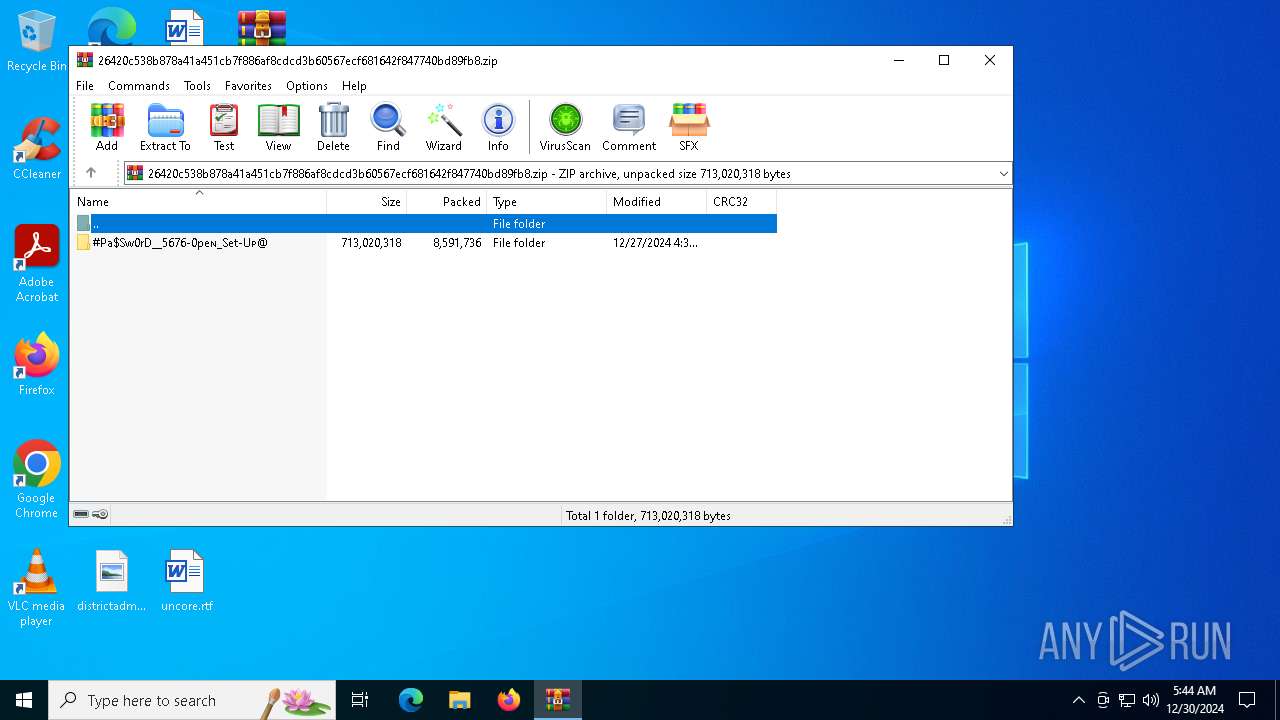
| File name: | 26420c538b878a41a451cb7f886af8cdcd3b60567ecf681642f847740bd89fb8.zip |
| Full analysis: | https://app.any.run/tasks/b168e79e-b5a7-48e6-ab82-0a9f82c41f4f |
| Verdict: | Malicious activity |
| Analysis date: | December 30, 2024, 05:44:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | A7E58F4E61160D04CE1E266DE6593C16 |
| SHA1: | C328DB135775C78AC69538726A4AA53A45AEB115 |
| SHA256: | 26420C538B878A41A451CB7F886AF8CDCD3B60567ECF681642F847740BD89FB8 |
| SSDEEP: | 98304:ptCNk8bBnB6EJ9opxzDz4cxMkKthMLQm5YQ+tgSk4G/Xh798Rd1kSj1OTkqgaFBC:5YvL1ypoEvqoQJF |
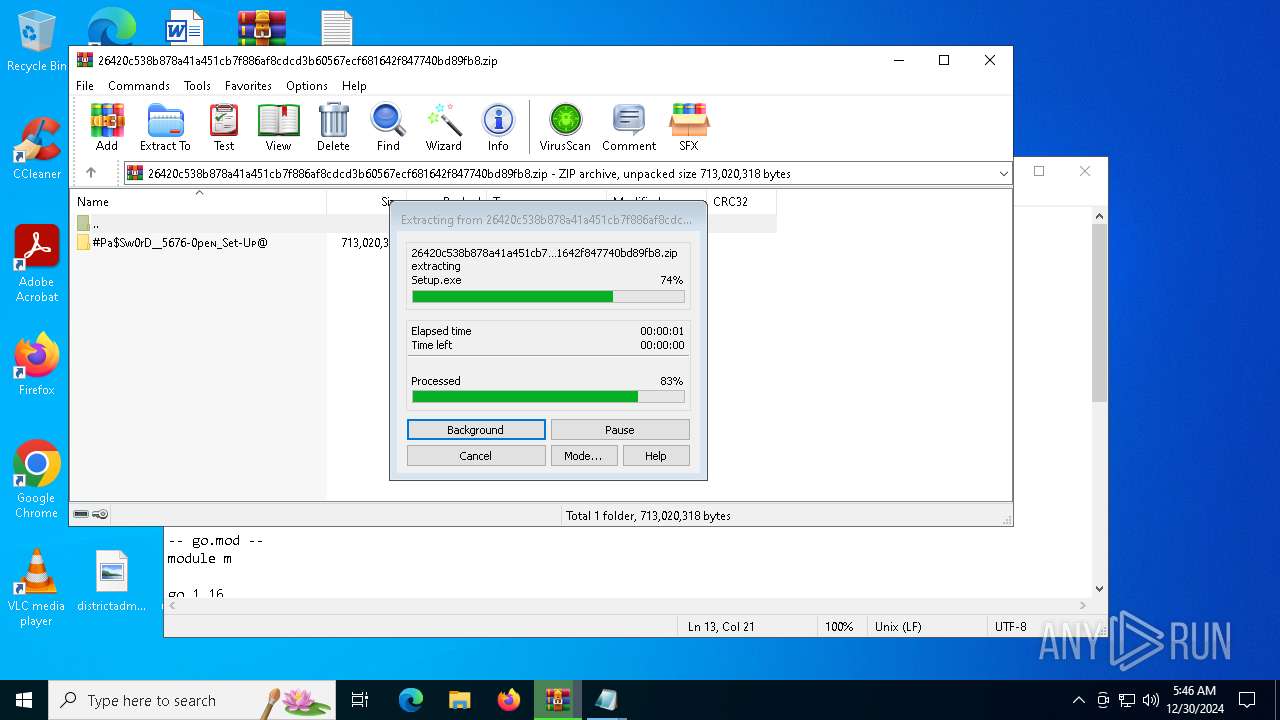
MALICIOUS
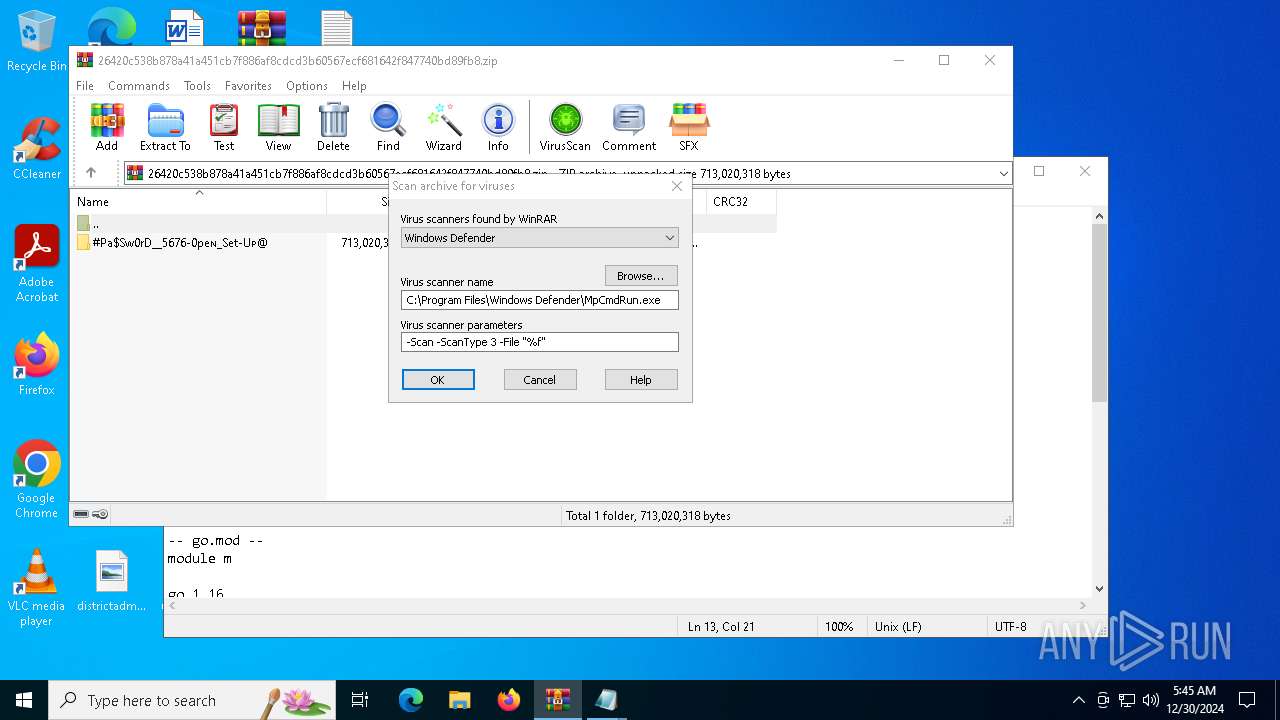
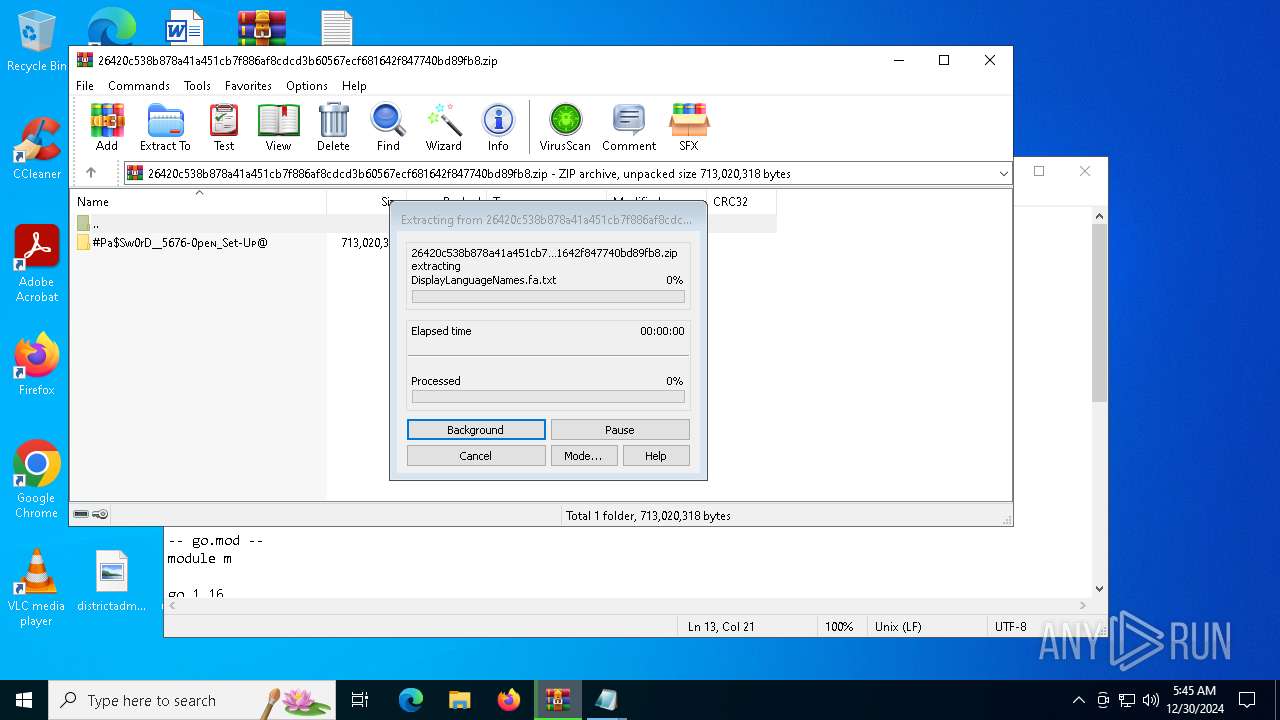
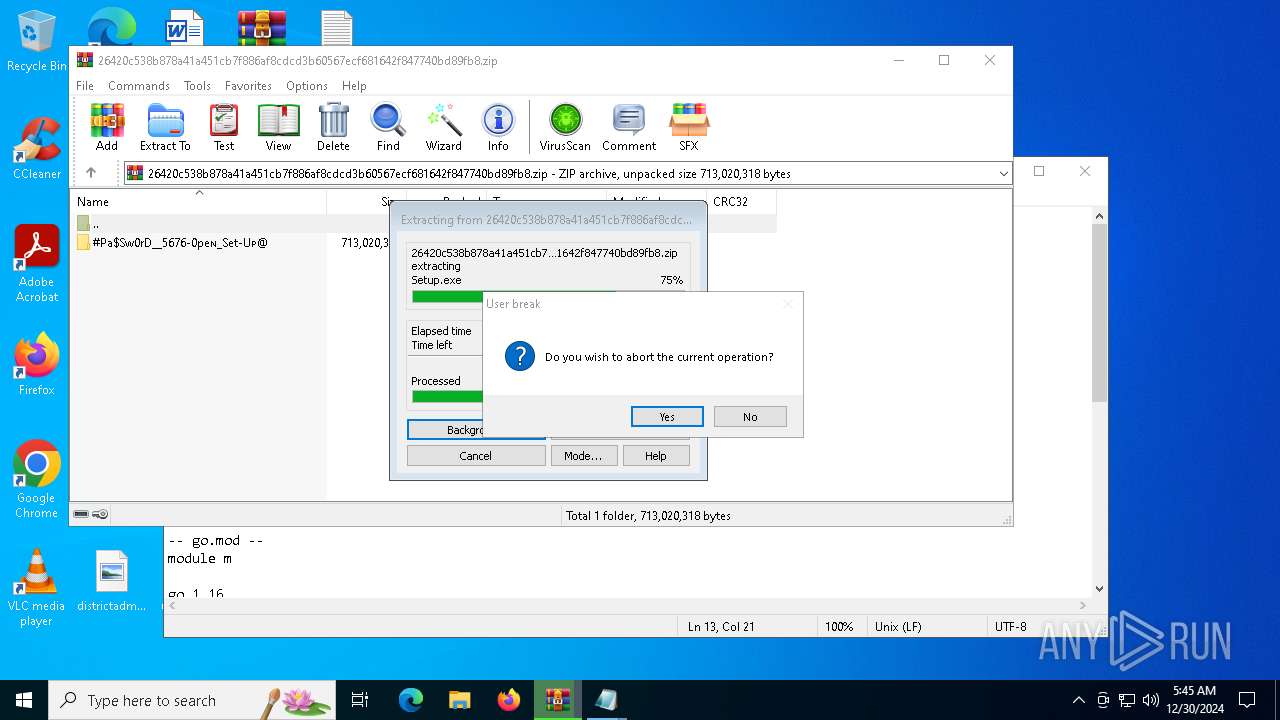
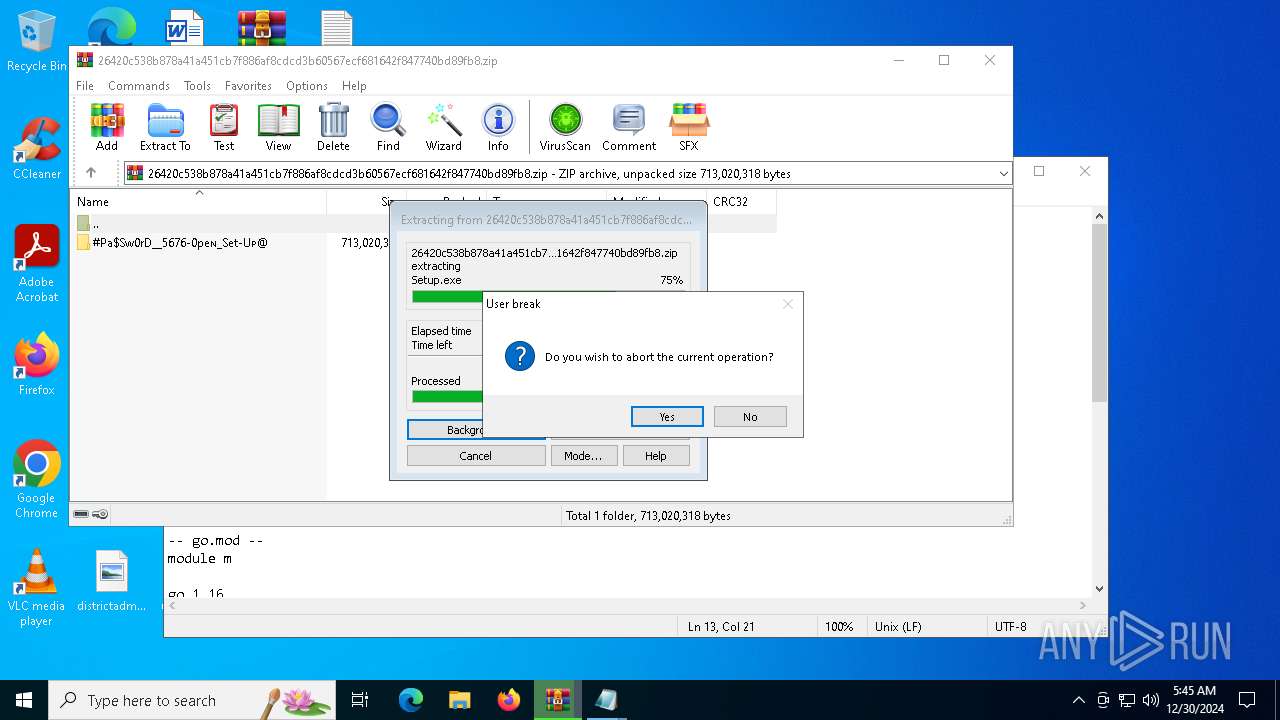
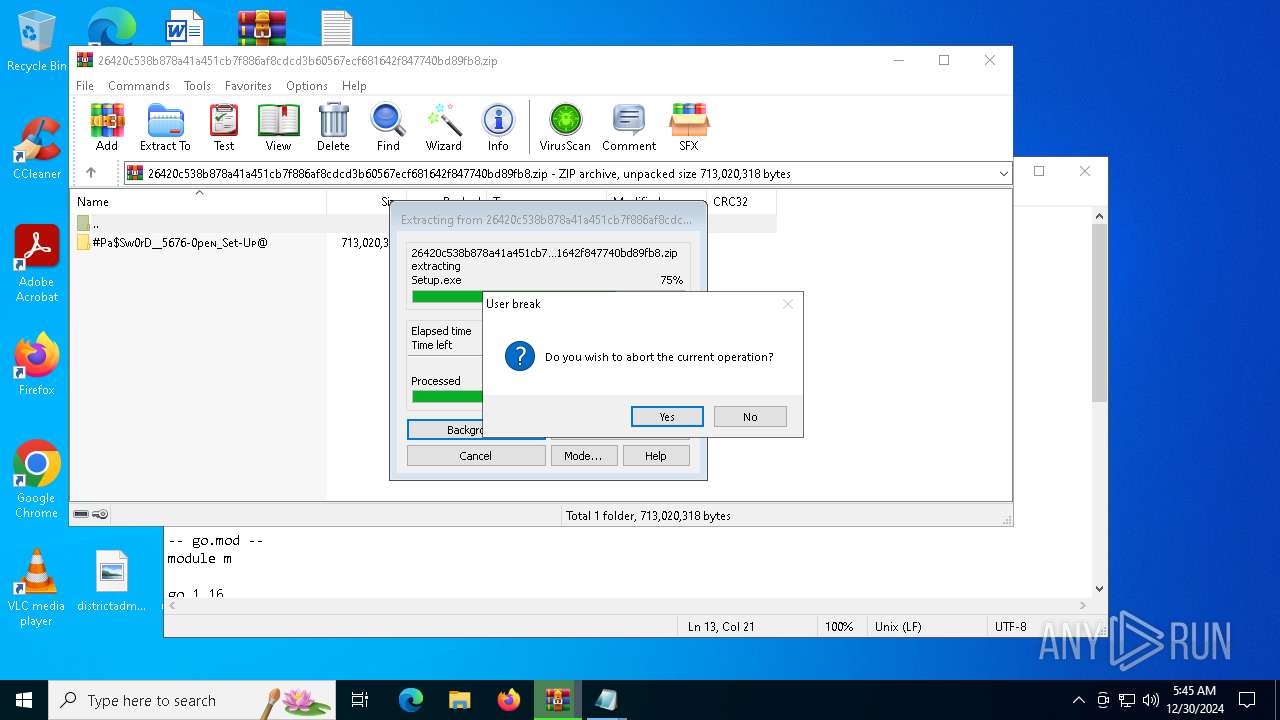
Generic archive extractor
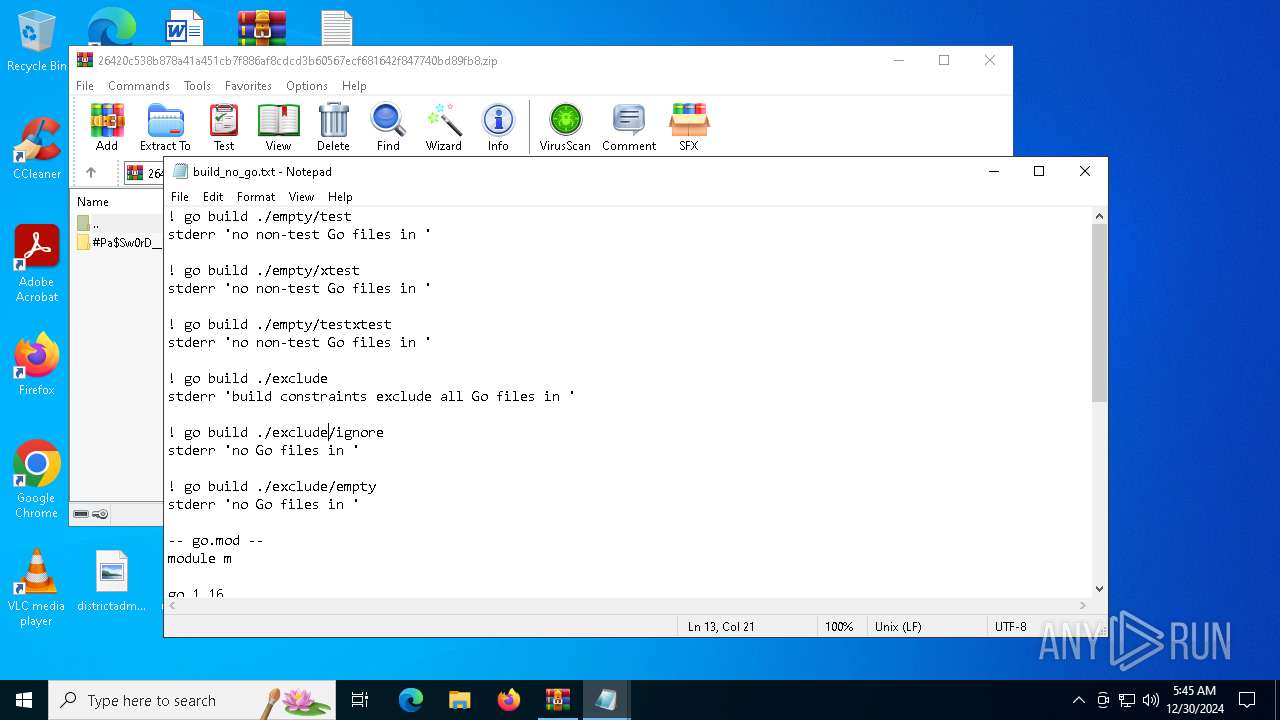
- WinRAR.exe (PID: 5432)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 5432)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5432)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 5432)
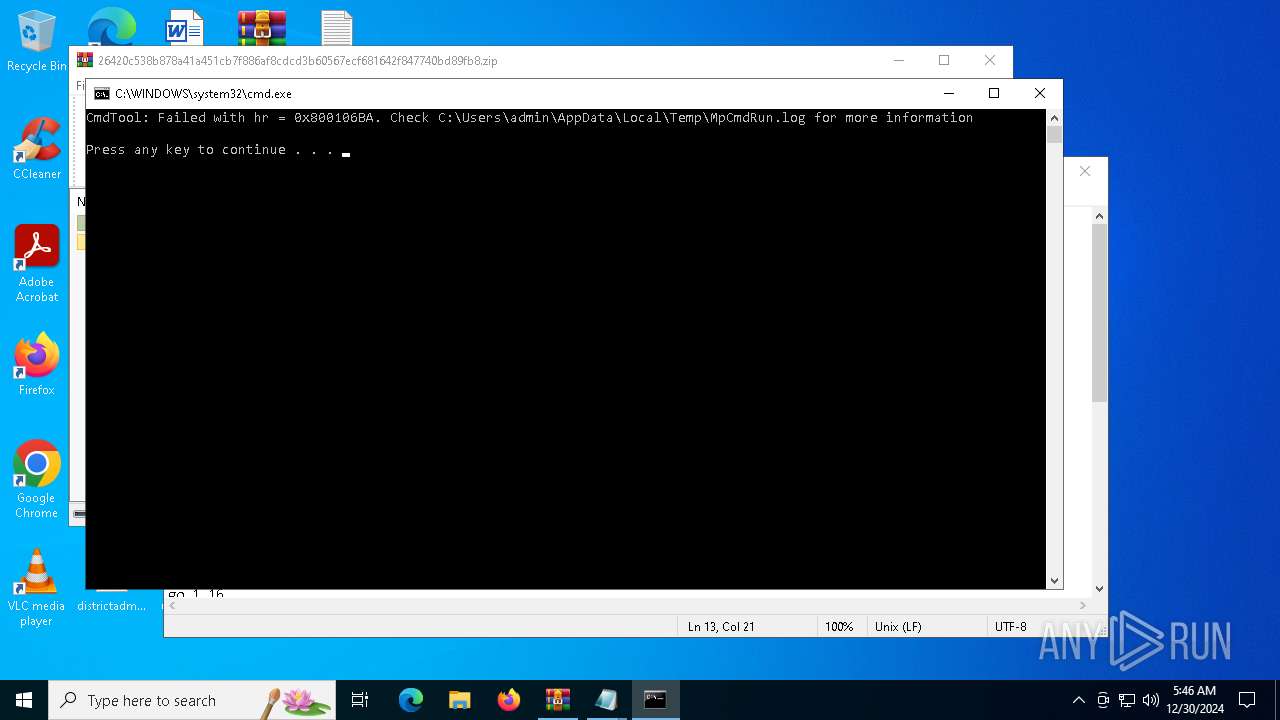
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 5432)
Executing commands from a ".bat" file
- WinRAR.exe (PID: 5432)
INFO
Reads security settings of Internet Explorer
- notepad.exe (PID: 1520)
- notepad.exe (PID: 2408)
- notepad.exe (PID: 1744)
- notepad.exe (PID: 3700)
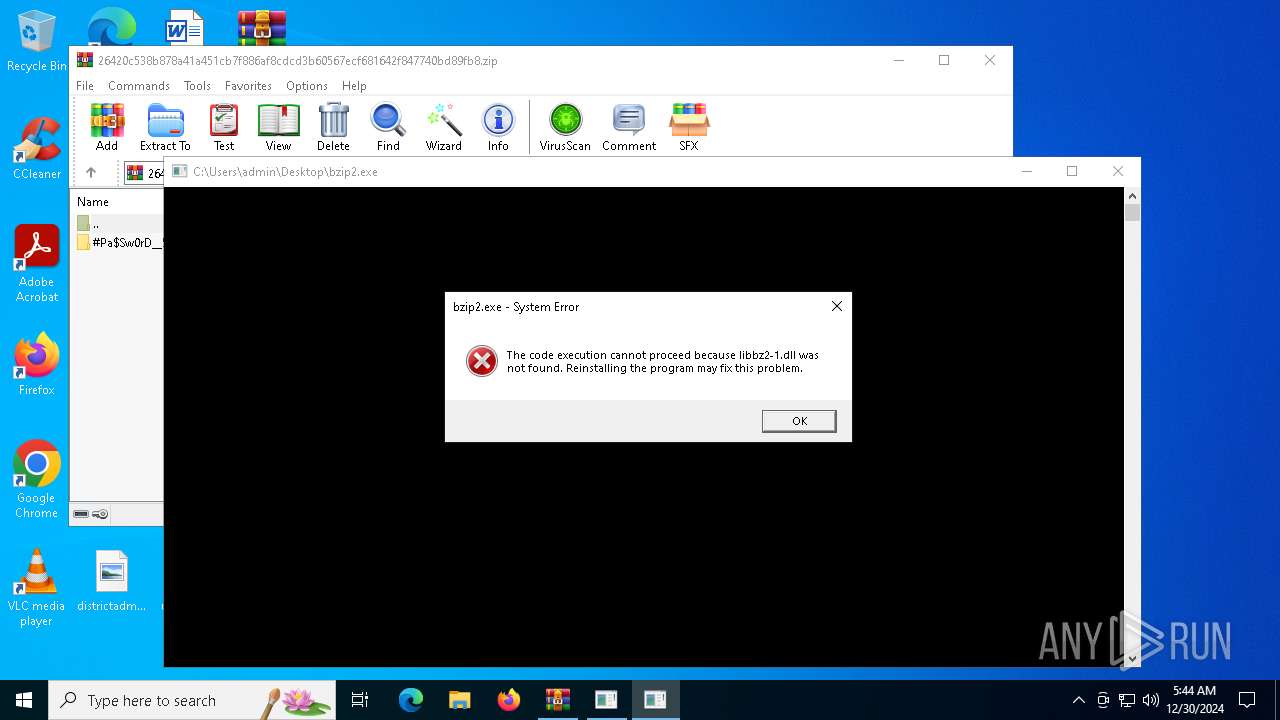
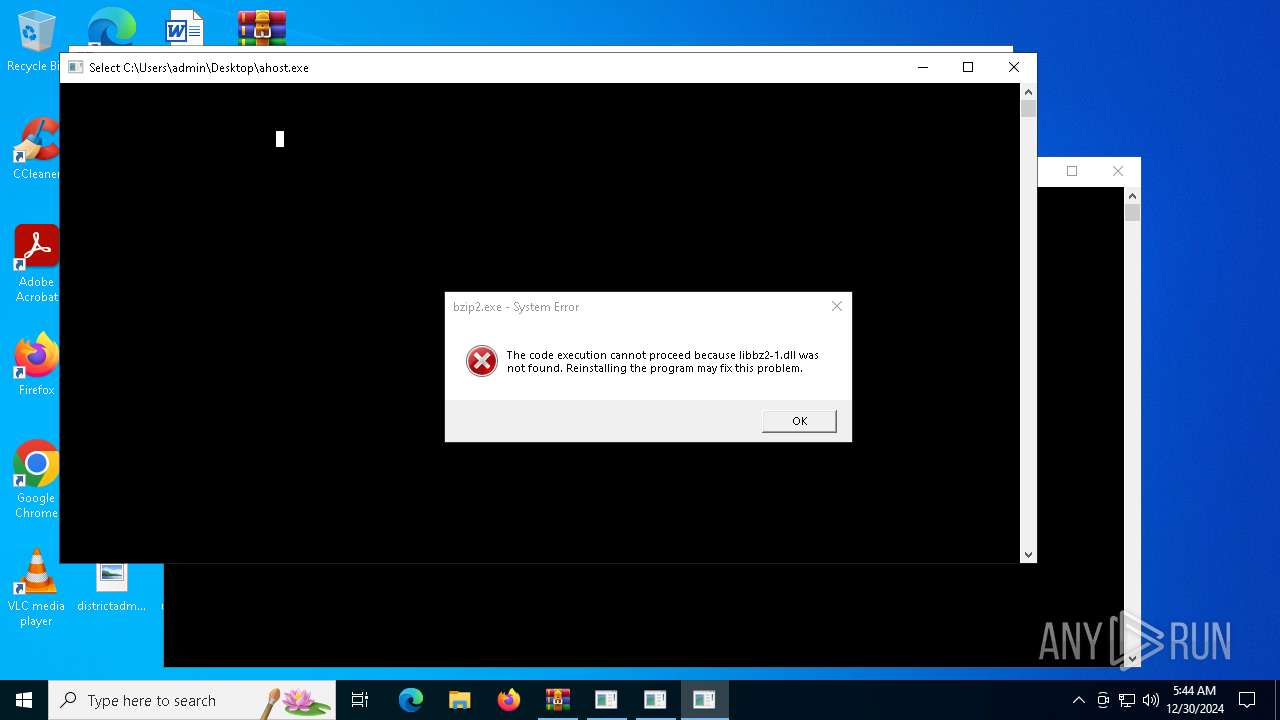
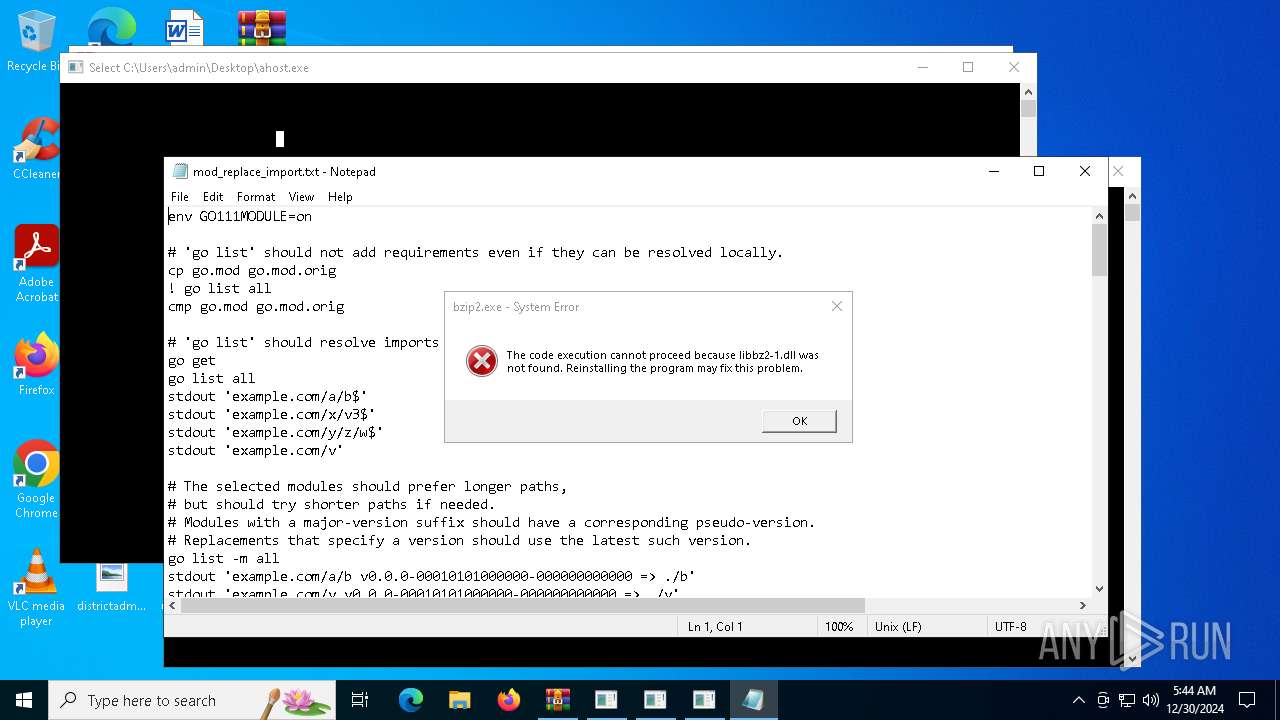
Manual execution by a user
- notepad.exe (PID: 1520)
- notepad.exe (PID: 1744)
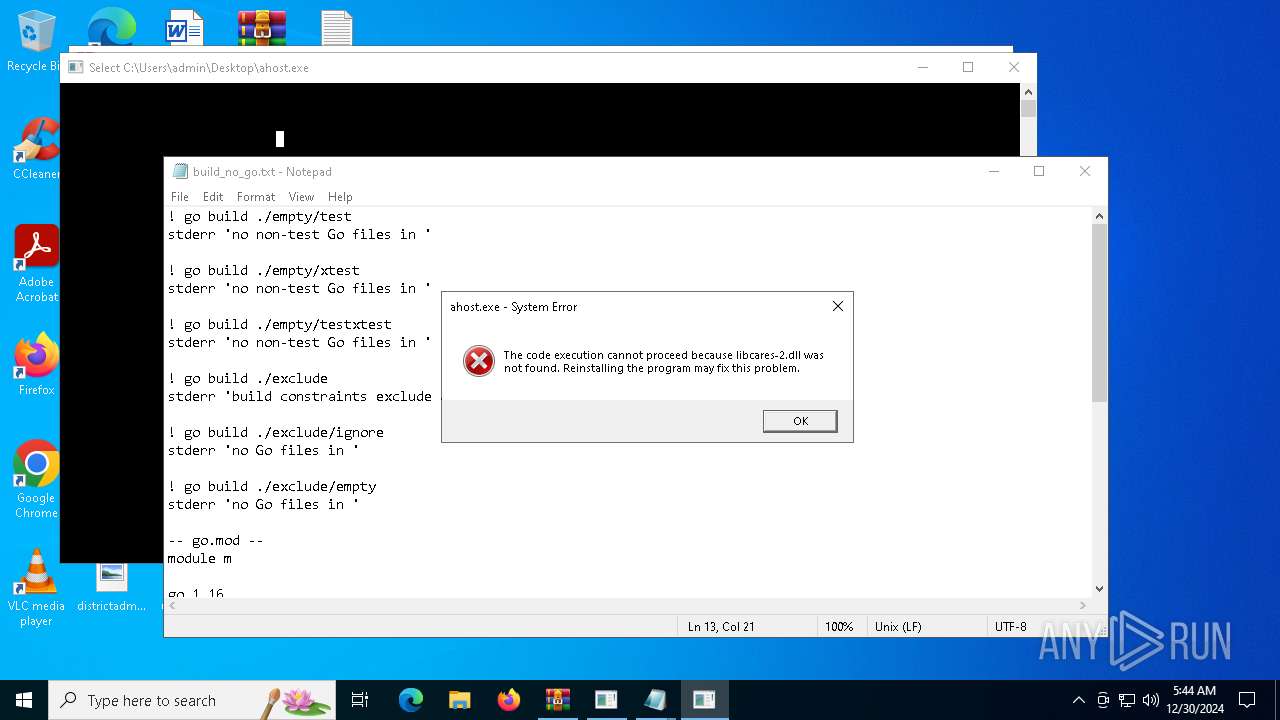
- ahost.exe (PID: 5032)
- notepad.exe (PID: 3700)
- bzip2.exe (PID: 3876)
- connect.exe (PID: 4428)
- notepad.exe (PID: 2408)
Checks supported languages
- connect.exe (PID: 4428)
- MpCmdRun.exe (PID: 4388)
Reads the computer name
- connect.exe (PID: 4428)
- MpCmdRun.exe (PID: 4388)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5432)
The sample compiled with english language support
- WinRAR.exe (PID: 5432)
The process uses the downloaded file
- WinRAR.exe (PID: 5432)
Create files in a temporary directory
- MpCmdRun.exe (PID: 4388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
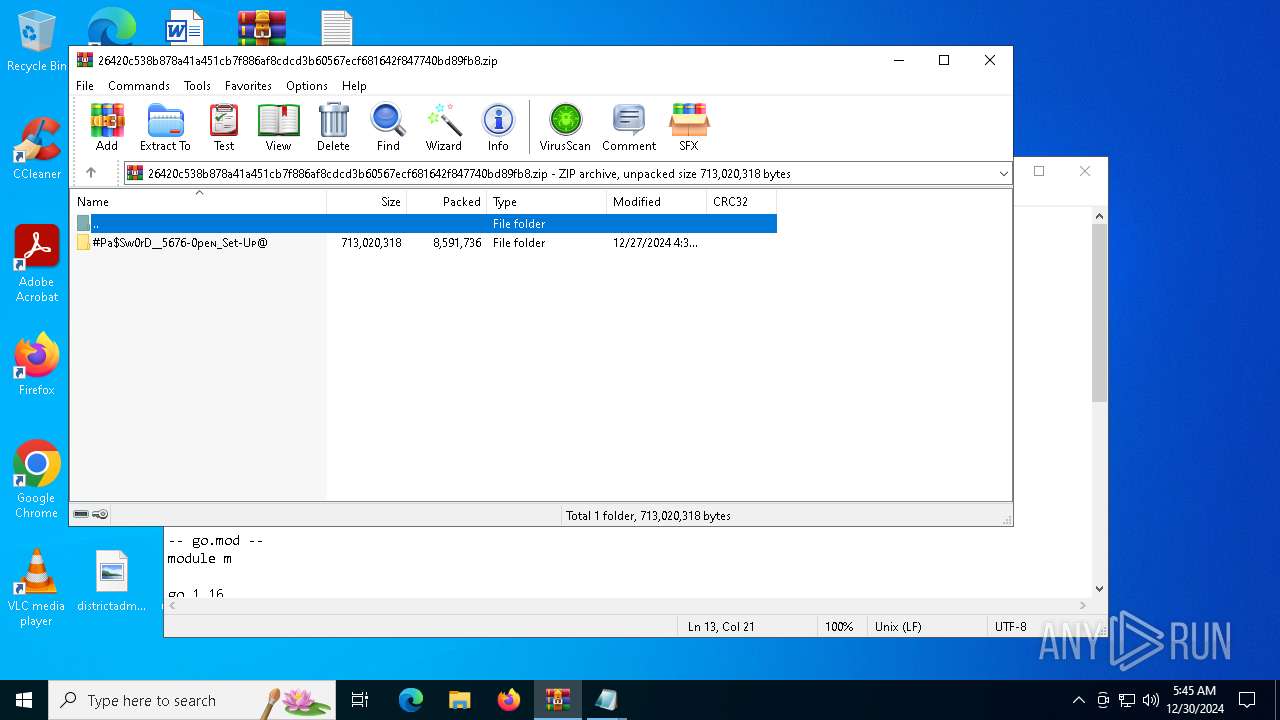
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0800 |
| ZipCompression: | None |
| ZipModifyDate: | 2024:12:27 17:39:30 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | #Pa$Sw0rD__5676-0peɴ_Set-Uᴘ@/ |
Total processes
134
Monitored processes
14
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
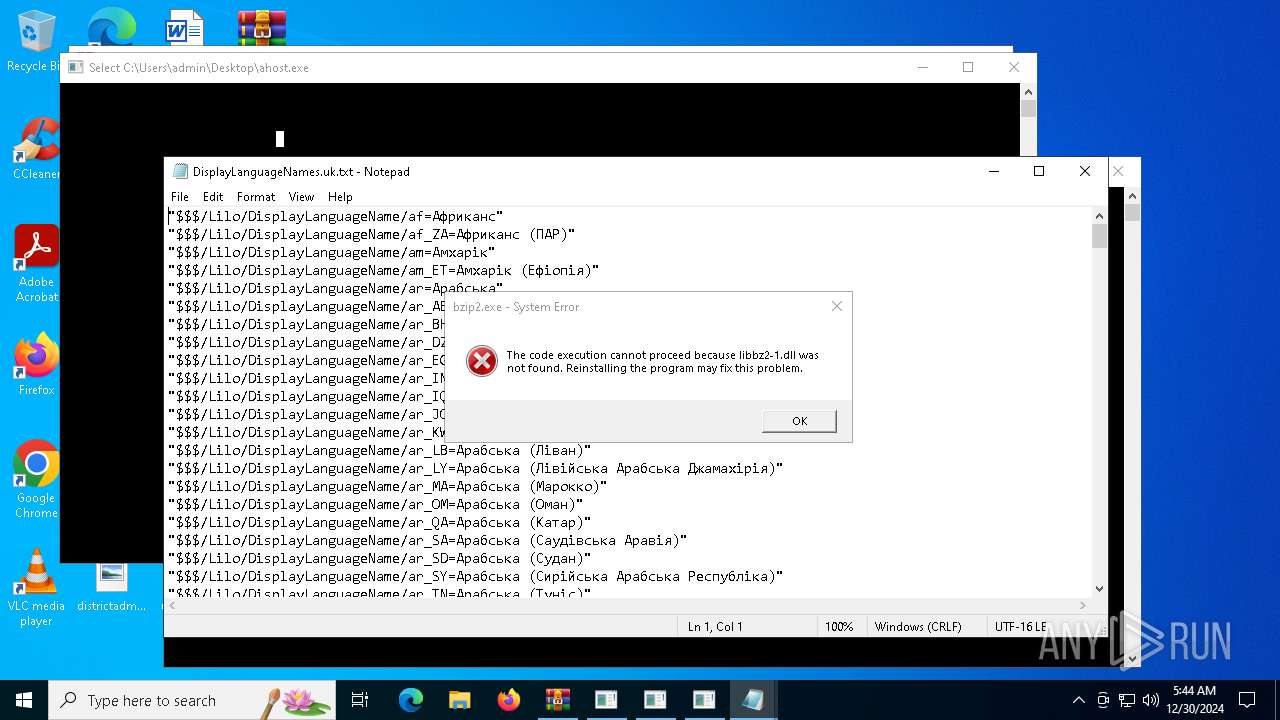
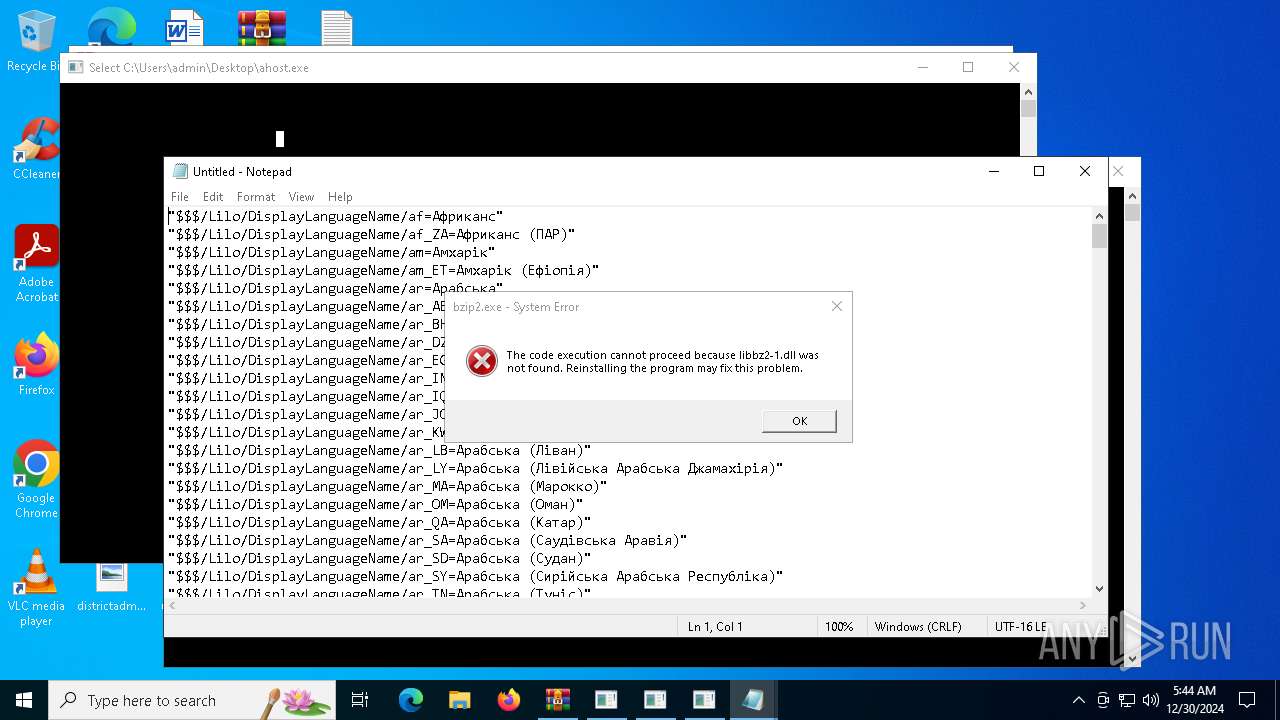
| 1520 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\DisplayLanguageNames.uk.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
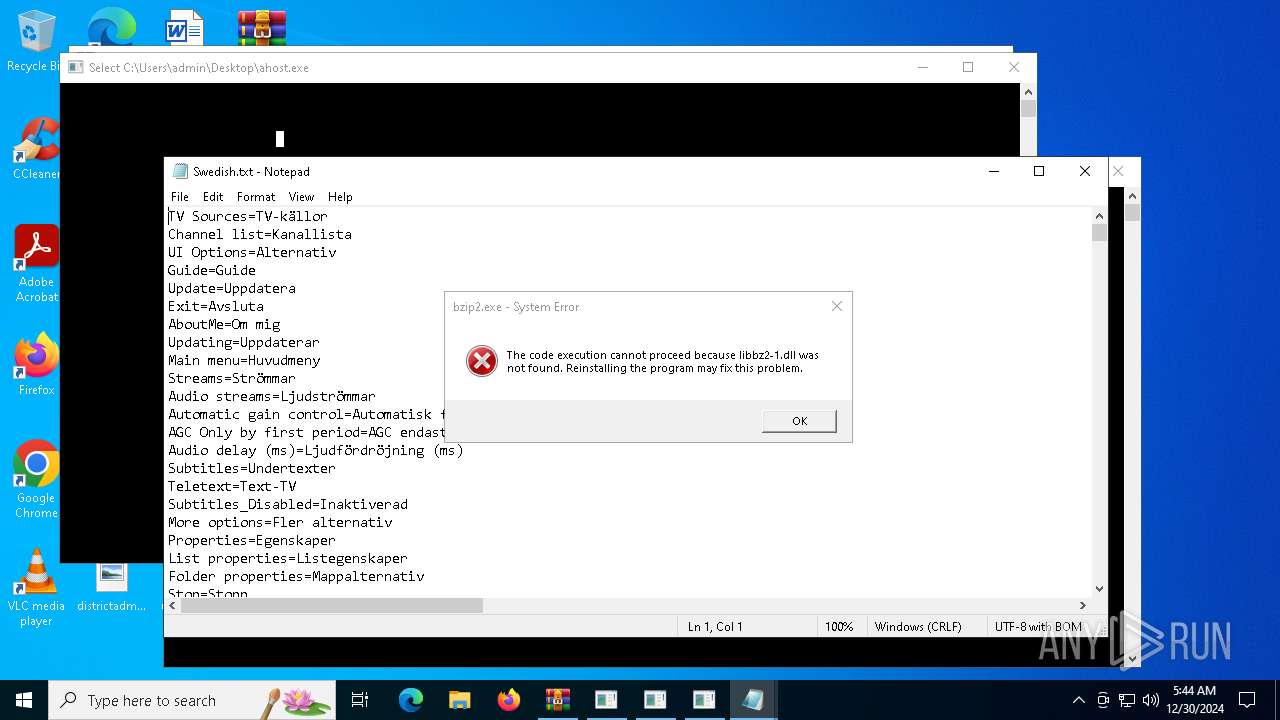
| 1744 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Swedish.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | connect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
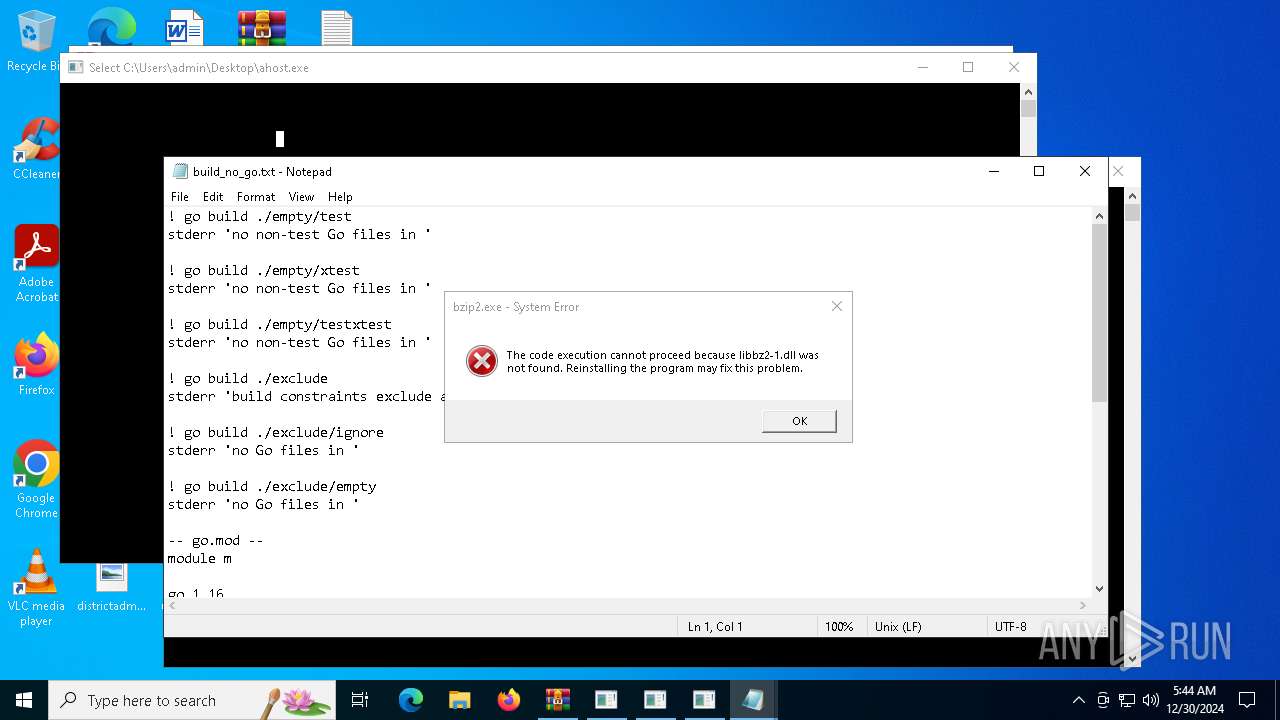
