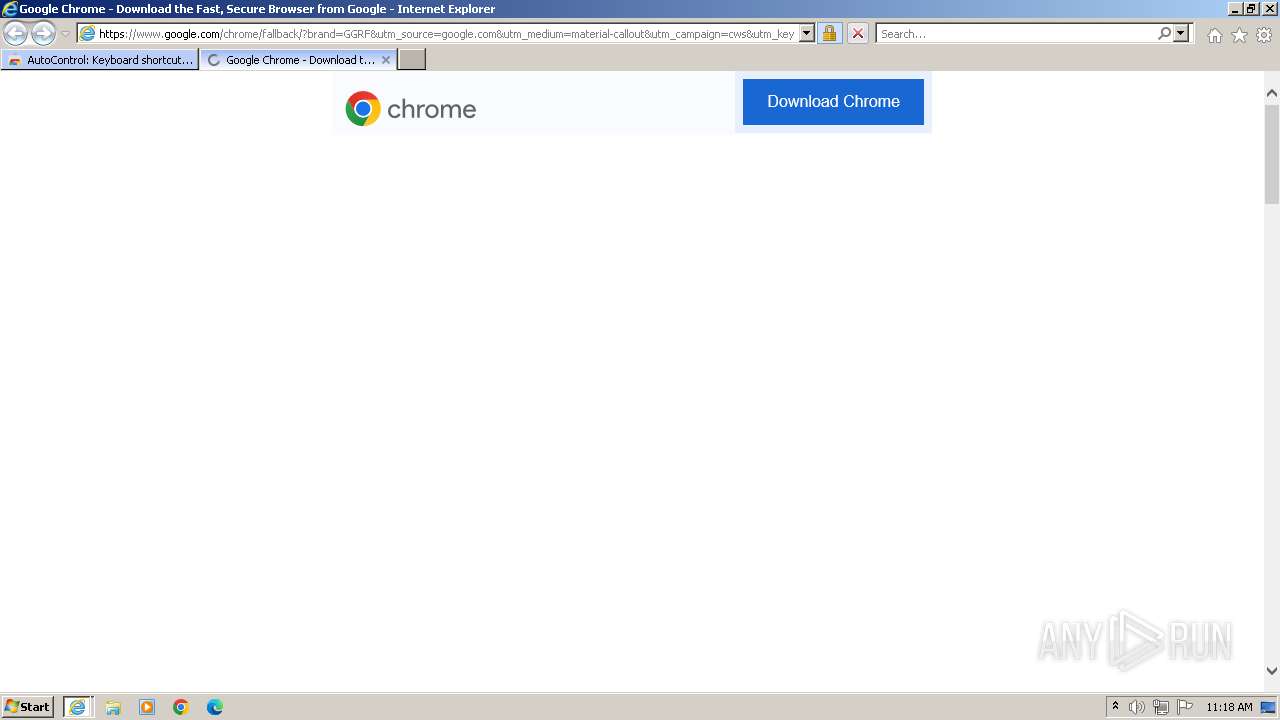
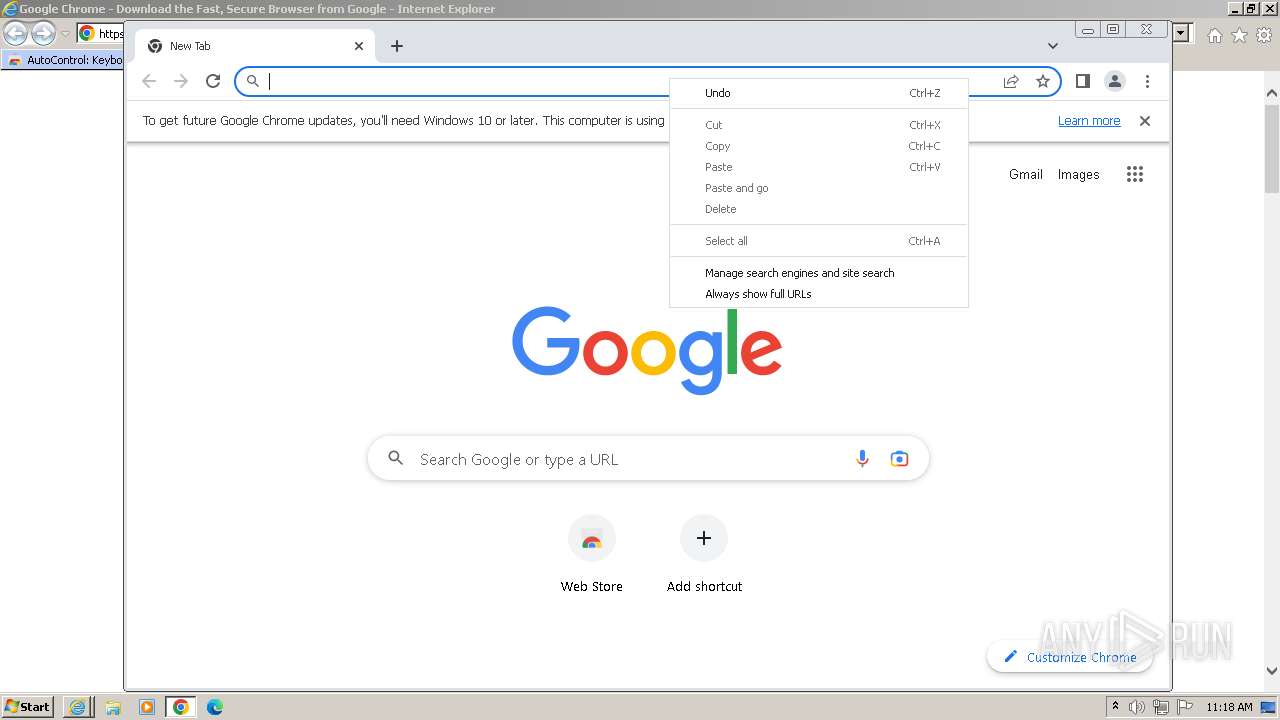
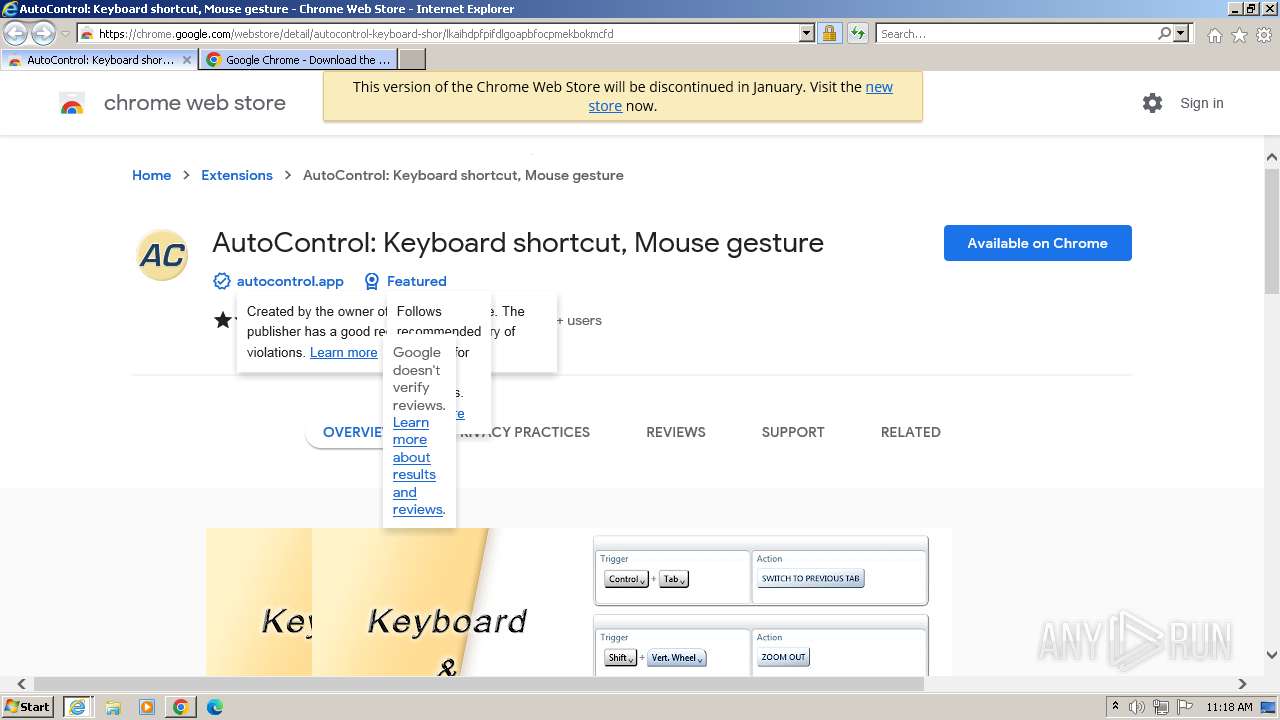
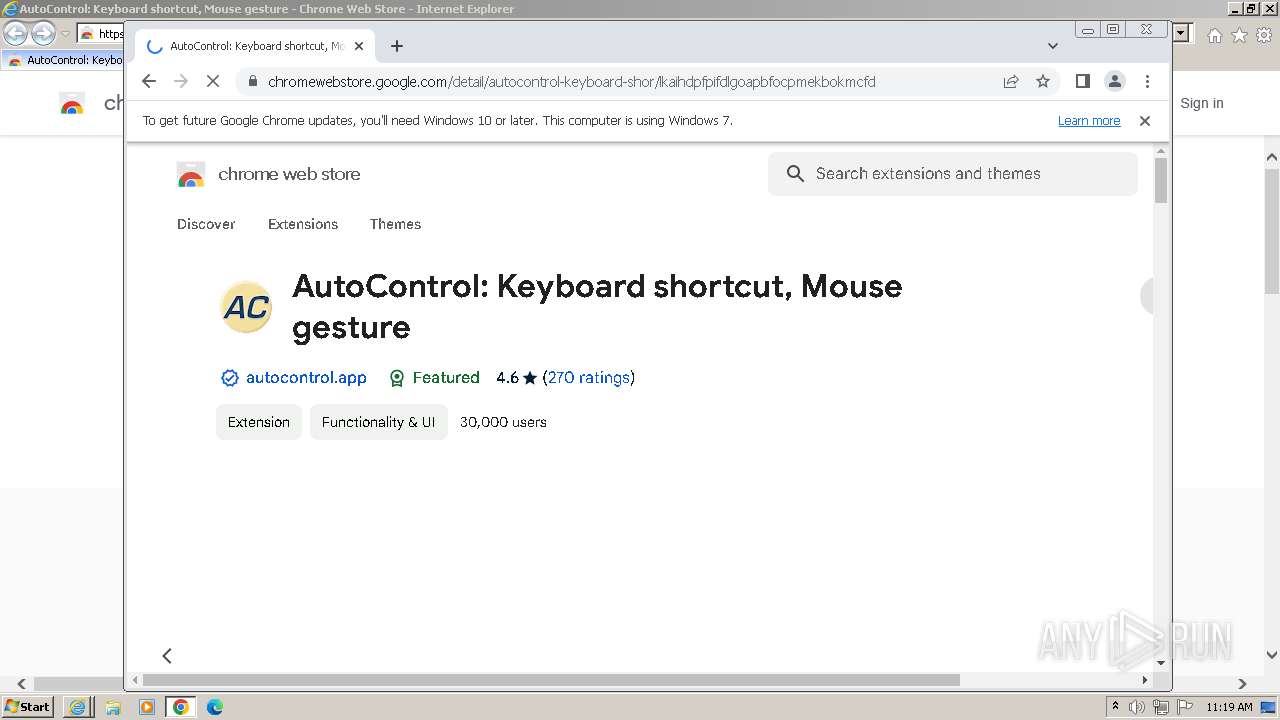
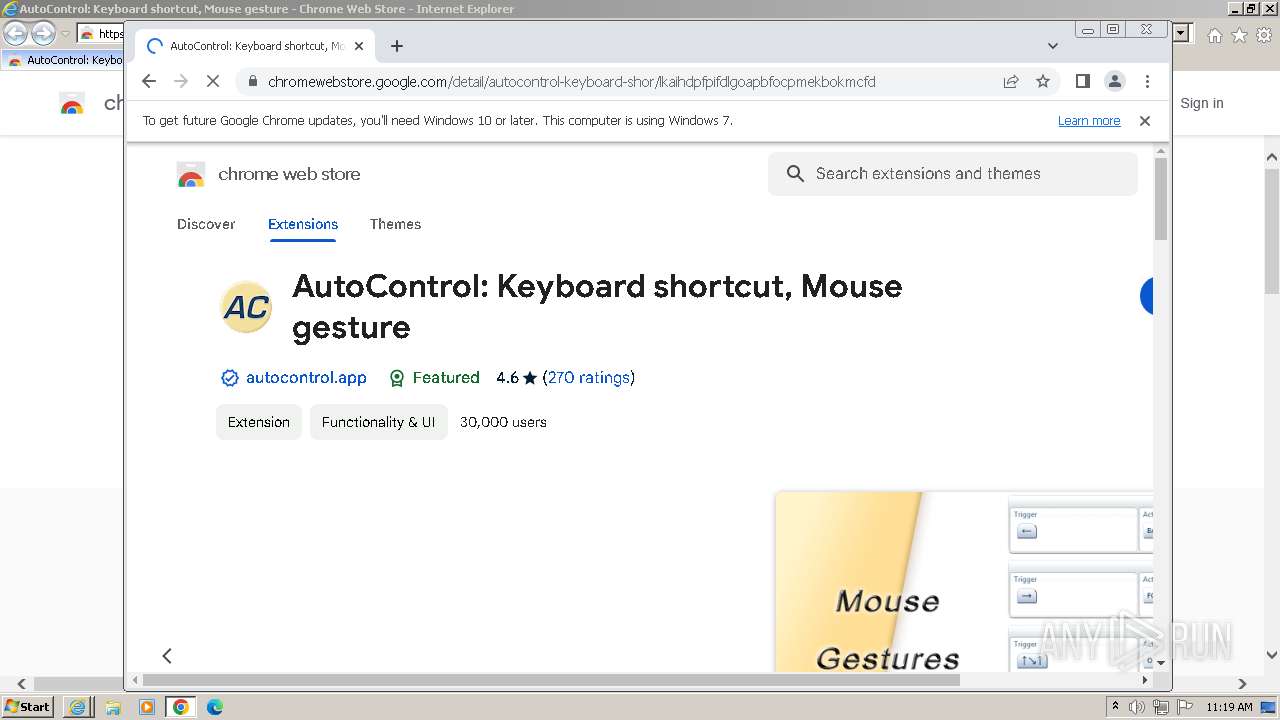
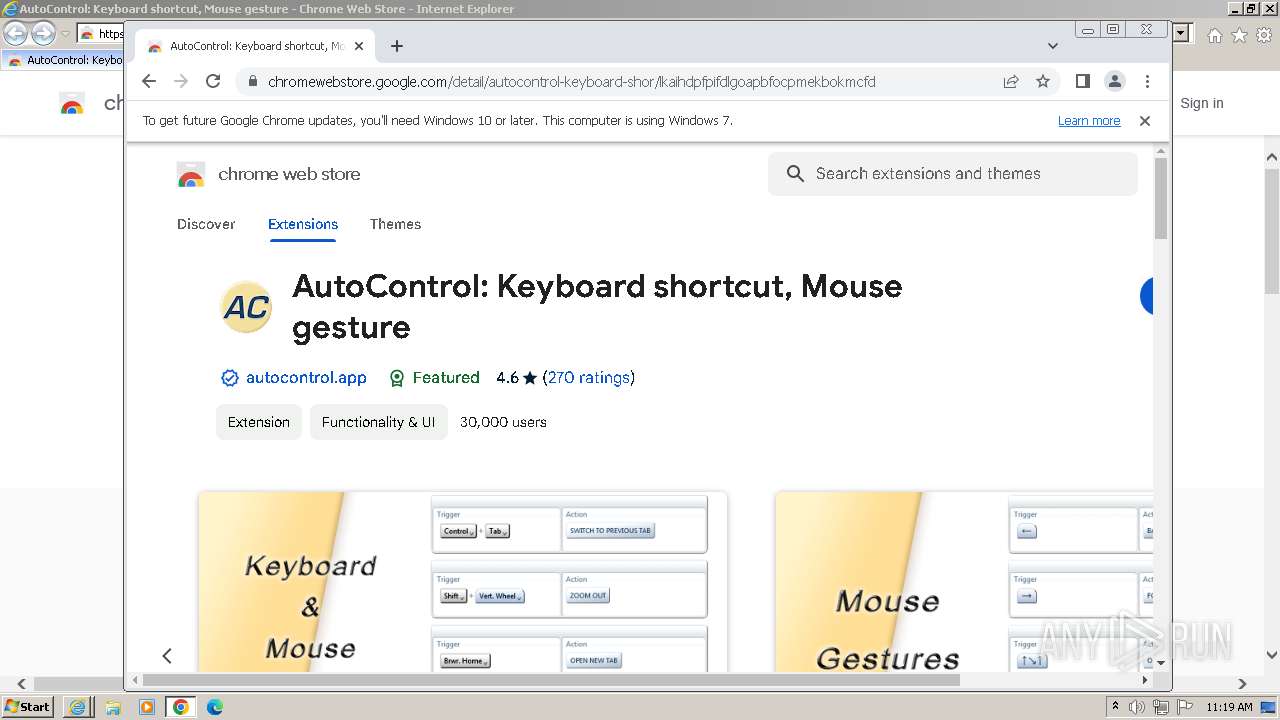
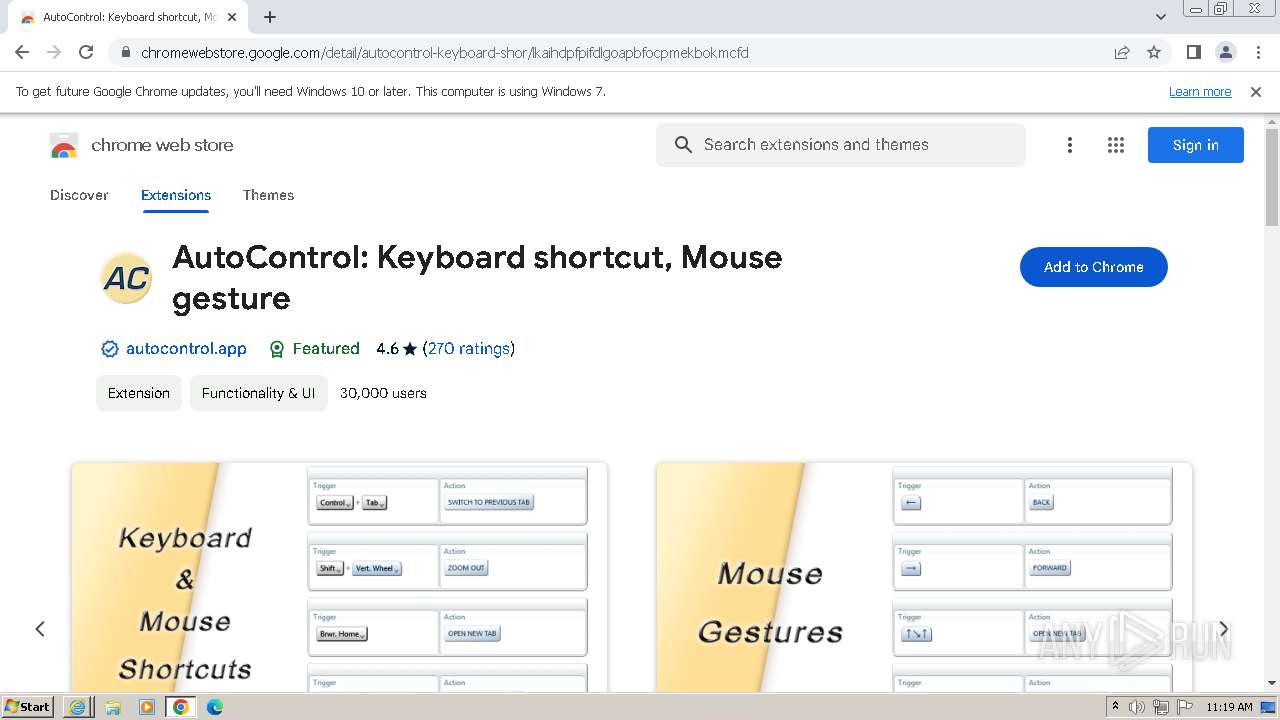
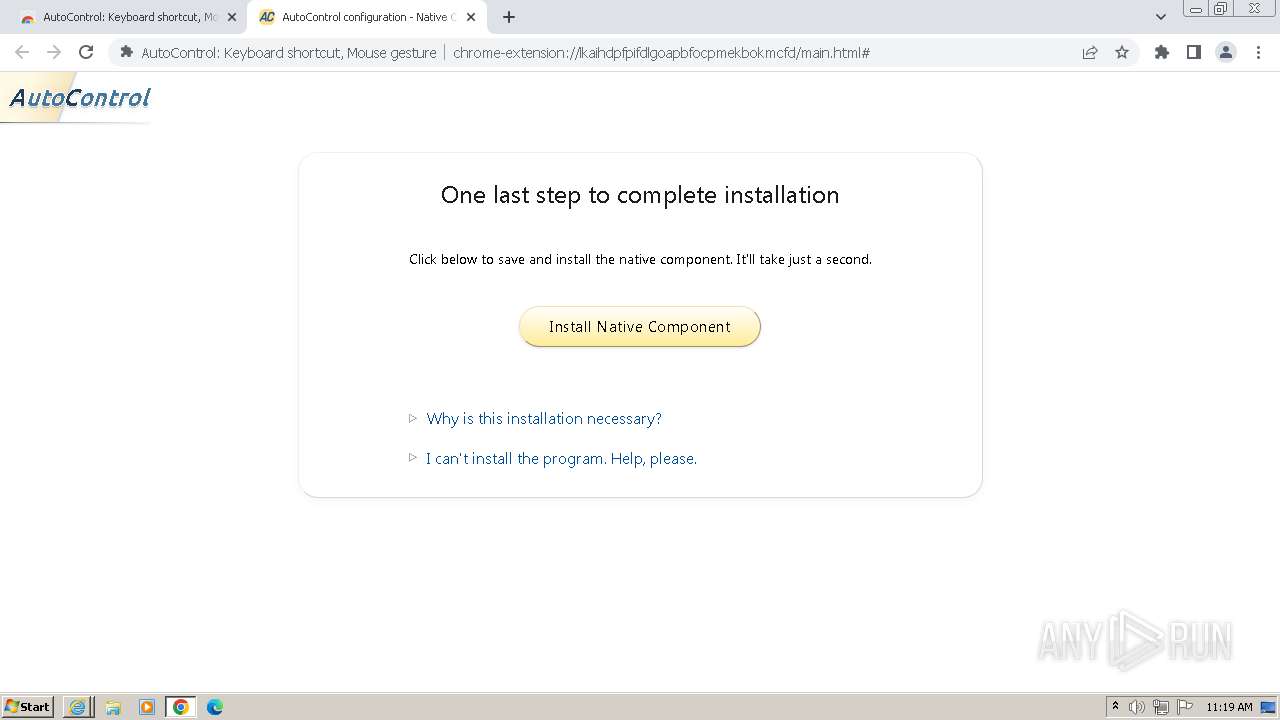
| URL: | https://chrome.google.com/webstore/detail/autocontrol-keyboard-shor/lkaihdpfpifdlgoapbfocpmekbokmcfd |
| Full analysis: | https://app.any.run/tasks/fc69c541-788a-4885-9113-e3d67005891f |
| Verdict: | Malicious activity |
| Analysis date: | December 11, 2023, 11:18:35 |
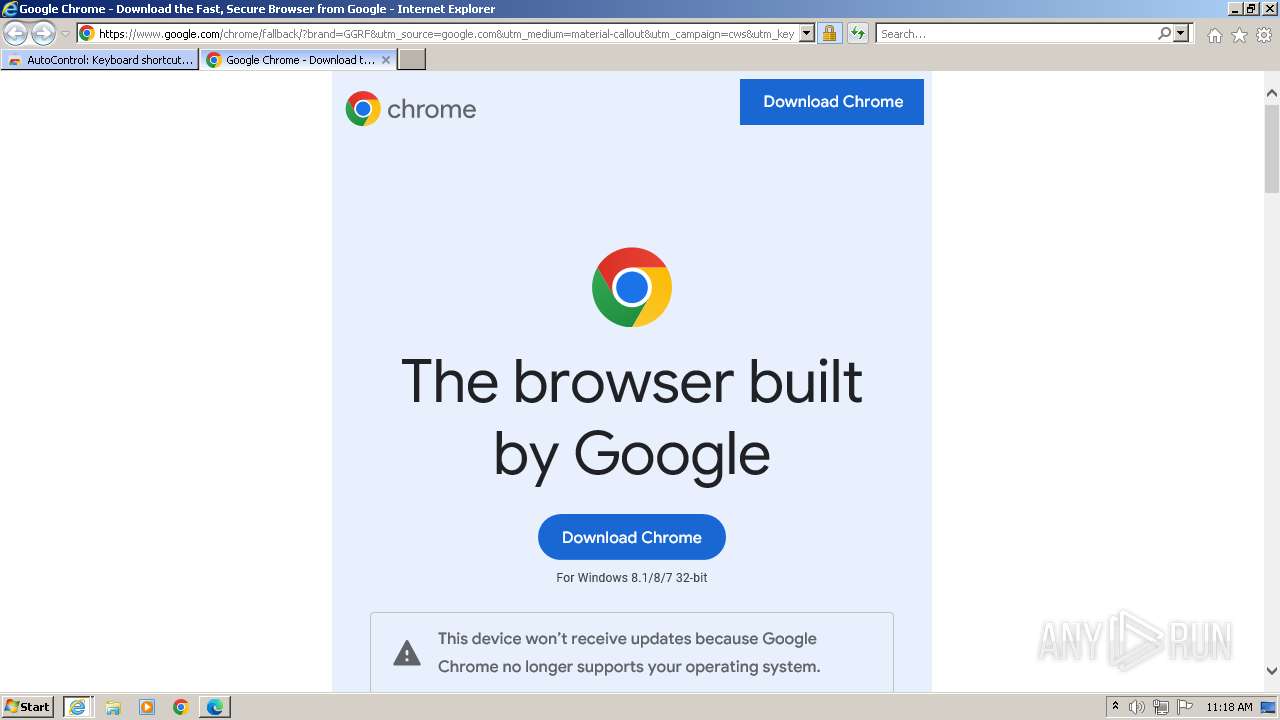
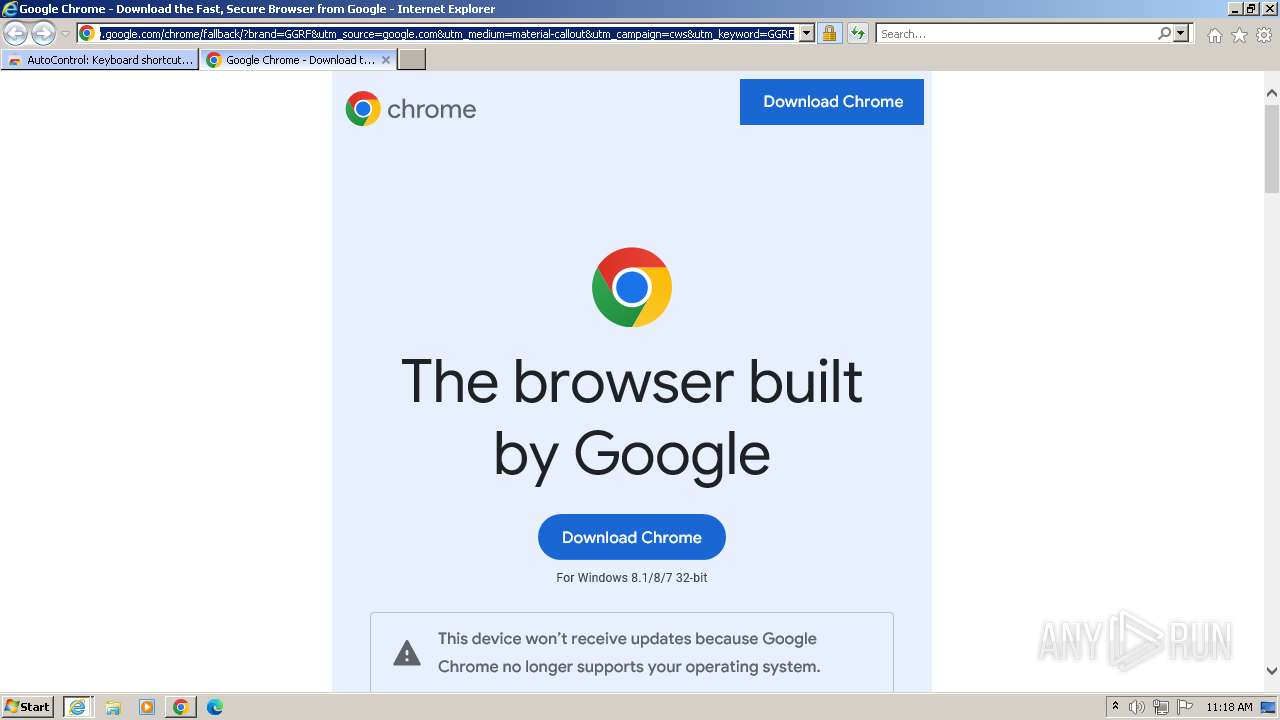
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 50562528F6CEA7373B50692BF3CCAC69 |
| SHA1: | 05CB7017494D623411EC86773E6000ADE5F22878 |
| SHA256: | 25D179FD39102CE45504BD017AC892A52765ED591E697B9E62D50D5D5C88B251 |
| SSDEEP: | 3:N8Qa9t3u0A2RKelJCKNKGKLJOlZCBGUVIGd:2Qa9c01RnJoOewUiY |
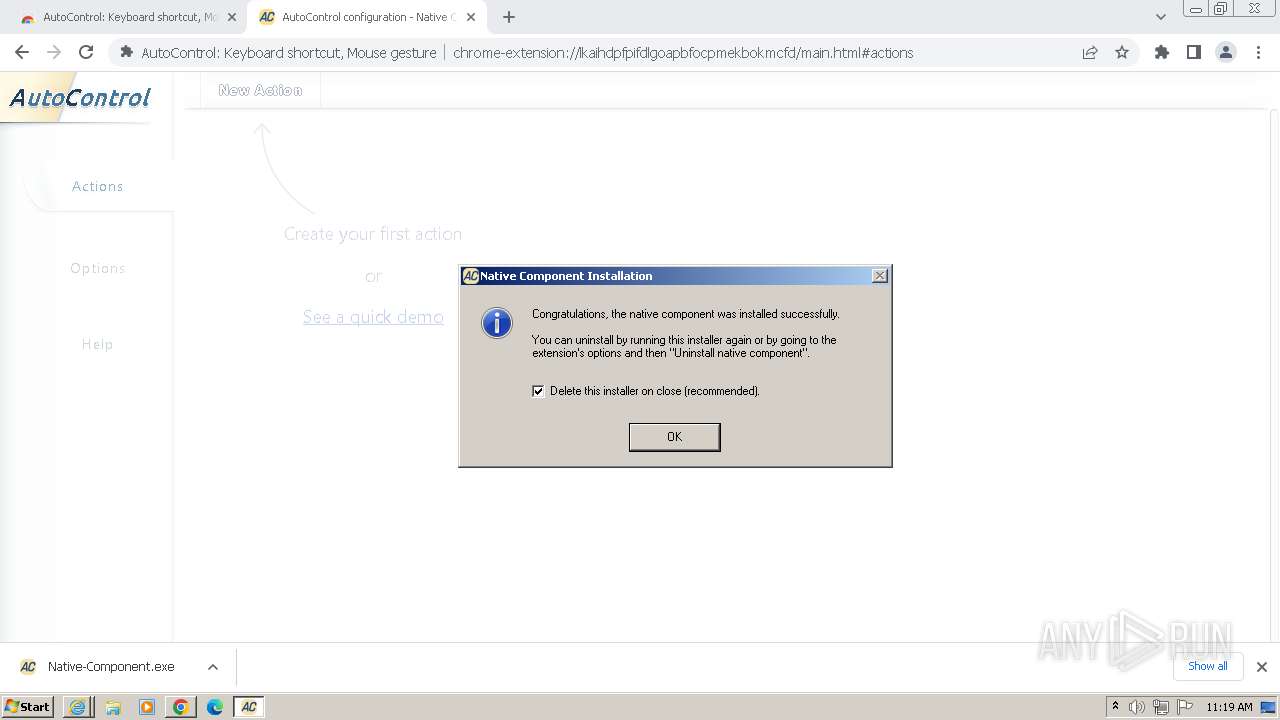
MALICIOUS
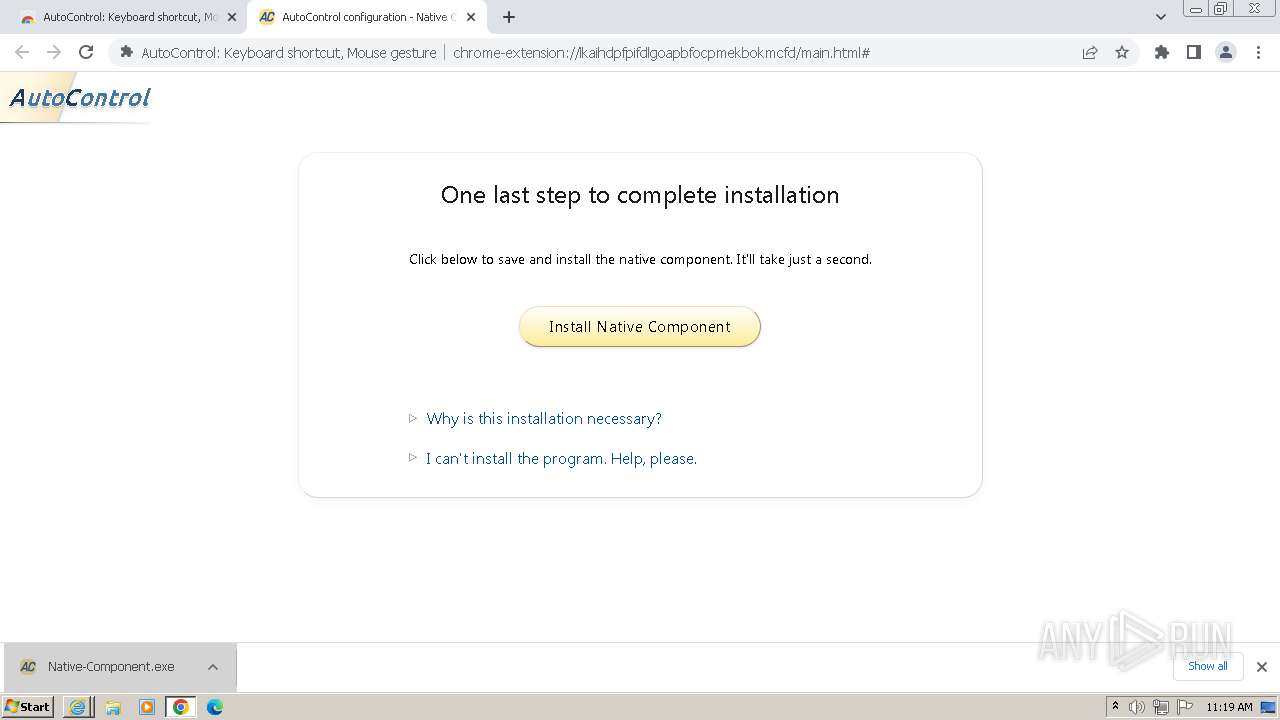
