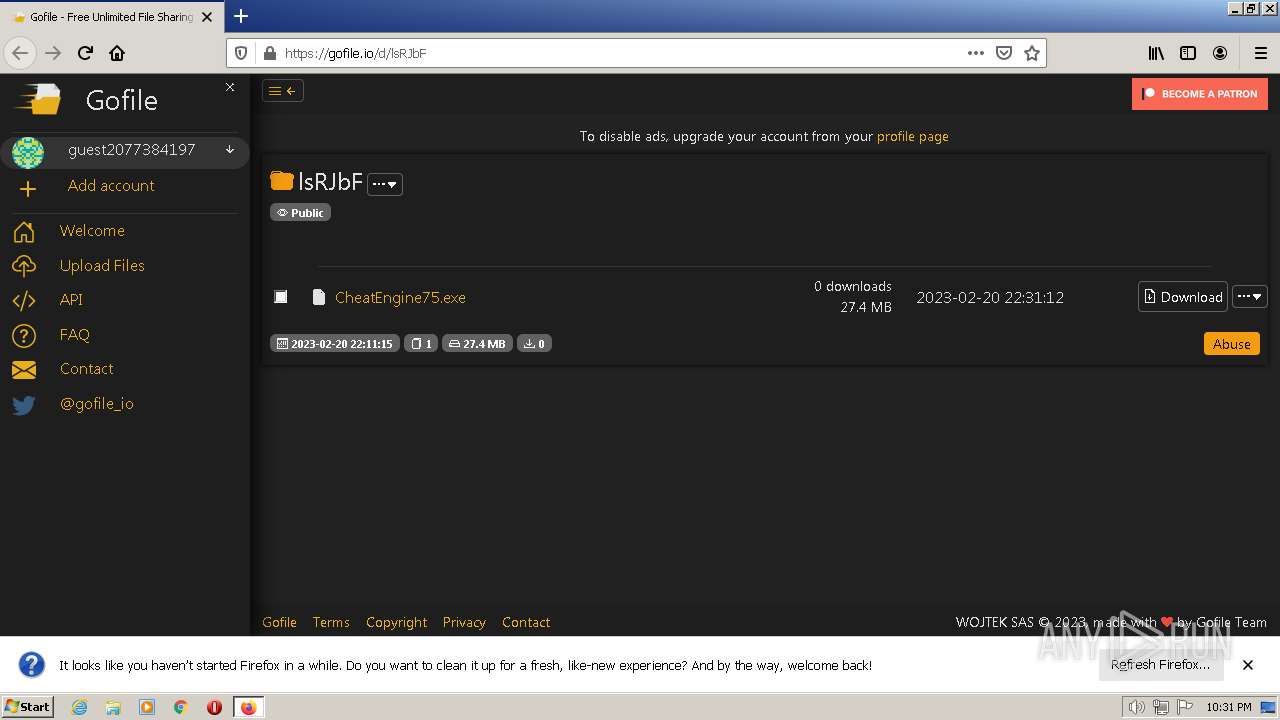
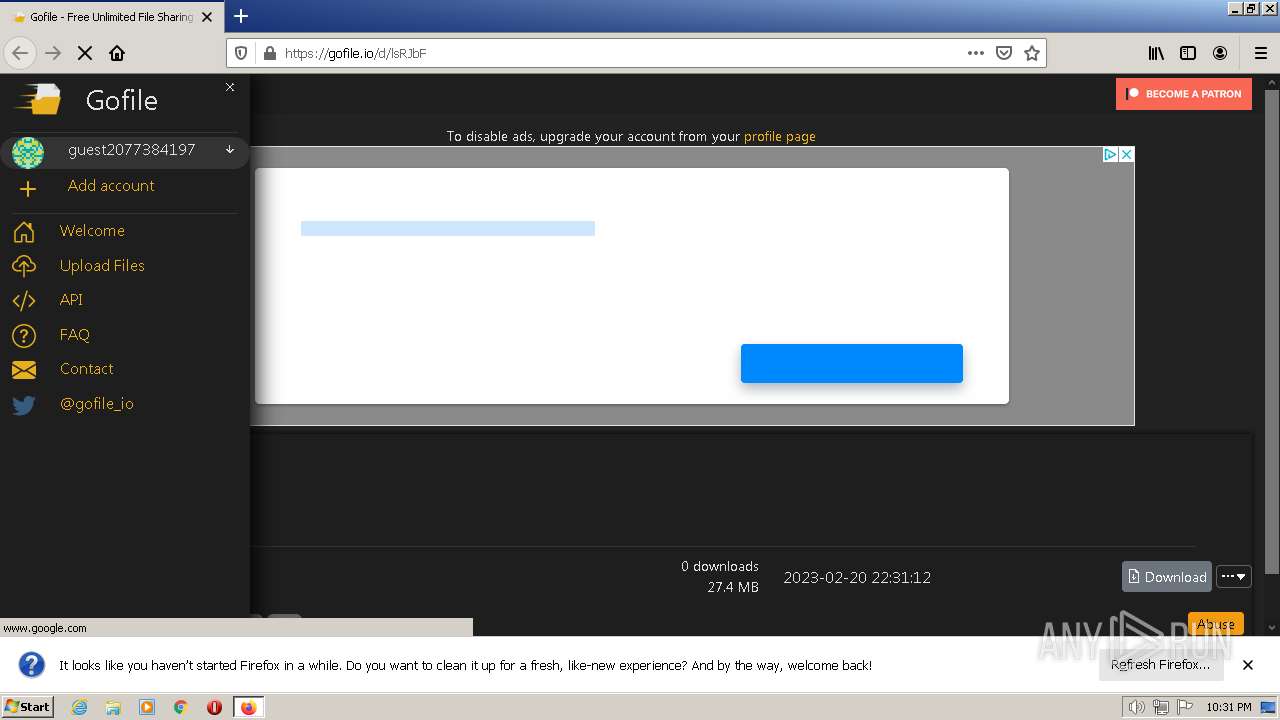
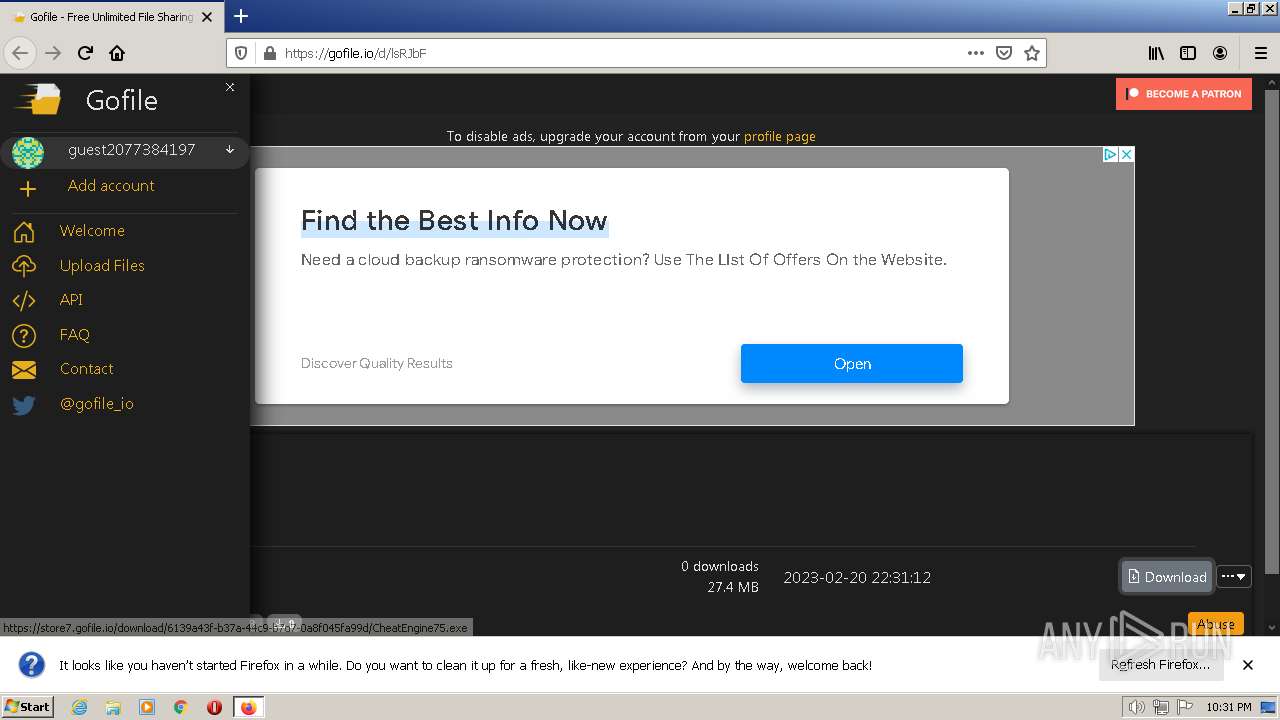
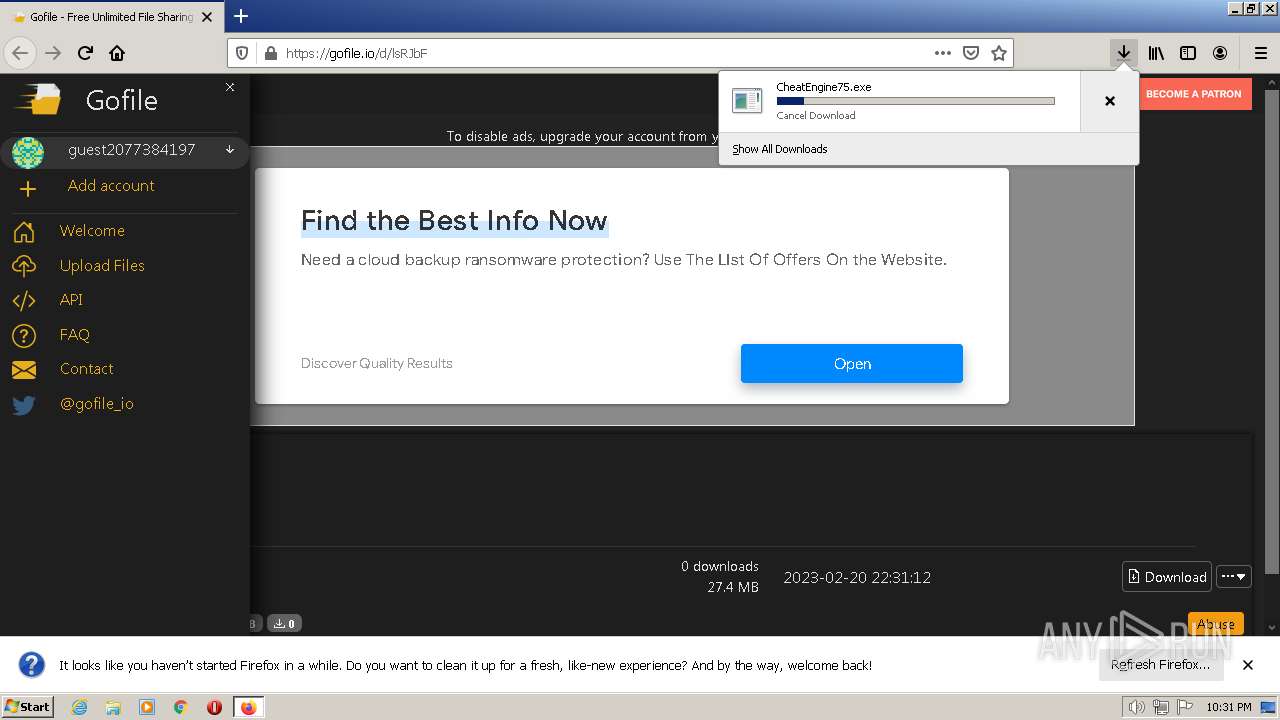
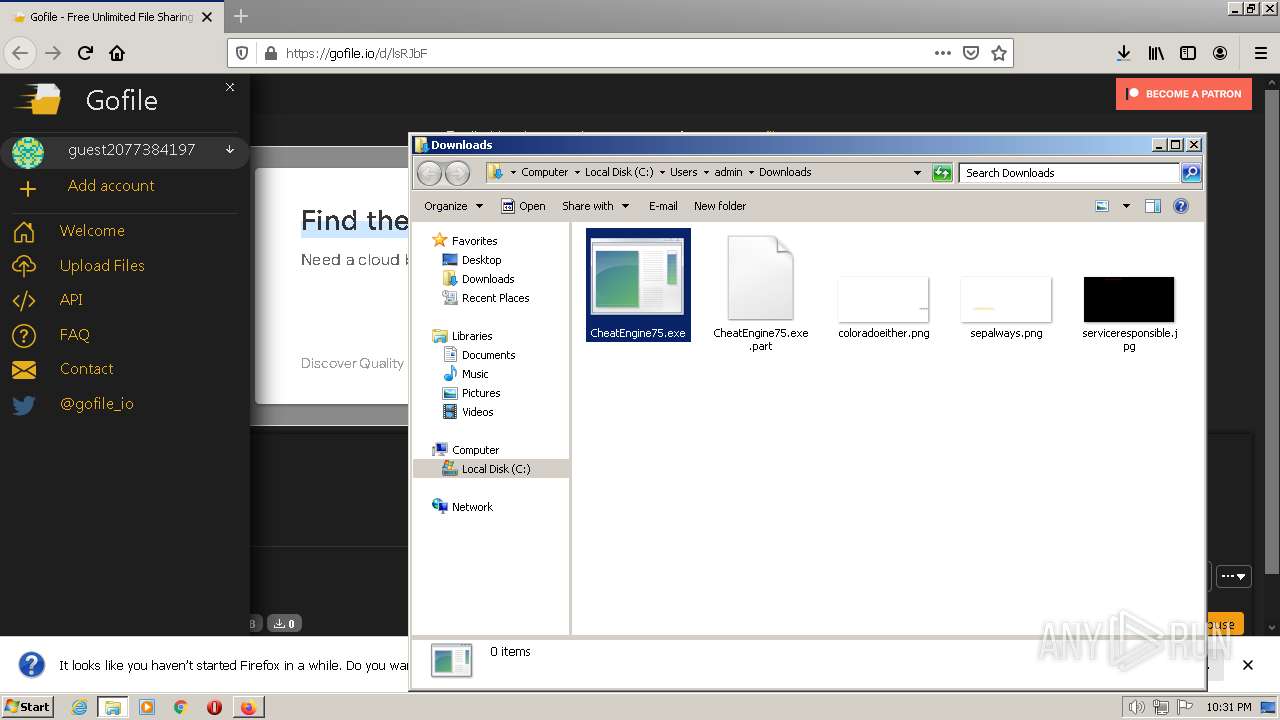
| URL: | https://gofile.io/d/lsRJbF |
| Full analysis: | https://app.any.run/tasks/008bfbdb-7ba7-43df-a6ea-f2b7ae458f74 |
| Verdict: | Malicious activity |
| Analysis date: | February 20, 2023, 22:31:25 |
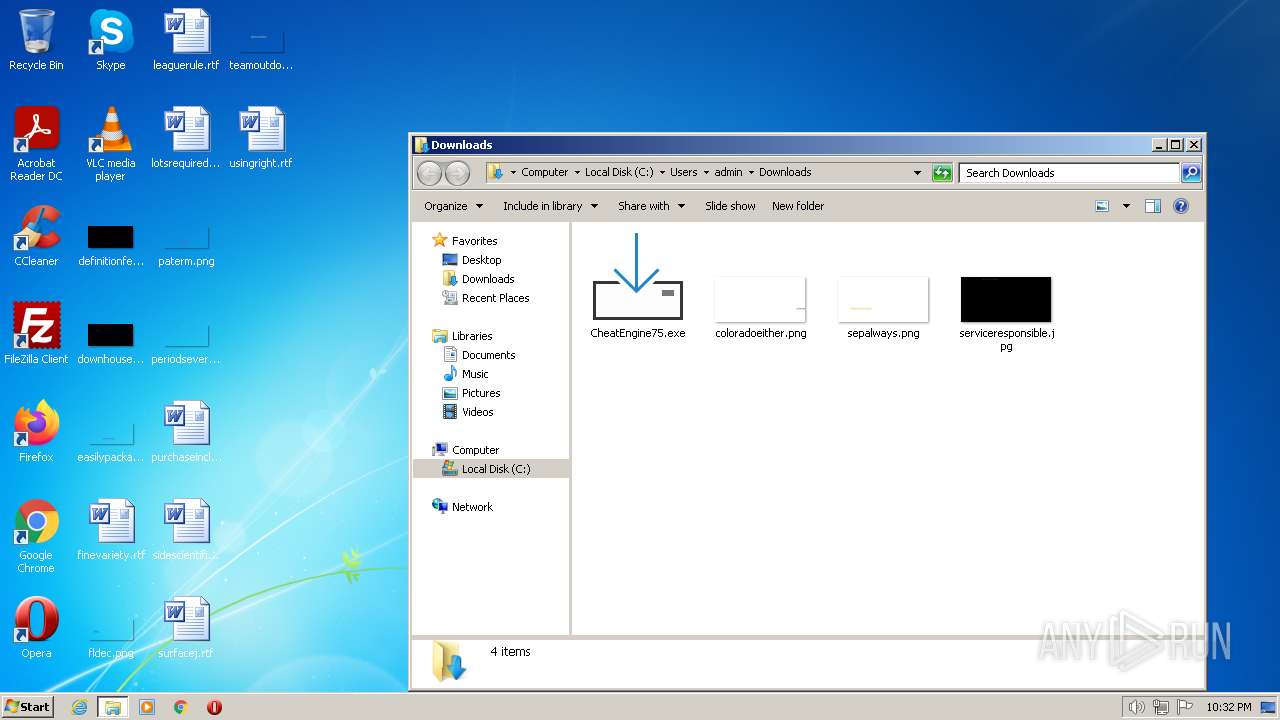
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 73FC0C1B6333FCD01C3FD0C56BB116BF |
| SHA1: | 8BDCE295C0E09556F0B14BCCAA58270EC50E2AD4 |
| SHA256: | 25F6B15C0816F68F3FCACEA49F3DC2D0A0D97F620F5B40CE3DFFC41CBB46F69B |
| SSDEEP: | 3:N8rxL1YfD:2Z+ |
MALICIOUS
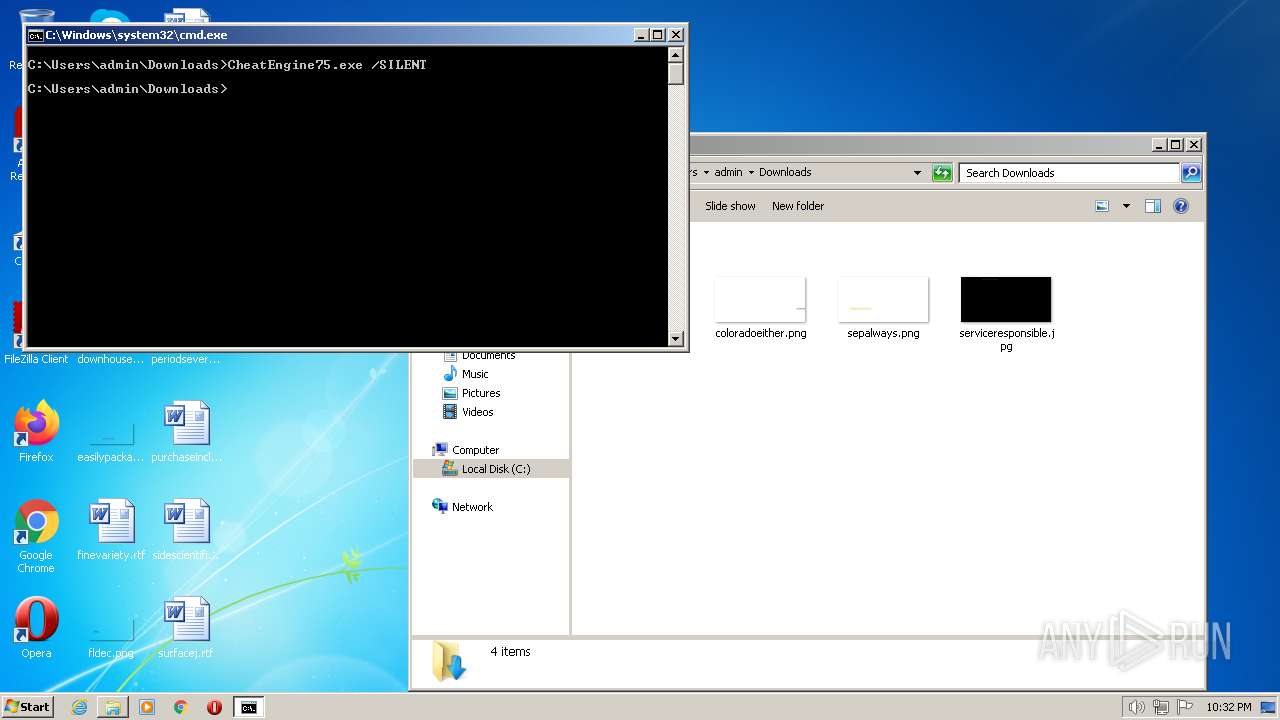
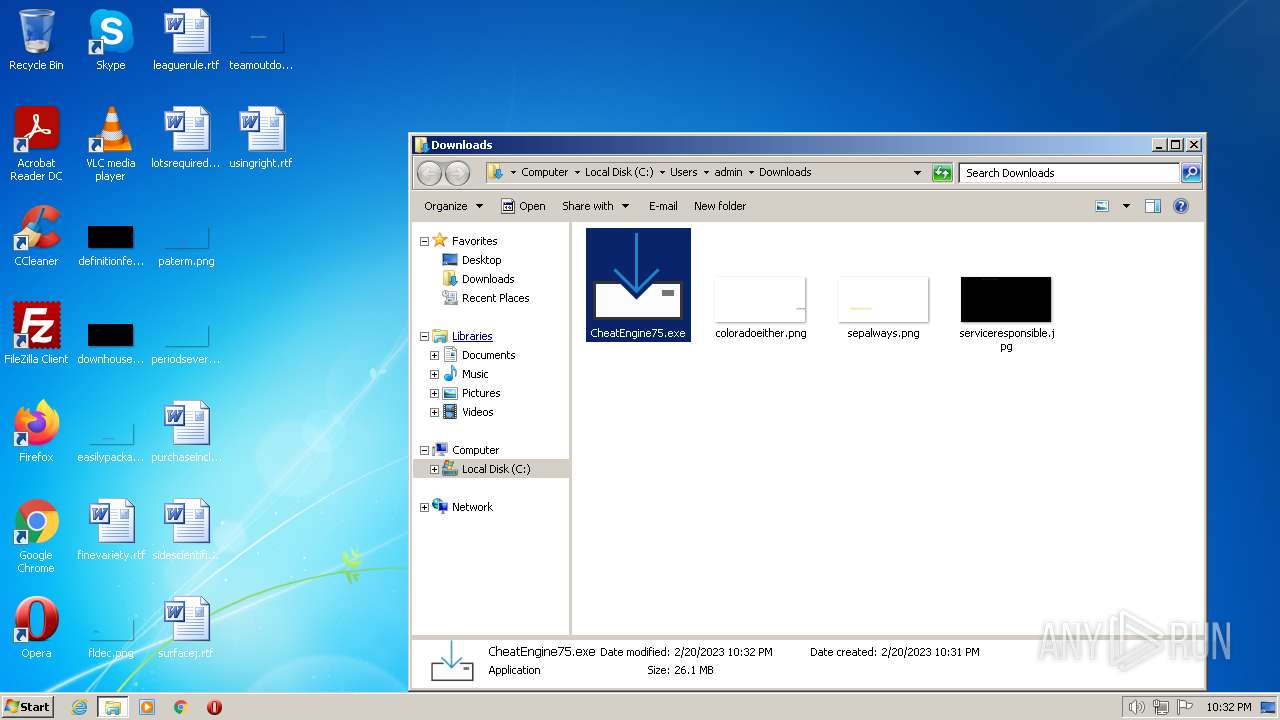
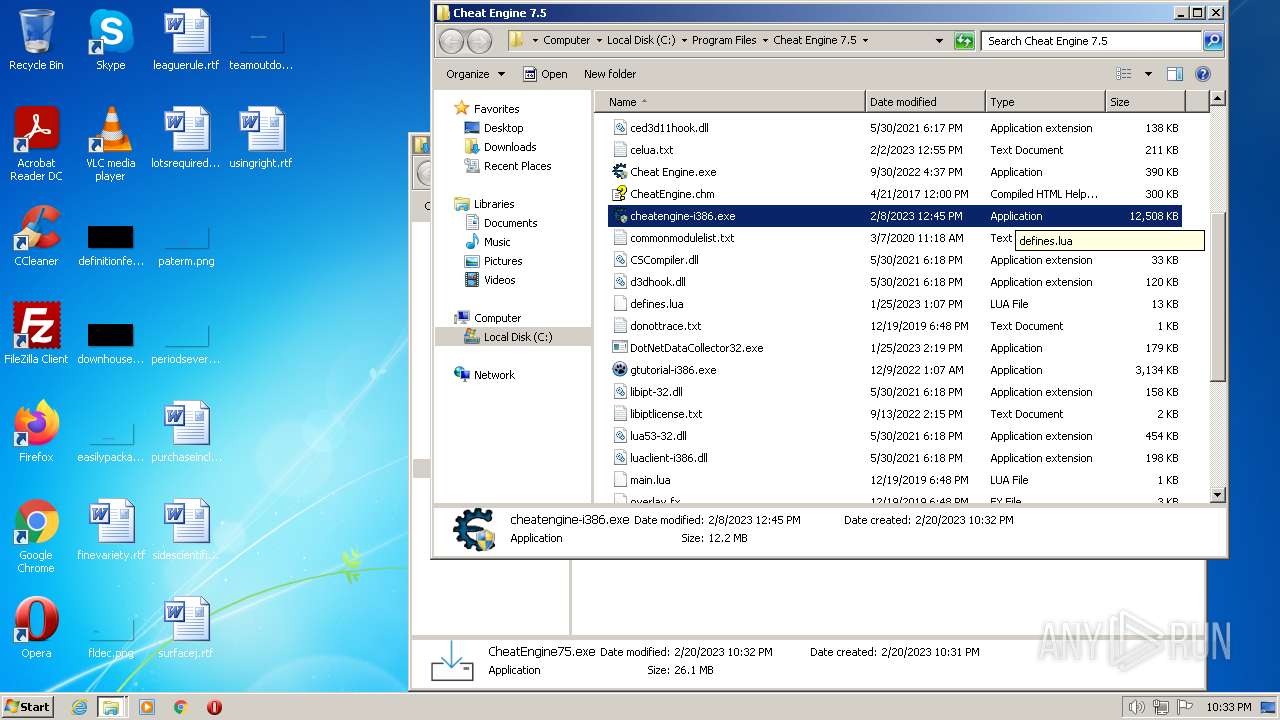
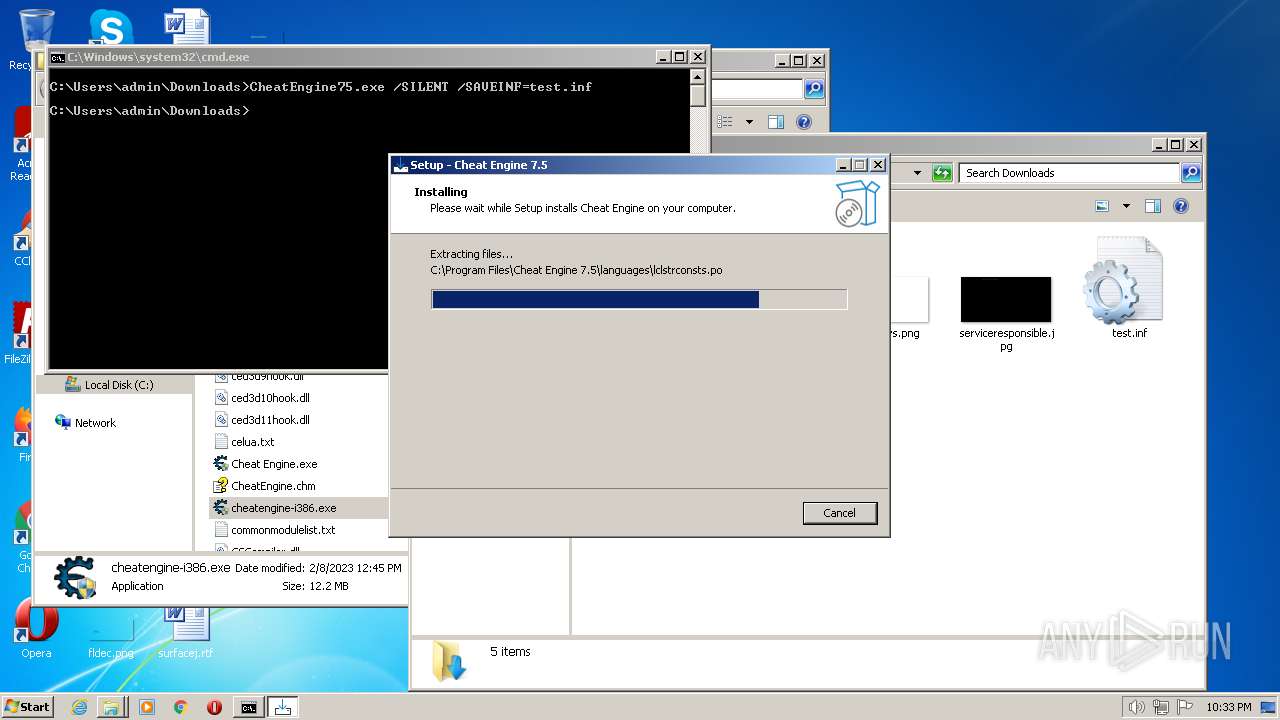
Drops the executable file immediately after the start
- CheatEngine75.exe (PID: 3508)
- CheatEngine75.exe (PID: 3408)
- CheatEngine75.exe (PID: 3024)
- CheatEngine75.tmp (PID: 124)
- CheatEngine75.exe (PID: 376)
- CheatEngine75.exe (PID: 2756)
- CheatEngine75.exe (PID: 3488)
- CheatEngine75.tmp (PID: 3636)
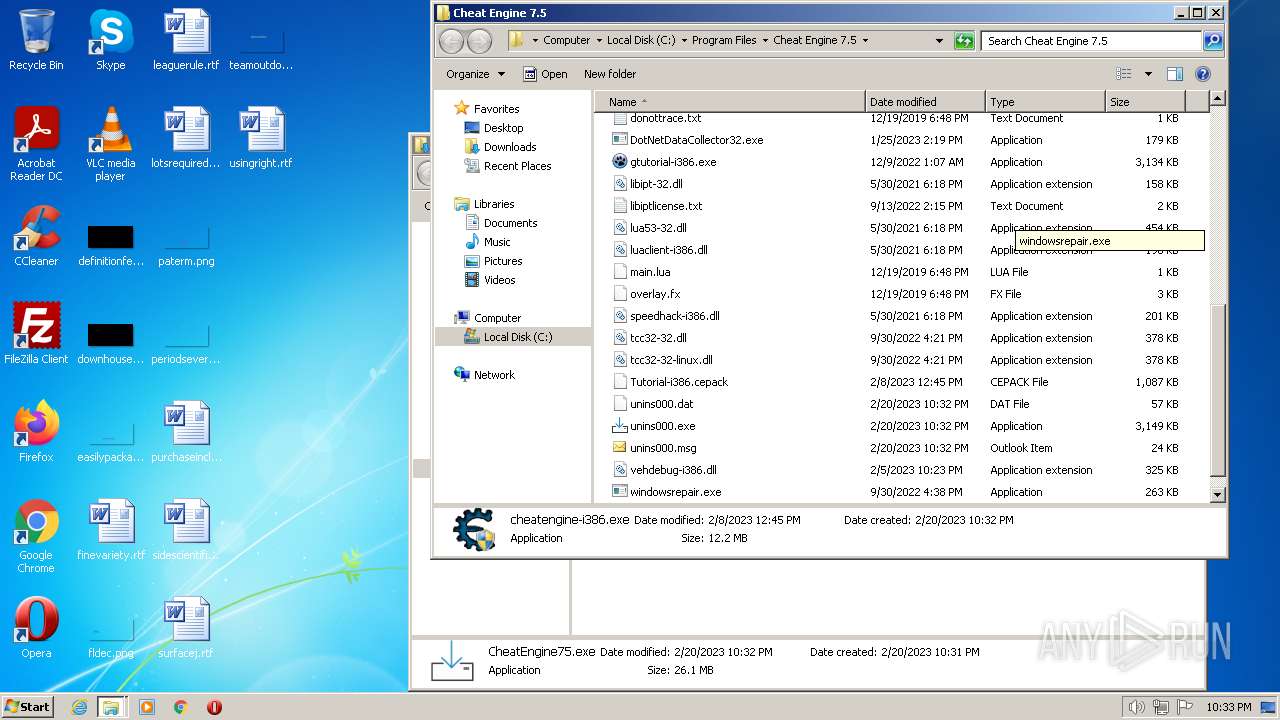
Application was dropped or rewritten from another process
- CheatEngine75.exe (PID: 3408)
- CheatEngine75.exe (PID: 3508)
- windowsrepair.exe (PID: 2808)
- CheatEngine75.exe (PID: 3024)
- CheatEngine75.exe (PID: 376)
- CheatEngine75.exe (PID: 2756)
- CheatEngine75.exe (PID: 3488)
- windowsrepair.exe (PID: 2640)
Starts NET.EXE for service management
- net.exe (PID: 1000)
- net.exe (PID: 3072)
- CheatEngine75.tmp (PID: 124)
- net.exe (PID: 2512)
- CheatEngine75.tmp (PID: 3636)
