| File name: | testest.msi |
| Full analysis: | https://app.any.run/tasks/b1bacd88-e0c3-44e0-b290-3306d386f676 |
| Verdict: | Malicious activity |
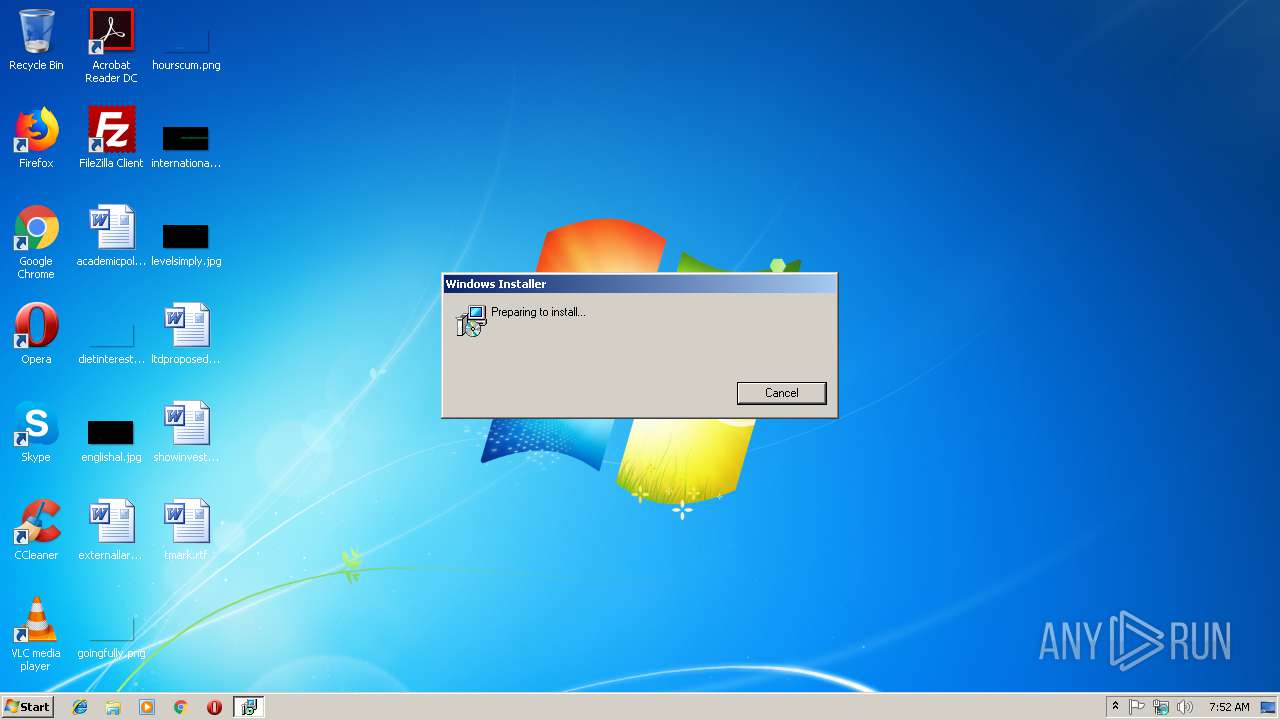
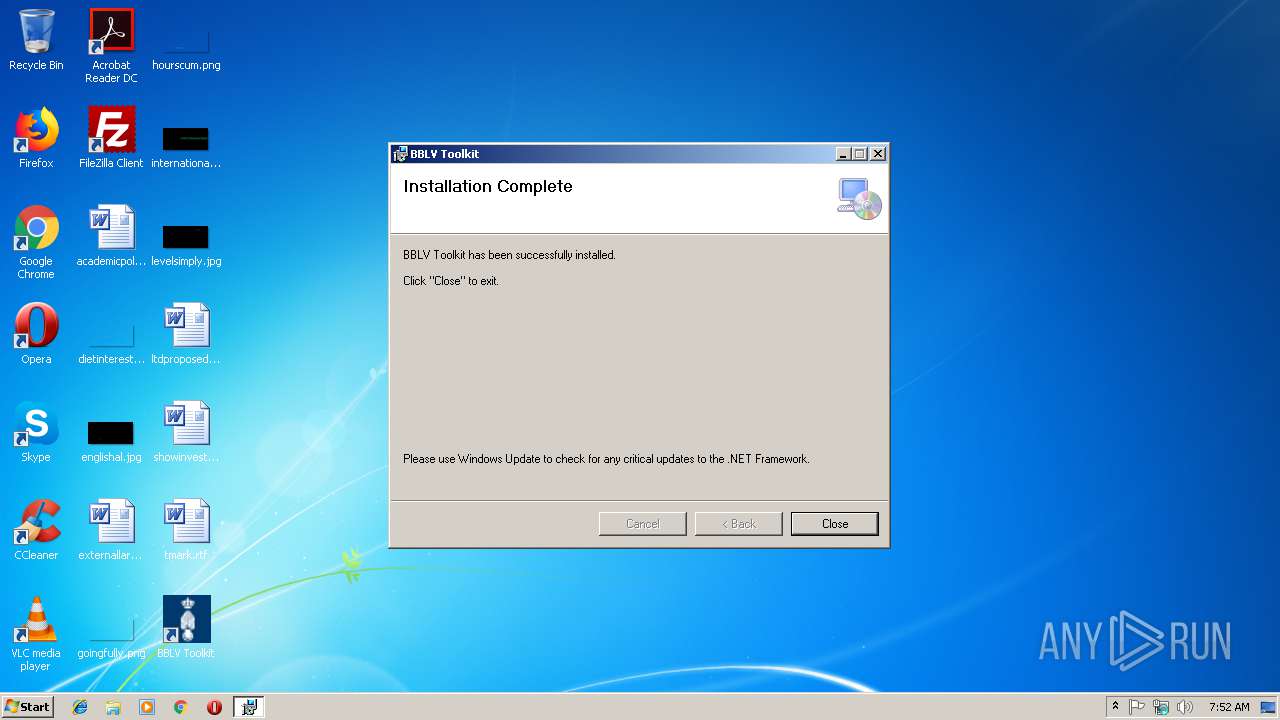
| Analysis date: | December 06, 2018, 07:52:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-msi |
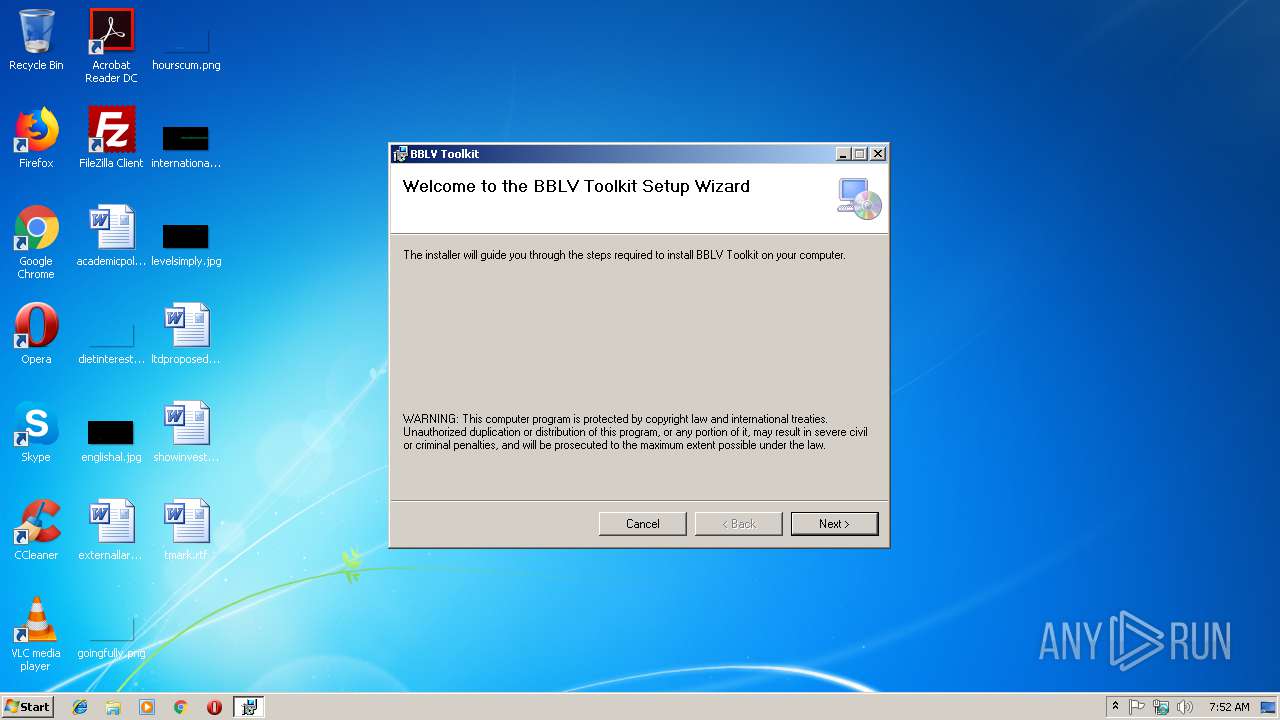
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, MSI Installer, Create Time/Date: Mon Jun 21 08:00:00 1999, Name of Creating Application: Windows Installer, Security: 1, Code page: 1252, Template: Intel;1033, Number of Pages: 200, Revision Number: {C6713ABA-9A7A-43C5-9DE9-DBD4E477A9EE}, Title: BBLV Toolkit, Author: IVENT, Number of Words: 2, Last Saved Time/Date: Mon Mar 13 09:46:04 2017, Last Printed: Mon Mar 13 09:46:04 2017 |
| MD5: | 2BBB072457EFDD15B9033695B7AC997A |
| SHA1: | 7899CE132A1872EC6FF75D72C814DBDF8343001E |
| SHA256: | 266B9672C07C9D1D15D919C8BEAA73645FFB33601C5EFD636F312085459B2C9F |
| SSDEEP: | 12288:qO24xEXlQUAZKaEmTO9sD1BM6Qj1cRYztmNpGpqhLDW/b:qONUAfBNQepNpAqQ |
MALICIOUS
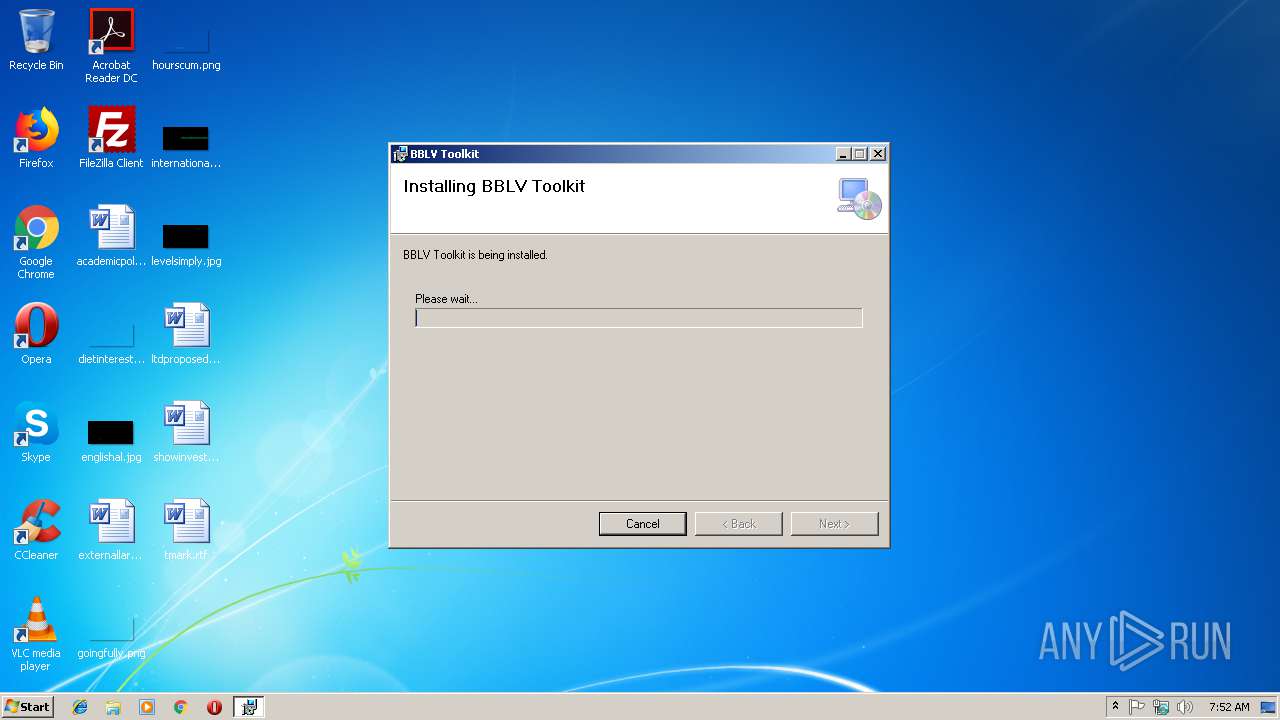
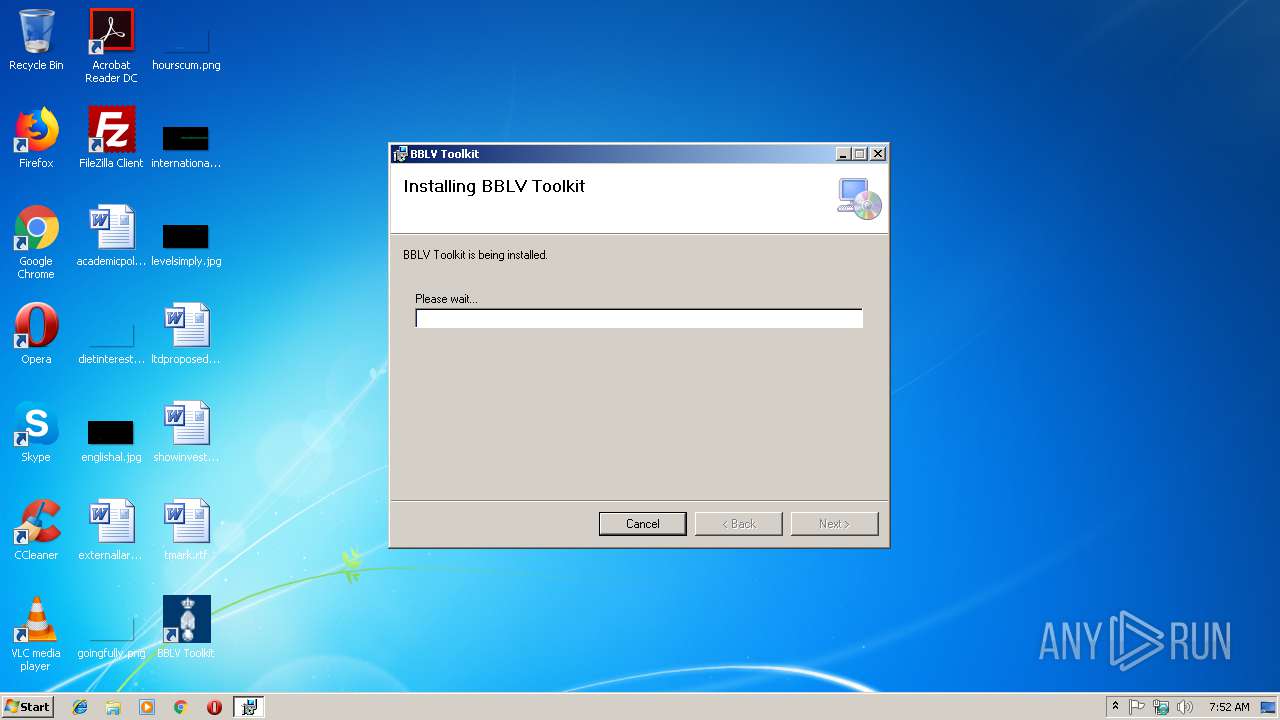
Application was dropped or rewritten from another process
- Toolkit.exe (PID: 3820)
Loads dropped or rewritten executable
- Toolkit.exe (PID: 3820)
SUSPICIOUS
Executable content was dropped or overwritten
- msiexec.exe (PID: 2576)
Creates files in the user directory
- msiexec.exe (PID: 2576)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 2724)
Searches for installed software
- msiexec.exe (PID: 2576)
Creates files in the program directory
- msiexec.exe (PID: 2576)
Application launched itself
- msiexec.exe (PID: 2576)
Creates a software uninstall entry
- msiexec.exe (PID: 2576)
Loads dropped or rewritten executable
- msiexec.exe (PID: 2576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (90.2) |
|---|---|---|
| .msp | | | Windows Installer Patch (8.4) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CreateDate: | 1999:06:21 07:00:00 |
|---|---|
| Software: | Windows Installer |
| Security: | Password protected |
| CodePage: | Windows Latin 1 (Western European) |
| Template: | Intel;1033 |
| Pages: | 200 |
| RevisionNumber: | {C6713ABA-9A7A-43C5-9DE9-DBD4E477A9EE} |
| Title: | BBLV Toolkit |
| Subject: | - |
| Author: | IVENT |
| Keywords: | - |
| Comments: | - |
| Words: | 2 |
| ModifyDate: | 2017:03:13 09:46:04 |
| LastPrinted: | 2017:03:13 09:46:04 |
Total processes
39
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2272 | C:\Windows\system32\MsiExec.exe -Embedding A774AA03716ED663993185563805B63C C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2344 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "00000550" "00000330" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2576 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2724 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2984 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\testest.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
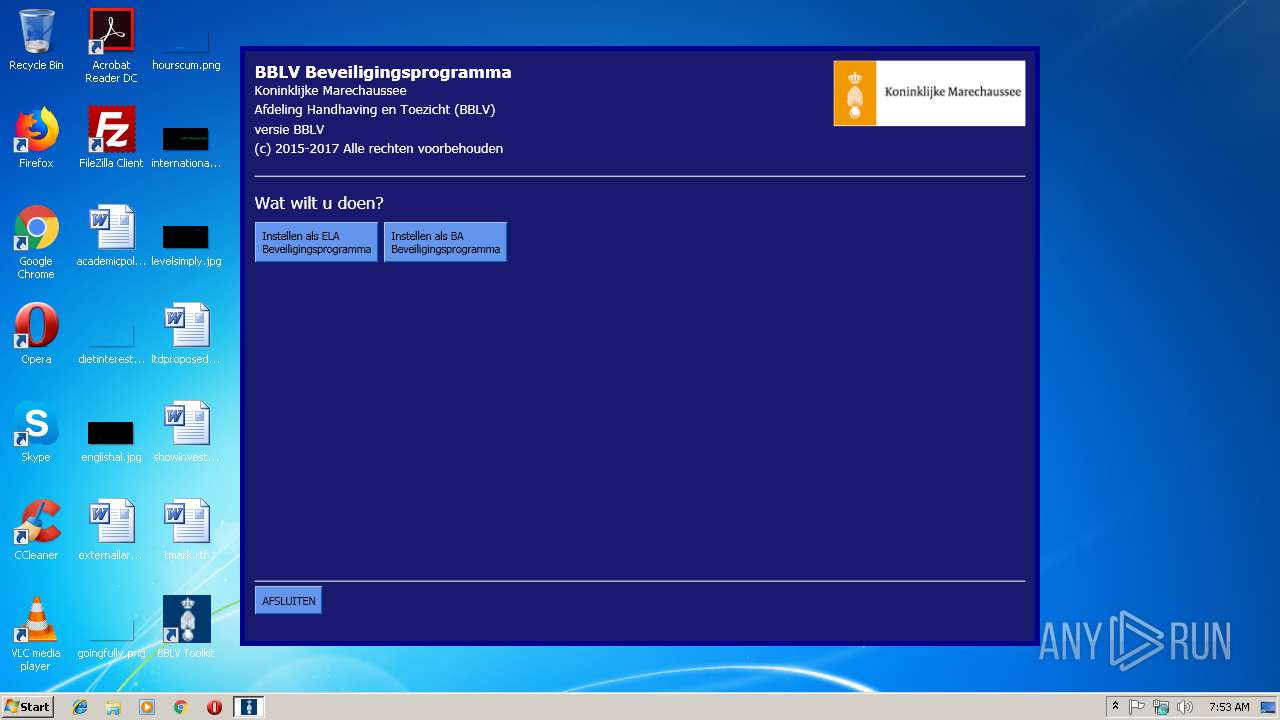
| 3820 | "C:\Program Files\IVENT\BBLV Toolkit\Toolkit.exe" | C:\Program Files\IVENT\BBLV Toolkit\Toolkit.exe | — | explorer.exe | |||||||||||
User: admin Company: IVENT Integrity Level: MEDIUM Description: applicatie Beveiligingsprogramma Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3916 | C:\Windows\system32\MsiExec.exe -Embedding 9B4E290051A0CE91F185158CC0031BD9 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
635
Read events
348
Write events
275
Delete events
12
Modification events
