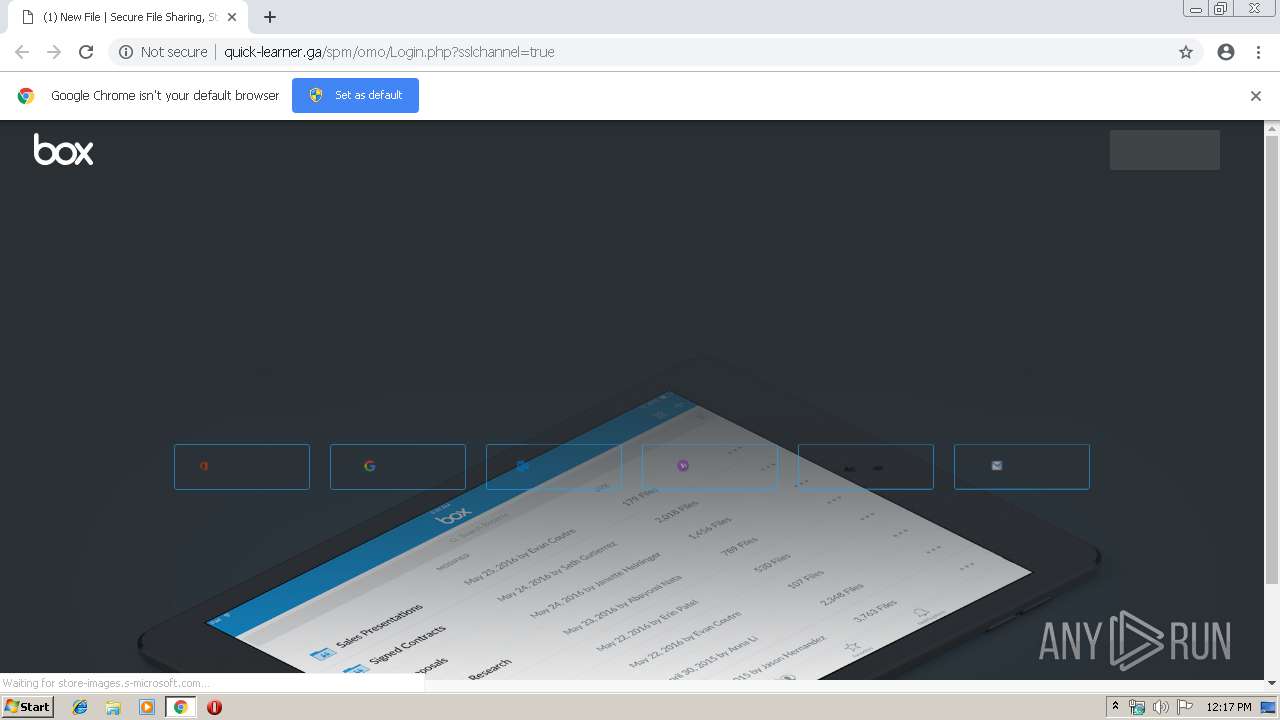
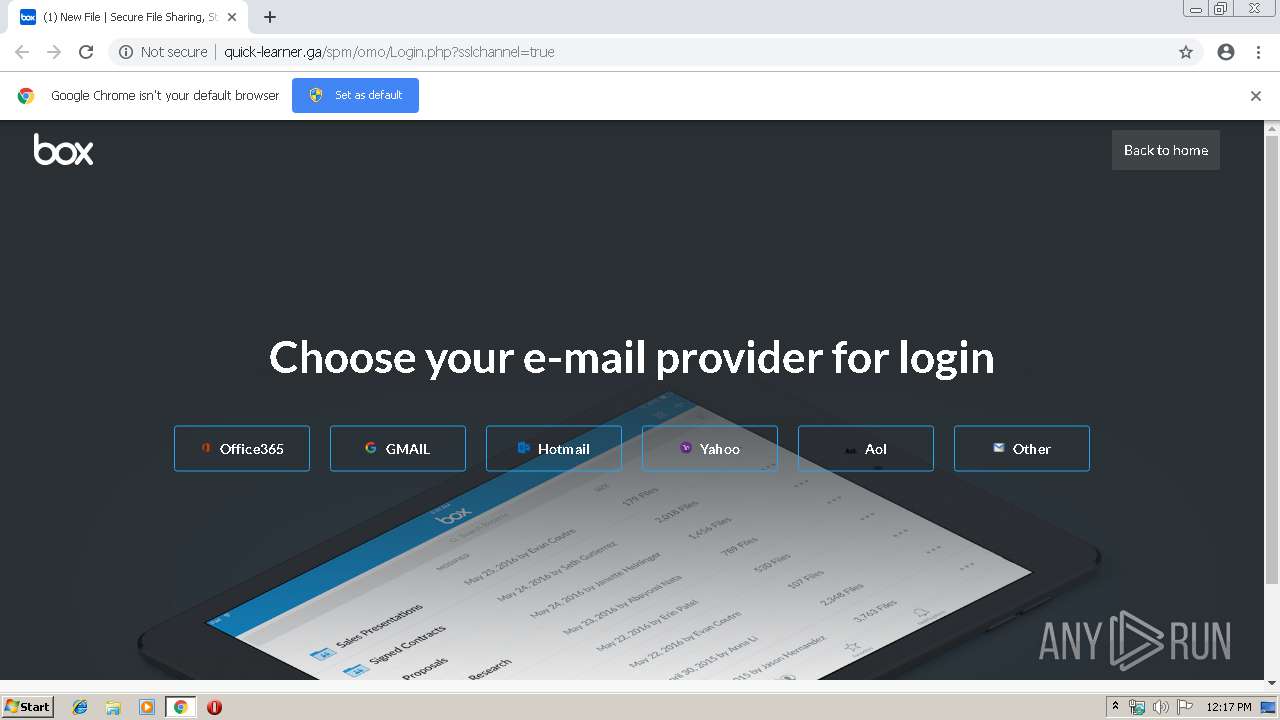
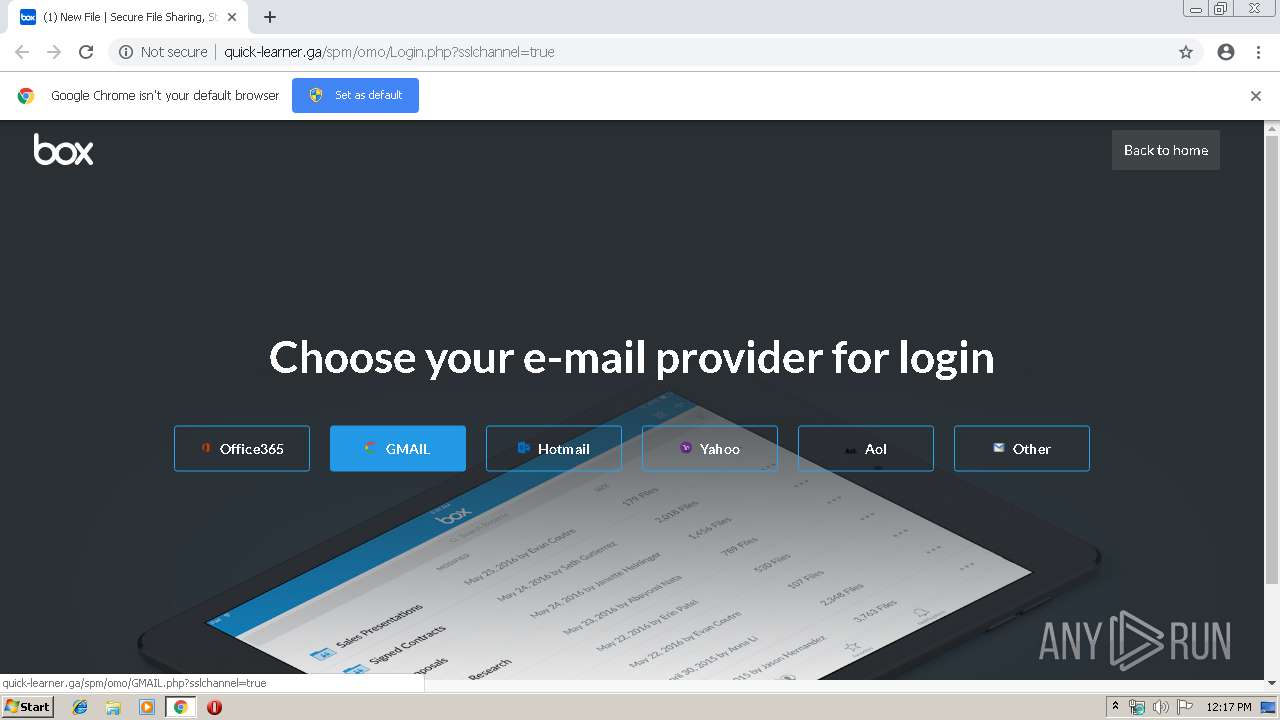
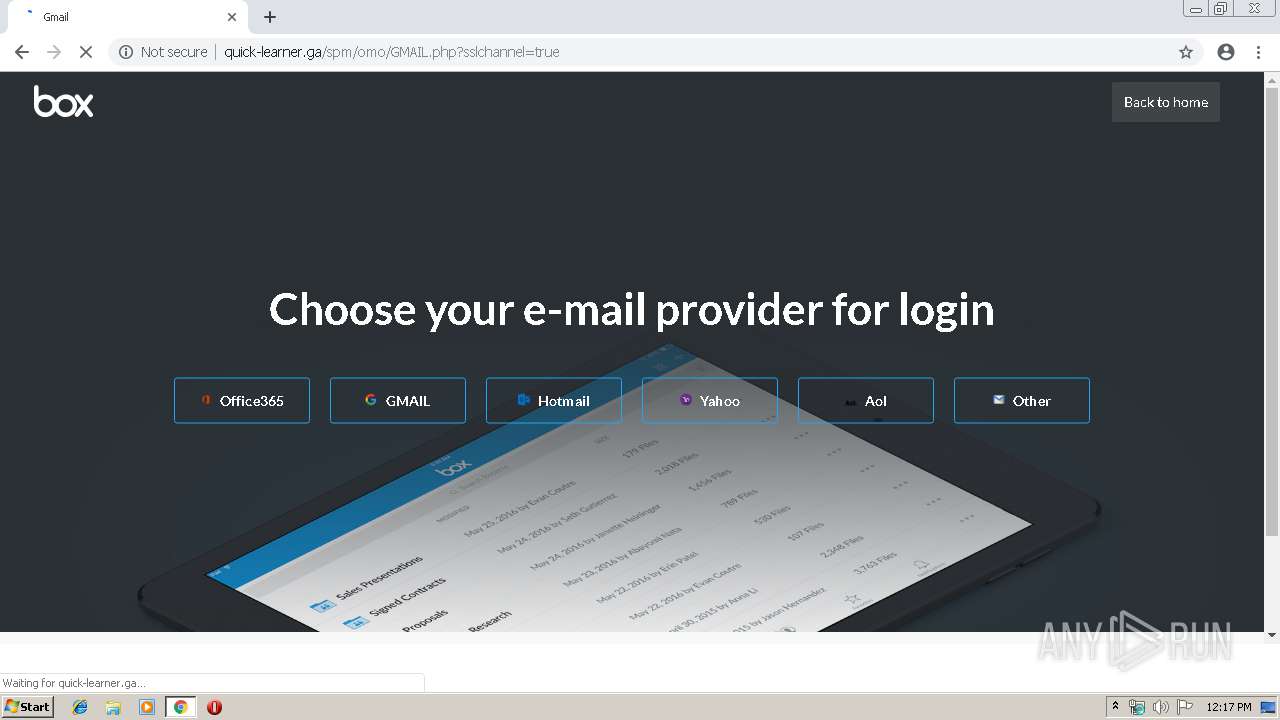
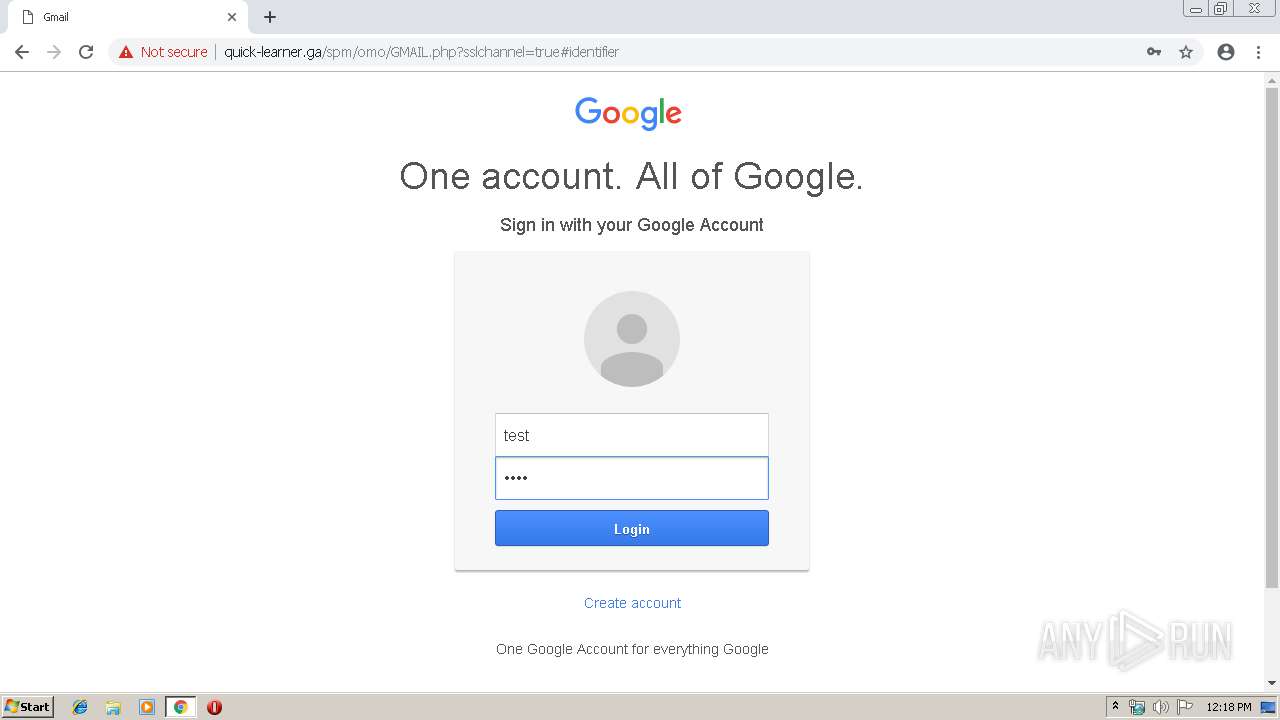
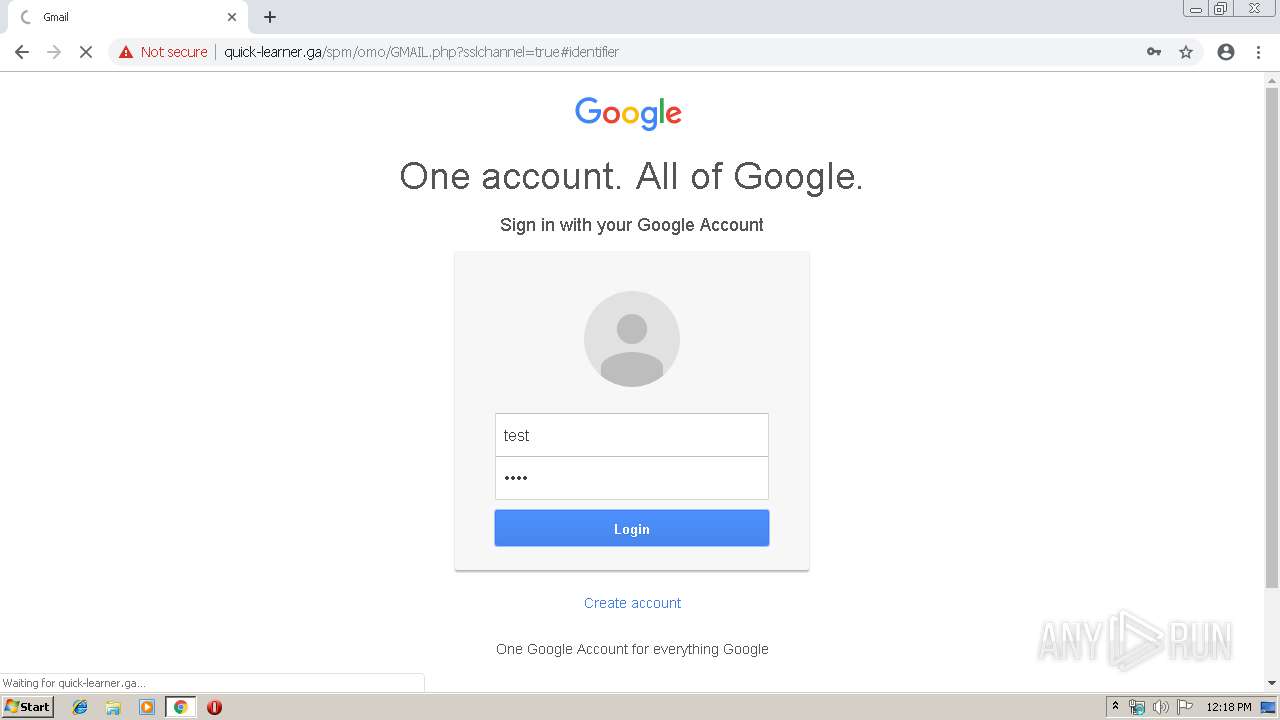
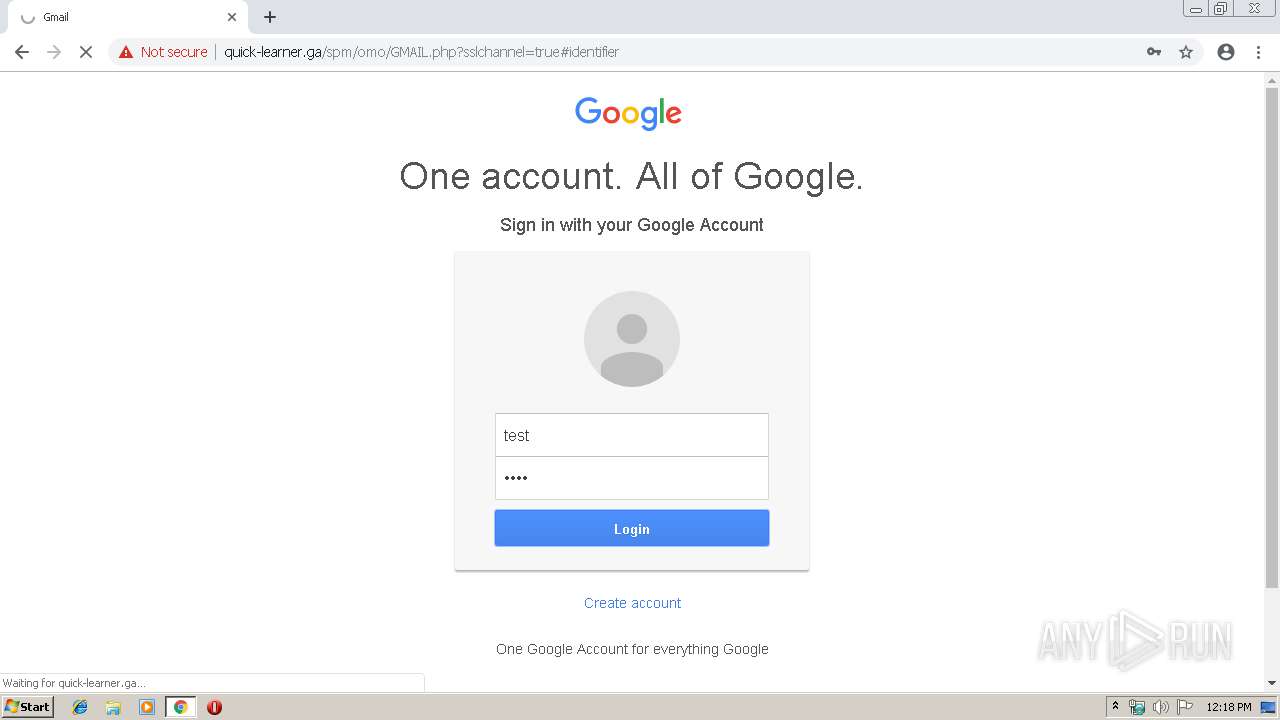
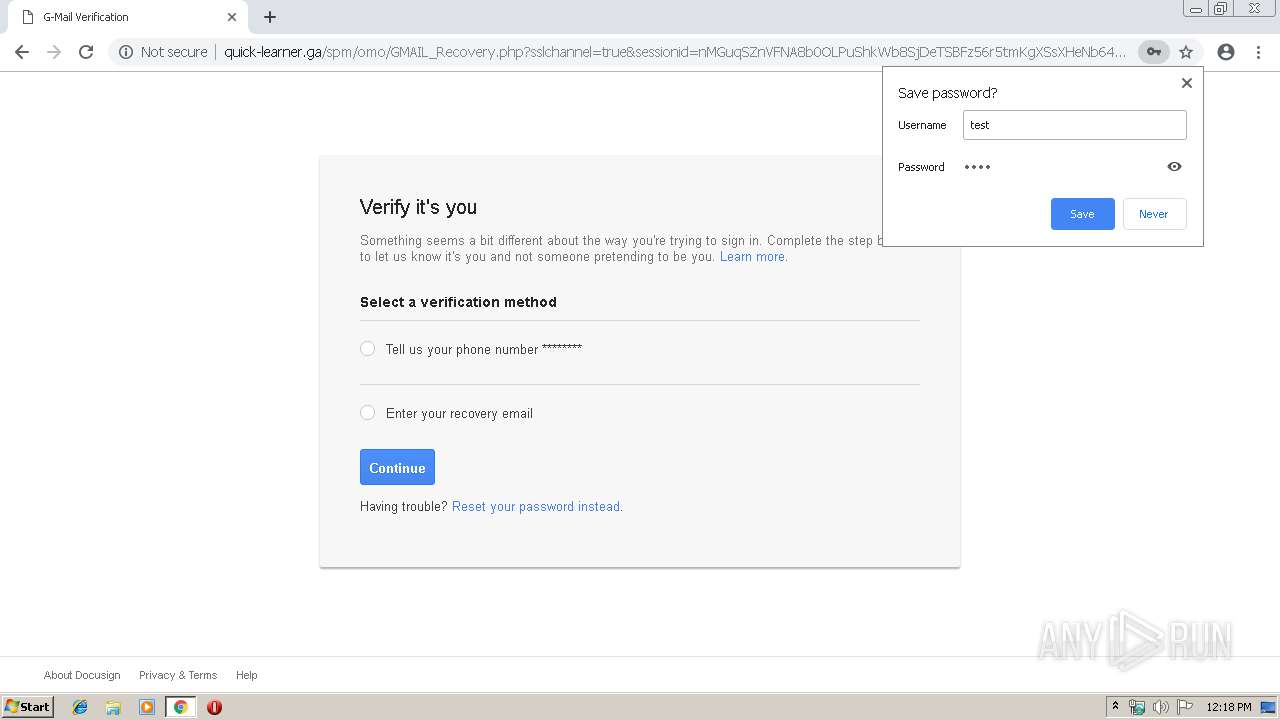
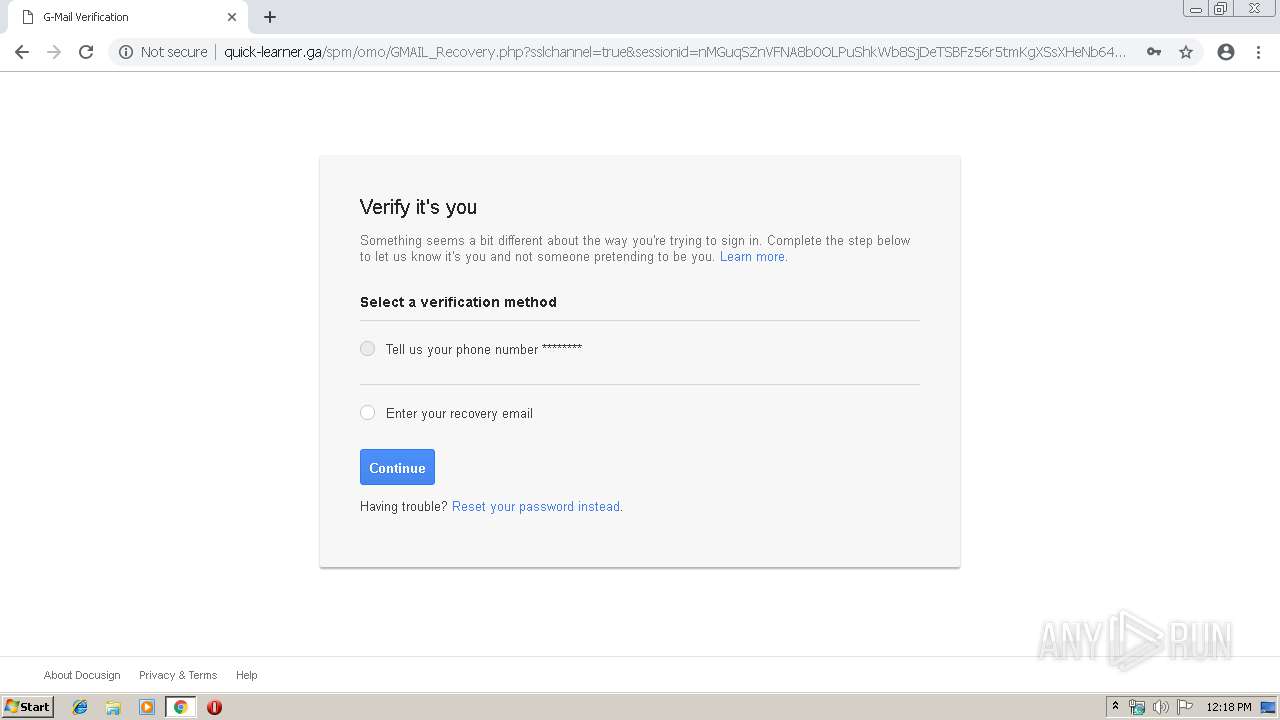
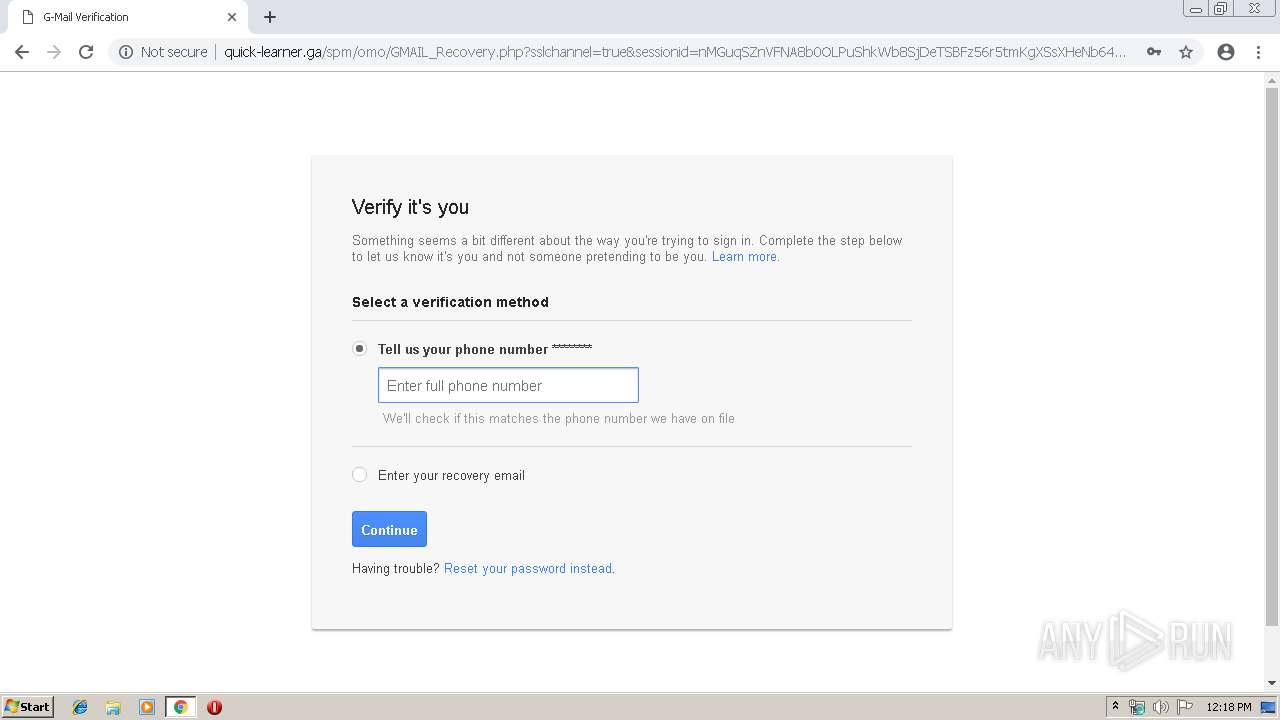
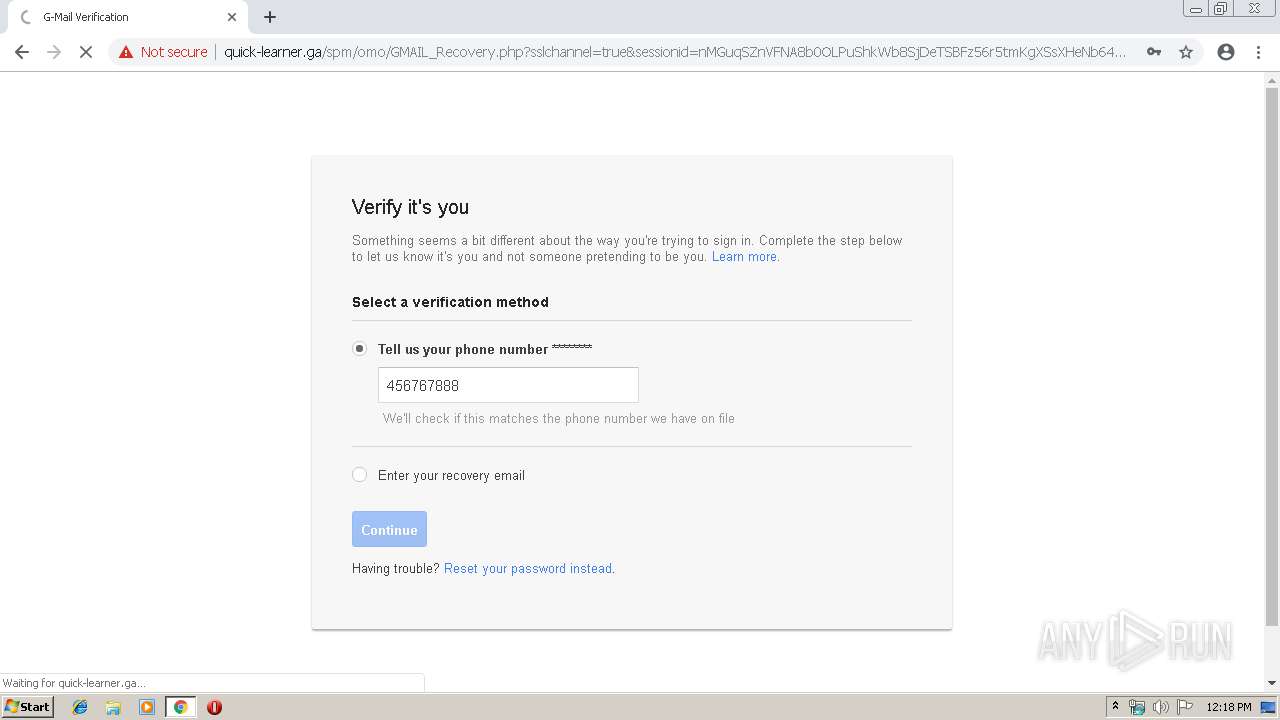
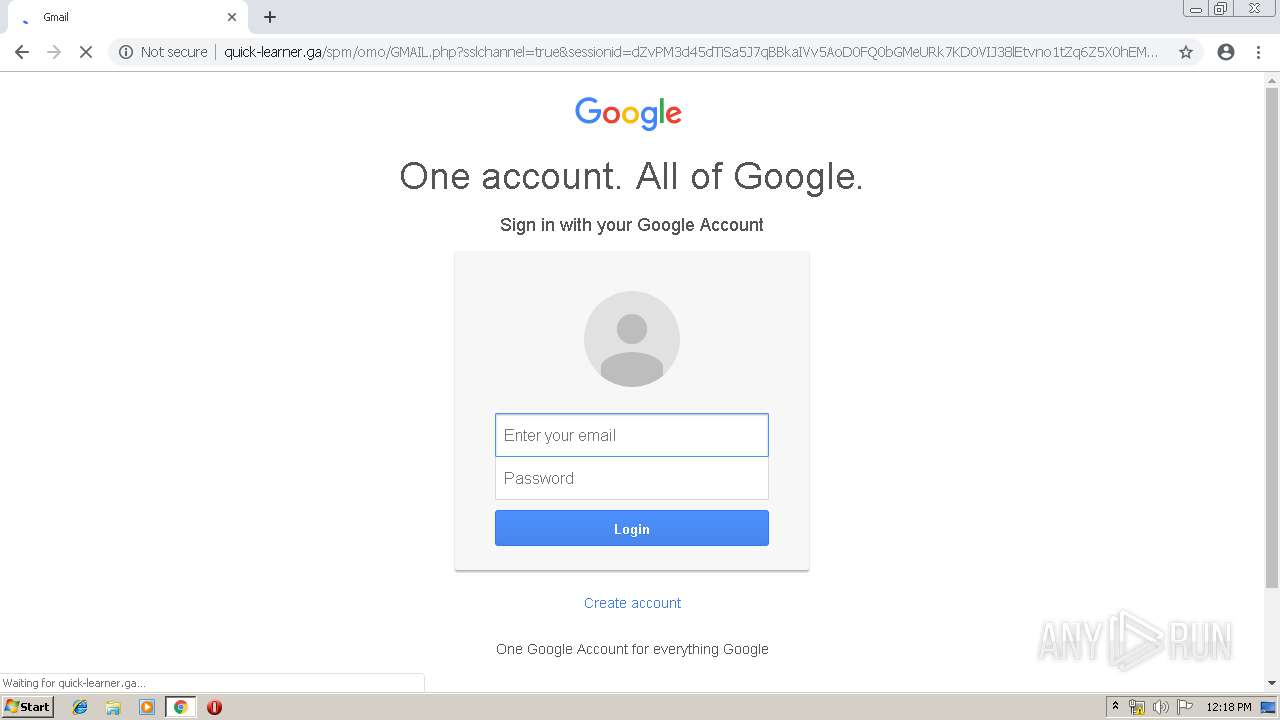
| URL: | http://quick-learner.ga/spm/omo/index.php |
| Full analysis: | https://app.any.run/tasks/62e27699-f589-413f-861d-76b52f08b5ee |
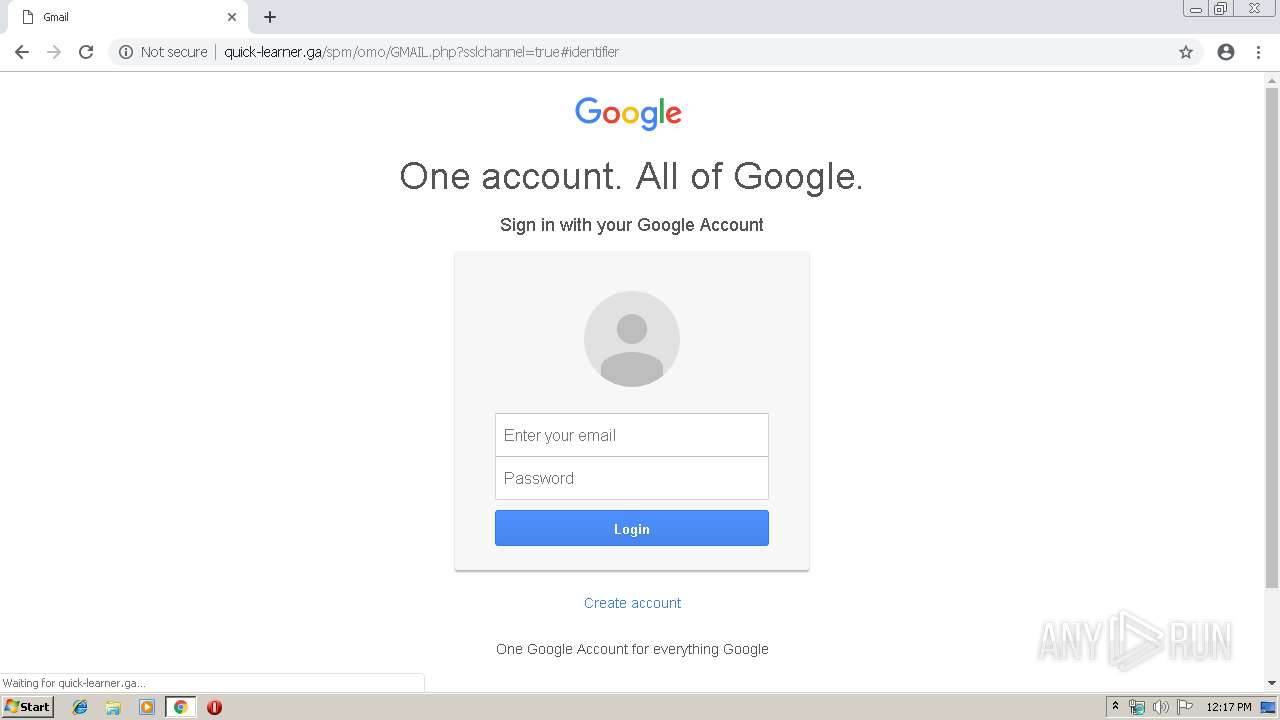
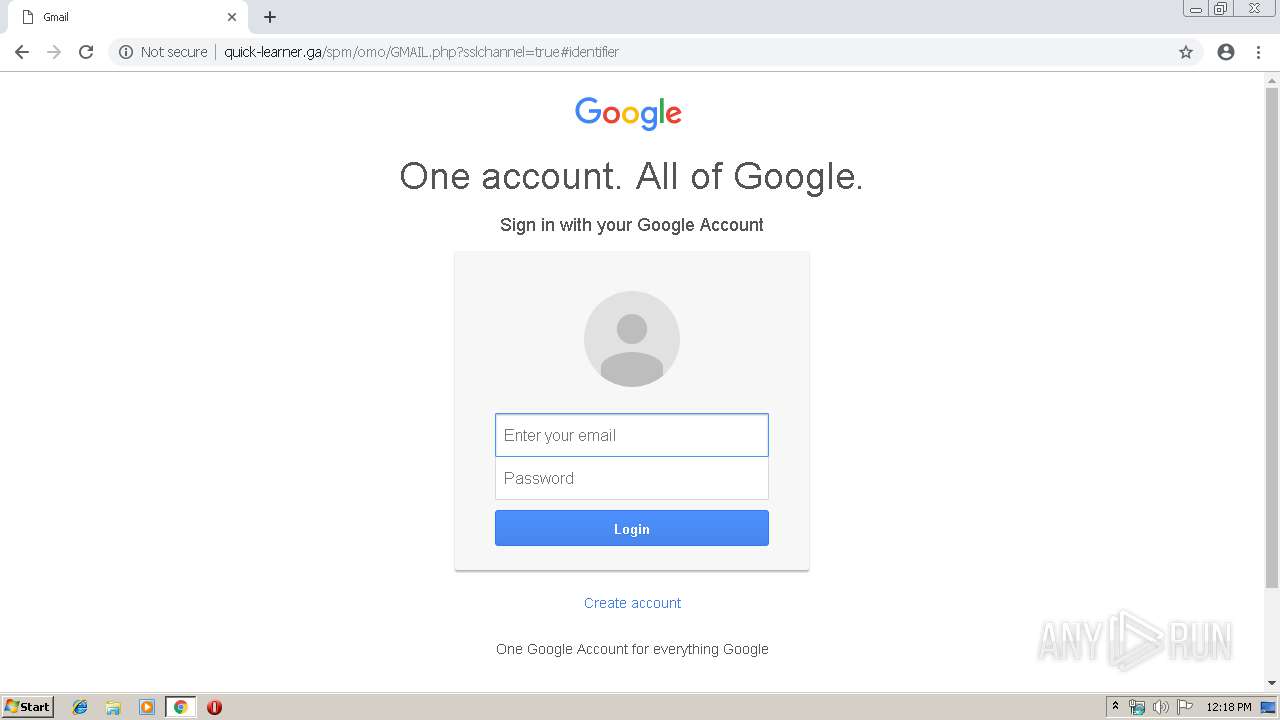
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 12:17:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1A1B1D9AB69F9500E4ACE6382CE13B10 |
| SHA1: | 11CADE24FA9AB4D42B358B84AFCE5A1D0635A2BE |
| SHA256: | 265E07466A24221E4C76114FCABFD8FB3EB792F484CE8577D79D33B09F2179F4 |
| SSDEEP: | 3:N1KPD0hbcoKGKPHn:CYlFUHn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1252)
INFO
Application launched itself
- chrome.exe (PID: 1252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
16
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=264 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16584214297696695215 --mojo-platform-channel-handle=3464 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://quick-learner.ga/spm/omo/index.php | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --service-pipe-token=6802940444899208819 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6802940444899208819 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2124 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5306442471095324621 --mojo-platform-channel-handle=3368 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2934121498688513396 --mojo-platform-channel-handle=3228 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --service-pipe-token=3068258364574766071 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3068258364574766071 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2132 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12384283658895180724 --mojo-platform-channel-handle=3460 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f620f18,0x6f620f28,0x6f620f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=984,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9767620293730585136 --mojo-platform-channel-handle=976 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
565
Read events
469
Write events
91
Delete events
5
Modification events
| (PID) Process: | (1252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1252-13197644258762375 |
Value: 259 | |||
| (PID) Process: | (1252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (1252) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
41
Text files
134
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 1252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 1252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\48f430b9-197f-4809-b8c5-b3747cdb460e.tmp | — | |
MD5:— | SHA256:— | |||
| 1252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
39
DNS requests
14
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3960 | chrome.exe | GET | 301 | 104.25.167.107:80 | http://cdn.iconscout.com/icon/free/png-512/yahoo-49-789855.png | US | — | — | whitelisted |
3960 | chrome.exe | GET | 200 | 159.203.58.237:80 | http://quick-learner.ga/spm/omo/assets/img/home_masthead_ipadonly.jpg | CA | image | 83.6 Kb | suspicious |
3960 | chrome.exe | GET | 200 | 159.203.58.237:80 | http://quick-learner.ga/spm/omo/assets/img/Boston.png | CA | image | 7.54 Kb | suspicious |
3960 | chrome.exe | GET | 200 | 159.203.58.237:80 | http://quick-learner.ga/spm/omo/assets/img/Pandora.png | CA | image | 16.5 Kb | suspicious |
3960 | chrome.exe | GET | 200 | 159.203.58.237:80 | http://quick-learner.ga/spm/omo/assets/img/favicon.ico | CA | image | 14.7 Kb | suspicious |
3960 | chrome.exe | GET | 200 | 159.203.58.237:80 | http://quick-learner.ga/spm/omo/assets/css/css_whE_FIKmCdJjmQukMY5DBbmkss9qZjXENYcyIcR-90c.css | CA | text | 18.1 Kb | suspicious |
3960 | chrome.exe | GET | 200 | 159.203.58.237:80 | http://quick-learner.ga/spm/omo/index.php | CA | html | 113 b | suspicious |
3960 | chrome.exe | GET | 200 | 159.203.58.237:80 | http://quick-learner.ga/spm/omo/assets/css/css_yXMMnLSSpPunfPzrxqTY5Fxi0thyZrjewLEjqduzimc.css | CA | text | 7.06 Kb | suspicious |
3960 | chrome.exe | GET | 200 | 159.203.58.237:80 | http://quick-learner.ga/spm/omo/assets/img/PG_433x90.png | CA | image | 4.81 Kb | suspicious |
3960 | chrome.exe | GET | 200 | 159.203.58.237:80 | http://quick-learner.ga/spm/omo/assets/css/css.css | CA | text | 4.48 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3960 | chrome.exe | 172.217.16.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 173.194.150.219:80 | r5---sn-5goeen7r.gvt1.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 159.203.58.237:80 | quick-learner.ga | Digital Ocean, Inc. | CA | suspicious |
3960 | chrome.exe | 104.25.167.107:443 | cdn.iconscout.com | Cloudflare Inc | US | shared |
3960 | chrome.exe | 104.24.21.54:80 | pngimg.com | Cloudflare Inc | US | shared |
3960 | chrome.exe | 74.120.188.204:443 | vignette.wikia.nocookie.net | — | US | suspicious |
3960 | chrome.exe | 91.198.174.208:443 | upload.wikimedia.org | Wikimedia Foundation, Inc. | NL | suspicious |
3960 | chrome.exe | 104.25.167.107:80 | cdn.iconscout.com | Cloudflare Inc | US | shared |
3960 | chrome.exe | 2.18.235.21:443 | store-images.s-microsoft.com | Akamai International B.V. | — | whitelisted |
3960 | chrome.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
quick-learner.ga |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
store-images.s-microsoft.com |
| whitelisted |
upload.wikimedia.org |
| whitelisted |
cdn.iconscout.com |
| whitelisted |
pngimg.com |
| whitelisted |
vignette.wikia.nocookie.net |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1072 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ga Domain |
3960 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP POST Request to Suspicious *.ga Domain |
3960 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP POST Request to Suspicious *.ga Domain |
3960 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP POST Request to Suspicious *.ga Domain |