| 2408 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\build_no_go.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3488 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$VR5432.39966\Rar$Scan112679.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3700 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\mod_replace_import.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3876 | "C:\Users\admin\Desktop\bzip2.exe" | C:\Users\admin\Desktop\bzip2.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225781 Modules
| |||||||||||||||
| 4120 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | bzip2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
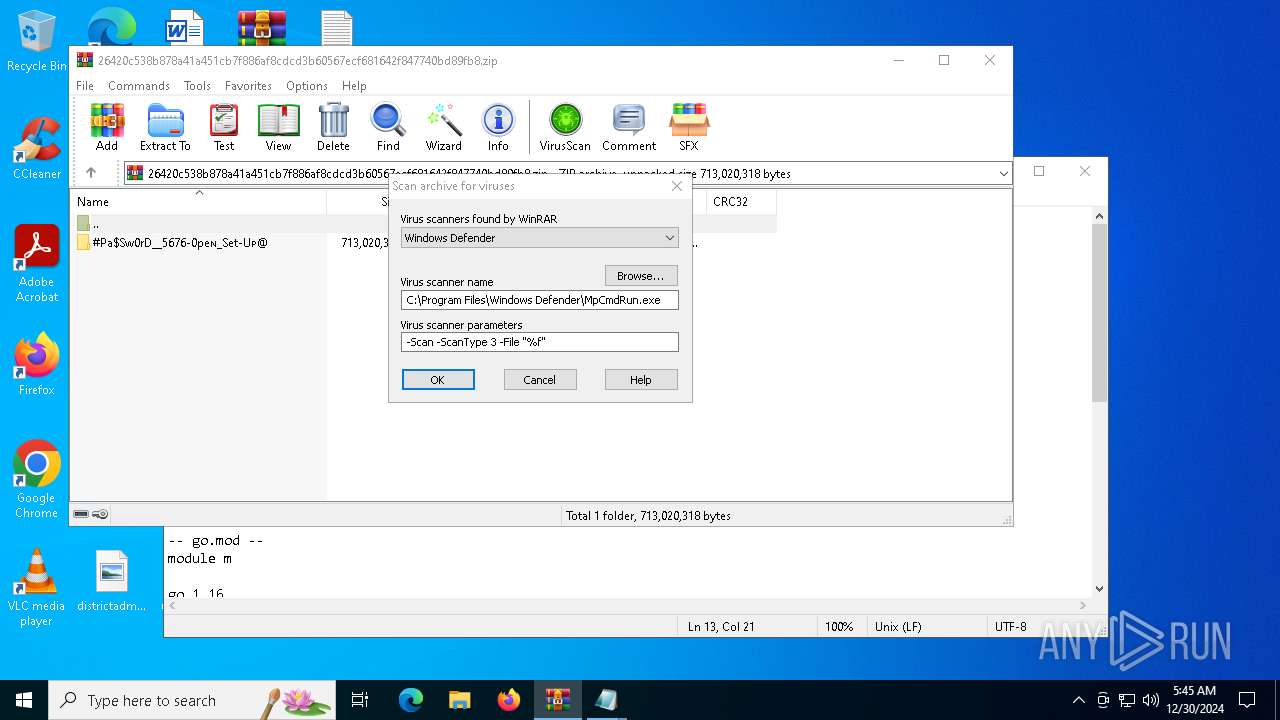
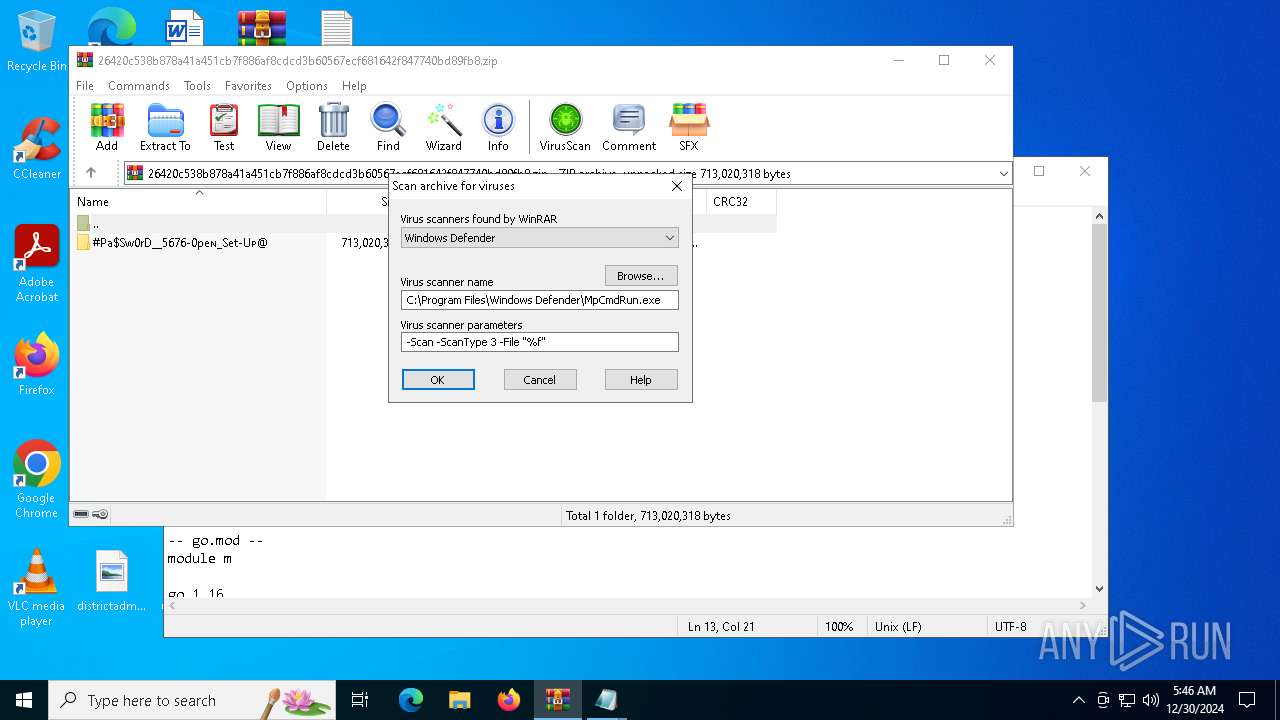
| 4388 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR5432.39966" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4428 | "C:\Users\admin\Desktop\connect.exe" | C:\Users\admin\Desktop\connect.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 423
Read events
2 413
Write events
10
Delete events
0
Modification events
| (PID) Process: | (5432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\26420c538b878a41a451cb7f886af8cdcd3b60567ecf681642f847740bd89fb8.zip | |||
| (PID) Process: | (5432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\VirusScan |
| Operation: | write | Name: | DefScanner |
Value: Windows Defender | |||
Executable files
22
Suspicious files
4
Text files
88
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR5432.33413\26420c538b878a41a451cb7f886af8cdcd3b60567ecf681642f847740bd89fb8.zip\#Pa$Sw0rD__5676-0peɴ_Set-Uᴘ@\Config\ga.txt | text | |
MD5:B4295E254B9DFC90E0093188257C007C | SHA256:406669ECBDF562E773B9CDF831CF5F63C3DD1A012C3521A41227C9141511D959 | |||
| 5432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR5432.33413\26420c538b878a41a451cb7f886af8cdcd3b60567ecf681642f847740bd89fb8.zip\#Pa$Sw0rD__5676-0peɴ_Set-Uᴘ@\Config\mod_list.txt | text | |
MD5:A651545EBAC407934B9C4CC1EE5D62D8 | SHA256:D3FDE0FC938D802398B694F84F6AE5EA340C37D6889C14B5BBDBC84C79419020 | |||
| 5432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR5432.33413\26420c538b878a41a451cb7f886af8cdcd3b60567ecf681642f847740bd89fb8.zip\#Pa$Sw0rD__5676-0peɴ_Set-Uᴘ@\Config\DisplayLanguageNames.fa.txt | text | |
MD5:59A00623B4B640EFCFBB205563B2A27A | SHA256:977CE09D594A79582B30B71DCF558E1CF3C5CE28C8813E3D2A1B524D6F76B7DF | |||
| 5432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR5432.33413\26420c538b878a41a451cb7f886af8cdcd3b60567ecf681642f847740bd89fb8.zip\#Pa$Sw0rD__5676-0peɴ_Set-Uᴘ@\Config\build_no_go.txt | text | |
MD5:4423738EA11C32298E0DF0E160DFCB6F | SHA256:99C037FEA2E972065B6ADD7BAE526491B91F41A765257876A09D0FA3F075D1CA | |||
| 5432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR5432.33413\26420c538b878a41a451cb7f886af8cdcd3b60567ecf681642f847740bd89fb8.zip\#Pa$Sw0rD__5676-0peɴ_Set-Uᴘ@\Config\DisplayLanguageNames.ja_JP.txt | text | |
MD5:468293226B9E51736BE5FD18A7A428E5 | SHA256:A3E756356ACA1A07A49B90B6B546D6C56AB8D7B1D1595C70F00A0DA2AA5CBC01 | |||
| 5432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR5432.33413\26420c538b878a41a451cb7f886af8cdcd3b60567ecf681642f847740bd89fb8.zip\#Pa$Sw0rD__5676-0peɴ_Set-Uᴘ@\Config\cy.txt | text | |
MD5:0F5662A68805D859F871EDC07E766A57 | SHA256:931DE741A6C8F1348A946623776FE36C55DD2FC384C7B1478225F7467853199E | |||
| 5432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR5432.33413\26420c538b878a41a451cb7f886af8cdcd3b60567ecf681642f847740bd89fb8.zip\#Pa$Sw0rD__5676-0peɴ_Set-Uᴘ@\Config\fold.txt | text | |
MD5:EC70D9AC95E4D0C8ECFC859D46E2EB3C | SHA256:16F84C45C630CE3071A164AA46FD2DC09B2F9CCD992072C8660FC2F737F8780F | |||
| 5432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR5432.33413\26420c538b878a41a451cb7f886af8cdcd3b60567ecf681642f847740bd89fb8.zip\#Pa$Sw0rD__5676-0peɴ_Set-Uᴘ@\Config\DisplayLanguageNames.uk.txt | text | |
MD5:524C44CB3B0E0F4C9B402D27C4042B8C | SHA256:55C9F811369A94794266ABE3CA4078732F506463D0E6FA115C6CF7FF6898B798 | |||
| 5432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR5432.33413\26420c538b878a41a451cb7f886af8cdcd3b60567ecf681642f847740bd89fb8.zip\#Pa$Sw0rD__5676-0peɴ_Set-Uᴘ@\Config\mod_replace_import.txt | text | |
MD5:75167CD6A35994124A0E4F1CB24F02E4 | SHA256:C9458651F018744E56046D1EB053CFA2A22F223AB9764B163DBF247A934387BD | |||
| 5432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR5432.33413\26420c538b878a41a451cb7f886af8cdcd3b60567ecf681642f847740bd89fb8.zip\#Pa$Sw0rD__5676-0peɴ_Set-Uᴘ@\Config\jvm.hprof.txt | text | |
MD5:C677FF69E70DC36A67C72A3D7EF84D28 | SHA256:B055BF25B07E5AC70E99B897FB8152F288769065B5B84387362BB9CC2E6C9D38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
18
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4516 | RUXIMICS.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 1.01 Kb | whitelisted |
712 | svchost.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 1.01 Kb | whitelisted |
4516 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
712 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 1.01 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
4516 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.23.209.149:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
712 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4516 | RUXIMICS.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
712 | svchost.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4516 | RUXIMICS.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |