| File name: | AOMEI.exe |
| Full analysis: | https://app.any.run/tasks/74c3f894-f252-4a49-a5a5-68160c7eeb4f |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2021, 09:06:04 |
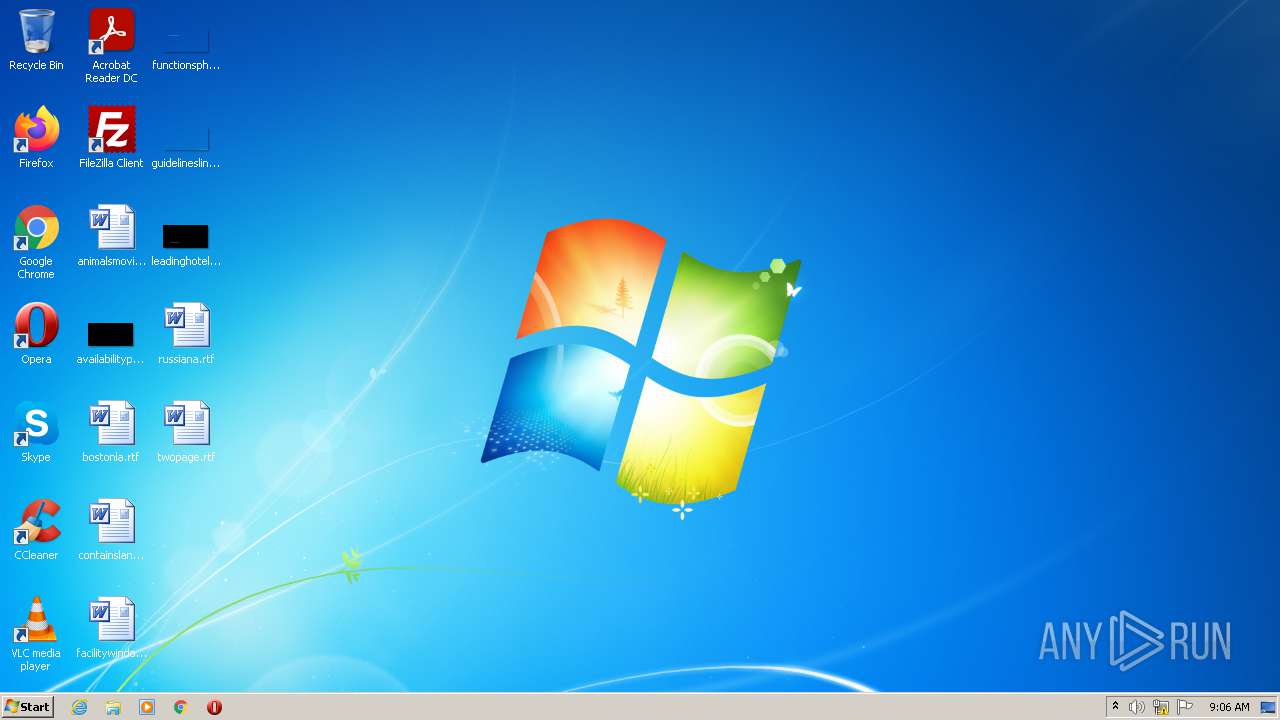
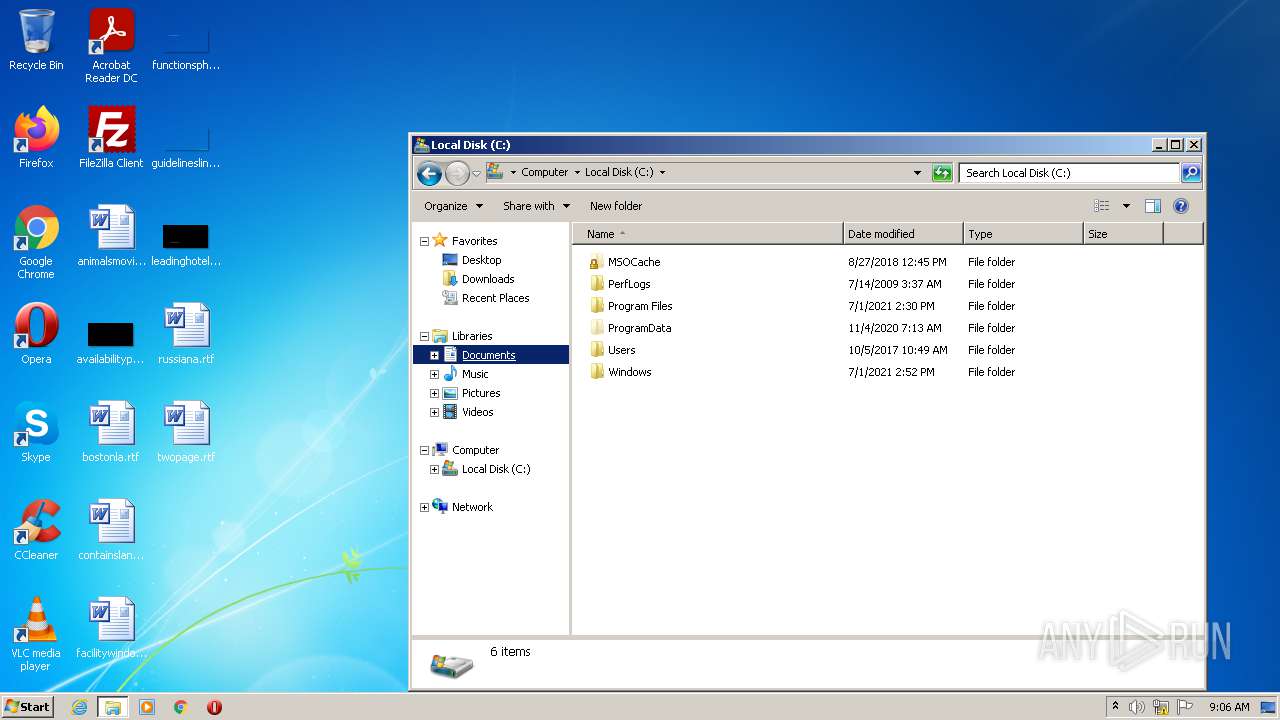
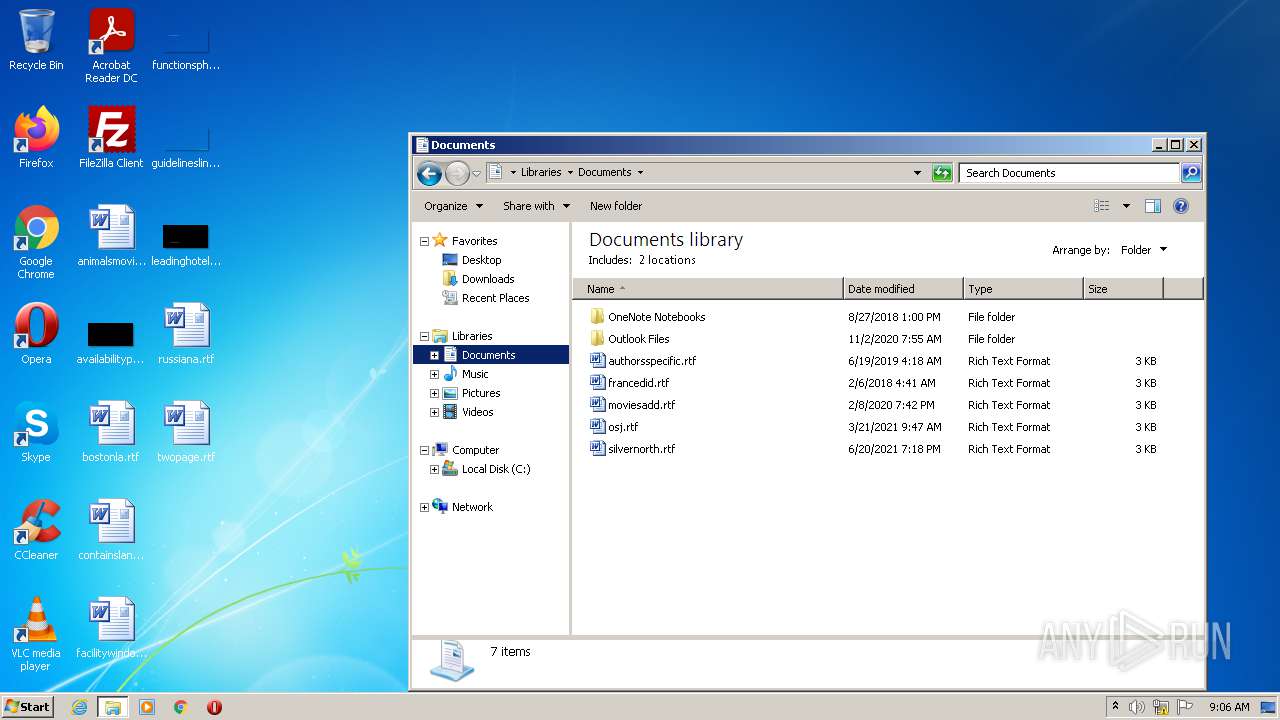
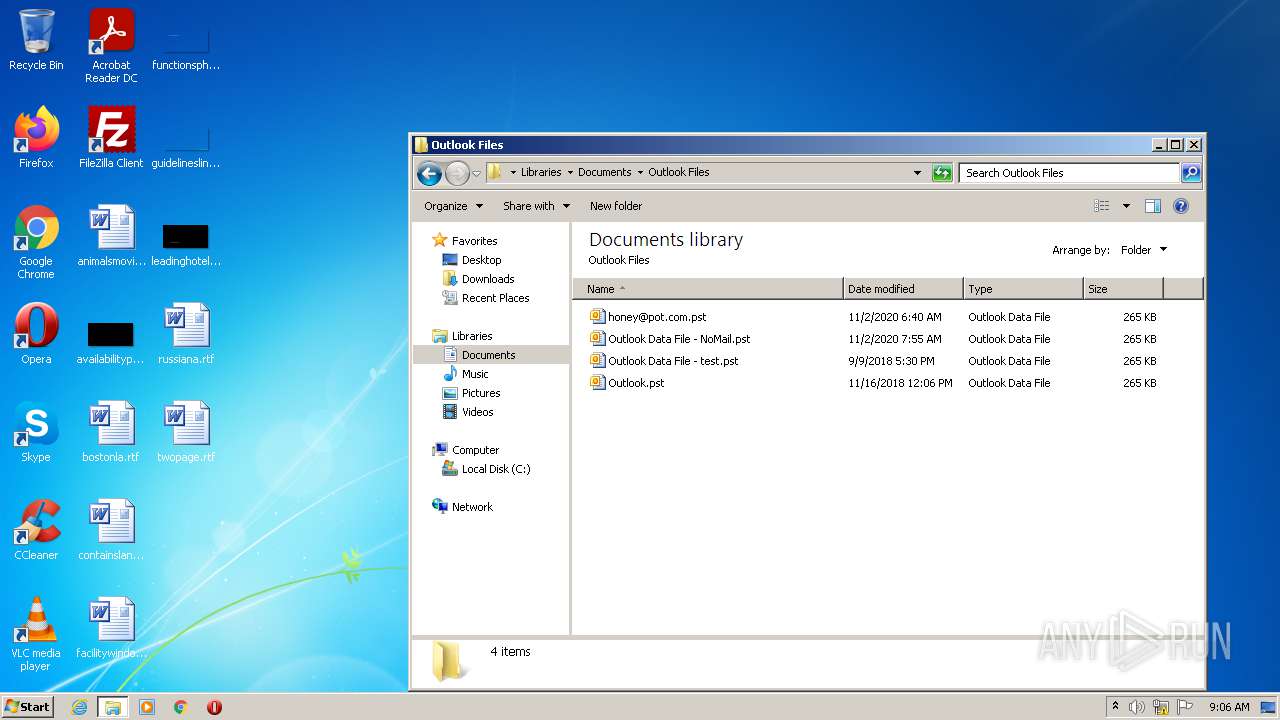
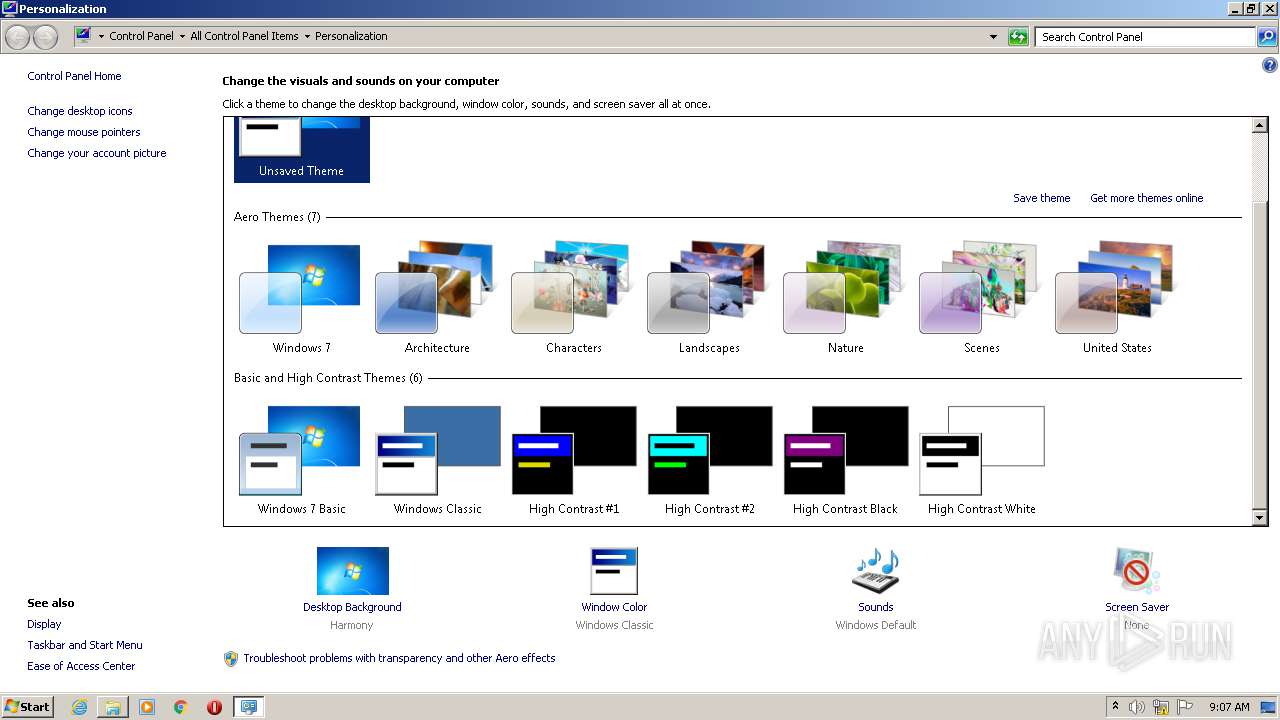
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9022C6EE966FA94DE5758771E629DDD6 |
| SHA1: | F2A6947FDE5EECC92BC92CBDCF35DB78F5652831 |
| SHA256: | 26062B2E01B128DDB524F3C5C1B09723F3D18D21939C750E773F7D7FE9D4D302 |
| SSDEEP: | 3072:tRHC+lH3QKW0j94tZC0kxp7F1QLUUmgRU4rjYIwli/ji095fIh47Md8brs9wx+uw:OM62F1FUmgRU4rjty0u0PIhQ8DiAAvc |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- AOMEI.exe (PID: 3816)
Reads the computer name
- AOMEI.exe (PID: 3816)
Reads the date of Windows installation
- AOMEI.exe (PID: 3816)
Reads Windows Product ID
- AOMEI.exe (PID: 3816)
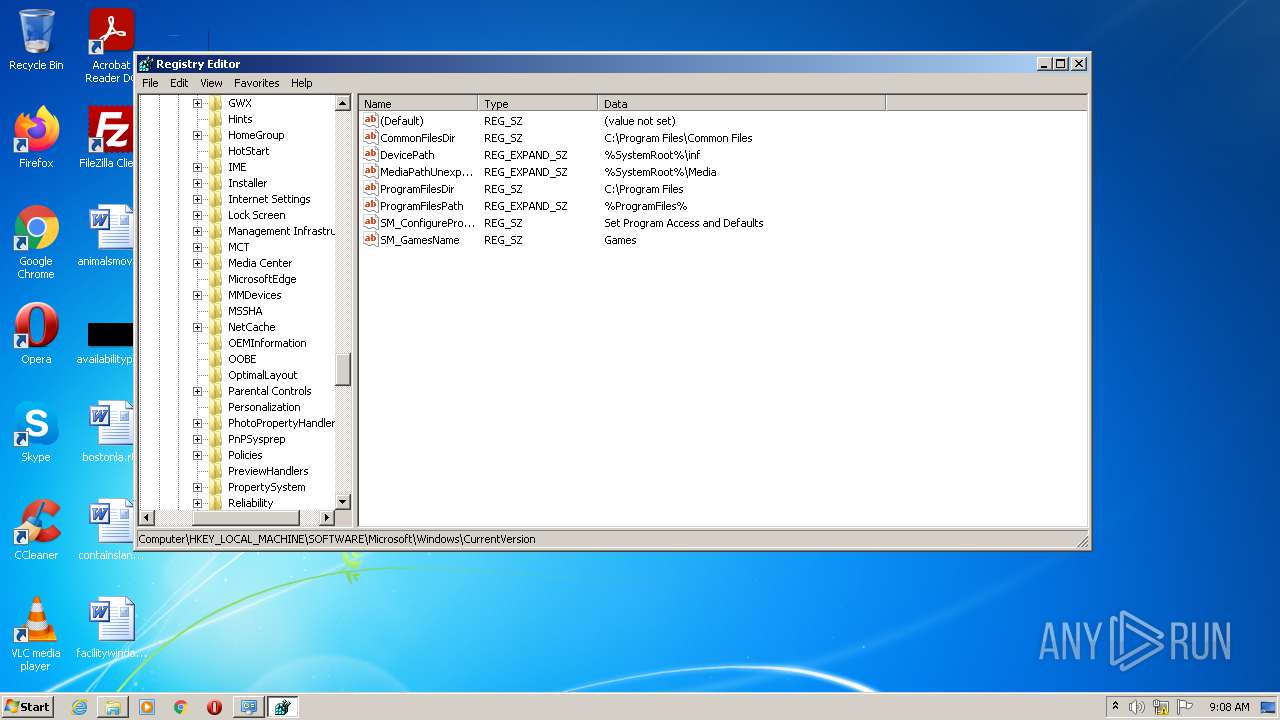
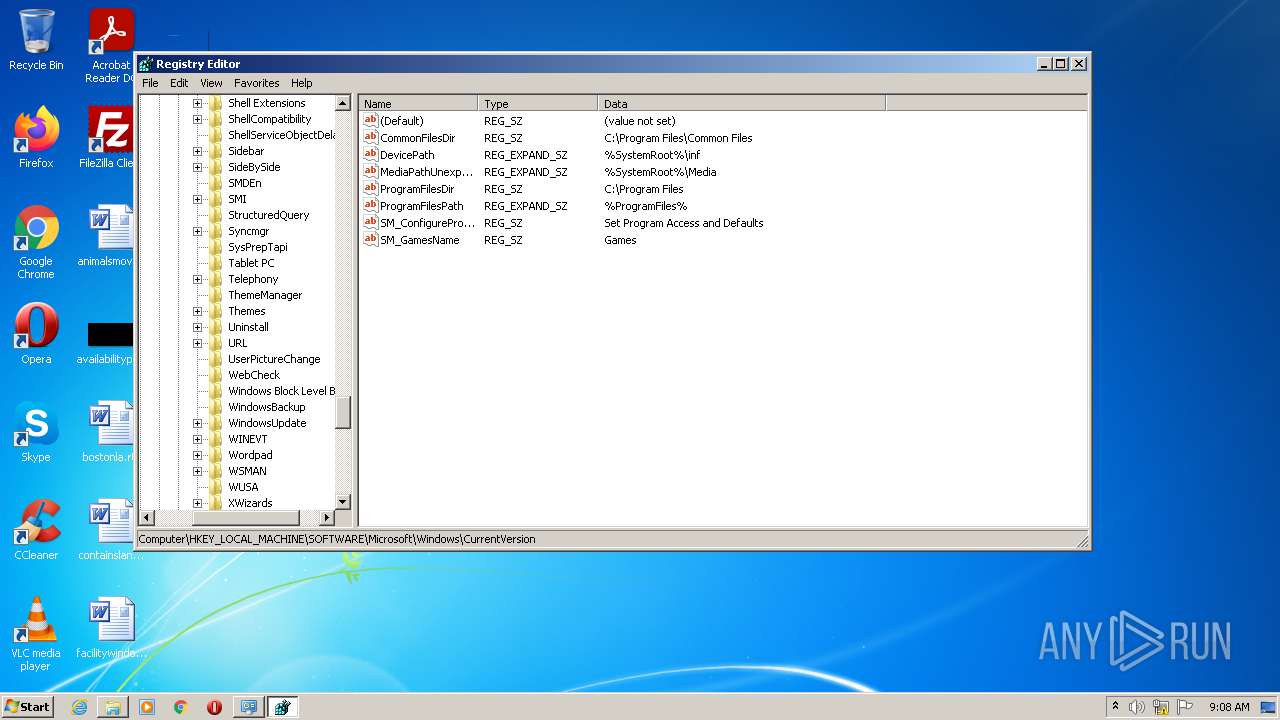
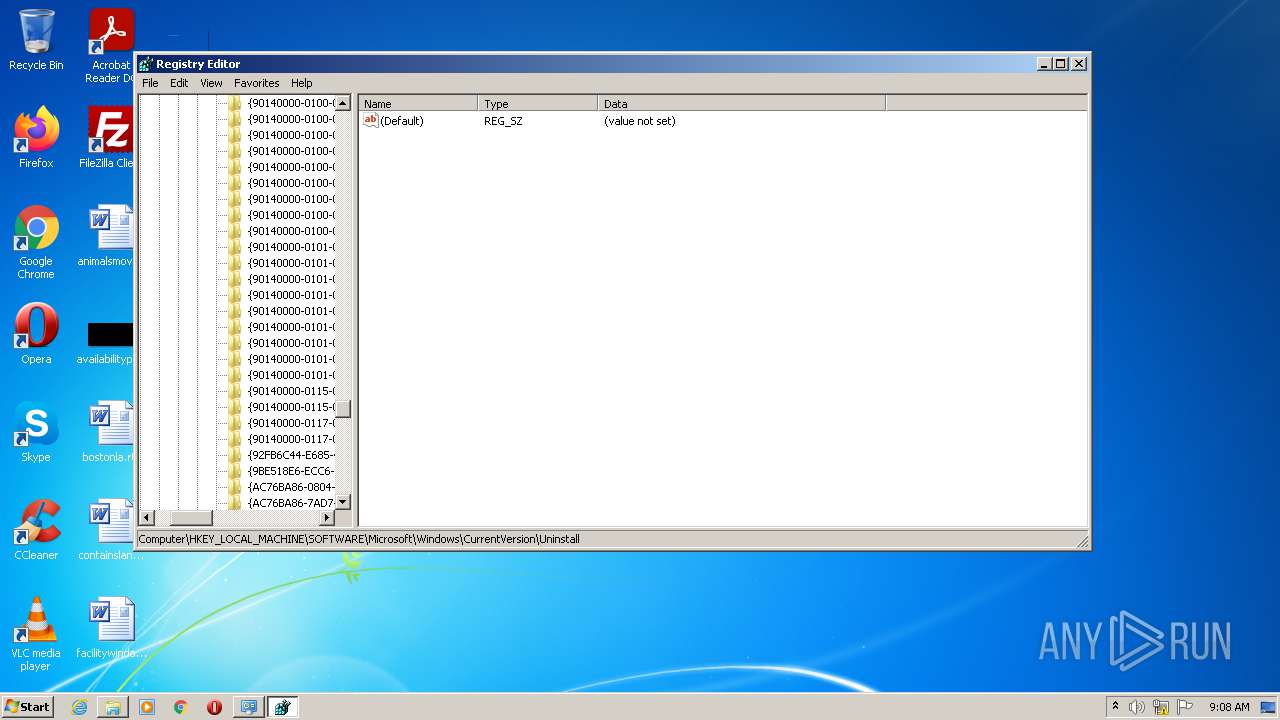
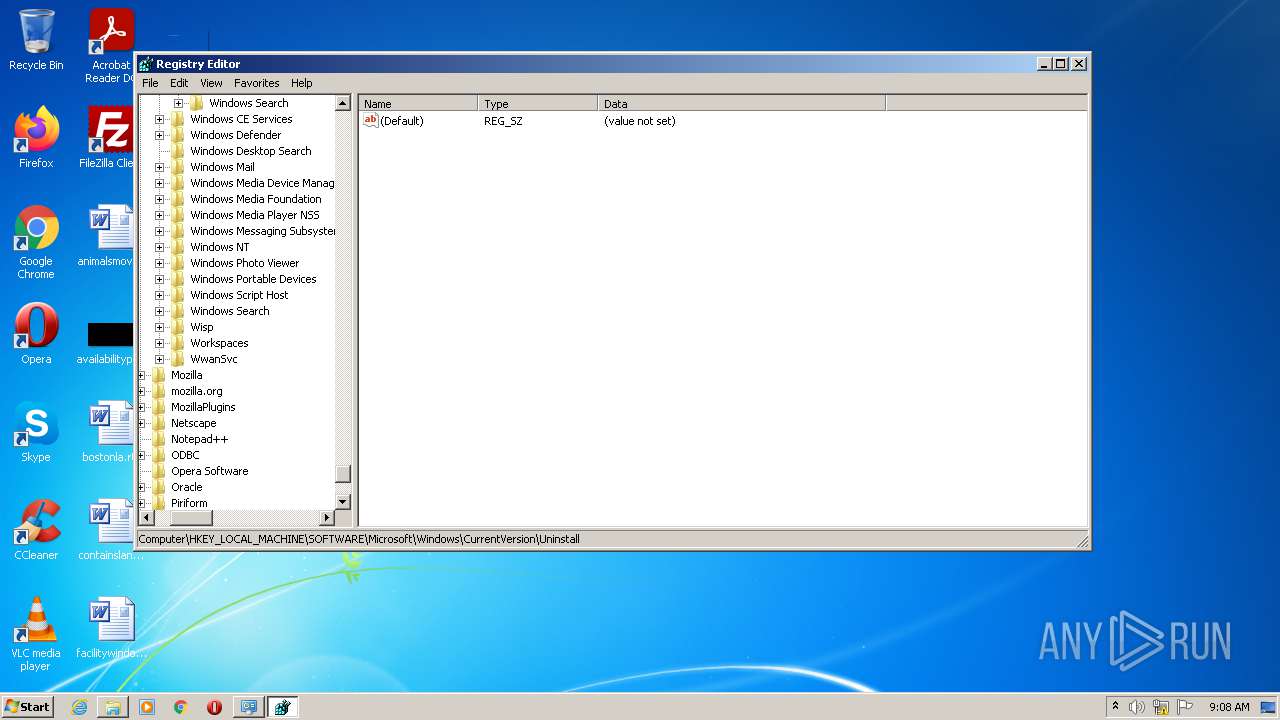
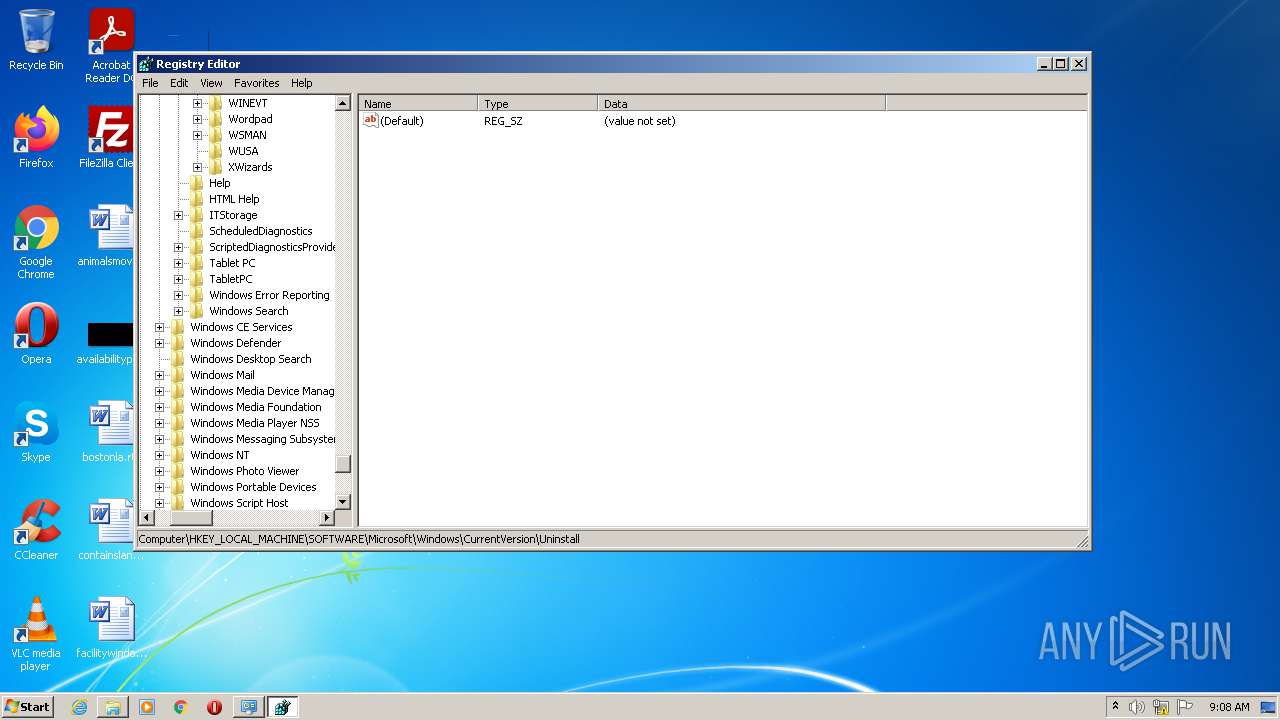
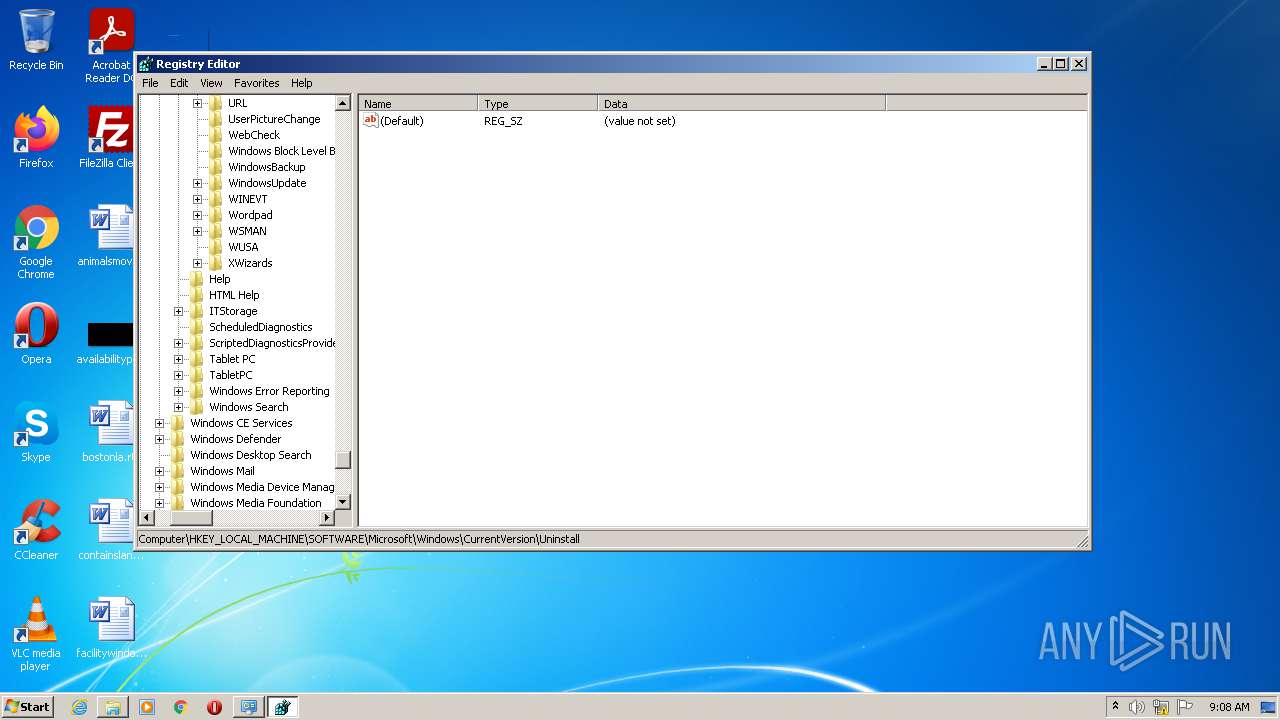
Searches for installed software
- AOMEI.exe (PID: 3816)
INFO
Reads settings of System Certificates
- AOMEI.exe (PID: 3816)
Reads the computer name
- explorer.exe (PID: 4092)
Checks supported languages
- explorer.exe (PID: 4092)
- regedit.exe (PID: 1128)
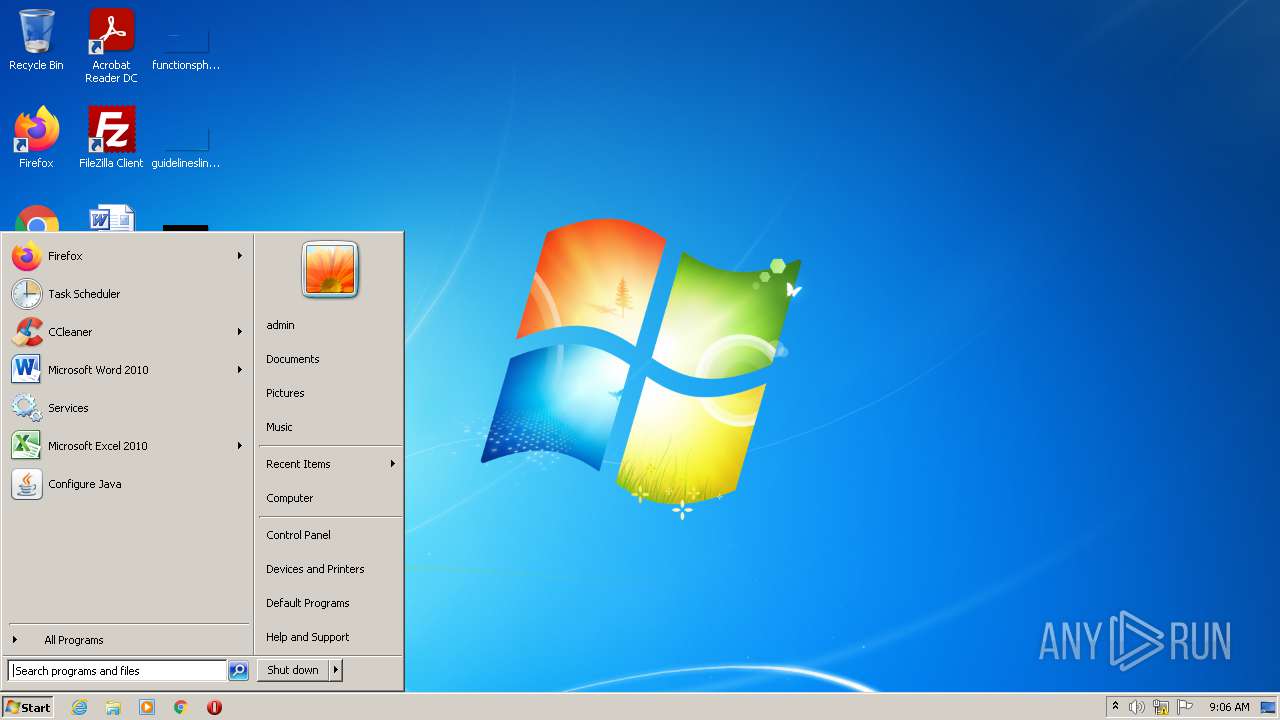
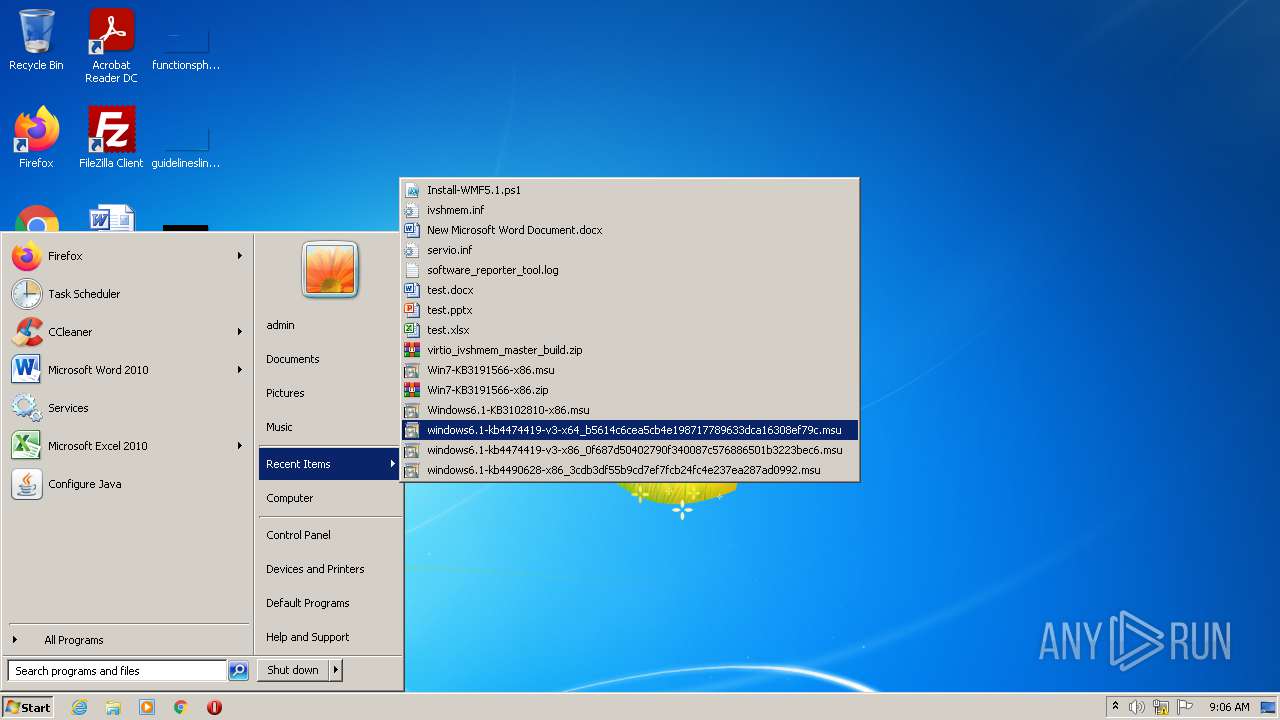
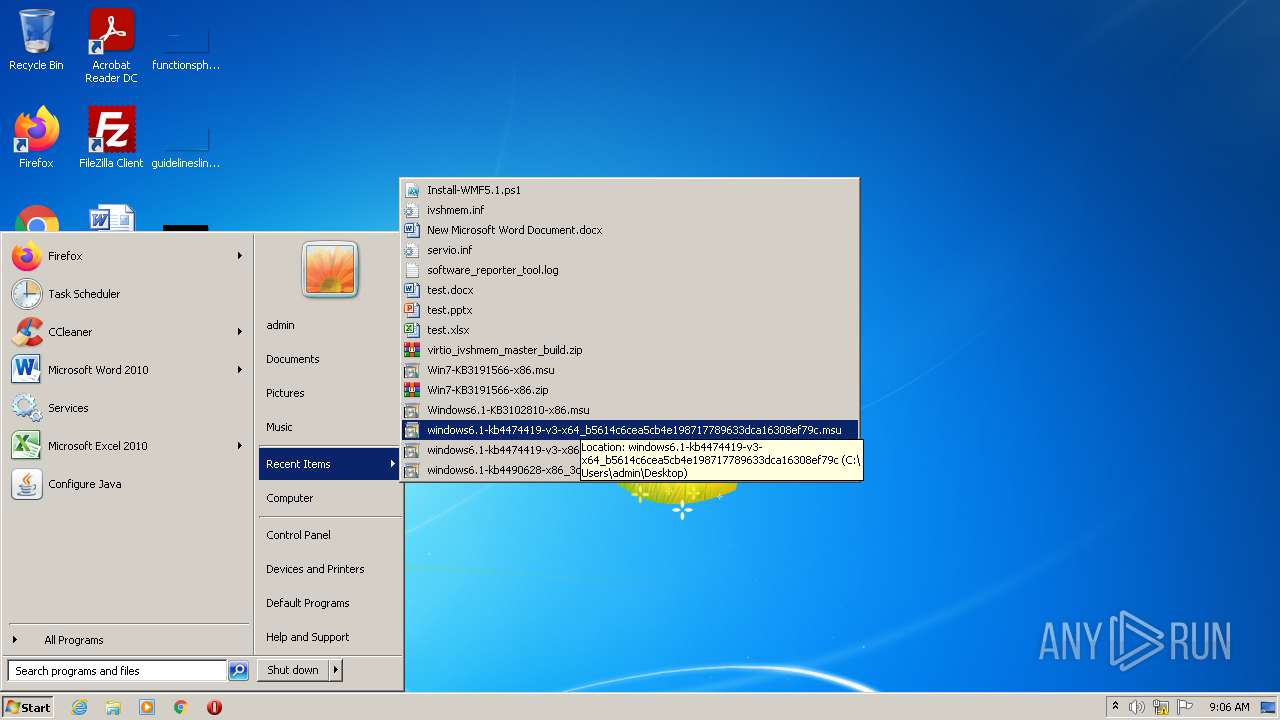
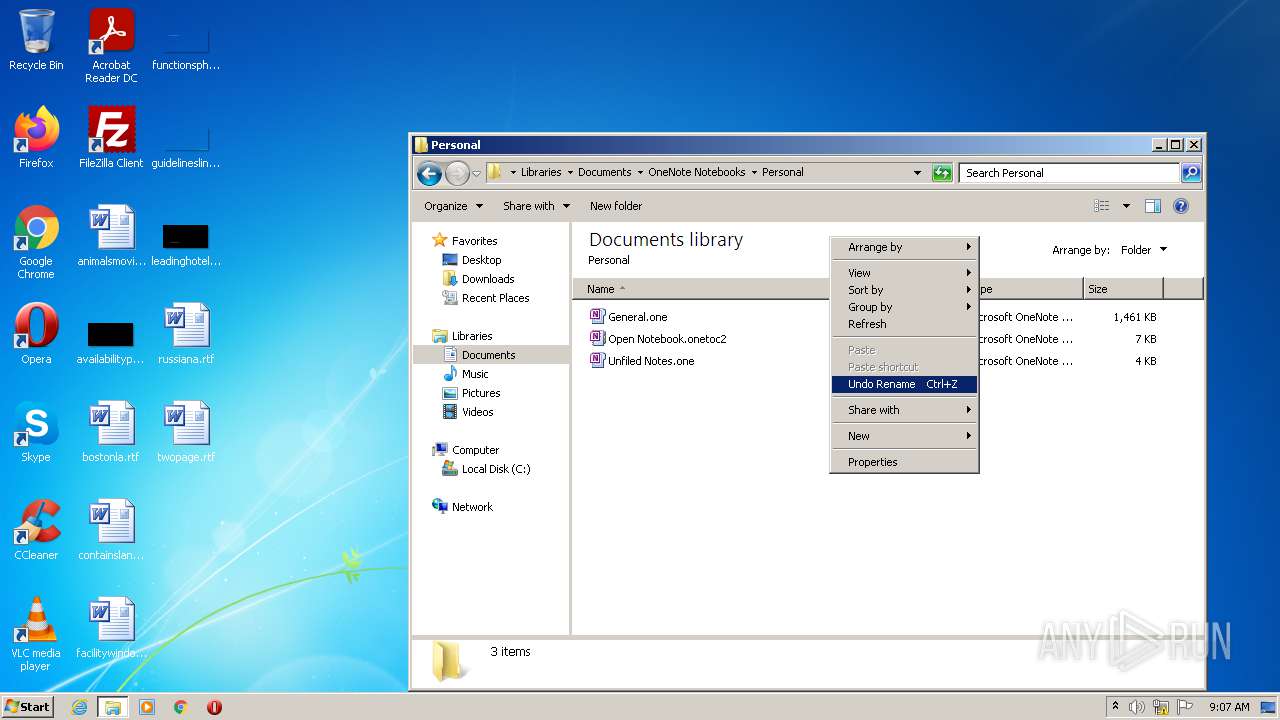
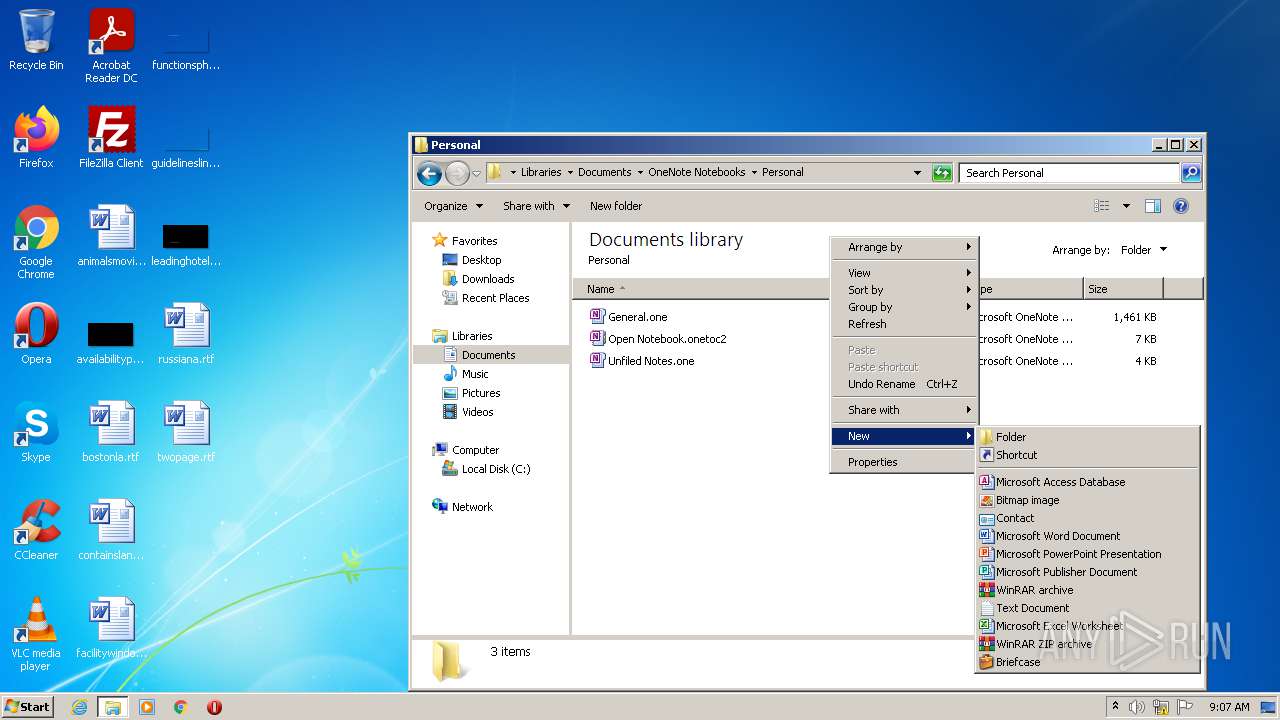
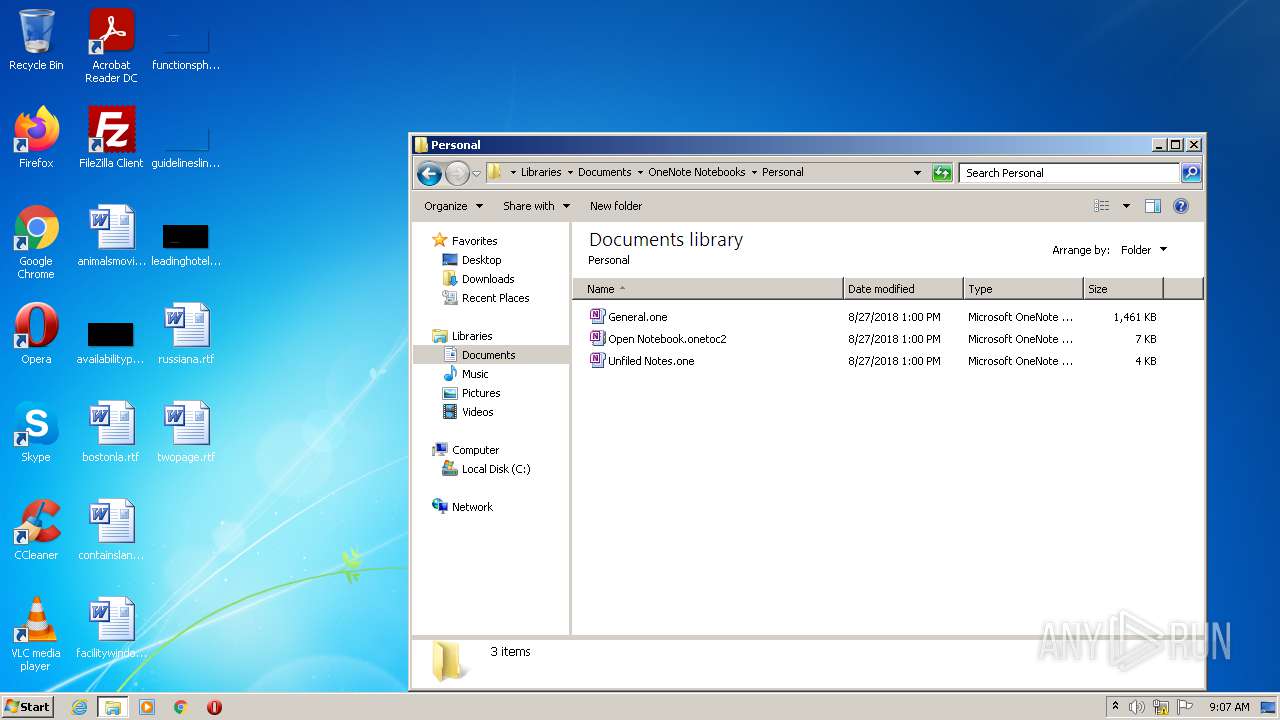
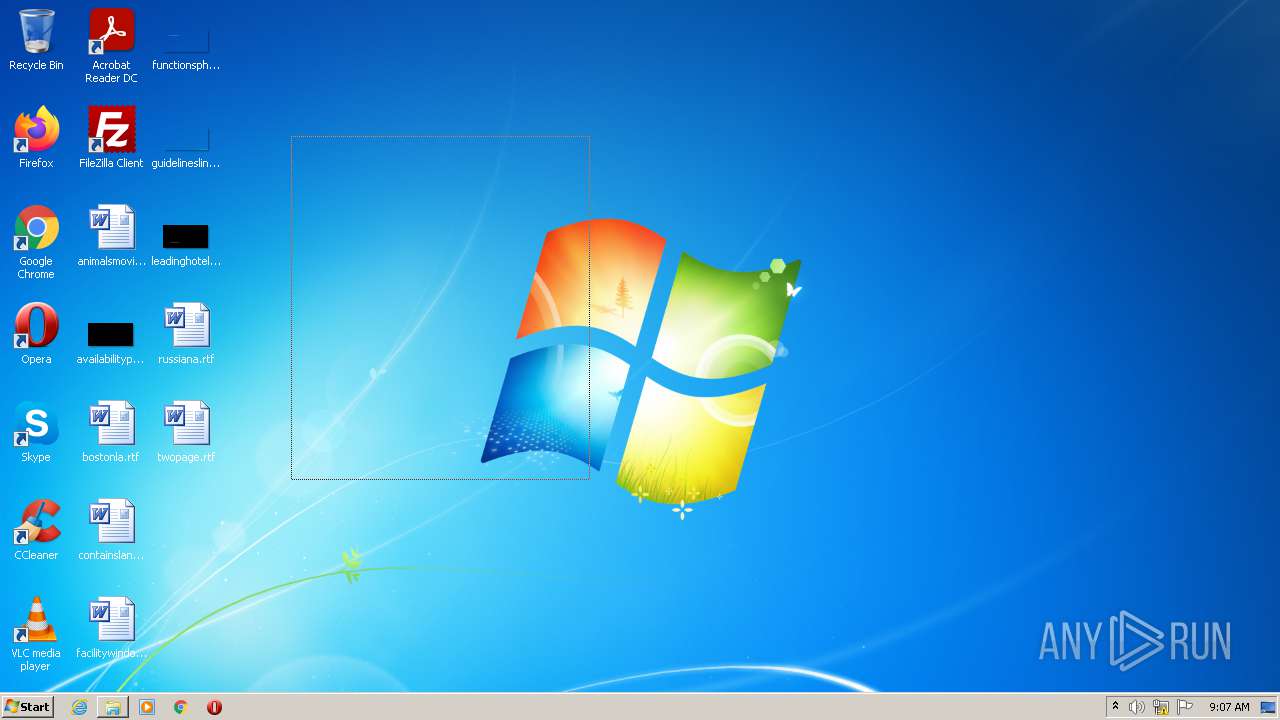
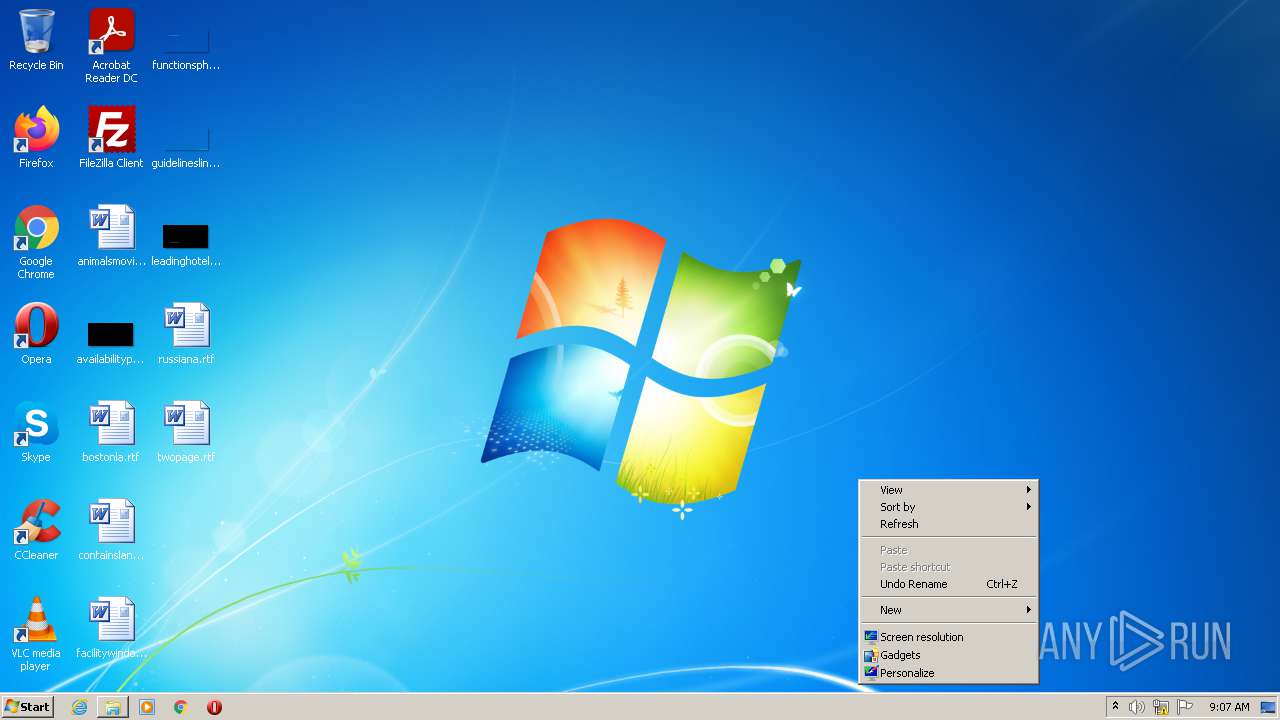
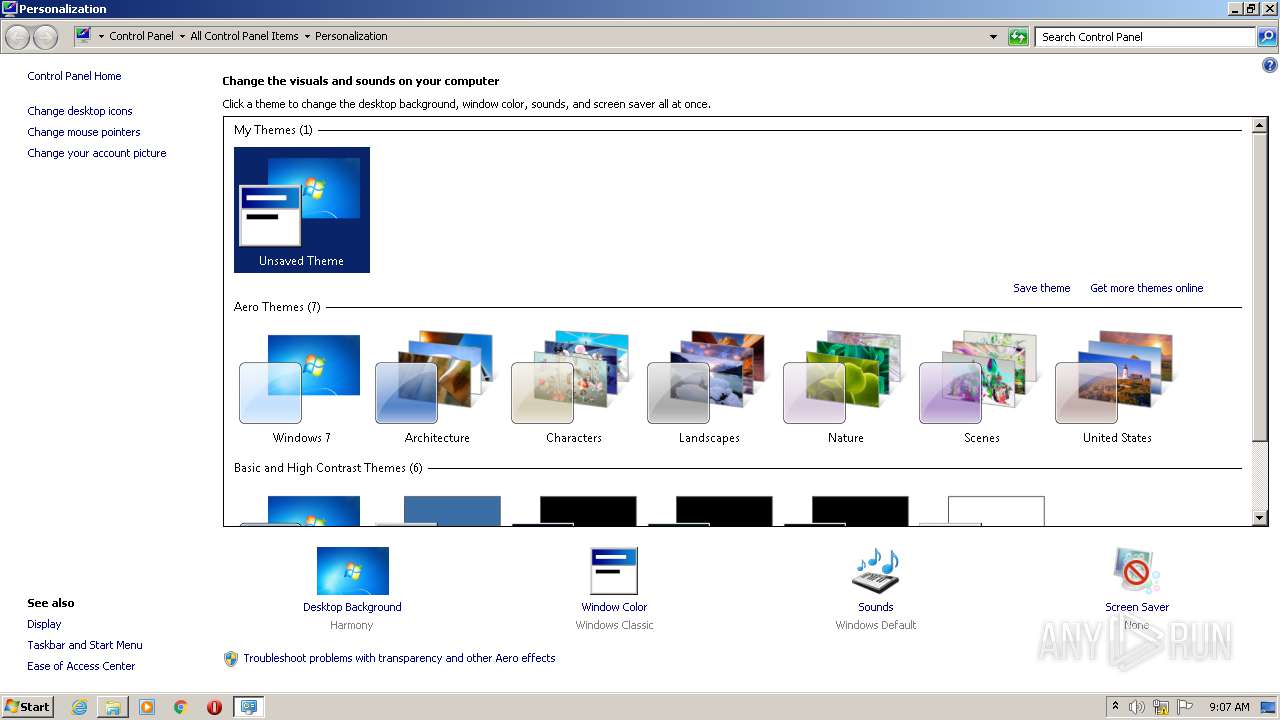
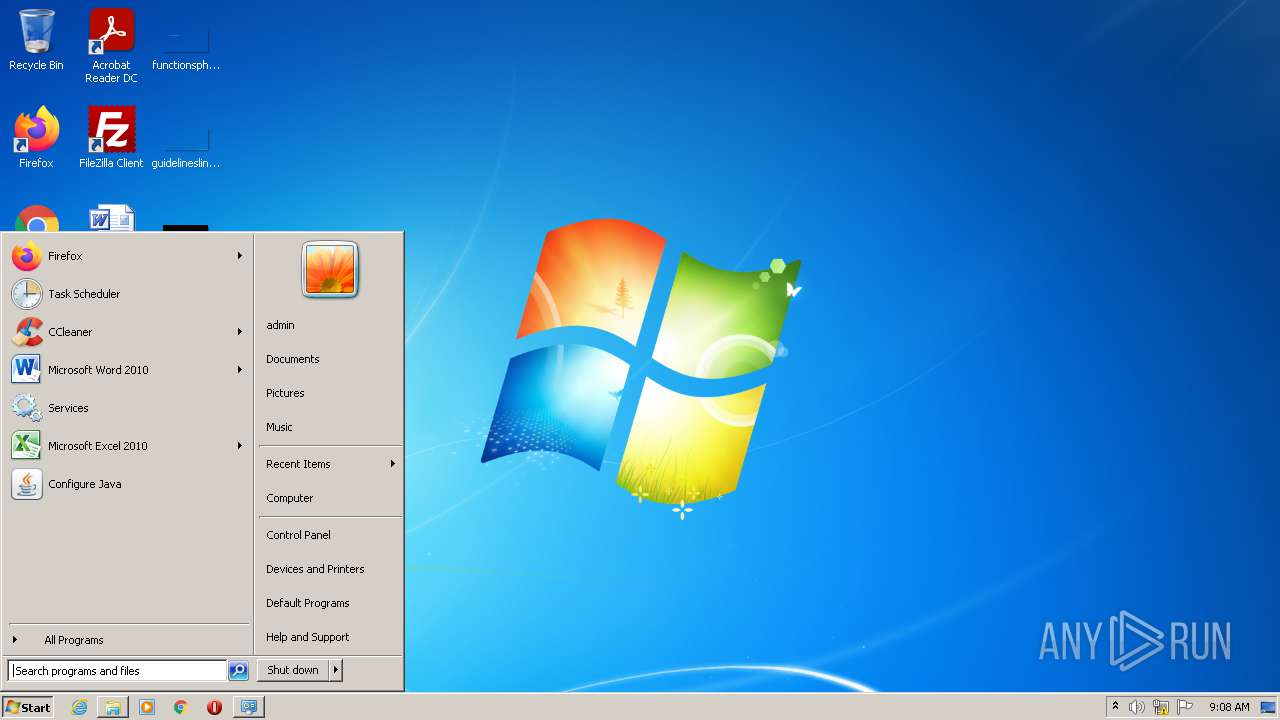
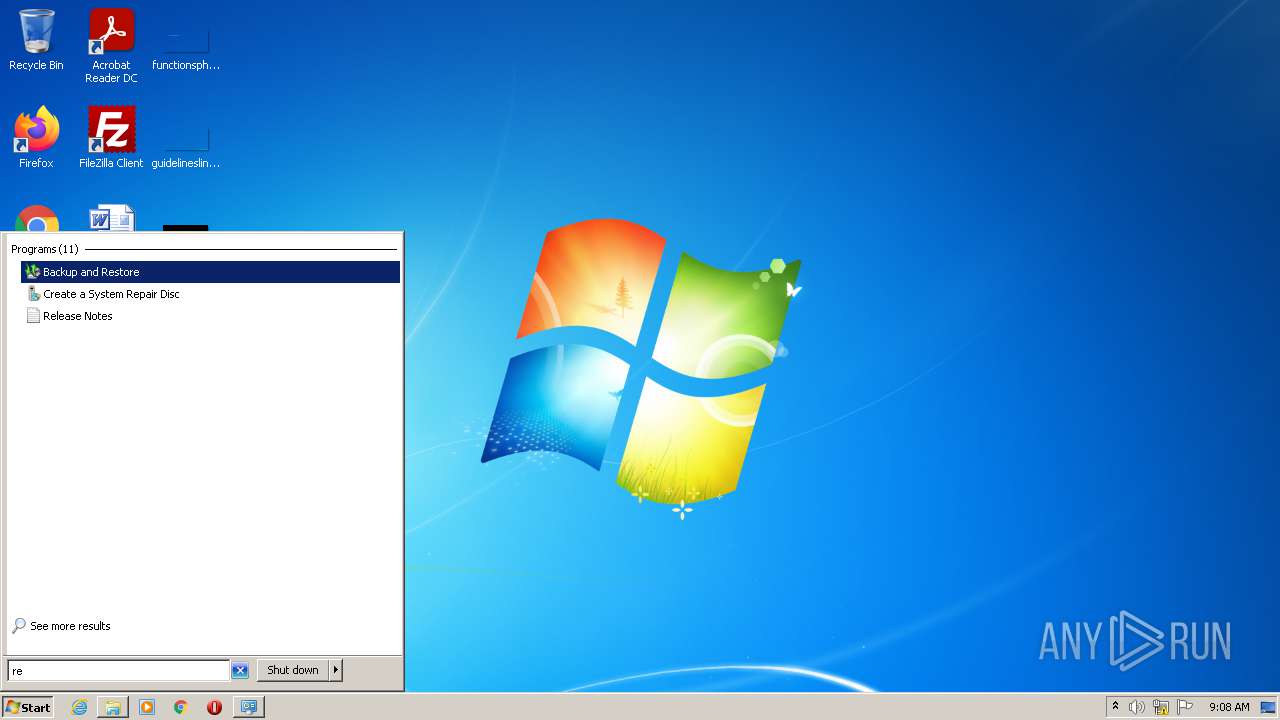
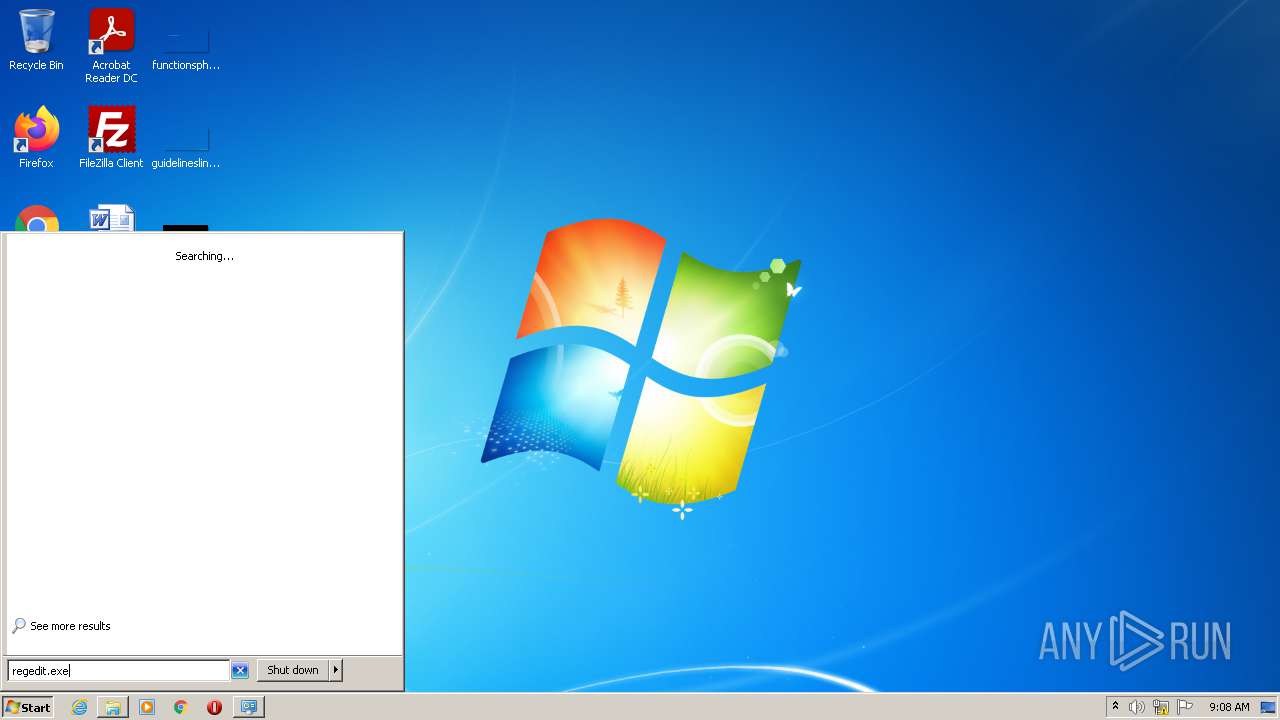
Manual execution by user
- explorer.exe (PID: 4092)
- regedit.exe (PID: 1128)
- regedit.exe (PID: 3172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:09:14 00:02:00+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 127488 |
| InitializedDataSize: | 117760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xead4 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.0.0 |
| ProductVersionNumber: | 6.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | AOMEI Technology Co., Ltd |
| FileDescription: | AOMEI Partition Assistant v6.0 |
| InternalName: | Partition Assistant |
| FileVersion: | 6.0.0.0 |
| LegalCopyright: | � AOMEI Technology Co., Ltd |
| ProductName: | AOMEI Partition Assistant v6.0 |
| ProductVersion: | 6.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Sep-2016 22:02:00 |
| Detected languages: |
|
| CompanyName: | AOMEI Technology Co., Ltd |
| FileDescription: | AOMEI Partition Assistant v6.0 |
| InternalName: | Partition Assistant |
| FileVersion: | 6.0.0.0 |
| LegalCopyright: | � AOMEI Technology Co., Ltd |
| ProductName: | AOMEI Partition Assistant v6.0 |
| ProductVersion: | 6.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 13-Sep-2016 22:02:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F0A6 | 0x0001F200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.72963 |
.rdata | 0x00021000 | 0x00006510 | 0x00006600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.24916 |
.data | 0x00028000 | 0x000126D8 | 0x00010800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.77767 |
.rsrc | 0x0003B000 | 0x00197DF8 | 0x00005E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.37699 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
4 | 2.56318 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
5 | 2.6949 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
305 | 2.97219 | 512 | Latin 1 / Western European | English - United States | RT_DIALOG |
306 | 3.10966 | 248 | Latin 1 / Western European | English - United States | RT_DIALOG |
307 | 2.79455 | 160 | Latin 1 / Western European | English - United States | RT_DIALOG |
311 | 3.06584 | 238 | Latin 1 / Western European | English - United States | RT_DIALOG |
1093 | 1.91924 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
4039 | 3.34089 | 740 | Latin 1 / Western European | English - United States | RT_STRING |
4040 | 3.32816 | 824 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
CRYPT32.dll |
CRYPTUI.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
MSIMG32.dll |
OLEAUT32.dll |
Total processes
44
Monitored processes
4
Malicious processes
1
Suspicious processes
0
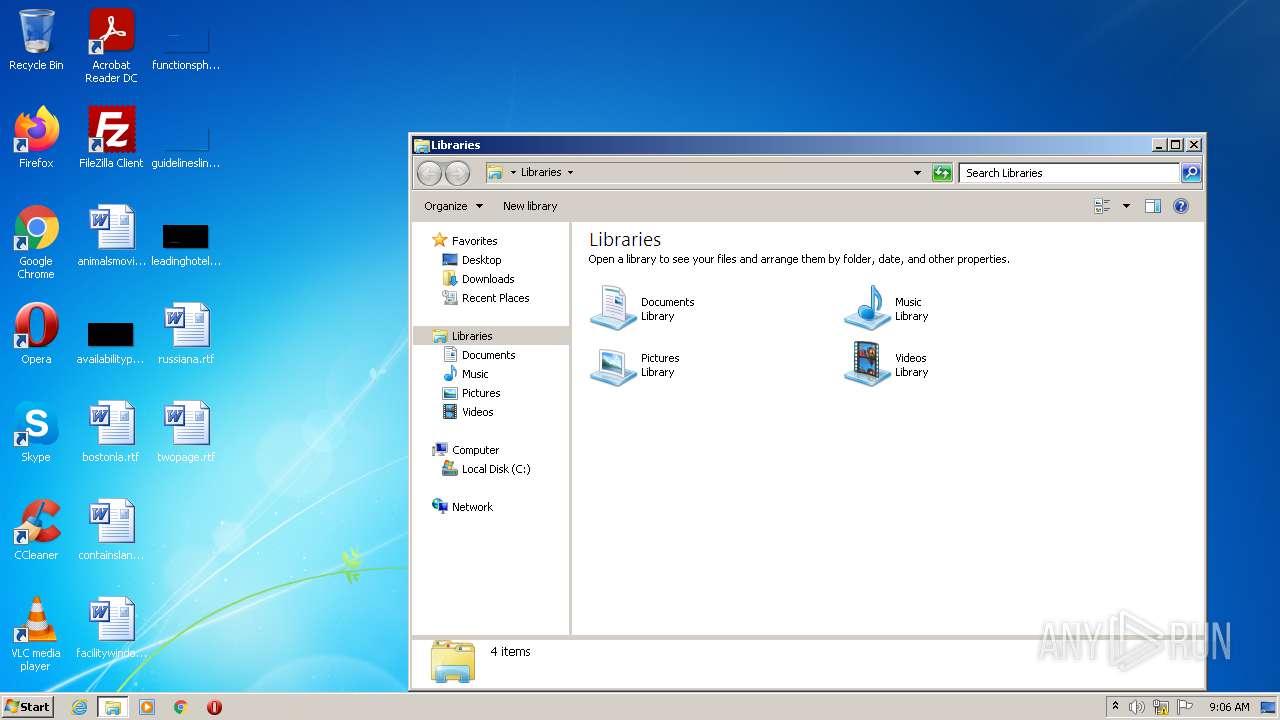
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1128 | "C:\Windows\regedit.exe" | C:\Windows\regedit.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3172 | "C:\Windows\regedit.exe" | C:\Windows\regedit.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3816 | "C:\Users\admin\AppData\Local\Temp\AOMEI.exe" | C:\Users\admin\AppData\Local\Temp\AOMEI.exe | — | Explorer.EXE | |||||||||||
User: admin Company: AOMEI Technology Co., Ltd Integrity Level: MEDIUM Description: AOMEI Partition Assistant v6.0 Exit code: 0 Version: 6.0.0.0 Modules
| |||||||||||||||
| 4092 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 048
Read events
2 039
Write events
9
Delete events
0
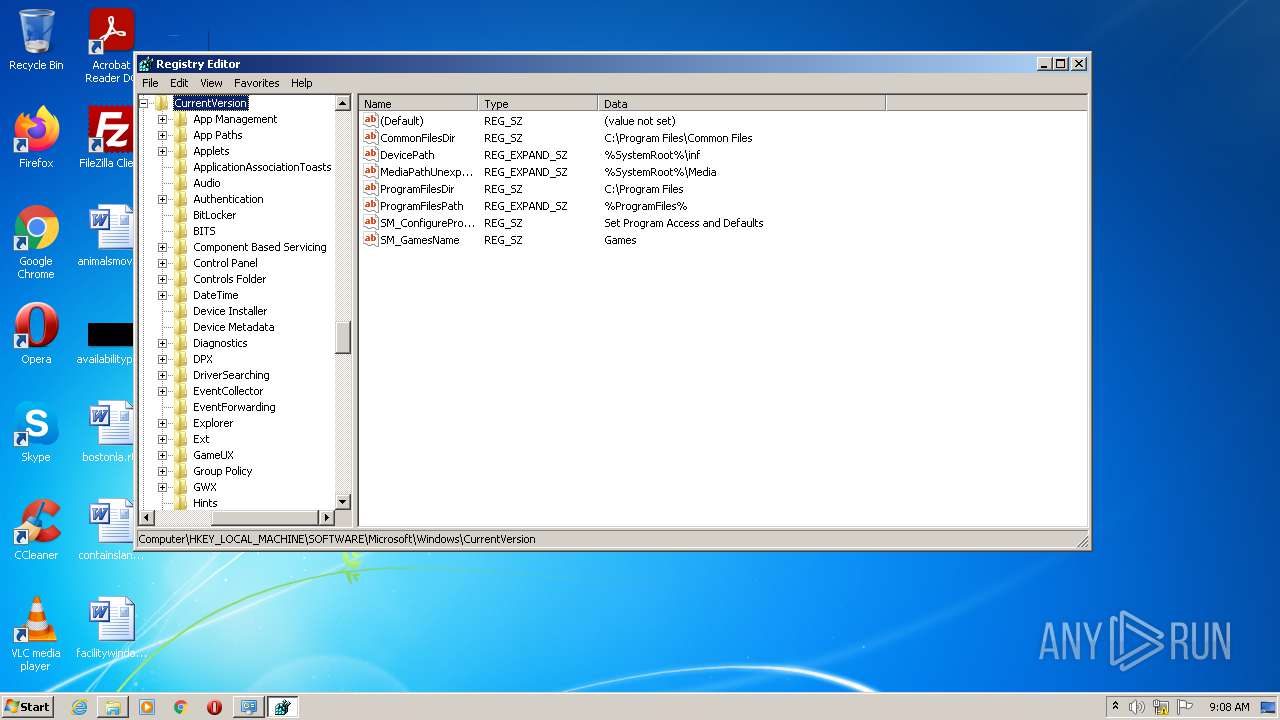
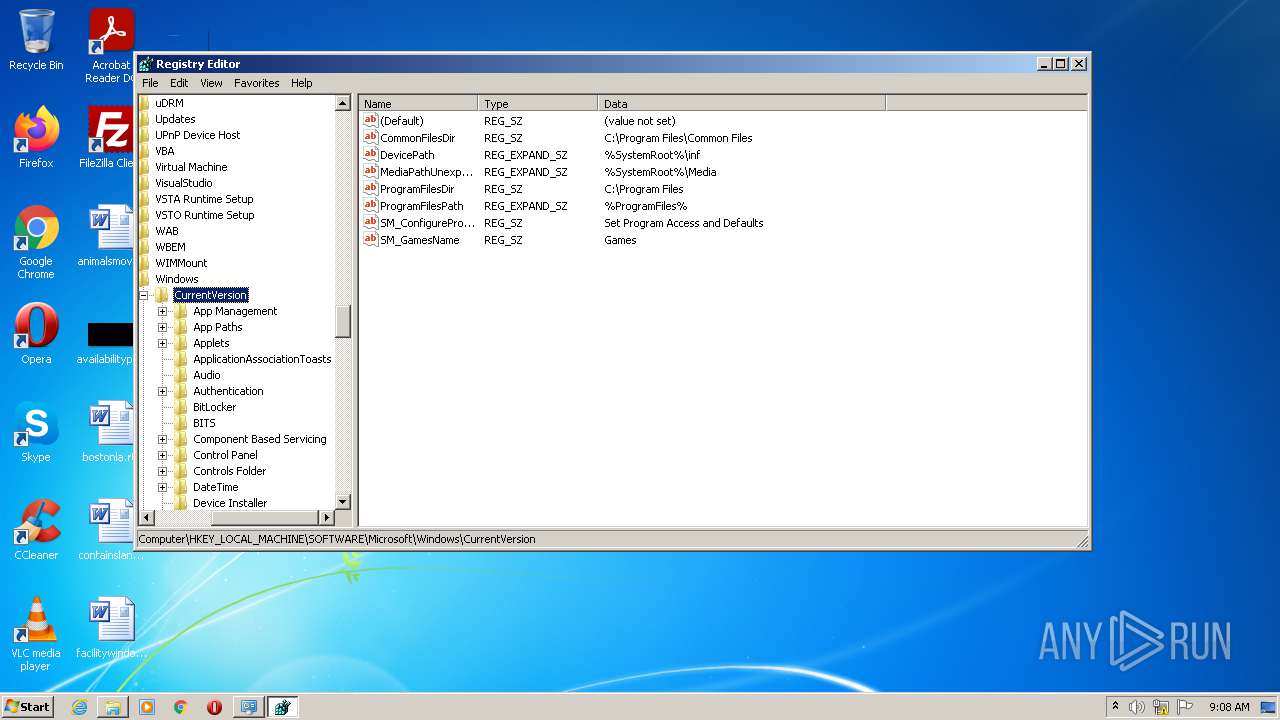
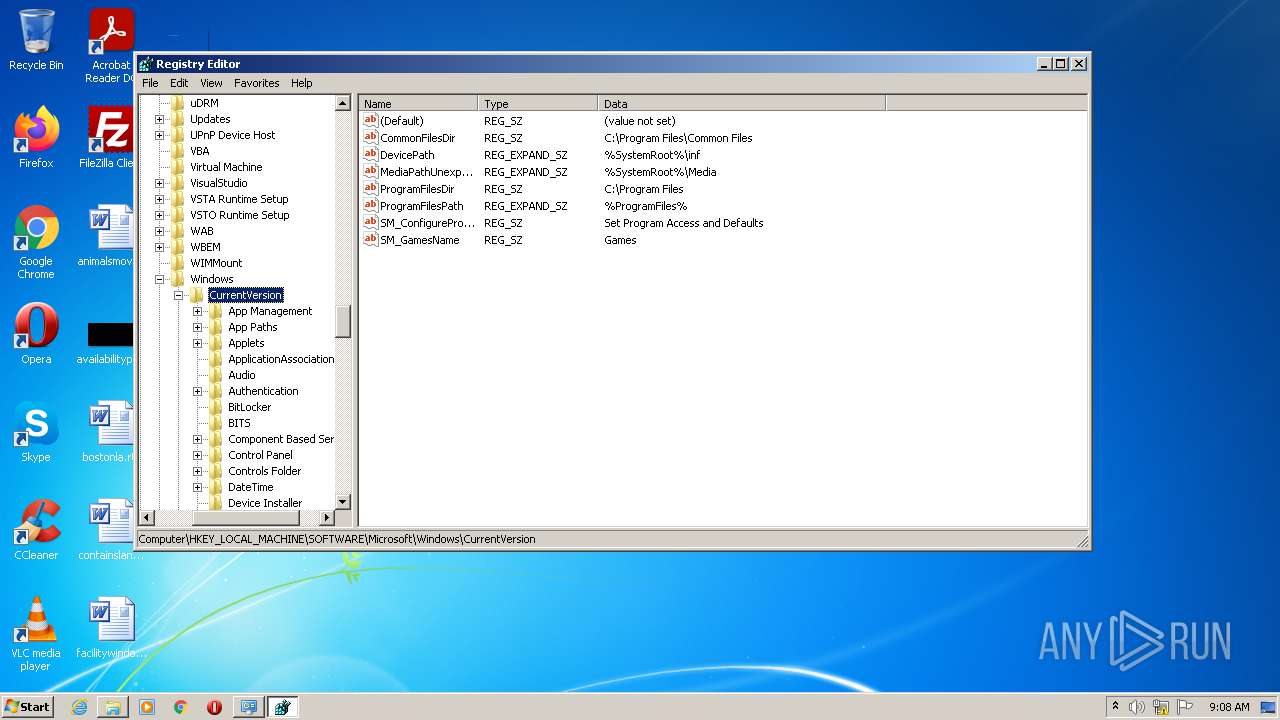
Modification events
| (PID) Process: | (3816) AOMEI.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 1 | |||
| (PID) Process: | (3816) AOMEI.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000020000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3816) AOMEI.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003C010000020000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3816) AOMEI.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003D010000020000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
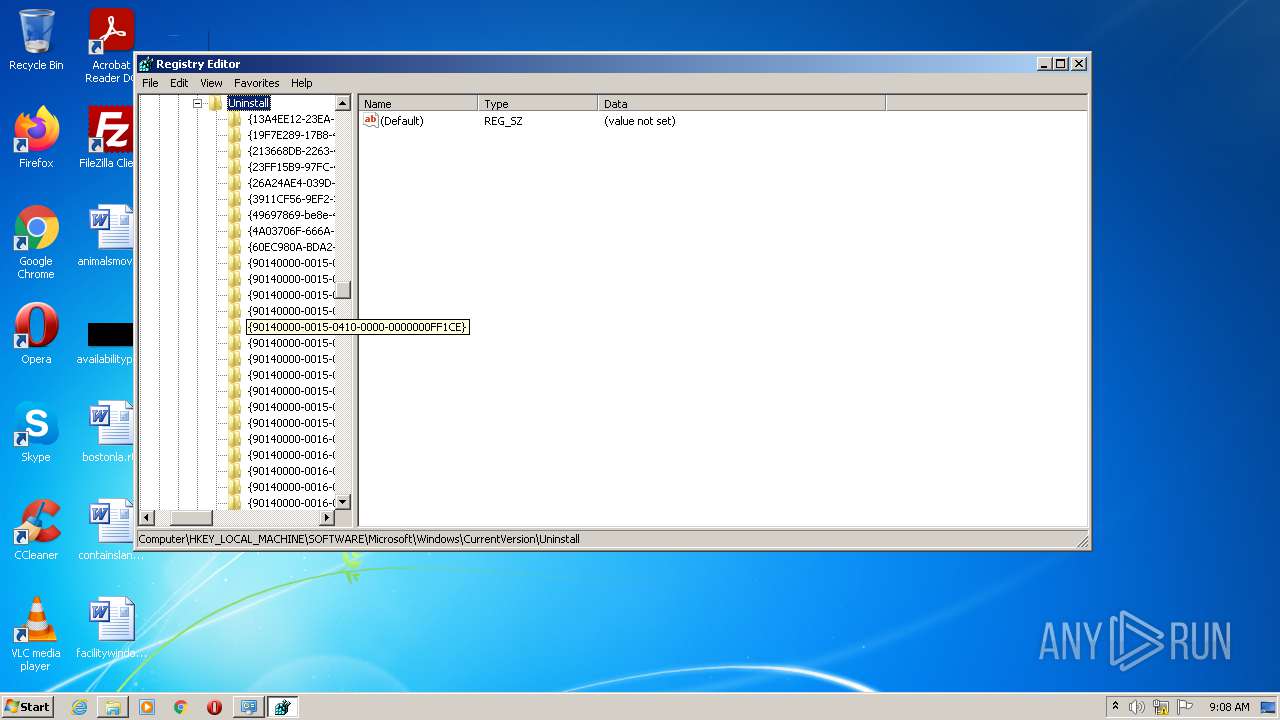
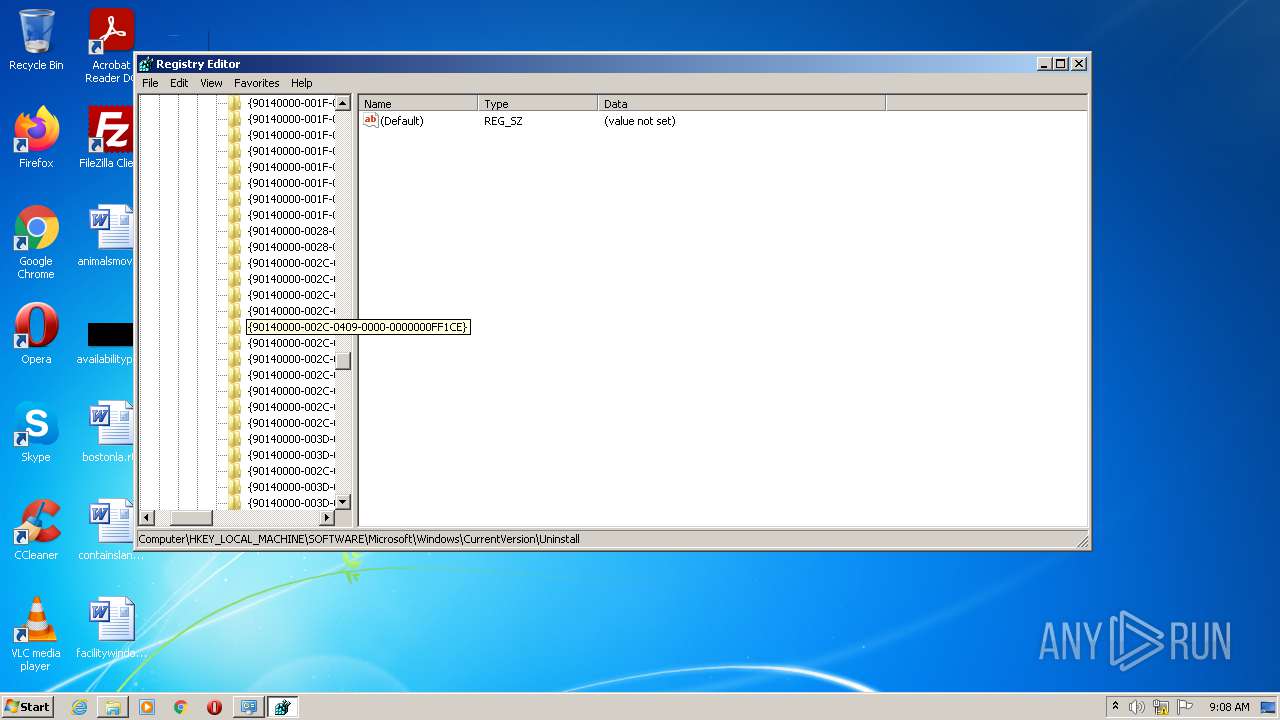
| (PID) Process: | (1128) regedit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Applets\Regedit |
| Operation: | write | Name: | View |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF85000000330000004504000028020000D800000078000000780000002001000001000000 | |||
| (PID) Process: | (1128) regedit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Applets\Regedit |
| Operation: | write | Name: | FindFlags |
Value: 14 | |||
| (PID) Process: | (1128) regedit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Applets\Regedit |
| Operation: | write | Name: | LastKey |
Value: Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
207
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
z8d6votuf496.net |
| unknown |
kde7wlqfg12z.org |
| unknown |
d2vk9in09iz4.top |
| unknown |
mz4pynch23s1.org |
| unknown |
7clefc5a30pu.org |
| unknown |
sdi7o9yzw96b.net |
| unknown |
d2roxq3glav4.top |
| unknown |
ez4par0hm38h.top |
| unknown |
nkhmf8h6ngdu.net |
| unknown |
4hqno9uz0pev.top |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |