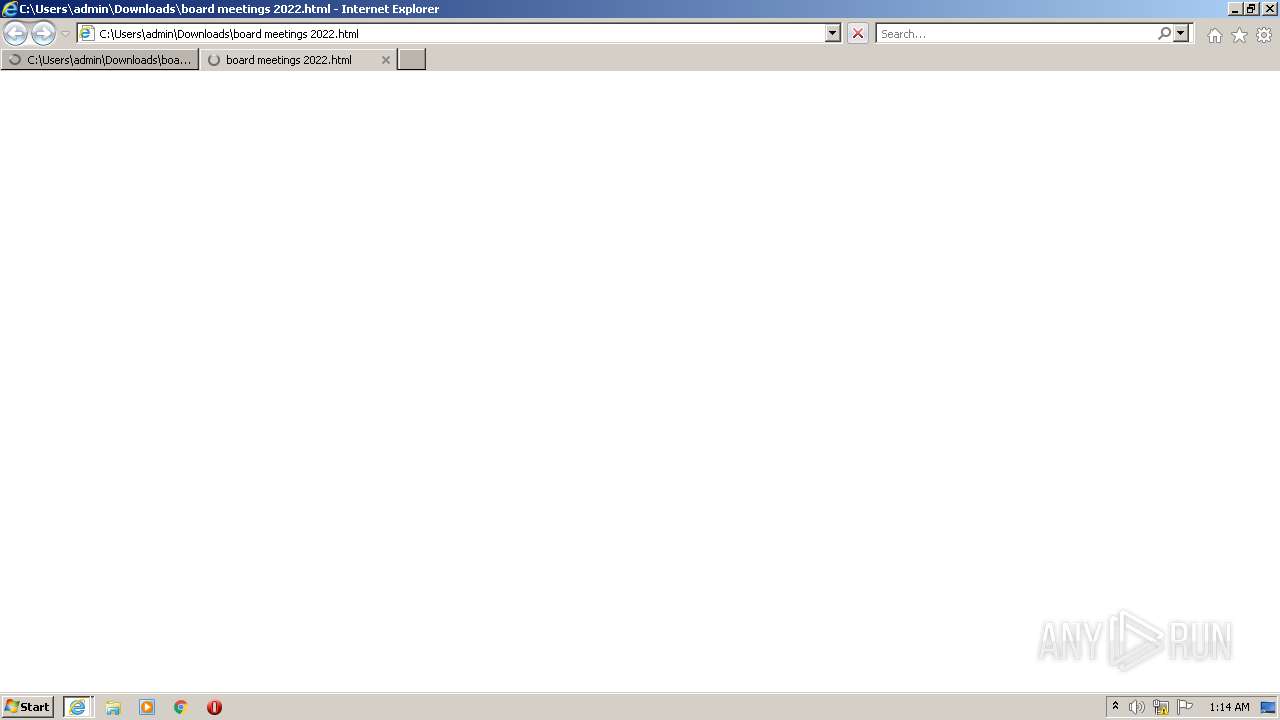
| File name: | board meetings 2022.html |
| Full analysis: | https://app.any.run/tasks/e9e6e069-252b-49d8-8a02-dfb0e7dc80e7 |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 00:14:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 5FF12FF23EF7BBA560CFCC23AF1413A7 |
| SHA1: | 595ED9A9F004645BC2A674D82E08946F50B2F6BC |
| SHA256: | 2624D36AD2145B3FDF5028D316BAD52C07AB0766C96EC0D28764A083C8EADCA4 |
| SSDEEP: | 192:SVg9j7T+tovVZ0nUMeYF1zB+D3oH5Ulddl6QfuesGHX1HKKL0ORBst/JtiepCmm0:SosoL0fe28cyY8YIX1ZL08gjGEL |
MALICIOUS
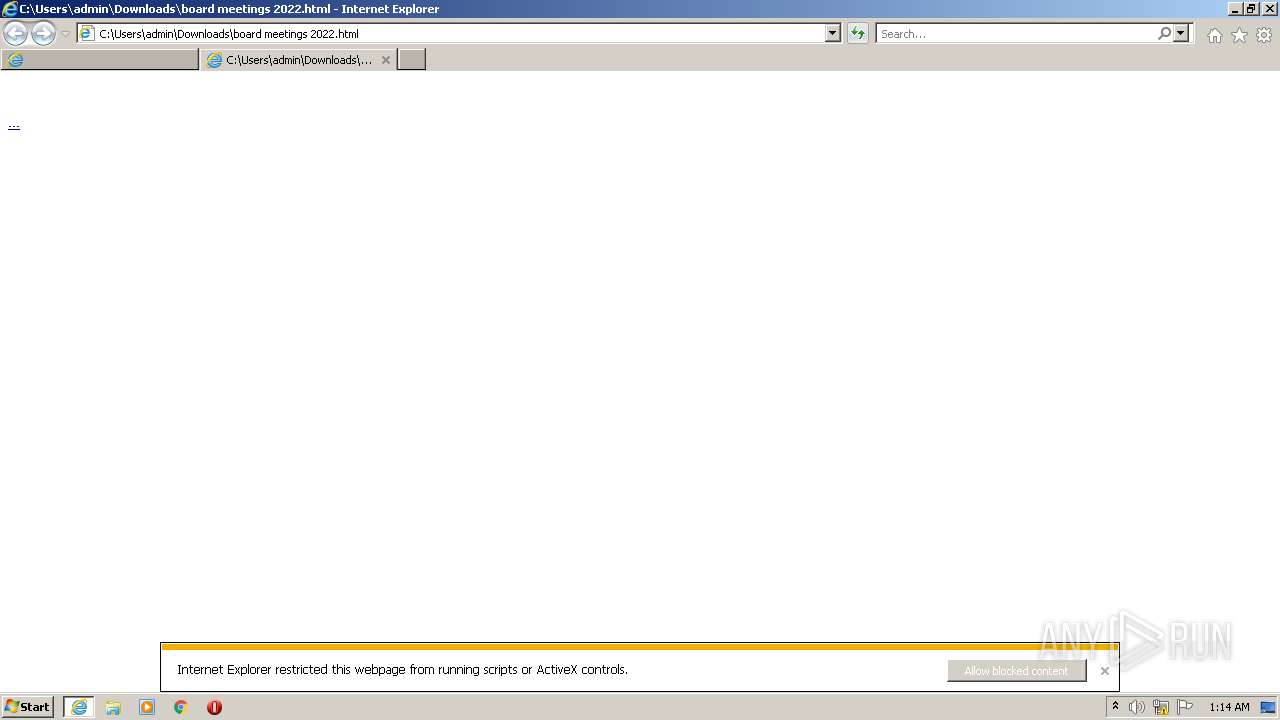
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3124)
- iexplore.exe (PID: 1572)
- iexplore.exe (PID: 780)
INFO
Checks supported languages
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 3124)
- iexplore.exe (PID: 1572)
- iexplore.exe (PID: 780)
Changes internet zones settings
- iexplore.exe (PID: 2956)
Reads the computer name
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 1572)
- iexplore.exe (PID: 3124)
- iexplore.exe (PID: 780)
Checks Windows Trust Settings
- iexplore.exe (PID: 3124)
- iexplore.exe (PID: 1572)
- iexplore.exe (PID: 780)
- iexplore.exe (PID: 2956)
Reads internet explorer settings
- iexplore.exe (PID: 3124)
- iexplore.exe (PID: 1572)
- iexplore.exe (PID: 780)
Application launched itself
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 3124)
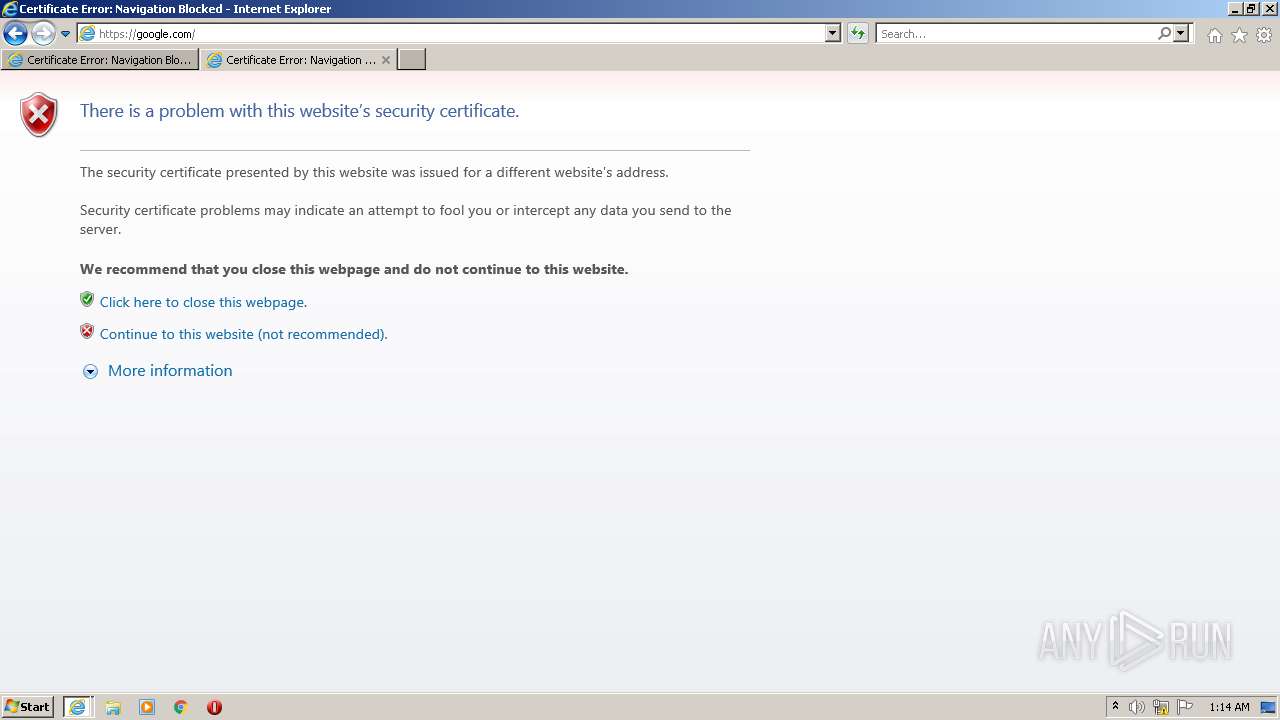
Reads settings of System Certificates
- iexplore.exe (PID: 1572)
- iexplore.exe (PID: 3124)
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
38
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 780 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2956 CREDAT:398593 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1572 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2956 CREDAT:144390 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2956 | "C:\Program Files\Internet Explorer\iexplore.exe" "C:\Users\admin\Downloads\board meetings 2022.html" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3124 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2956 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
34 844
Read events
34 606
Write events
237
Delete events
1
Modification events
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30988367 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30988367 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2956 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF993B3540A3A87DA2.TMP | atn | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF435B5C47F9C9A96A.TMP | atn | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{A004FC4F-4442-11ED-9A81-1203334A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{A004FC50-4442-11ED-9A81-1203334A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
43
DNS requests
15
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3124 | iexplore.exe | GET | 404 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?077684f90ea5cfbc | US | xml | 341 b | whitelisted |
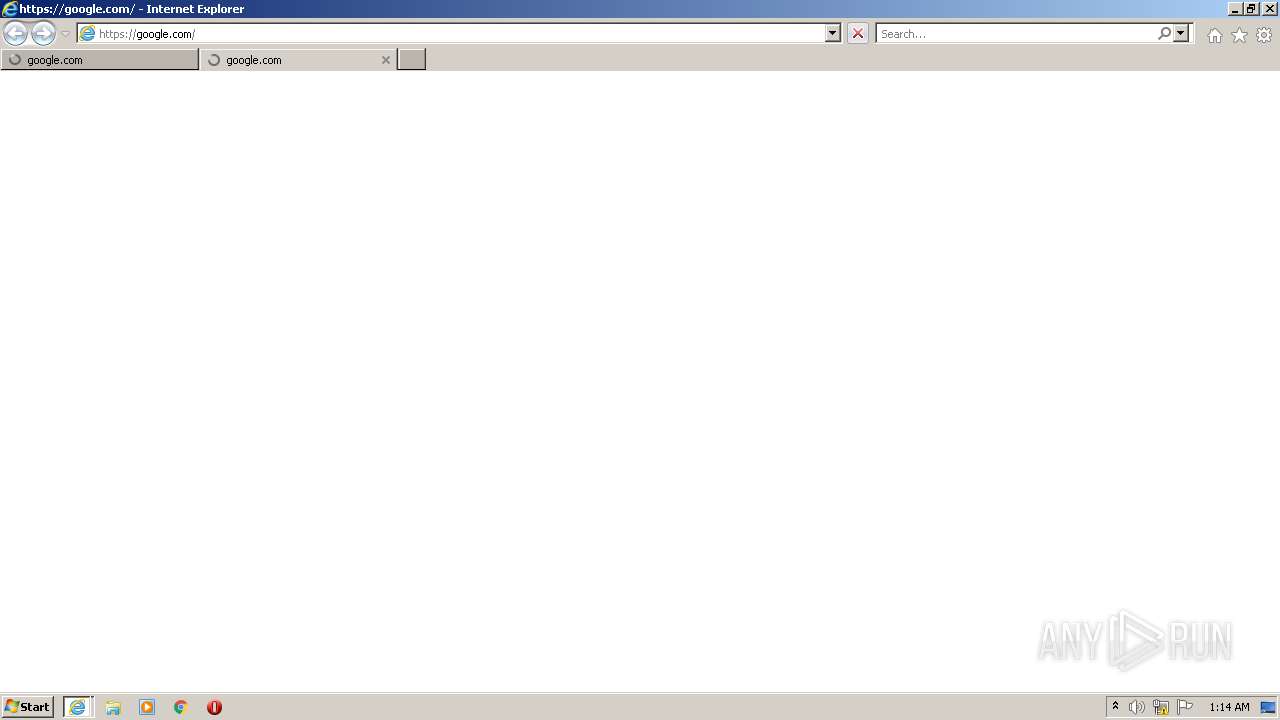
3124 | iexplore.exe | GET | 404 | 185.199.109.153:80 | http://makemeproud.github.io/jquery/convergence.css | NL | xml | 341 b | malicious |
3124 | iexplore.exe | GET | 404 | 185.199.109.153:80 | http://makemeproud.github.io/jquery/jquery_unbase.js | NL | xml | 341 b | malicious |
1572 | iexplore.exe | GET | 404 | 185.199.109.153:80 | http://makemeproud.github.io/jquery/convergence.css | NL | xml | 341 b | malicious |
1572 | iexplore.exe | GET | 404 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2a875695884195ad | US | xml | 341 b | whitelisted |
2956 | iexplore.exe | GET | 404 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8cdeeba6e468ea55 | US | xml | 341 b | whitelisted |
2956 | iexplore.exe | GET | 404 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ecd0fbd79a008311 | US | xml | 341 b | whitelisted |
2956 | iexplore.exe | GET | 404 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fed7e272b276c497 | US | xml | 341 b | whitelisted |
3124 | iexplore.exe | GET | 404 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9d36c2aa74afa64f | US | xml | 341 b | whitelisted |
1572 | iexplore.exe | GET | 404 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?eee096c3cd273048 | US | xml | 341 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3124 | iexplore.exe | 185.199.109.153:80 | makemeproud.github.io | FASTLY | US | shared |
3124 | iexplore.exe | 142.250.185.161:443 | lh3.googleusercontent.com | GOOGLE | US | whitelisted |
3124 | iexplore.exe | 142.250.185.74:443 | ajax.googleapis.com | GOOGLE | US | whitelisted |
1572 | iexplore.exe | 142.250.185.161:443 | lh3.googleusercontent.com | GOOGLE | US | whitelisted |
3124 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
1572 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
2956 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
400 | svchost.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
2956 | iexplore.exe | 184.31.86.154:443 | go.microsoft.com | AKAMAI-AS | DE | malicious |
2956 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
makemeproud.github.io |
| malicious |
lh3.googleusercontent.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
google.com |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
Threats
21 ETPRO signatures available at the full report