- net.exe (PID: 3616)
SUSPICIOUS
Executable content was dropped or overwritten
- CheatEngine75.exe (PID: 3508)
- CheatEngine75.exe (PID: 3408)
- CheatEngine75.exe (PID: 3024)
- CheatEngine75.exe (PID: 376)
- CheatEngine75.tmp (PID: 124)
- CheatEngine75.exe (PID: 2756)
- CheatEngine75.exe (PID: 3488)
- CheatEngine75.tmp (PID: 3636)
Reads the Windows owner or organization settings
- CheatEngine75.tmp (PID: 124)
- CheatEngine75.tmp (PID: 1668)
- CheatEngine75.tmp (PID: 3636)
Starts SC.EXE for service management
- CheatEngine75.tmp (PID: 124)
- CheatEngine75.tmp (PID: 3636)
Uses ICACLS.EXE to modify access control lists
- CheatEngine75.tmp (PID: 124)
- CheatEngine75.tmp (PID: 3636)
Changes default file association
- CheatEngine75.tmp (PID: 124)
Drops a file with too old compile date
- CheatEngine75.tmp (PID: 124)
- CheatEngine75.tmp (PID: 3636)
Searches for installed software
- CheatEngine75.tmp (PID: 1668)
- CheatEngine75.tmp (PID: 3636)
INFO
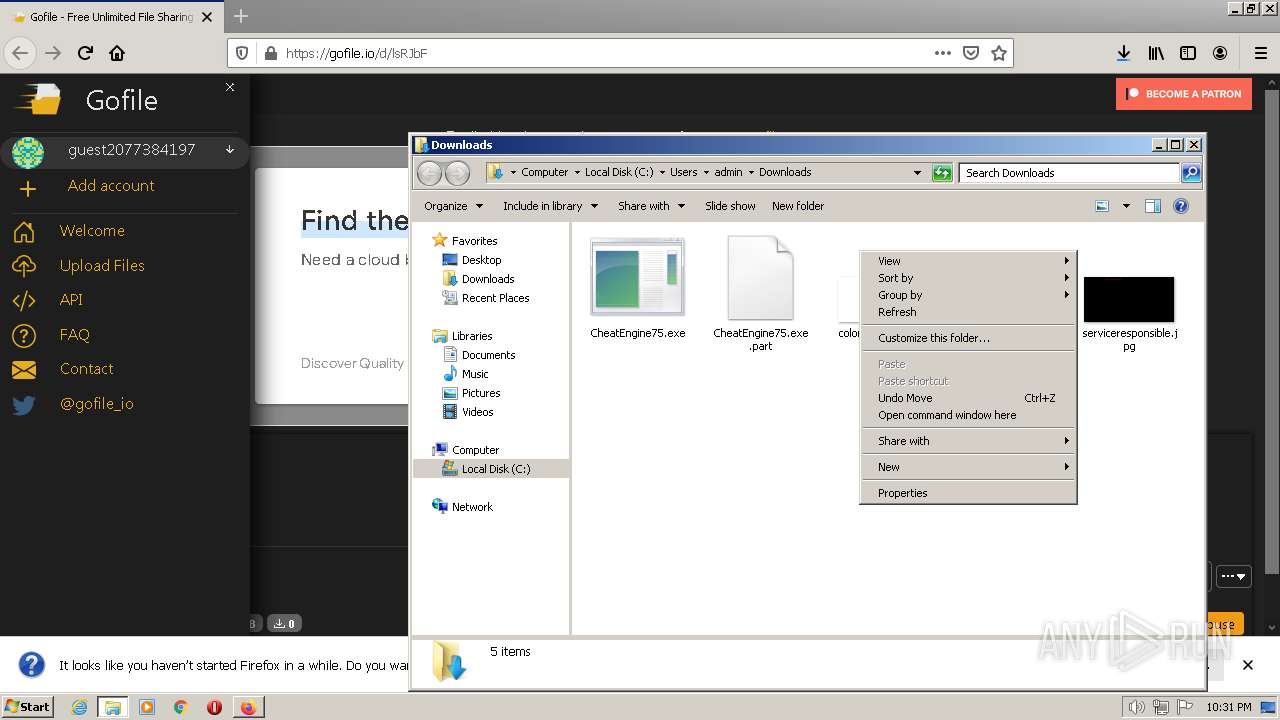
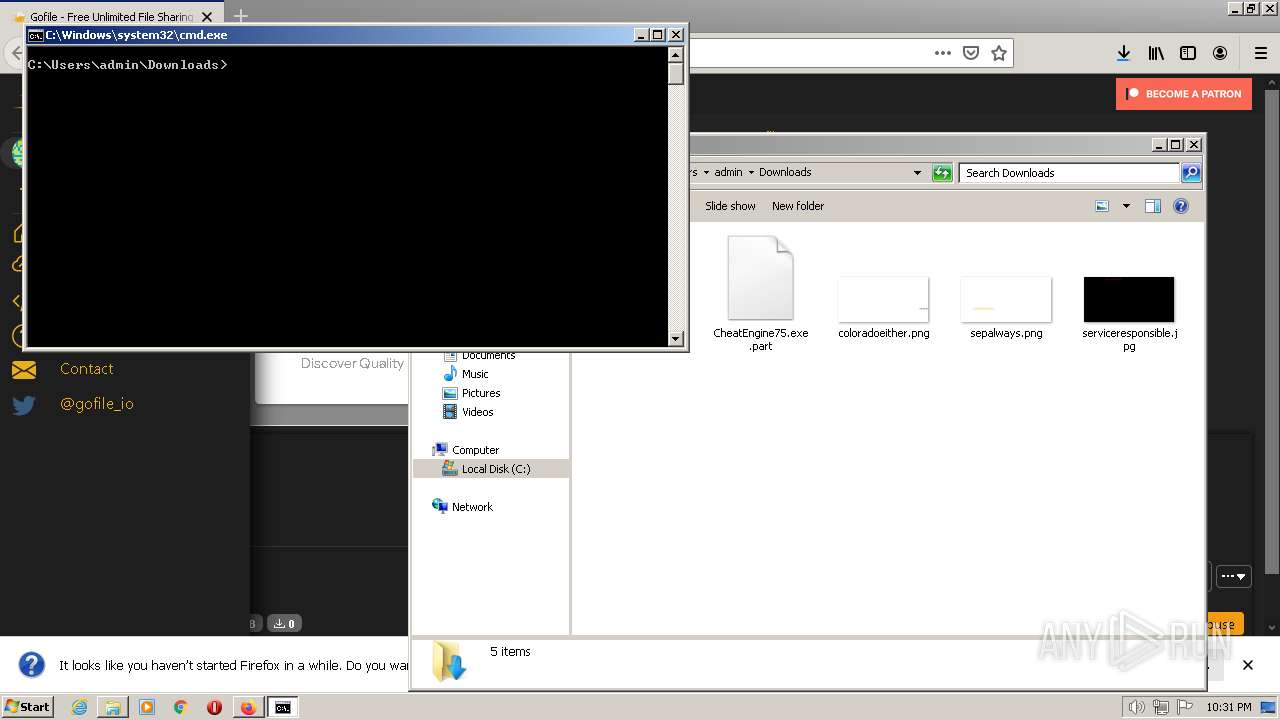
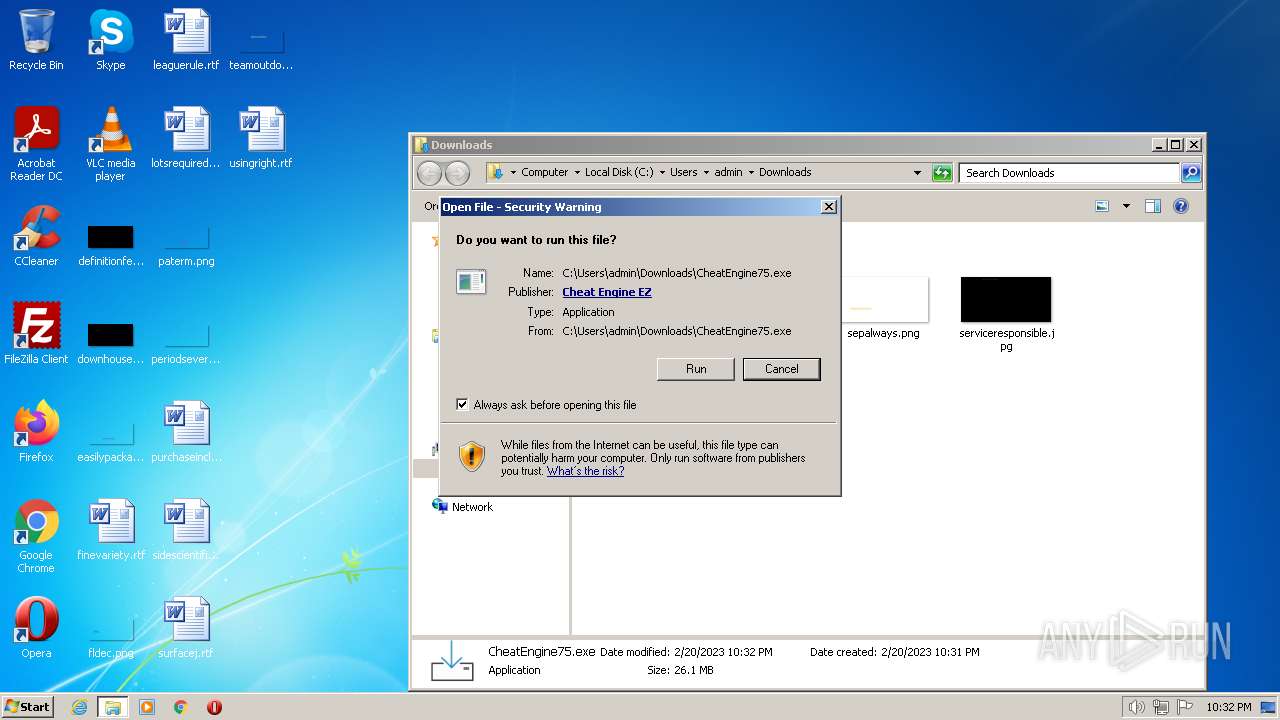
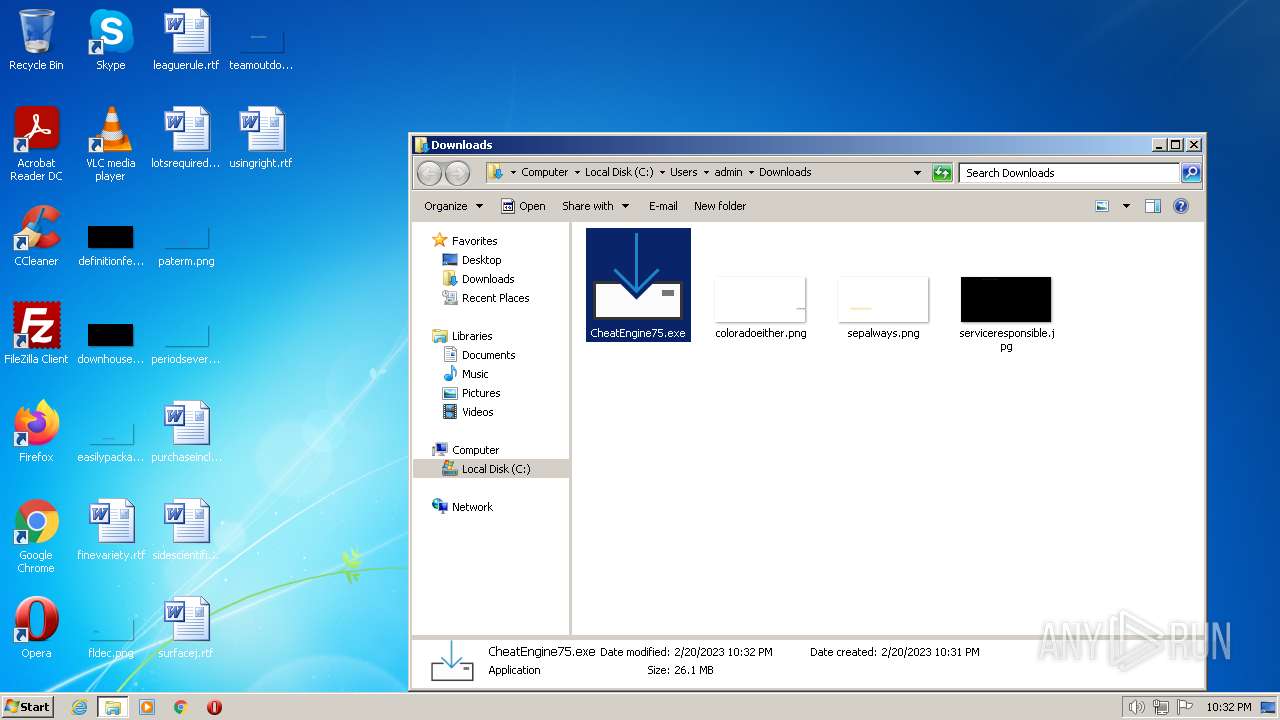
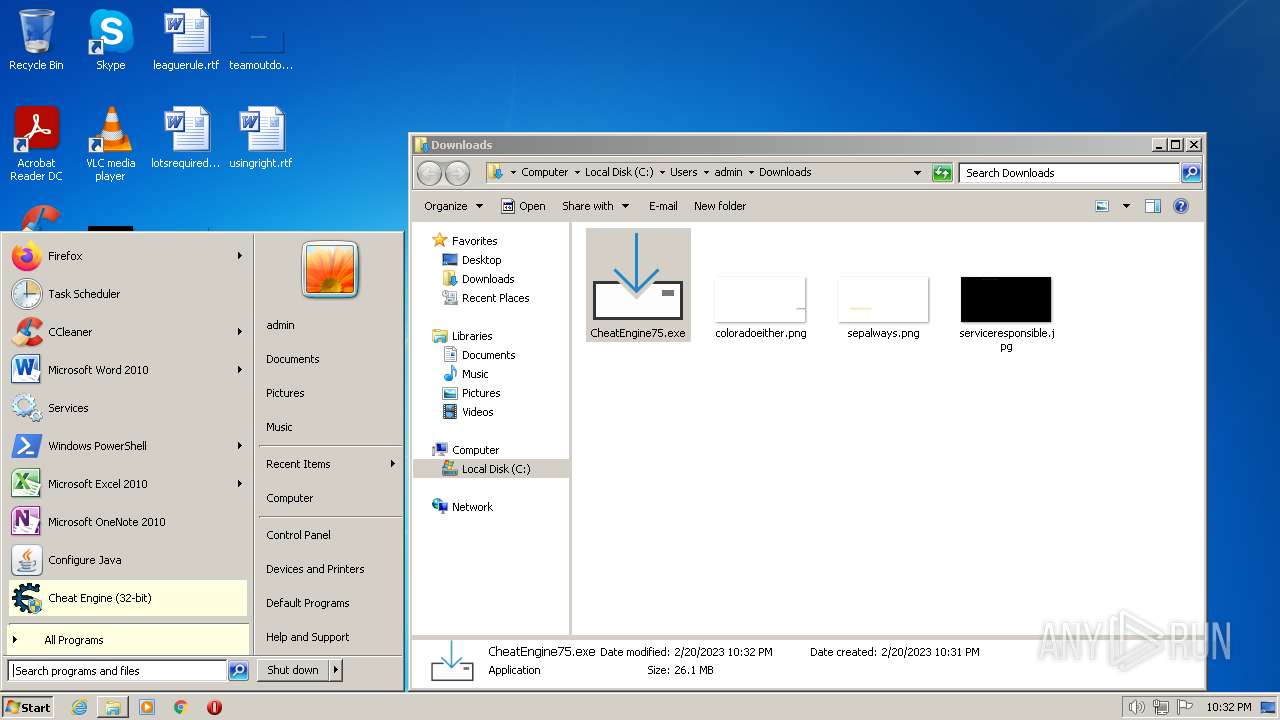
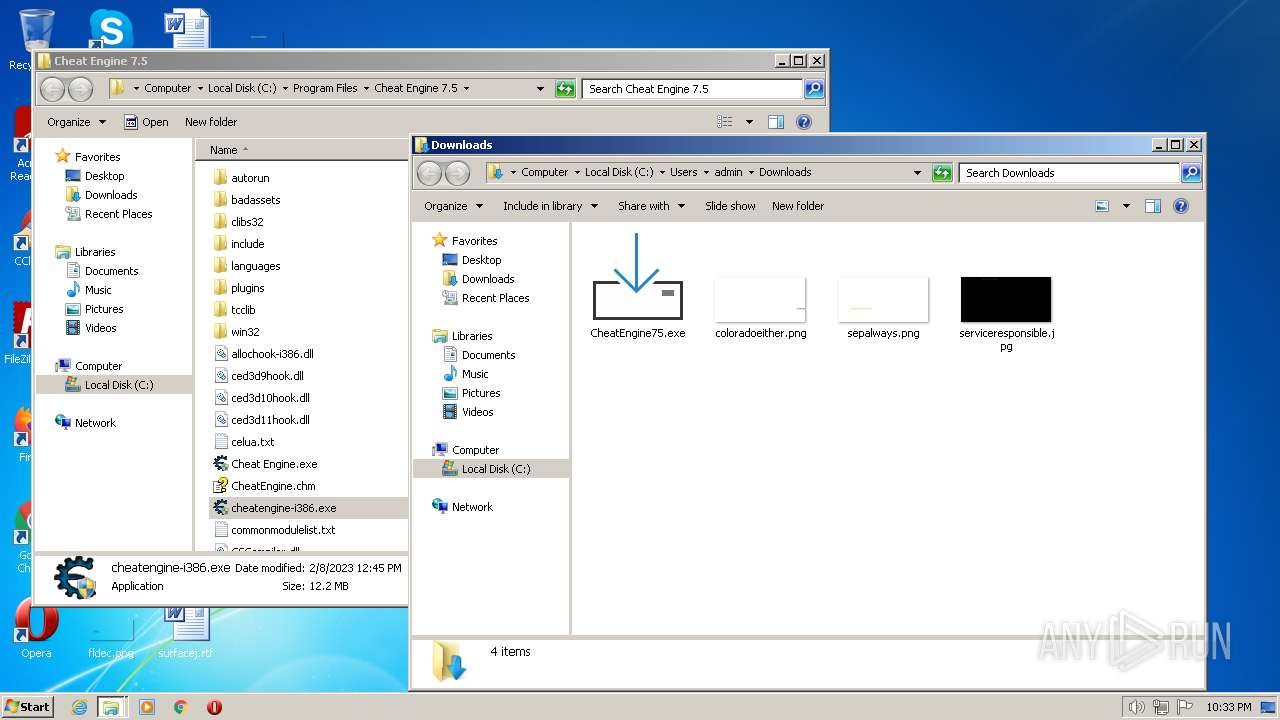
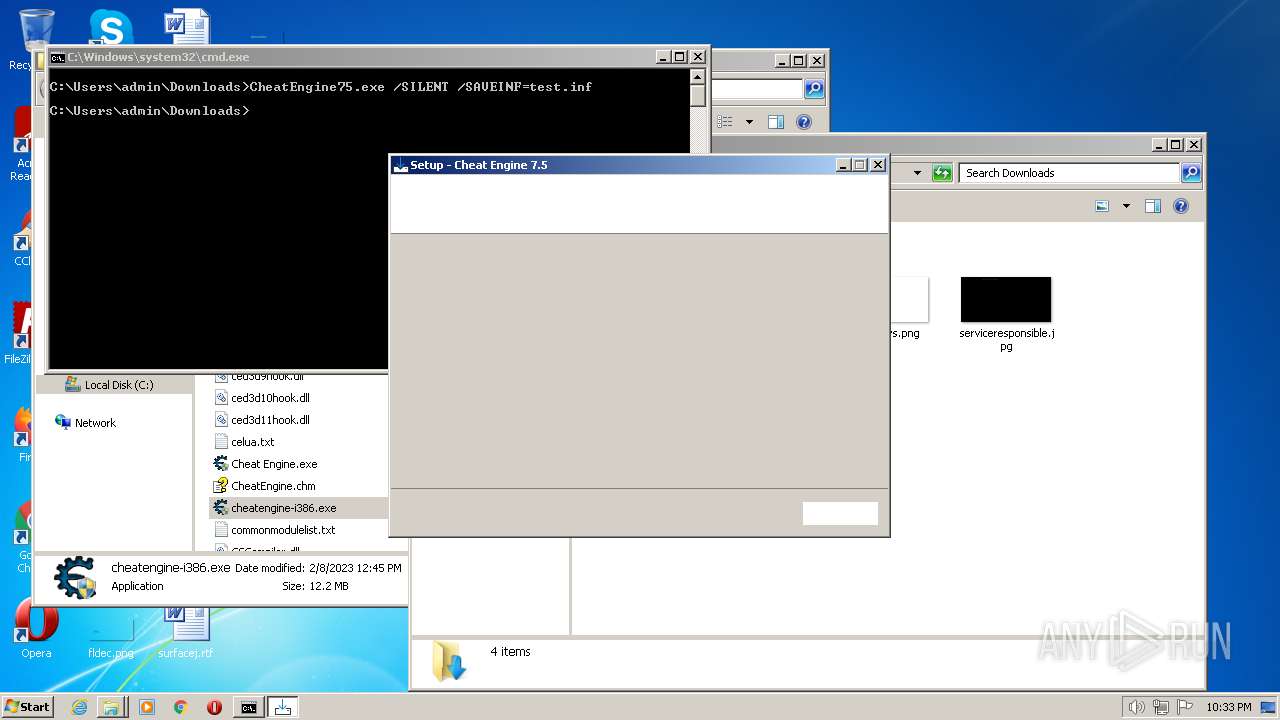
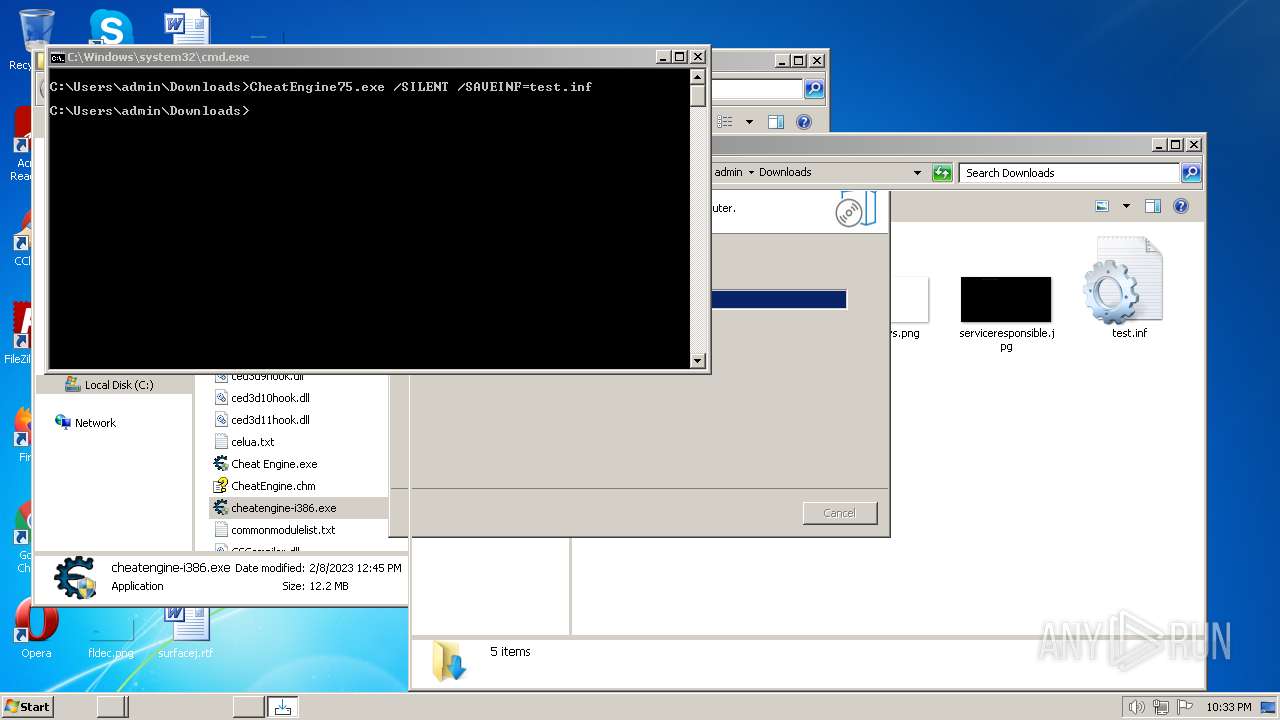
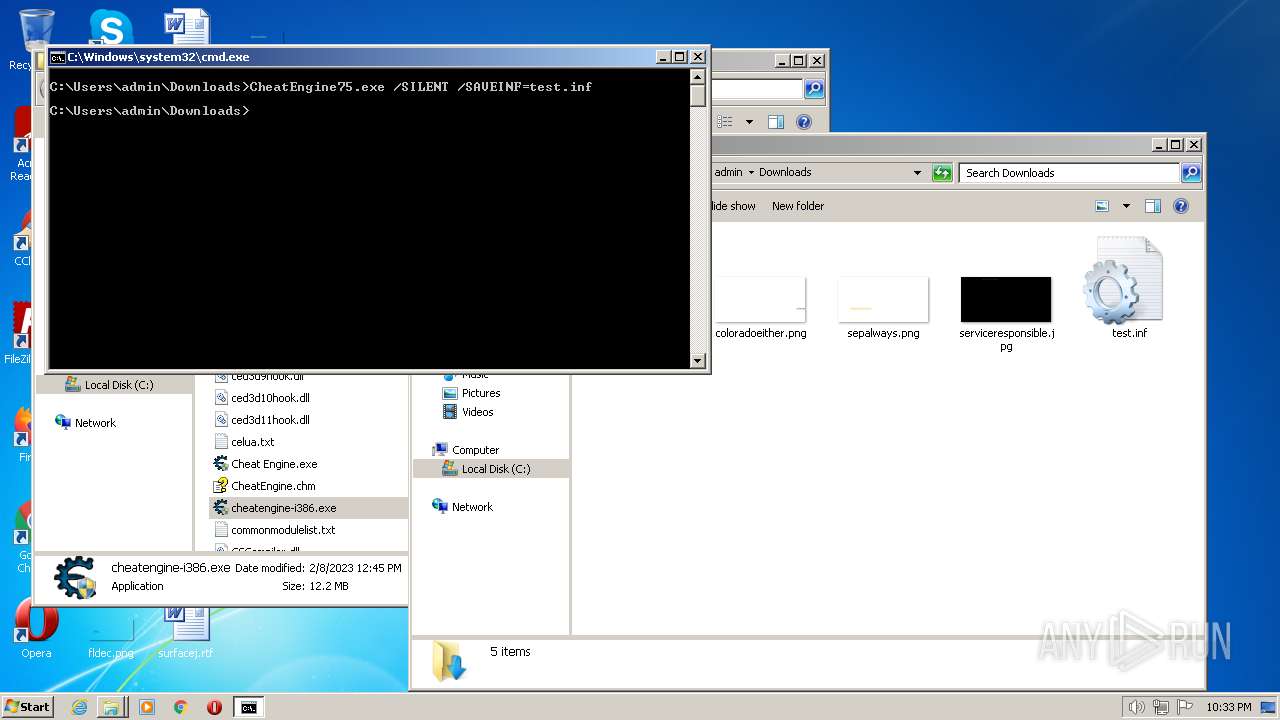
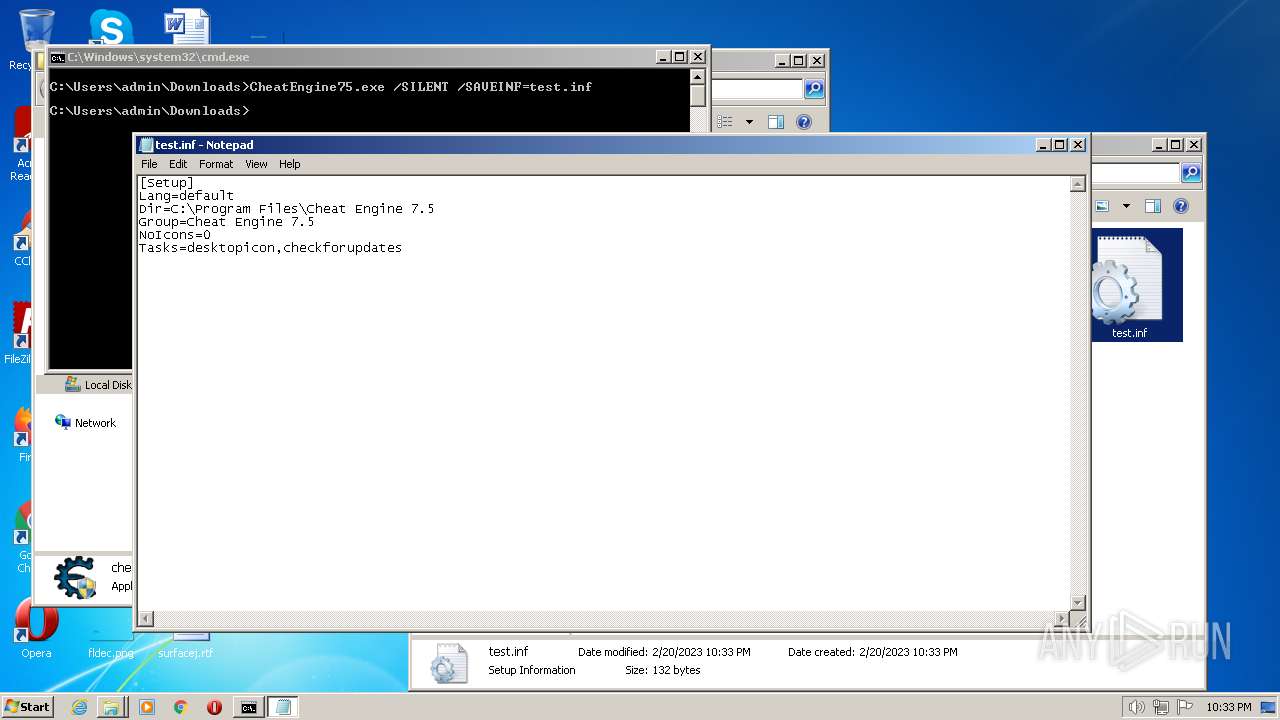
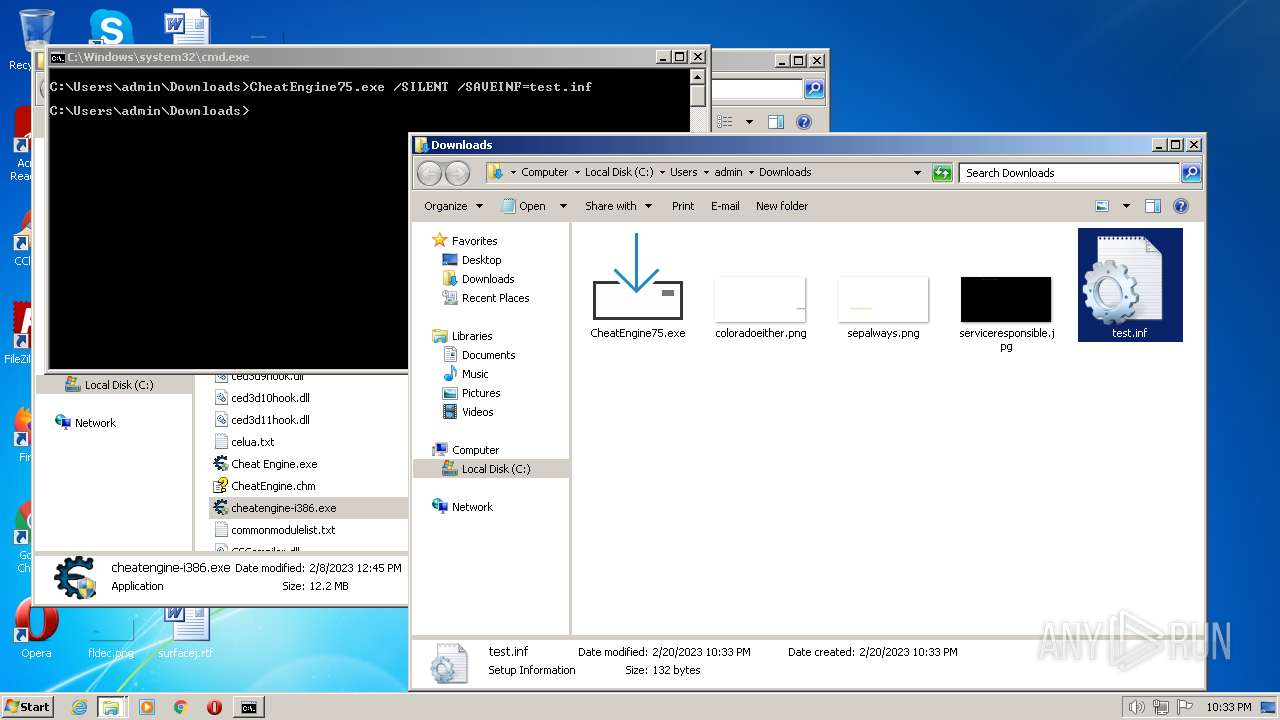
Manual execution by a user
- cmd.exe (PID: 1404)
- CheatEngine75.exe (PID: 3024)
- cmd.exe (PID: 3772)
- NOTEPAD.EXE (PID: 3392)
Executable content was dropped or overwritten
- firefox.exe (PID: 3200)
Create files in a temporary directory
- CheatEngine75.exe (PID: 3508)
- firefox.exe (PID: 3200)
