| download: | Secutrans.exe |
| Full analysis: | https://app.any.run/tasks/5d0d0b76-c0f3-48b6-b100-b213389c5495 |
| Verdict: | Malicious activity |
| Analysis date: | March 11, 2021, 08:30:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B9A10837AC24C43E008BD6121BA14367 |
| SHA1: | 26FCFB7D9C39D64E27BAF4AB940EDFF8792204D3 |
| SHA256: | 25CAAD5E3121392E5C3B421E5F6936FABBDFEE59E90AC1E2A27A3A2A6EAF9961 |
| SSDEEP: | 3072:zmJJ1xiRt79XcfsFPlKU2m+vad+bGtfUTi3:zmL1xiRtAsFdKUgvaVmS |
MALICIOUS
Changes settings of System certificates
- svchost.exe (PID: 1052)
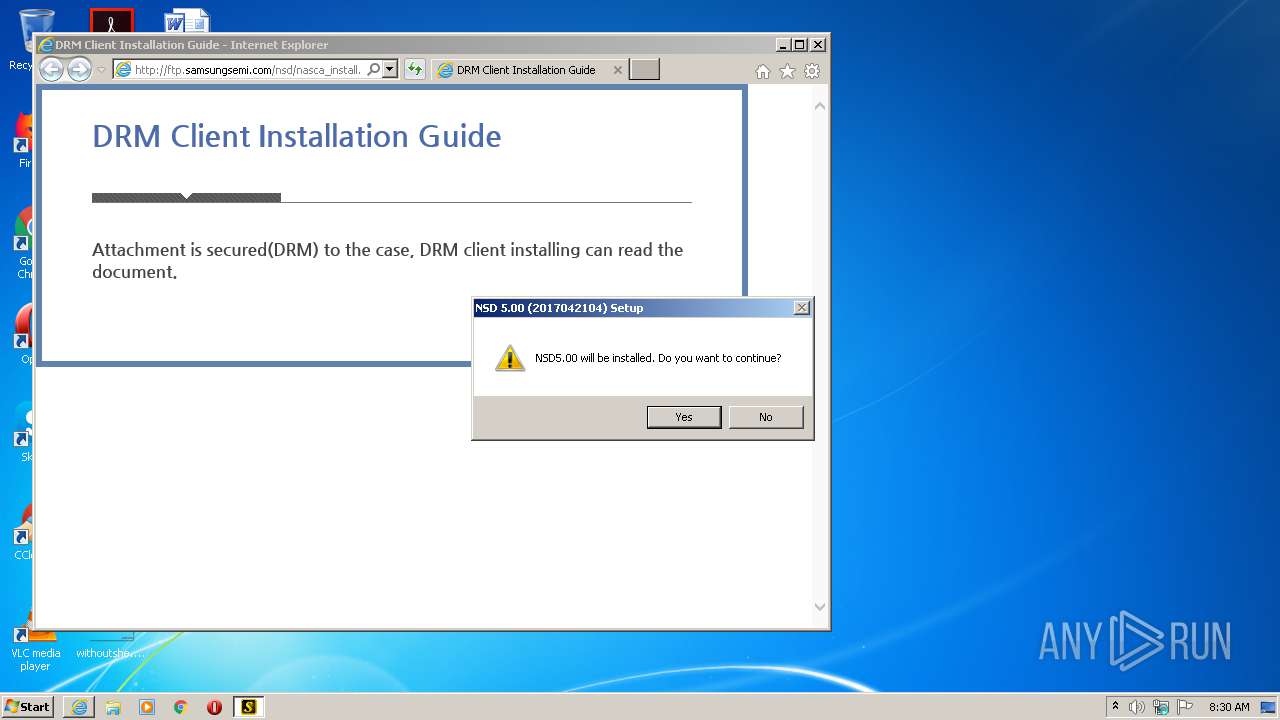
Application was dropped or rewritten from another process
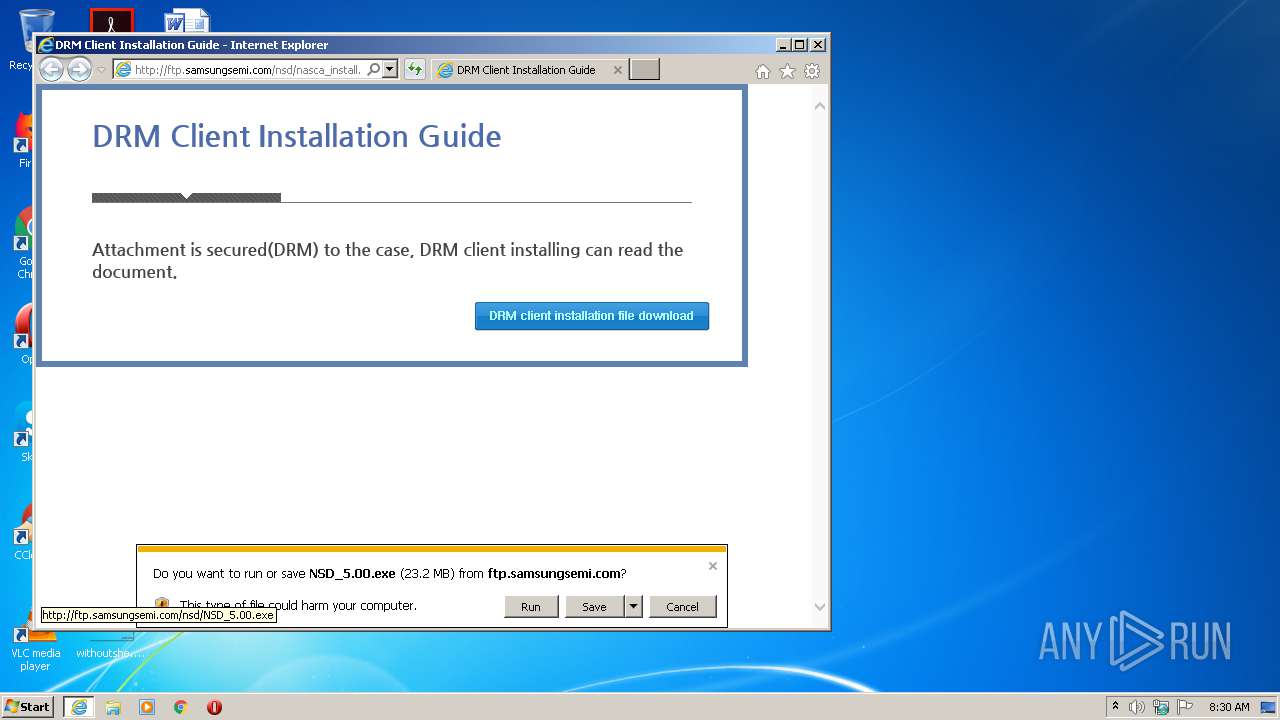
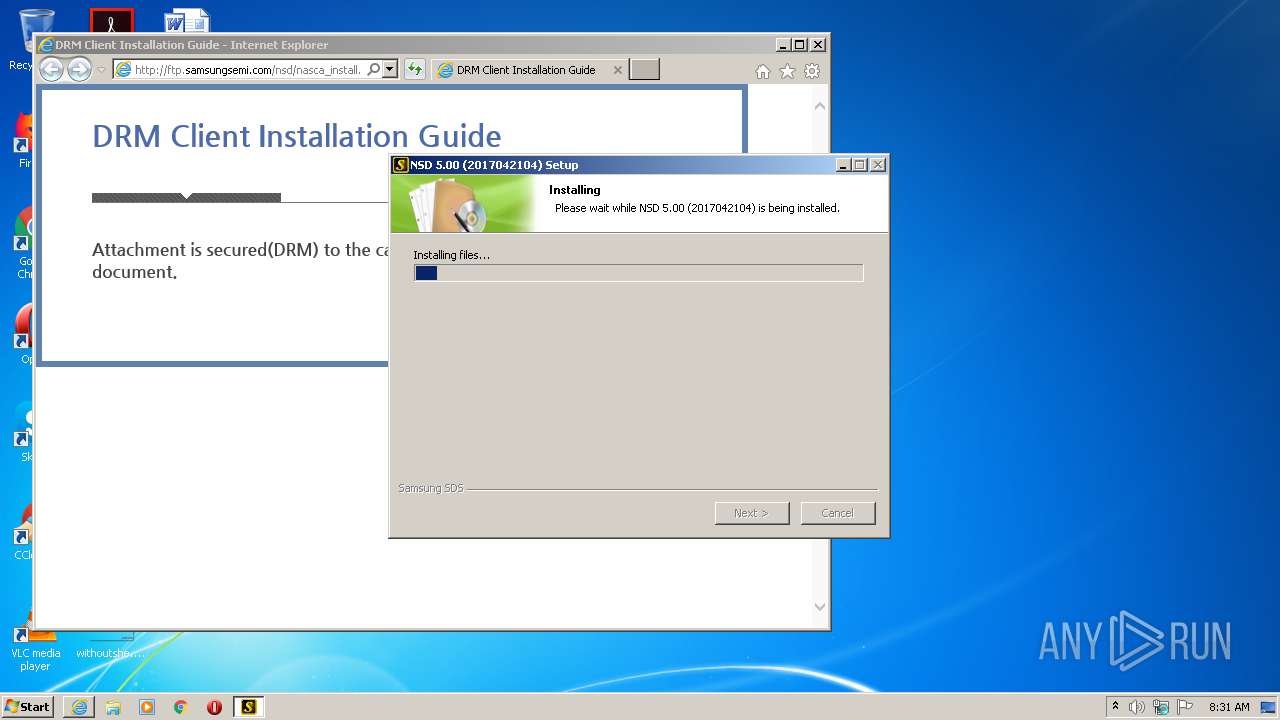
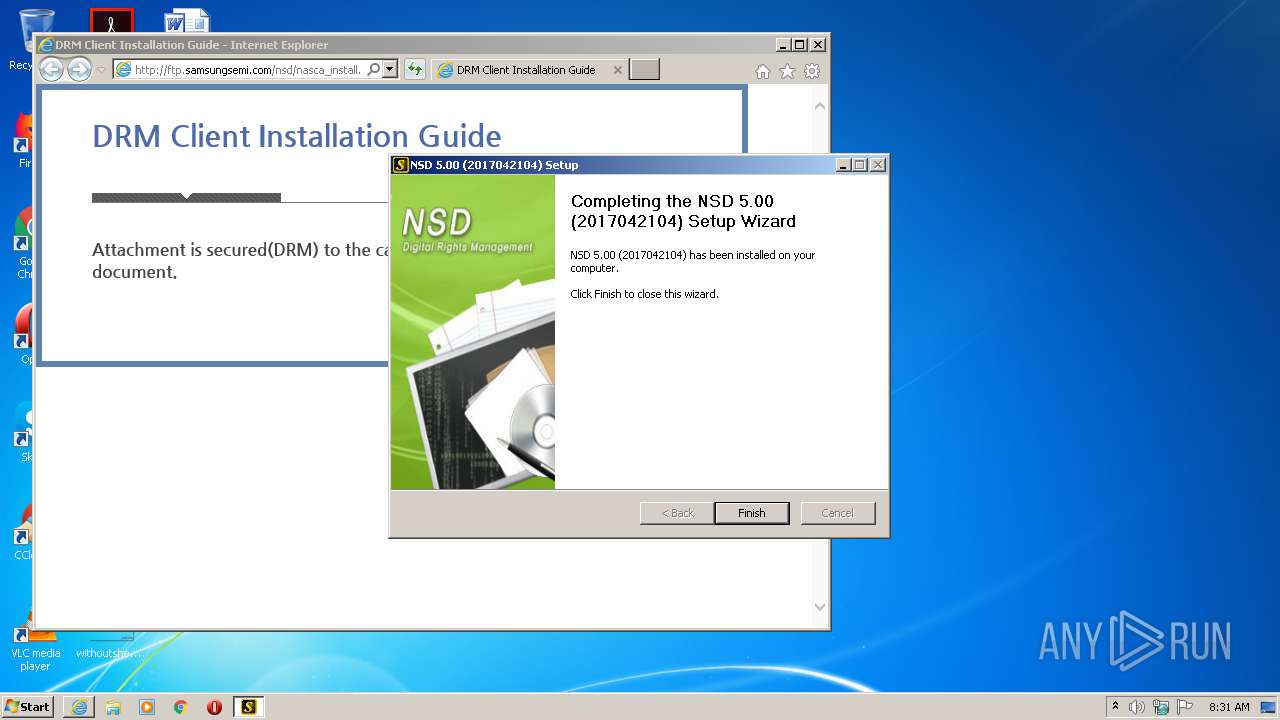
- NSD_5.00.exe (PID: 3504)
- NSD_5.00.exe (PID: 3840)
- pcdrmsvc.exe (PID: 2344)
- convini.exe (PID: 4076)
- pcdrmsvc.exe (PID: 884)
- nscfw.exe (PID: 748)
- nschim.exe (PID: 2080)
- convini.exe (PID: 4068)
Drops executable file immediately after starts
- NSD_5.00.exe (PID: 3840)
Loads dropped or rewritten executable
- NSD_5.00.exe (PID: 3840)
- regsvr32.exe (PID: 2568)
- regsvr32.exe (PID: 4028)
- regsvr32.exe (PID: 2348)
- wininit.exe (PID: 384)
- lsass.exe (PID: 488)
- services.exe (PID: 480)
- lsm.exe (PID: 496)
- svchost.exe (PID: 804)
- svchost.exe (PID: 844)
- svchost.exe (PID: 760)
- svchost.exe (PID: 872)
- svchost.exe (PID: 676)
- svchost.exe (PID: 596)
- svchost.exe (PID: 1840)
- IMEDICTUPDATE.EXE (PID: 1372)
- dwm.exe (PID: 288)
- taskeng.exe (PID: 2020)
- ctfmon.exe (PID: 976)
- SearchIndexer.exe (PID: 1064)
- explorer.exe (PID: 568)
- svchost.exe (PID: 1052)
- spoolsv.exe (PID: 1196)
- svchost.exe (PID: 1236)
- taskhost.exe (PID: 2004)
- SearchFilterHost.exe (PID: 3200)
- SearchProtocolHost.exe (PID: 3180)
- svchost.exe (PID: 2268)
- svchost.exe (PID: 3456)
- VSSVC.exe (PID: 3416)
- Secutrans.exe (PID: 2620)
- iexplore.exe (PID: 2176)
- host.exe (PID: 2400)
- iexplore.exe (PID: 2500)
- SearchProtocolHost.exe (PID: 3492)
- net1.exe (PID: 2708)
- net.exe (PID: 524)
- pcdrmsvc.exe (PID: 884)
- nschim.exe (PID: 2080)
Registers / Runs the DLL via REGSVR32.EXE
- NSD_5.00.exe (PID: 3840)
Starts NET.EXE for service management
- NSD_5.00.exe (PID: 3840)
Application was injected by another process
- wininit.exe (PID: 384)
- services.exe (PID: 480)
- svchost.exe (PID: 596)
- svchost.exe (PID: 1236)
- spoolsv.exe (PID: 1196)
- svchost.exe (PID: 1840)
- svchost.exe (PID: 844)
- svchost.exe (PID: 760)
- IMEDICTUPDATE.EXE (PID: 1372)
- taskeng.exe (PID: 2020)
- dwm.exe (PID: 288)
- lsass.exe (PID: 488)
- lsm.exe (PID: 496)
- svchost.exe (PID: 1052)
- svchost.exe (PID: 872)
- svchost.exe (PID: 2268)
- SearchIndexer.exe (PID: 1064)
- svchost.exe (PID: 3456)
- msiexec.exe (PID: 3372)
- SearchFilterHost.exe (PID: 3200)
- VSSVC.exe (PID: 3416)
- SearchProtocolHost.exe (PID: 3492)
- host.exe (PID: 2400)
- explorer.exe (PID: 568)
- ctfmon.exe (PID: 976)
- SearchProtocolHost.exe (PID: 3180)
- srvpost.exe (PID: 3772)
- svchost.exe (PID: 676)
- svchost.exe (PID: 804)
Runs injected code in another process
- nschim.exe (PID: 2080)
SUSPICIOUS
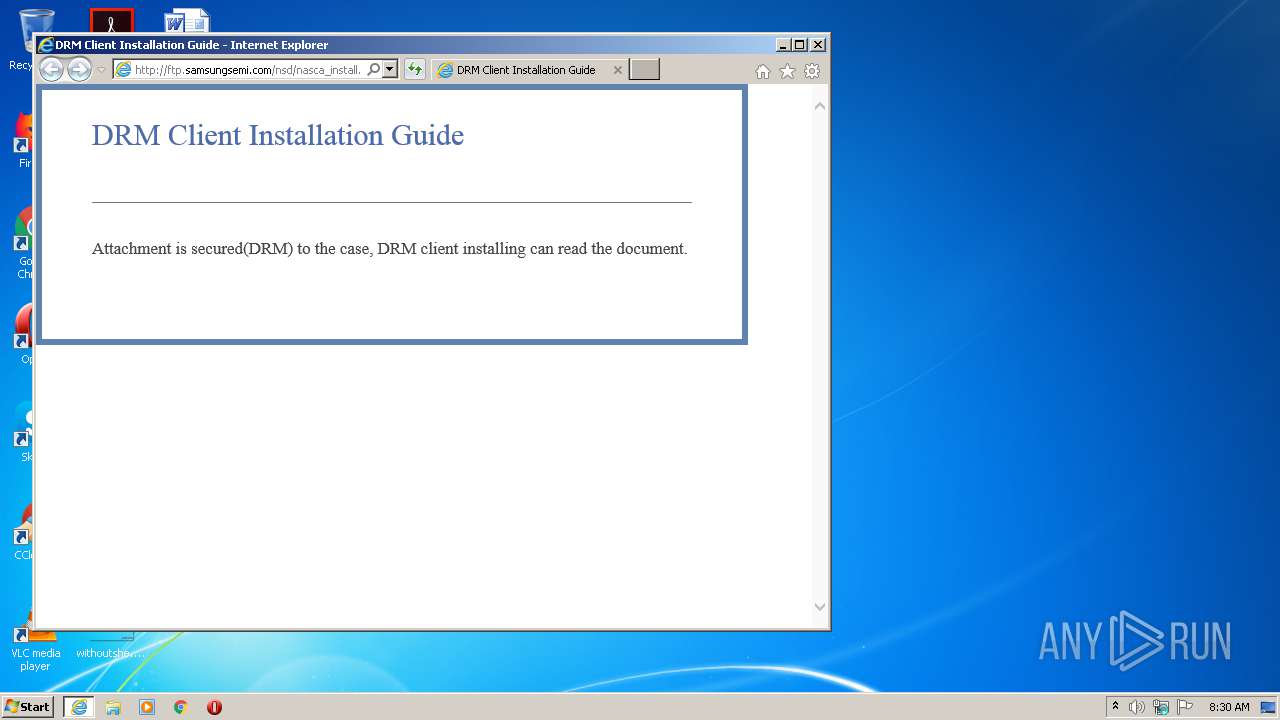
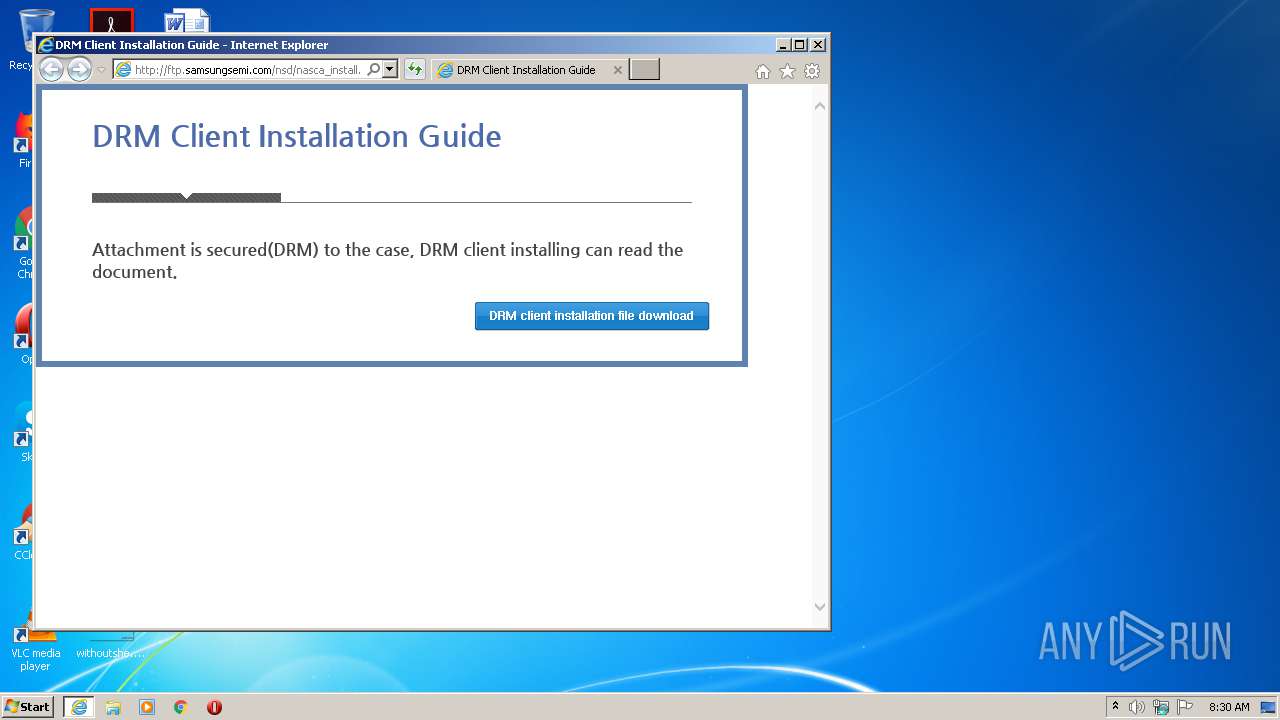
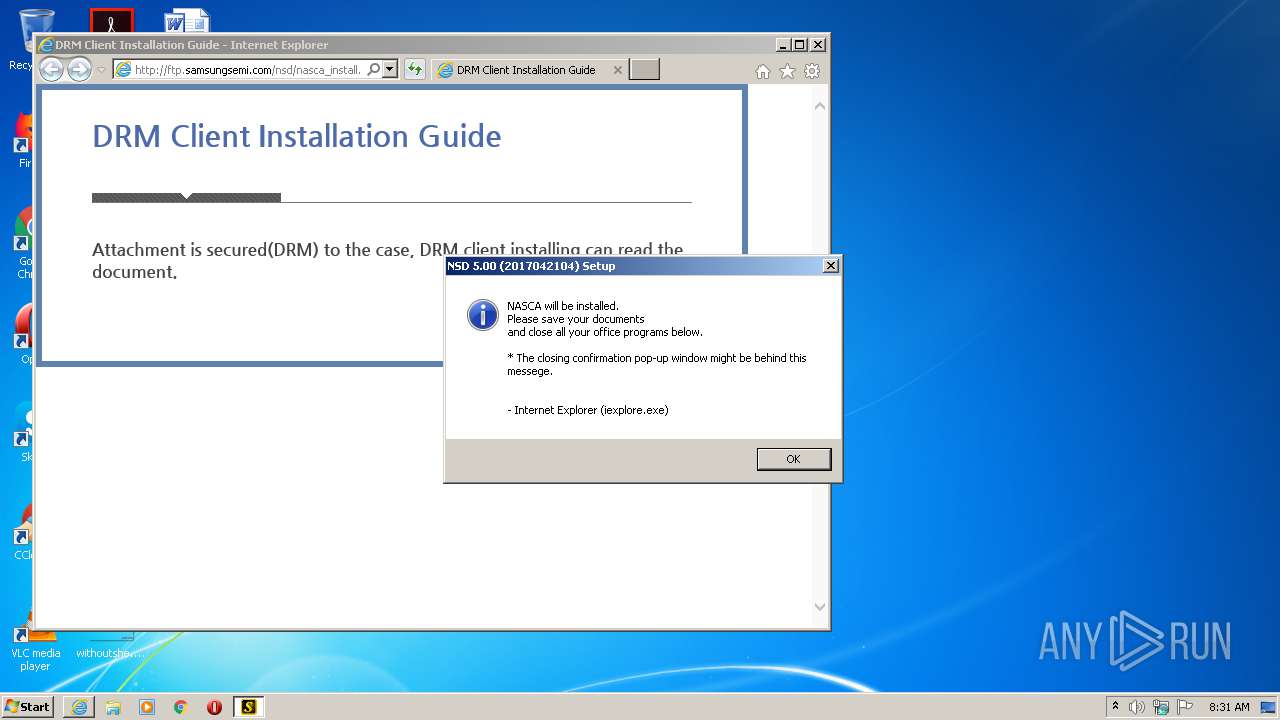
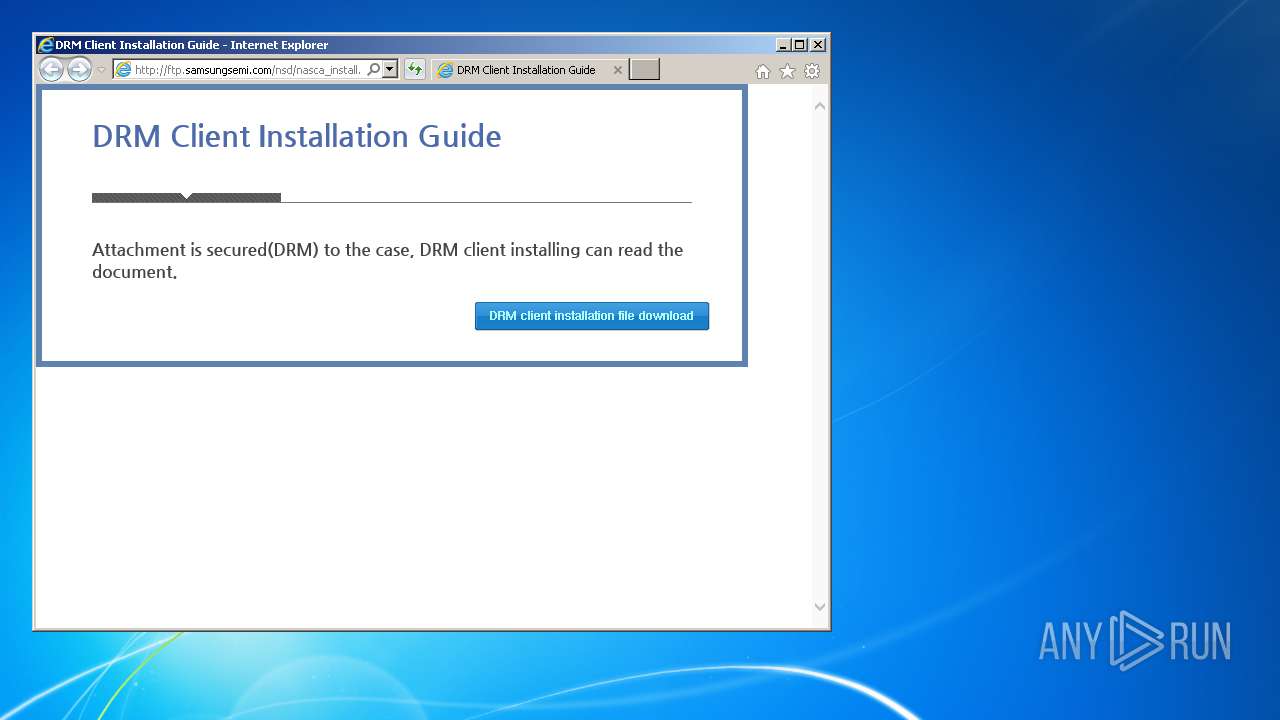
Starts Internet Explorer
- Secutrans.exe (PID: 2620)
Drops a file with too old compile date
- iexplore.exe (PID: 2176)
- NSD_5.00.exe (PID: 3840)
Executable content was dropped or overwritten
- iexplore.exe (PID: 2176)
- NSD_5.00.exe (PID: 3840)
Creates files in the program directory
- SearchIndexer.exe (PID: 1064)
- NSD_5.00.exe (PID: 3840)
Adds / modifies Windows certificates
- svchost.exe (PID: 1052)
Drops a file that was compiled in debug mode
- NSD_5.00.exe (PID: 3840)
Removes files from Windows directory
- NSD_5.00.exe (PID: 3840)
Uses NETSH.EXE for network configuration
- NSD_5.00.exe (PID: 3840)
Creates a directory in Program Files
- NSD_5.00.exe (PID: 3840)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 2568)
- regsvr32.exe (PID: 2348)
- regsvr32.exe (PID: 4028)
Creates a software uninstall entry
- NSD_5.00.exe (PID: 3840)
Creates files in the Windows directory
- pcdrmsvc.exe (PID: 2344)
- NSD_5.00.exe (PID: 3840)
- nschim.exe (PID: 2080)
- pcdrmsvc.exe (PID: 884)
- convini.exe (PID: 4068)
- explorer.exe (PID: 568)
Changes default file association
- pcdrmsvc.exe (PID: 2344)
- pcdrmsvc.exe (PID: 884)
Creates or modifies windows services
- services.exe (PID: 480)
- pcdrmsvc.exe (PID: 2344)
- pcdrmsvc.exe (PID: 884)
- nschim.exe (PID: 2080)
Executed as Windows Service
- pcdrmsvc.exe (PID: 884)
Low-level read access rights to disk partition
- NSD_5.00.exe (PID: 3840)
INFO
Reads internet explorer settings
- iexplore.exe (PID: 2500)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2176)
Reads settings of System Certificates
- svchost.exe (PID: 1052)
- iexplore.exe (PID: 2176)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2176)
Changes settings of System certificates
- iexplore.exe (PID: 2176)
Changes internet zones settings
- iexplore.exe (PID: 2176)
Application launched itself
- iexplore.exe (PID: 2176)
Loads dropped or rewritten executable
- msiexec.exe (PID: 3372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:12:03 06:38:33+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 65536 |
| InitializedDataSize: | 94208 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8b89 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2014.12.3.23 |
| ProductVersionNumber: | 2014.12.3.23 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Korean |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | |
| FileDescription: | NASCAInfoCollector |
| FileVersion: | 2014, 12, 3, 23 |
| InternalName: | NASCAInfoCollector |
| LegalCopyright: | Copyright ⓒ 2014 |
| LegalTrademarks: | - |
| OriginalFileName: | NASCAInfoCollector.exe |
| PrivateBuild: | - |
| ProductName: | NASCAInfoCollector |
| ProductVersion: | 2014, 12, 3, 23 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Dec-2014 05:38:33 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | NASCAInfoCollector |
| FileVersion: | 2014, 12, 3, 23 |
| InternalName: | NASCAInfoCollector |
| LegalCopyright: | Copyright ⓒ 2014 |
| LegalTrademarks: | - |
| OriginalFilename: | NASCAInfoCollector.exe |
| PrivateBuild: | - |
| ProductName: | NASCAInfoCollector |
| ProductVersion: | 2014, 12, 3, 23 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 03-Dec-2014 05:38:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F265 | 0x00010000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47373 |
.rdata | 0x00011000 | 0x00004264 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.62602 |
.data | 0x00016000 | 0x0000A700 | 0x00009000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.27272 |
.rsrc | 0x00021000 | 0x00006A10 | 0x00007000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18263 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.45043 | 904 | UNKNOWN | Korean - Korea | RT_VERSION |
2 | 3.14388 | 744 | UNKNOWN | Korean - Korea | RT_ICON |
3 | 3.03 | 296 | UNKNOWN | Korean - Korea | RT_ICON |
4 | 3.43825 | 3752 | UNKNOWN | Korean - Korea | RT_ICON |
5 | 3.2186 | 2216 | UNKNOWN | Korean - Korea | RT_ICON |
6 | 2.07287 | 1384 | UNKNOWN | Korean - Korea | RT_ICON |
7 | 5.36445 | 9640 | UNKNOWN | Korean - Korea | RT_ICON |
8 | 5.61095 | 4264 | UNKNOWN | Korean - Korea | RT_ICON |
9 | 5.54256 | 1128 | UNKNOWN | Korean - Korea | RT_ICON |
101 | 4.41032 | 354 | UNKNOWN | Korean - Korea | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
Total processes
74
Monitored processes
54
Malicious processes
39
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | netsh advfirewall firewall add rule name="PC-DRM-P4" dir=out action=allow protocol=UDP localport=15036 | C:\Windows\system32\netsh.exe | — | NSD_5.00.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 288 | "C:\Windows\system32\Dwm.exe" | C:\Windows\System32\dwm.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 384 | wininit.exe | C:\Windows\System32\wininit.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Start-Up Application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 480 | C:\Windows\system32\services.exe | C:\Windows\System32\services.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Services and Controller app Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 488 | C:\Windows\system32\lsass.exe | C:\Windows\System32\lsass.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Local Security Authority Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 496 | C:\Windows\system32\lsm.exe | C:\Windows\System32\lsm.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Local Session Manager Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 524 | "C:\Windows\system32\net.exe" start PcdrmSvc | C:\Windows\system32\net.exe | — | NSD_5.00.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 568 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 596 | C:\Windows\system32\svchost.exe -k DcomLaunch | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 676 | C:\Windows\system32\svchost.exe -k RPCSS | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 091
Read events
3 312
Write events
763
Delete events
16
Modification events
| (PID) Process: | (2620) Secutrans.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2620) Secutrans.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3679602522 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30873168 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A6000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
59
Suspicious files
25
Text files
66
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2004 | taskhost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\V01.log | — | |
MD5:— | SHA256:— | |||
| 2004 | taskhost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\WebCacheV01.dat | — | |
MD5:— | SHA256:— | |||
| 844 | svchost.exe | C:\Windows\ServiceProfiles\LocalService\AppData\Local\~FontCache-S-1-5-21-1302019708-1500728564-335382590-1000.dat | — | |
MD5:— | SHA256:— | |||
| 2176 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF46412E6C6CBBA820.TMP | — | |
MD5:— | SHA256:— | |||
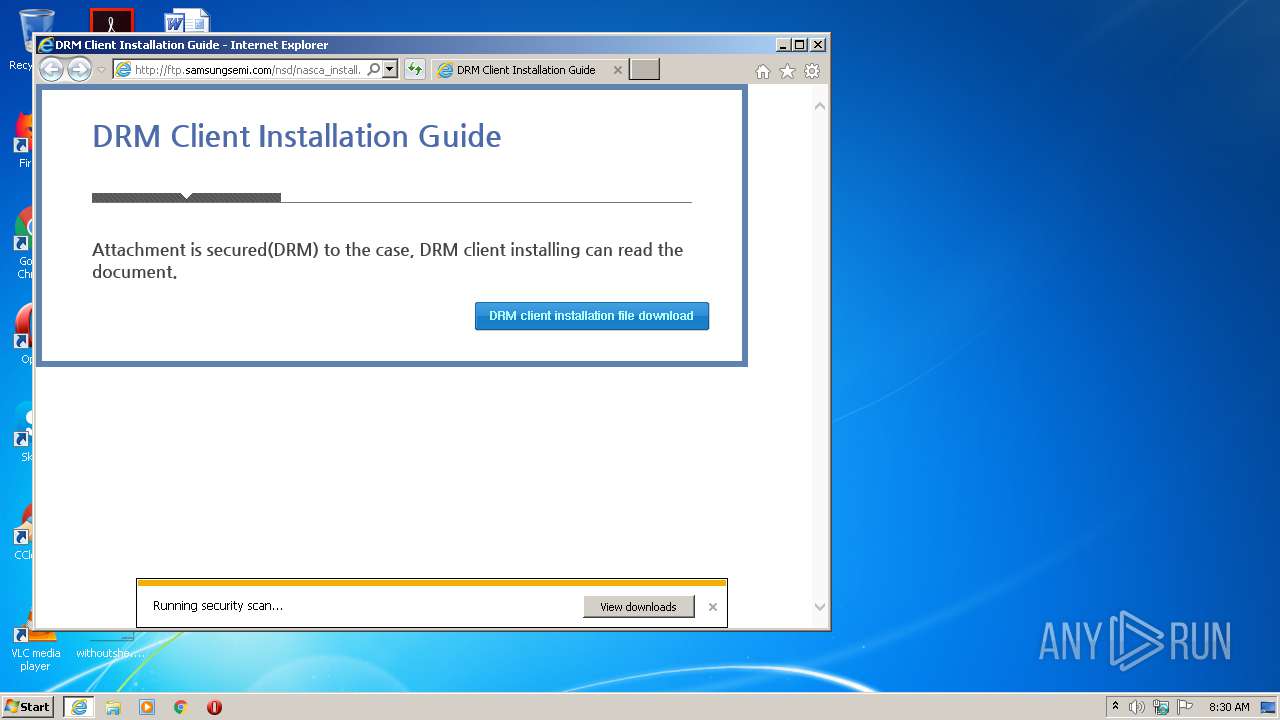
| 2500 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\NSD_5.00[1].exe | — | |
MD5:— | SHA256:— | |||
| 2500 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\NSD_5.00.exe.segrls0.partial | — | |
MD5:— | SHA256:— | |||
| 2176 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\NSD_5.00.exe.segrls0.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2176 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab5AAC.tmp | — | |
MD5:— | SHA256:— | |||
| 2176 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar5AAD.tmp | — | |
MD5:— | SHA256:— | |||
| 2176 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab5ABE.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
20
DNS requests
10
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
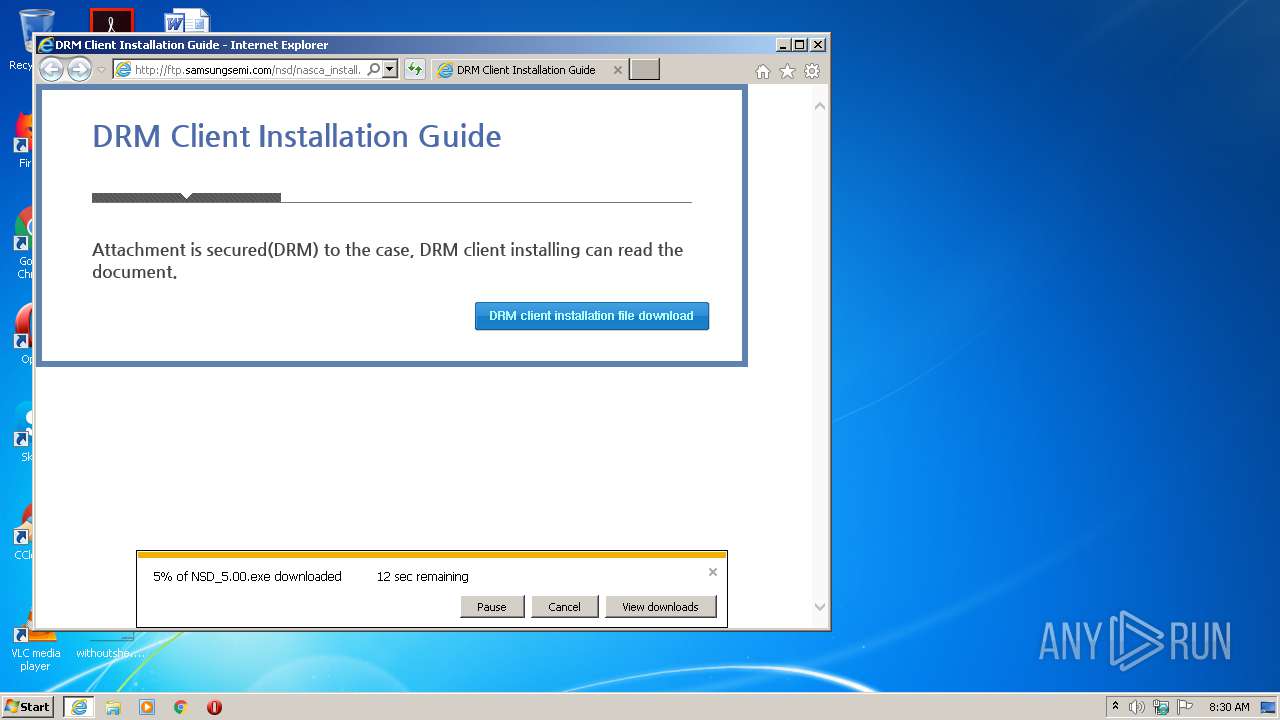
2500 | iexplore.exe | GET | 200 | 211.36.85.25:80 | http://ftp.samsungsemi.com/nsd/nasca_install.jsp?OS=34&INST=0&TYPE=1&COMP=&VER=&BUILD= | KR | html | 2.14 Kb | suspicious |
2500 | iexplore.exe | GET | 200 | 211.36.85.25:80 | http://ftp.samsungsemi.com/css/style.css | KR | text | 362 b | suspicious |
2500 | iexplore.exe | GET | 200 | 211.36.85.25:80 | http://ftp.samsungsemi.com/css/jquery-ui.min.css | KR | text | 29.4 Kb | suspicious |
2500 | iexplore.exe | GET | 200 | 211.36.85.25:80 | http://ftp.samsungsemi.com/js/common.js | KR | text | 13.3 Kb | suspicious |
2500 | iexplore.exe | GET | 200 | 211.36.85.25:80 | http://ftp.samsungsemi.com/css/common.css | KR | text | 6.59 Kb | suspicious |
2500 | iexplore.exe | GET | 200 | 211.36.85.25:80 | http://ftp.samsungsemi.com/js/jquery.form.js | KR | text | 41.2 Kb | suspicious |
2500 | iexplore.exe | GET | 200 | 211.36.85.25:80 | http://ftp.samsungsemi.com/images/sa/line.gif | KR | image | 1.18 Kb | suspicious |
2500 | iexplore.exe | GET | 200 | 211.36.85.25:80 | http://ftp.samsungsemi.com/js/jquery.blockUI.js | KR | text | 19.4 Kb | suspicious |
2500 | iexplore.exe | GET | 200 | 211.36.85.25:80 | http://ftp.samsungsemi.com/images/btn_pack.gif | KR | image | 8.68 Kb | suspicious |
2500 | iexplore.exe | GET | 200 | 211.36.85.25:80 | http://ftp.samsungsemi.com/js/json2.js | KR | text | 17.6 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2500 | iexplore.exe | 211.36.85.25:80 | ftp.samsungsemi.com | SamsungSDS Inc. | KR | suspicious |
2176 | iexplore.exe | 211.36.85.25:80 | ftp.samsungsemi.com | SamsungSDS Inc. | KR | suspicious |
2176 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2176 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2176 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2176 | iexplore.exe | 8.248.113.254:80 | www.download.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ftp.samsungsemi.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2500 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
NSD_5.00.exe | Load DLL |
NSD_5.00.exe | Init InstallProc : 38401414609 |
NSD_5.00.exe | START SUCCESS!!!!!! |