| download: | exploit-main.dll |
| Full analysis: | https://app.any.run/tasks/44bab0d0-c59f-4dc3-b85f-0fb180a0efb1 |
| Verdict: | Suspicious activity |
| Analysis date: | January 25, 2019, 00:19:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | F214D1CA9B2E7C67F8AEF7B16249563E |
| SHA1: | 68F541DCF73A2FDA9EF6FAA360990459FA36AAF2 |
| SHA256: | 2607BD17641DC2DCC3269399347A988D61F9883E57E3700070C279A3E9523B44 |
| SSDEEP: | 12288:qRrO9WYln6O/tfob47ztgjV7cVVdhDkzYFTQXhBOmr9XW2:xVgqWYFT6pr9 |
MALICIOUS
Loads dropped or rewritten executable
- WerFault.exe (PID: 3052)
- svchost.exe (PID: 844)
- explorer.exe (PID: 116)
SUSPICIOUS
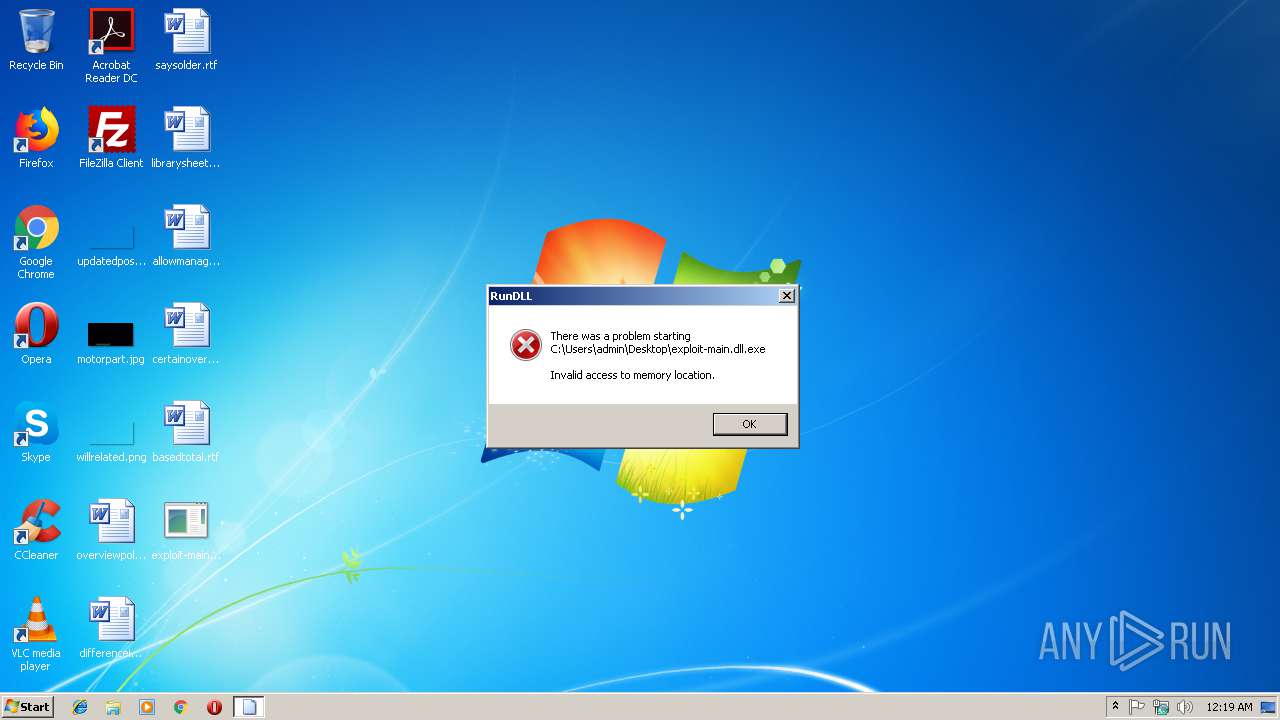
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 116)
INFO
Loads main object executable
- rundll32.exe (PID: 2804)
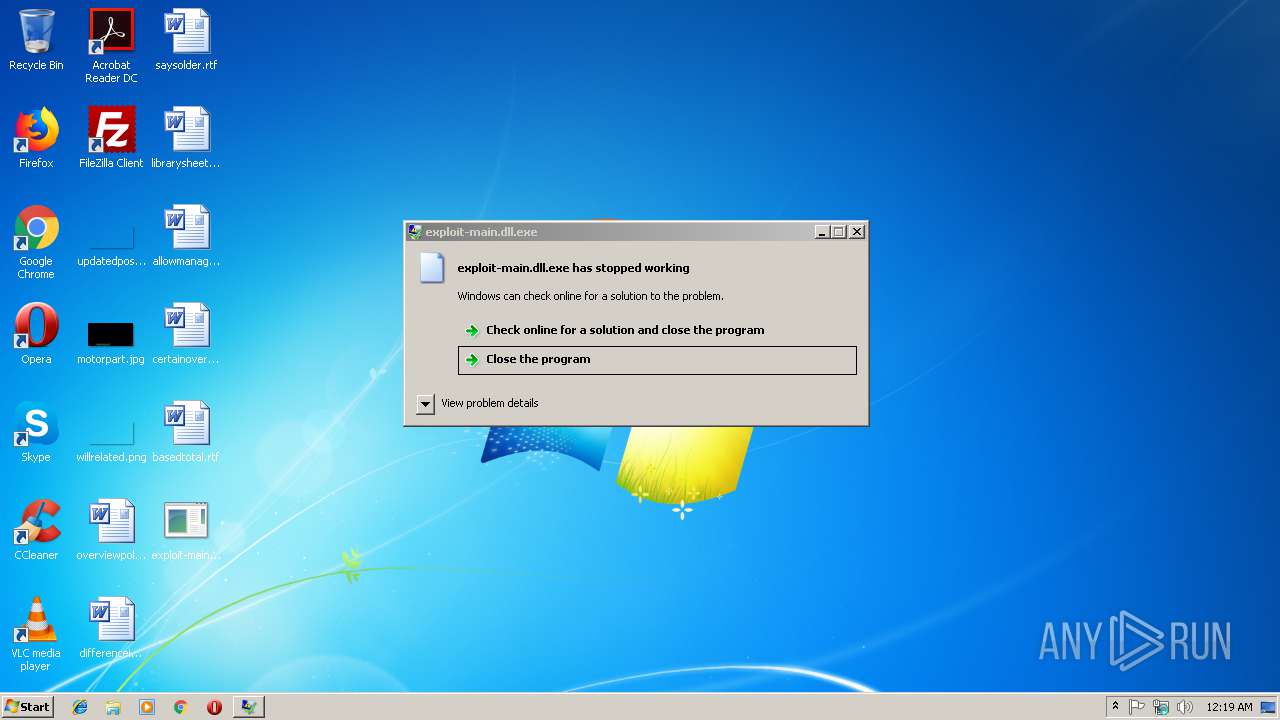
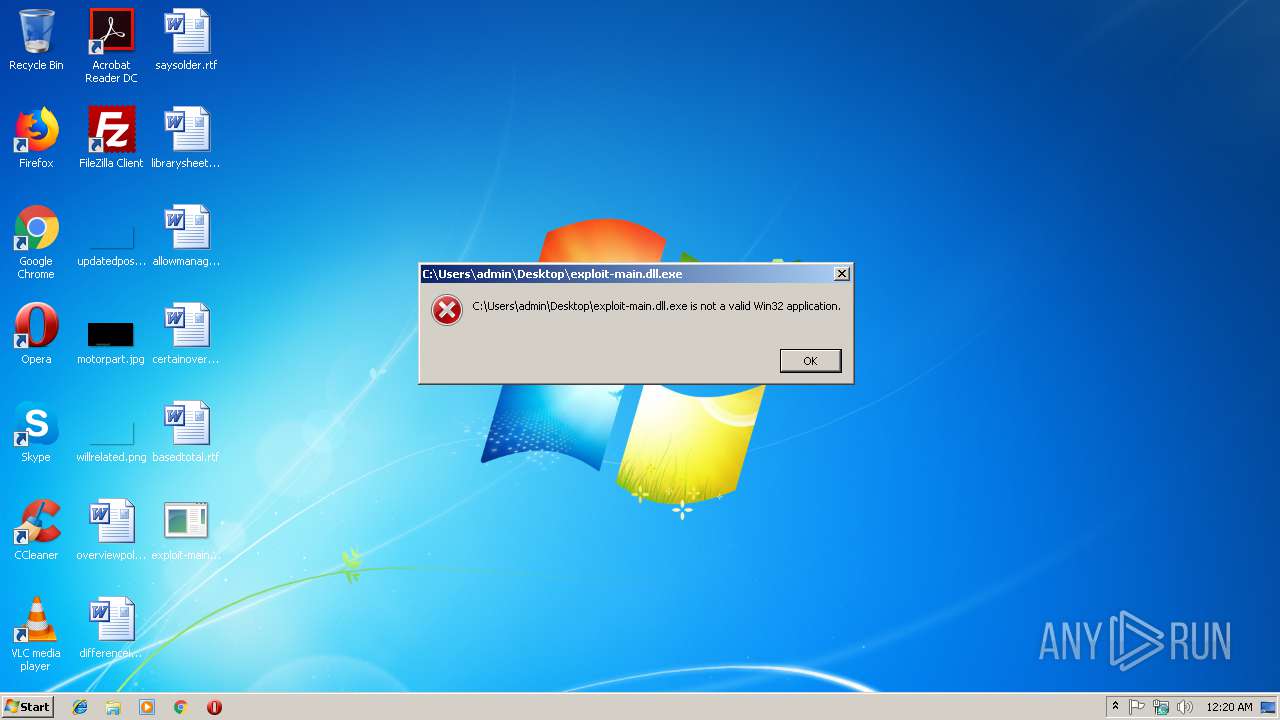
Application was crashed
- rundll32.exe (PID: 2804)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:13 09:14:51+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.14 |
| CodeSize: | 419840 |
| InitializedDataSize: | 143360 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x36712 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Dec-2018 08:14:51 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 13-Dec-2018 08:14:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0006667E | 0x00066800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67681 |
.rdata | 0x00068000 | 0x0001B39E | 0x0001B400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.95372 |
.data | 0x00084000 | 0x00002280 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.72285 |
.rsrc | 0x00087000 | 0x000001E0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.72473 |
.reloc | 0x00088000 | 0x00005524 | 0x00005600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.68852 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
2 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
WININET.dll |
WS2_32.dll |
Total processes
32
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 844 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2804 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\Desktop\exploit-main.dll.exe", DllMain | C:\Windows\System32\rundll32.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 3221225477 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3052 | C:\Windows\system32\WerFault.exe -u -p 2804 -s 208 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
874
Read events
874
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 844 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 3052 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportArchive\AppCrash_rundll32.exe_exp_9c780731a5b4acb9bdfd7bc73180e99f3d4c51_0bf5a7ee\Report.wer | binary | |
MD5:— | SHA256:— | |||
| 3052 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\rundll32.exe.2804.dmp | dmp | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report