| URL: | https://annasex.us19.list-manage.com/track/click?u=a920eef5d82f47070646173c1&id=b4b9f32cea&e=e92379053d |
| Full analysis: | https://app.any.run/tasks/f48505ae-2e64-4fce-ab50-6030d40eb4b0 |
| Verdict: | Malicious activity |
| Analysis date: | September 18, 2018, 17:36:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 29870D38CF876064D30B2FB1020D2AD2 |
| SHA1: | F69BC9A73A18780DFDC6552E60592654EA38EF6E |
| SHA256: | 267223B3E393F9AF9263016D784C895A327FDE1D4CB759C5E97CC0C41ACEEC11 |
| SSDEEP: | 3:N8NdCWIVULGGRXEGcJMkN+dXAF5Eu4G:2N4NULEGcJMrul |
MALICIOUS
Loads dropped or rewritten executable
- software_reporter_tool.exe (PID: 1792)
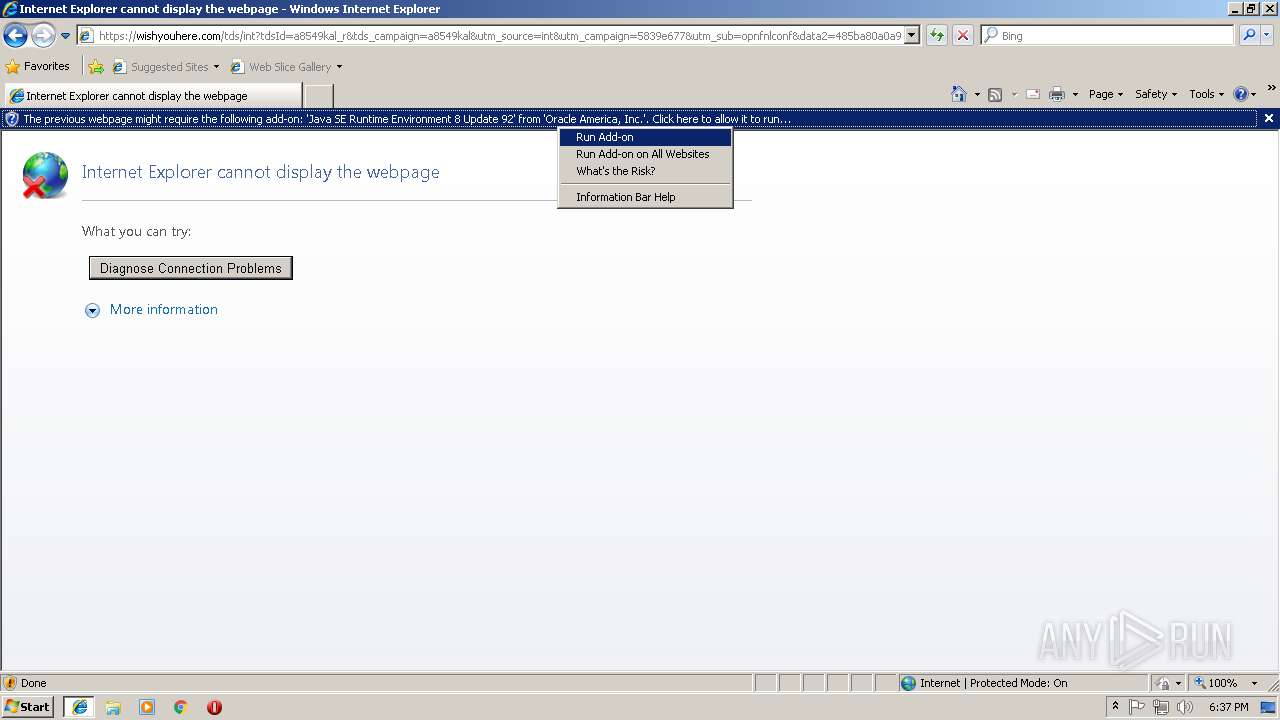
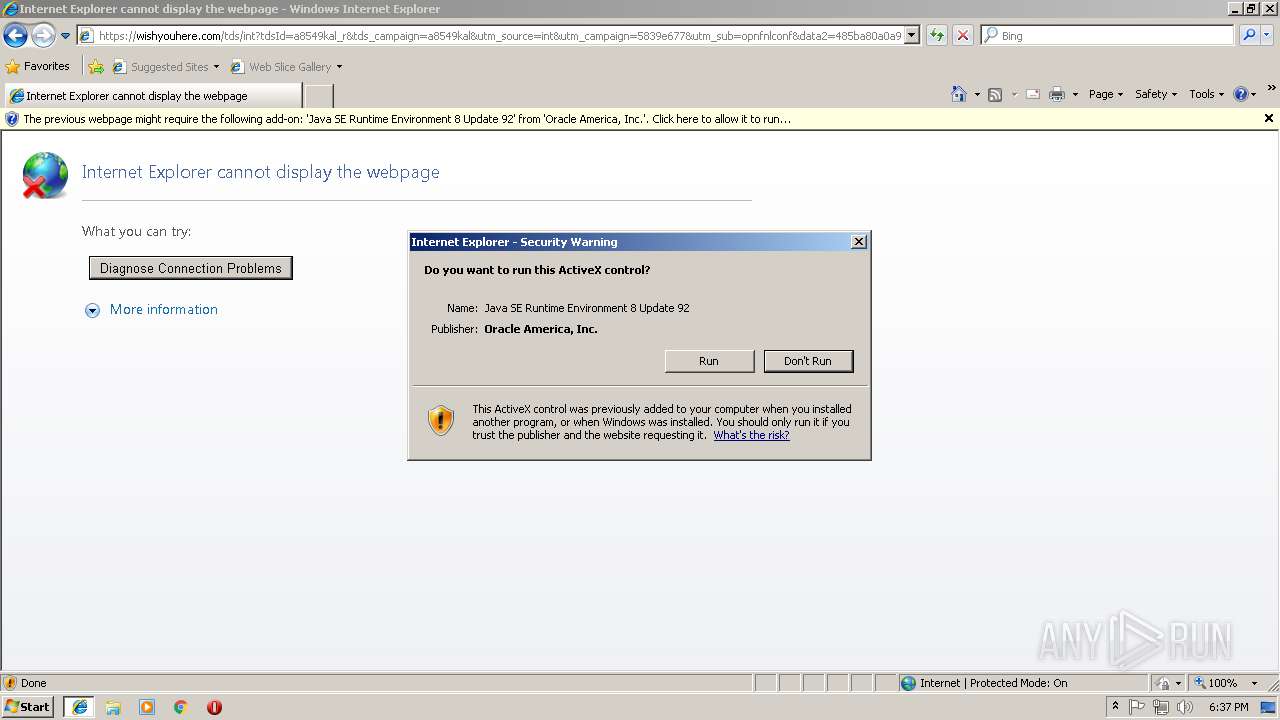
SUSPICIOUS
Executes JAVA applets
- iexplore.exe (PID: 3128)
Application launched itself
- software_reporter_tool.exe (PID: 2768)
- software_reporter_tool.exe (PID: 4032)
Executable content was dropped or overwritten
- software_reporter_tool.exe (PID: 1792)
Check for Java to be installed
- iexplore.exe (PID: 3128)
Searches for installed software
- software_reporter_tool.exe (PID: 1792)
INFO
Creates files in the user directory
- iexplore.exe (PID: 3128)
- iexplore.exe (PID: 3204)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3068)
Application launched itself
- iexplore.exe (PID: 3204)
- chrome.exe (PID: 2080)
Reads Internet Cache Settings
- iexplore.exe (PID: 3128)
Loads the Task Scheduler COM API
- software_reporter_tool.exe (PID: 2768)
- software_reporter_tool.exe (PID: 4032)
Reads internet explorer settings
- iexplore.exe (PID: 3128)
Changes settings of System certificates
- chrome.exe (PID: 2080)
Changes internet zones settings
- iexplore.exe (PID: 3204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
57
Monitored processes
25
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,12630670311130784881,211485738681116169,131072 --enable-features=PasswordImport --service-pipe-token=81E8C89D6BCAC2F8FF9EEA32476DB86A --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=81E8C89D6BCAC2F8FF9EEA32476DB86A --renderer-client-id=6 --mojo-platform-channel-handle=2140 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 600 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_9\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.suppression.11.92.2" "false" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | iexplore.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: LOW Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=916,12630670311130784881,211485738681116169,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7AF04FC9A534DD5438EAD39D24D35162 --mojo-platform-channel-handle=3784 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,12630670311130784881,211485738681116169,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=0BB6C9CB40CF667B393467548349A606 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=0BB6C9CB40CF667B393467548349A606 --renderer-client-id=7 --mojo-platform-channel-handle=3768 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,12630670311130784881,211485738681116169,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=9AFF3A15BE15FFB0CF482965302C0CC5 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9AFF3A15BE15FFB0CF482965302C0CC5 --renderer-client-id=12 --mojo-platform-channel-handle=3820 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1792 | "c:\users\admin\appdata\local\google\chrome\user data\swreporter\33.170.201\software_reporter_tool.exe" --use-crash-handler-with-id="\\.\pipe\crashpad_4032_XILMKVYRWTDRJOWA" --sandboxed-process-id=2 --init-done-notifier=344 --sandbox-mojo-pipe-token=D617F577AA61840F2F9B8E54CAABF712 --mojo-platform-channel-handle=280 --engine=2 | c:\users\admin\appdata\local\google\chrome\user data\swreporter\33.170.201\software_reporter_tool.exe | software_reporter_tool.exe | ||||||||||||
User: admin Company: Google Integrity Level: MEDIUM Description: Software Reporter Tool Exit code: 0 Version: 33.170.201 Modules
| |||||||||||||||
| 1972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=916,12630670311130784881,211485738681116169,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=07E6AE85D0147FE5B7AF4B9FBB8EAEF0 --mojo-platform-channel-handle=1480 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,12630670311130784881,211485738681116169,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=C2D886D04AAE04AF18DB8C76D519B5FD --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=C2D886D04AAE04AF18DB8C76D519B5FD --renderer-client-id=9 --mojo-platform-channel-handle=3388 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=916,12630670311130784881,211485738681116169,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=34AD816A9805CC8ED9C59315FB1C30FE --mojo-platform-channel-handle=3836 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 357
Read events
1 097
Write events
240
Delete events
20
Modification events
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005C000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {757481D3-BB69-11E8-BFAB-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070900020012001100250006009802 | |||
Executable files
7
Suspicious files
40
Text files
72
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3204 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3128 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@wooga2[1].txt | — | |
MD5:— | SHA256:— | |||
| 3128 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U2ZG9DE0\pNHB[1].txt | — | |
MD5:— | SHA256:— | |||
| 3128 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab722.tmp | — | |
MD5:— | SHA256:— | |||
| 3128 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar723.tmp | — | |
MD5:— | SHA256:— | |||
| 3128 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab734.tmp | — | |
MD5:— | SHA256:— | |||
| 3128 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar735.tmp | — | |
MD5:— | SHA256:— | |||
| 3128 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab7B3.tmp | — | |
MD5:— | SHA256:— | |||
| 3128 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar7B4.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
43
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3204 | iexplore.exe | GET | 200 | 35.157.252.211:80 | http://wooga2.info/favicon.ico | DE | — | — | unknown |
3128 | iexplore.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 53.8 Kb | whitelisted |
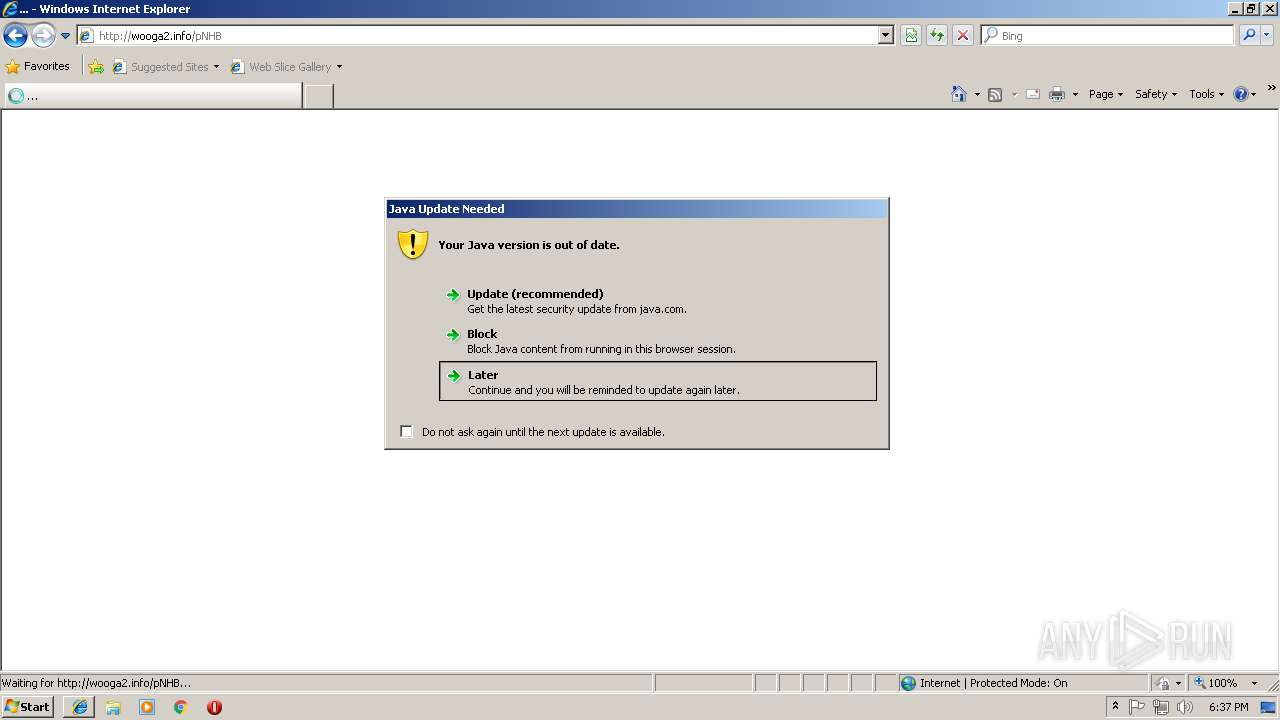
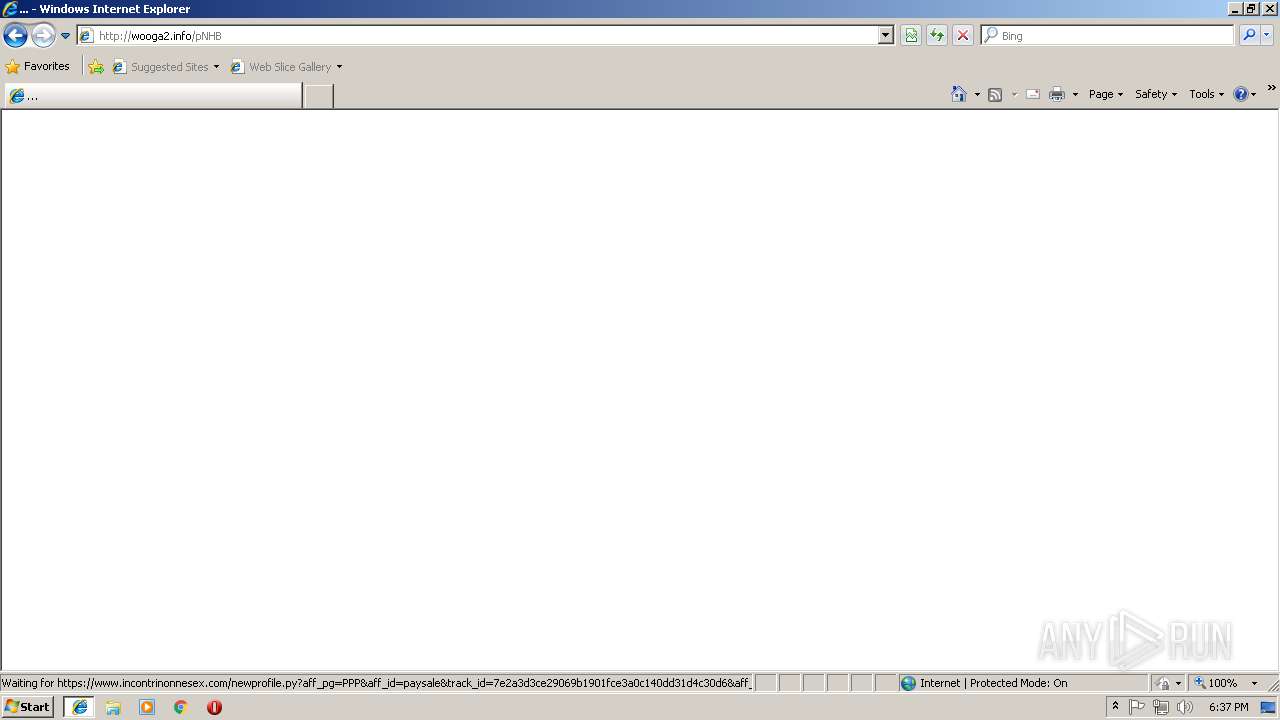
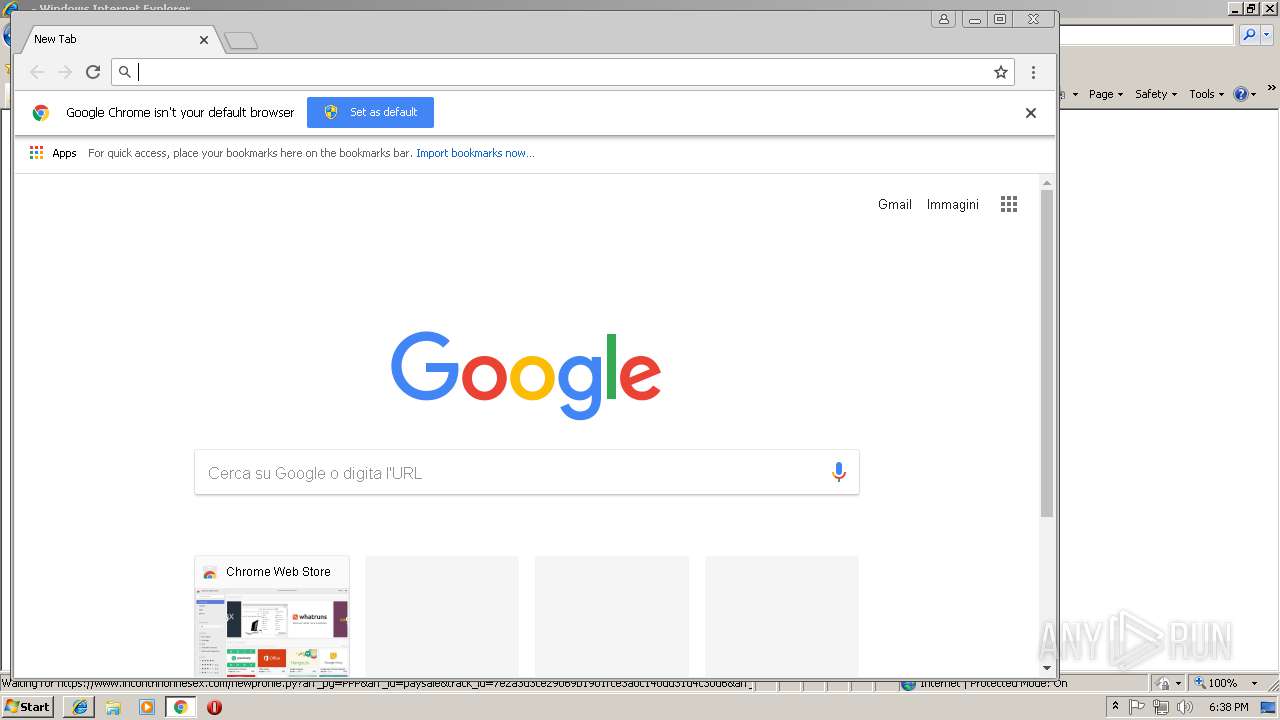
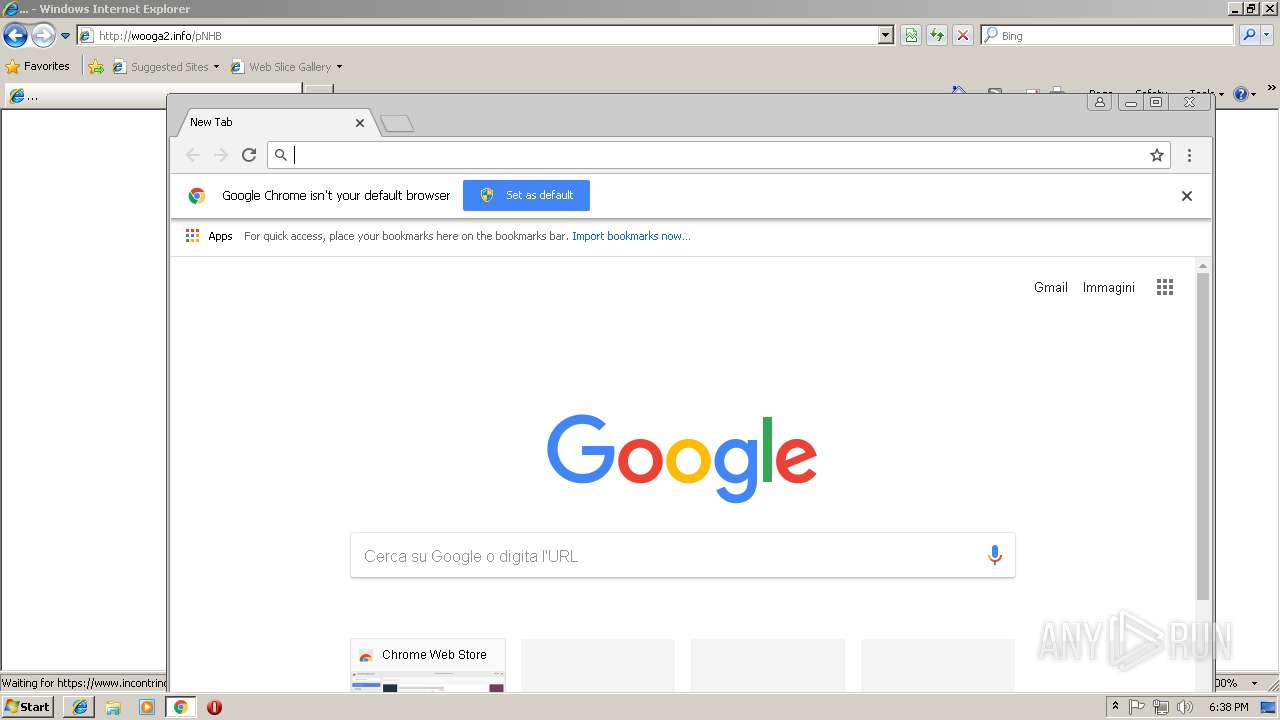
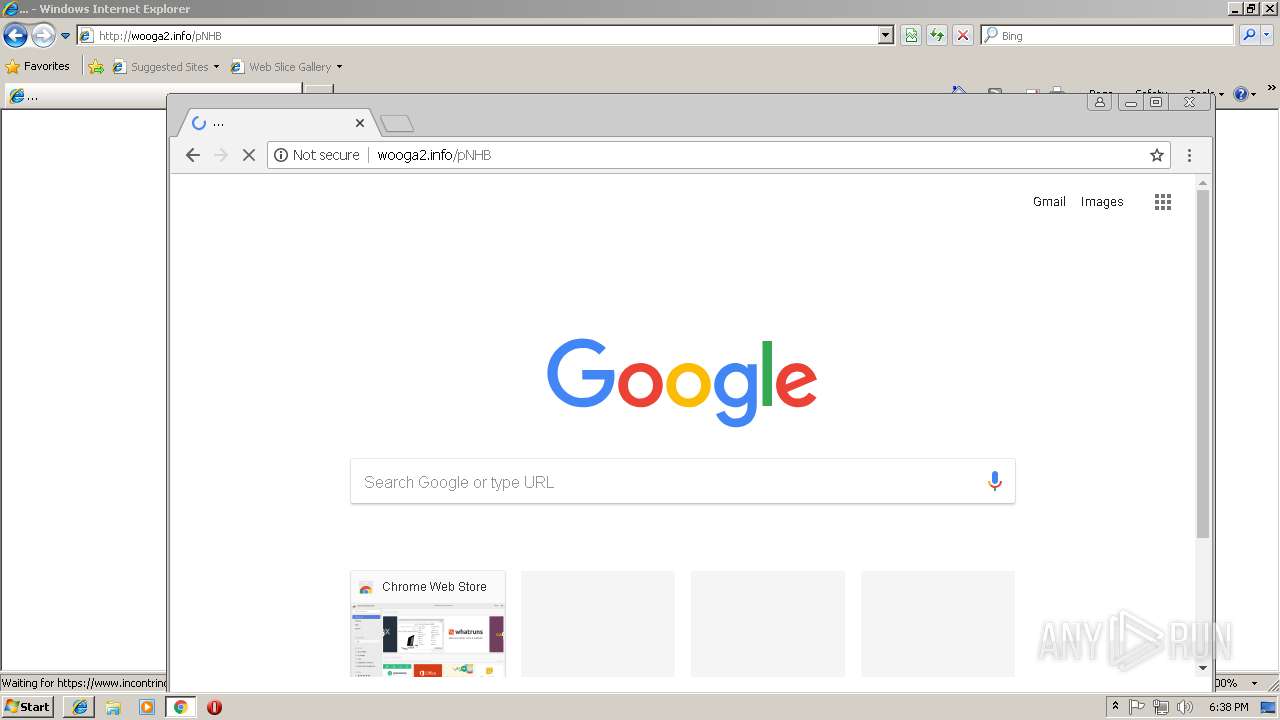
3128 | iexplore.exe | GET | 200 | 35.157.252.211:80 | http://wooga2.info/pNHB | DE | html | 6.70 Kb | unknown |
3128 | iexplore.exe | GET | 304 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 53.8 Kb | whitelisted |
2080 | chrome.exe | GET | 200 | 54.192.94.130:80 | http://dhwazjqhzfp7d.cloudfront.net/assets/application-55532ffc0ccf334323bc935e9e1072a3fe016a2d03956a28042c2c69a13c4654.js | US | text | 49.8 Kb | whitelisted |
3128 | iexplore.exe | GET | 301 | 54.83.52.76:80 | http://bit.do/ewXbH | US | html | 303 b | shared |
3128 | iexplore.exe | GET | 200 | 35.157.252.211:80 | http://wooga2.info/pNHB | DE | html | 6.67 Kb | unknown |
3128 | iexplore.exe | POST | 200 | 35.157.252.211:80 | http://wooga2.info/post/data | DE | compressed | 6.70 Kb | unknown |
2080 | chrome.exe | POST | 200 | 18.184.84.52:80 | http://wooga2.info/post/data | US | compressed | 6.71 Kb | unknown |
3204 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3204 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3128 | iexplore.exe | 104.108.52.148:443 | annasex.us19.list-manage.com | Akamai Technologies, Inc. | NL | whitelisted |
3128 | iexplore.exe | 35.157.252.211:80 | wooga2.info | Amazon.com, Inc. | DE | unknown |
3128 | iexplore.exe | 54.192.94.158:80 | dhwazjqhzfp7d.cloudfront.net | Amazon.com, Inc. | US | unknown |
3204 | iexplore.exe | 35.157.252.211:80 | wooga2.info | Amazon.com, Inc. | DE | unknown |
3128 | iexplore.exe | 52.29.55.65:443 | wishyouhere.com | Amazon.com, Inc. | DE | unknown |
3128 | iexplore.exe | 54.192.94.211:80 | x.ss2.us | Amazon.com, Inc. | US | whitelisted |
3128 | iexplore.exe | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3128 | iexplore.exe | 66.154.93.230:443 | www.incontrinonnesex.com | Cyber Wurx LLC | US | unknown |
2080 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
annasex.us19.list-manage.com |
| unknown |
bit.do |
| shared |
wooga2.info |
| unknown |
dhwazjqhzfp7d.cloudfront.net |
| whitelisted |
wishyouhere.com |
| unknown |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
www.loveaholics.com |
| suspicious |
www.incontrinonnesex.com |
| unknown |