| File name: | Pacman_smoking_crack.exe |
| Full analysis: | https://app.any.run/tasks/af2e2221-7ac9-4735-bee3-94489a0078d2 |
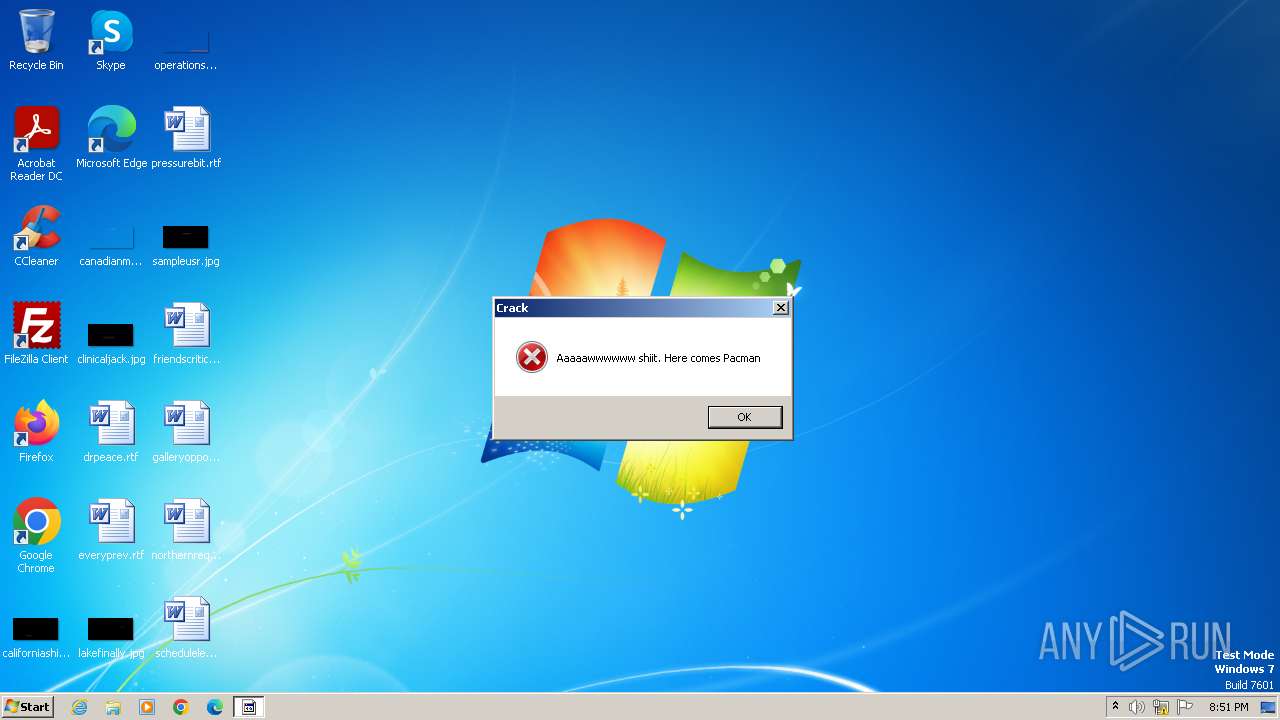
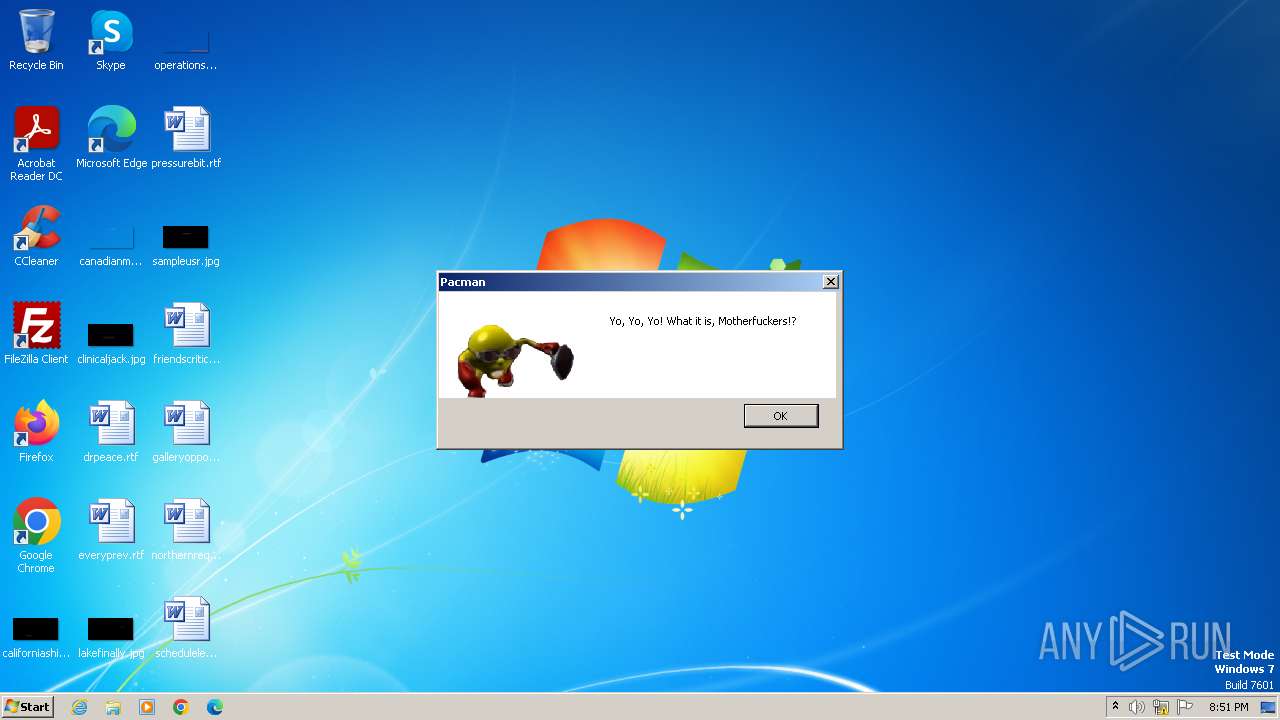
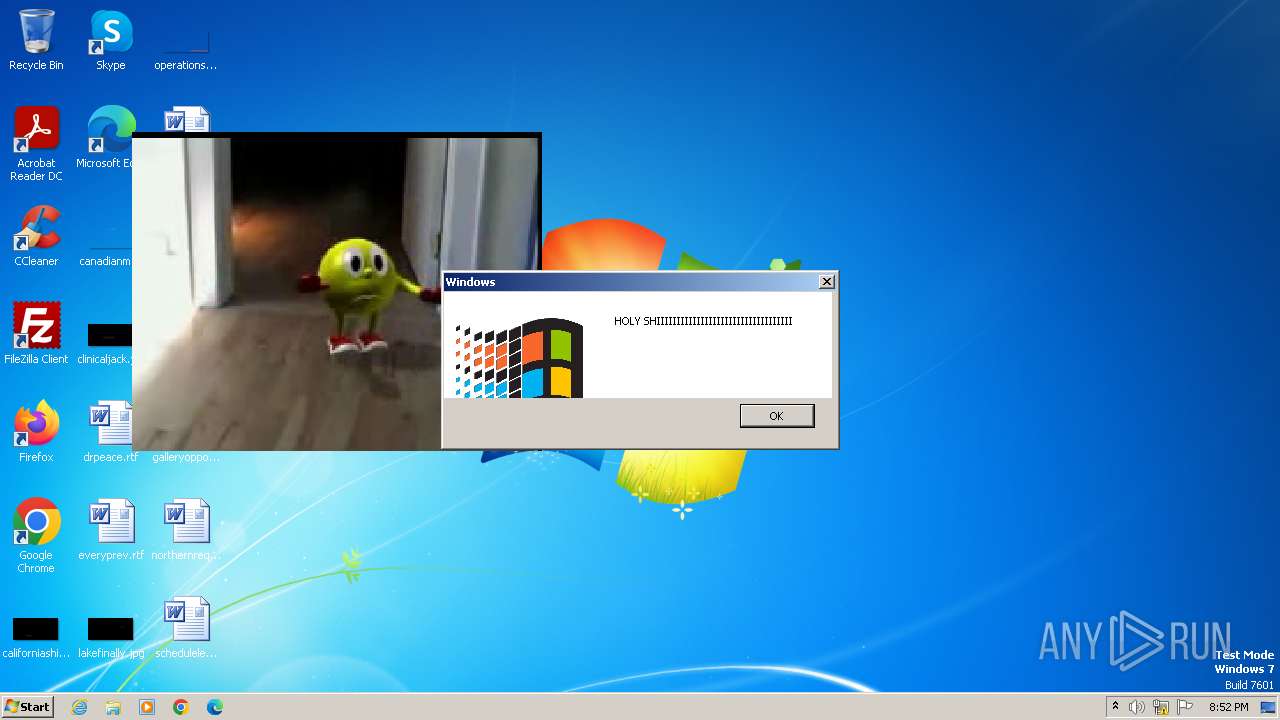
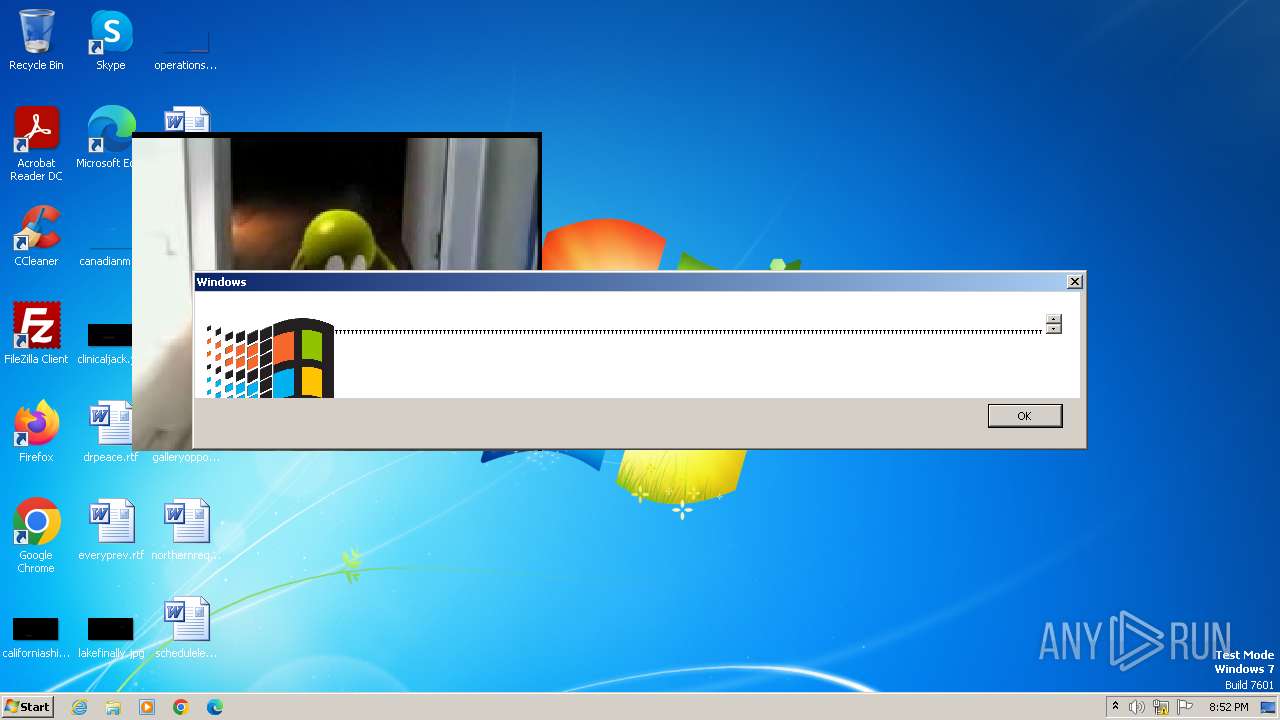
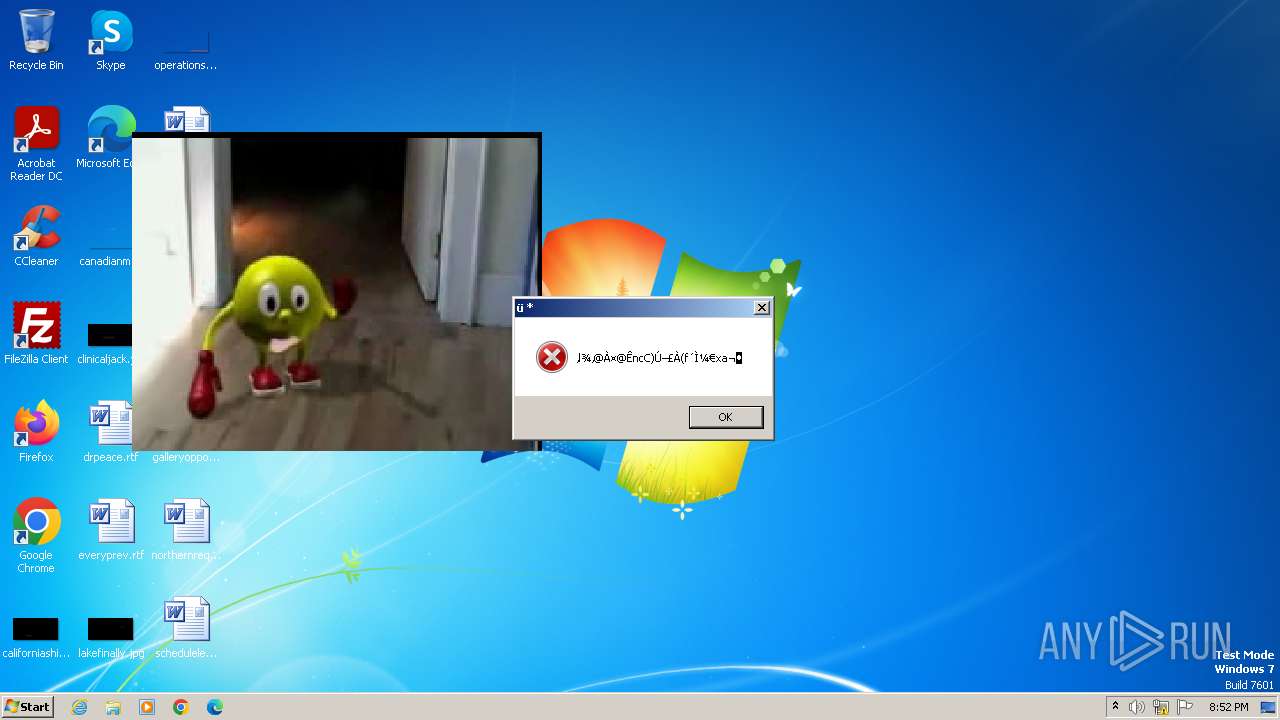
| Verdict: | Malicious activity |
| Analysis date: | November 27, 2023, 20:51:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 9E47F64C453DB4A8FAF435EEE2D1D687 |
| SHA1: | 9872F7C94E3D7CE72696E6F8D94343C1E8AEFC35 |
| SHA256: | 265E864719F5935C5BBC087B1984FED5B1471AAD61F2568873C2AFF0B1B8B41B |
| SSDEEP: | 98304:qsJi3gtWLExqLsY9jAaRgHuF07yp4f29sTahwXeVELC5IvmN8jqxAnOlUbSJY/Wr:qsJi3gtWLExqLsY9jAaRgHuF07yp4f2L |
MALICIOUS
Drops the executable file immediately after the start
- Pacman_smoking_crack.exe (PID: 2476)
SUSPICIOUS
Reads the Internet Settings
- Pacman_smoking_crack.exe (PID: 2476)
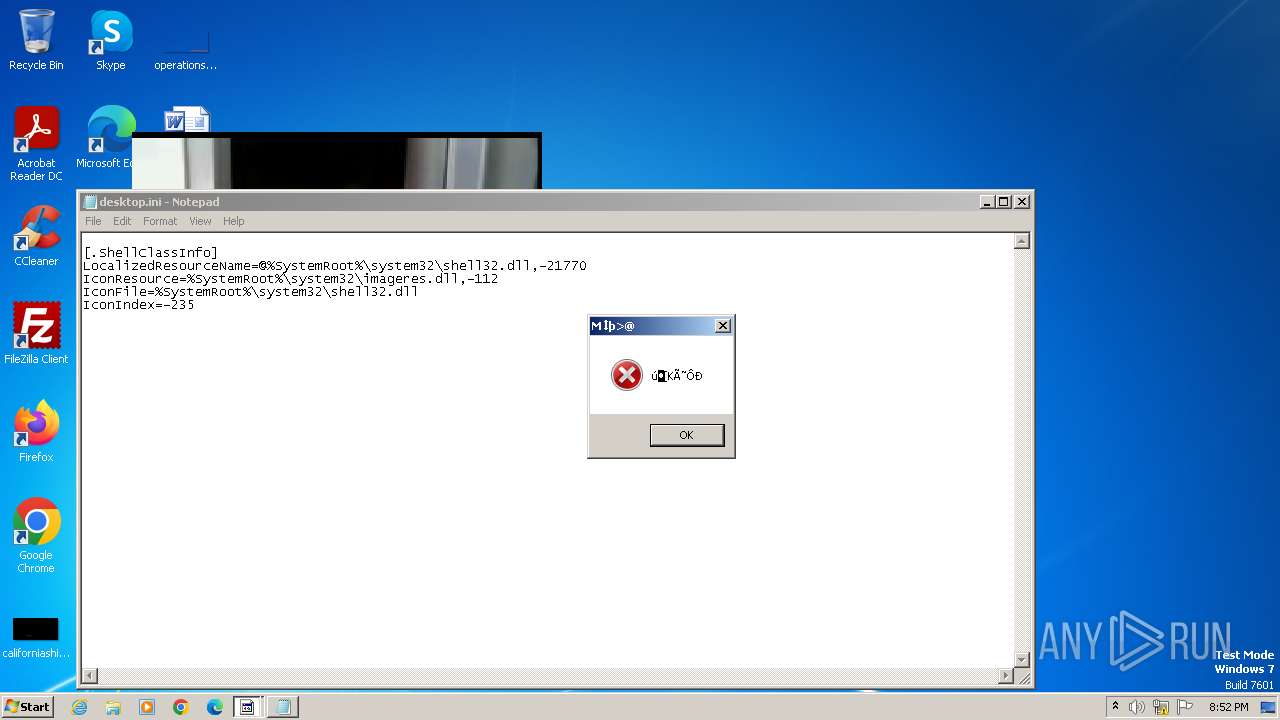
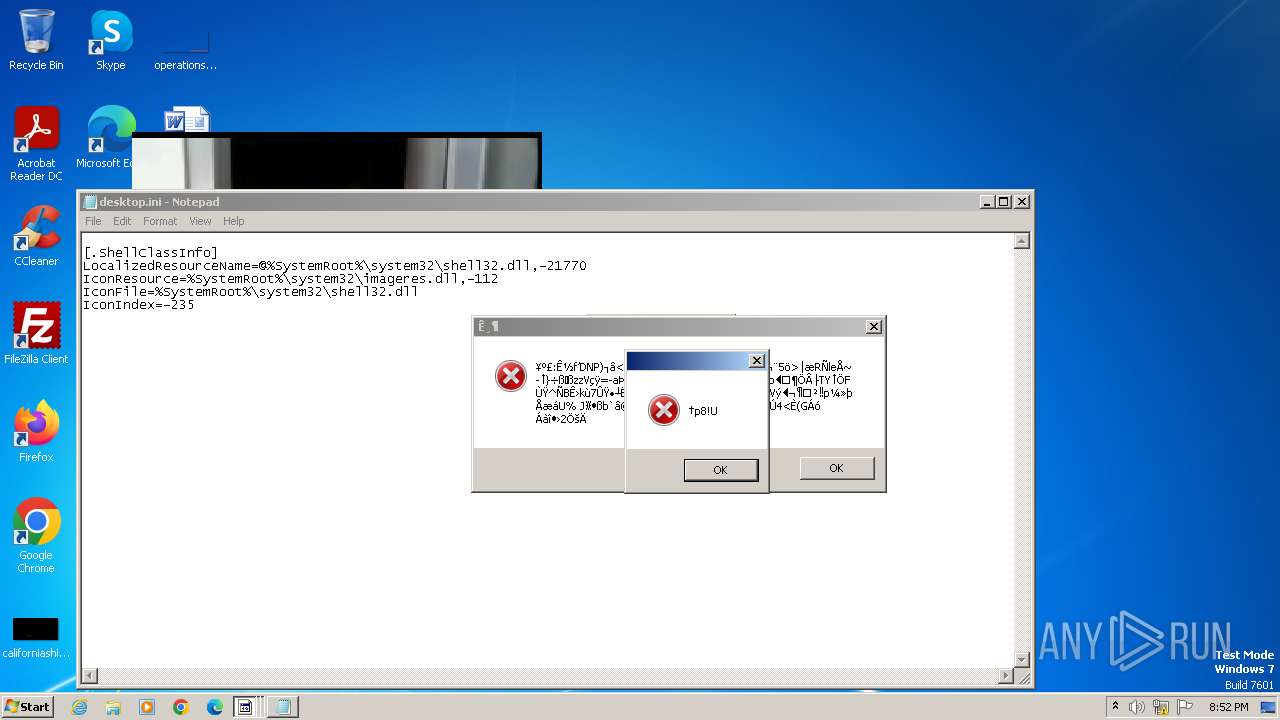
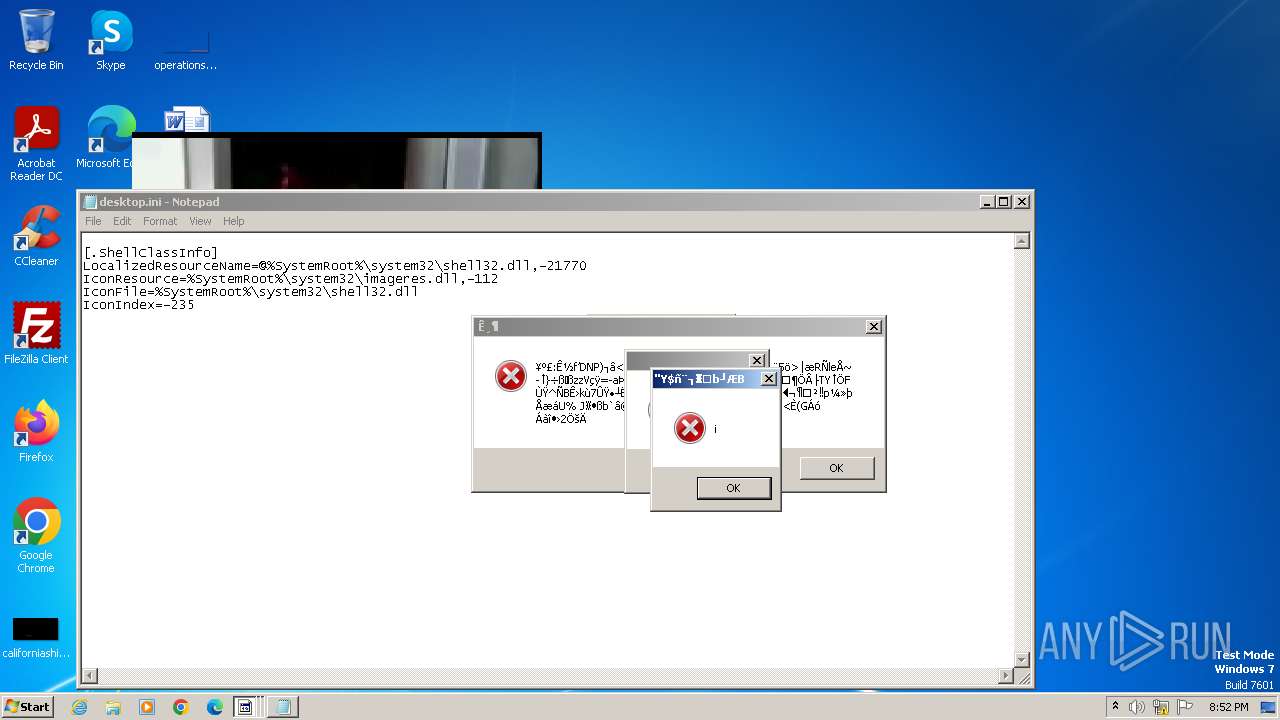
Start notepad (likely ransomware note)
- Pacman_smoking_crack.exe (PID: 2476)
Changes default file association
- WINWORD.EXE (PID: 2540)
Creates/Modifies COM task schedule object
- WINWORD.EXE (PID: 2540)
The system shut down or reboot
- Pacman_smoking_crack.exe (PID: 2476)
INFO
Reads the machine GUID from the registry
- Pacman_smoking_crack.exe (PID: 2476)
Checks supported languages
- Pacman_smoking_crack.exe (PID: 2476)
Reads the computer name
- Pacman_smoking_crack.exe (PID: 2476)
Checks proxy server information
- Pacman_smoking_crack.exe (PID: 2476)
Reads Microsoft Office registry keys
- Pacman_smoking_crack.exe (PID: 2476)
Create files in a temporary directory
- Pacman_smoking_crack.exe (PID: 2476)
Reads Environment values
- Pacman_smoking_crack.exe (PID: 2476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:07:06 20:13:23+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 5703680 |
| InitializedDataSize: | 5120 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x57270a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | WindowsFormsApplication2 |
| FileVersion: | 1.0.0.0 |
| InternalName: | Free crack.exe |
| LegalCopyright: | Copyright © 2013 |
| LegalTrademarks: | - |
| OriginalFileName: | Free crack.exe |
| ProductName: | WindowsFormsApplication2 |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
53
Monitored processes
11
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
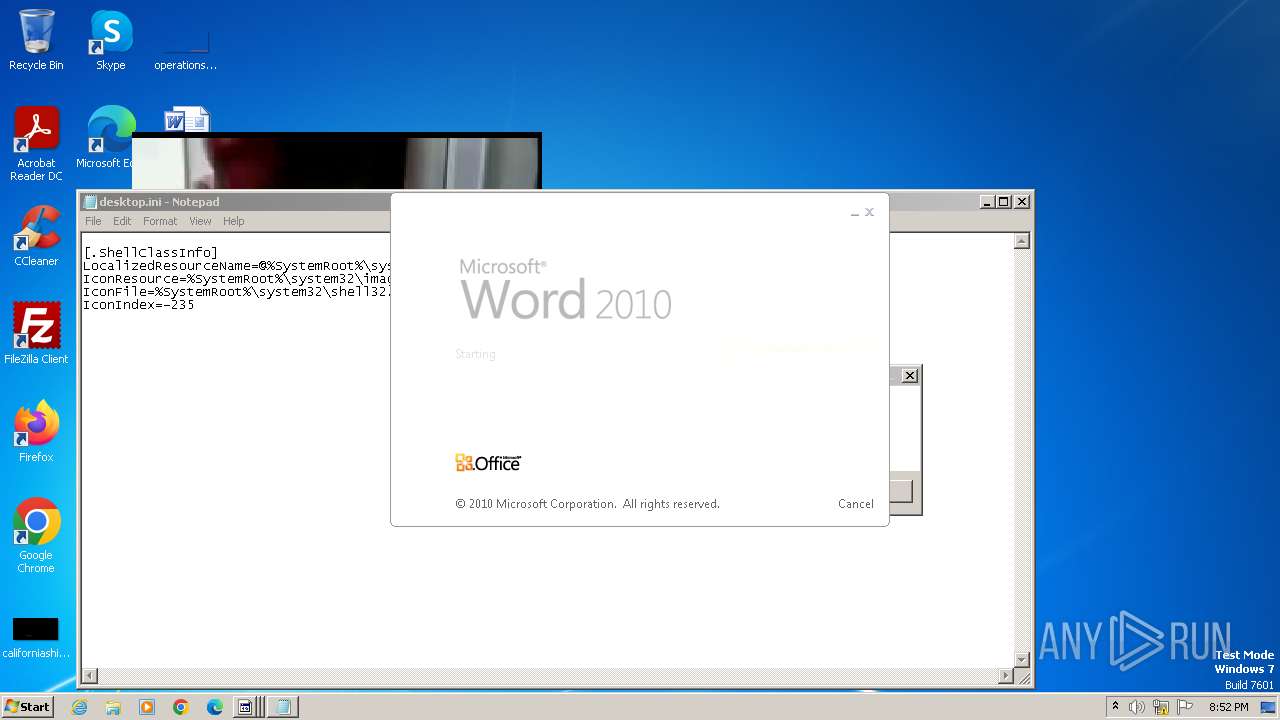
| 304 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Documents\~$atherfunction.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Pacman_smoking_crack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1420 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Documents\weatherfunction.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Pacman_smoking_crack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Documents\~$atherfunction.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Pacman_smoking_crack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2320 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Documents\everynothing.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Pacman_smoking_crack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2476 | "C:\Users\admin\AppData\Local\Temp\Pacman_smoking_crack.exe" | C:\Users\admin\AppData\Local\Temp\Pacman_smoking_crack.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: WindowsFormsApplication2 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
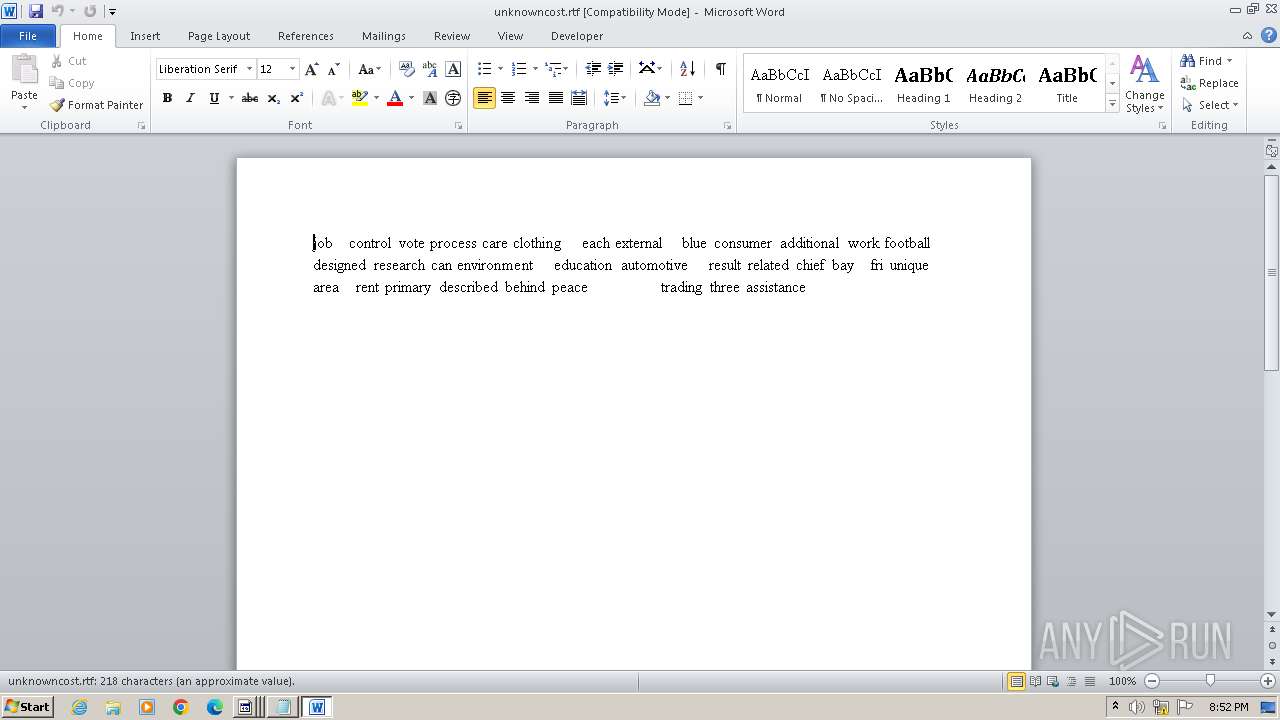
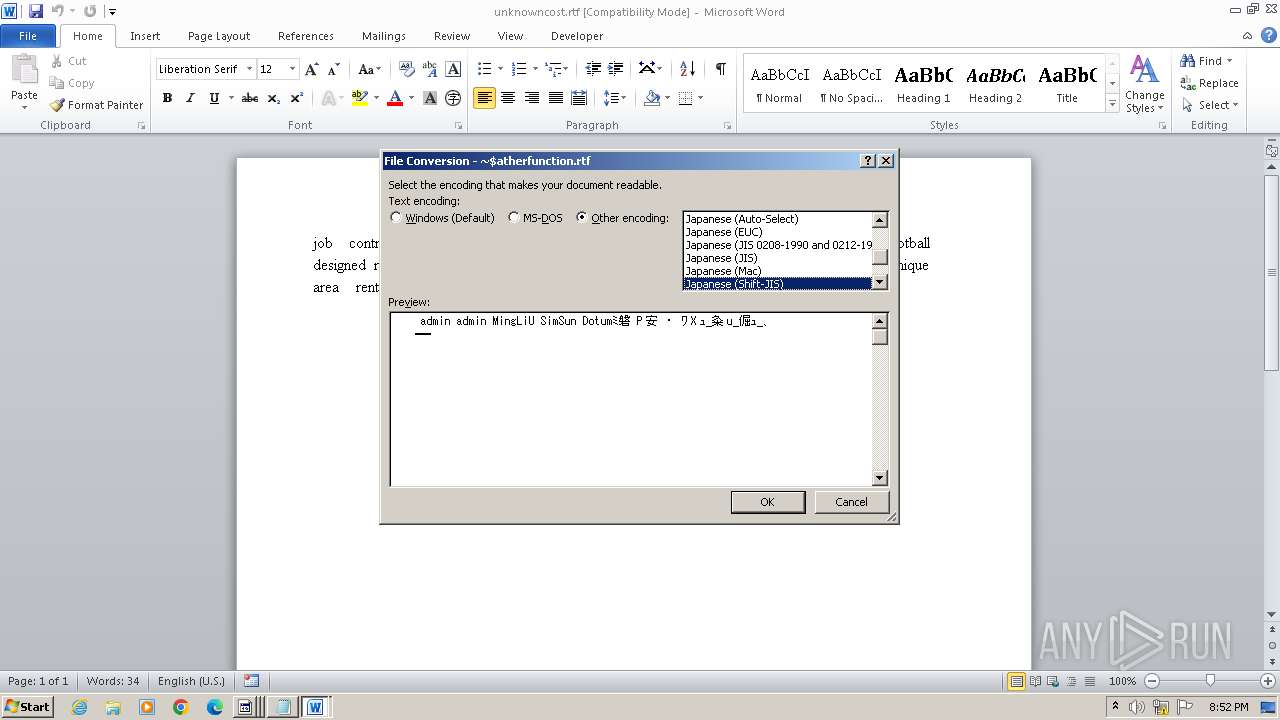
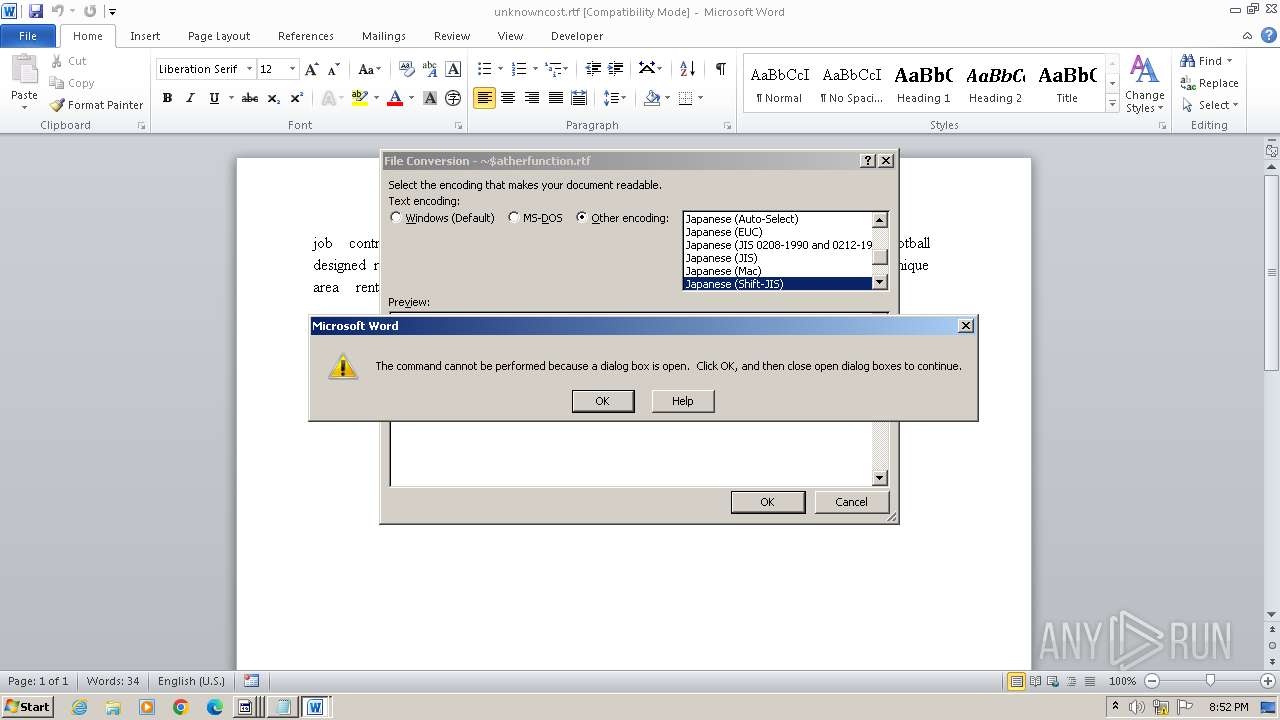
| 2540 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Documents\unknowncost.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Pacman_smoking_crack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2584 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Documents\weatherfunction.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Pacman_smoking_crack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2980 | "C:\Users\admin\AppData\Local\Temp\Pacman_smoking_crack.exe" | C:\Users\admin\AppData\Local\Temp\Pacman_smoking_crack.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WindowsFormsApplication2 Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3080 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Documents\unknowncost.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Pacman_smoking_crack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3768 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Documents\desktop.ini | C:\Windows\System32\notepad.exe | — | Pacman_smoking_crack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
9 035
Read events
8 334
Write events
216
Delete events
485
Modification events
| (PID) Process: | (2476) Pacman_smoking_crack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2476) Pacman_smoking_crack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000059010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2476) Pacman_smoking_crack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | AutoMetadataCurrentDownloadCount |
Value: 0 | |||
| (PID) Process: | (2476) Pacman_smoking_crack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | AutoMetadataCurrent500ServerErrorCount |
Value: 0 | |||
| (PID) Process: | (2476) Pacman_smoking_crack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | AutoMetadataCurrent503ServerErrorCount |
Value: 0 | |||
| (PID) Process: | (2476) Pacman_smoking_crack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | AutoMetadataCurrentOtherServerErrorCount |
Value: 0 | |||
| (PID) Process: | (2476) Pacman_smoking_crack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | AutoMetadataCurrentNetworkErrorCount |
Value: 0 | |||
| (PID) Process: | (2476) Pacman_smoking_crack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | AutoMetadataLastResetTime |
Value: 657617561 | |||
| (PID) Process: | (2476) Pacman_smoking_crack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | MediaLibraryCreateNewDatabase |
Value: 0 | |||
| (PID) Process: | (2476) Pacman_smoking_crack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences\HME |
| Operation: | write | Name: | LocalLibraryID |
Value: {DAC4D6EA-B3BD-49F1-AC83-5867016FCE18} | |||
Executable files
3
Suspicious files
21
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2540 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8B4F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1420 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR96B9.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2476 | Pacman_smoking_crack.exe | C:\Users\admin\AppData\Local\Temp\AxInterop.WMPLib.dll | executable | |
MD5:A40E9564563DCD8D3E790D989775C2F1 | SHA256:94C261CD4C9845047A6F74152F86611A5D3E0F5EDA152FE2C9936E6289A26754 | |||
| 2584 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA291.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2320 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAE58.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2476 | Pacman_smoking_crack.exe | C:\Users\admin\crack\wincrack.mp3 | binary | |
MD5:D4063B5C1B63E7F3323739BF7567ADB3 | SHA256:070E14504B956F5942C565064EB8BB564B5419C36092639C98ECC7DDD7D2356D | |||
| 2540 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\unknowncost.rtf.LNK | binary | |
MD5:32A5251399C229238E38FFACC1E9086B | SHA256:5EE14207FFDF1595D85202A76481A7C72382F6D2F43292B249A9D86FB682BD74 | |||
| 3080 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRBA2F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2304 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRC626.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 304 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD1FD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
6
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1080 | svchost.exe | GET | 200 | 8.253.204.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b257947f6e02507e | unknown | compressed | 4.66 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 8.253.204.121:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |