analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
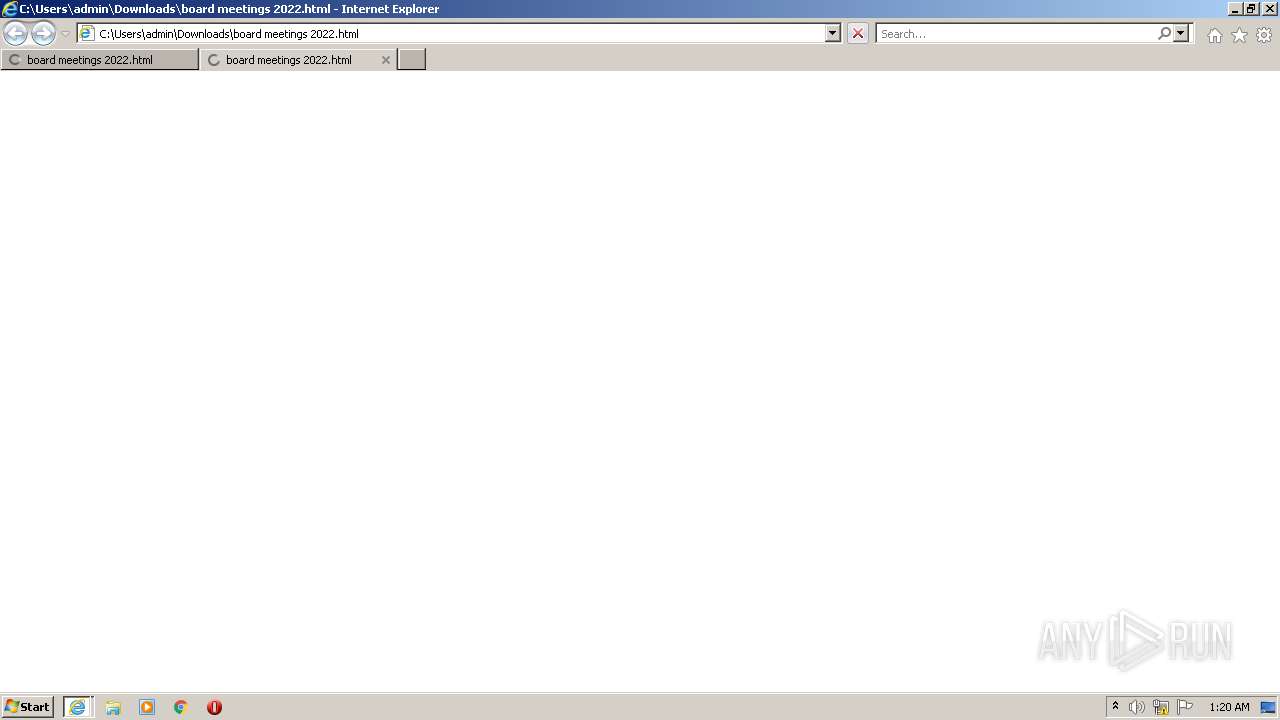
| File name: | board meetings 2022.html |
| Full analysis: | https://app.any.run/tasks/1f1fb882-8ad0-4f25-8483-f8941246e72b |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 00:20:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 5FF12FF23EF7BBA560CFCC23AF1413A7 |
| SHA1: | 595ED9A9F004645BC2A674D82E08946F50B2F6BC |
| SHA256: | 2624D36AD2145B3FDF5028D316BAD52C07AB0766C96EC0D28764A083C8EADCA4 |
| SSDEEP: | 192:SVg9j7T+tovVZ0nUMeYF1zB+D3oH5Ulddl6QfuesGHX1HKKL0ORBst/JtiepCmm0:SosoL0fe28cyY8YIX1ZL08gjGEL |
MALICIOUS
No malicious indicators.SUSPICIOUS
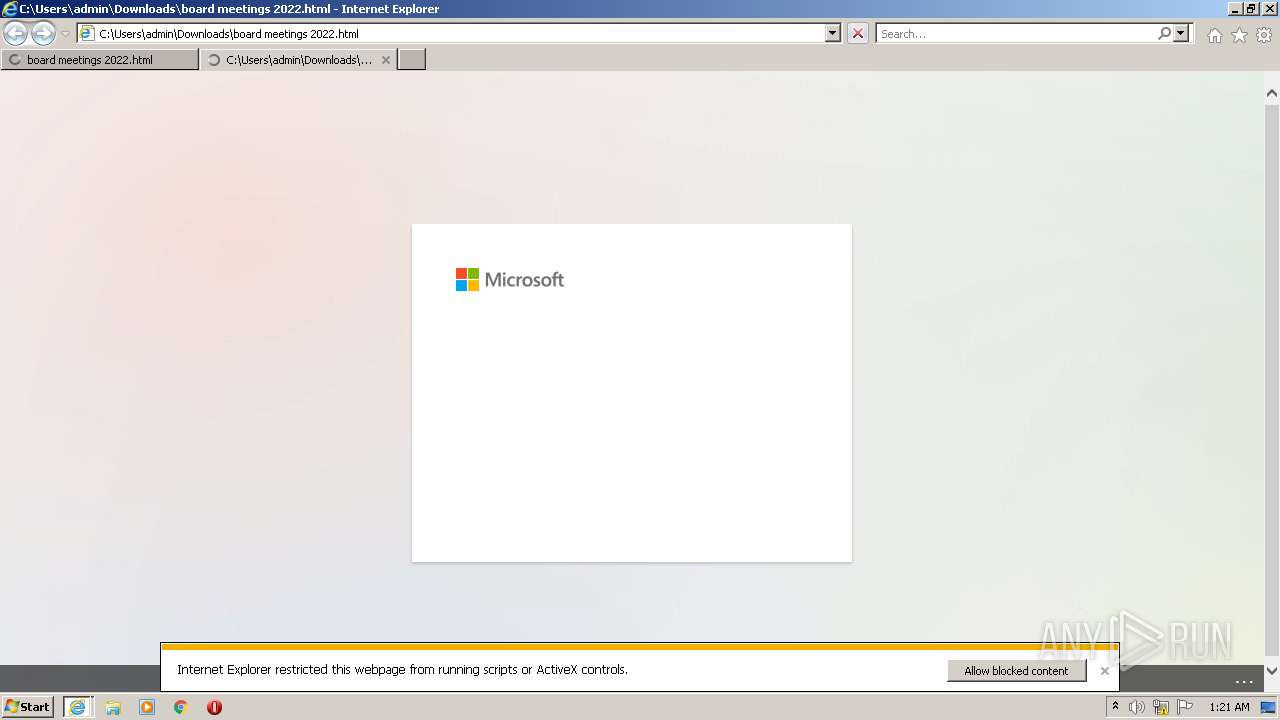
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3636)
- iexplore.exe (PID: 1964)
- iexplore.exe (PID: 432)
- iexplore.exe (PID: 3488)
INFO
Reads the computer name
- iexplore.exe (PID: 1144)
- iexplore.exe (PID: 3636)
- iexplore.exe (PID: 1964)
- iexplore.exe (PID: 3488)
- iexplore.exe (PID: 432)
Checks supported languages
- iexplore.exe (PID: 3636)
- iexplore.exe (PID: 1144)
- iexplore.exe (PID: 1964)
- iexplore.exe (PID: 3488)
- iexplore.exe (PID: 432)
Application launched itself
- iexplore.exe (PID: 1144)
- iexplore.exe (PID: 1964)
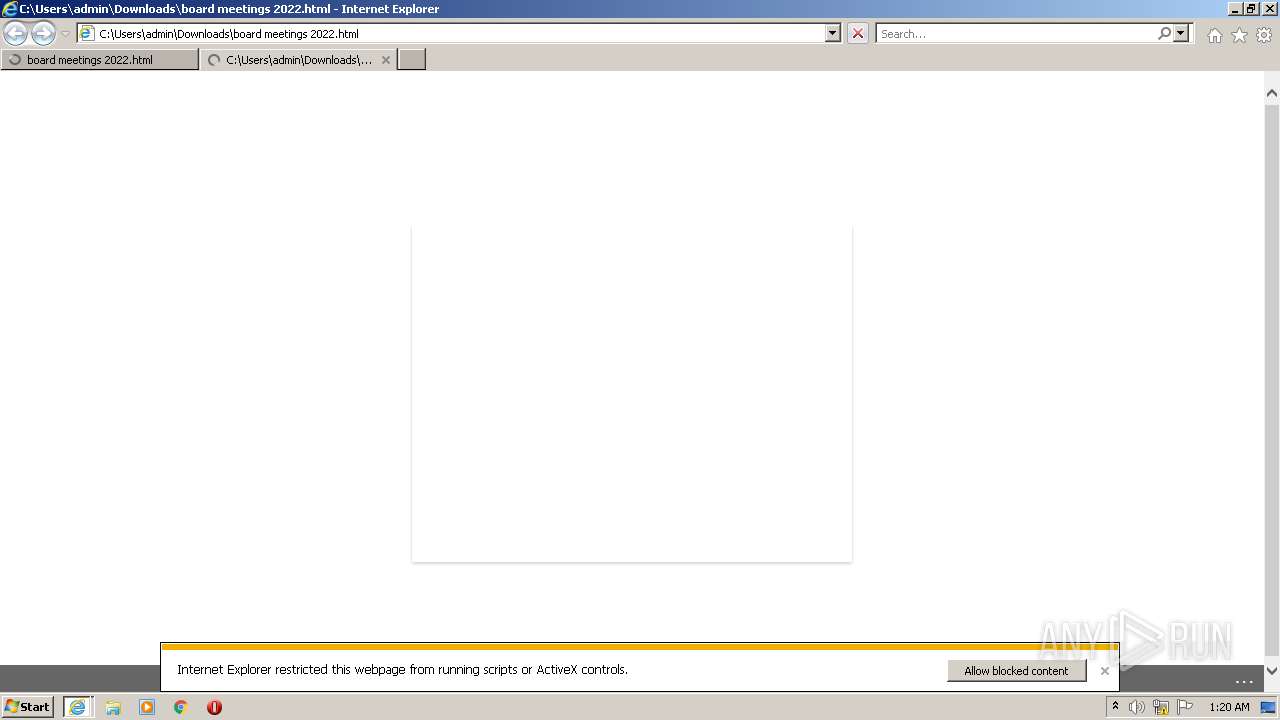
Changes internet zones settings
- iexplore.exe (PID: 1144)
Reads internet explorer settings
- iexplore.exe (PID: 3636)
- iexplore.exe (PID: 1964)
- iexplore.exe (PID: 432)
- iexplore.exe (PID: 3488)
Changes settings of System certificates
- iexplore.exe (PID: 3636)
- iexplore.exe (PID: 1964)
- iexplore.exe (PID: 1144)
Reads settings of System Certificates
- iexplore.exe (PID: 3636)
- iexplore.exe (PID: 1964)
- iexplore.exe (PID: 1144)
- iexplore.exe (PID: 432)
- iexplore.exe (PID: 3488)
Checks Windows Trust Settings
- iexplore.exe (PID: 3636)
- iexplore.exe (PID: 1964)
- iexplore.exe (PID: 1144)
- iexplore.exe (PID: 432)
- iexplore.exe (PID: 3488)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3636)
- iexplore.exe (PID: 1964)
- iexplore.exe (PID: 1144)
Creates files in the user directory
- iexplore.exe (PID: 432)
- iexplore.exe (PID: 1144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
39
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1144 | "C:\Program Files\Internet Explorer\iexplore.exe" "C:\Users\admin\Downloads\board meetings 2022.html" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3636 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1144 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1964 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1144 CREDAT:144390 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3488 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1144 CREDAT:398593 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 432 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1144 CREDAT:595201 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
38 670
Read events
38 405
Write events
257
Delete events
8
Modification events
| (PID) Process: | (1144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30988368 | |||
| (PID) Process: | (1144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30988368 | |||
| (PID) Process: | (1144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
16
Text files
33
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F07644E38ED7C9F37D11EEC6D4335E02_D4DDF242A8972F898C0FE0D6EA6919E3 | binary | |
MD5:BE166A90C85DFFE75B02077EF470EFC5 | SHA256:C8B15638DC24C075A3B33C904B86101826B892E9D5CCC1BF0C75CA67EB8BDE5C | |||
| 1964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E87CE99F124623F95572A696C80EFCAF_CD6513E45B8AAEA8DF3E8B0C926693B8 | binary | |
MD5:AAA09CFA9F947BE3A231E488740D6094 | SHA256:1F3599FFBE2D8ADADB6278147810FE5CE46A95EA9BE69DEFD6D726BF987CE8F3 | |||
| 1964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:13D4682EC9966381CB66FED394E04D51 | SHA256:63FBEA98C106045A166DF9D00C89A52F794DD486258011E9C93982ED1FB15D5E | |||
| 1964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:5A11C6099B9E5808DFB08C5C9570C92F | SHA256:91291A5EDC4E10A225D3C23265D236ECC74473D9893BE5BD07E202D95B3FB172 | |||
| 1964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | der | |
MD5:E1817D34D647D15C961327938AA58C4A | SHA256:CA2D2DB19D9A688484F592397EBC22270DC2B6F653C583B8DFDF27CFF24E0E07 | |||
| 1964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F07644E38ED7C9F37D11EEC6D4335E02_D4DDF242A8972F898C0FE0D6EA6919E3 | der | |
MD5:4D6B344F7E5123552495C56971708CEF | SHA256:8092E24C3C24D08FFEBCA3781AF0EC9574604E1AE4BD40D2C21865C3297F44BC | |||
| 1964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:F7983D8FD8DDD6DF665E3E5EB736D1C4 | SHA256:173C1E435668AB7C8E2D30A020D2E63D66979911CDF19E0D50F68E697D2CAFC6 | |||
| 3636 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\jquery_unbase[1].htm | html | |
MD5:4F8E702CC244EC5D4DE32740C0ECBD97 | SHA256:9E17CB15DD75BBBD5DBB984EDA674863C3B10AB72613CF8A39A00C3E11A8492A | |||
| 1964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:263161AC9919D46E343F7ED7EE9C0601 | SHA256:7102B0D776EFF30865FB29EC4066BBE644357024A5D427A931907B464CCBD3F6 | |||
| 1964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\convergence[1].css | text | |
MD5:86CA1EAB49390C5D96B6B6905177FF64 | SHA256:66A32B59F08AA67433CF5C3F9C7A887CAD0CE579D2CEE0B1630B86A2DBF81B89 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
81
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1964 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
1964 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEB%2Fvu3PmotRDEvKn%2FiRyWpo%3D | US | der | 471 b | whitelisted |
1964 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3636 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
1964 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
3636 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ec8be17d2a00e2db | US | compressed | 4.70 Kb | whitelisted |
1144 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
1964 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCgVmpFkizRxRLqxUFbbeRm | US | der | 472 b | whitelisted |
3636 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?963278f1613c0784 | US | compressed | 4.70 Kb | whitelisted |
432 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECY%2B0YL3%2ByMOCtPdrqPffYg%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3636 | iexplore.exe | 172.217.17.106:443 | ajax.googleapis.com | GOOGLE | US | whitelisted |
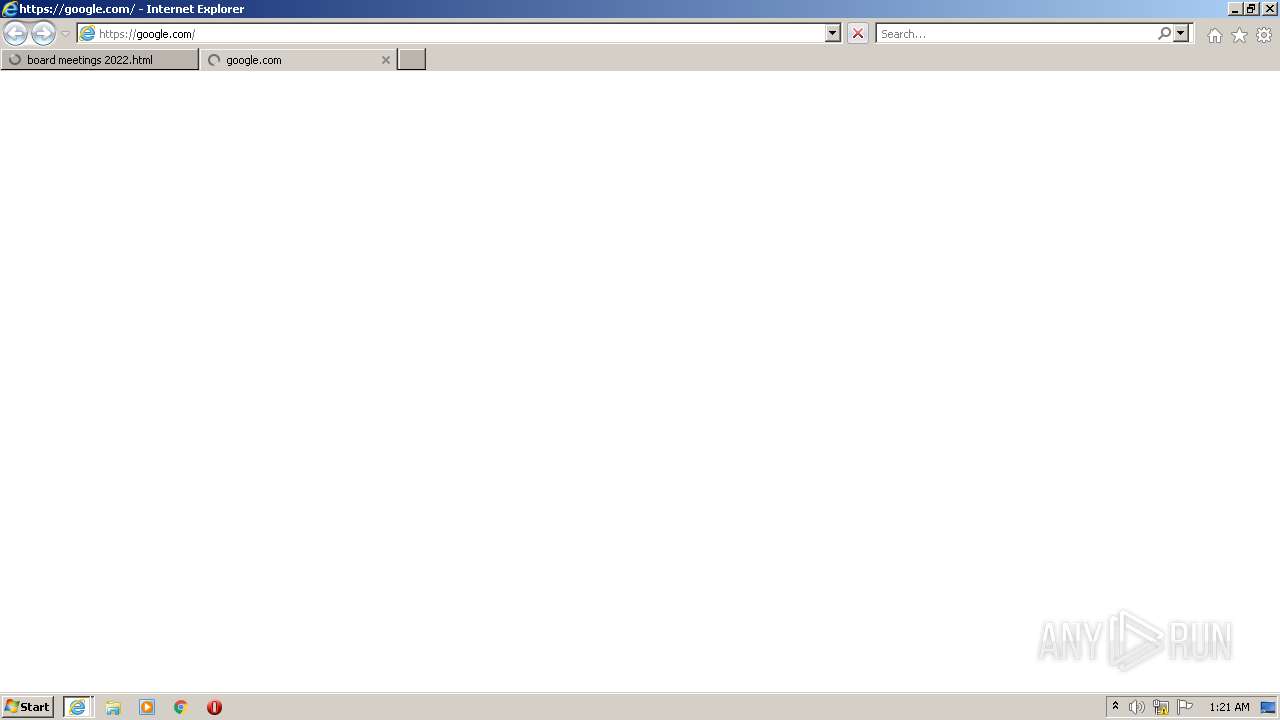
3636 | iexplore.exe | 185.199.108.153:80 | makemeproud.github.io | FASTLY | US | shared |
3636 | iexplore.exe | 142.250.187.161:443 | lh3.googleusercontent.com | GOOGLE | US | whitelisted |
3636 | iexplore.exe | 185.199.108.153:443 | makemeproud.github.io | FASTLY | US | shared |
1964 | iexplore.exe | 172.217.17.106:443 | ajax.googleapis.com | GOOGLE | US | whitelisted |
1964 | iexplore.exe | 185.199.108.153:443 | makemeproud.github.io | FASTLY | US | shared |
1964 | iexplore.exe | 185.199.108.153:80 | makemeproud.github.io | FASTLY | US | shared |
1964 | iexplore.exe | 142.250.187.161:443 | lh3.googleusercontent.com | GOOGLE | US | whitelisted |
3636 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3636 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
makemeproud.github.io |
| malicious |
lh3.googleusercontent.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
www.google.com |
| whitelisted |