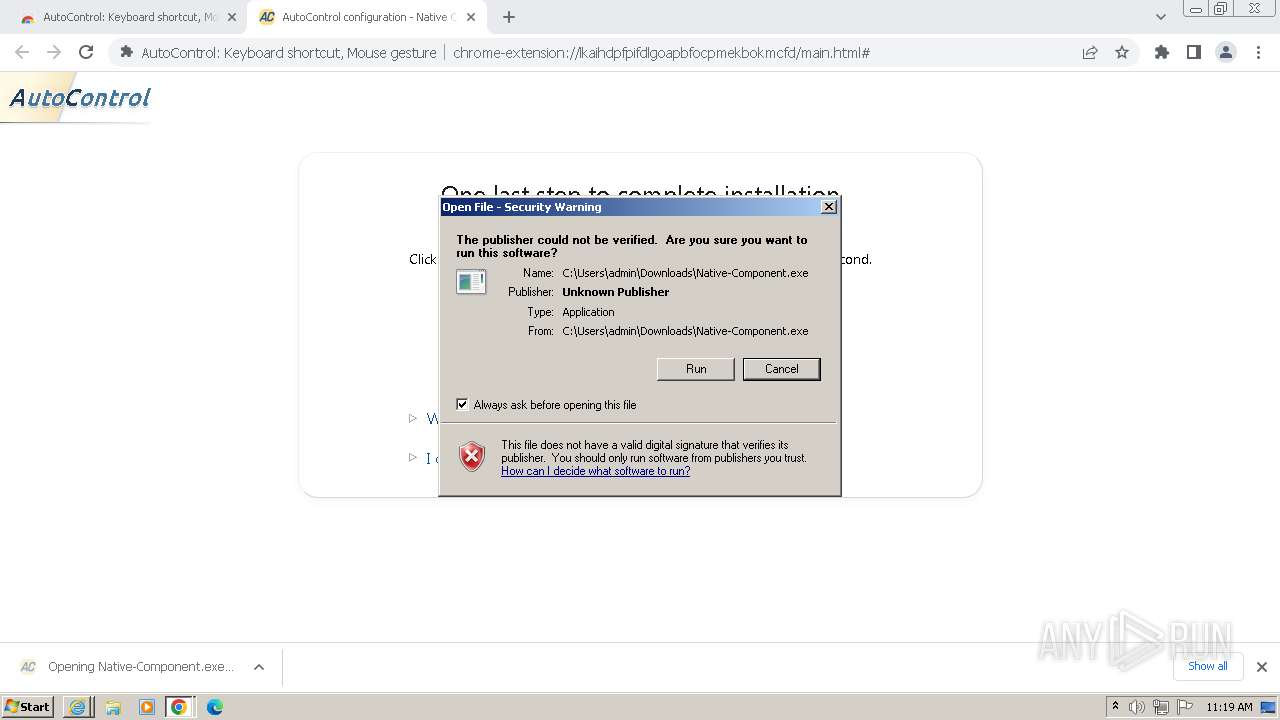
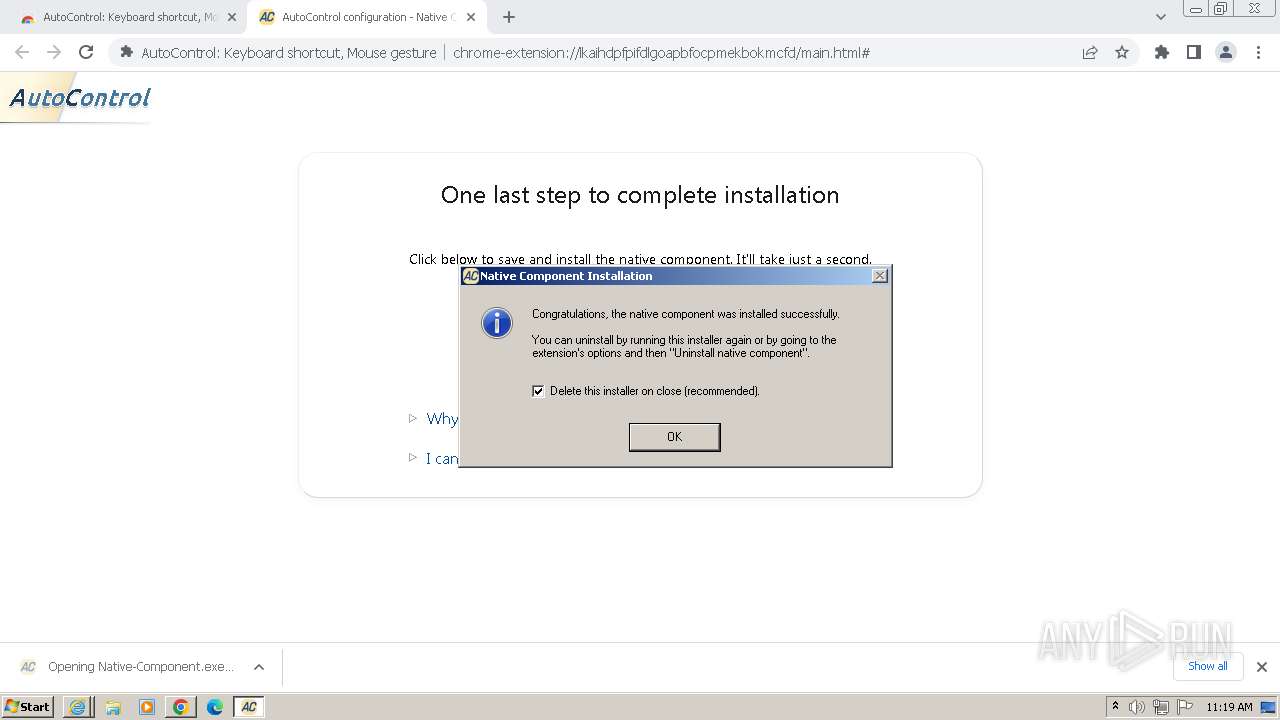
Drops the executable file immediately after the start
- Native-Component.exe (PID: 2848)
- AutoControlZero.exe (PID: 3592)
Starts CMD.EXE for commands execution
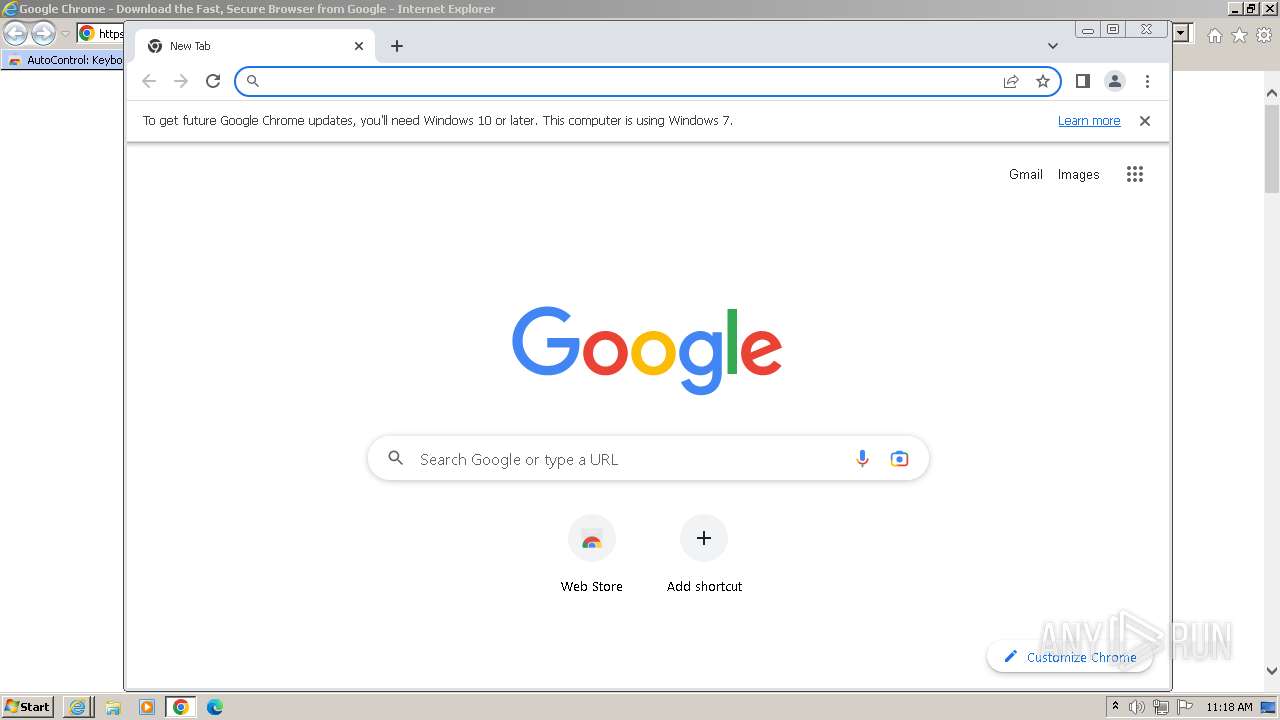
- chrome.exe (PID: 3496)
Starts CMD.EXE for self-deleting
- Native-Component.exe (PID: 2848)
SUSPICIOUS
Process drops legitimate windows executable
- chrome.exe (PID: 3496)
Starts CMD.EXE for commands execution
- AutoControlZero.exe (PID: 3592)
- Native-Component.exe (PID: 2848)
- AutoCtrl_2023.11.26.0.exe (PID: 2820)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 2904)
INFO
Application launched itself
- iexplore.exe (PID: 1088)
- chrome.exe (PID: 3496)
Manual execution by a user
- wmpnscfg.exe (PID: 3428)
- chrome.exe (PID: 3496)
Reads the computer name
- wmpnscfg.exe (PID: 3428)
- Native-Component.exe (PID: 2848)
Checks supported languages
- wmpnscfg.exe (PID: 3428)
- Native-Component.exe (PID: 2848)
- AutoControlZero.exe (PID: 3592)
- AutoCtrl_2023.11.26.0.exe (PID: 2820)
The executable file from the user directory is run by the CMD process
- AutoControlZero.exe (PID: 3592)
Drops the executable file immediately after the start
- chrome.exe (PID: 3496)
The process uses the downloaded file
- chrome.exe (PID: 4088)
- chrome.exe (PID: 3496)
- chrome.exe (PID: 4056)
- Native-Component.exe (PID: 2848)
Creates files or folders in the user directory
- Native-Component.exe (PID: 2848)
- AutoControlZero.exe (PID: 3592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
93
Monitored processes
50
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | ping localhost -n 3 | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3968 --field-trial-handle=1160,i,3390995333548598115,10063178112097487220,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3600 --field-trial-handle=1160,i,3390995333548598115,10063178112097487220,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3476 --field-trial-handle=1160,i,3390995333548598115,10063178112097487220,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=2320 --field-trial-handle=1160,i,3390995333548598115,10063178112097487220,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1420 --field-trial-handle=1160,i,3390995333548598115,10063178112097487220,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=4456 --field-trial-handle=1160,i,3390995333548598115,10063178112097487220,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://chrome.google.com/webstore/detail/autocontrol-keyboard-shor/lkaihdpfpifdlgoapbfocpmekbokmcfd" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3684 --field-trial-handle=1160,i,3390995333548598115,10063178112097487220,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3364 --field-trial-handle=1160,i,3390995333548598115,10063178112097487220,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
27 768
Read events
27 615
Write events
150
Delete events
3
Modification events
| (PID) Process: | (1088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
8
Suspicious files
147
Text files
473
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3676 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:E8CB74E142399AAFFE1B3D5197D063B5 | SHA256:5475566D32B02CF46E150613CFC00DF4658335439281224FF4AE37081FF2036F | |||
| 3676 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E87CE99F124623F95572A696C80EFCAF_9FBD3BA6168F3C4317F2AAB1E548FE96 | binary | |
MD5:BB6F7CB0560AA31970D2993DFEE19C05 | SHA256:A181CA8EEE71B93A132F181BC7279B18EC65477A164878E5339841F1802E1ACB | |||
| 3676 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\m=consumer[1].js | text | |
MD5:CF7F9FBF99E8DC1B65875E94059E8411 | SHA256:1F0A643969CCFE9F07E1ABEB1FDD5E67D02109BA224942CA5DD11E0B6F3D505D | |||
| 3676 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:8DD4DFC7BD1B8A14B85CE0EA9F5373C7 | SHA256:57898C6E727E7CE0BB595E7E710C8395CE5C3EA4FFF5AAB831E2F101343D2276 | |||
| 3676 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\lkaihdpfpifdlgoapbfocpmekbokmcfd[1].htm | html | |
MD5:513A08F046ABD701C12660A851C5D24C | SHA256:8790EB2A5D861B6C7D89FD142A7AB102FACA7B55F6C25A5BDDB55FAC99385DC7 | |||
| 3676 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\5X9A3JUV.txt | text | |
MD5:CDB136B928FC1789A45B6BCBE83FBCCF | SHA256:E5BC869F797AA9784FCCA56238158A7EBF34361657FF324C7175C8D55F3EED0D | |||
| 3676 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\rs=AAxzQIW0c2tDwnfx_QJLw0SPQwr3YV19_g[1].css | text | |
MD5:1995AEC9BEF693D4710127A74CB5F940 | SHA256:5208EECB457C642FA55FC89CADBCED77A5B900D682EF4AA2C8E44E3EDC582CD9 | |||
| 3676 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:4B5E158A06994A92501A2ABA449C8FE2 | SHA256:3987CE3969746BF195F4B4FD6C9274D10E738FEE176F748D18638799D29B6C70 | |||
| 3676 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:D62EE607524CD6AC5E14E1E27A8CC35A | SHA256:038C9D31C45B2406D65C721EB0E04FF57C76510D974D640B6EB851EA6531115B | |||
| 3676 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F2DDCD2B5F37625B82E81F4976CEE400_BB0E5383BB6E3CF78C8AC8388DB6A7BF | binary | |
MD5:AA3287399CE8F2AFAF18EC9995660DE1 | SHA256:F77AAFCE9E8E6BDC213D0D1AD6AEFD3AF5856D0ECFB99F5F6E4A0E8BB283E570 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
102
DNS requests
76
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3676 | iexplore.exe | GET | 200 | 23.53.40.10:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ae379654bbbca709 | DE | compressed | 4.66 Kb | unknown |
3676 | iexplore.exe | GET | 200 | 23.53.40.10:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?25fa4254fbf74a53 | DE | compressed | 4.66 Kb | unknown |
3676 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | binary | 1.41 Kb | unknown |
3676 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGpYRvzN3kAuEMlMWsqSFLc%3D | US | binary | 471 b | unknown |
3676 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | binary | 724 b | unknown |
3676 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCoEWSzoUVcHQncueI8VZKp | US | binary | 472 b | unknown |
3676 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCZXmpIP%2Bo%2BHhJmodADfw%2Fc | US | binary | 472 b | unknown |
3676 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQClj3zJOwEs2AlR6v%2BfUXog | US | binary | 472 b | unknown |
3044 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEA1uFYrLabZxEtE2U5X5DGM%3D | US | binary | 471 b | unknown |
1080 | svchost.exe | GET | 200 | 95.101.54.112:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?050227ea171c2f81 | DE | compressed | 65.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
3676 | iexplore.exe | 142.250.186.46:443 | chrome.google.com | GOOGLE | US | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3676 | iexplore.exe | 23.53.40.10:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3676 | iexplore.exe | 172.217.18.99:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
3676 | iexplore.exe | 142.250.181.227:443 | www.gstatic.com | GOOGLE | US | whitelisted |
3676 | iexplore.exe | 216.58.206.40:443 | www.googletagmanager.com | GOOGLE | US | unknown |
1088 | iexplore.exe | 172.217.18.4:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
chrome.google.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| whitelisted |
region1.google-analytics.com |
| whitelisted |
apis.google.com |
| whitelisted |