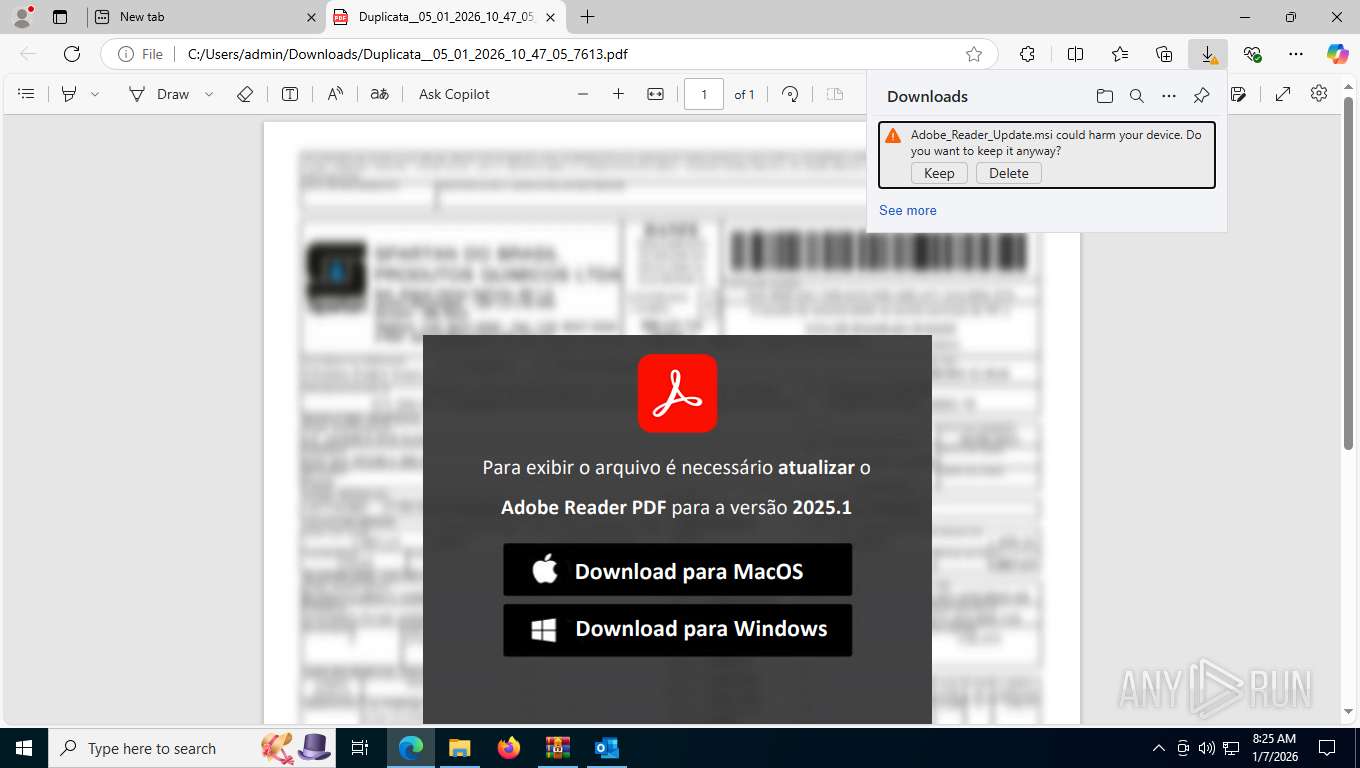
| Verdict: | Malicious activity |
| Analysis date: | January 07, 2026, 13:22:12 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v4.5 to extract, compression method=deflate |
| MD5: | F96695D7FA46AF457D03F52CDBB8731B |
| SHA1: | F26B13A9F36E5C522DC61F3AEA8F0DFF4724CCF7 |
| SHA256: | 26730AEB20A0087C6878760AD08D248AC5B8500B4DC7412EE7D105989076C7A3 |
| SSDEEP: | 12288:P+UHr+UmveKA6gRRRZ5Eh+qgE/hdctqtsG+J:P+UL+Umva6aLZ5EDgahdctqtszJ |
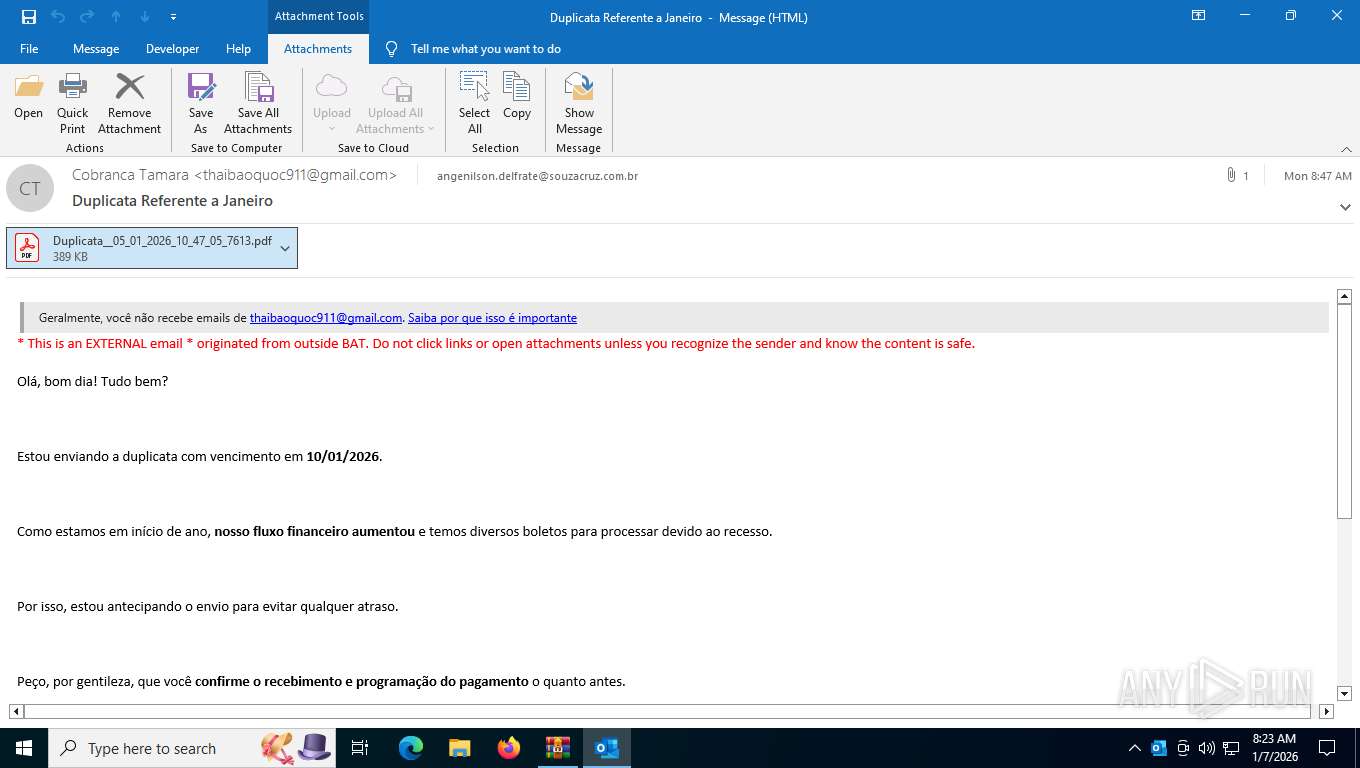
MALICIOUS
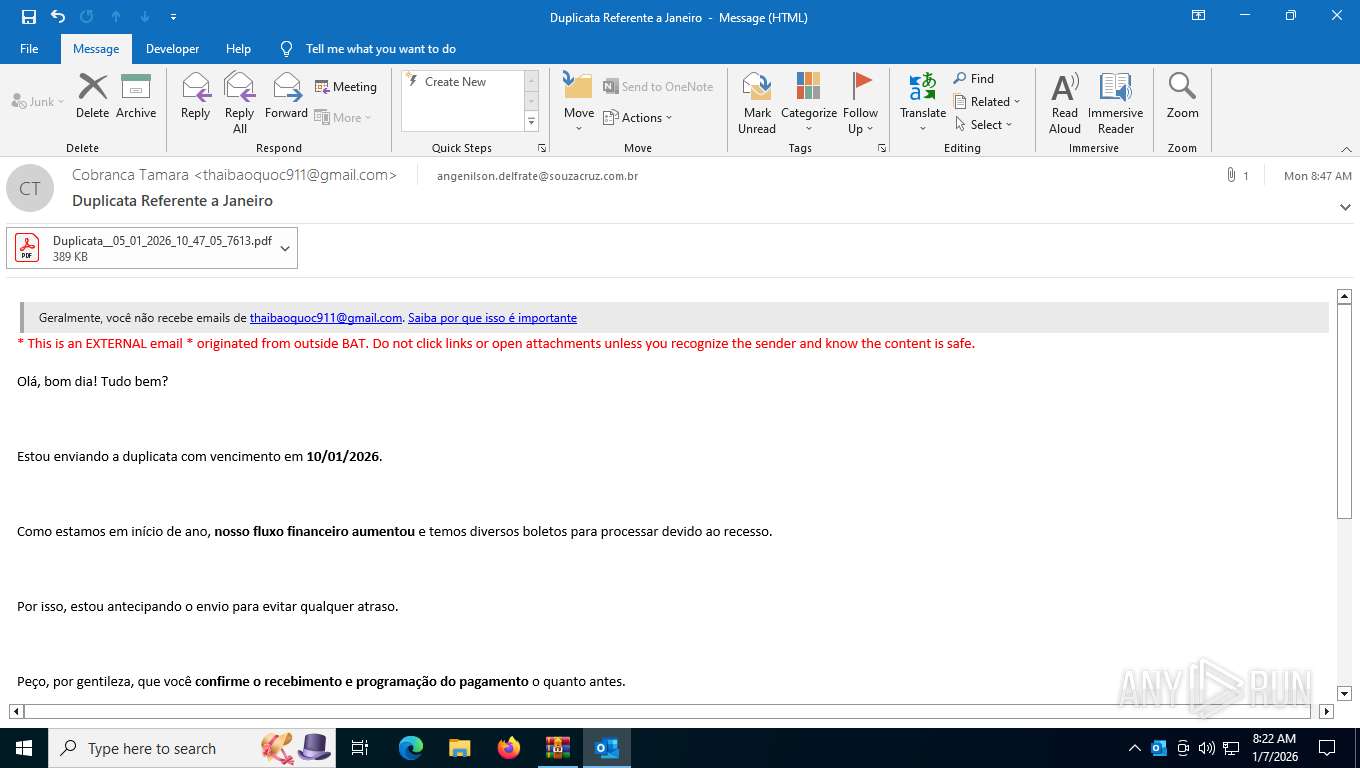
Phishing has been detected
- WinRAR.exe (PID: 7600)
- WinRAR.exe (PID: 7600)
- OUTLOOK.EXE (PID: 2424)
- OUTLOOK.EXE (PID: 2424)
SUSPICIOUS
Reads Microsoft Outlook installation path
- WinRAR.exe (PID: 7600)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7600)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 7600)
- OpenWith.exe (PID: 6820)
Application launched itself
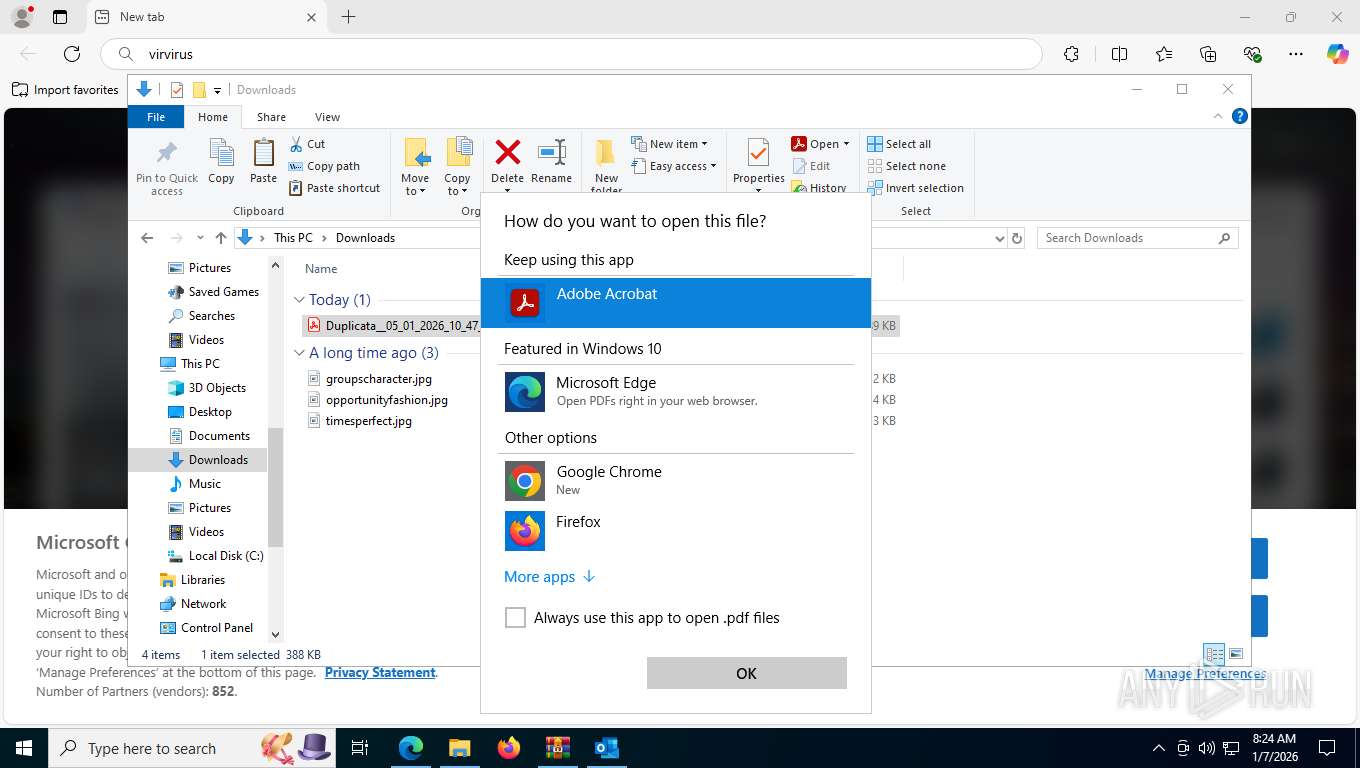
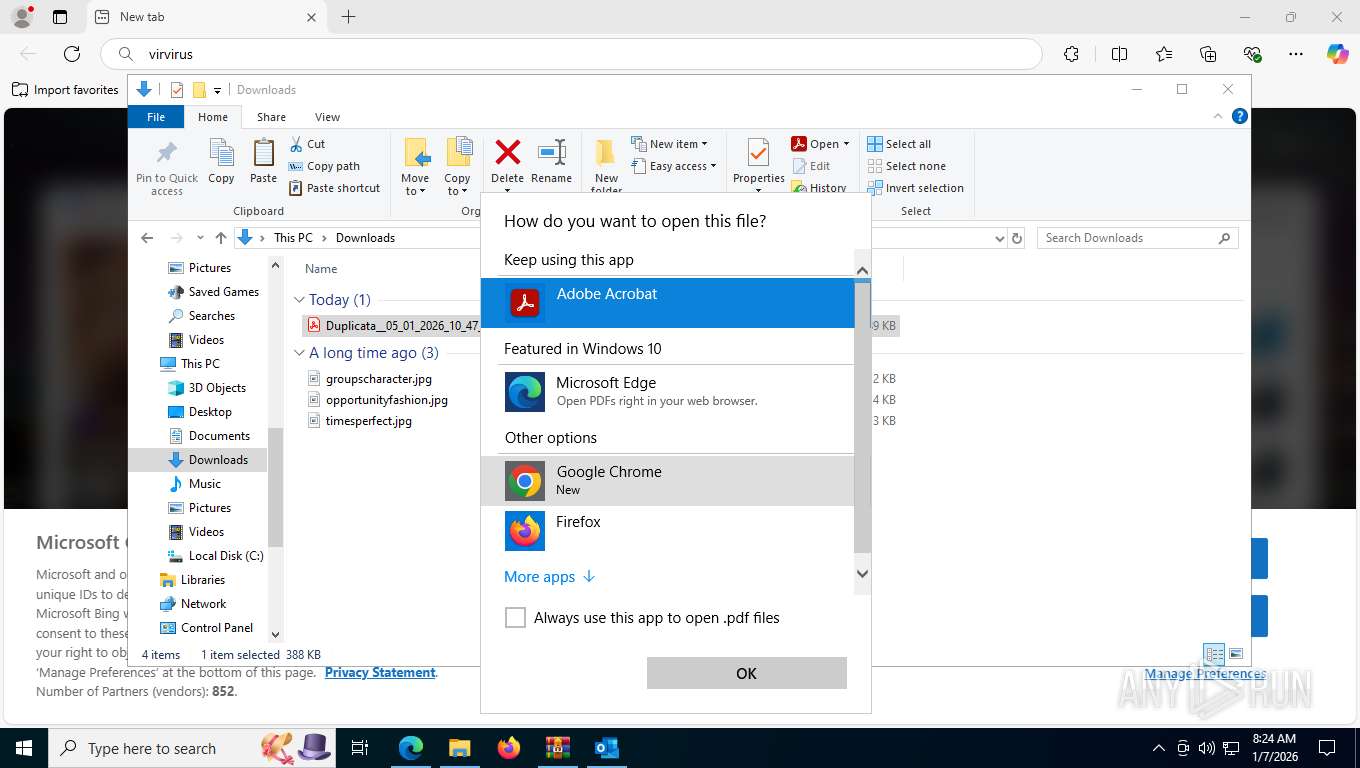
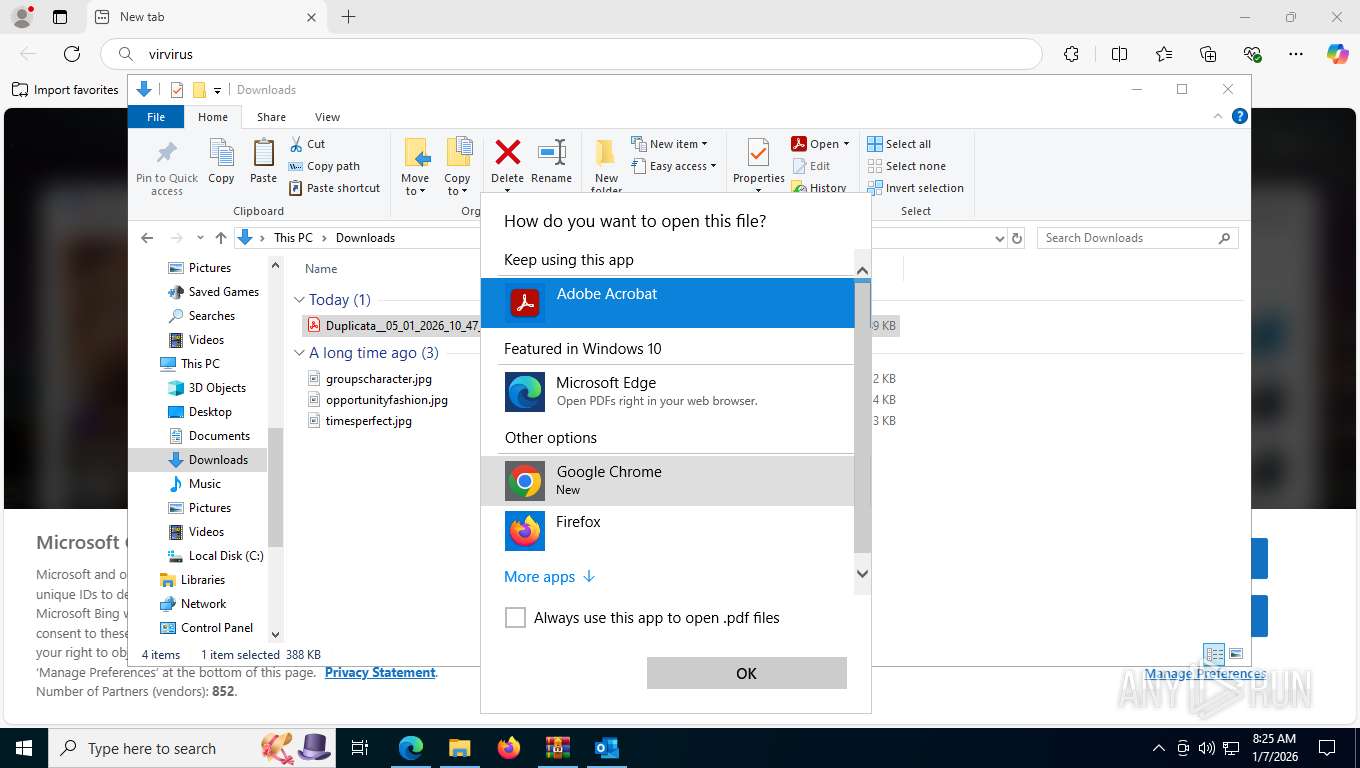
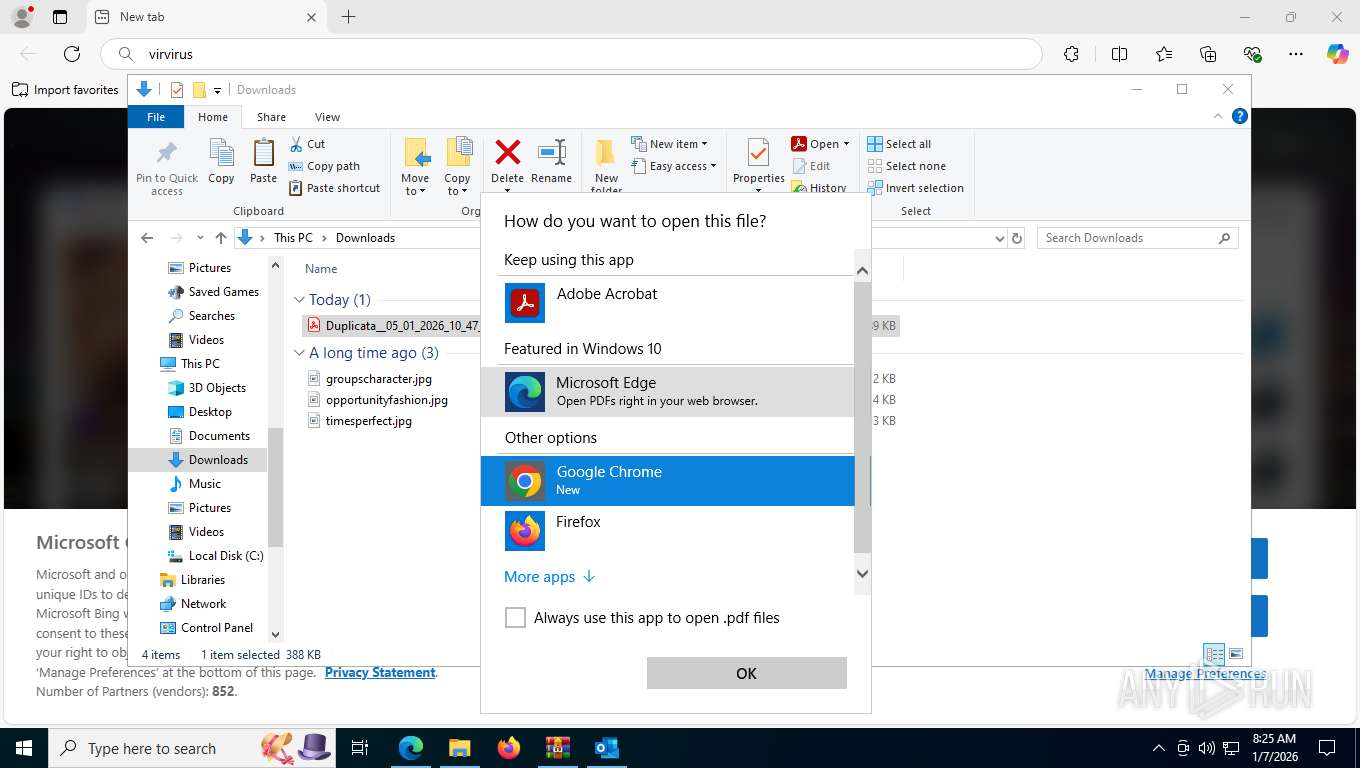
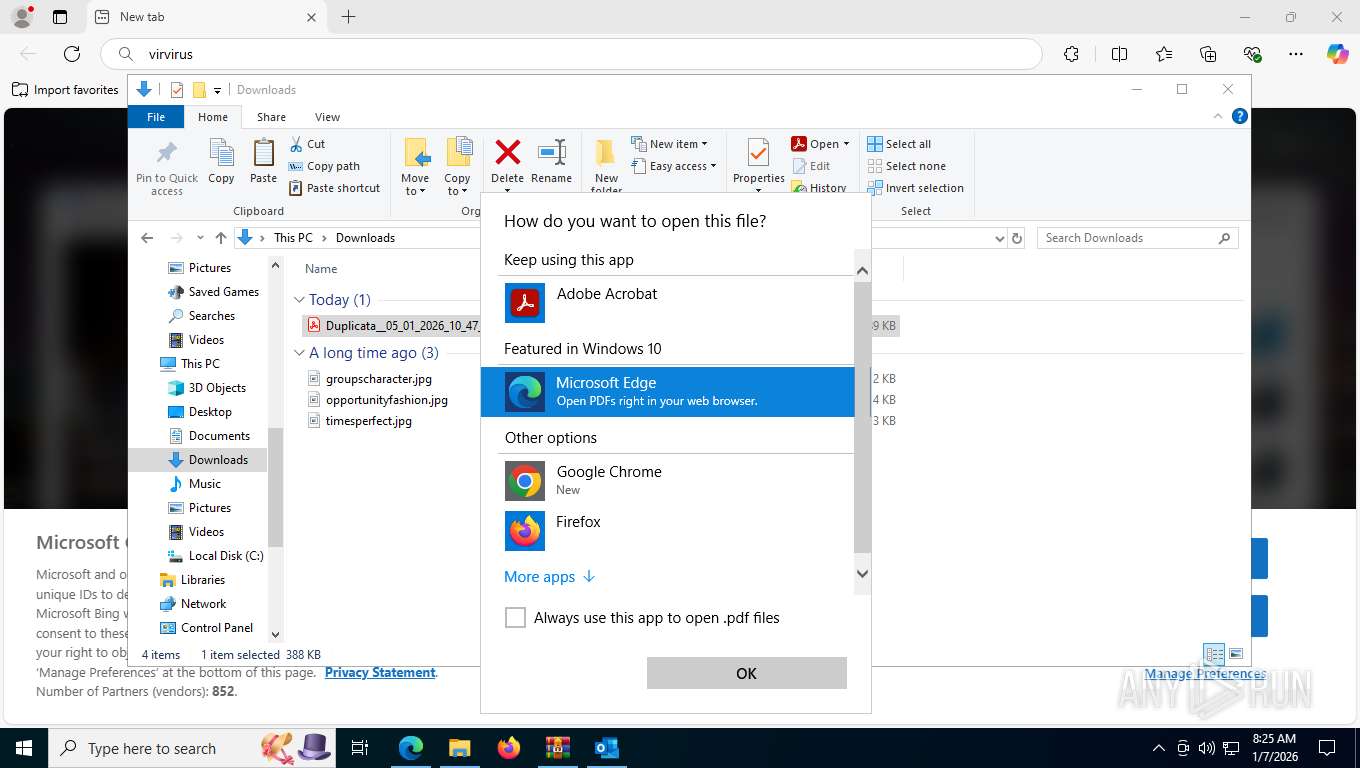
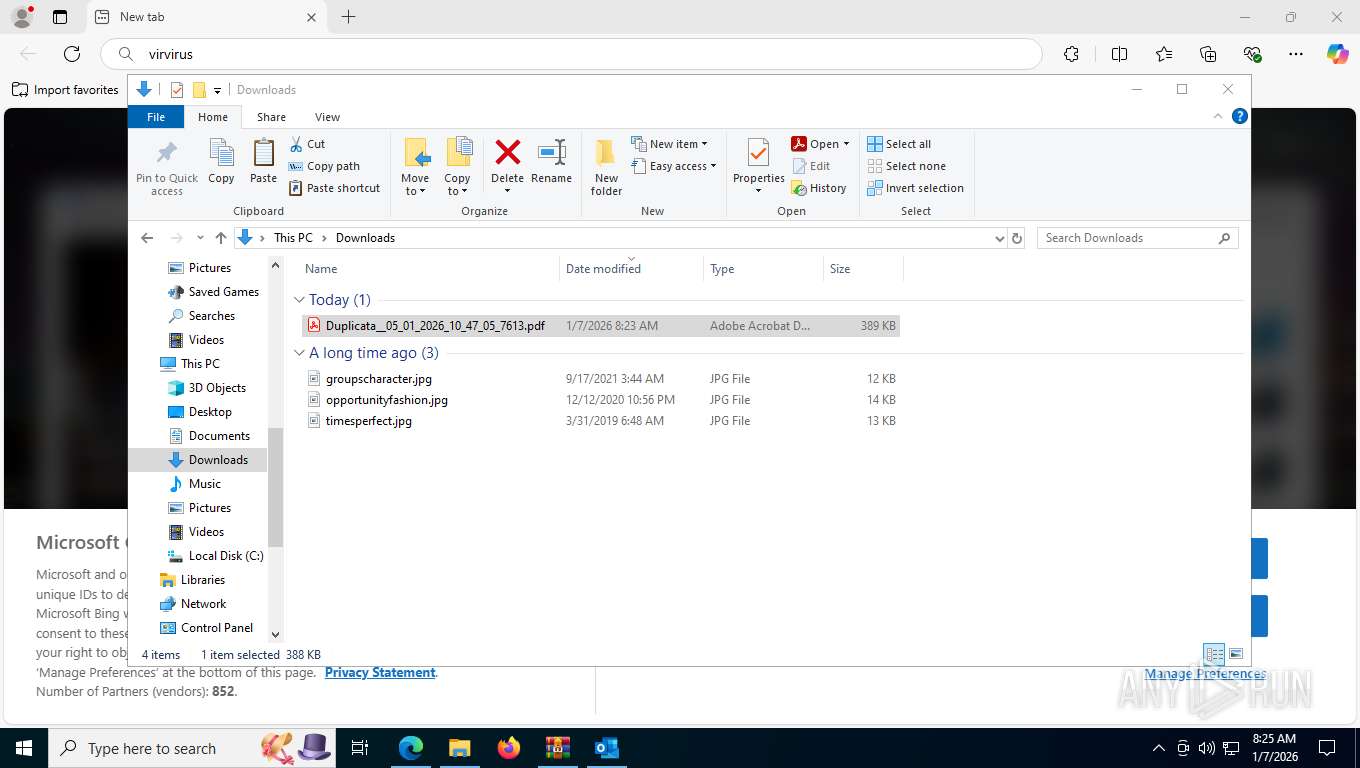
- Acrobat.exe (PID: 7860)
- msedge.exe (PID: 8112)
Checks supported languages
- TextInputHost.exe (PID: 1600)
- identity_helper.exe (PID: 4140)
Reads the computer name
- TextInputHost.exe (PID: 1600)
- identity_helper.exe (PID: 4140)
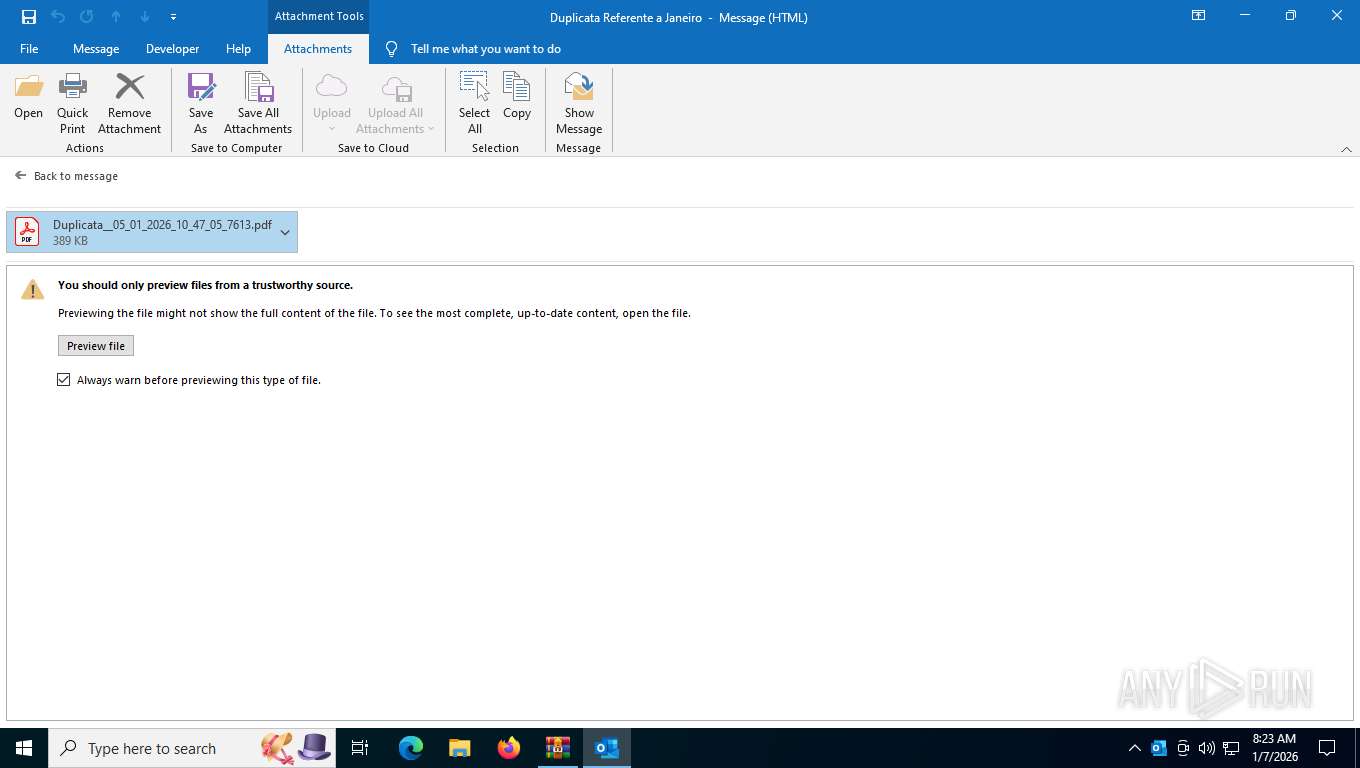
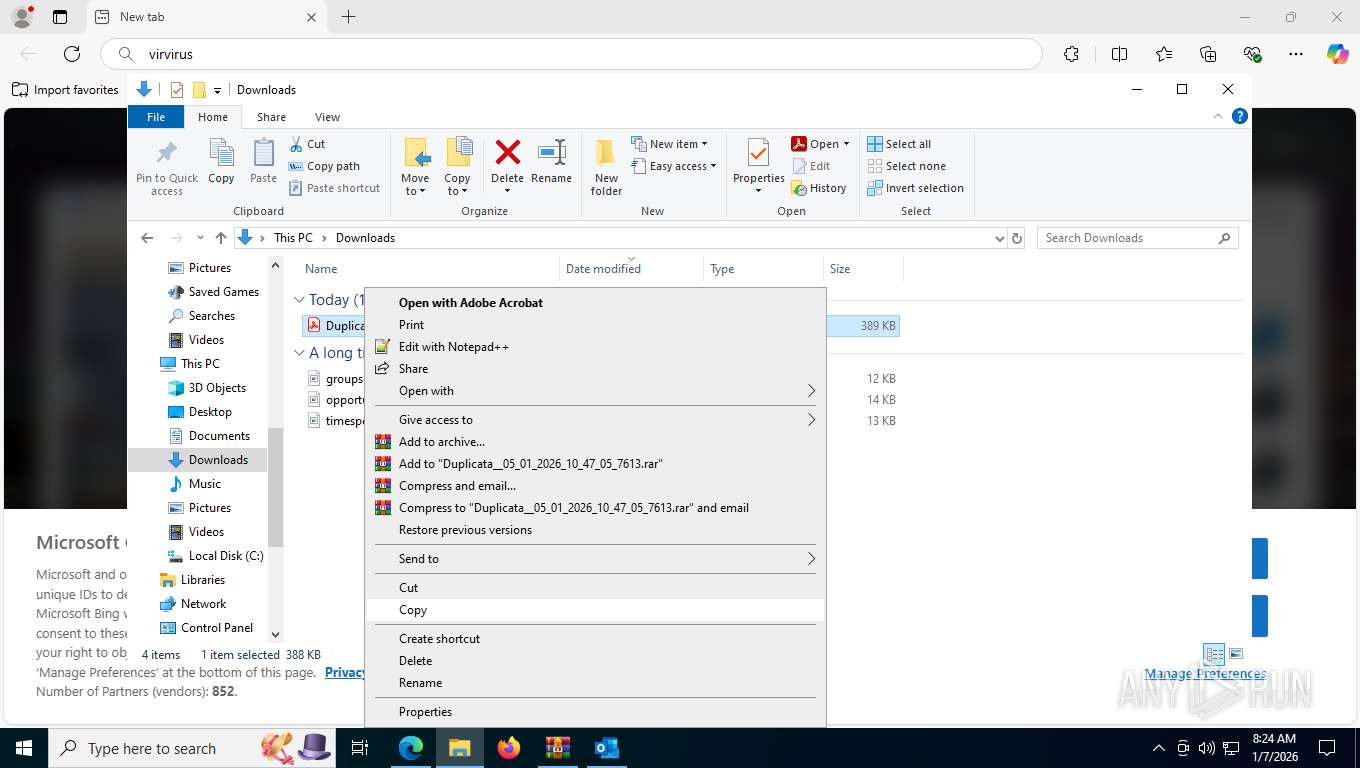
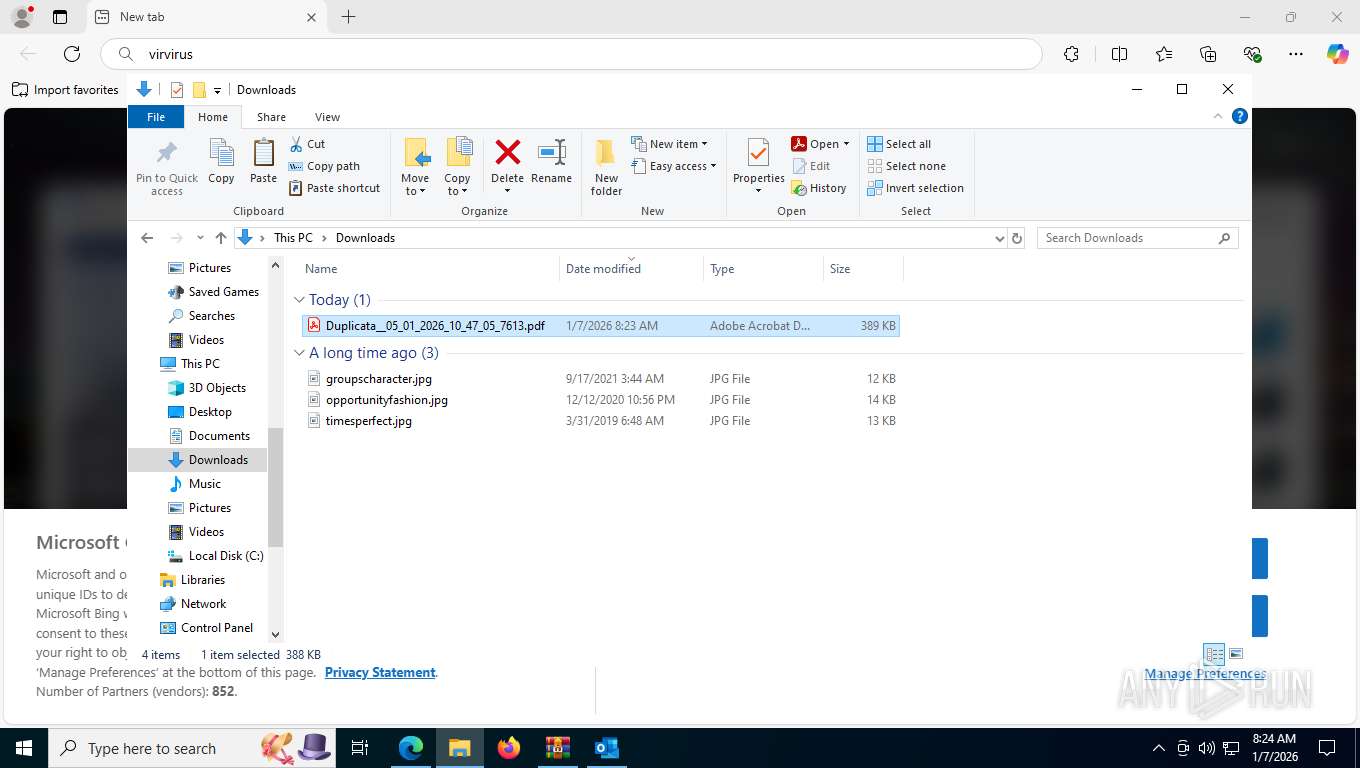
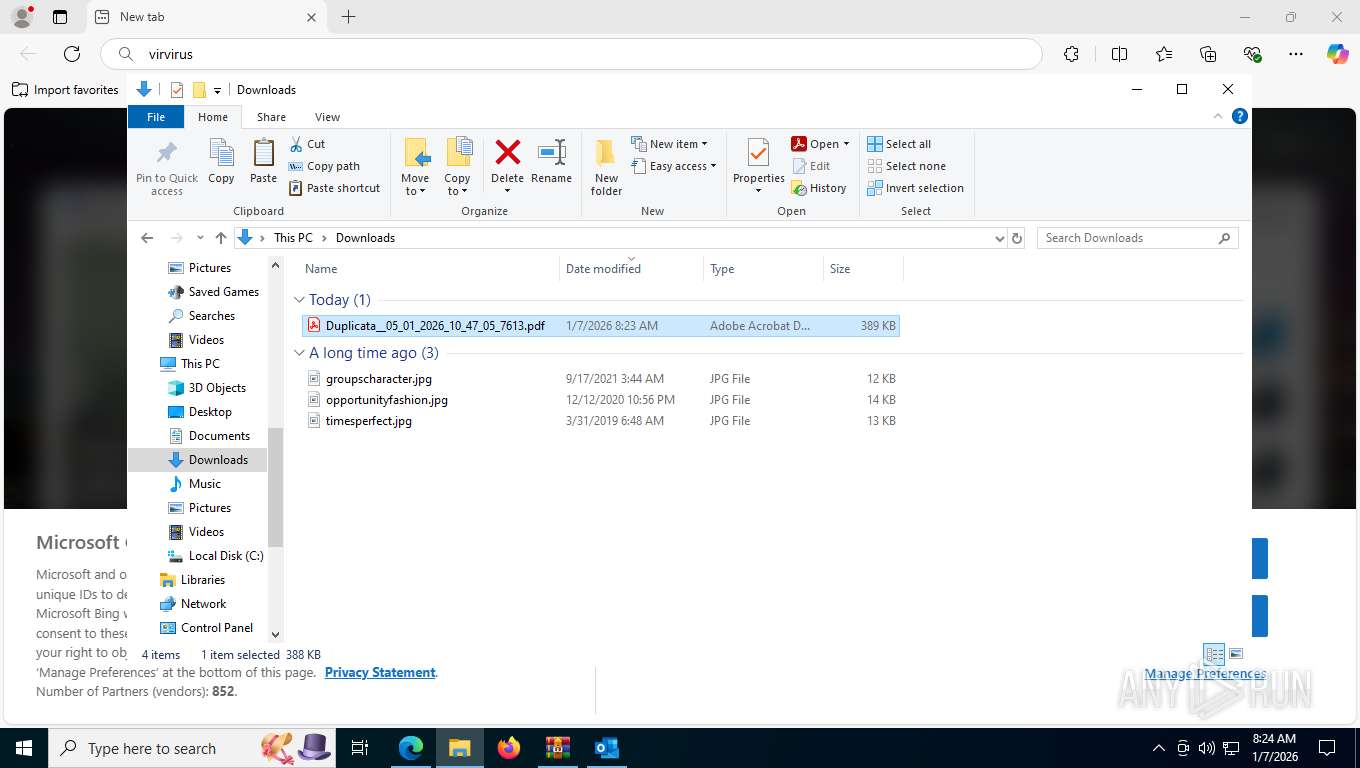
Manual execution by a user
- msedge.exe (PID: 8112)
Reads Environment values
- identity_helper.exe (PID: 4140)
Checks proxy server information
- slui.exe (PID: 1700)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 6820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 45 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2026:01:07 13:19:00 |
| ZipCRC: | 0x7a43646e |
| ZipCompressedSize: | 4294967295 |
| ZipUncompressedSize: | 4294967295 |
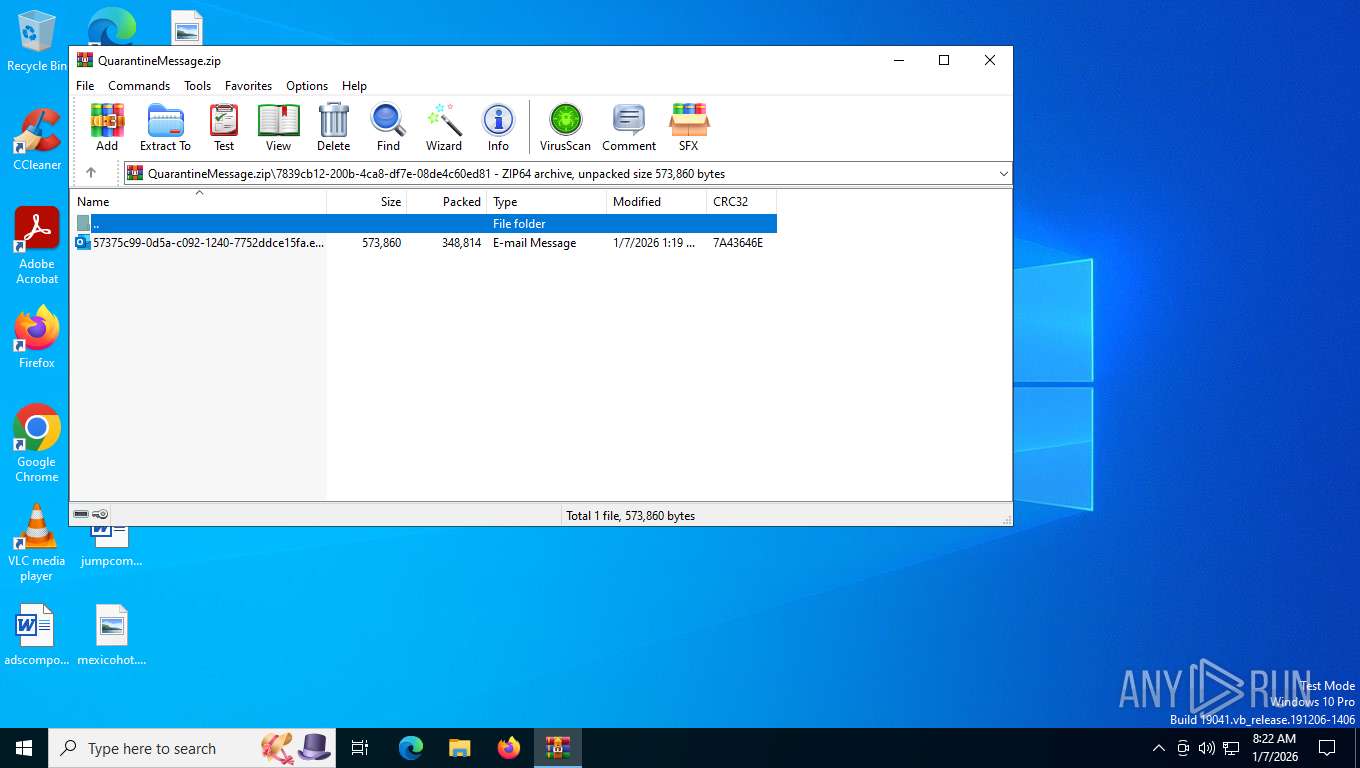
| ZipFileName: | 7839cb12-200b-4ca8-df7e-08de4c60ed81/57375c99-0d5a-c092-1240-7752ddce15fa.eml |
Total processes
194
Monitored processes
42
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1092 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=2012,i,16245265200338075717,13139417488263327447,262144 --variations-seed-version --mojo-platform-channel-handle=6832 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=21 --always-read-main-dll --field-trial-handle=5732,i,16245265200338075717,13139417488263327447,262144 --variations-seed-version --mojo-platform-channel-handle=5560 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1340 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6028,i,16245265200338075717,13139417488263327447,262144 --variations-seed-version --mojo-platform-channel-handle=5124 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1348 | C:\WINDOWS\system32\prevhost.exe {DC6EFB56-9CFA-464D-8880-44885D7DC193} -Embedding | C:\Windows\System32\prevhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Preview Handler Surrogate Host Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1492 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6796,i,16245265200338075717,13139417488263327447,262144 --variations-seed-version --mojo-platform-channel-handle=5424 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1600 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 1700 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
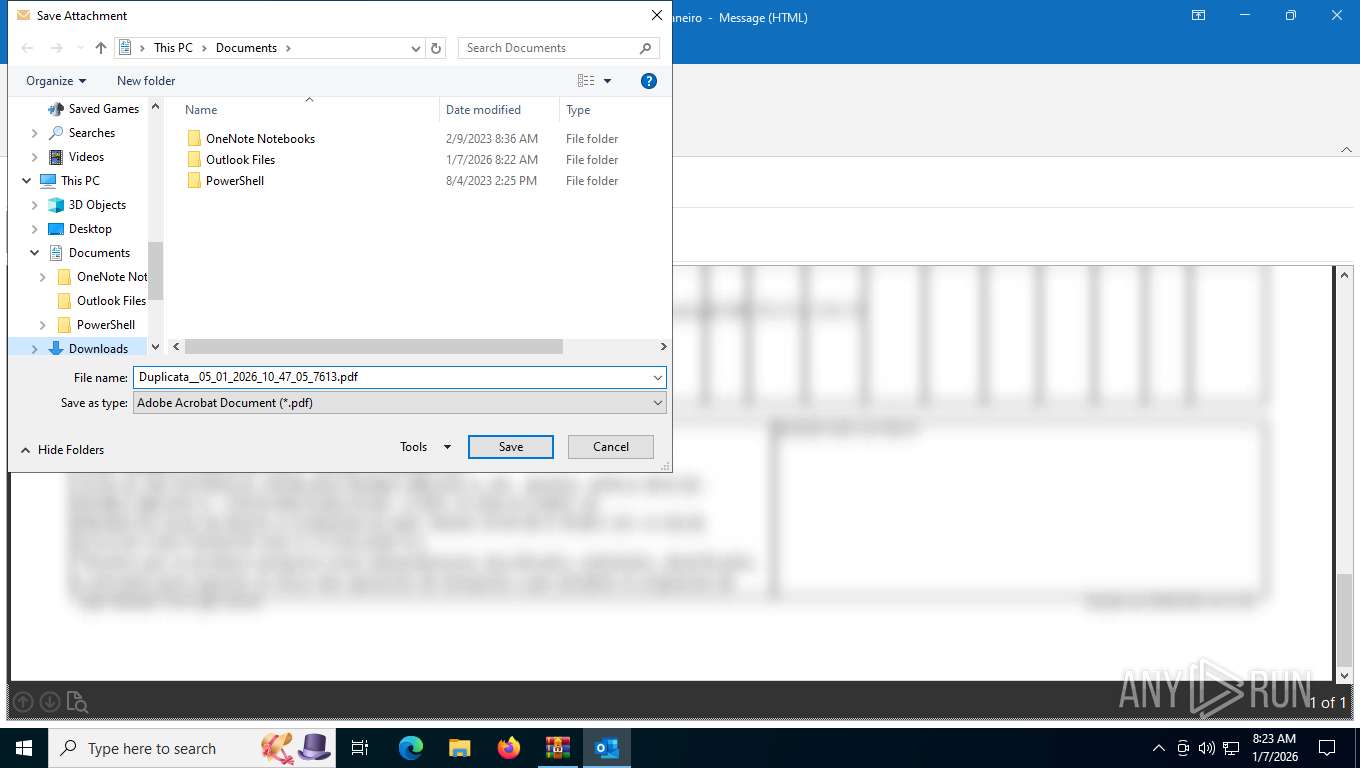
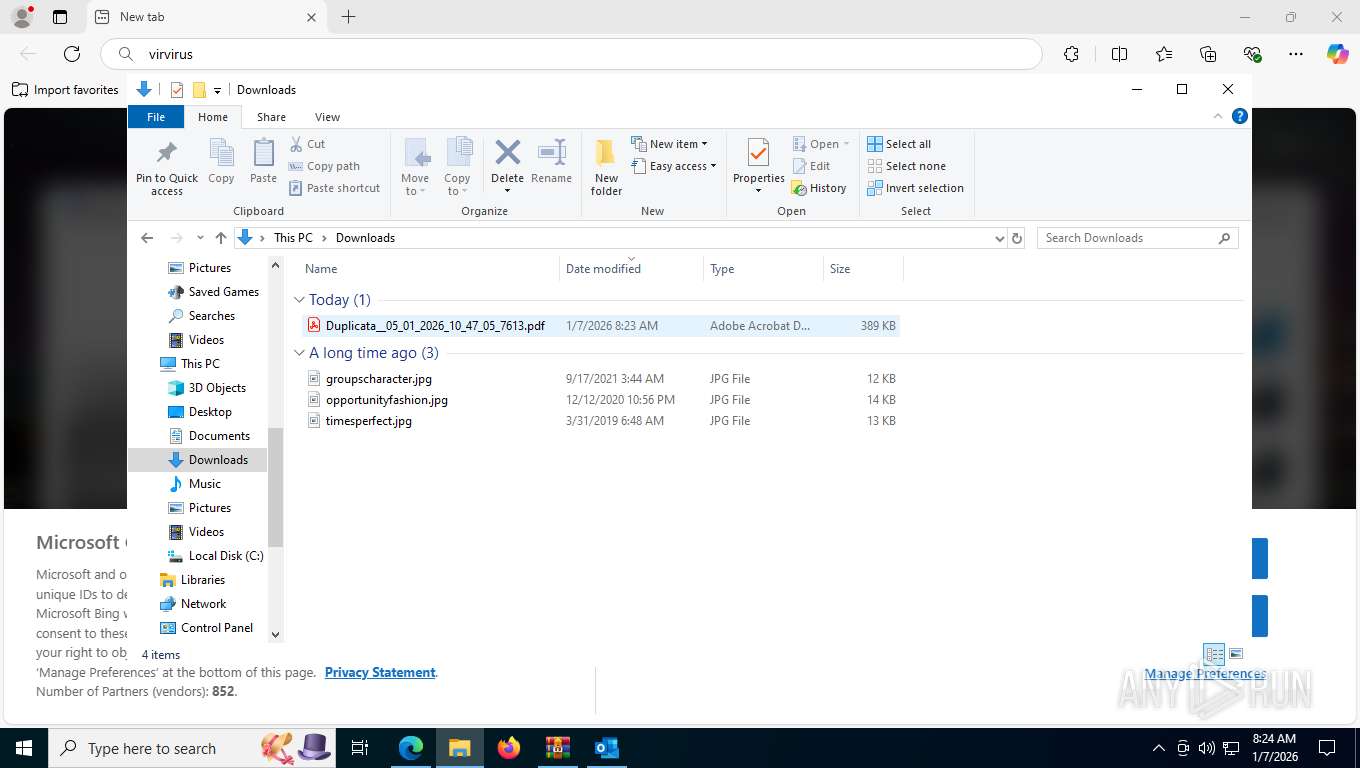
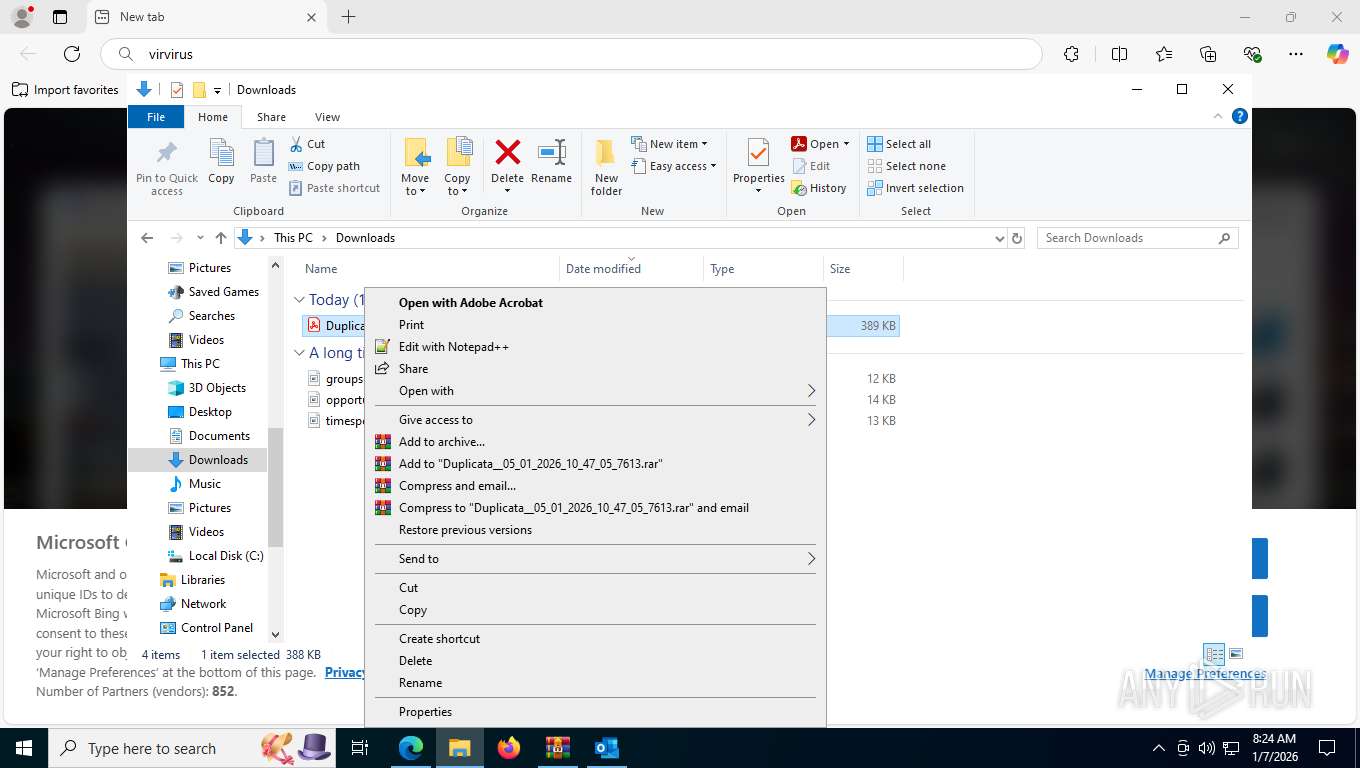
| 1780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument C:\Users\admin\Downloads\Duplicata__05_01_2026_10_47_05_7613.pdf | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | OpenWith.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
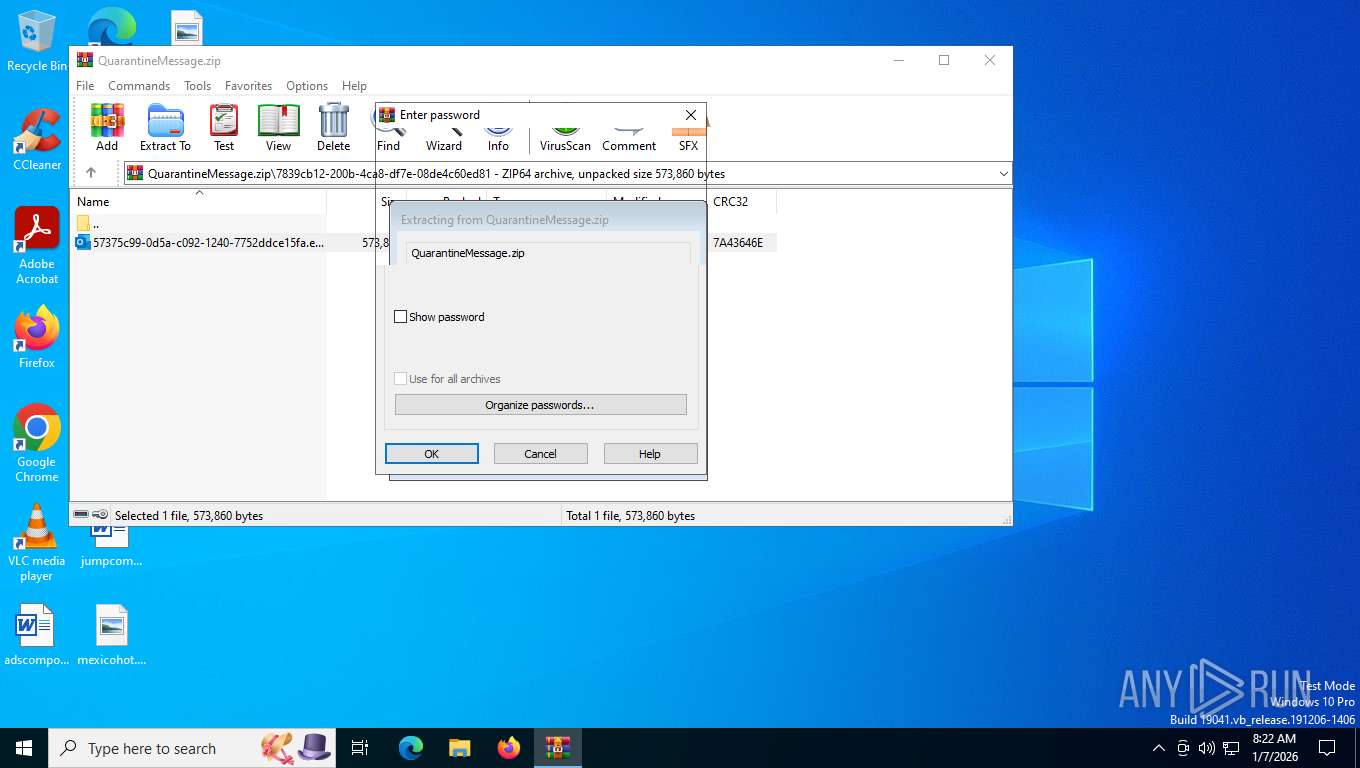
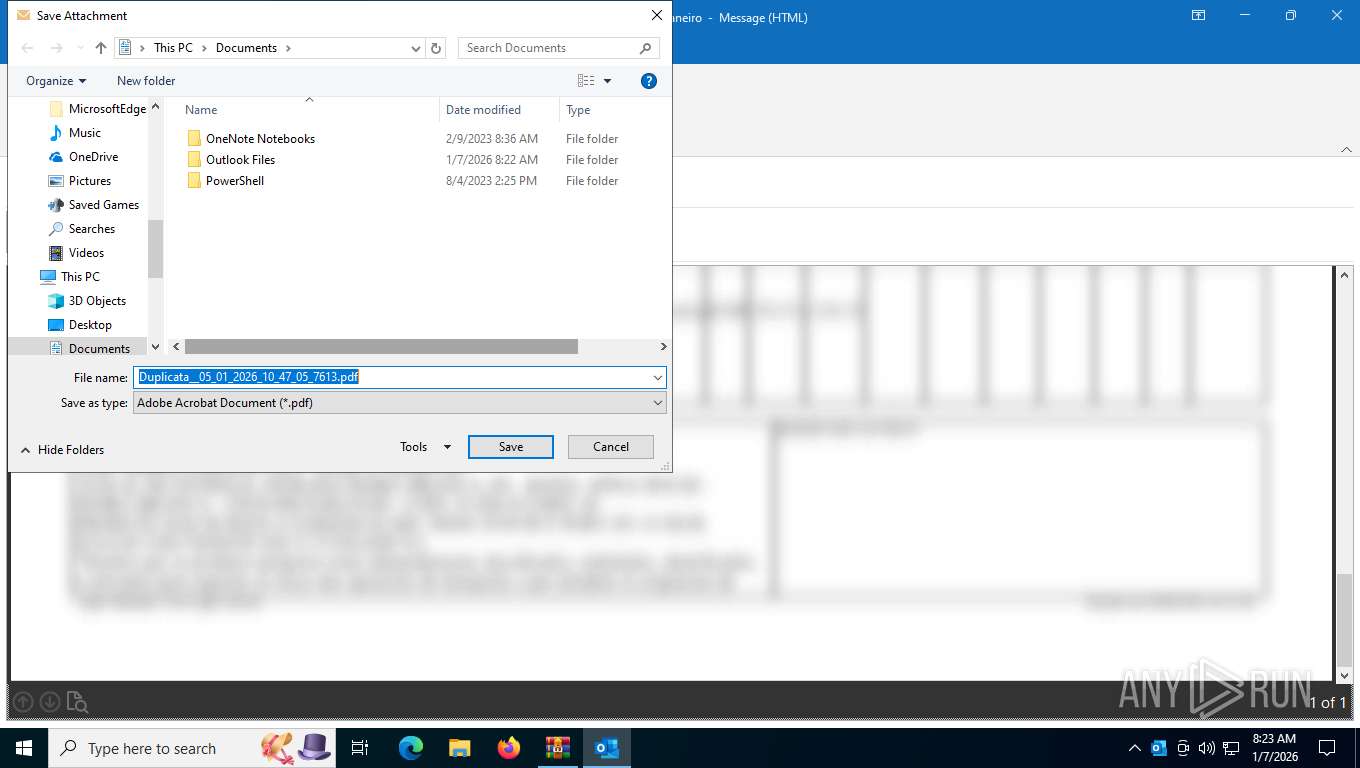
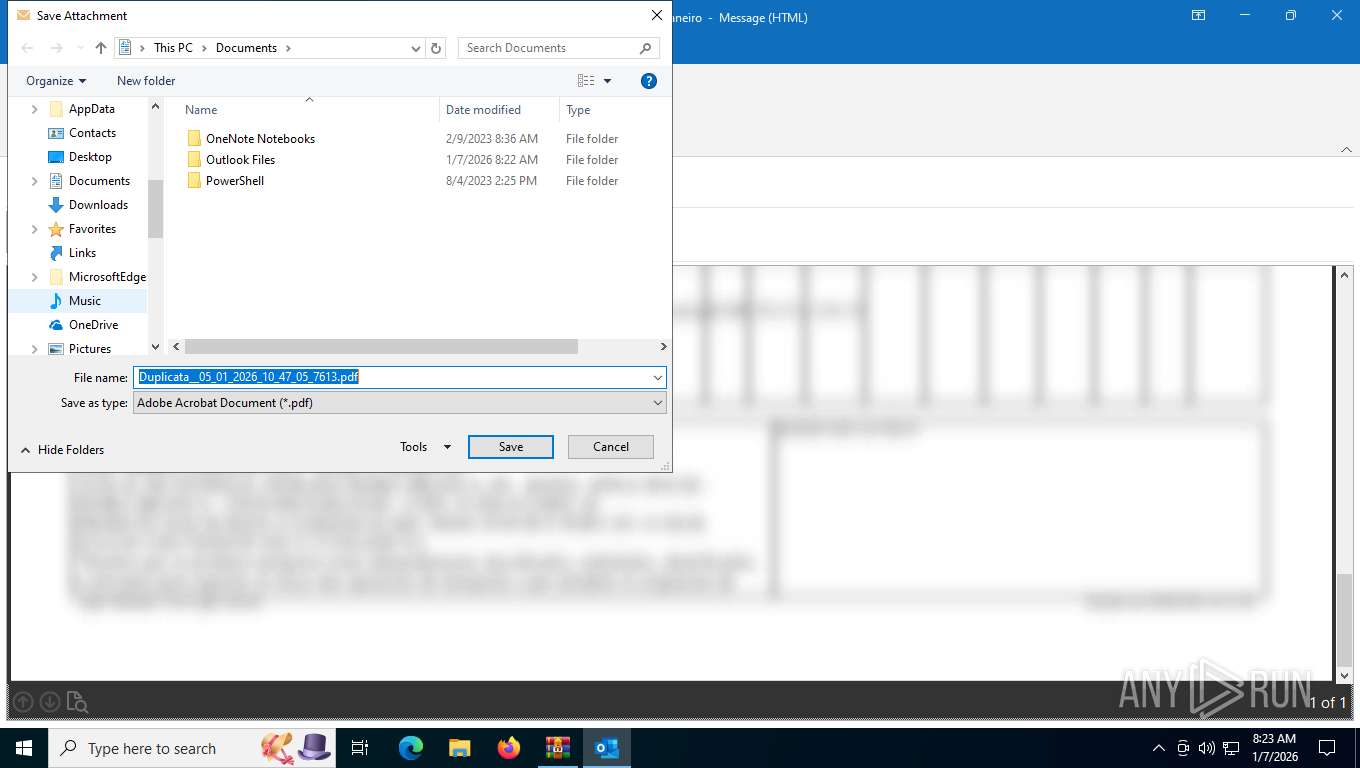
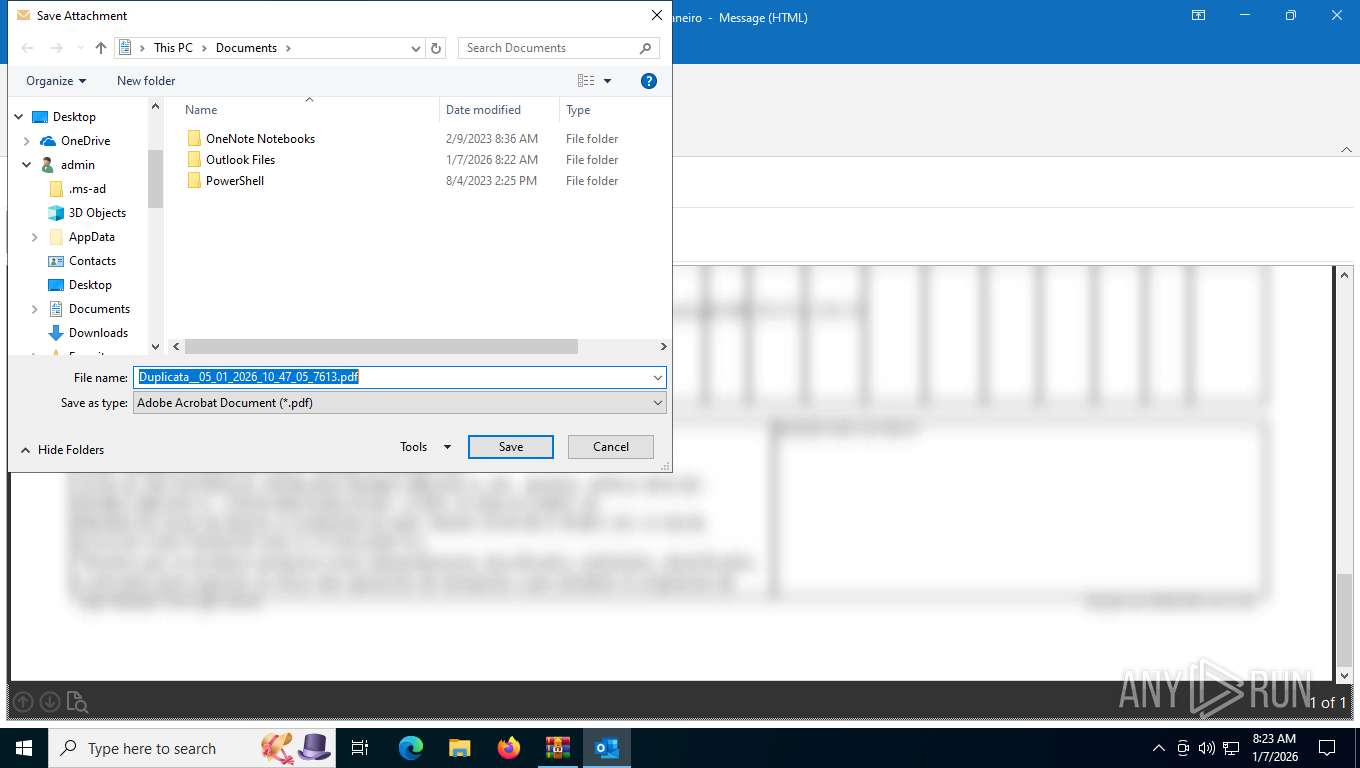
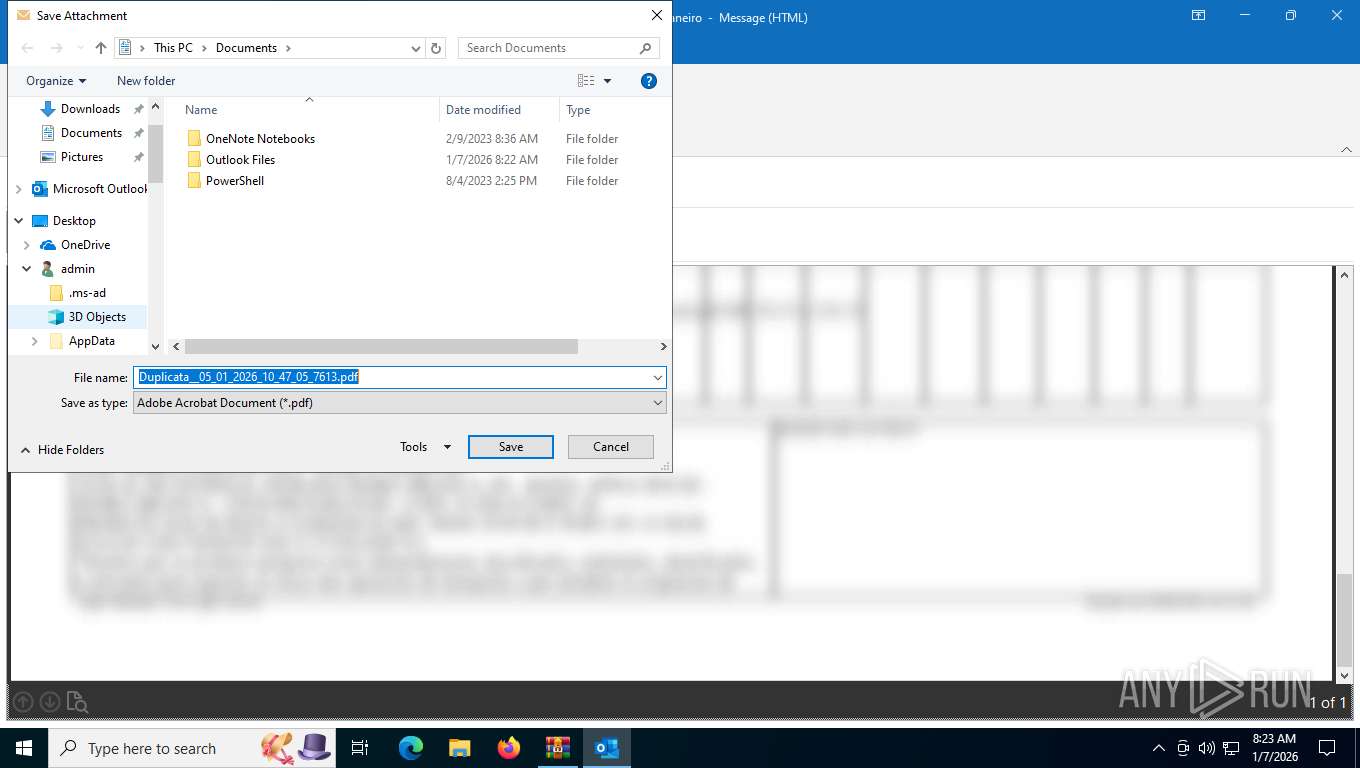
| 2424 | "C:\Program Files\Microsoft Office\Root\Office16\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Rar$DIb7600.28837\57375c99-0d5a-c092-1240-7752ddce15fa.eml" | C:\Program Files\Microsoft Office\root\Office16\OUTLOOK.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 2508 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2320,i,16245265200338075717,13139417488263327447,262144 --variations-seed-version --mojo-platform-channel-handle=2292 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
25 766
Read events
24 473
Write events
1 146
Delete events
147
Modification events
| (PID) Process: | (7600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\QuarantineMessage.zip | |||
| (PID) Process: | (7600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (7600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.eml\OpenWithProgids |
| Operation: | write | Name: | Outlook.File.eml.15 |
Value: | |||
Executable files
27
Suspicious files
425
Text files
318
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2424 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 7600 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb7600.28837\57375c99-0d5a-c092-1240-7752ddce15fa.eml:OECustomProperty | binary | |
MD5:9F2417EB64F2912EA5A917561E194D48 | SHA256:672AE9895B5AB5ACA9332A6CE202C8D7AB5CC5E14F9132BC32CDF04A3B33E558 | |||
| 7600 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb7600.28837\57375c99-0d5a-c092-1240-7752ddce15fa.eml | binary | |
MD5:92BB3B24FDE84E03FE4D67F271A5048B | SHA256:54645867AE96F3188EC254B196DB2AFDB00999C983D750416353C5E54304B307 | |||
| 2424 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_6372E0472AFF76BB926C97818BC773B9 | binary | |
MD5:53D9AE4896D366B1B7B7E9D65778CB0E | SHA256:801256CF63E8546D42E19402F06B316FF870FEF75752028A101229B6D1ABFC82 | |||
| 2424 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntitiesUpdated.bin | text | |
MD5:478AEAEF3371ED83E91DD37A4F3EBDFF | SHA256:171979B48938F07E91E0985716CDB838F2410B466D0360F634A0FEF3A2AB15B9 | |||
| 2424 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_DBE94A85F8649B4FBBEA7ED958BFE171.dat | xml | |
MD5:9CA1DA1D62A9FF574E63B8946B541C96 | SHA256:B6B10A07FAA634027F3780E77FC3B165DCF7D37E800195BFF5E147CCC492B828 | |||
| 2424 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\olk6582.tmp | binary | |
MD5:C586A98A5AC1E82996B1C8638B0A6D52 | SHA256:2FC293333DFE576E22CF96016807CDCDFDD1B853DCADBEE8D8ABB5518C3BC776 | |||
| 2424 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:F67A362FEB31601A74EB3544B9DD3A48 | SHA256:AF947F61034DC574FE7D849DA847F48322A6D64261D6F58512FF31B31CAAD9E7 | |||
| 2424 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\FC346320-4298-4E21-B201-F1DA36B4091F | xml | |
MD5:C9C63D141AE0CA005F623E4B1B5247A9 | SHA256:27CB08E4CD53EAE84B0734A3E6B8EC8F4604CD8FCD8594E9554F6348D0B4CD39 | |||
| 2424 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:822CCBF2C1497461056CB73B0F6591D6 | SHA256:82DDED03B8E21A1D37F56ED42C810BF45504AD5651C5CC430F46D5BEF090AE33 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
505
TCP/UDP connections
121
DNS requests
99
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | US | — | — | whitelisted |
1164 | svchost.exe | POST | 200 | 20.190.160.64:443 | https://login.live.com/RST2.srf | US | xml | 11.1 Kb | whitelisted |
7508 | SIHClient.exe | GET | 200 | 13.85.23.206:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
2392 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
7508 | SIHClient.exe | GET | 200 | 74.179.77.204:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
7508 | SIHClient.exe | GET | 304 | 74.179.77.204:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
1164 | svchost.exe | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
2392 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
1164 | svchost.exe | POST | 200 | 20.190.160.64:443 | https://login.live.com/RST2.srf | US | xml | 10.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6236 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2392 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3412 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1164 | svchost.exe | 20.190.160.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1164 | svchost.exe | 172.66.2.5:80 | ocsp.digicert.com | CLOUDFLARENET | US | whitelisted |
2392 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2392 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6244 | msedge.exe | Misc activity | ET INFO URL Shortener Service Domain in DNS Lookup (is .gd) |
6244 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (is .gd) |
6244 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (is .gd) |
6244 | msedge.exe | Misc activity | ET INFO URL Shortener Service Domain in DNS Lookup (is .gd) |
— | — | Potentially Bad Traffic | ET ATTACK_RESPONSE PowerShell NoProfile Command Received In Powershell Stagers |
— | — | Potentially Bad Traffic | ET HUNTING schtasks change Command in HTTP Body Response |
— | — | A Network Trojan was detected | LOADER [ANY.RUN] Gen.Powershell.Downloader Script Payload |