| File name: | Chipso.rar |
| Full analysis: | https://app.any.run/tasks/f4892f99-ba76-4a15-bad8-b5d23ea7e8d4 |
| Verdict: | Malicious activity |
| Analysis date: | October 26, 2019, 20:20:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
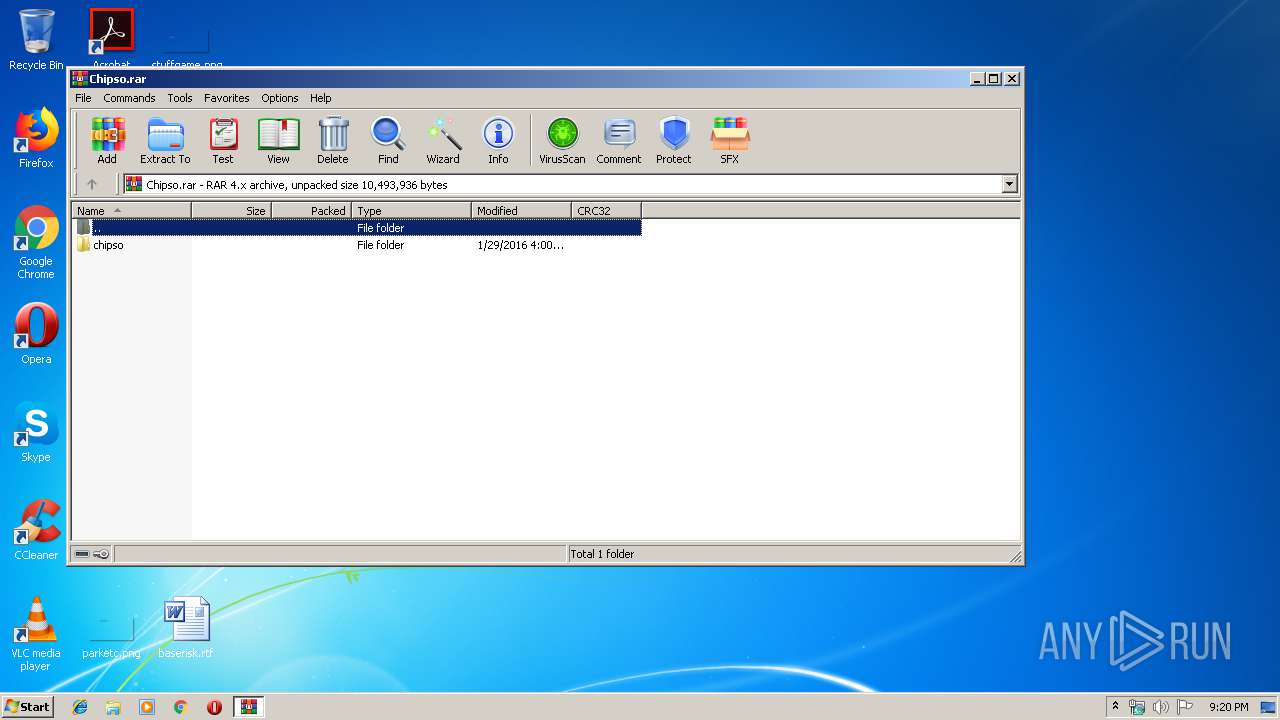
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | E3F51A6AF1913AD76DA67AC43E001F9D |
| SHA1: | 623C59AA7C9CA226318BFFB12552E00CF841ECA7 |
| SHA256: | 266A5C6B6FE74301238E977333B5C3D4EB76D016CBA72CE4D8B9EB46A8424F58 |
| SSDEEP: | 49152:uYUj67PMxadRwr5vy94+BY04MT5fx2JaUJnDL:uFj2MEd2r5K9n91pEhJf |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3488)
- tmp1.jpg (PID: 2356)
- Chips.exe (PID: 1028)
- explorer.exe (PID: 352)
Application was dropped or rewritten from another process
- Chipso-crc.exe (PID: 2856)
- tmp2.exe (PID: 3948)
- tmp1.jpg (PID: 2356)
- emv.exe (PID: 2968)
- Chips.exe (PID: 1028)
Changes the autorun value in the registry
- tmp2.exe (PID: 3948)
SUSPICIOUS
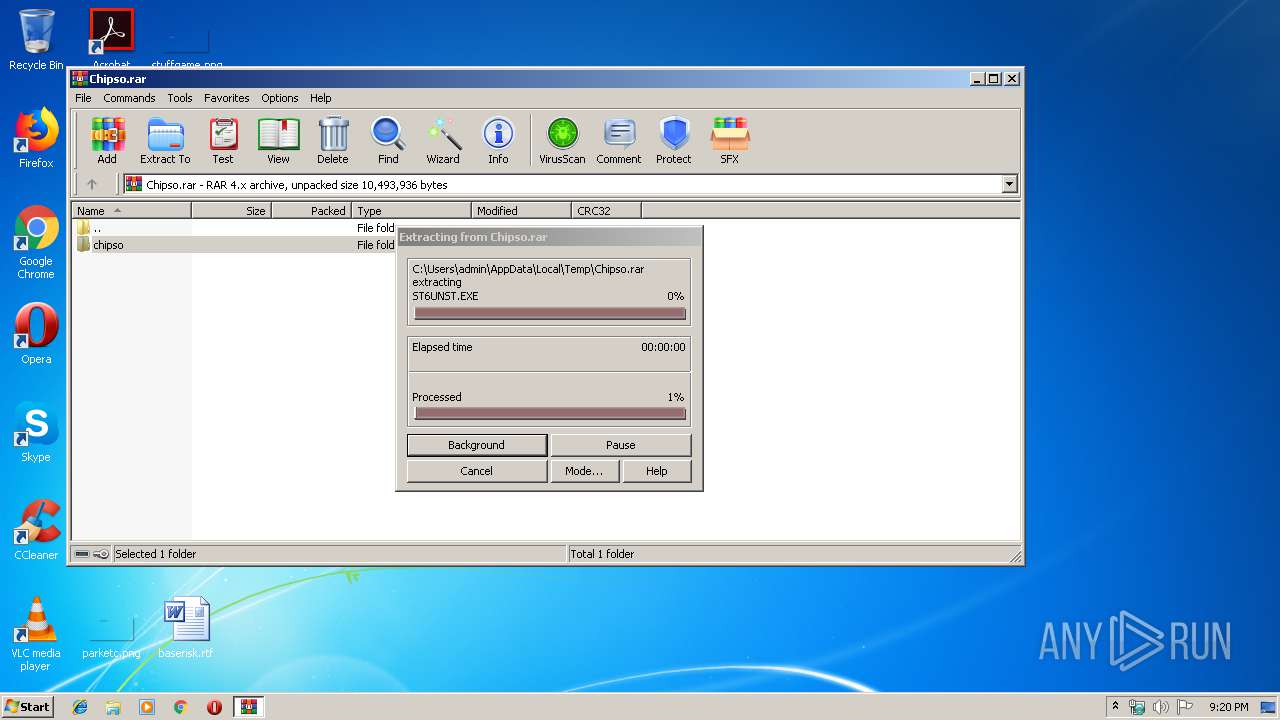
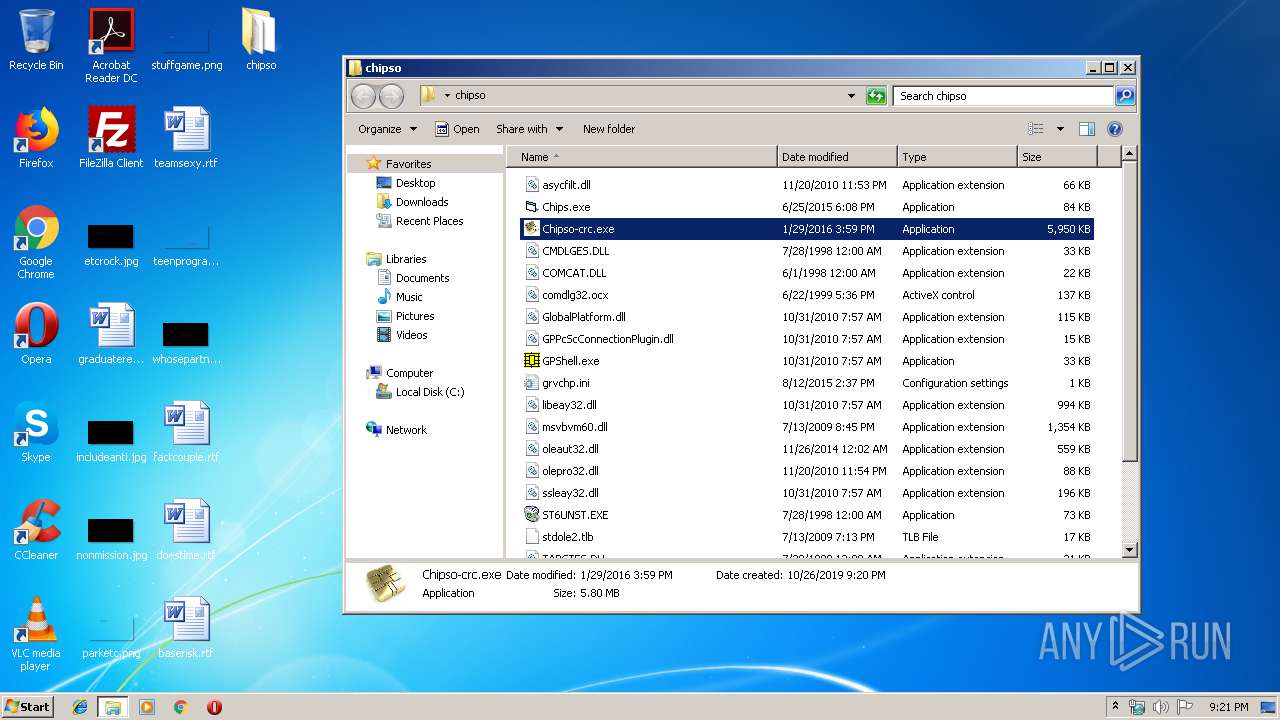
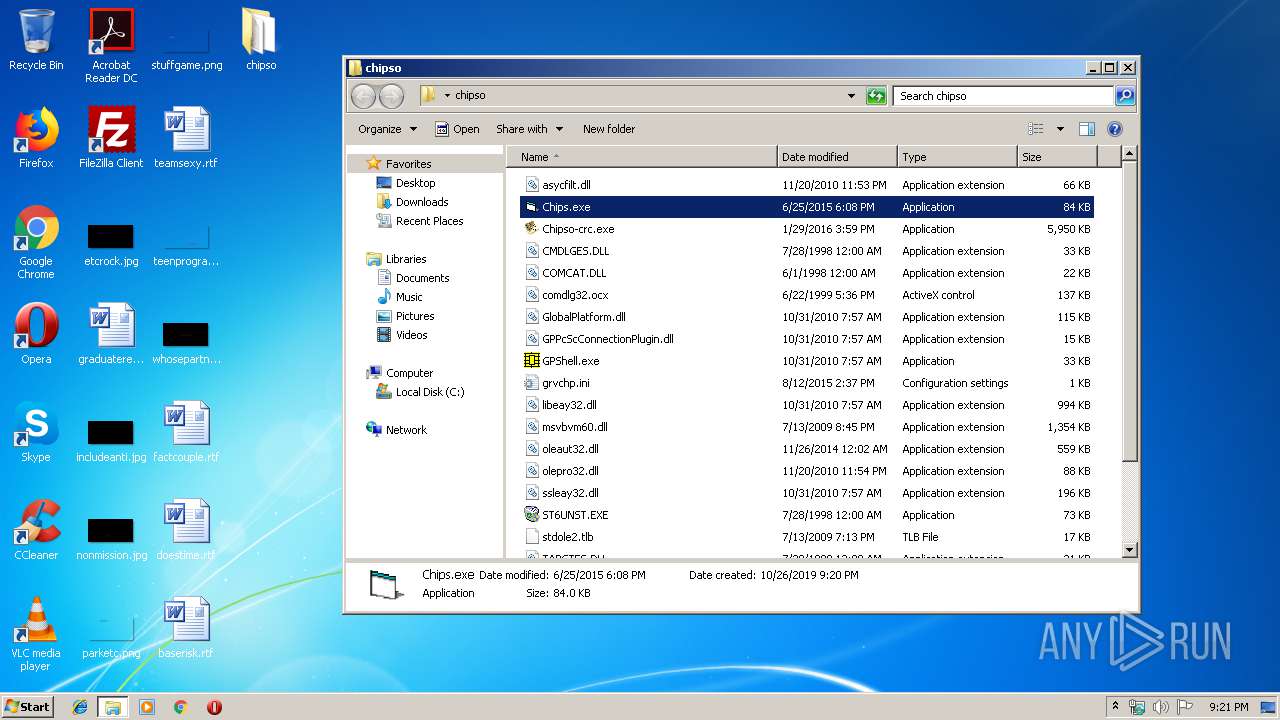
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1972)
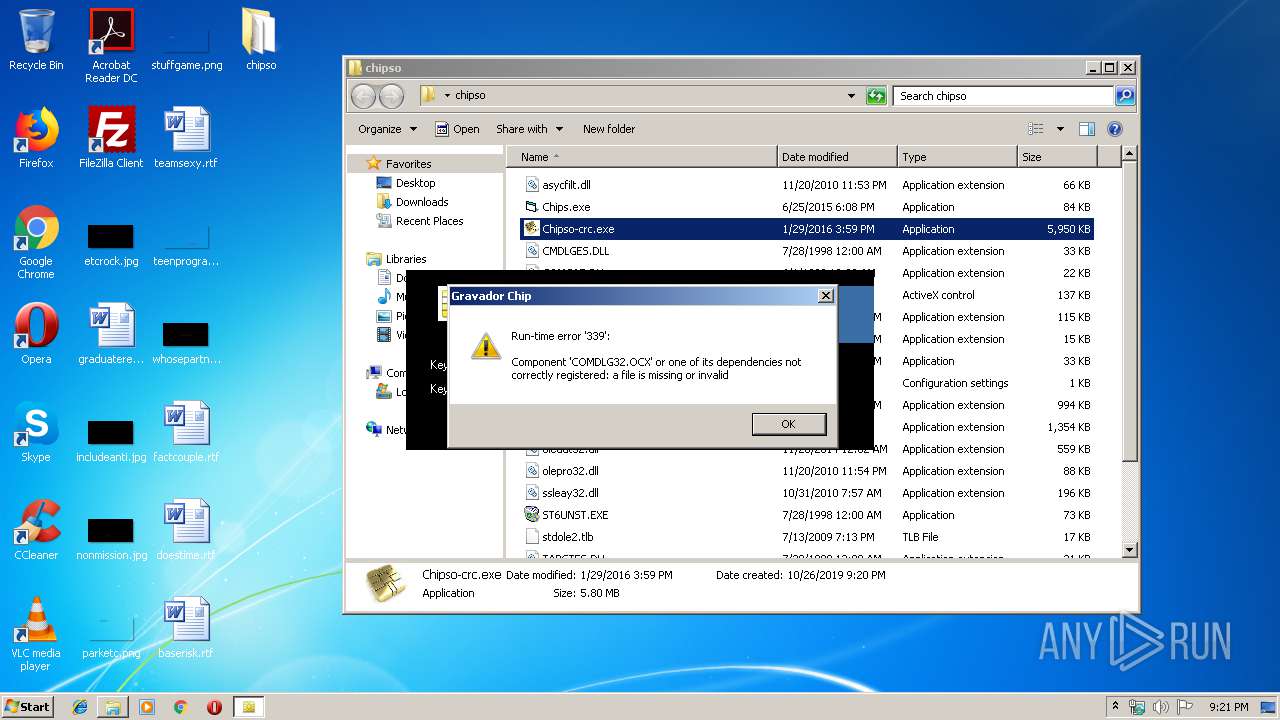
- Chipso-crc.exe (PID: 2856)
- tmp2.exe (PID: 3948)
Starts application with an unusual extension
- cmd.exe (PID: 2236)
Creates files in the user directory
- tmp2.exe (PID: 3948)
Starts CMD.EXE for commands execution
- Chipso-crc.exe (PID: 2856)
Starts itself from another location
- tmp2.exe (PID: 3948)
Reads default file associations for system extensions
- explorer.exe (PID: 352)
INFO
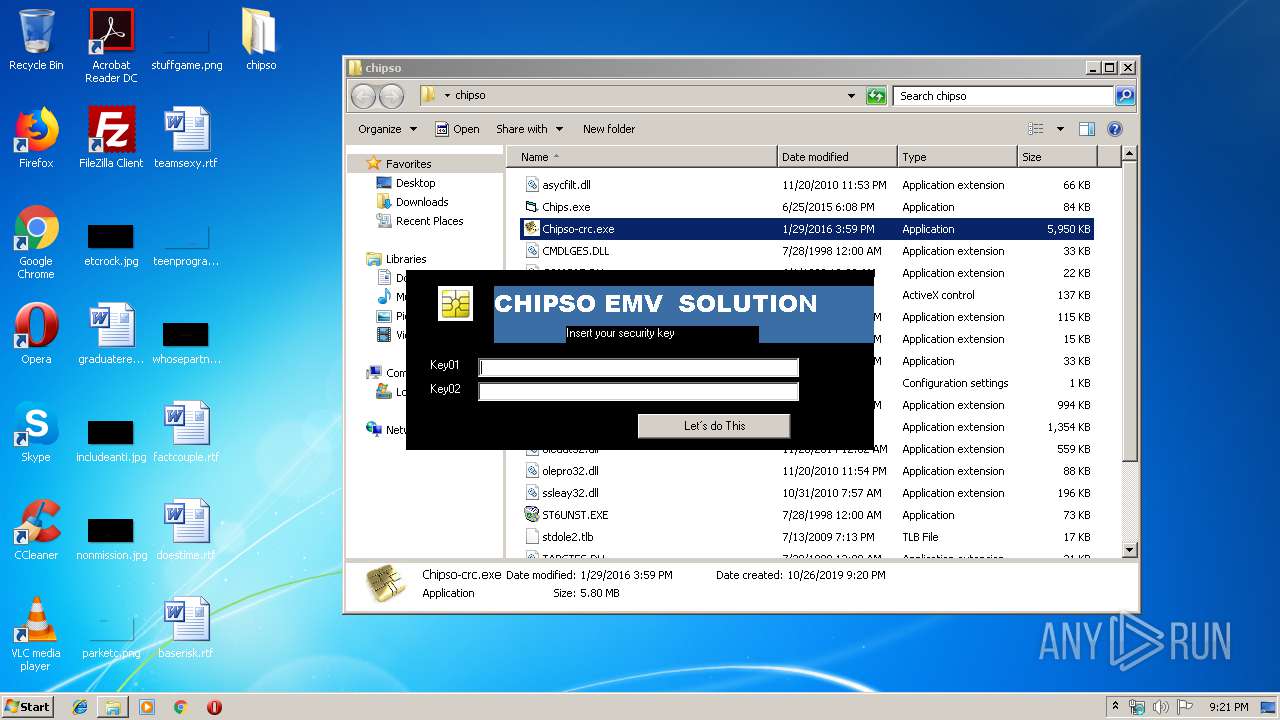
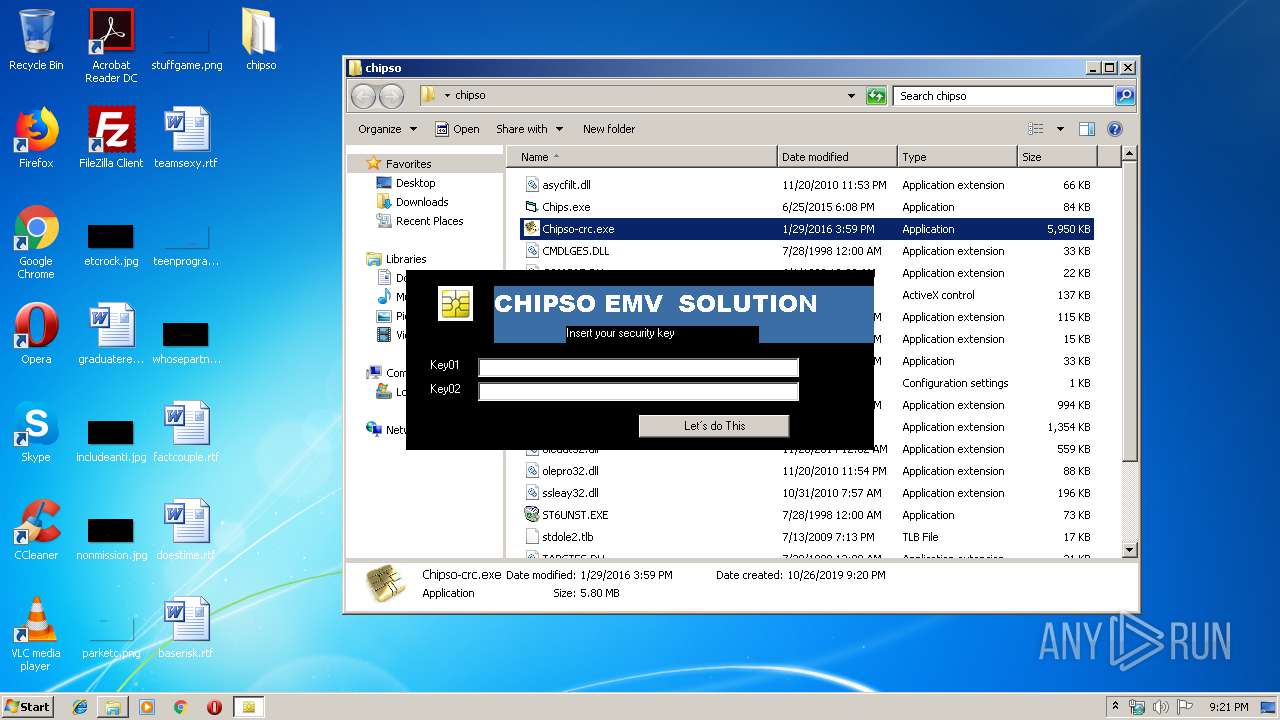
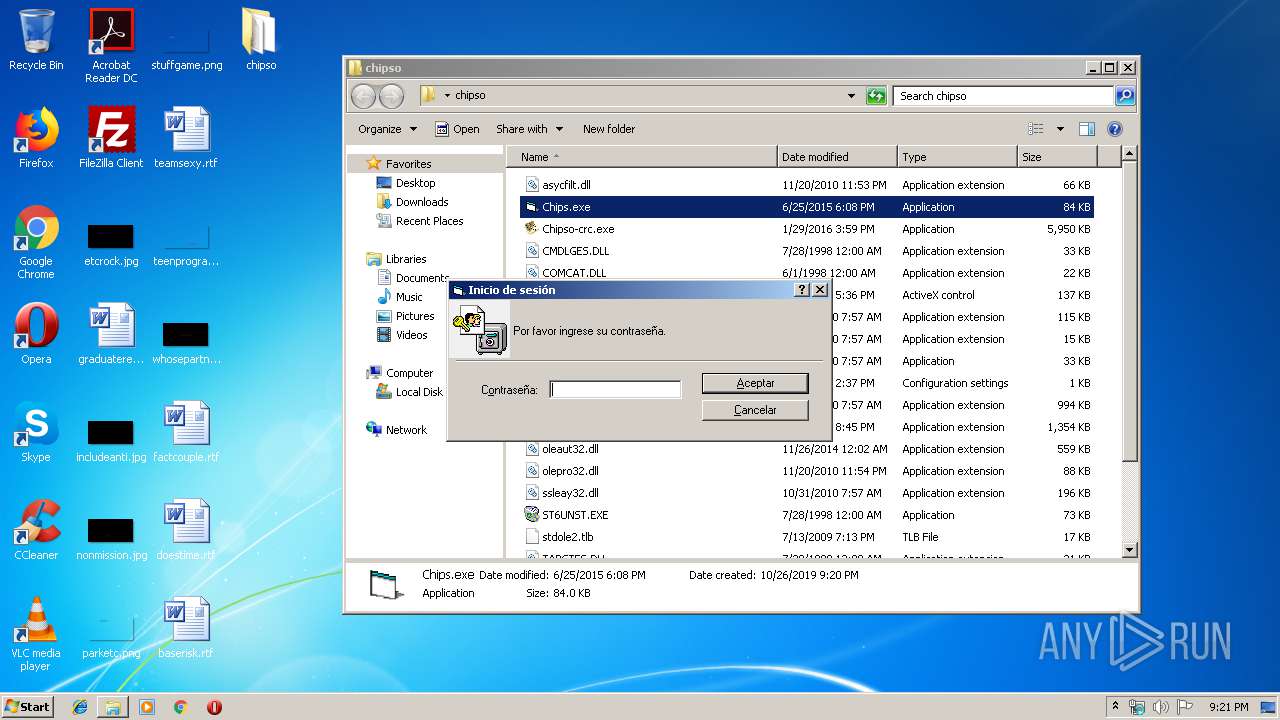
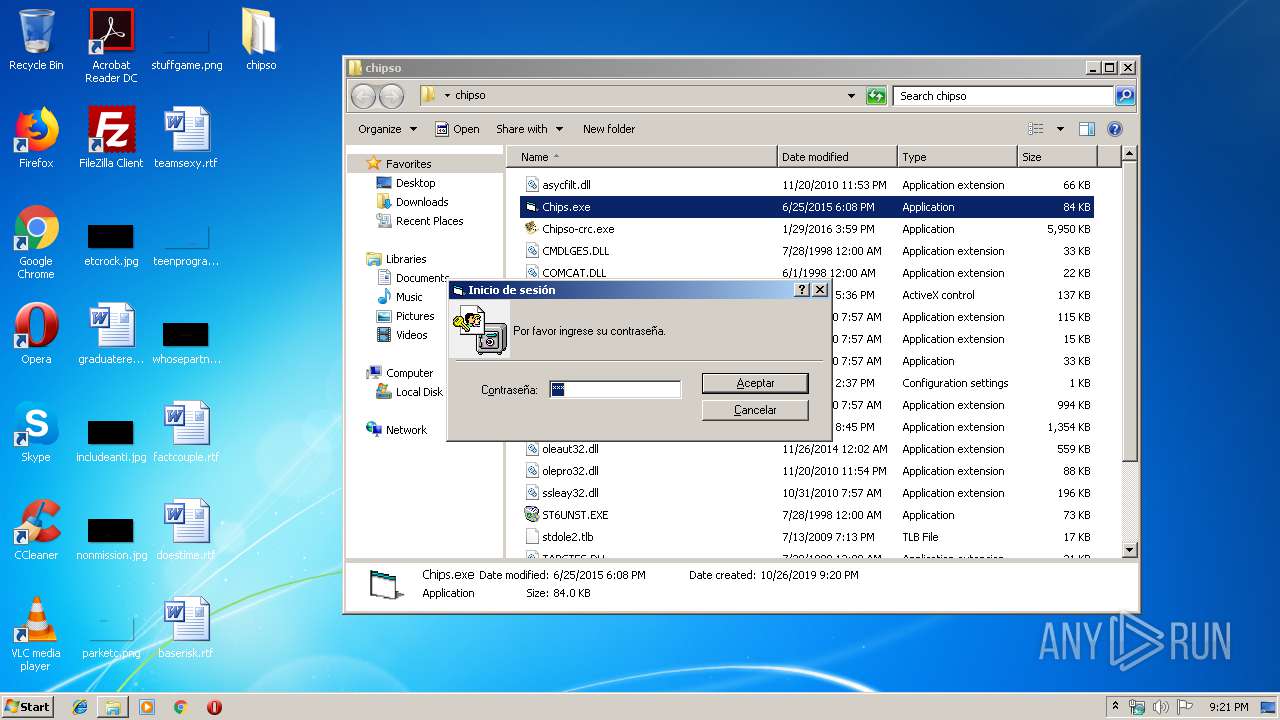
Manual execution by user
- Chipso-crc.exe (PID: 2856)
- Chips.exe (PID: 1028)
Dropped object may contain Bitcoin addresses
- Chipso-crc.exe (PID: 2856)
- tmp2.exe (PID: 3948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 36569 |
|---|---|
| UncompressedSize: | 67584 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2010:11:20 23:53:26 |
| PackingMethod: | Normal |
| ArchivedFileName: | chipso\asycfilt.dll |
Total processes
45
Monitored processes
10
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
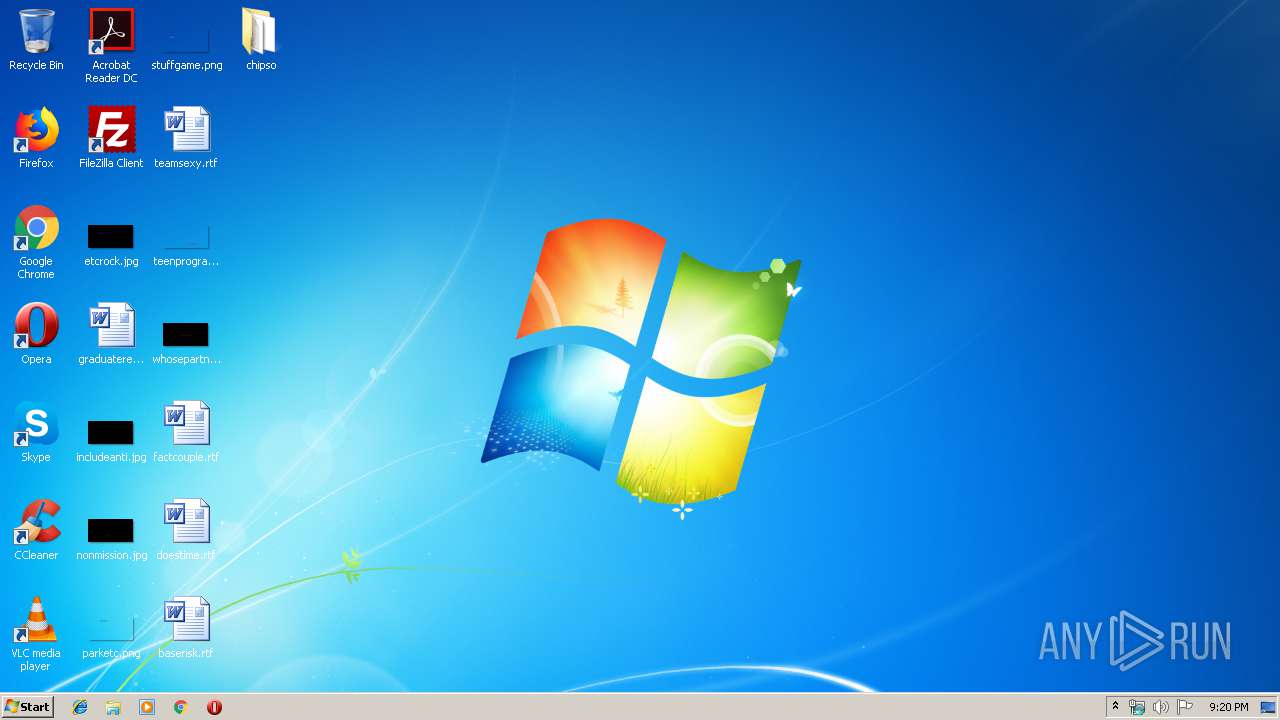
| 1028 | "C:\Users\admin\Desktop\chipso\Chips.exe" | C:\Users\admin\Desktop\chipso\Chips.exe | — | explorer.exe | |||||||||||
User: admin Company: Personal Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
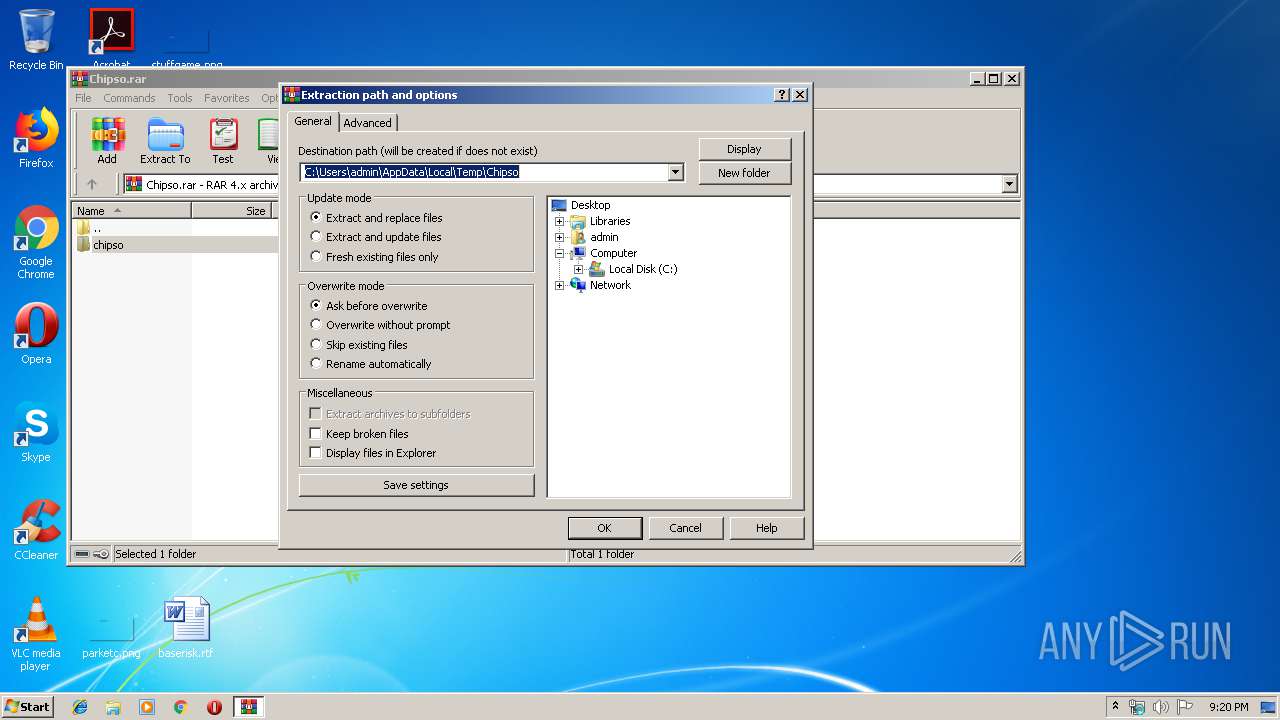
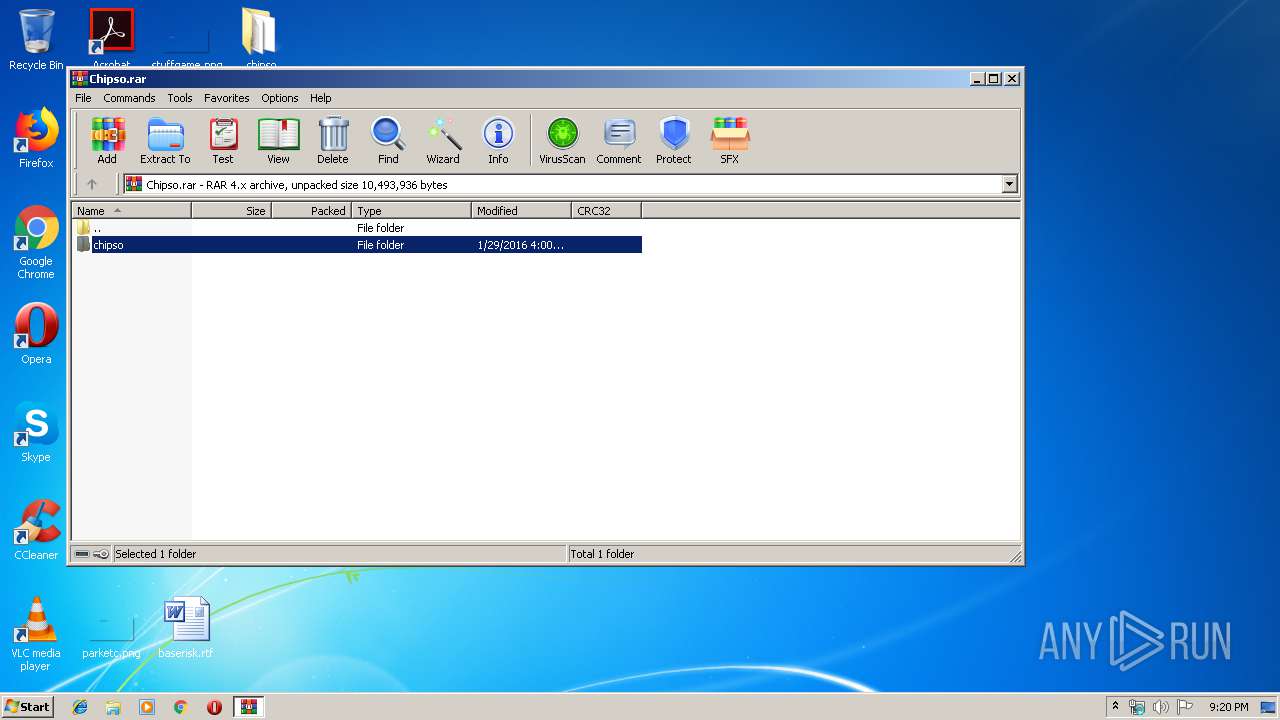
| 1972 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Chipso.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
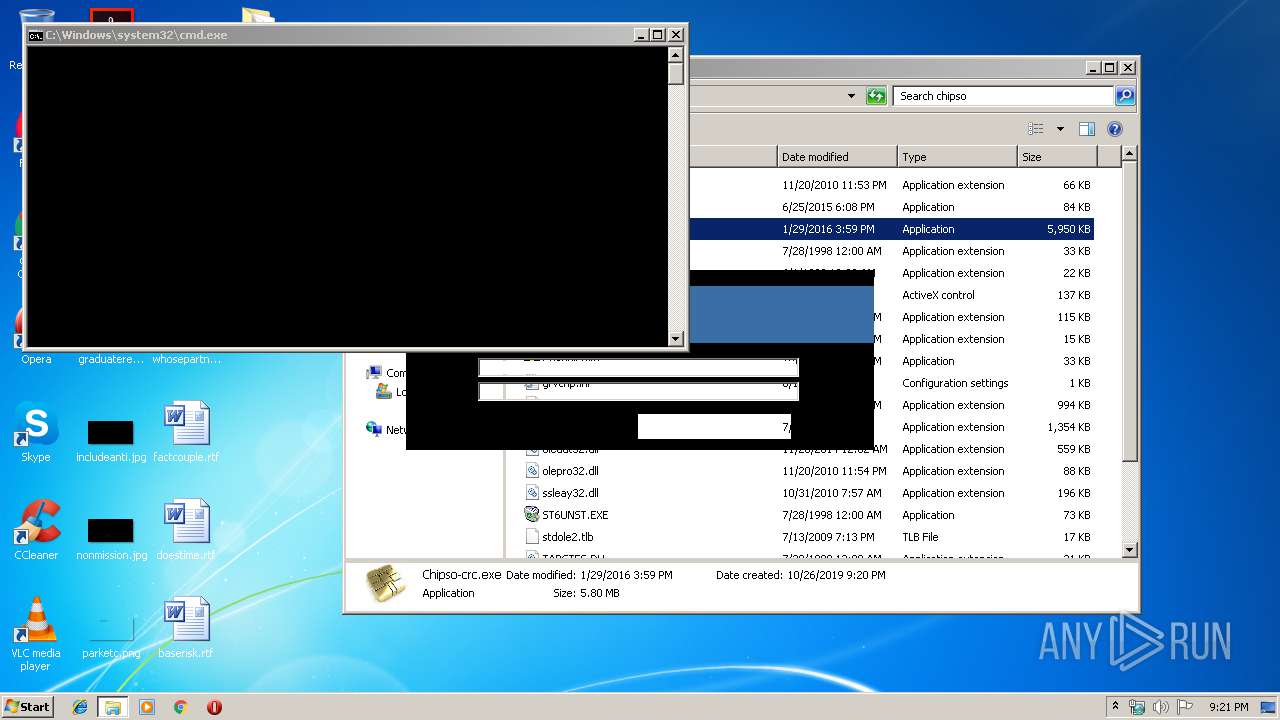
| 2236 | C:\Windows\system32\cmd.exe /c start %temp%\tmp1.jpg | C:\Windows\system32\cmd.exe | — | Chipso-crc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2356 | C:\Users\admin\AppData\Local\Temp\tmp1.jpg | C:\Users\admin\AppData\Local\Temp\tmp1.jpg | — | cmd.exe | |||||||||||
User: admin Company: HackTheWorld Integrity Level: MEDIUM Exit code: 0 Version: 1.00.0122 Modules
| |||||||||||||||
| 2408 | C:\Windows\system32\cmd.exe /c start %temp%\tmp2.exe | C:\Windows\system32\cmd.exe | — | Chipso-crc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
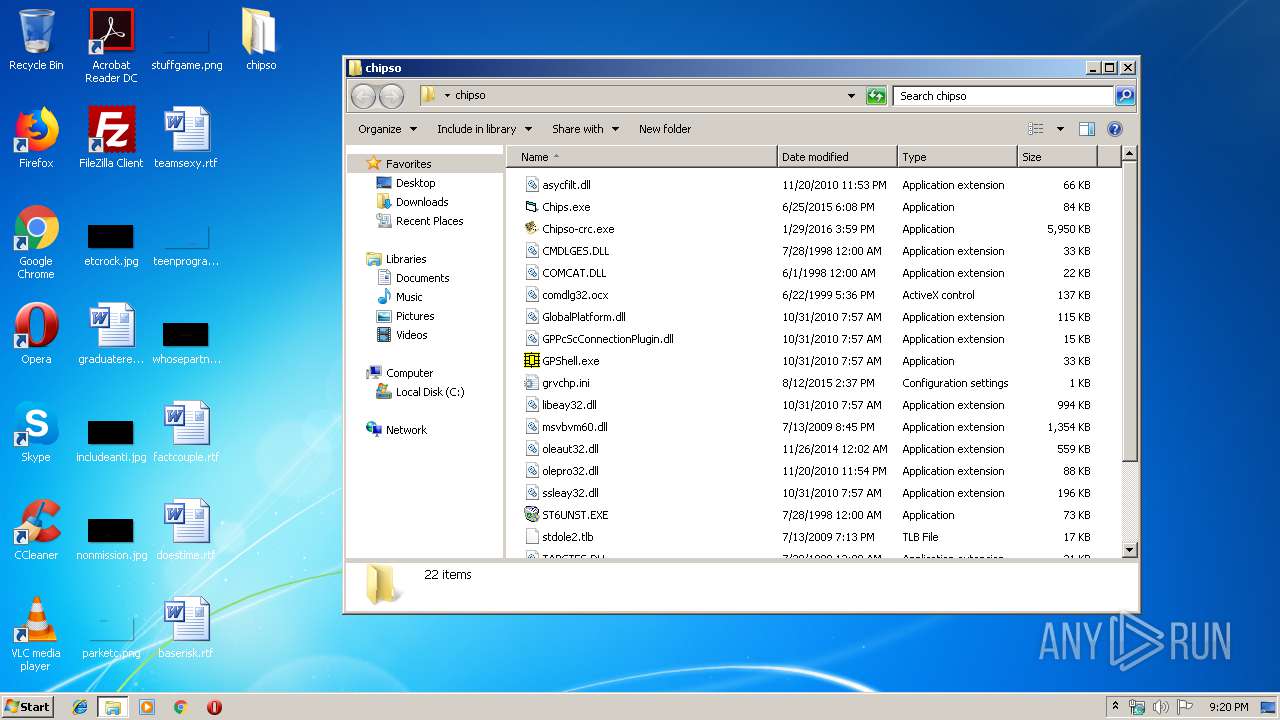
| 2856 | "C:\Users\admin\Desktop\chipso\Chipso-crc.exe" | C:\Users\admin\Desktop\chipso\Chipso-crc.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2968 | "C:\Users\admin\AppData\Local\Drpbx\emv.exe" C:\Users\admin\AppData\Local\Temp\tmp2.exe | C:\Users\admin\AppData\Local\Drpbx\emv.exe | — | tmp2.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Chip Writer Exit code: 0 Version: 37.0.2.5583 Modules
| |||||||||||||||
| 3488 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3948 | C:\Users\admin\AppData\Local\Temp\tmp2.exe | C:\Users\admin\AppData\Local\Temp\tmp2.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Chip Writer Exit code: 0 Version: 37.0.2.5583 Modules
| |||||||||||||||
Total events
2 197
Read events
2 115
Write events
82
Delete events
0
Modification events
| (PID) Process: | (1972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1972) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Chipso.rar | |||
| (PID) Process: | (1972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
25
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1972 | WinRAR.exe | C:\Users\admin\Desktop\chipso\Chipso-crc.exe | executable | |
MD5:— | SHA256:— | |||
| 1972 | WinRAR.exe | C:\Users\admin\Desktop\chipso\comdlg32.ocx | executable | |
MD5:D76F0EAB36F83A31D411AEAF70DA7396 | SHA256:46F4FDB12C30742FF4607876D2F36CF432CDC7EC3D2C99097011448FC57E997C | |||
| 1972 | WinRAR.exe | C:\Users\admin\Desktop\chipso\COMCAT.DLL | executable | |
MD5:3B180DA2B50B954A55FE37AFBA58D428 | SHA256:96D04CDFAF4F4D7B8722B139A15074975D4C244302F78034B7BE65DF1A92FD03 | |||
| 1972 | WinRAR.exe | C:\Users\admin\Desktop\chipso\GPPcScConnectionPlugin.dll | executable | |
MD5:2F99E012379E8C950B0BDE761C5CCA0F | SHA256:5D84EC3F8DEE7438B0049D5DC201A68A99F3E471A4C9ACAC48DD7F67F89FD178 | |||
| 1972 | WinRAR.exe | C:\Users\admin\Desktop\chipso\asycfilt.dll | executable | |
MD5:088CF5B6380FB9002F2A4246F812225D | SHA256:3E7205FEBC5B2432EE3655CD71D630A5D5EA609995F43053B1B5EB8917C46453 | |||
| 1972 | WinRAR.exe | C:\Users\admin\Desktop\chipso\Chips.exe | executable | |
MD5:— | SHA256:— | |||
| 1972 | WinRAR.exe | C:\Users\admin\Desktop\chipso\grvchp.ini | text | |
MD5:— | SHA256:— | |||
| 2356 | tmp1.jpg | C:\Users\admin\AppData\Local\Temp\~DFF2E71ACA18C6D042.TMP | — | |
MD5:— | SHA256:— | |||
| 1972 | WinRAR.exe | C:\Users\admin\Desktop\chipso\msvbvm60.dll | executable | |
MD5:5343A19C618BC515CEB1695586C6C137 | SHA256:2246B4FEAE199408EA66D4A90C1589026F4A5800CE5A28E583B94506A8A73DCE | |||
| 1972 | WinRAR.exe | C:\Users\admin\Desktop\chipso\stdole2.tlb | executable | |
MD5:89F4D0DD6606A2FE15931E6888DBBC8D | SHA256:513D9F6DB0D993DB6D720DF1FF4FED2C6A9B067522CDEE389CA40D3B618B6A55 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report