| (PID) Process: | (2984) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2576) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 400000000000000032EA99A8388DD401100A0000CC090000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2576) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 400000000000000032EA99A8388DD401100A0000CC090000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2576) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 20 | |||
| (PID) Process: | (2576) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000125B0CA9388DD401100A0000CC090000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2576) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000006CBD0EA9388DD401100A00008C080000E8030000010000000000000000000000F14088ED72F0DE478F1BA78511A3DB250000000000000000 | |||
| (PID) Process: | (2724) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D44618A9388DD401A40A0000DC0C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2724) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D44618A9388DD401A40A000020090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2724) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D44618A9388DD401A40A000014090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2724) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D44618A9388DD401A40A0000D80C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
8
Suspicious files
6
Text files
77
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2984 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI6EC8.tmp | — | |
MD5:— | SHA256:— | |||
| 2984 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI6F36.tmp | — | |
MD5:— | SHA256:— | |||
| 2576 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2576 | msiexec.exe | C:\Windows\Installer\MSIBB53.tmp | — | |
MD5:— | SHA256:— | |||
| 2576 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF14A42A757B45257B.TMP | — | |
MD5:— | SHA256:— | |||
| 2576 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{ed8840f1-f072-47de-8f1b-a78511a3db25}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
| 2344 | DrvInst.exe | C:\Windows\INF\setupapi.ev3 | binary | |
MD5:— | SHA256:— | |||
| 2576 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
| 2344 | DrvInst.exe | C:\Windows\INF\setupapi.dev.log | ini | |
MD5:— | SHA256:— | |||
| 2724 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report