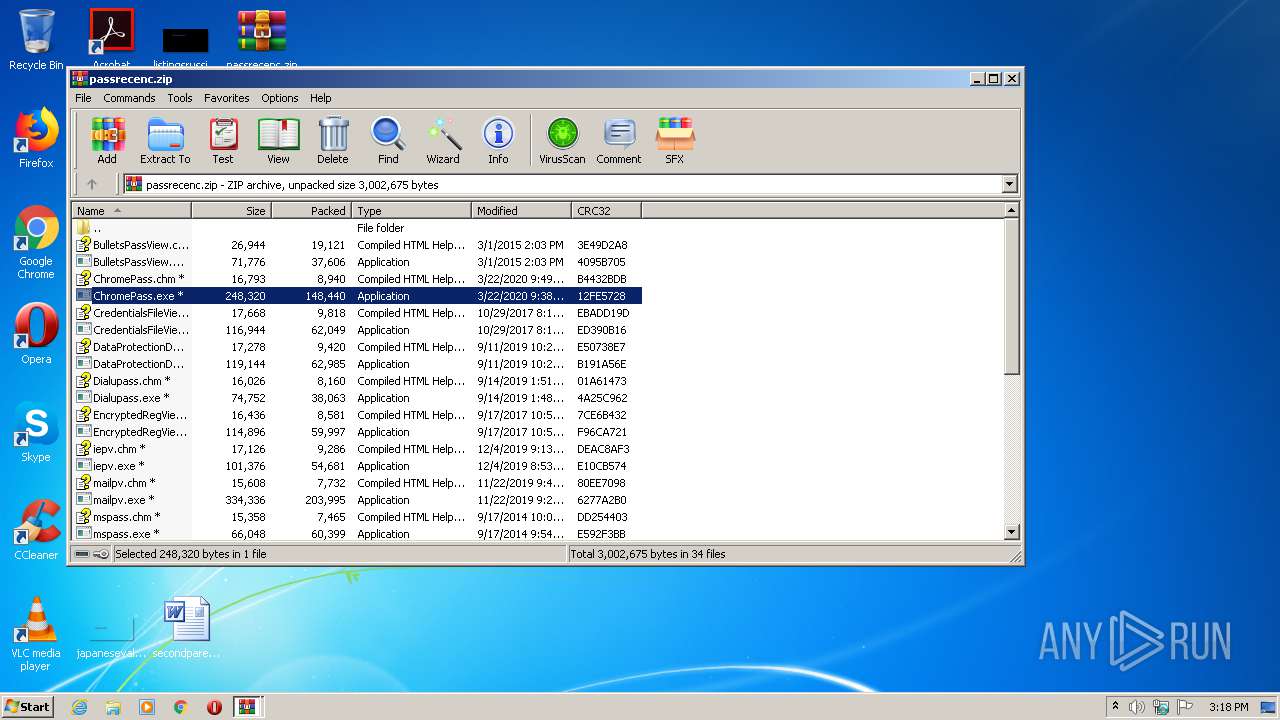
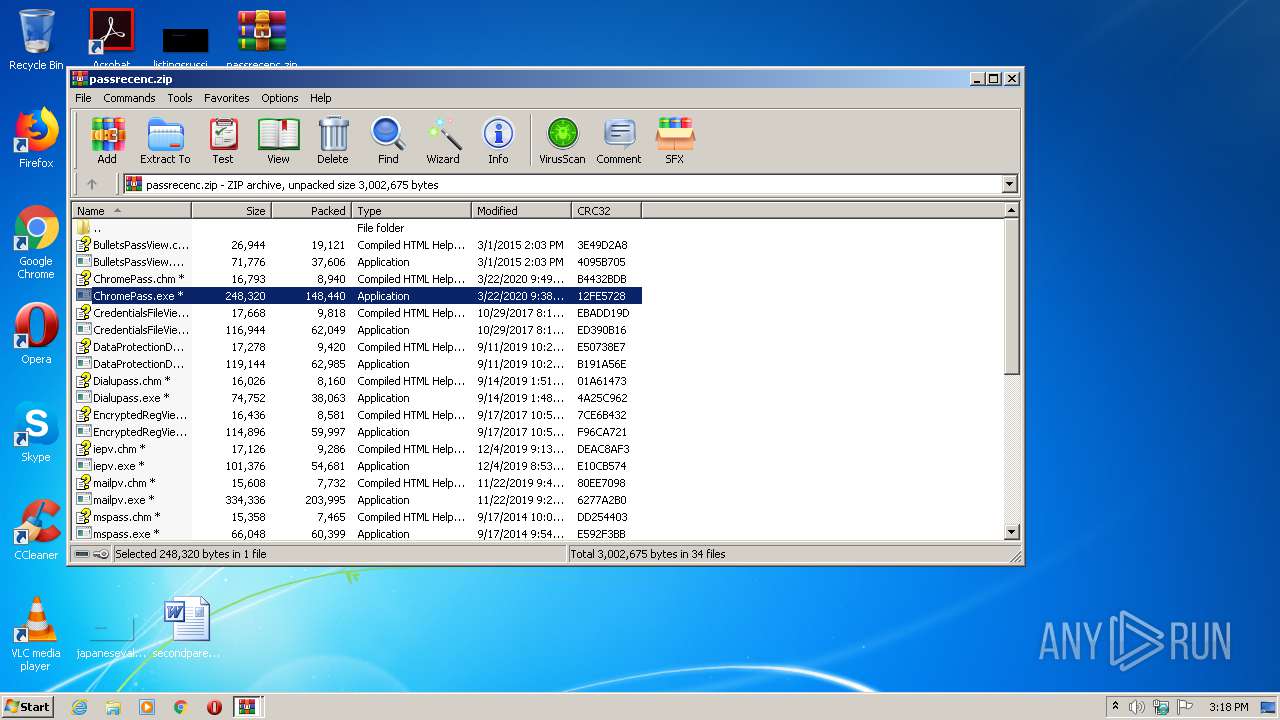
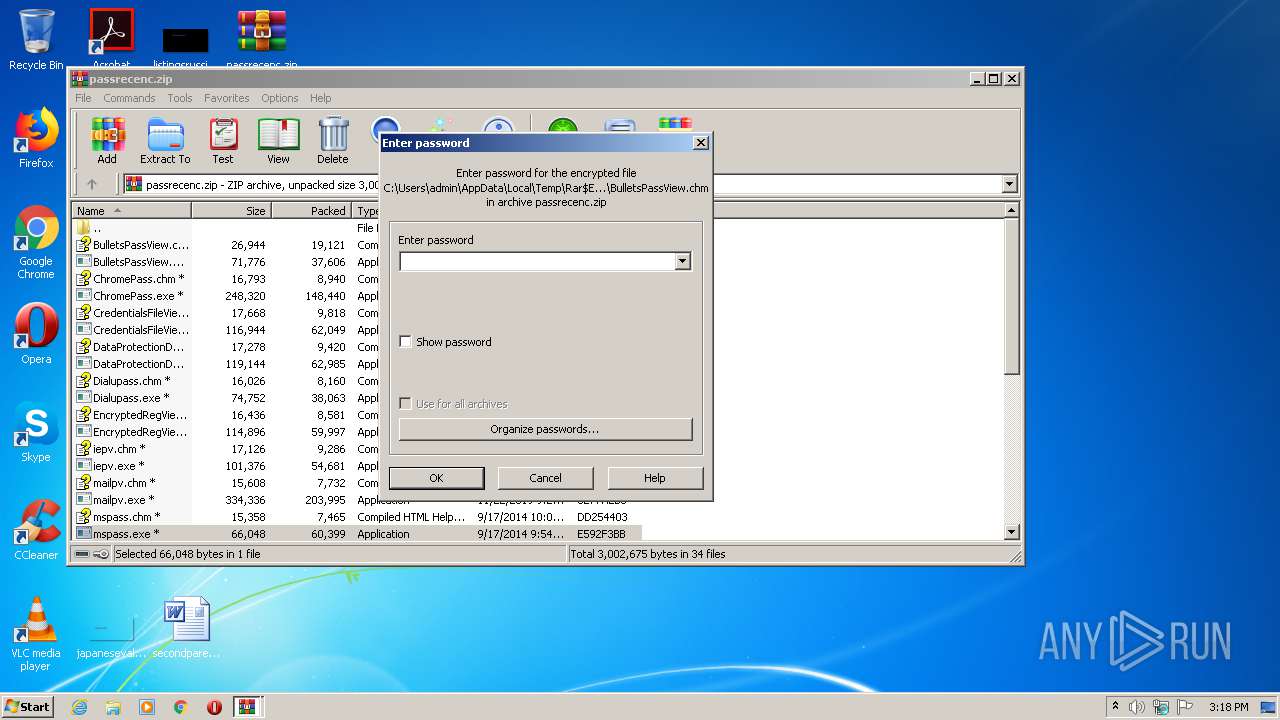
| File name: | passrecenc.zip |
| Full analysis: | https://app.any.run/tasks/c520a7f3-859f-4370-a684-3a8c035a0959 |
| Verdict: | Suspicious activity |
| Analysis date: | September 26, 2020, 14:17:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | A6C88E0CC95EB1B52FCBAED76DA56C03 |
| SHA1: | 2EFBF36F9B6D5A7CFC7EBE027F7D8188417C4ABB |
| SHA256: | 261E5D8516FE1BAF93481AD069B723633B996F933968327F99F6564E3A3B929B |
| SSDEEP: | 49152:QG07jxfp+ccaNWgMjL+UGMXyI1zAVptLIFSE/Ia:QG07jxRF5NWgshGMXz1sVpsga |
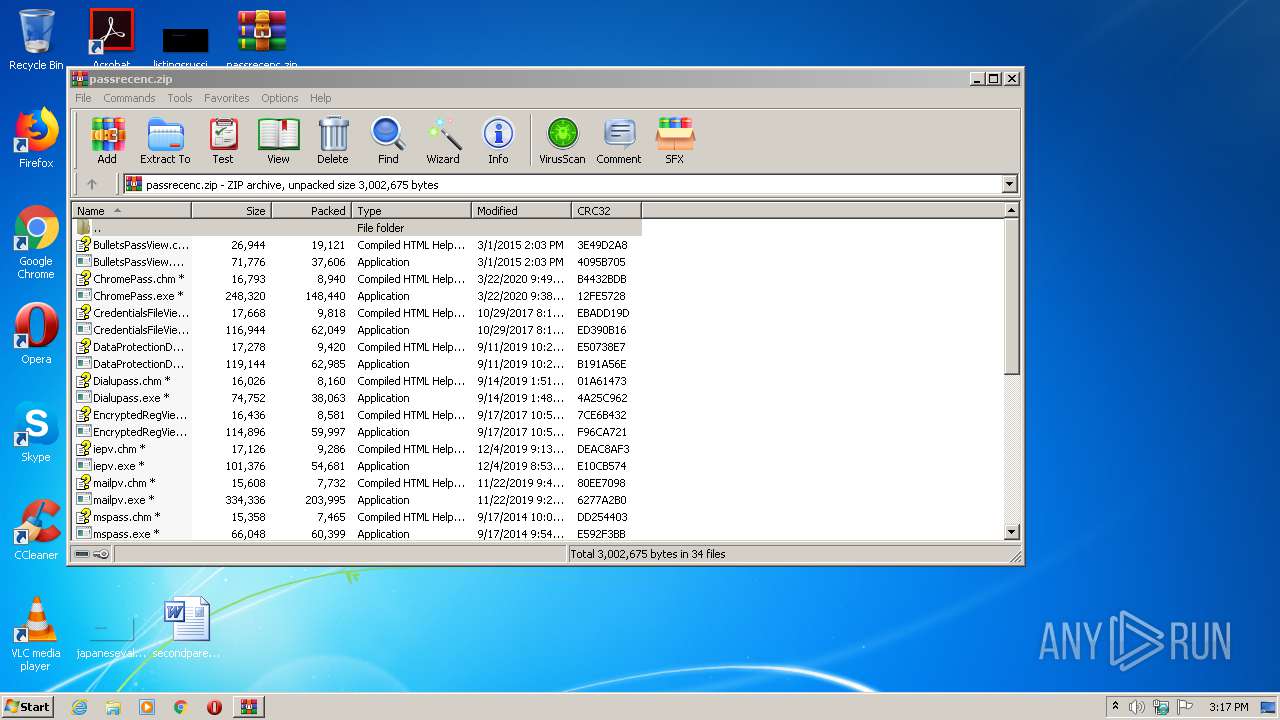
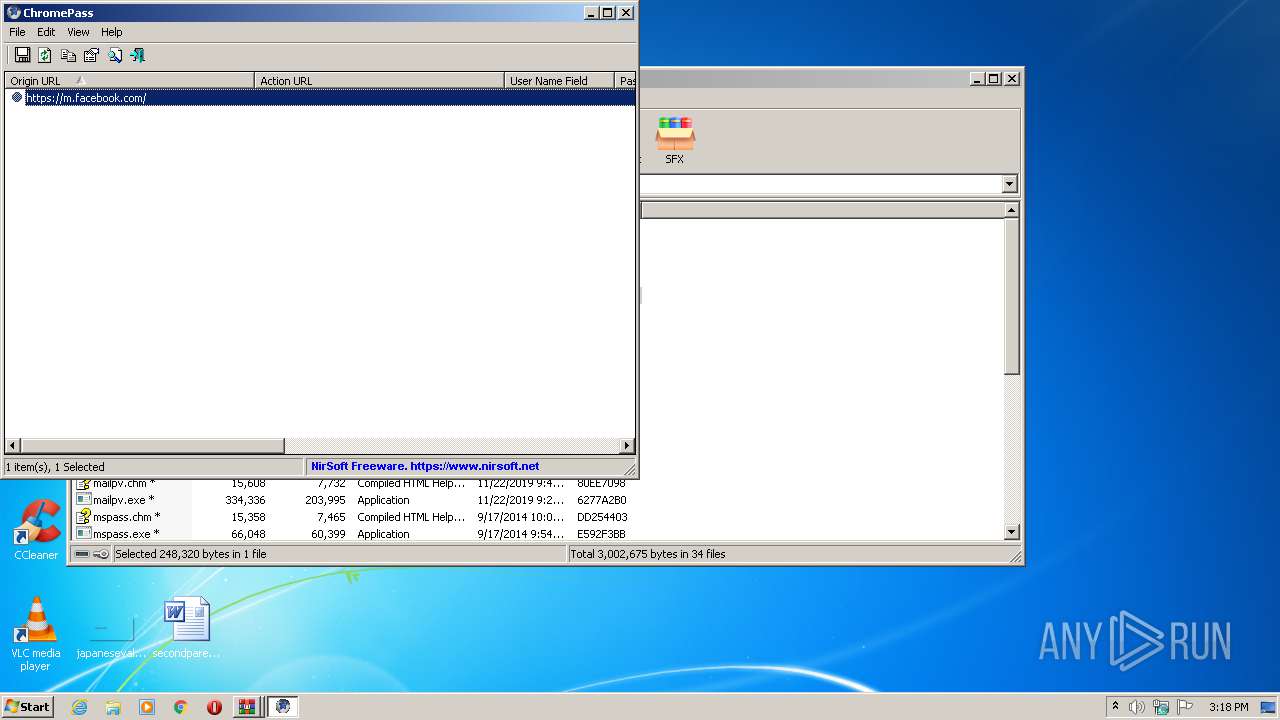
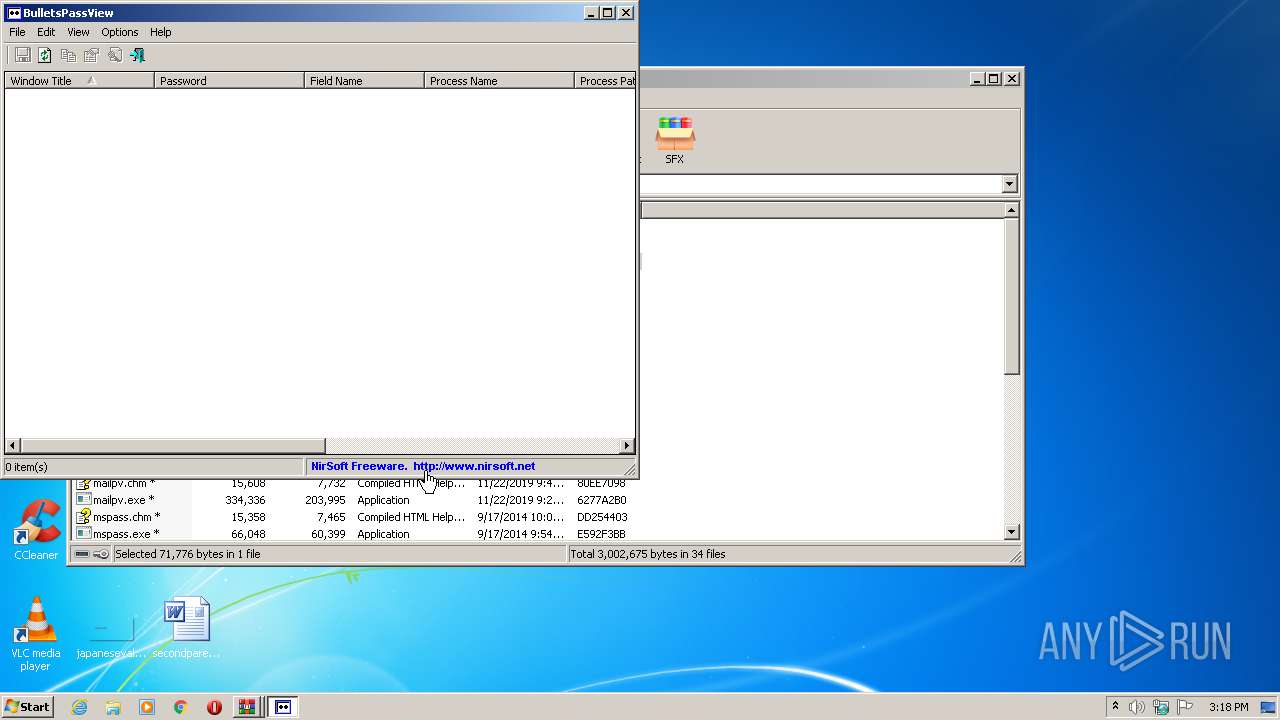
MALICIOUS
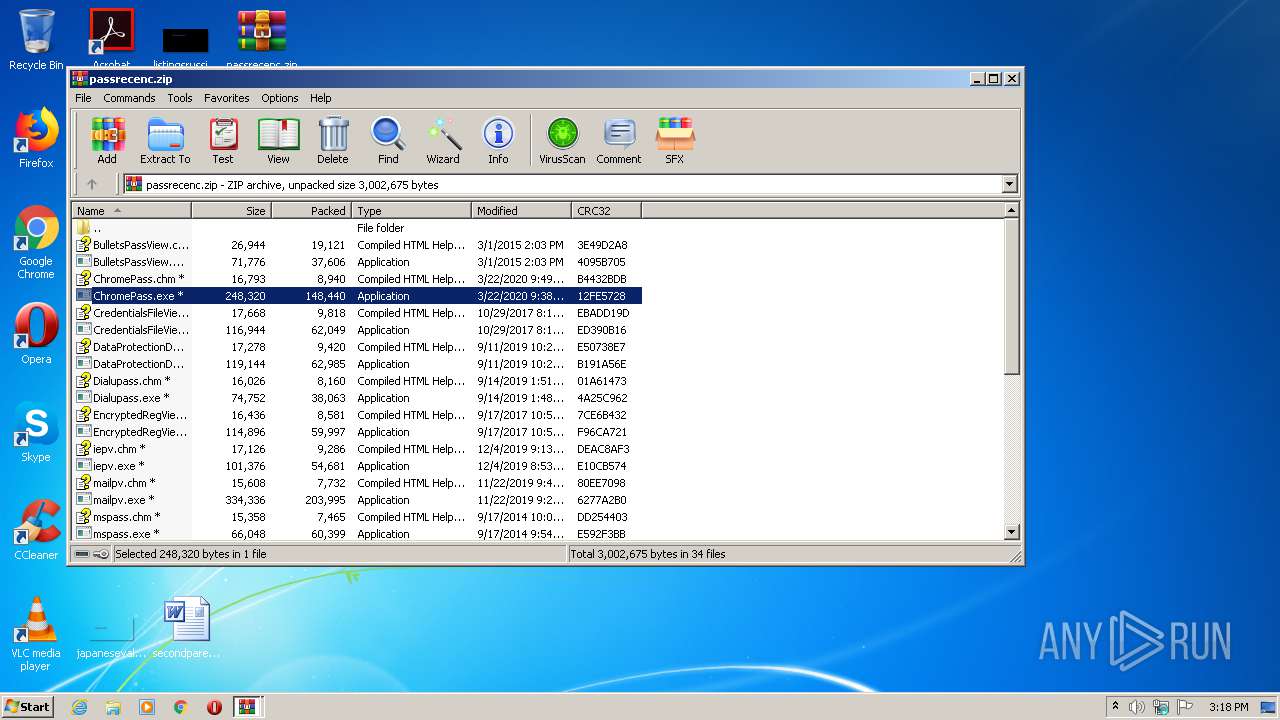
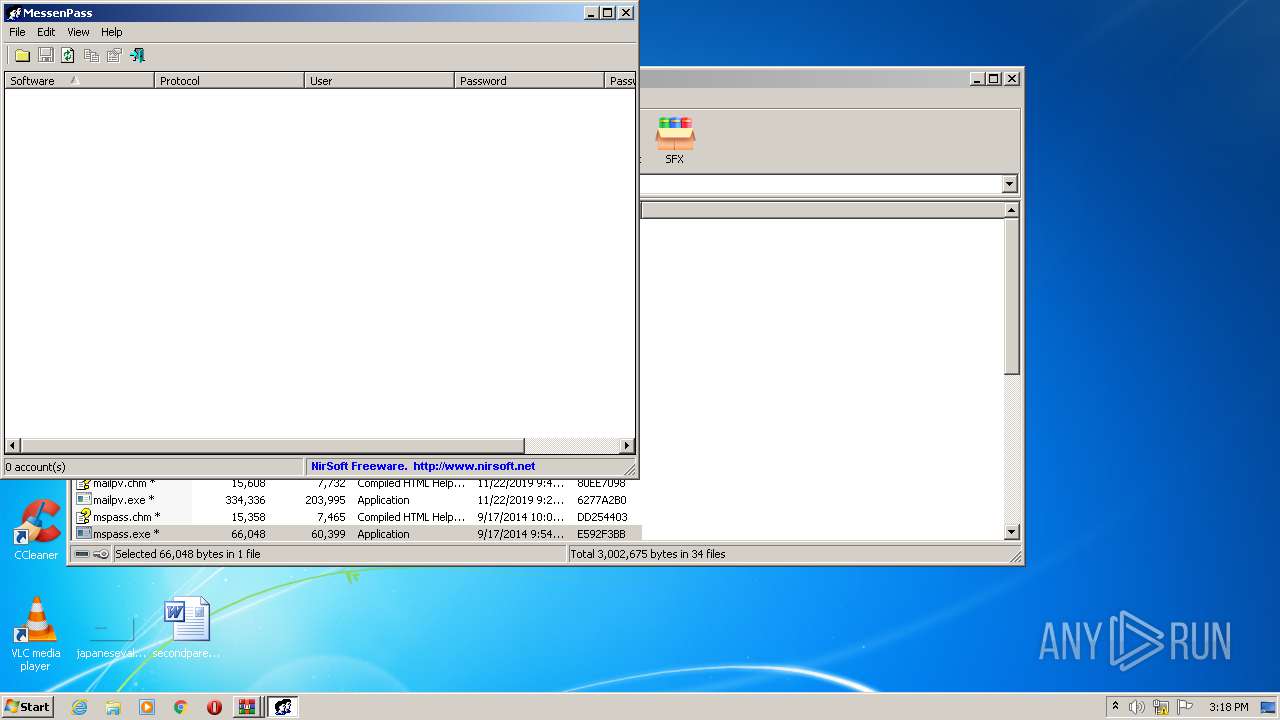
Actions looks like stealing of personal data
- ChromePass.exe (PID: 1064)
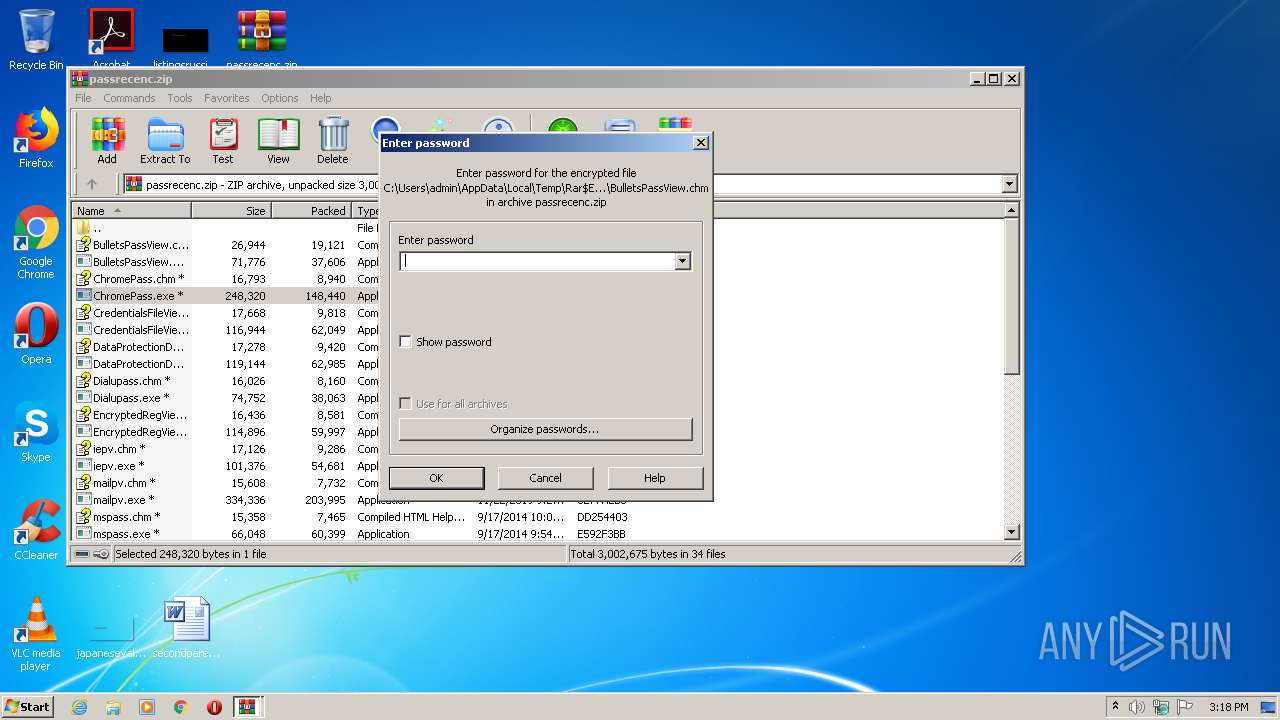
Application was dropped or rewritten from another process
- ChromePass.exe (PID: 1064)
- BulletsPassView.exe (PID: 272)
- mspass.exe (PID: 3704)
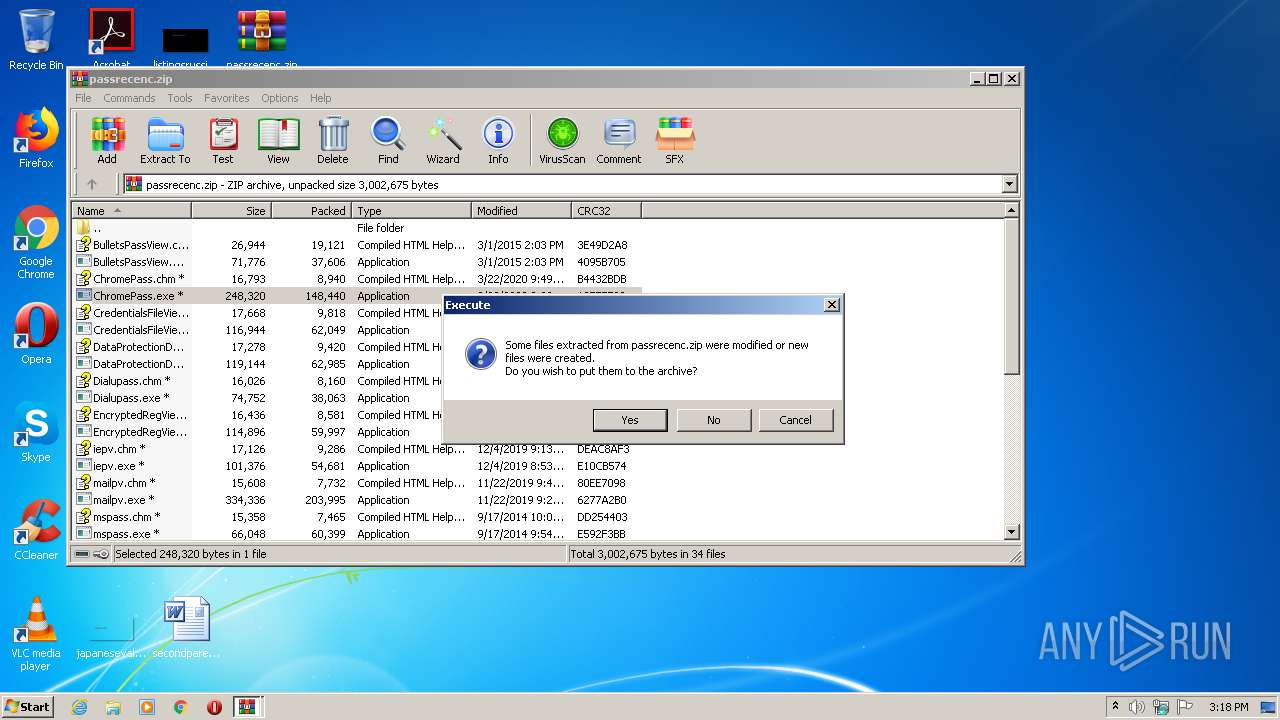
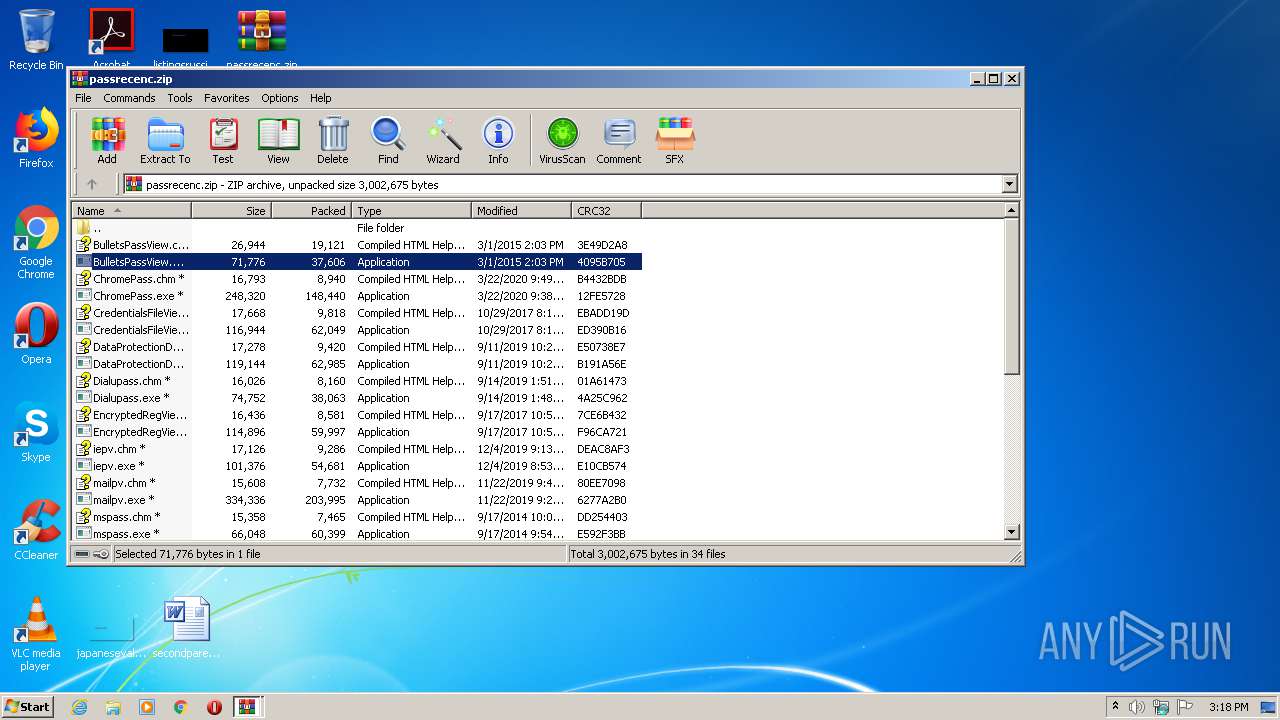
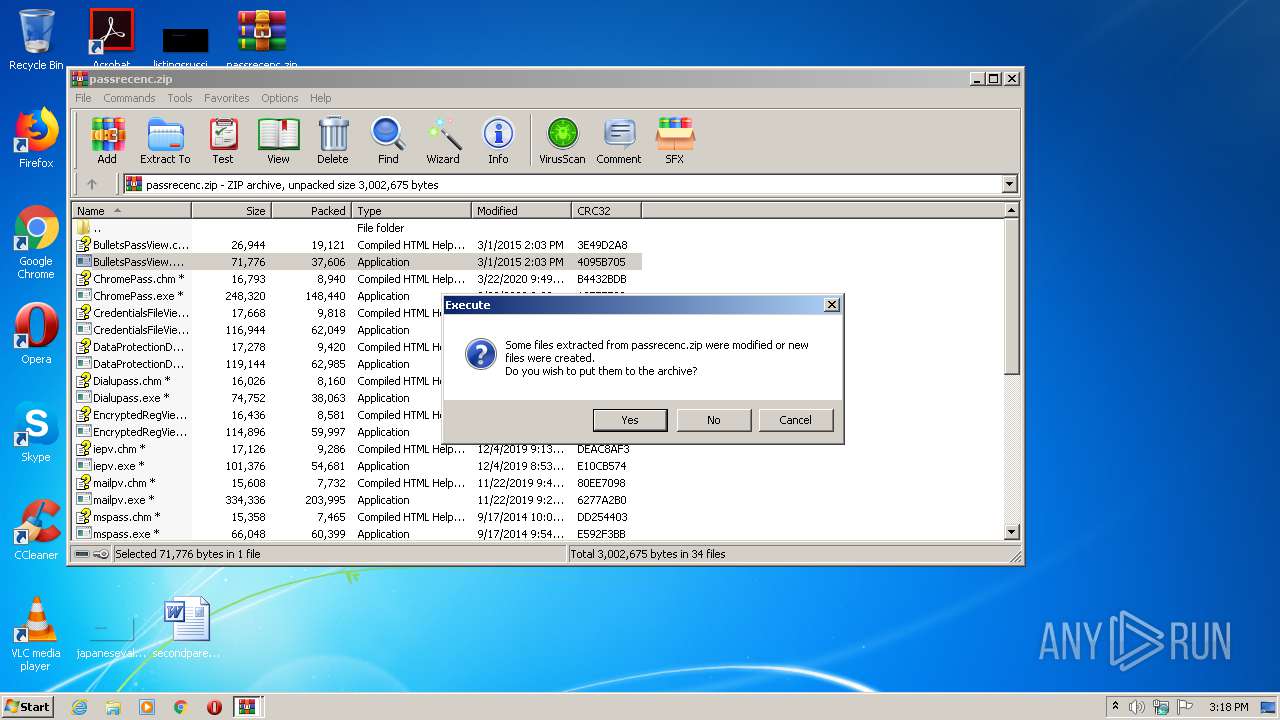
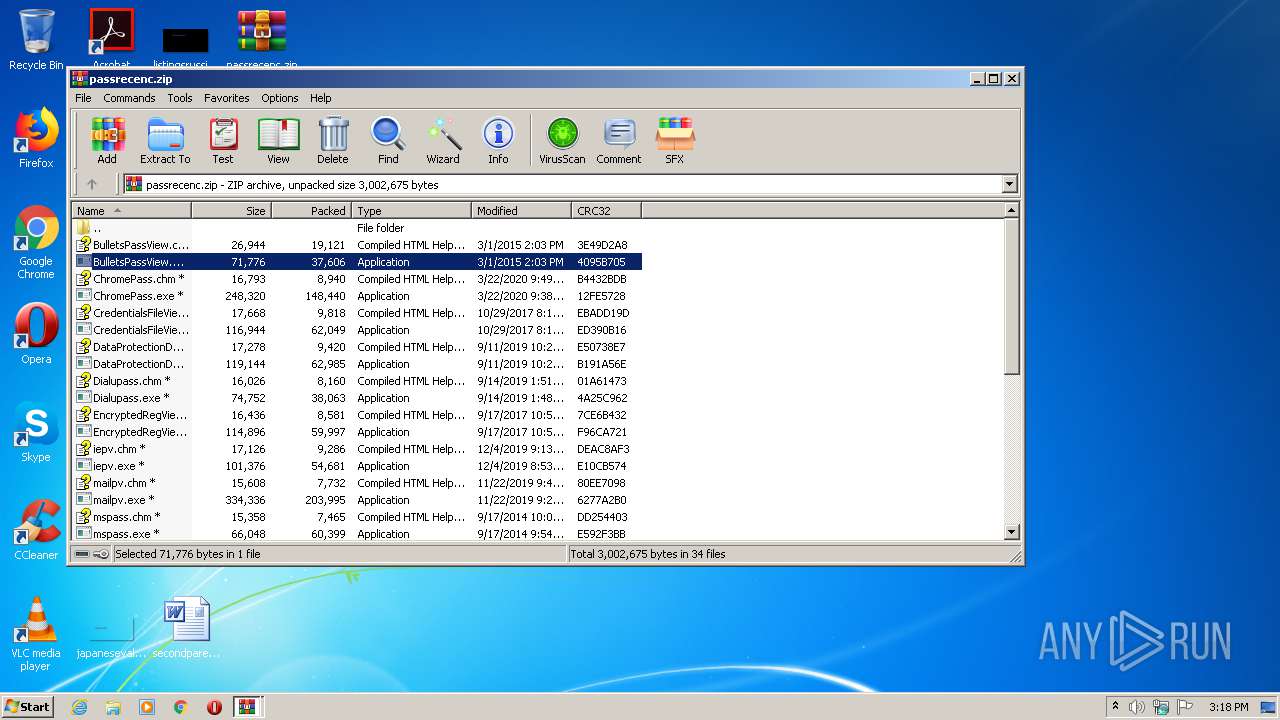
SUSPICIOUS
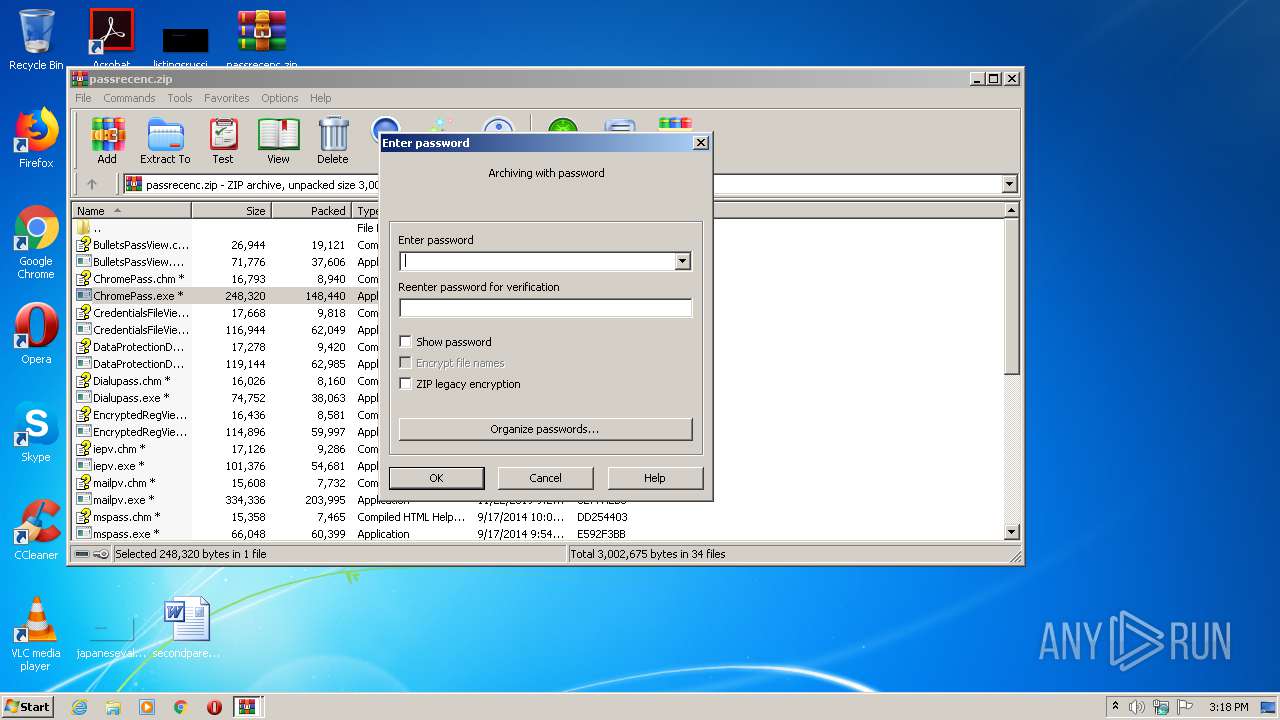
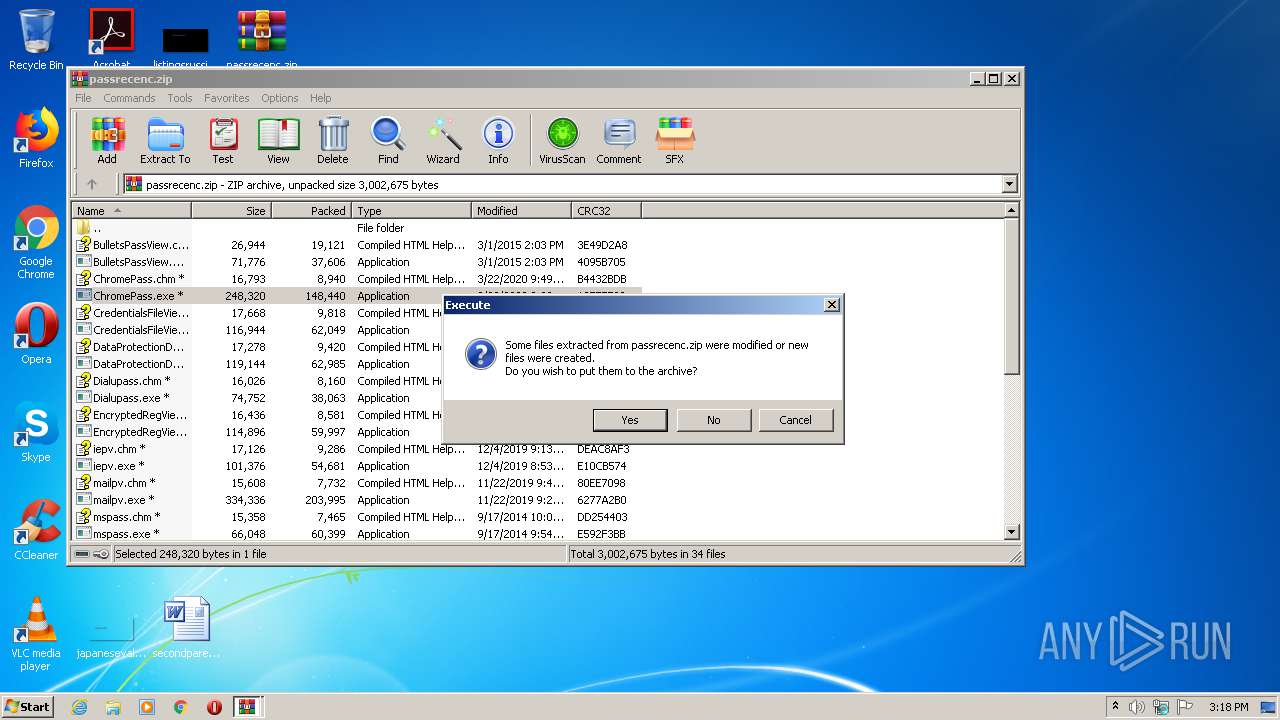
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1796)
INFO
Manual execution by user
- WinRAR.exe (PID: 1796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2015:03:01 17:03:25 |
| ZipCRC: | 0x3e49d2a8 |
| ZipCompressedSize: | 19121 |
| ZipUncompressedSize: | 26944 |
| ZipFileName: | BulletsPassView.chm |
Total processes
42
Monitored processes
5
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
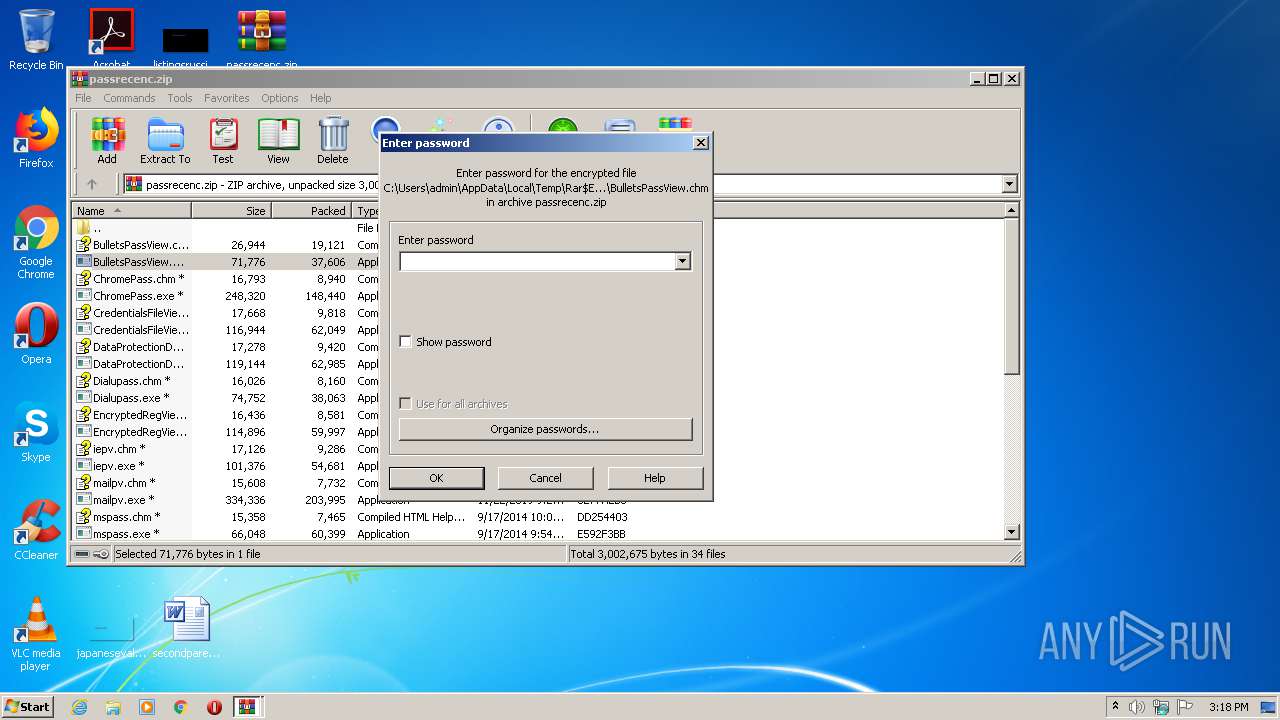
| 272 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb1796.23561\BulletsPassView.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb1796.23561\BulletsPassView.exe | — | WinRAR.exe | |||||||||||
User: admin Company: NirSoft Integrity Level: MEDIUM Description: BulletsPassView Exit code: 0 Version: 1.32 Modules
| |||||||||||||||
| 1064 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb1796.21206\ChromePass.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb1796.21206\ChromePass.exe | WinRAR.exe | ||||||||||||
User: admin Company: NirSoft Integrity Level: MEDIUM Description: Chrome Password Recovery Exit code: 0 Version: 1.51 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\passrecenc.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2364 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\passrecenc.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3704 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb1796.25147\mspass.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb1796.25147\mspass.exe | — | WinRAR.exe | |||||||||||
User: admin Company: NirSoft Integrity Level: MEDIUM Description: IM Password Recovery Exit code: 0 Version: 1.43 | |||||||||||||||
Total events
842
Read events
816
Write events
26
Delete events
0
Modification events
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\passrecenc.zip | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\hhctrl.ocx,-452 |
Value: Compiled HTML Help file | |||
| (PID) Process: | (1796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
Executable files
36
Suspicious files
0
Text files
31
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1796.21206\ChromePass.exe | executable | |
MD5:— | SHA256:— | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1796.21206\DataProtectionDecryptor.chm | chi | |
MD5:— | SHA256:— | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1796.21206\DataProtectionDecryptor.exe | executable | |
MD5:— | SHA256:— | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1796.21206\EncryptedRegView.exe | executable | |
MD5:— | SHA256:— | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1796.21206\CredentialsFileView.chm | chi | |
MD5:— | SHA256:— | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1796.21206\CredentialsFileView.exe | executable | |
MD5:— | SHA256:— | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1796.21206\ChromePass.chm | chi | |
MD5:2D070C104CF02EFAA8B752C8BF53DB80 | SHA256:3B0FB69F8911588B915F4CEE7077E32B7F226BD0DB0EB8336DD6B146BBE66671 | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1796.21206\BulletsPassView.exe | executable | |
MD5:E40C9293EA0B6D62A0F62F40212DF07B | SHA256:B19DFE440E515C39928B475A946656A12B1051E98E0DF36C016586B34A766D5C | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1796.21206\EncryptedRegView.chm | chi | |
MD5:EC99CDA2E1B89B25D3A1C8925005F66F | SHA256:83BD82522E8C63FC3F14989E5BB61E2946AF46B2A7CFE847A9A0A57387669EF5 | |||
| 1796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1796.21206\Dialupass.chm | chi | |
MD5:287F794AA15CB93FA91B763B34FE3A3A | SHA256:1E3EC12FBE9825C1EB044994D27C6FB97E5B2CEE352D114B0AE6F8862E2A2DD5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report