| File name: | Delta V3.61 b_08196012.exe |
| Full analysis: | https://app.any.run/tasks/5997eab1-d6ce-43ca-b487-6c21214884f8 |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2024, 04:36:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1198DAAA23F0AF650C7CD4555FBEF9E8 |
| SHA1: | 783F86460785027A41A84E41B42A05B4D4A1A462 |
| SHA256: | 25C846183E10BD2A146325EFFECDDBABF0F390717FD11D597012A033E6DAF600 |
| SSDEEP: | 98304:pQR6VdJ09uqigD3RAMF6LgaZze6wXCawiMVQwP3F1PwuQqkZObuyX+QuZUREMsLb:A1+GiB+ |
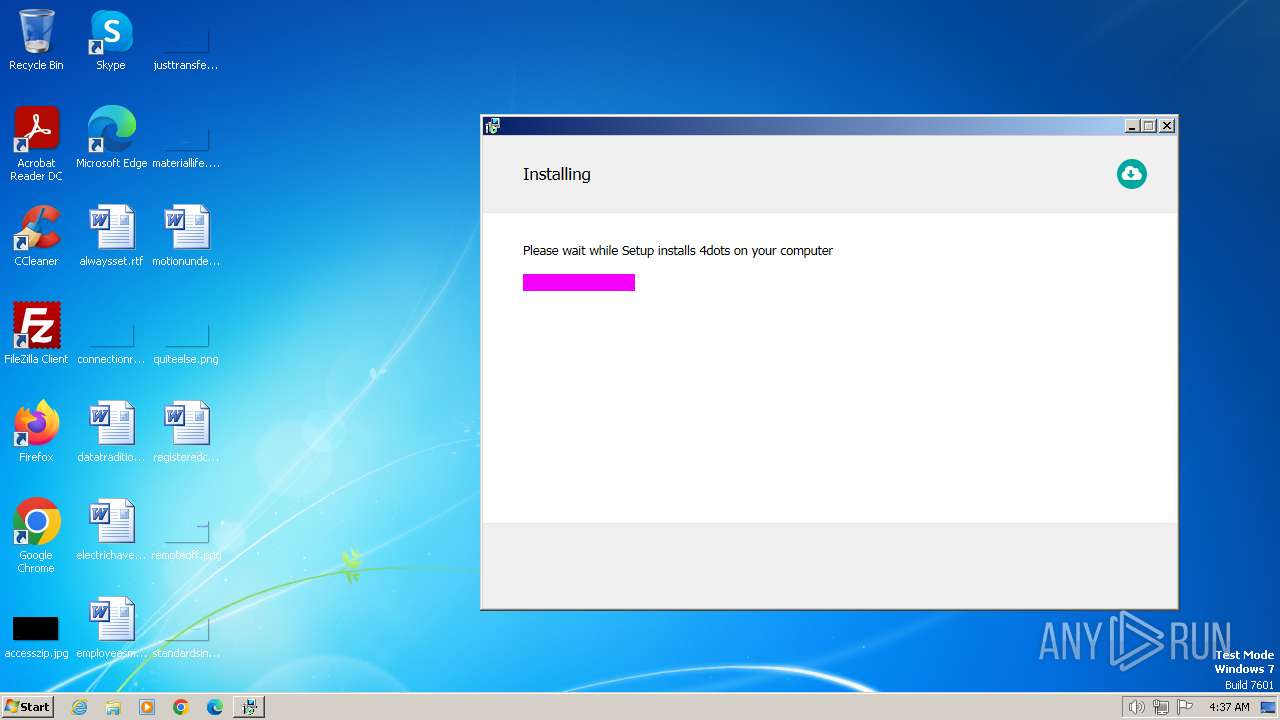
MALICIOUS
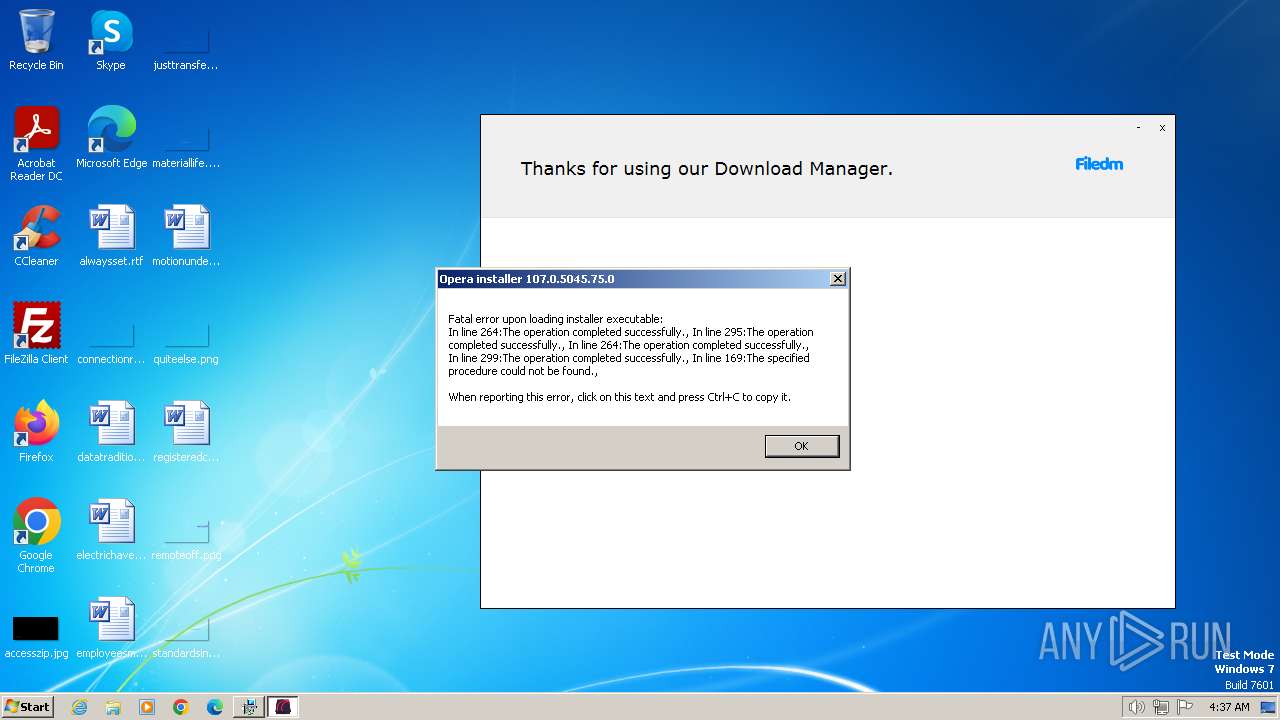
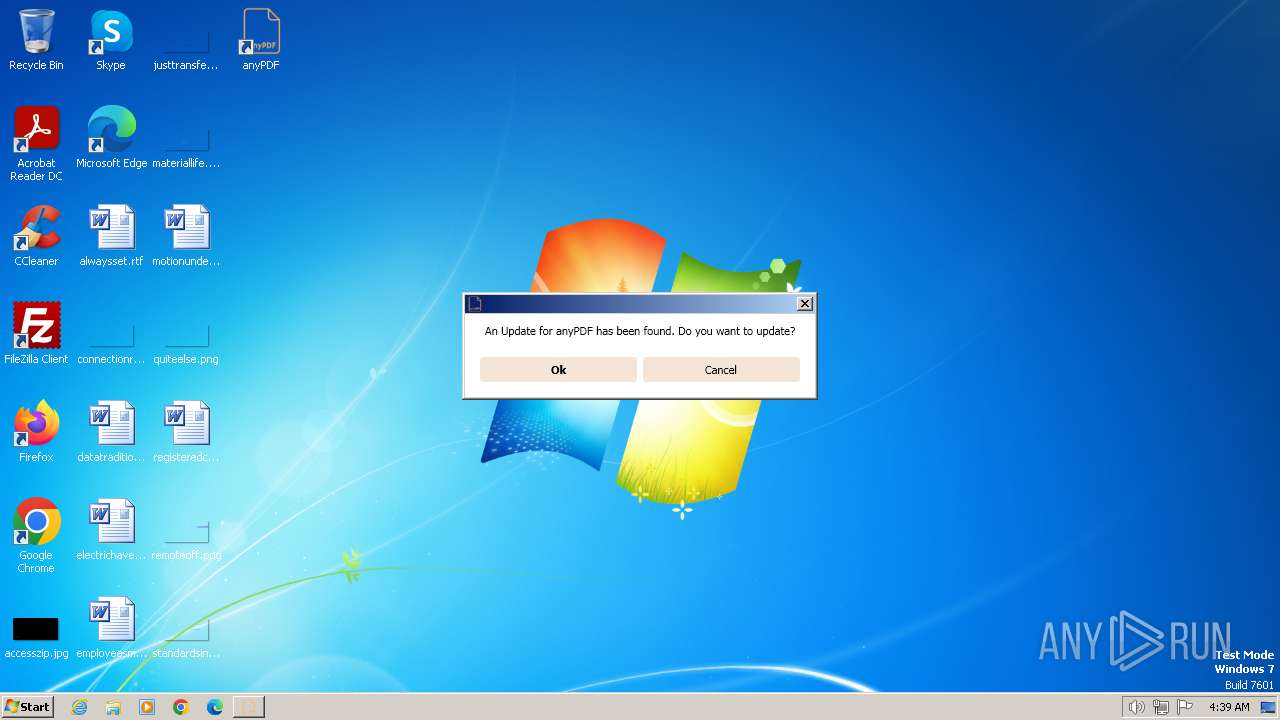
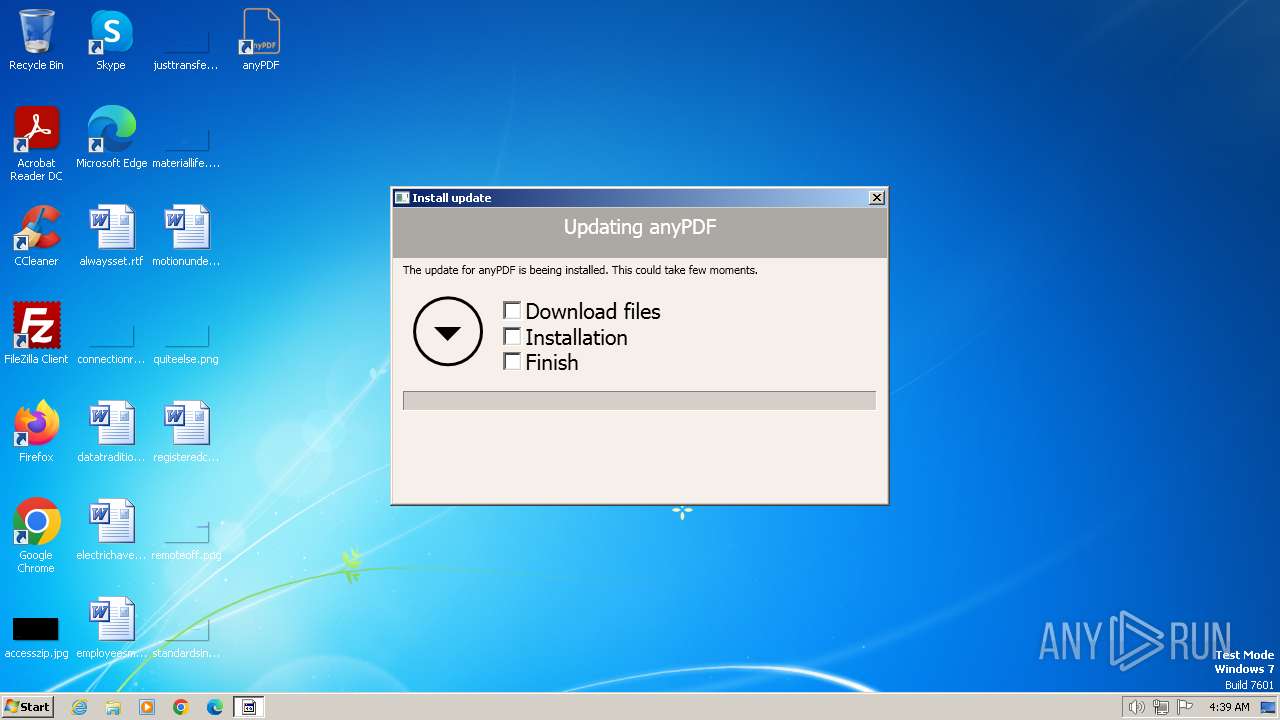
Drops the executable file immediately after the start
- Delta V3.61 b_08196012.exe (PID: 3392)
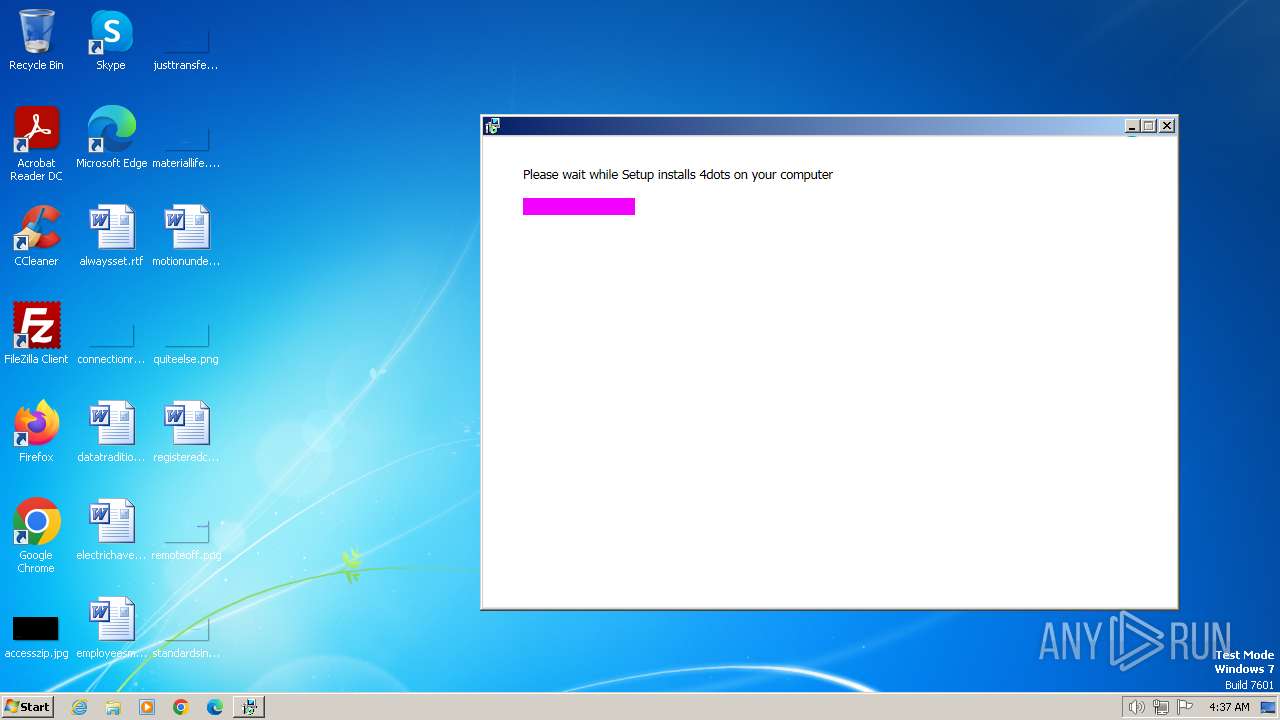
- setup08196012.exe (PID: 796)
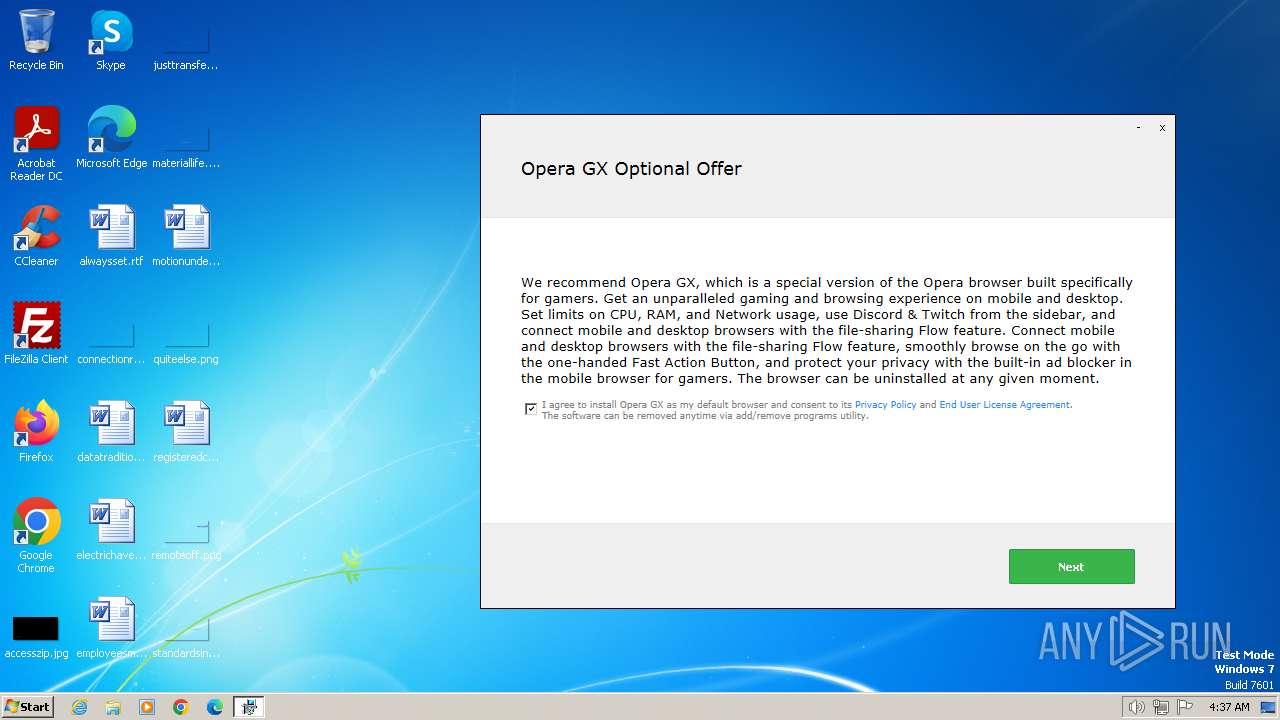
- OperaGX.exe (PID: 764)
- Downloader.exe (PID: 3956)
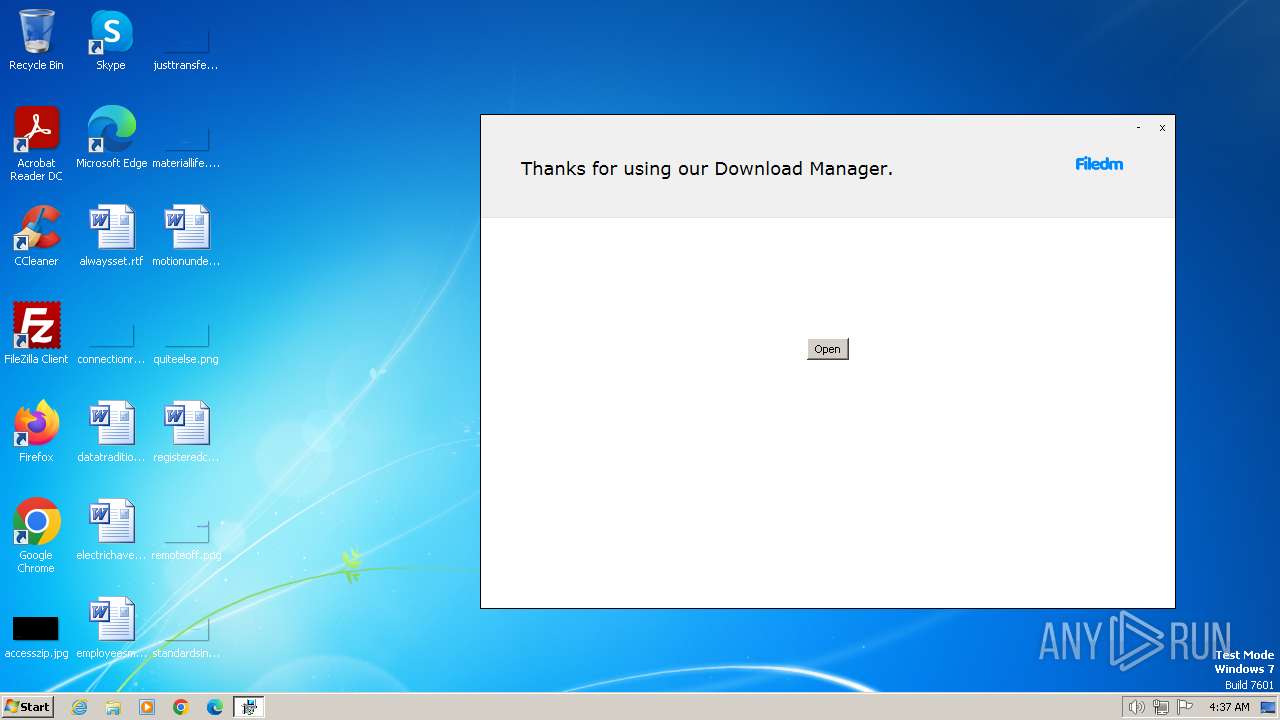
Actions looks like stealing of personal data
- setup08196012.exe (PID: 796)
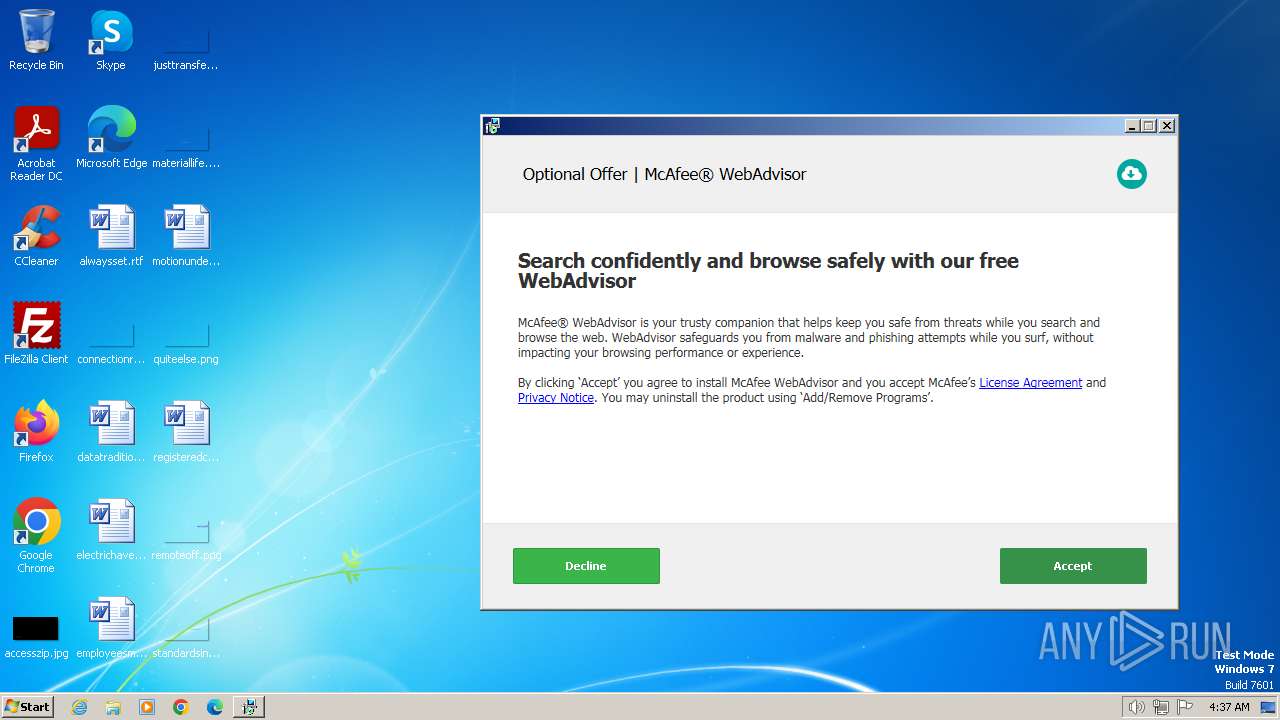
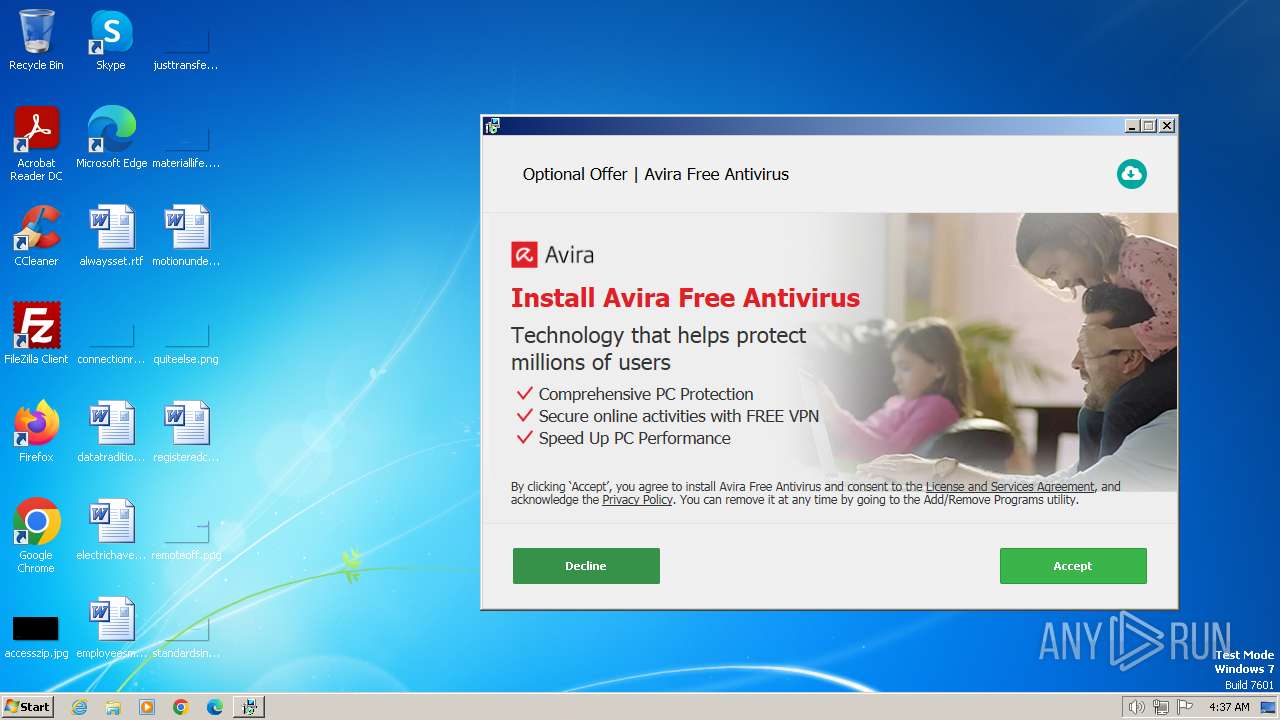
- OfferInstaller.exe (PID: 3544)
- PdfOpenDriver.exe (PID: 3584)
Changes the autorun value in the registry
- Downloader.exe (PID: 3956)
SUSPICIOUS
Reads settings of System Certificates
- Delta V3.61 b_08196012.exe (PID: 3392)
- setup08196012.exe (PID: 796)
- OfferInstaller.exe (PID: 3544)
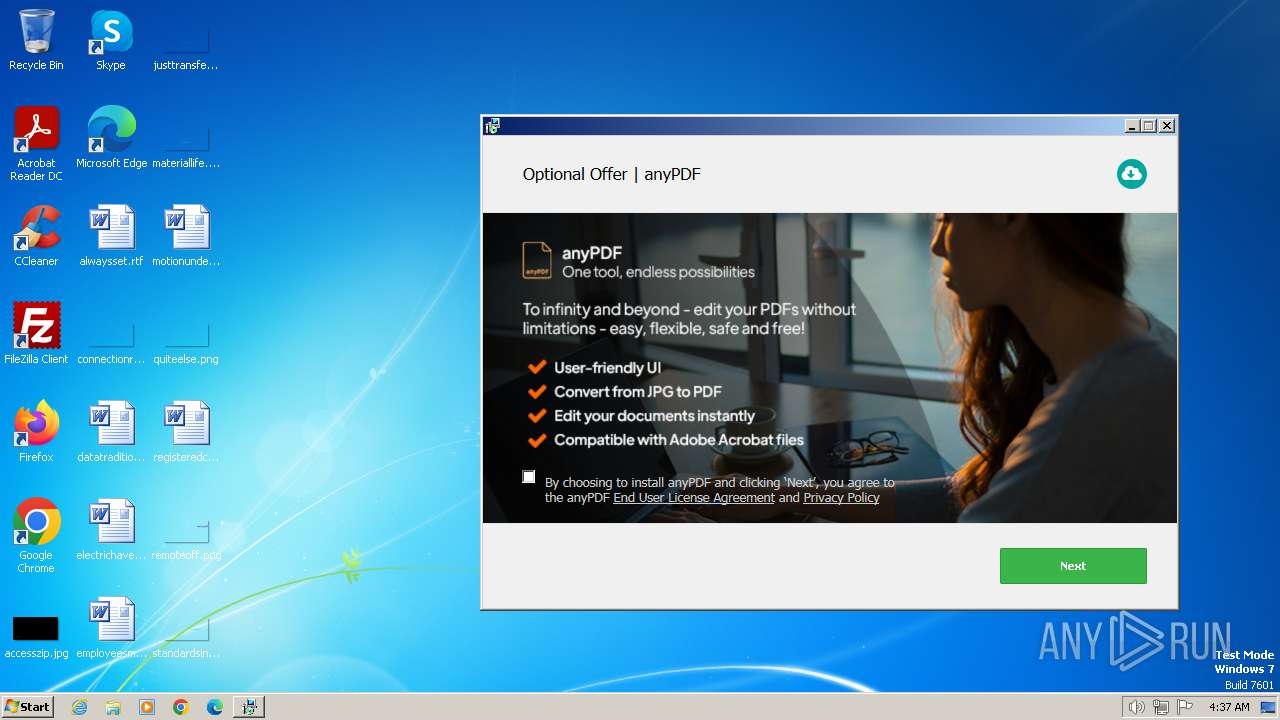
- anyPDF.exe (PID: 3664)
- Downloader.exe (PID: 3956)
- PdfOpenDriver.exe (PID: 3584)
- anyPDF.exe (PID: 2692)
- filezilla.exe (PID: 1852)
Reads the Internet Settings
- Delta V3.61 b_08196012.exe (PID: 3392)
- setup08196012.exe (PID: 796)
- setup08196012.exe (PID: 1768)
- OfferInstaller.exe (PID: 3544)
- cmd.exe (PID: 2588)
- anyPDF.exe (PID: 3664)
- Downloader.exe (PID: 3956)
- anyPDF.exe (PID: 2692)
- PdfOpenDriver.exe (PID: 3584)
Reads security settings of Internet Explorer
- Delta V3.61 b_08196012.exe (PID: 3392)
- setup08196012.exe (PID: 796)
- setup08196012.exe (PID: 1768)
- OfferInstaller.exe (PID: 3544)
- anyPDF.exe (PID: 3664)
- Downloader.exe (PID: 3956)
- anyPDF.exe (PID: 2692)
Checks Windows Trust Settings
- Delta V3.61 b_08196012.exe (PID: 3392)
- setup08196012.exe (PID: 796)
Executable content was dropped or overwritten
- Delta V3.61 b_08196012.exe (PID: 3392)
- setup08196012.exe (PID: 796)
- OperaGX.exe (PID: 764)
- Downloader.exe (PID: 3956)
The process drops C-runtime libraries
- setup08196012.exe (PID: 796)
Process drops legitimate windows executable
- setup08196012.exe (PID: 796)
- Downloader.exe (PID: 3956)
The process creates files with name similar to system file names
- setup08196012.exe (PID: 796)
Reads the Windows owner or organization settings
- setup08196012.exe (PID: 796)
- OfferInstaller.exe (PID: 3544)
Searches for installed software
- setup08196012.exe (PID: 796)
Adds/modifies Windows certificates
- Delta V3.61 b_08196012.exe (PID: 3392)
- setup08196012.exe (PID: 796)
Get information on the list of running processes
- cmd.exe (PID: 1864)
- cmd.exe (PID: 1376)
Executing commands from a ".bat" file
- setup08196012.exe (PID: 796)
- OfferInstaller.exe (PID: 3544)
Starts CMD.EXE for commands execution
- setup08196012.exe (PID: 796)
- OfferInstaller.exe (PID: 3544)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 1864)
- cmd.exe (PID: 1376)
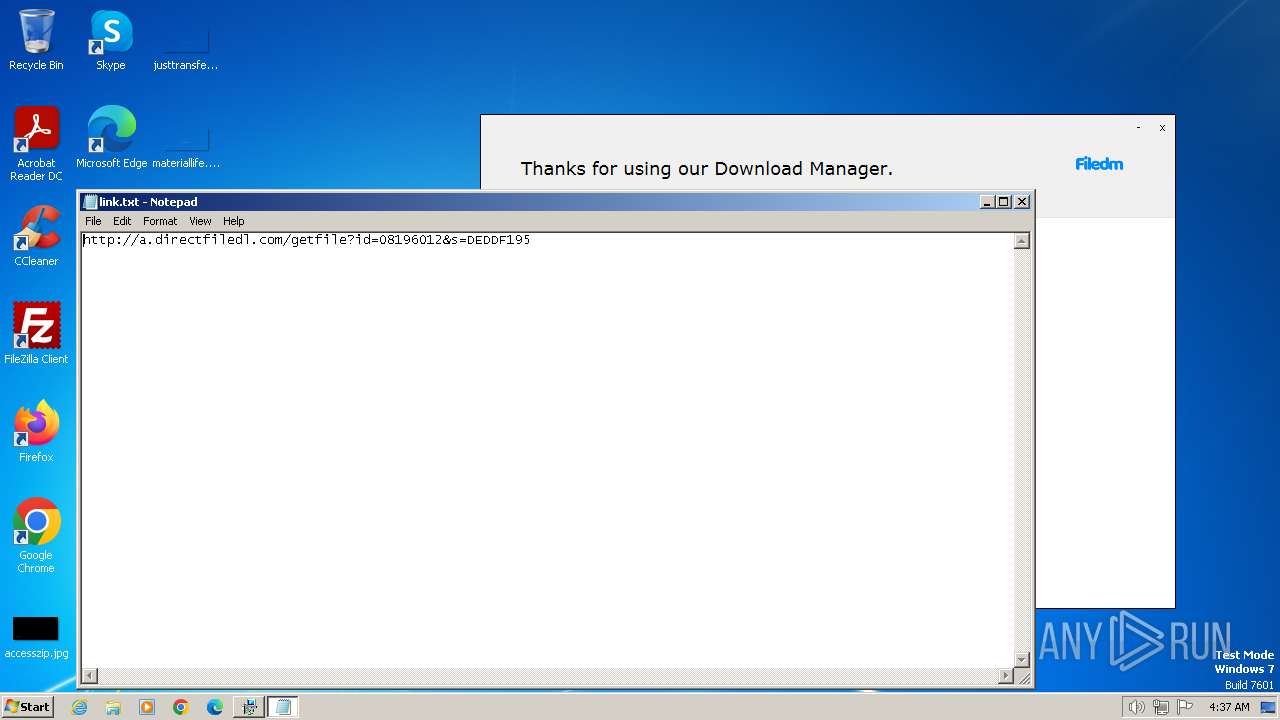
Start notepad (likely ransomware note)
- Delta V3.61 b_08196012.exe (PID: 3392)
INFO
Checks supported languages
- Delta V3.61 b_08196012.exe (PID: 3392)
- setup08196012.exe (PID: 796)
- OfferInstaller.exe (PID: 3544)
- setup08196012.exe (PID: 1768)
- OperaGX.exe (PID: 764)
- Downloader.exe (PID: 3956)
- anyPDF.exe (PID: 3664)
- anyPDF.exe (PID: 2692)
- PdfOpenDriver.exe (PID: 3584)
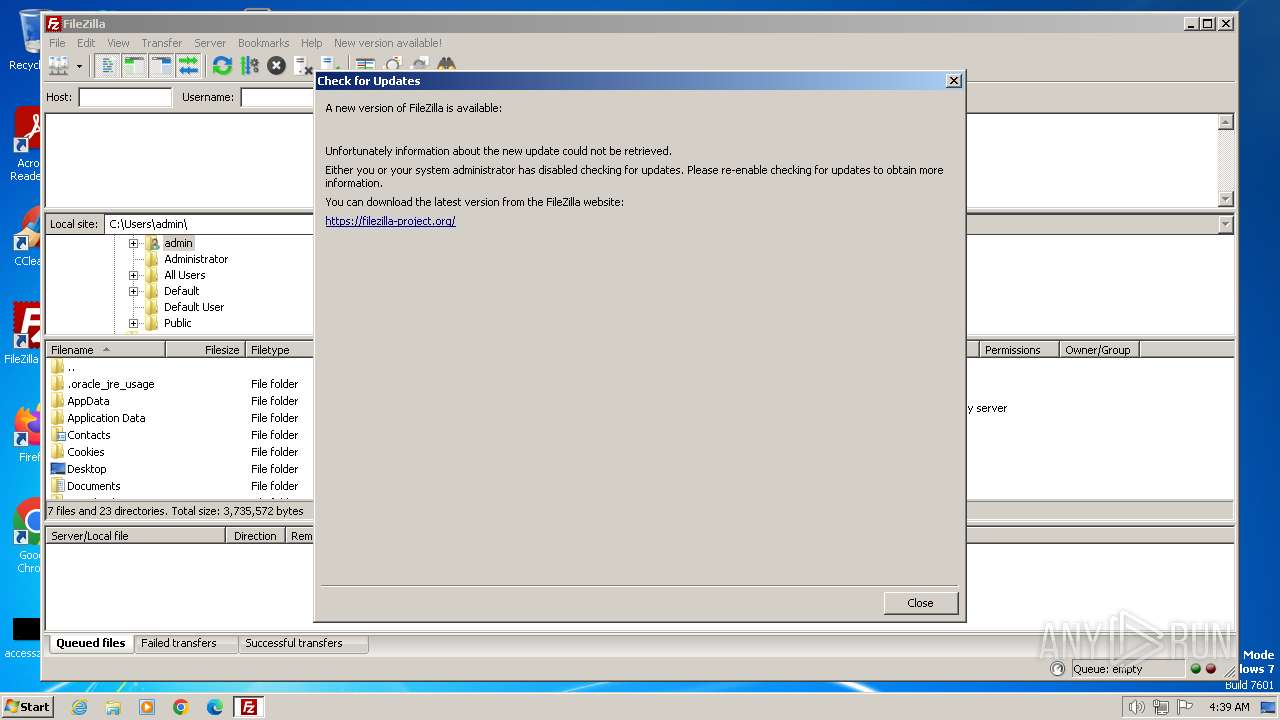
- filezilla.exe (PID: 1852)
Reads the computer name
- Delta V3.61 b_08196012.exe (PID: 3392)
- setup08196012.exe (PID: 796)
- OfferInstaller.exe (PID: 3544)
- setup08196012.exe (PID: 1768)
- Downloader.exe (PID: 3956)
- anyPDF.exe (PID: 3664)
- anyPDF.exe (PID: 2692)
- PdfOpenDriver.exe (PID: 3584)
- filezilla.exe (PID: 1852)
Checks proxy server information
- Delta V3.61 b_08196012.exe (PID: 3392)
Reads the machine GUID from the registry
- Delta V3.61 b_08196012.exe (PID: 3392)
- setup08196012.exe (PID: 796)
- setup08196012.exe (PID: 1768)
- OfferInstaller.exe (PID: 3544)
- Downloader.exe (PID: 3956)
- anyPDF.exe (PID: 3664)
- anyPDF.exe (PID: 2692)
- PdfOpenDriver.exe (PID: 3584)
- filezilla.exe (PID: 1852)
Reads the software policy settings
- Delta V3.61 b_08196012.exe (PID: 3392)
- setup08196012.exe (PID: 796)
- anyPDF.exe (PID: 3664)
- Downloader.exe (PID: 3956)
- anyPDF.exe (PID: 2692)
- PdfOpenDriver.exe (PID: 3584)
- OfferInstaller.exe (PID: 3544)
Creates files or folders in the user directory
- Delta V3.61 b_08196012.exe (PID: 3392)
- setup08196012.exe (PID: 796)
- OfferInstaller.exe (PID: 3544)
- OperaGX.exe (PID: 764)
- anyPDF.exe (PID: 3664)
- PdfOpenDriver.exe (PID: 3584)
- anyPDF.exe (PID: 2692)
- filezilla.exe (PID: 1852)
Create files in a temporary directory
- setup08196012.exe (PID: 796)
- Delta V3.61 b_08196012.exe (PID: 3392)
- setup08196012.exe (PID: 1768)
- OperaGX.exe (PID: 764)
- OfferInstaller.exe (PID: 3544)
Reads Environment values
- setup08196012.exe (PID: 796)
- OfferInstaller.exe (PID: 3544)
- anyPDF.exe (PID: 3664)
- Downloader.exe (PID: 3956)
- PdfOpenDriver.exe (PID: 3584)
- anyPDF.exe (PID: 2692)
Reads product name
- setup08196012.exe (PID: 796)
- OfferInstaller.exe (PID: 3544)
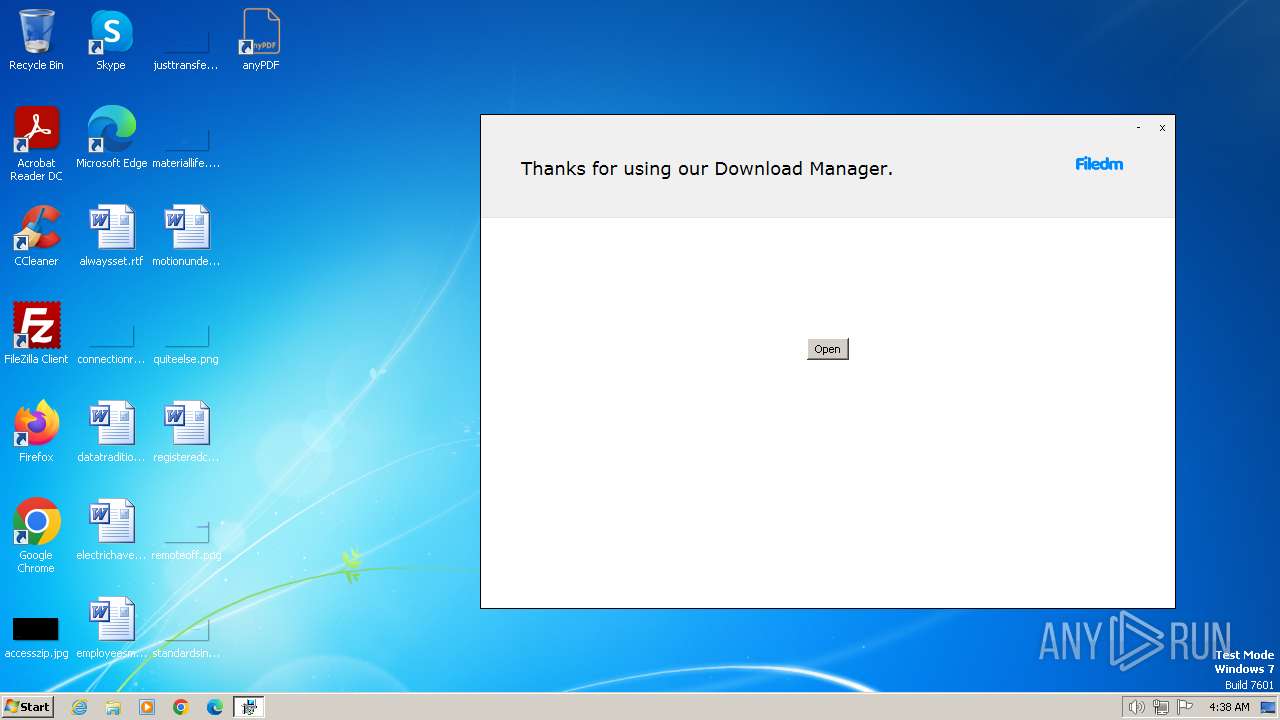
Manual execution by a user
- anyPDF.exe (PID: 3664)
- filezilla.exe (PID: 1852)
Creates files in the program directory
- Downloader.exe (PID: 3956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:02:24 20:04:55+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.22 |
| CodeSize: | 4347392 |
| InitializedDataSize: | 5656576 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x396dbb |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
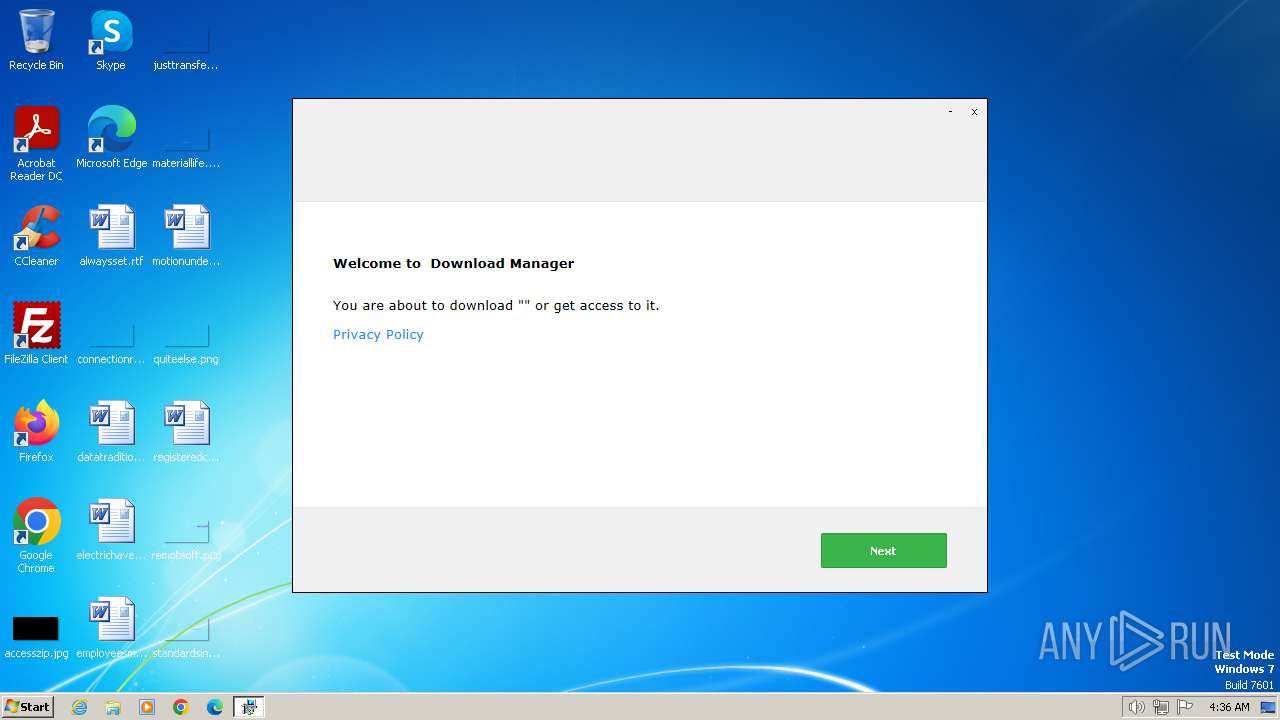
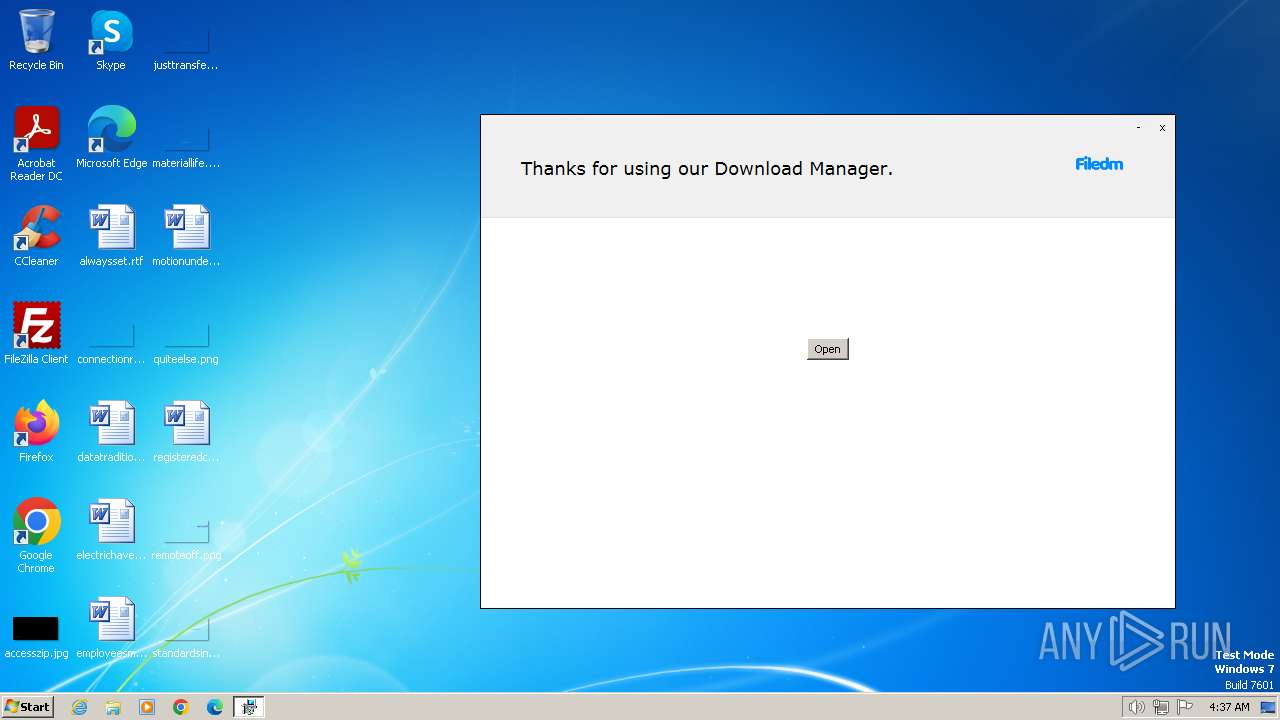
| FileDescription: | Download Manager |
| FileVersion: | 1 |
| InternalName: | Download Manager |
| LegalCopyright: | Download Manager |
| OriginalFileName: | Download Manager |
| ProductName: | Download Manager |
| ProductVersion: | 1 |
Total processes
83
Monitored processes
30
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 712 | find /I "796" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 764 | C:\Users\admin\AppData\Local\OperaGX.exe --silent --allusers=0 | C:\Users\admin\AppData\Local\OperaGX.exe | Delta V3.61 b_08196012.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: HIGH Description: Opera GX Installer Exit code: 2 Version: 107.0.5045.75 Modules
| |||||||||||||||
| 796 | C:\Users\admin\AppData\Local\setup08196012.exe hhwnd=2228666 hreturntoinstaller hextras=id:3d1253b881b6bcd-US-KA1rz | C:\Users\admin\AppData\Local\setup08196012.exe | Delta V3.61 b_08196012.exe | ||||||||||||
User: admin Company: DT001 Integrity Level: HIGH Description: Software Installation Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 984 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\ec05d89197b949eb6957b79472e8723d\anyPDF-h20-5.msi" /quiet | C:\Windows\System32\msiexec.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 992 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\link.txt | C:\Windows\System32\notepad.exe | — | Delta V3.61 b_08196012.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1072 | find /I "3544" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1288 | tasklist /FI "PID eq 3544" /fo csv | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1376 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\H2OCleanup.bat"" | C:\Windows\System32\cmd.exe | — | OfferInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1540 | timeout 5 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1768 | C:\Users\admin\AppData\Local\setup08196012.exe hready | C:\Users\admin\AppData\Local\setup08196012.exe | — | Delta V3.61 b_08196012.exe | |||||||||||
User: admin Company: DT001 Integrity Level: HIGH Description: Software Installation Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
62 540
Read events
62 216
Write events
304
Delete events
20
Modification events
| (PID) Process: | (3392) Delta V3.61 b_08196012.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3392) Delta V3.61 b_08196012.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (3392) Delta V3.61 b_08196012.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (3392) Delta V3.61 b_08196012.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
| (PID) Process: | (3392) Delta V3.61 b_08196012.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoDetect |
Value: | |||
| (PID) Process: | (3392) Delta V3.61 b_08196012.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005C010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3392) Delta V3.61 b_08196012.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3392) Delta V3.61 b_08196012.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3392) Delta V3.61 b_08196012.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3392) Delta V3.61 b_08196012.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
60
Suspicious files
15
Text files
57
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3392 | Delta V3.61 b_08196012.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_45E3C223BCF135987E4038FB6B0DBA13 | binary | |
MD5:037AE8164352CA91E80AD33054D1906D | SHA256:07C018EB07002663D5248DAA8A65EAF587955E3DB45735E7E3AC9CB13D7D664E | |||
| 3392 | Delta V3.61 b_08196012.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\service[1].htm | text | |
MD5:F9D4655BBB31D3745D1D1671E3A09F4A | SHA256:C09DC2BA6150D341E056631E8FBC1A91AFCD6D87759BDE08E75A1FC506641203 | |||
| 3392 | Delta V3.61 b_08196012.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\geo[1].htm | text | |
MD5:5D39A862DBA7977529EC0CDF42D4AA7B | SHA256:9124A7F2F685BAE024A19810C85A734EB38ECA116787B3A15AB1A43B4B948C33 | |||
| 3392 | Delta V3.61 b_08196012.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:0416E9B7E260B440F6621FC7E43AF6FE | SHA256:614BED26553344718C7E86E12A0FC756B1BAEC6B2258074147D8AEEB665B7CD2 | |||
| 3392 | Delta V3.61 b_08196012.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_45E3C223BCF135987E4038FB6B0DBA13 | binary | |
MD5:3AB20F009FF370FBE9AE728E630ED50C | SHA256:E894D5029D94BC029B0A1B6FE7B2C1942D7DB70ECF4011A4881E5E94B768EAF4 | |||
| 3392 | Delta V3.61 b_08196012.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\3465EF07B9A6512425B2408FA7DBF4E5_F38ABF5BFFF4E687C6F66BAEAE5ADE1C | binary | |
MD5:54BA23667E89E15EE9A0216FEBDCCAA7 | SHA256:7E19630BAE2B53A1C885E67D31AD3B9ECD4946D37DF1E2F52A7827E5BBFE6AD9 | |||
| 3392 | Delta V3.61 b_08196012.exe | C:\Users\admin\AppData\Local\setup08196012.exe | executable | |
MD5:29D3A70CEC060614E1691E64162A6C1E | SHA256:CC70B093A19610E9752794D757AEC9EF07CA862EA9267EC6F9CC92B2AA882C72 | |||
| 3392 | Delta V3.61 b_08196012.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\3465EF07B9A6512425B2408FA7DBF4E5_F38ABF5BFFF4E687C6F66BAEAE5ADE1C | binary | |
MD5:9C30B268FEA21D3DD0ECF37EC91057FD | SHA256:8332FEA0E49A59C9B80AC504E87CF96F207757B84AC06FB0B19306A00D6DE957 | |||
| 796 | setup08196012.exe | C:\Users\admin\AppData\Local\Temp\ec05d89197b949eb6957b79472e8723d\vcruntime140.dll | executable | |
MD5:1A84957B6E681FCA057160CD04E26B27 | SHA256:9FAEAA45E8CC986AF56F28350B38238B03C01C355E9564B849604B8D690919C5 | |||
| 796 | setup08196012.exe | C:\Users\admin\AppData\Local\Temp\ec05d89197b949eb6957b79472e8723d\ServiceHide.dll | executable | |
MD5:72990C7E32EE6C811EA3D2EA64523234 | SHA256:E77E0B4F2762F76A3EAAADF5A3138A35EC06ECE80EDC4B3396DE7A601F8DA1B3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
56
DNS requests
29
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3392 | Delta V3.61 b_08196012.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?04b2dea8abd60a79 | unknown | — | — | unknown |
3392 | Delta V3.61 b_08196012.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/s/gts1d4/tE2rewqz3dw/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSMBFDqU0NJQdZdEGU3bkhj0FoRrQQUJeIYDrJXkZQq5dRdhpCD3lOzuJICECdevec1BTW3CTOOyMl566o%3D | unknown | binary | 471 b | unknown |
3392 | Delta V3.61 b_08196012.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
3392 | Delta V3.61 b_08196012.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIAjrICMzZli2TN25s%3D | unknown | binary | 724 b | unknown |
3392 | Delta V3.61 b_08196012.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/s/gts1d4/0keShi7yRCM/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSMBFDqU0NJQdZdEGU3bkhj0FoRrQQUJeIYDrJXkZQq5dRdhpCD3lOzuJICEQCsv8pCRp4QTwlHpeDlD%2BBJ | unknown | binary | 472 b | unknown |
3392 | Delta V3.61 b_08196012.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?86d6139f3b7ef26c | unknown | compressed | 67.5 Kb | unknown |
3392 | Delta V3.61 b_08196012.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
3392 | Delta V3.61 b_08196012.exe | GET | 200 | 69.192.161.44:80 | http://x2.c.lencr.org/ | unknown | binary | 299 b | unknown |
3392 | Delta V3.61 b_08196012.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | binary | 724 b | unknown |
3392 | Delta V3.61 b_08196012.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAsA6S1NbXMfyjBZx8seGIY%3D | unknown | binary | 314 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3392 | Delta V3.61 b_08196012.exe | 35.190.60.70:443 | www.dlsft.com | GOOGLE | US | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3392 | Delta V3.61 b_08196012.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3392 | Delta V3.61 b_08196012.exe | 142.250.186.131:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
796 | setup08196012.exe | 104.17.9.52:443 | flow.lavasoft.com | CLOUDFLARENET | — | shared |
796 | setup08196012.exe | 104.18.68.73:443 | sos.adaware.com | CLOUDFLARENET | — | unknown |
3392 | Delta V3.61 b_08196012.exe | 188.114.96.3:443 | filedm.com | CLOUDFLARENET | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dlsft.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.google.com |
| whitelisted |
flow.lavasoft.com |
| whitelisted |
sos.adaware.com |
| whitelisted |
dlsft.com |
| unknown |
filedm.com |
| malicious |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
Threats
6 ETPRO signatures available at the full report
Process | Message |
|---|---|
Delta V3.61 b_08196012.exe | at initializeDynamicVariables (this://app/main.html(329))
|
Delta V3.61 b_08196012.exe | |
Delta V3.61 b_08196012.exe | at getFileInfo.@285@39 (this://app/main.html(307))
|
Delta V3.61 b_08196012.exe | Error: (undefined) has no property - value
|
Delta V3.61 b_08196012.exe | |
setup08196012.exe | file:resources/tis/TranslateOfferTemplate.tis(82) : warning :'async' does not contain any 'await'
|
setup08196012.exe | Error: File not found - sciterwrapper:console.tis
|
setup08196012.exe | at sciter:init-script.tis
|
setup08196012.exe | |
setup08196012.exe | |