- CheatEngine75.exe (PID: 3408)
- CheatEngine75.exe (PID: 3024)
- CheatEngine75.exe (PID: 376)
- CheatEngine75.exe (PID: 2756)
- CheatEngine75.exe (PID: 3488)
The process uses the downloaded file
- firefox.exe (PID: 3200)
Drops the executable file immediately after the start
- firefox.exe (PID: 3200)
Checks supported languages
- CheatEngine75.exe (PID: 3508)
- CheatEngine75.exe (PID: 3408)
- CheatEngine75.tmp (PID: 3248)
- CheatEngine75.tmp (PID: 124)
- windowsrepair.exe (PID: 2808)
- CheatEngine75.exe (PID: 3024)
- CheatEngine75.tmp (PID: 128)
- CheatEngine75.exe (PID: 376)
- CheatEngine75.tmp (PID: 1668)
- CheatEngine75.exe (PID: 2756)
- CheatEngine75.tmp (PID: 2296)
- CheatEngine75.exe (PID: 3488)
- CheatEngine75.tmp (PID: 3636)
Reads the computer name
- CheatEngine75.tmp (PID: 3248)
- CheatEngine75.tmp (PID: 124)
- CheatEngine75.tmp (PID: 128)
- CheatEngine75.tmp (PID: 1668)
- CheatEngine75.tmp (PID: 2296)
- CheatEngine75.tmp (PID: 3636)
The process checks LSA protection
- CheatEngine75.tmp (PID: 3248)
- CheatEngine75.tmp (PID: 124)
- CheatEngine75.tmp (PID: 128)
- CheatEngine75.tmp (PID: 1668)
- CheatEngine75.tmp (PID: 2296)
- CheatEngine75.tmp (PID: 3636)
Application was dropped or rewritten from another process
- CheatEngine75.tmp (PID: 3248)
- CheatEngine75.tmp (PID: 124)
- CheatEngine75.tmp (PID: 128)
- CheatEngine75.tmp (PID: 1668)
- CheatEngine75.tmp (PID: 2296)
- CheatEngine75.tmp (PID: 3636)
Application launched itself
- firefox.exe (PID: 3032)
- firefox.exe (PID: 3200)
Drops a file that was compiled in debug mode
- CheatEngine75.tmp (PID: 124)
- CheatEngine75.tmp (PID: 3636)
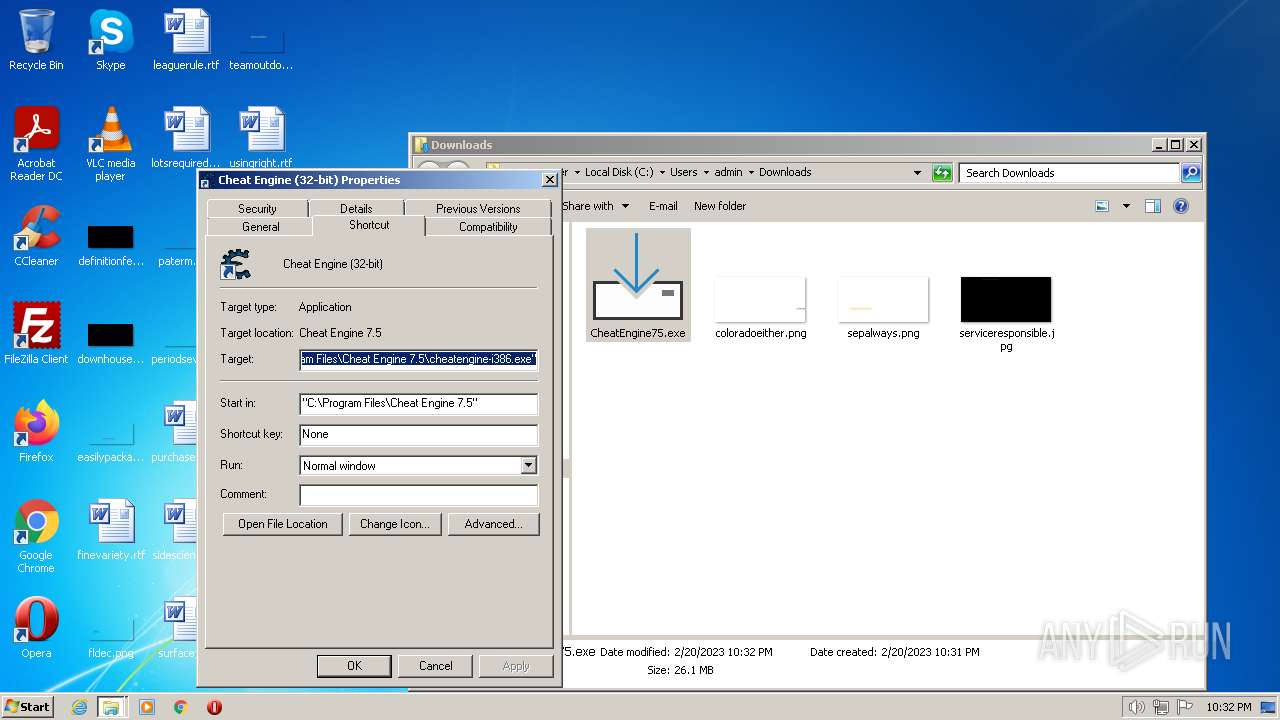
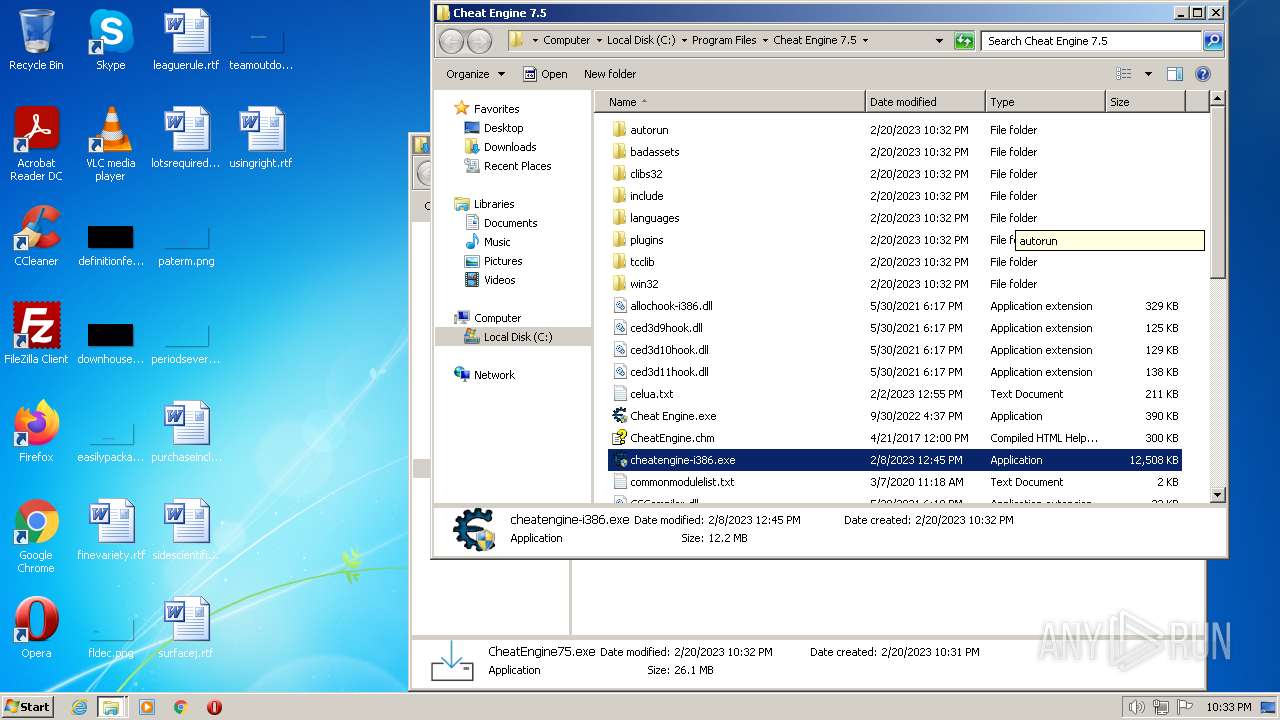
Creates a software uninstall entry
- CheatEngine75.tmp (PID: 124)
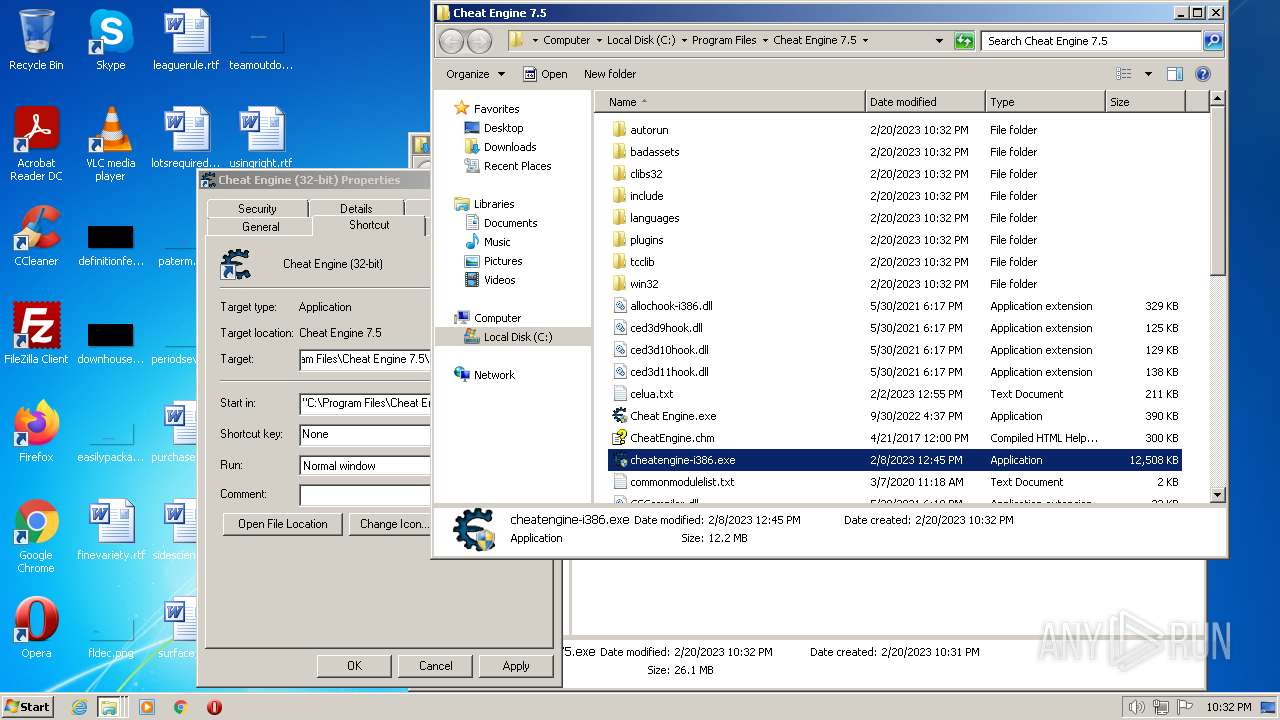
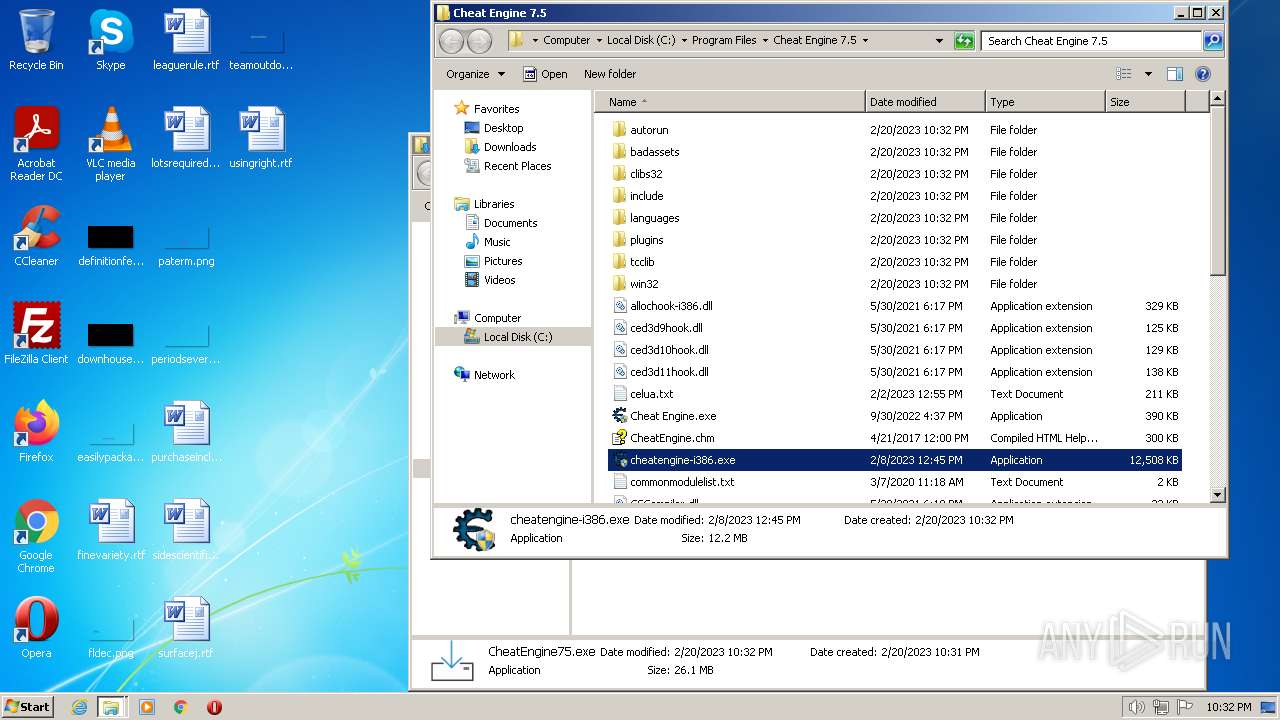
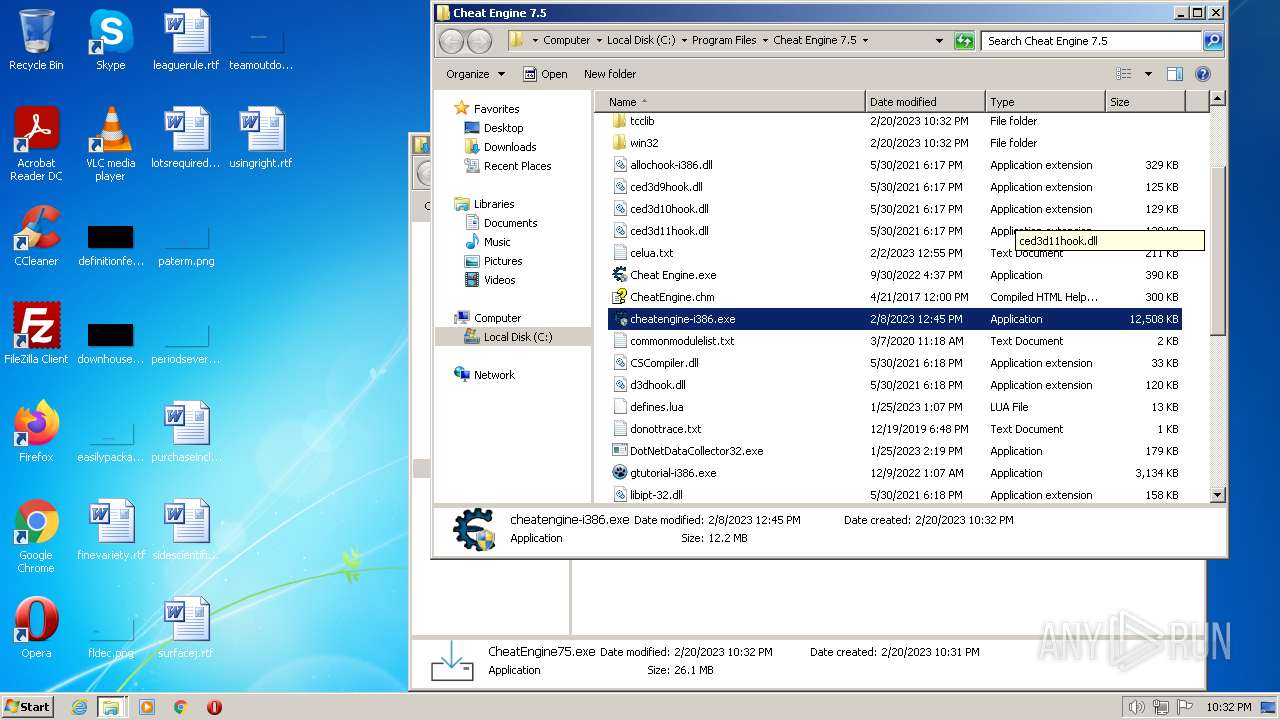
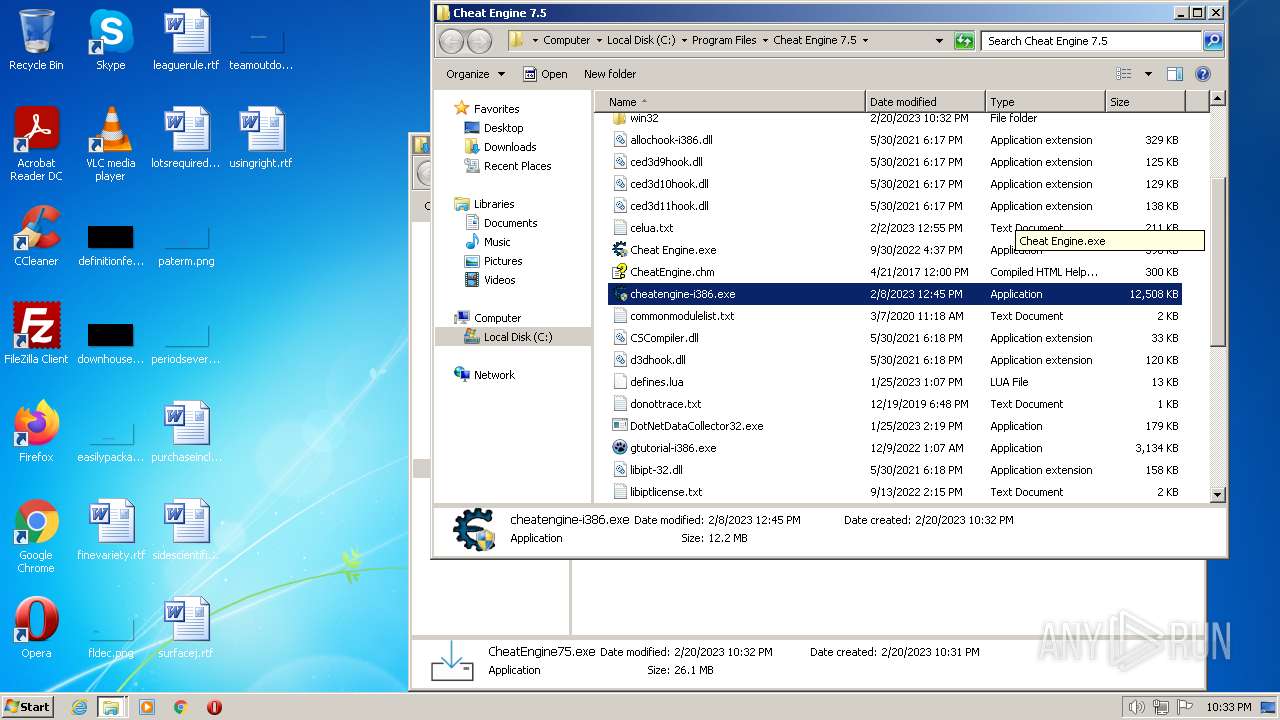
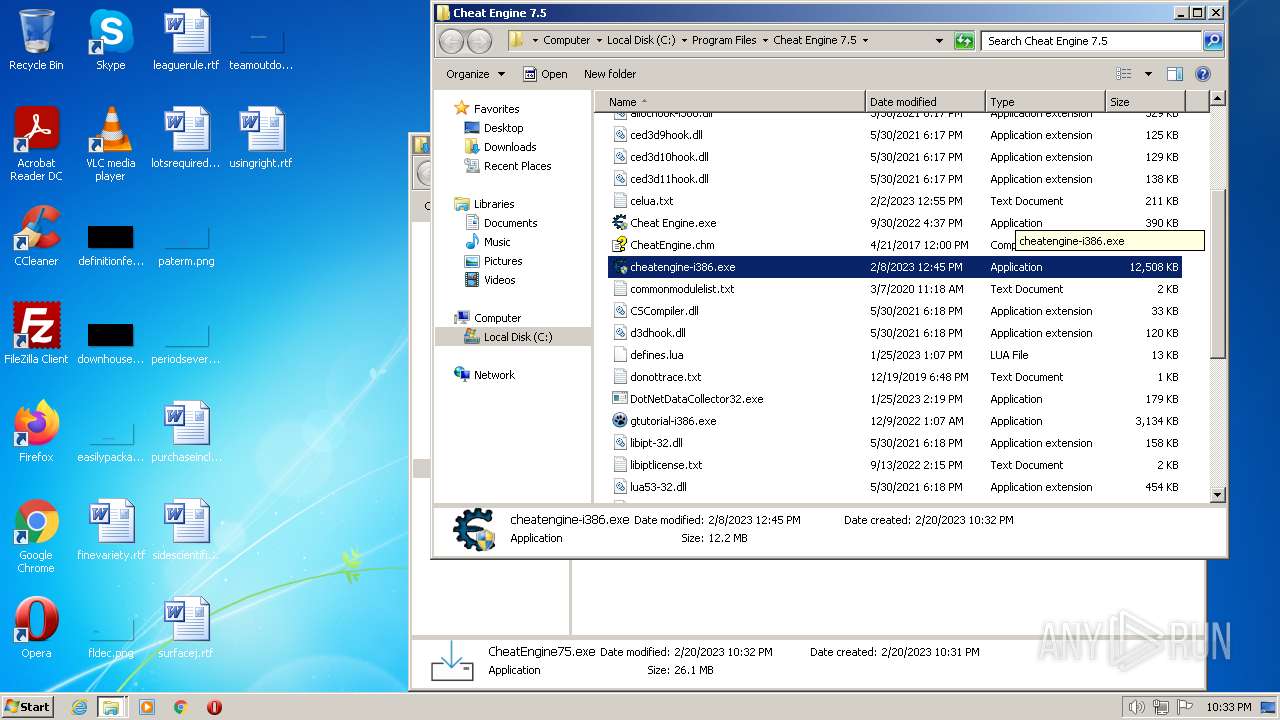
Creates files in the program directory
- CheatEngine75.tmp (PID: 124)
- CheatEngine75.tmp (PID: 3636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
108
Monitored processes
42
Malicious processes
13
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
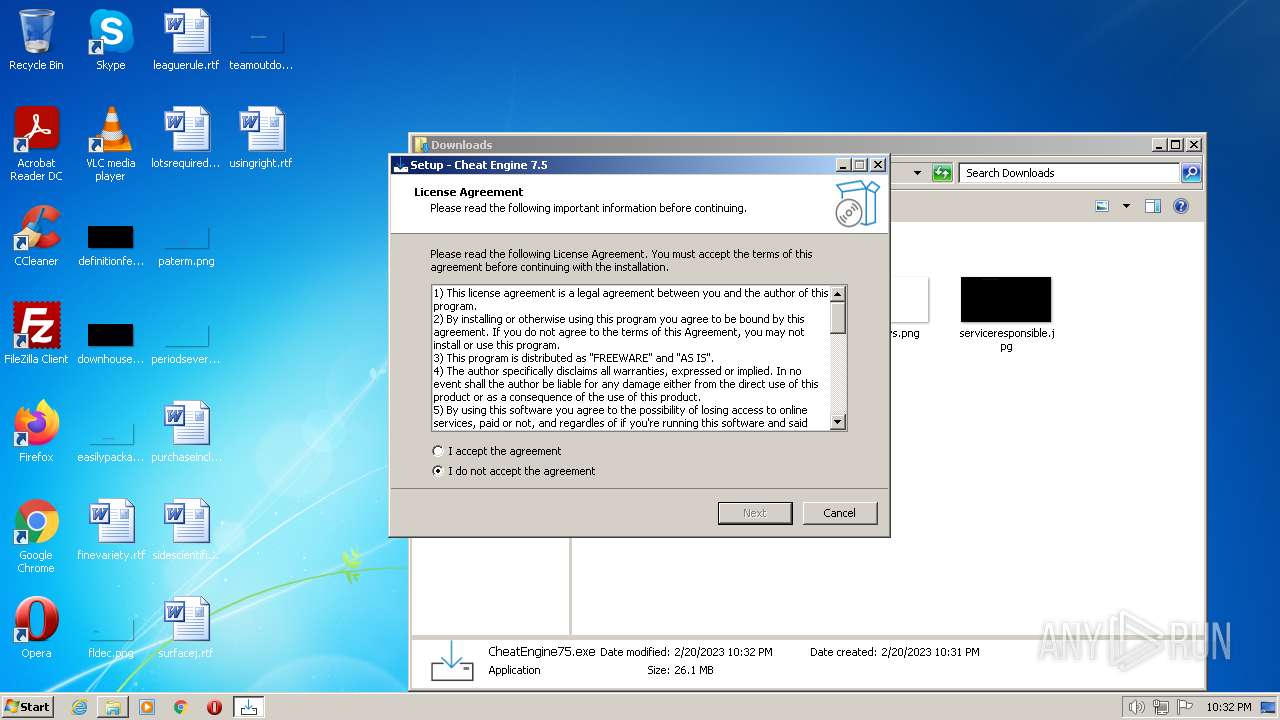
| 124 | "C:\Users\admin\AppData\Local\Temp\is-1GGNO.tmp\CheatEngine75.tmp" /SL5="$110140,26511452,832512,C:\Users\admin\Downloads\CheatEngine75.exe" /SPAWNWND=$12015E /NOTIFYWND=$701F6 /SILENT | C:\Users\admin\AppData\Local\Temp\is-1GGNO.tmp\CheatEngine75.tmp | CheatEngine75.exe | ||||||||||||
User: admin Company: Cheat Engine Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 128 | "C:\Users\admin\AppData\Local\Temp\is-V8V9M.tmp\CheatEngine75.tmp" /SL5="$1F0196,26511452,832512,C:\Users\admin\Downloads\CheatEngine75.exe" | C:\Users\admin\AppData\Local\Temp\is-V8V9M.tmp\CheatEngine75.tmp | — | CheatEngine75.exe | |||||||||||
User: admin Company: Cheat Engine Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 376 | "C:\Users\admin\Downloads\CheatEngine75.exe" /SPAWNWND=$14015E /NOTIFYWND=$1F0196 | C:\Users\admin\Downloads\CheatEngine75.exe | CheatEngine75.tmp | ||||||||||||
User: admin Company: Cheat Engine Integrity Level: HIGH Description: Cheat Engine Setup Exit code: 0 Version: 7.5.0.0 Modules
| |||||||||||||||
| 1000 | "net" stop BadlionAntic | C:\Windows\system32\net.exe | — | CheatEngine75.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3200.20.1811353308\1763862569" -childID 3 -isForBrowser -prefsHandle 2004 -prefMapHandle 1848 -prefsLen 7307 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3200 "\\.\pipe\gecko-crash-server-pipe.3200" 1756 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1404 | "cmd.exe" /s /k pushd "C:\Users\admin\Downloads" | C:\Windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1668 | "C:\Users\admin\AppData\Local\Temp\is-LJD1B.tmp\CheatEngine75.tmp" /SL5="$1A0190,26511452,832512,C:\Users\admin\Downloads\CheatEngine75.exe" /SPAWNWND=$14015E /NOTIFYWND=$1F0196 | C:\Users\admin\AppData\Local\Temp\is-LJD1B.tmp\CheatEngine75.tmp | — | CheatEngine75.exe | |||||||||||
User: admin Company: Cheat Engine Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1684 | "icacls" "C:\Program Files\Cheat Engine 7.5" /grant *S-1-15-2-1:(OI)(CI)(RX) | C:\Windows\system32\icacls.exe | — | CheatEngine75.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 1332 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 1752 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3200.28.1885467409\1129866675" -childID 5 -isForBrowser -prefsHandle 3476 -prefMapHandle 3444 -prefsLen 7849 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3200 "\\.\pipe\gecko-crash-server-pipe.3200" 3380 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1756 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3200.13.704763238\1094923406" -childID 2 -isForBrowser -prefsHandle 2936 -prefMapHandle 2956 -prefsLen 6644 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3200 "\\.\pipe\gecko-crash-server-pipe.3200" 2300 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
Total events
36 102
Read events
35 922
Write events
160
Delete events
20
Modification events
| (PID) Process: | (3032) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: E50924A40E000000 | |||
| (PID) Process: | (3200) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 728D25A40E000000 | |||
| (PID) Process: | (3200) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (3200) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (3200) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
| (PID) Process: | (3200) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
| (PID) Process: | (3200) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|ServicesSettingsServer |
Value: https://firefox.settings.services.mozilla.com/v1 | |||
| (PID) Process: | (3200) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|SecurityContentSignatureRootHash |
Value: 97:E8:BA:9C:F1:2F:B3:DE:53:CC:42:A4:E6:57:7E:D6:4D:F4:93:C2:47:B4:14:FE:A0:36:81:8D:38:23:56:0E | |||
| (PID) Process: | (3200) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3200) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003E010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
242
Suspicious files
258
Text files
1 760
Unknown types
110
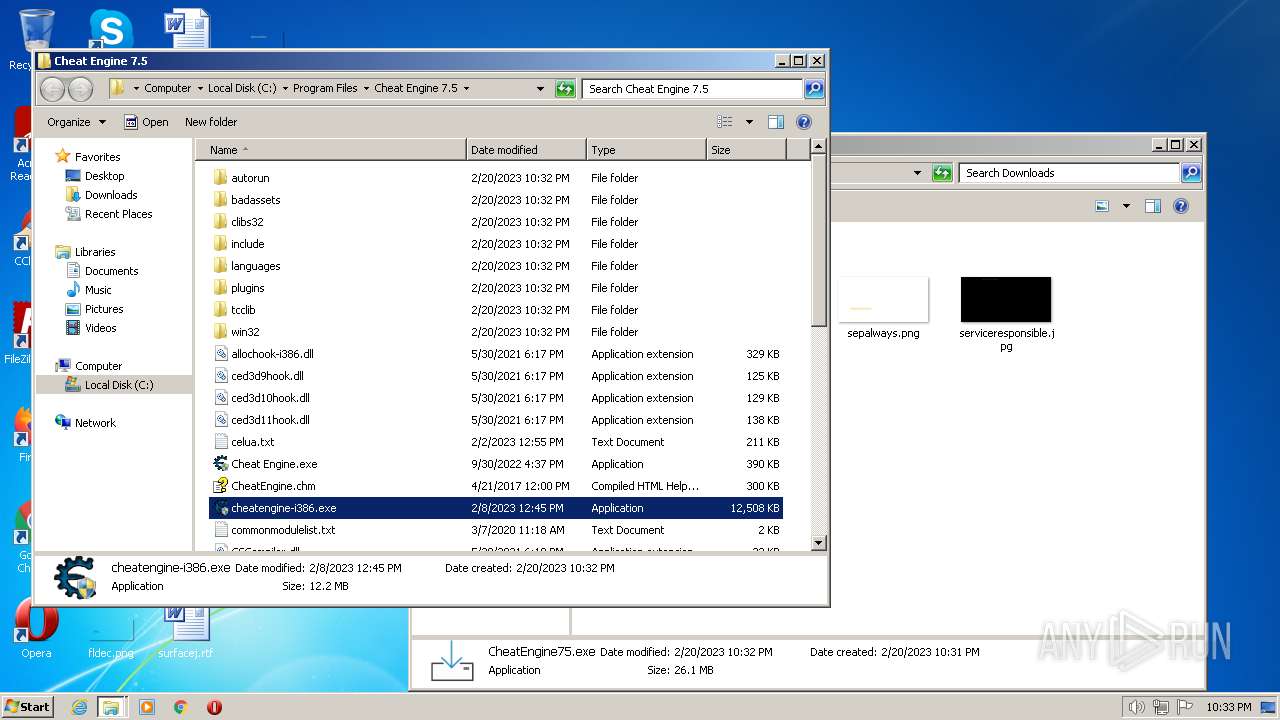
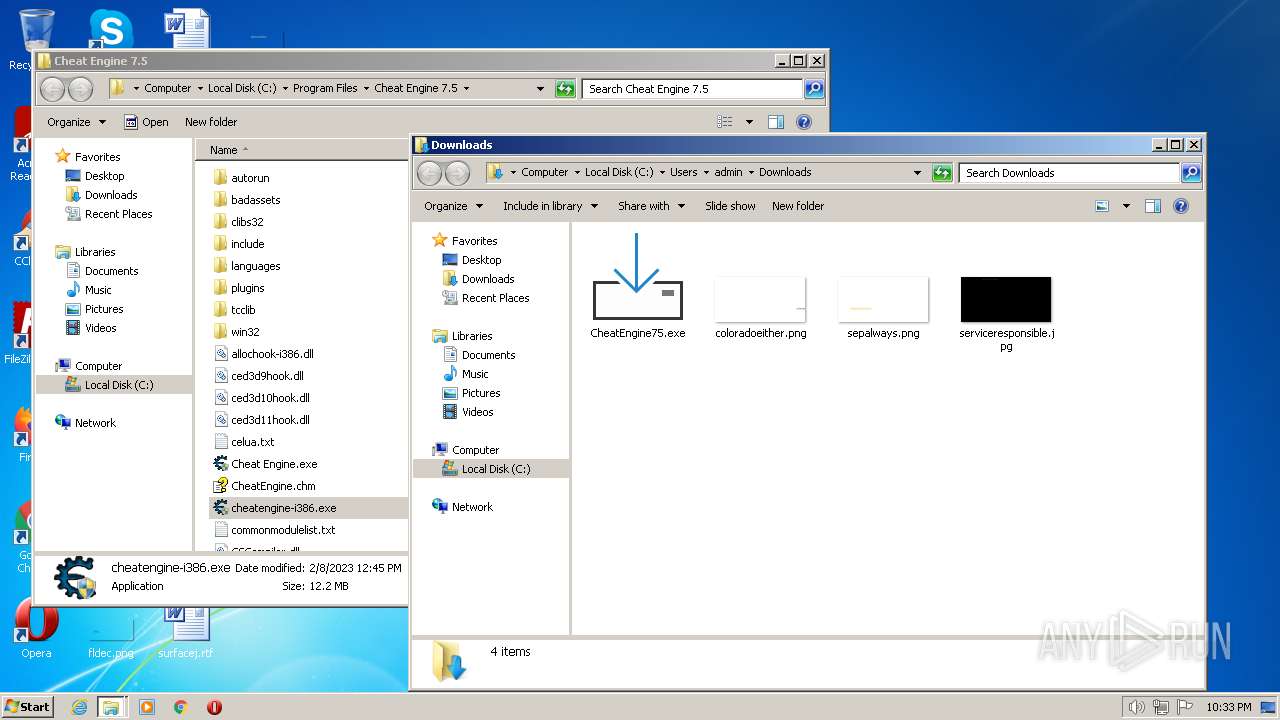
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3200 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3200 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 3200 | firefox.exe | C:\Users\admin\AppData\Local\Temp\mz_etilqs_NxUjMQZB9WiSU4v | binary | |
MD5:— | SHA256:— | |||
| 3200 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\places.sqlite-wal | sqlite-wal | |
MD5:— | SHA256:— | |||
| 3200 | firefox.exe | C:\Users\admin\AppData\Local\Temp\mz_etilqs_dj2Iwacqrooy20G | binary | |
MD5:— | SHA256:— | |||
| 3200 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-wal | binary | |
MD5:— | SHA256:— | |||
| 3200 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3200 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | text | |
MD5:299A2B747C11E4BDA194E563FEA4A699 | SHA256:94EE461F62E8B4A0A65471A41E10C8C56722B73C0A019D76ACA7F5BAF109813E | |||
| 3200 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:299A2B747C11E4BDA194E563FEA4A699 | SHA256:94EE461F62E8B4A0A65471A41E10C8C56722B73C0A019D76ACA7F5BAF109813E | |||
| 3200 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
80
DNS requests
191
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3200 | firefox.exe | POST | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3200 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 279 b | whitelisted |
3200 | firefox.exe | POST | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3200 | firefox.exe | POST | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3200 | firefox.exe | POST | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
3200 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt | US | text | 8 b | whitelisted |
3200 | firefox.exe | POST | 200 | 184.24.77.56:80 | http://r3.o.lencr.org/ | US | der | 503 b | shared |
3200 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3200 | firefox.exe | POST | 200 | 184.24.77.56:80 | http://r3.o.lencr.org/ | US | der | 503 b | shared |
3200 | firefox.exe | POST | 200 | 184.24.77.56:80 | http://r3.o.lencr.org/ | US | der | 503 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3200 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
3200 | firefox.exe | 51.38.43.18:443 | gofile.io | OVH SAS | FR | suspicious |
3200 | firefox.exe | 35.241.9.150:443 | firefox.settings.services.mozilla.com | GOOGLE | US | suspicious |
3200 | firefox.exe | 184.24.77.56:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
3200 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | suspicious |
3200 | firefox.exe | 35.164.234.103:443 | location.services.mozilla.com | AMAZON-02 | US | unknown |
3200 | firefox.exe | 54.200.178.235:443 | push.services.mozilla.com | AMAZON-02 | US | unknown |
3200 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
3200 | firefox.exe | 51.178.66.33:443 | gofile.io | OVH SAS | FR | suspicious |
3200 | firefox.exe | 18.66.122.78:443 | snippets.cdn.mozilla.net | AMAZON-02 | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
gofile.io |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
r3.o.lencr.org |
| shared |
a1887.dscq.akamai.net |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
prod.content-signature-chains.prod.webservices.mozgcp.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
— | — | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
— | — | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
3200 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3200 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
— | — | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
— | — | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
— | — | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
— | — | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
— | — | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |