analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
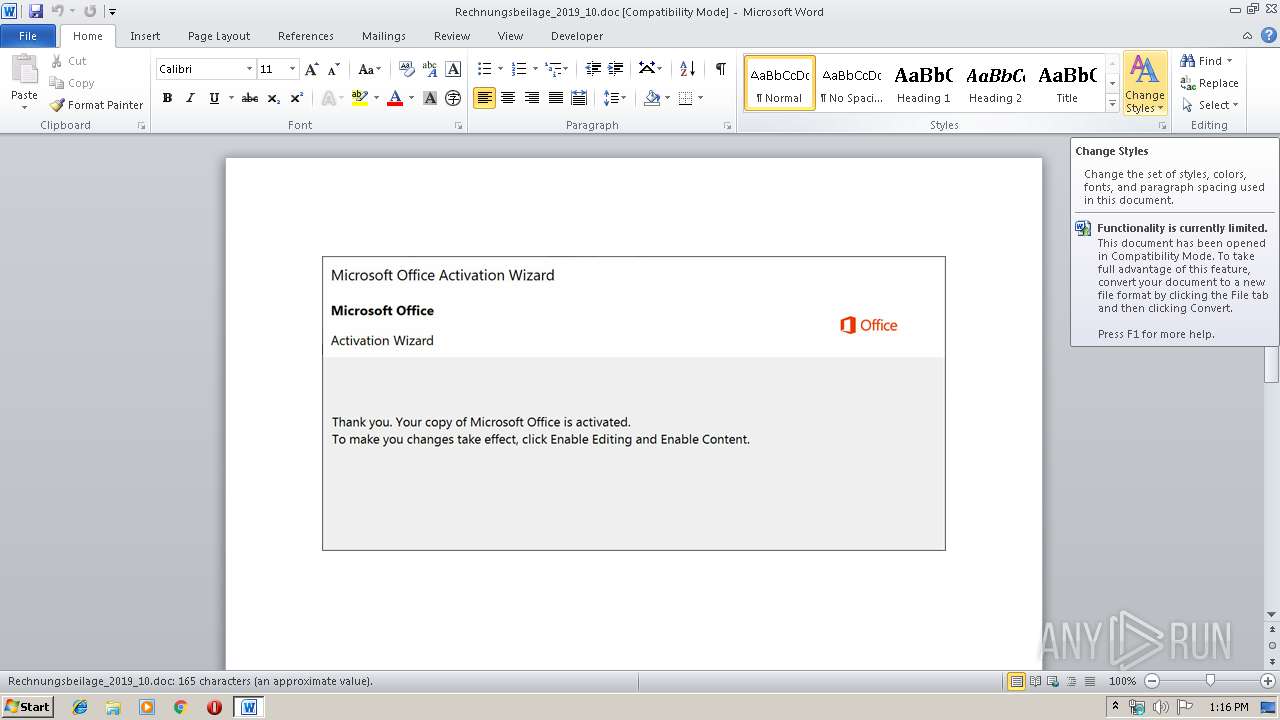
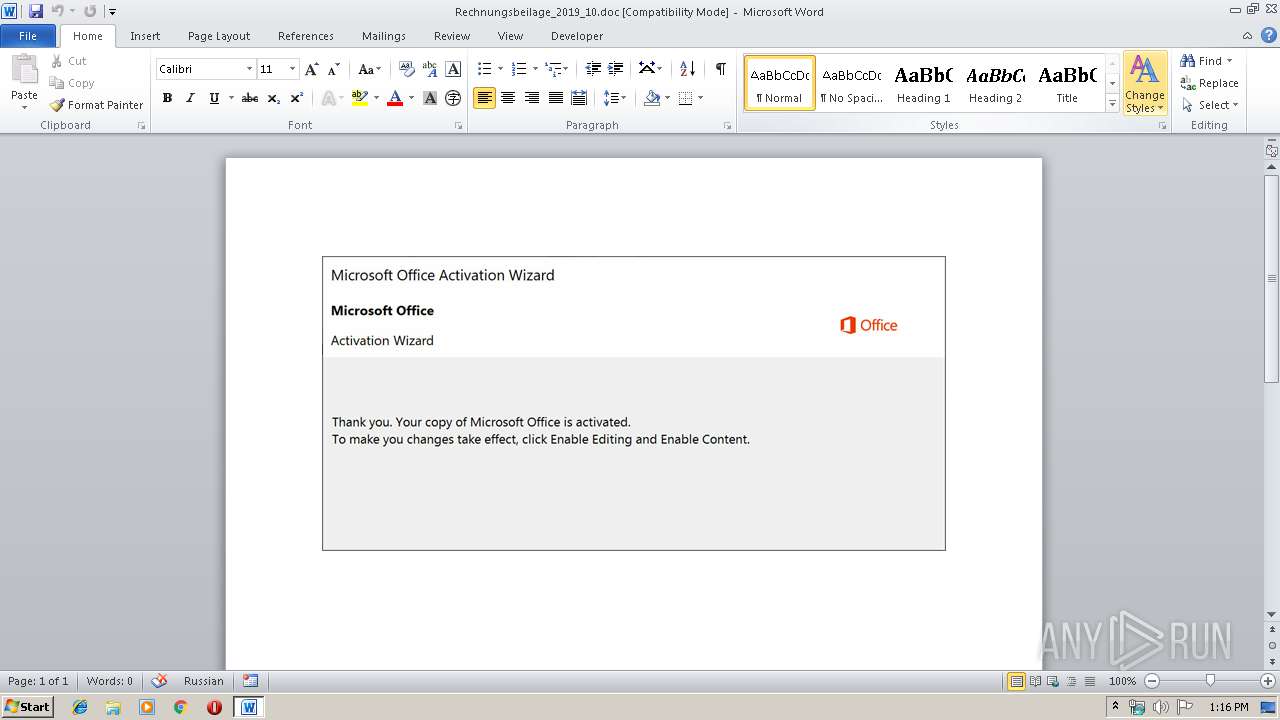
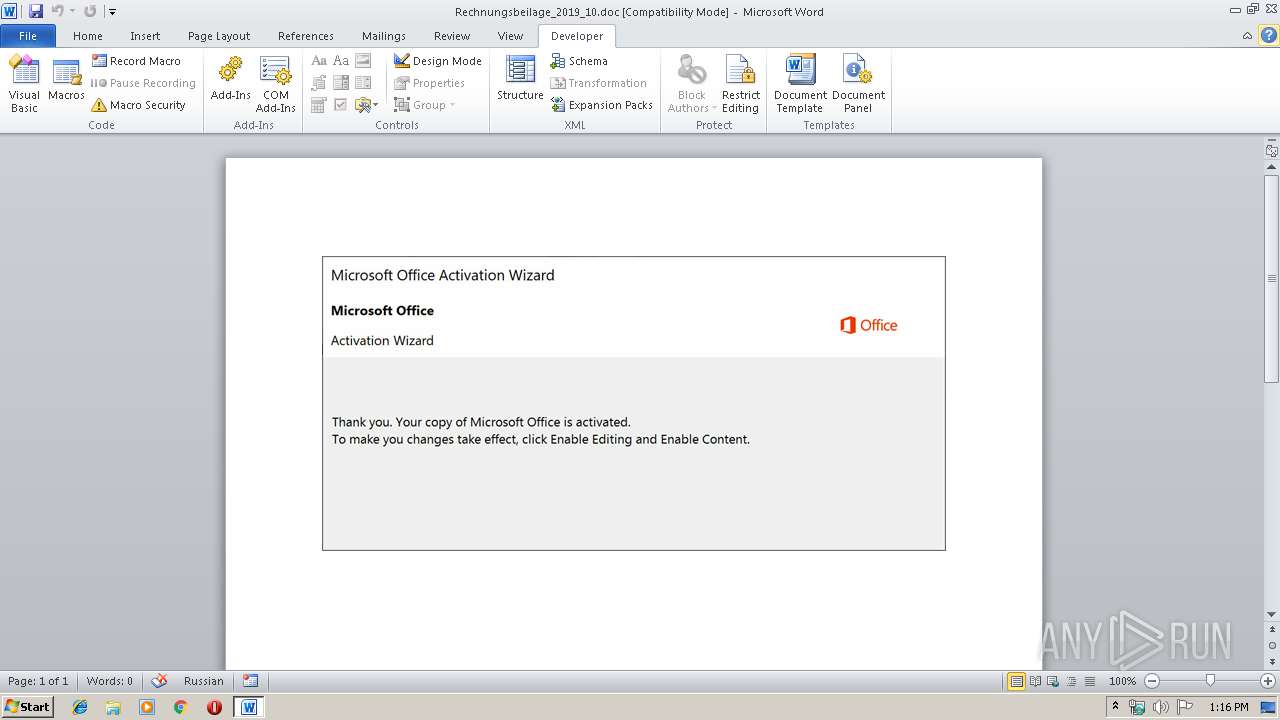
| File name: | Rechnungsbeilage_2019_10.doc |
| Full analysis: | https://app.any.run/tasks/581cb8a4-7ad8-4141-b24c-1fc8f465ba9c |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 14, 2019, 12:15:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Licensed, Subject: Sleek, Author: Alivia Heaney, Keywords: Generic Concrete Gloves, Comments: Legacy, Template: Normal.dotm, Last Saved By: Sharon Kulas, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Oct 14 09:04:00 2019, Last Saved Time/Date: Mon Oct 14 09:04:00 2019, Number of Pages: 1, Number of Words: 30, Number of Characters: 171, Security: 0 |
| MD5: | BF6386482CFDA4C2CF49A9977AD4DE8E |
| SHA1: | 96E23E01340130A30B26D2D02D62543672B1CD1D |
| SHA256: | 263DD7396F687A1E78663B389367D98D48C7C996B3364C7F9A9989057DEC8765 |
| SSDEEP: | 1536:1aHde0oPOXrkKPubsYwKjtrzu5rGImRoHynvwMMITLxQOXxrt:1aHde0oWQKgdzSrGtKyIwLx3B |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
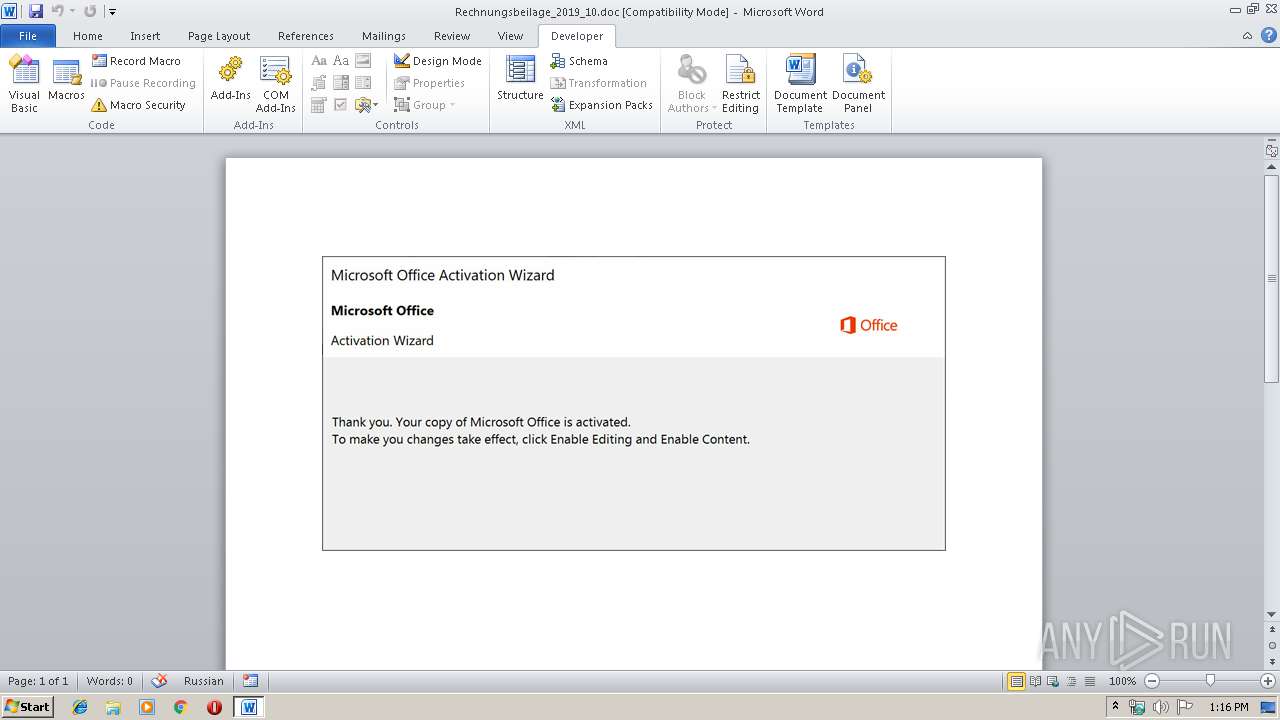
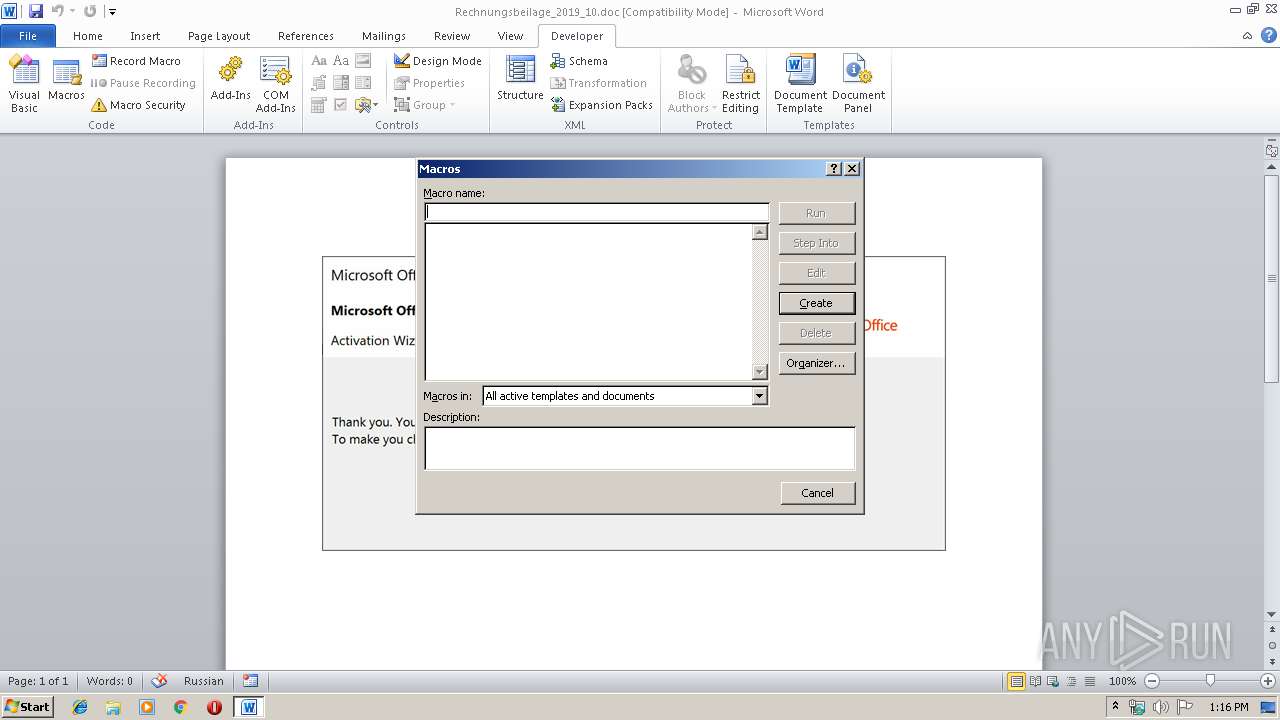
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2132)
Creates files in the user directory
- WINWORD.EXE (PID: 2132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Licensed |
|---|---|
| Subject: | Sleek |
| Author: | Alivia Heaney |
| Keywords: | Generic Concrete Gloves |
| Comments: | Legacy |
| Template: | Normal.dotm |
| LastModifiedBy: | Sharon Kulas |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:10:14 08:04:00 |
| ModifyDate: | 2019:10:14 08:04:00 |
| Pages: | 1 |
| Words: | 30 |
| Characters: | 171 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Baumbach, Beahan and Robel |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 200 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Flatley |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
35
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2132 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rechnungsbeilage_2019_10.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 14.0.6024.1000 | ||||
Total events
1 734
Read events
948
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA87F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:032137C277DE1C872AA06B62213ACCC1 | SHA256:7E00F1AC2624CEA6291D38D3F5F94762B2AC9FDEC4ECDF56B1015B495B1FEC98 | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6CDF0FDA.wmf | wmf | |
MD5:269079719C29E1BEEAAE23DF44F86236 | SHA256:729951FF4665499157AB0FC60A0D18CE0A3A1065E71CE53C63693337EFCE3D51 | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$chnungsbeilage_2019_10.doc | pgc | |
MD5:146141B8379763031E5E398273A38863 | SHA256:02DA1159E2870F57D84474A60214442E2CF33D9AB46F9E84813A4FBAD46259E7 | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:C01B83F834E36ADAC1677F1CC2484D3A | SHA256:84DD366110FEA4355323532A4AA5736FE971DD34B3270494BDA0E7A80C0578BD | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CCCF42D7.wmf | wmf | |
MD5:CE43F1FAC623BBC22C924624C31BF65B | SHA256:244A3D4B24DDA0A0FAEC64647C2197C7384FA976E4BD883BF50A993D8E94E8FE | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A9B7FEAE.wmf | wmf | |
MD5:06F116F5289FD8609C33FE3C057CBA17 | SHA256:E07460B58A057DF5A4A8313B940635273EAB0E568AB542A2769DD59706977F13 | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\82270EEC.wmf | wmf | |
MD5:23C61EFF2C9537B396A529B3B0C12121 | SHA256:A7F360740F97CB1F5181E5CBF3A41FBC3CD747057EF126E57EC843DCA0FB4877 | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\57827321.wmf | wmf | |
MD5:2C97E10BF3282BAA098DDF1D46269321 | SHA256:9CC1ED822001BF61339B8899DE78EFE0076A6838028754FB172BF97110211EB2 | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A0F9C9FD.wmf | wmf | |
MD5:3D85CB8DB19F871BFAB7D2E13347CBB7 | SHA256:E757A558435B96E8A65C4299276A3EB8CF323152BA1DA6A2A9B836CDE01218DE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report