| File name: | 01716999_3 |
| Full analysis: | https://app.any.run/tasks/d642a4e9-446c-4257-845b-1a59527da53f |
| Verdict: | Malicious activity |
| Analysis date: | December 13, 2019, 03:29:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D030566977768F71D8968282E536727C |
| SHA1: | E23540FEBAB10ACFD03124C9348857A218DE51FE |
| SHA256: | 265D56A99611DF9F872335FEB449921F1E8D1EAE7E72C83D1B7745DCCD2D385E |
| SSDEEP: | 98304:8a2VxbvzJSh+QY5AoNrBFfzglVPrQOv3/5K1IS3vF6UQQXZ5FLrk31tK:Z2vzJ5QOBk8Ov3/YuSFQQJ5Fklc |
MALICIOUS
Application was dropped or rewritten from another process
- RsDoctor.exe (PID: 2752)
- RSDChkEx.exe (PID: 3892)
- RSDChkEx.exe (PID: 3144)
- RSDChkEx.exe (PID: 2496)
Loads dropped or rewritten executable
- RSDChkEx.exe (PID: 3892)
- RsDoctor.exe (PID: 2752)
- RSDChkEx.exe (PID: 3144)
- RSDChkEx.exe (PID: 2496)
SUSPICIOUS
Reads internet explorer settings
- RsDoctor.exe (PID: 2752)
Executable content was dropped or overwritten
- 01716999_3.exe (PID: 784)
INFO
Reads settings of System Certificates
- RsDoctor.exe (PID: 2752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 107520 |
| InitializedDataSize: | 310784 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1a238 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.9.0.11 |
| ProductVersionNumber: | 0.9.0.11 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
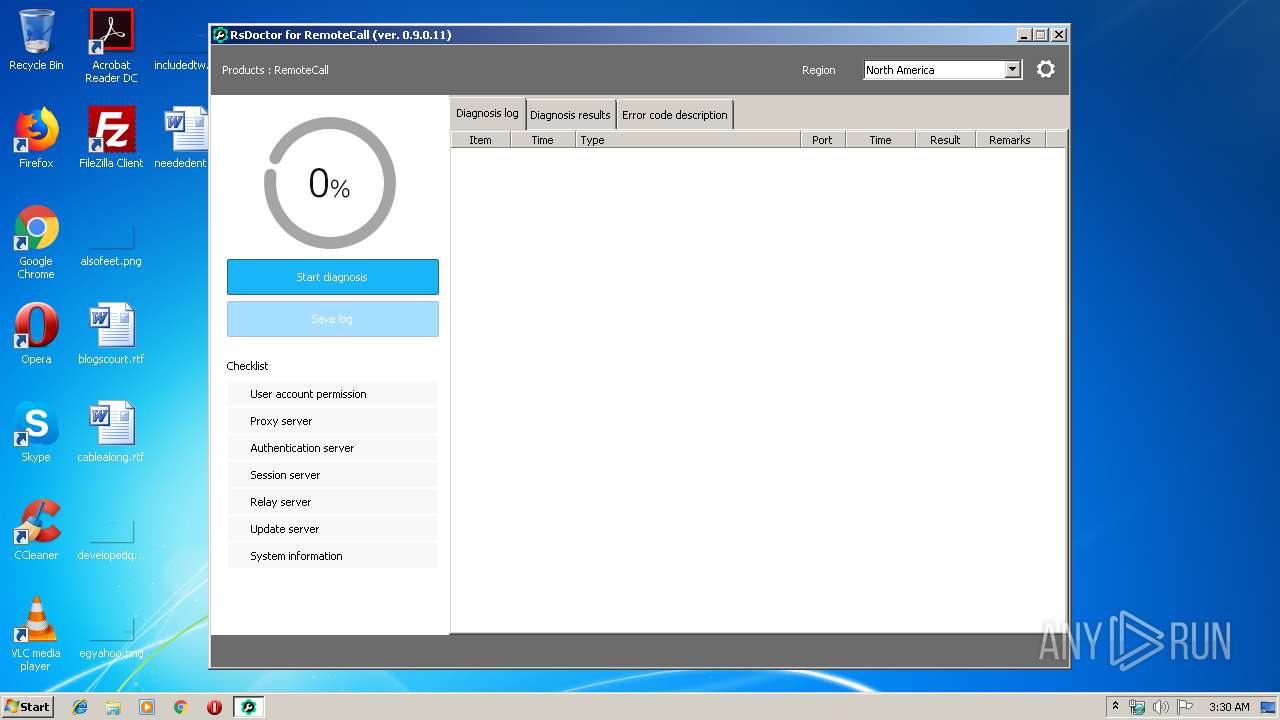
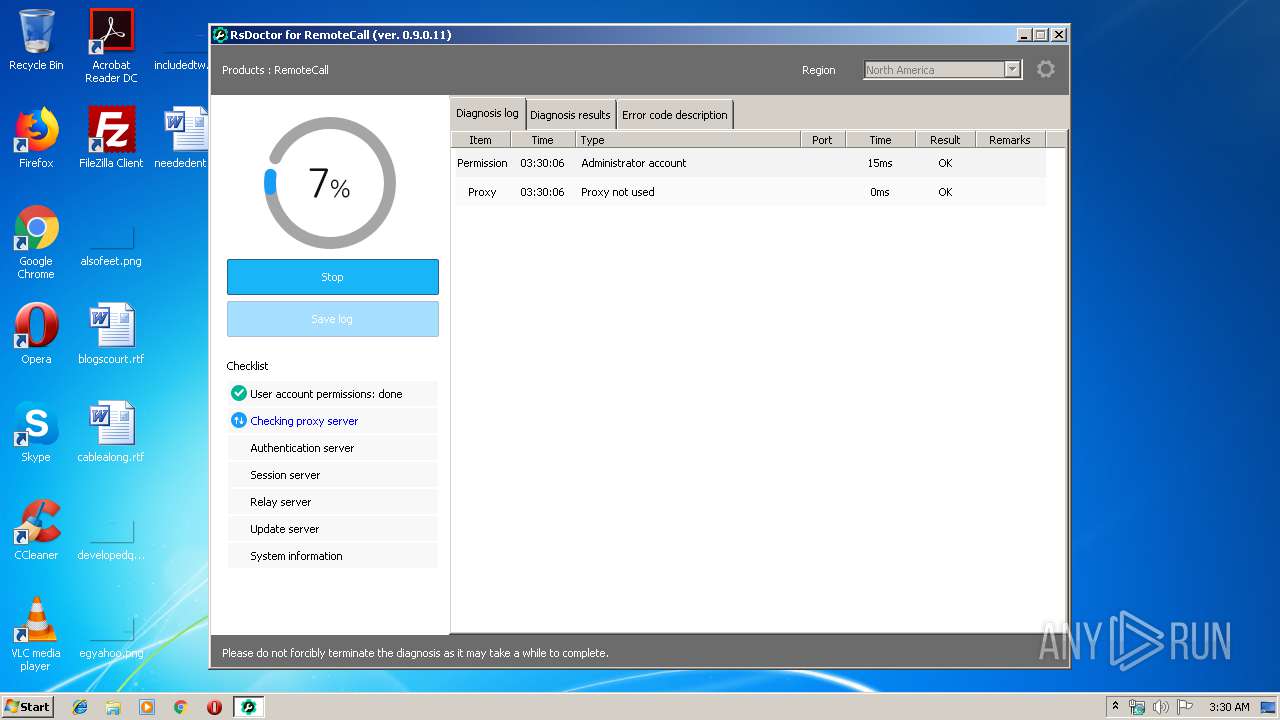
| CompanyName: | Rsupport Corporation |
| FileDescription: | RsDoctor |
| FileVersion: | 0.9.0.11 |
| InternalName: | RSDoctor.exe |
| LegalCopyright: | Copyright 2017 Rsupport Co. All rights reserved. |
| OriginalFileName: | RSDoctor.exe |
| ProductName: | RsDoctor |
| ProductVersion: | 0.9.0.11 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| CompanyName: | Rsupport Corporation |
| FileDescription: | RsDoctor |
| FileVersion: | 0.9.0.11 |
| InternalName: | RSDoctor.exe |
| LegalCopyright: | Copyright 2017 Rsupport Co. All rights reserved. |
| OriginalFilename: | RSDoctor.exe |
| ProductName: | RsDoctor |
| ProductVersion: | 0.9.0.11 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0001A3B0 | 0x0001A400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50326 |
DATA | 0x0001C000 | 0x00000D1C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43792 |
BSS | 0x0001D000 | 0x00A02585 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00A20000 | 0x00000EC4 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.63351 |
.tls | 0x00A21000 | 0x0000000C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00A22000 | 0x00000025 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.441241 |
.reloc | 0x00A23000 | 0x00001E0C | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00A25000 | 0x00049DD8 | 0x00049E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 3.71667 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.747 | 416 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.44707 | 744 | Latin 1 / Western European | Korean - Korea | RT_ICON |
3 | 3.30788 | 296 | Latin 1 / Western European | Korean - Korea | RT_ICON |
4 | 5.0919 | 3752 | Latin 1 / Western European | Korean - Korea | RT_ICON |
5 | 5.55772 | 2216 | Latin 1 / Western European | Korean - Korea | RT_ICON |
6 | 5.37348 | 1384 | Latin 1 / Western European | Korean - Korea | RT_ICON |
7 | 3.50707 | 270376 | Latin 1 / Western European | Korean - Korea | RT_ICON |
8 | 4.06201 | 9640 | Latin 1 / Western European | Korean - Korea | RT_ICON |
9 | 4.34809 | 4264 | Latin 1 / Western European | Korean - Korea | RT_ICON |
10 | 5.10701 | 1128 | Latin 1 / Western European | Korean - Korea | RT_ICON |
Imports
advapi32.dll |
gdi32.dll |
kernel32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
Total processes
42
Monitored processes
6
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 784 | "C:\Users\admin\AppData\Local\Temp\01716999_3.exe" | C:\Users\admin\AppData\Local\Temp\01716999_3.exe | explorer.exe | ||||||||||||
User: admin Company: Rsupport Corporation Integrity Level: HIGH Description: RsDoctor Exit code: 0 Version: 0.9.0.11 Modules
| |||||||||||||||
| 2496 | "C:\Users\admin\AppData\Local\Temp\~sfx00681EC7EB\RSDChkEx.exe" -u | C:\Users\admin\AppData\Local\Temp\~sfx00681EC7EB\RSDChkEx.exe | — | RsDoctor.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225504 Modules
| |||||||||||||||
| 2752 | "C:\Users\admin\AppData\Local\Temp\~sfx00681EC7EB\RsDoctor.exe" | C:\Users\admin\AppData\Local\Temp\~sfx00681EC7EB\RsDoctor.exe | 01716999_3.exe | ||||||||||||
User: admin Company: Rsupport Corporation Integrity Level: HIGH Description: RsDoctor Exit code: 0 Version: 0.9.0.11 Modules
| |||||||||||||||
| 2996 | "C:\Users\admin\AppData\Local\Temp\01716999_3.exe" | C:\Users\admin\AppData\Local\Temp\01716999_3.exe | — | explorer.exe | |||||||||||
User: admin Company: Rsupport Corporation Integrity Level: MEDIUM Description: RsDoctor Exit code: 3221226540 Version: 0.9.0.11 Modules
| |||||||||||||||
| 3144 | "C:\Users\admin\AppData\Local\Temp\~sfx00681EC7EB\RSDChkEx.exe" -s | C:\Users\admin\AppData\Local\Temp\~sfx00681EC7EB\RSDChkEx.exe | — | RsDoctor.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225504 Modules
| |||||||||||||||
| 3892 | "C:\Users\admin\AppData\Local\Temp\~sfx00681EC7EB\RSDChkEx.exe" -i | C:\Users\admin\AppData\Local\Temp\~sfx00681EC7EB\RSDChkEx.exe | — | RsDoctor.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225504 Modules
| |||||||||||||||
Total events
509
Read events
470
Write events
38
Delete events
1
Modification events
| (PID) Process: | (784) 01716999_3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (784) 01716999_3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2752) RsDoctor.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2752) RsDoctor.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2752) RsDoctor.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RsDoctor_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2752) RsDoctor.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RsDoctor_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2752) RsDoctor.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RsDoctor_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2752) RsDoctor.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RsDoctor_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2752) RsDoctor.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RsDoctor_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2752) RsDoctor.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RsDoctor_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
13
Suspicious files
4
Text files
23
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 784 | 01716999_3.exe | C:\Users\admin\AppData\Local\Temp\~sfx00681EC7EB\drvi.dll | executable | |
MD5:— | SHA256:— | |||
| 784 | 01716999_3.exe | C:\Users\admin\AppData\Local\Temp\~sfx00681EC7EB\rcproclu.dll | executable | |
MD5:— | SHA256:— | |||
| 784 | 01716999_3.exe | C:\Users\admin\AppData\Local\Temp\~sfx00681EC7EB\rc45.dll | executable | |
MD5:— | SHA256:— | |||
| 784 | 01716999_3.exe | C:\Users\admin\AppData\Local\Temp\~sfx00681EC7EB\rsdoctor.ini | text | |
MD5:— | SHA256:— | |||
| 784 | 01716999_3.exe | C:\Users\admin\AppData\Local\Temp\~sfx00681EC7EB\RsDoctor.exe | executable | |
MD5:— | SHA256:— | |||
| 784 | 01716999_3.exe | C:\Users\admin\AppData\Local\Temp\~sfx00681EC7EB\rsdreset.jpg | image | |
MD5:— | SHA256:— | |||
| 784 | 01716999_3.exe | C:\Users\admin\AppData\Local\Temp\~sfx00681EC7EB\rsd_eng.lng | text | |
MD5:— | SHA256:— | |||
| 784 | 01716999_3.exe | C:\Users\admin\AppData\Local\Temp\~sfx00681EC7EB\RSDChkEx.exe | executable | |
MD5:— | SHA256:— | |||
| 784 | 01716999_3.exe | C:\Users\admin\AppData\Local\Temp\~sfx00681EC7EB\psieng.dll | executable | |
MD5:— | SHA256:— | |||
| 784 | 01716999_3.exe | C:\Users\admin\AppData\Local\Temp\~sfx00681EC7EB\errcode.html | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
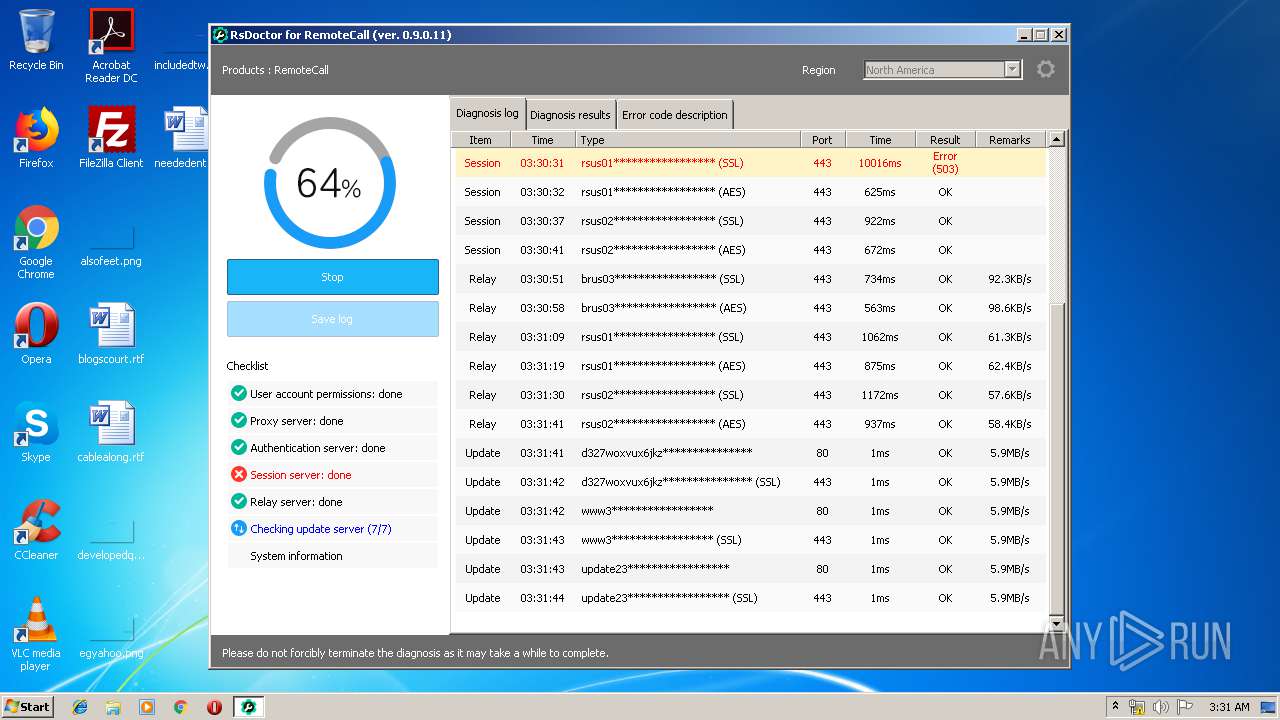
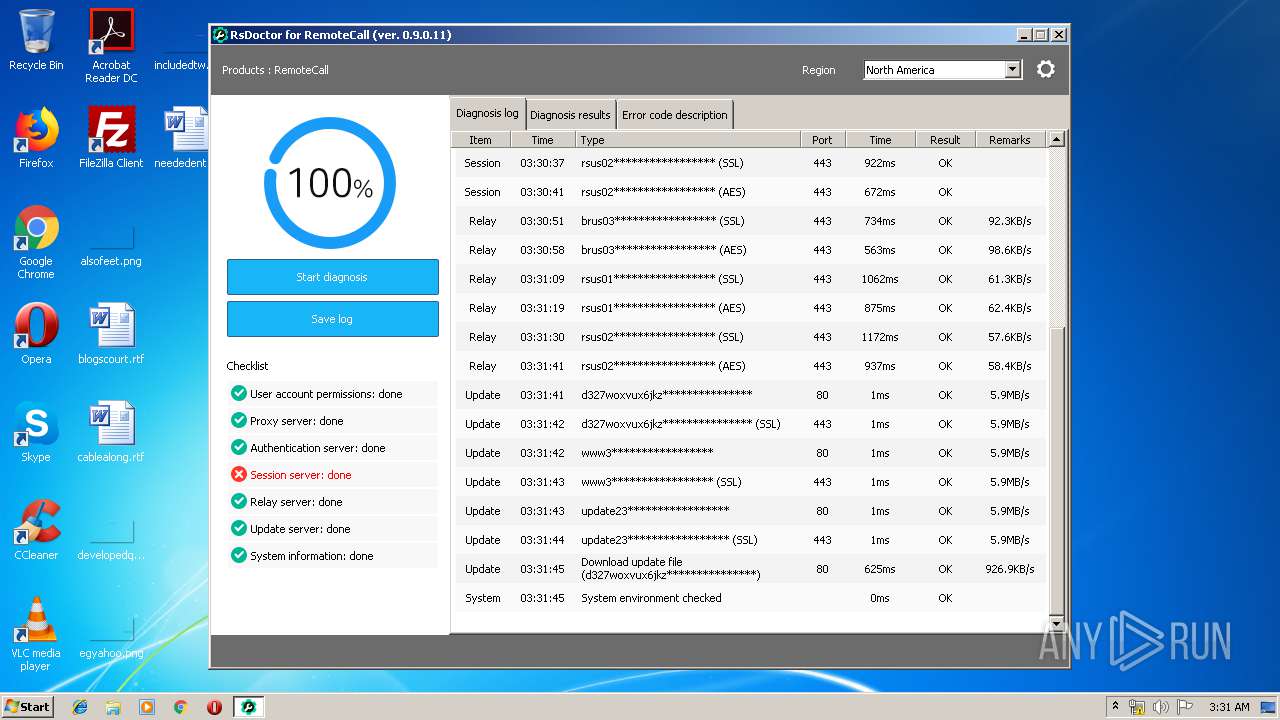
HTTP(S) requests
8
TCP/UDP connections
29
DNS requests
8
Threats
18
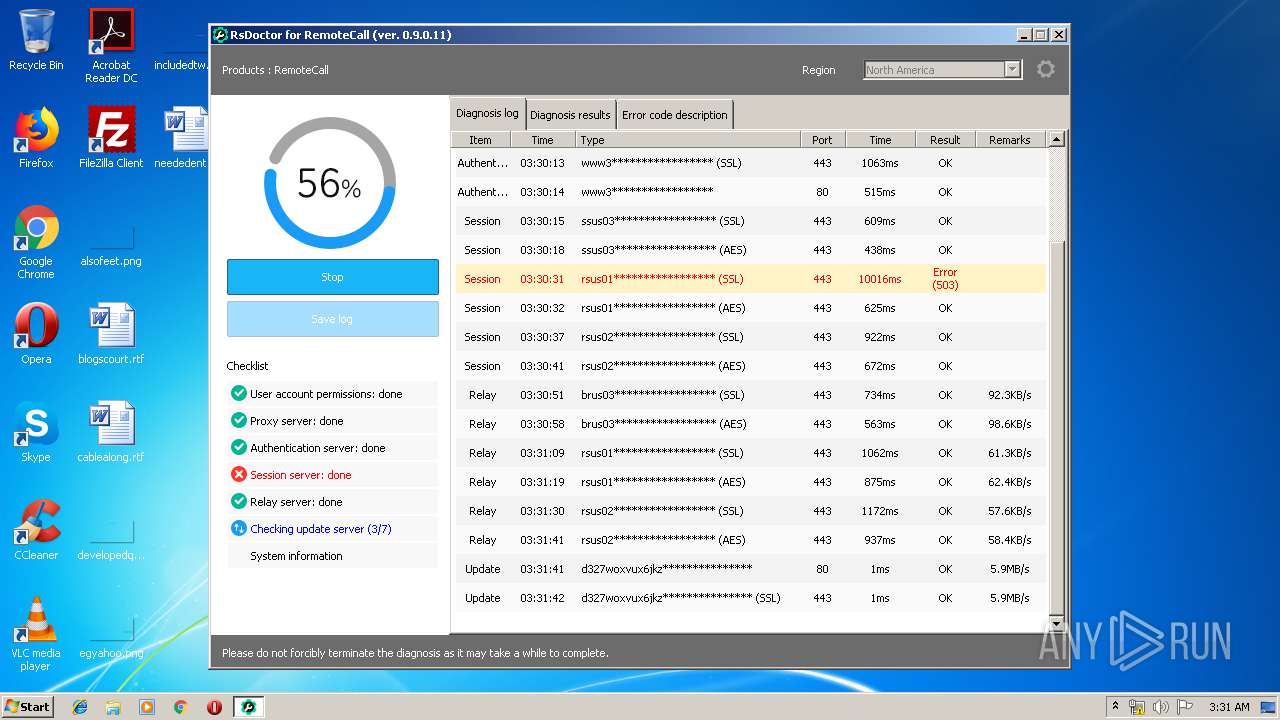
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2752 | RsDoctor.exe | GET | — | 52.196.240.247:80 | http://www3.startsupport.com/update/rcv50/provs.zip | JP | — | — | suspicious |
2752 | RsDoctor.exe | GET | 200 | 13.35.254.4:80 | http://d327woxvux6jkz.cloudfront.net/update/rcv50/provs.zip | US | compressed | 5.74 Kb | malicious |
2752 | RsDoctor.exe | GET | 200 | 13.35.254.4:80 | http://d327woxvux6jkz.cloudfront.net/update/rcv50/file000.rsz | US | binary | 565 Kb | malicious |
2752 | RsDoctor.exe | GET | — | 52.196.240.247:80 | http://www3.startsupport.com/update/rsdoctor/rsdsvrex.ini | JP | — | — | suspicious |
2752 | RsDoctor.exe | GET | 200 | 13.35.254.4:80 | http://d327woxvux6jkz.cloudfront.net/update/rcv50/provs.zip | US | compressed | 5.74 Kb | malicious |
2752 | RsDoctor.exe | POST | 200 | 13.124.218.176:80 | http://www1.startsupport.com/BootStrapper.aspx | KR | xml | 410 b | suspicious |
2752 | RsDoctor.exe | POST | 200 | 52.196.240.247:80 | http://www3.startsupport.com/BootStrapper.aspx | JP | xml | 410 b | suspicious |
2752 | RsDoctor.exe | GET | — | 52.193.103.23:80 | http://update23.startsupport.com/update/rcv50/provs.zip | JP | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
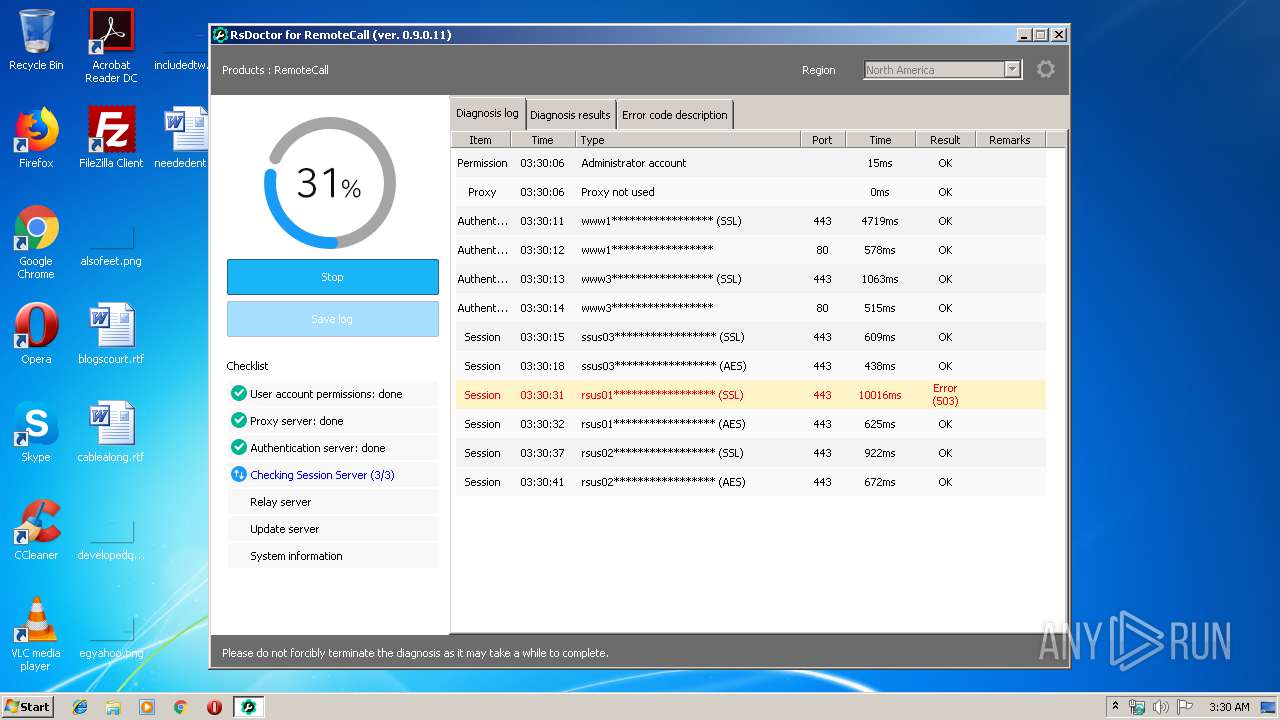
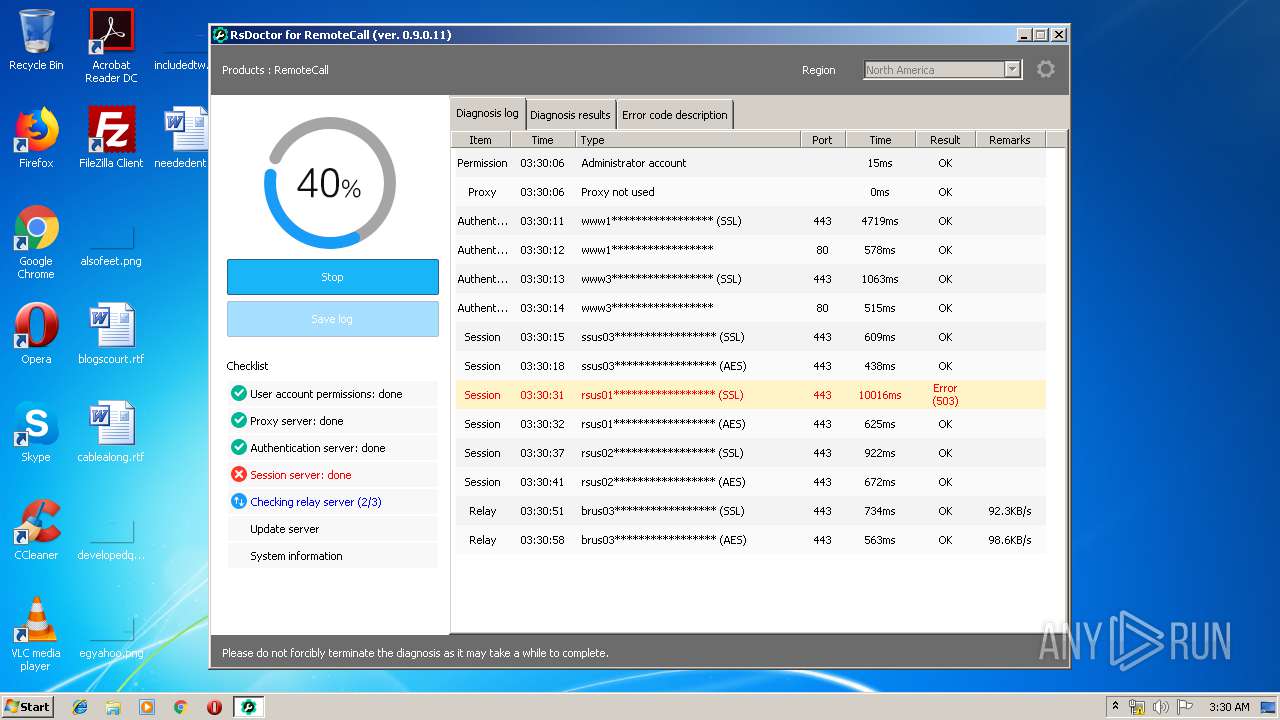
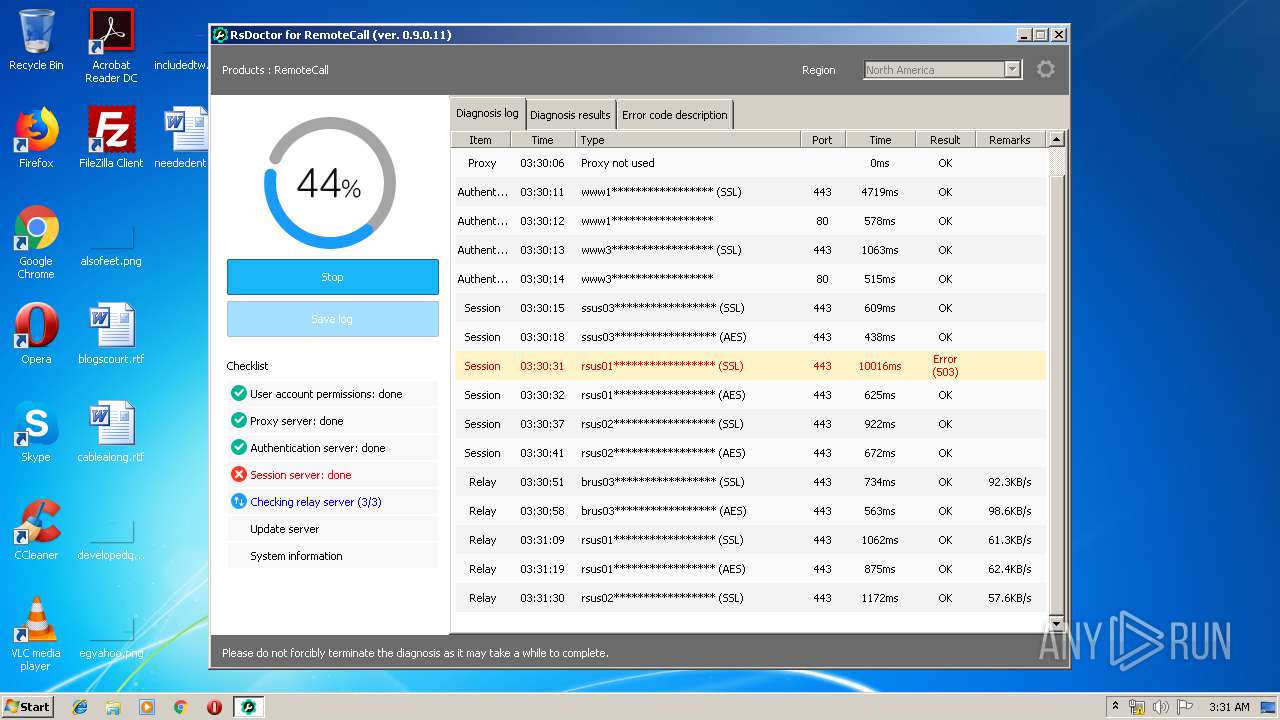
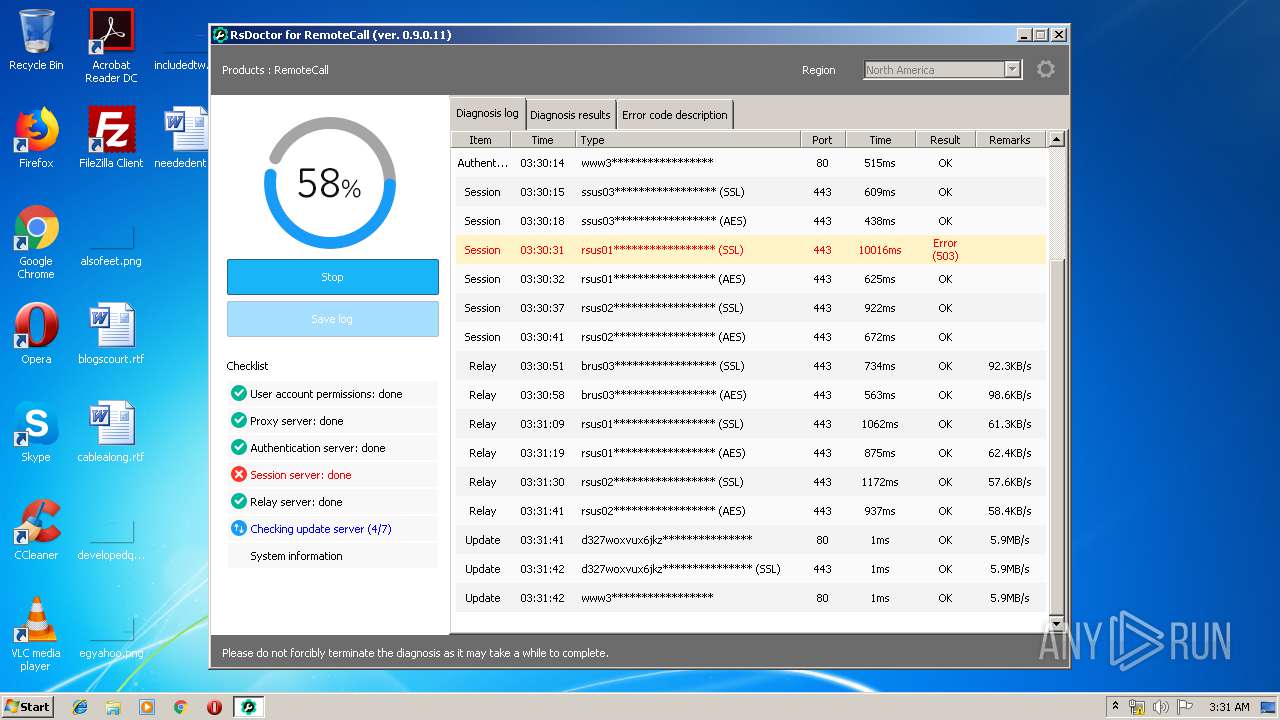
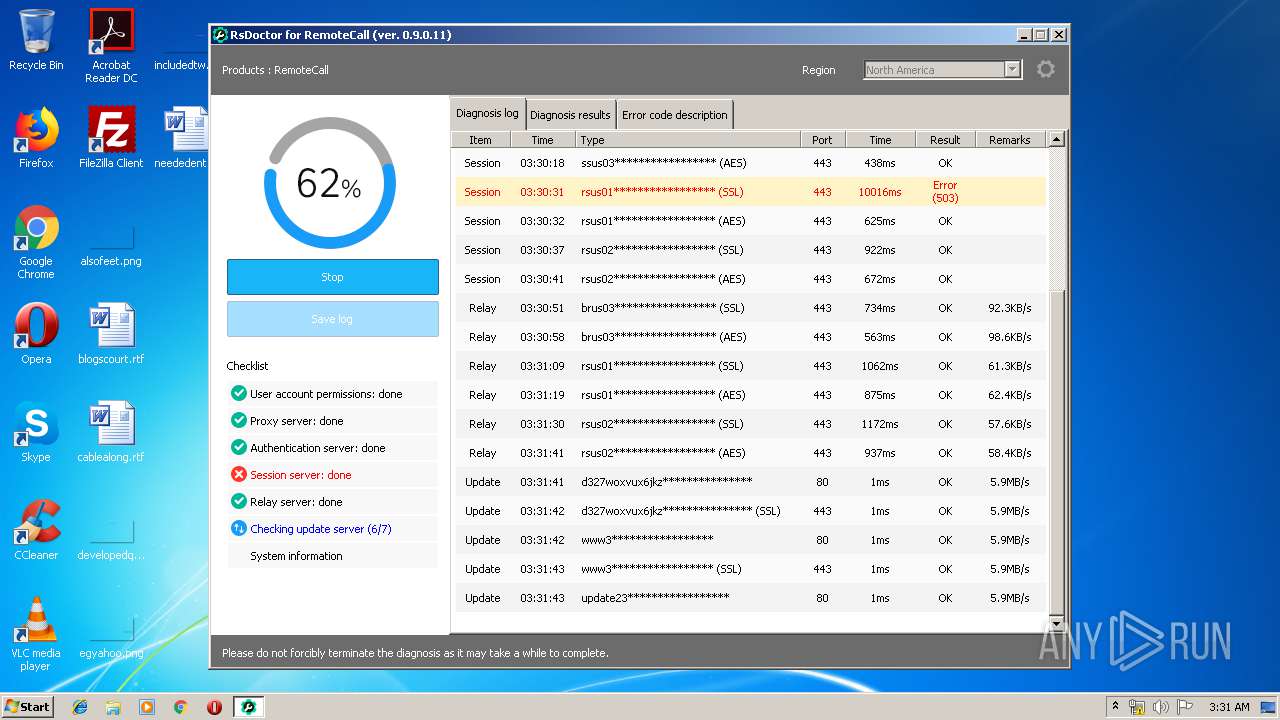
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
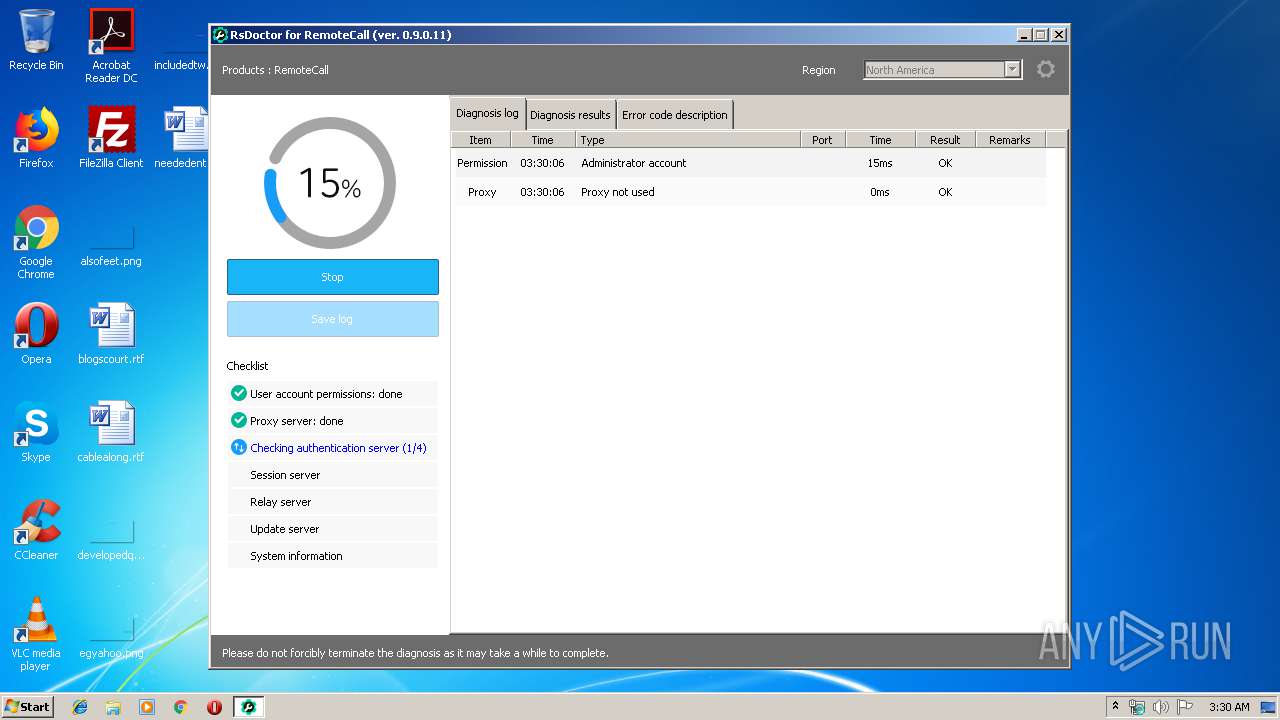
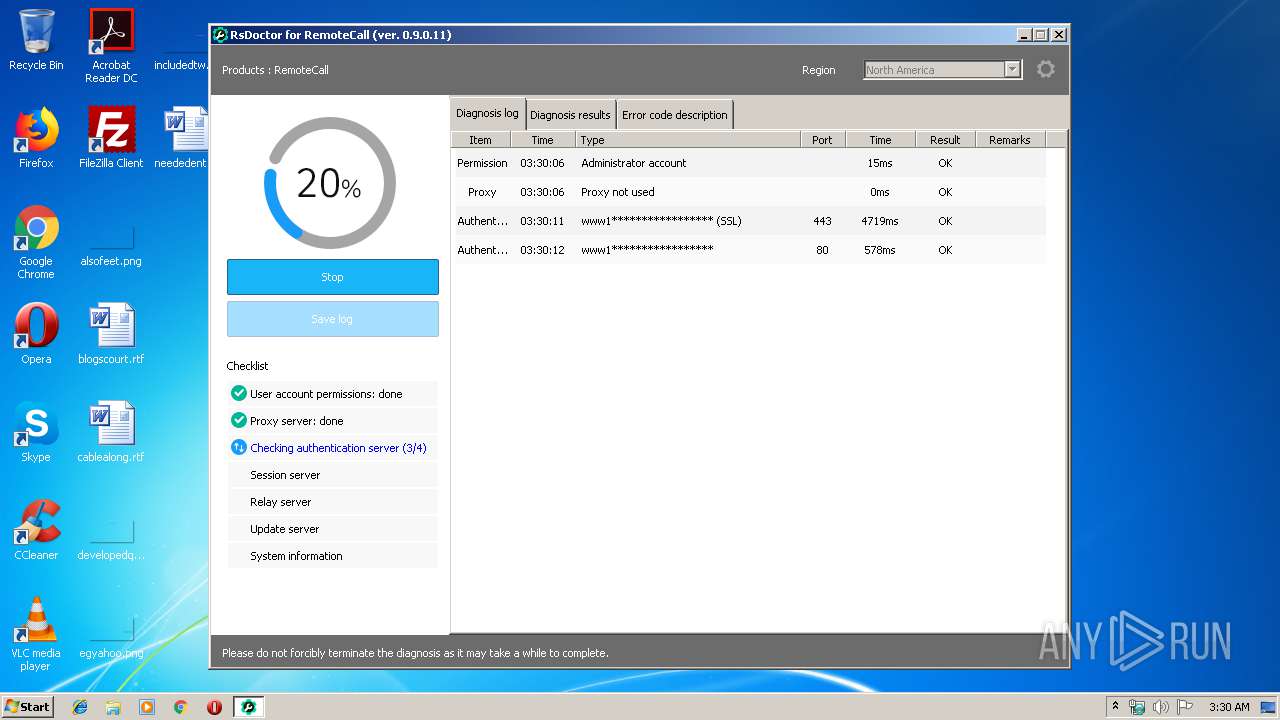
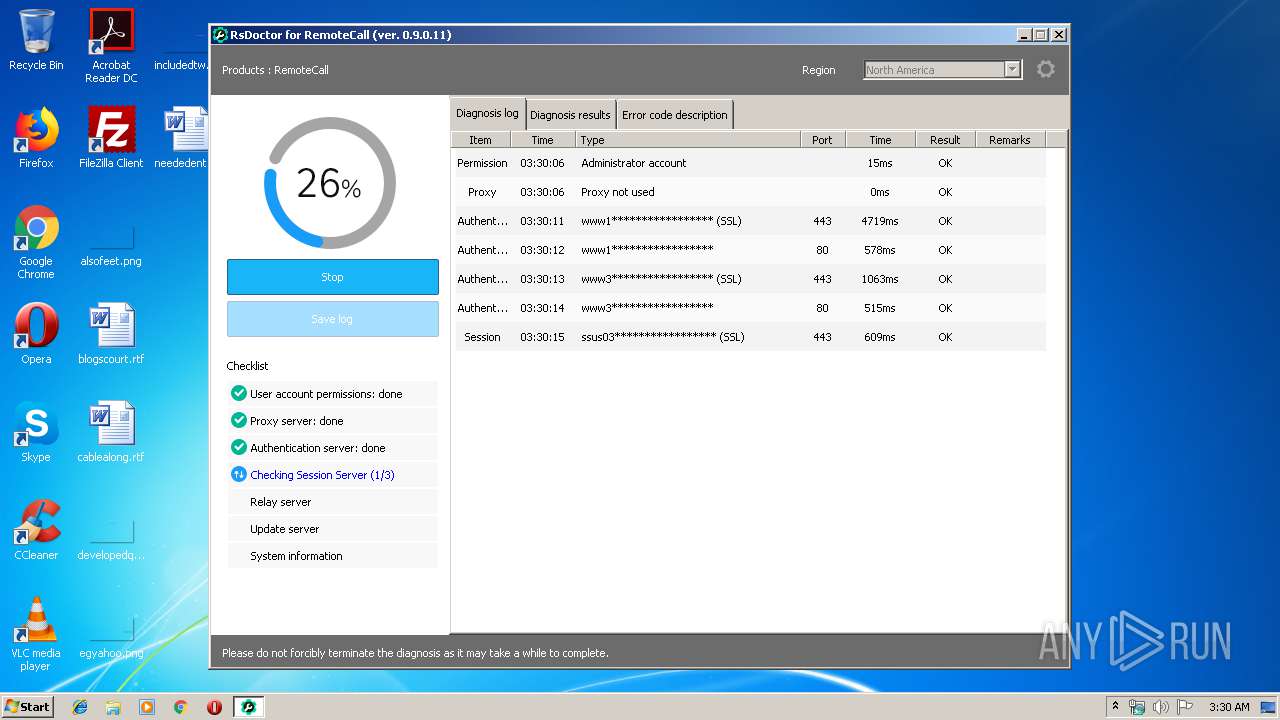
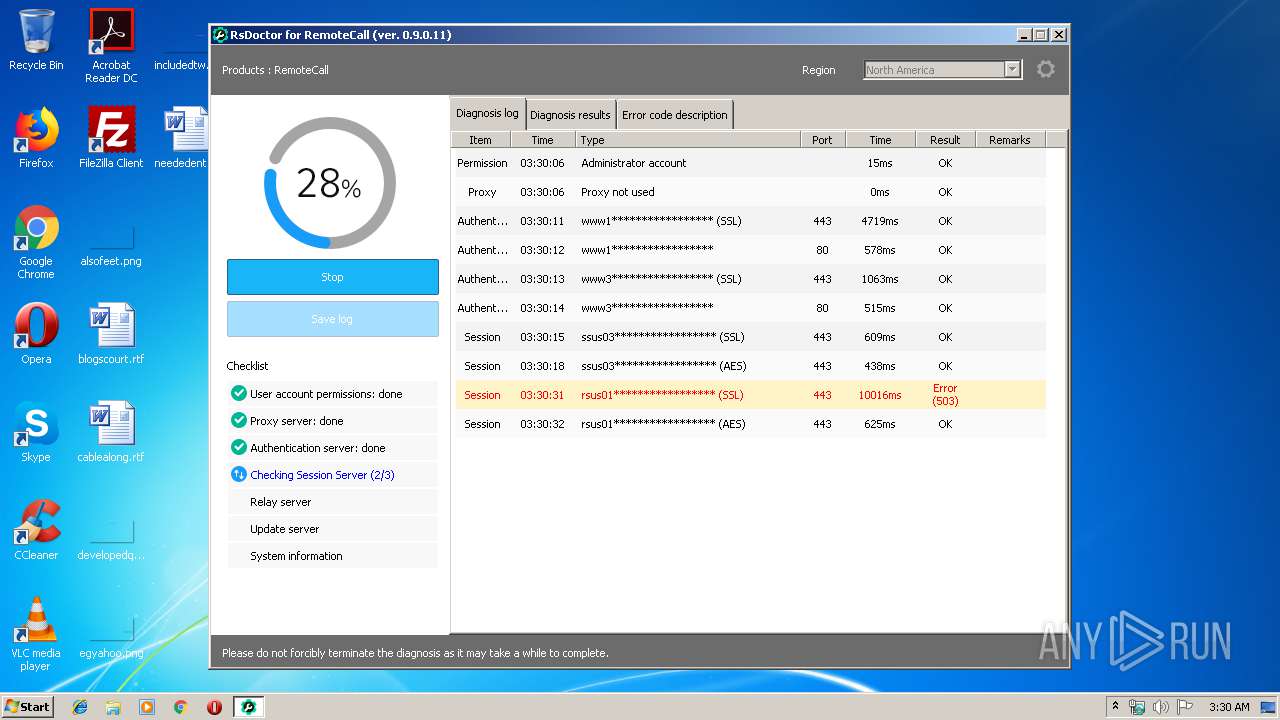
2752 | RsDoctor.exe | 52.196.240.247:80 | www3.startsupport.com | Amazon.com, Inc. | JP | unknown |
2752 | RsDoctor.exe | 13.124.218.176:80 | www1.startsupport.com | Amazon.com, Inc. | KR | suspicious |
2752 | RsDoctor.exe | 13.124.218.176:443 | www1.startsupport.com | Amazon.com, Inc. | KR | suspicious |
2752 | RsDoctor.exe | 34.197.55.207:443 | ssus03.startsupport.com | Amazon.com, Inc. | US | unknown |
2752 | RsDoctor.exe | 52.196.240.247:443 | www3.startsupport.com | Amazon.com, Inc. | JP | unknown |
2752 | RsDoctor.exe | 54.149.172.37:443 | rsus02.startsupport.com | Amazon.com, Inc. | US | unknown |
2752 | RsDoctor.exe | 52.193.103.23:80 | update23.startsupport.com | Amazon.com, Inc. | JP | unknown |
2752 | RsDoctor.exe | 52.9.17.232:443 | rsus01.startsupport.com | Amazon.com, Inc. | US | unknown |
2752 | RsDoctor.exe | 13.35.254.4:443 | d327woxvux6jkz.cloudfront.net | — | US | malicious |
2752 | RsDoctor.exe | 13.35.254.4:80 | d327woxvux6jkz.cloudfront.net | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www3.startsupport.com |
| suspicious |
www1.startsupport.com |
| suspicious |
ssus03.startsupport.com |
| unknown |
rsus01.startsupport.com |
| unknown |
rsus02.startsupport.com |
| unknown |
brus03.startsupport.com |
| unknown |
d327woxvux6jkz.cloudfront.net |
| malicious |
update23.startsupport.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2752 | RsDoctor.exe | Misc activity | ET POLICY Signed TLS Certificate with md5WithRSAEncryption |
2752 | RsDoctor.exe | Misc activity | ET POLICY Signed TLS Certificate with md5WithRSAEncryption |
2752 | RsDoctor.exe | Misc activity | ET POLICY Signed TLS Certificate with md5WithRSAEncryption |
2752 | RsDoctor.exe | Misc activity | ET POLICY Signed TLS Certificate with md5WithRSAEncryption |
2752 | RsDoctor.exe | Misc activity | ET POLICY Signed TLS Certificate with md5WithRSAEncryption |
2752 | RsDoctor.exe | Misc activity | ET POLICY Signed TLS Certificate with md5WithRSAEncryption |
2752 | RsDoctor.exe | Misc activity | ET POLICY Signed TLS Certificate with md5WithRSAEncryption |
2752 | RsDoctor.exe | Misc activity | ET POLICY Signed TLS Certificate with md5WithRSAEncryption |
2752 | RsDoctor.exe | Misc activity | ET POLICY Signed TLS Certificate with md5WithRSAEncryption |
2752 | RsDoctor.exe | Misc activity | ET POLICY Signed TLS Certificate with md5WithRSAEncryption |
Process | Message |
|---|---|
RsDoctor.exe | [CRCWeb::WebLog]Call Page2 : https://www1.startsupport.com:443/BootStrapper.aspx
|
RsDoctor.exe | [CRCWeb::WebLog]Call Page returncode : 992, status : 200
|
RsDoctor.exe | [CRCWeb::WebLog]Call Page2 : http://www1.startsupport.com:80/BootStrapper.aspx
|
RsDoctor.exe | [CRCWeb::WebLog]Call Page returncode : 992, status : 200
|
RsDoctor.exe | [CRCWeb::WebLog]Call Page2 : https://www3.startsupport.com:443/BootStrapper.aspx
|
RsDoctor.exe | [CRCWeb::WebLog]Call Page returncode : 992, status : 200
|
RsDoctor.exe | [CRCWeb::WebLog]Call Page2 : http://www3.startsupport.com:80/BootStrapper.aspx
|
RsDoctor.exe | [CRCWeb::WebLog]Call Page returncode : 992, status : 200
|
RsDoctor.exe | [CConnectObject::ReceiveProc] Thread Start
|
RsDoctor.exe | SocketConnectionDone(nConnectCode = 1125, dwError = 0)
|