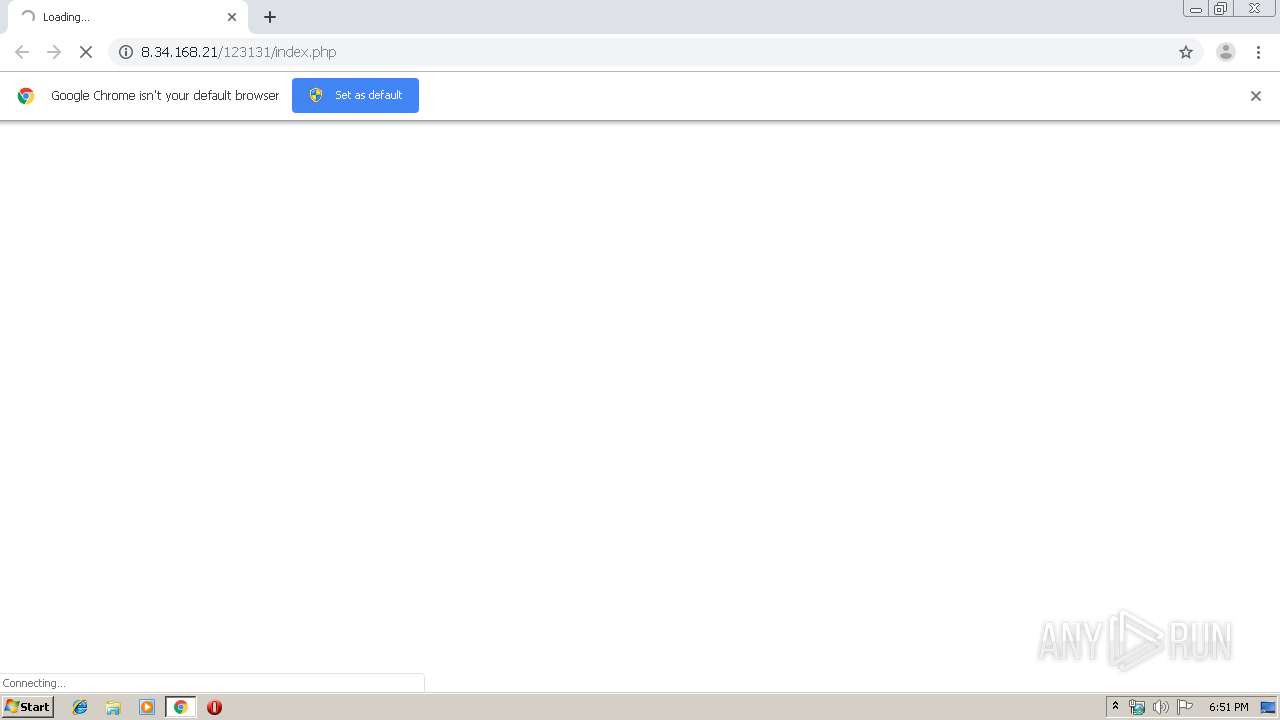
| URL: | http://8.34.168.21/123131/index.php |
| Full analysis: | https://app.any.run/tasks/58148660-d29e-4e28-9c0c-e9fe77e59733 |
| Verdict: | Malicious activity |
| Analysis date: | October 11, 2019, 17:51:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3AA74BA14C1D29ADAF0A1DA41B9D6154 |
| SHA1: | 1C5B543158A8D2677A81F8203FE06B5CFD55708E |
| SHA256: | 25C461ECF0C00BC1747D03AA45D7E64E4F50CAF3D5E73F51AC44BB131490BCA5 |
| SSDEEP: | 3:N1KRLUTdLEPGbHn:CtKdLNHn |
MALICIOUS
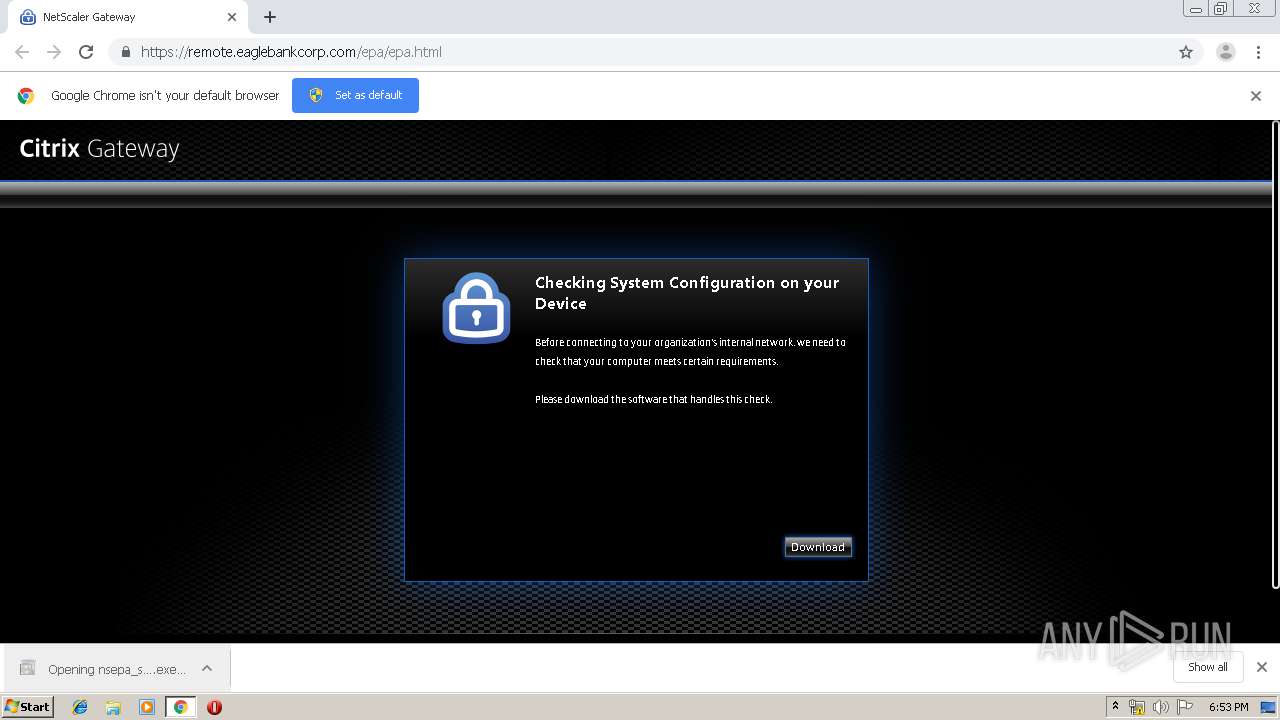
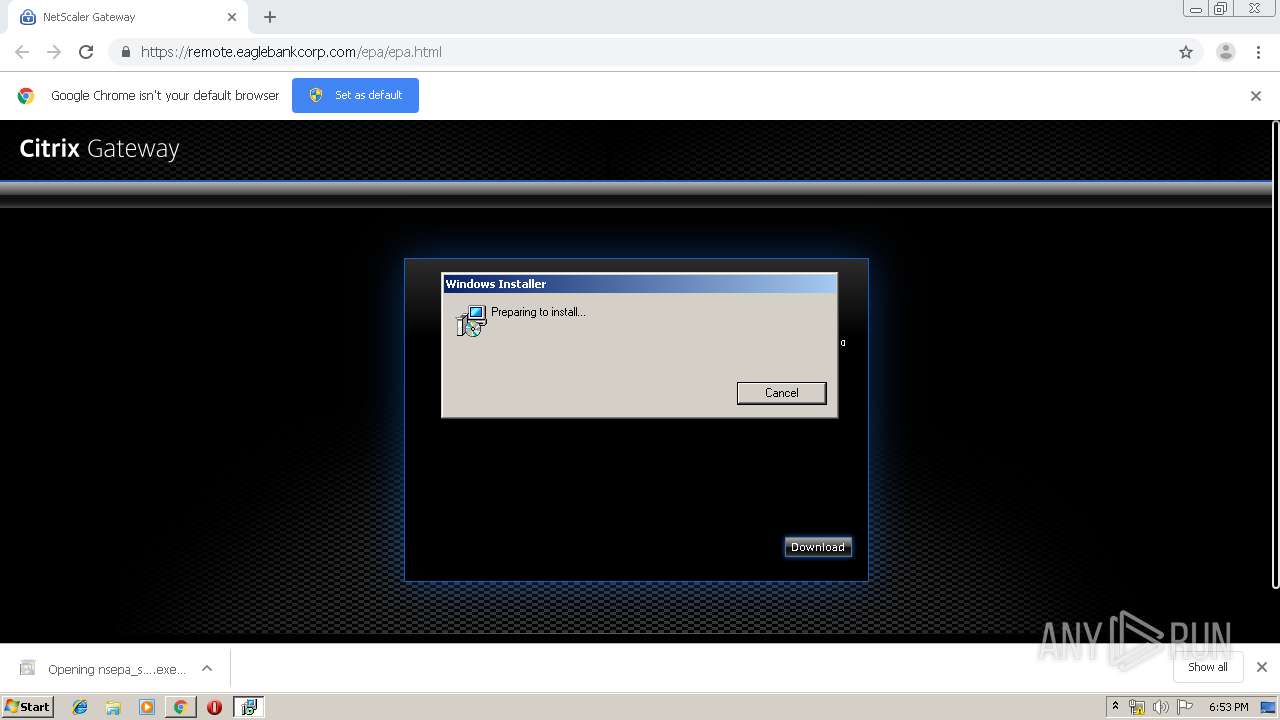
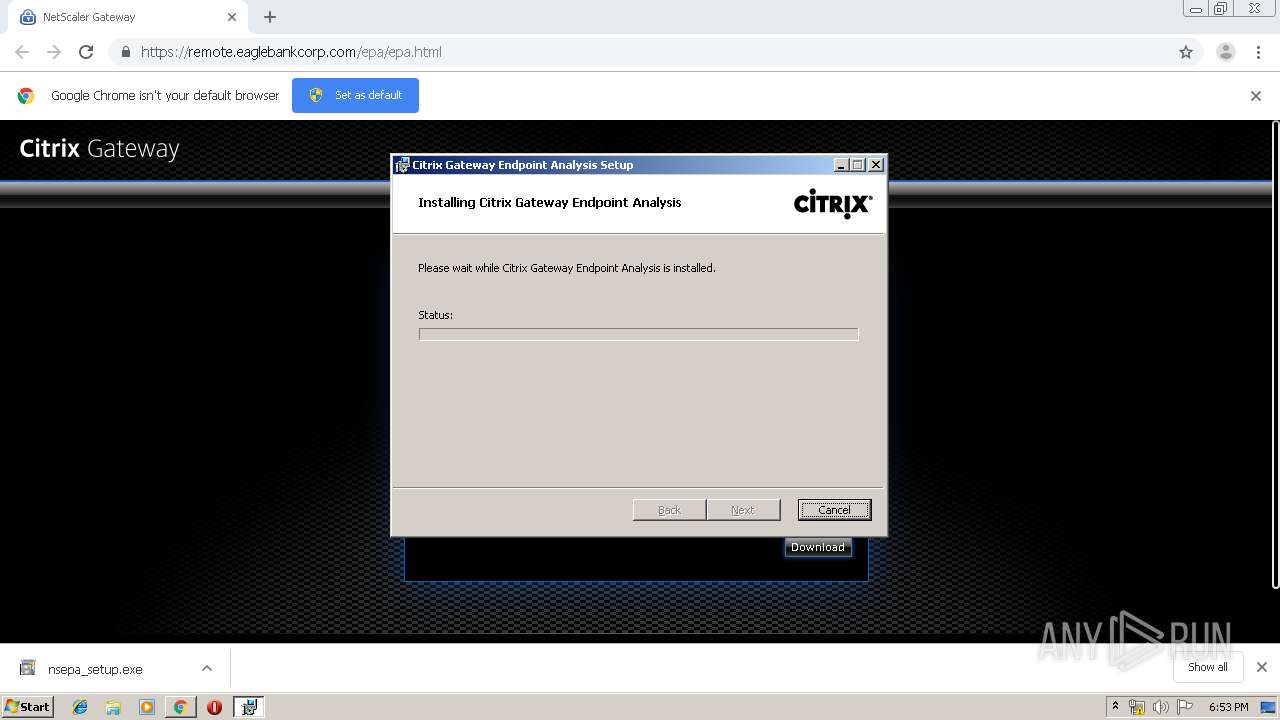
Application was dropped or rewritten from another process
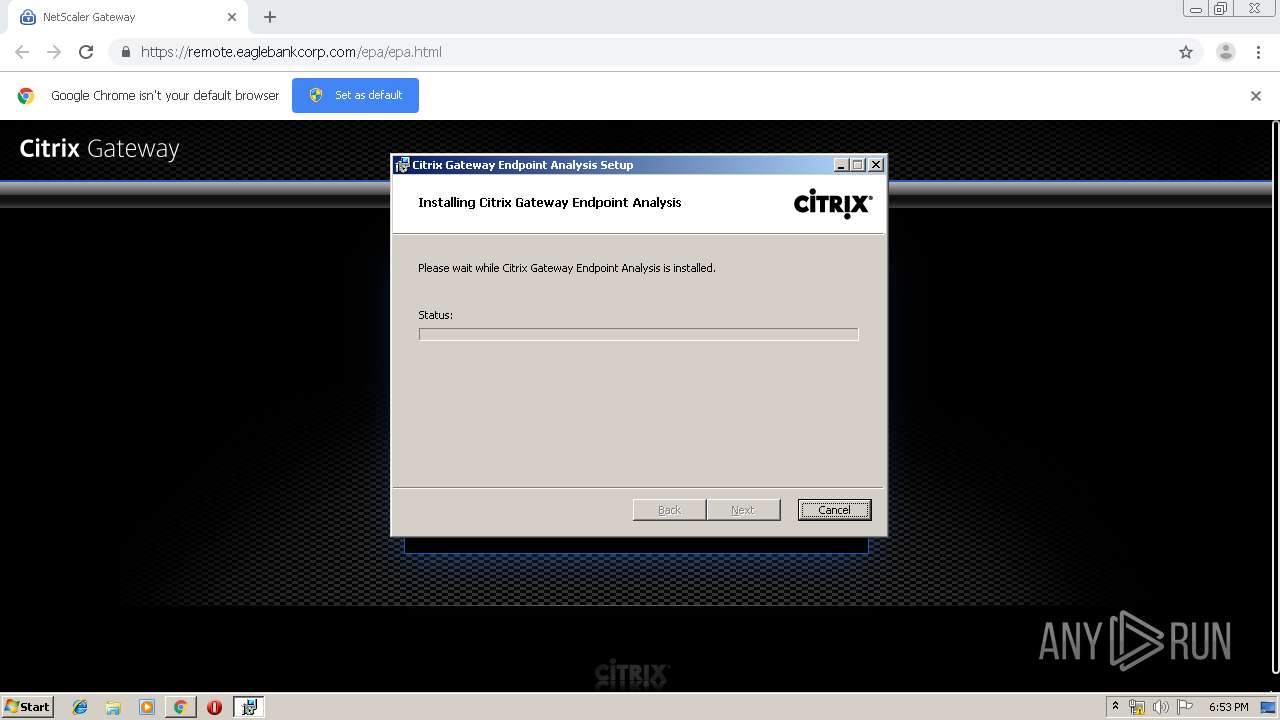
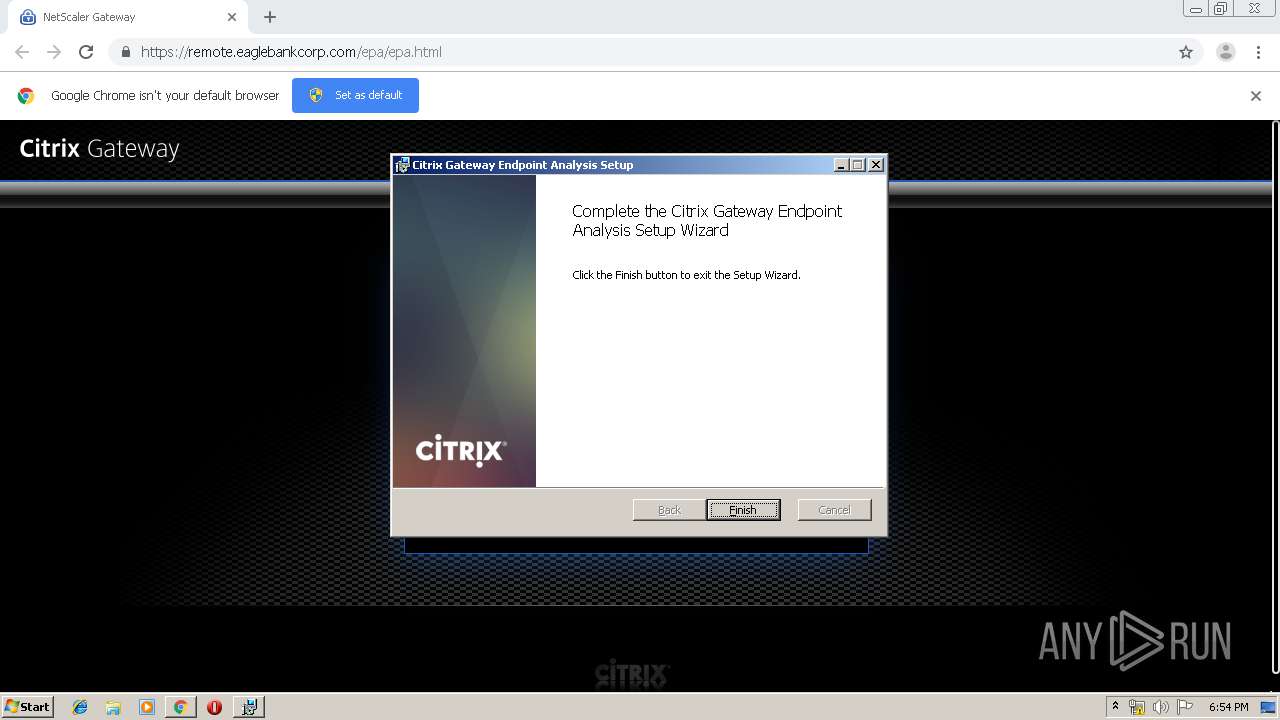
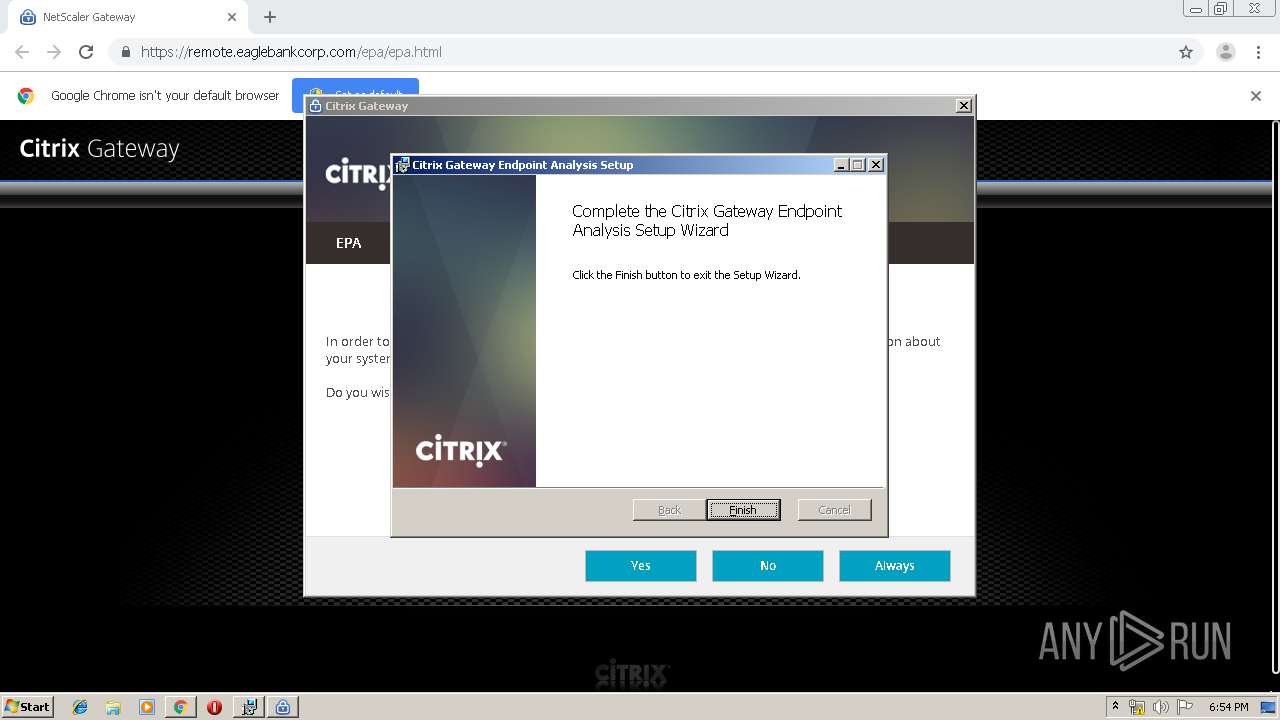
- nsepa_setup.exe (PID: 1816)
- nsepa_setup.exe (PID: 1744)
- combinedSetup.exe (PID: 1028)
- nsepa.exe (PID: 3508)
- epaPackage.exe (PID: 2340)
- nglauncher.exe (PID: 4024)
Changes settings of System certificates
- combinedSetup.exe (PID: 1028)
- nsepa.exe (PID: 3508)
Changes the autorun value in the registry
- nsepa_setup.exe (PID: 1816)
- epaPackage.exe (PID: 2340)
- rundll32.exe (PID: 3076)
- rundll32.exe (PID: 3636)
Loads dropped or rewritten executable
- nsepa.exe (PID: 3508)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 996)
- chrome.exe (PID: 656)
- nsepa_setup.exe (PID: 1816)
- msiexec.exe (PID: 2108)
- nsepa.exe (PID: 3508)
- epaPackage.exe (PID: 2340)
- cmd.exe (PID: 2456)
- rundll32.exe (PID: 3076)
- rundll32.exe (PID: 3636)
Modifies files in Chrome extension folder
- chrome.exe (PID: 996)
Executed as Windows Service
- vssvc.exe (PID: 184)
Adds / modifies Windows certificates
- combinedSetup.exe (PID: 1028)
- nsepa.exe (PID: 3508)
Modifies the open verb of a shell class
- msiexec.exe (PID: 2108)
Executed via COM
- DllHost.exe (PID: 3988)
- nsepa.exe (PID: 3508)
- unsecapp.exe (PID: 2240)
Reads internet explorer settings
- nsepa.exe (PID: 3508)
Creates files in the user directory
- nsepa.exe (PID: 3508)
Starts CMD.EXE for commands execution
- epaPackage.exe (PID: 2340)
- nsepa.exe (PID: 3508)
Searches for installed software
- nsepa.exe (PID: 3508)
Creates files in the Windows directory
- rundll32.exe (PID: 3076)
- rundll32.exe (PID: 3636)
Removes files from Windows directory
- rundll32.exe (PID: 3076)
- rundll32.exe (PID: 3636)
Creates files in the driver directory
- rundll32.exe (PID: 3076)
- rundll32.exe (PID: 3636)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 1560)
- cmd.exe (PID: 2612)
Creates or modifies windows services
- rundll32.exe (PID: 3636)
INFO
Application launched itself
- chrome.exe (PID: 996)
- msiexec.exe (PID: 2108)
Reads the hosts file
- chrome.exe (PID: 656)
- chrome.exe (PID: 996)
Reads Internet Cache Settings
- chrome.exe (PID: 996)
Searches for installed software
- msiexec.exe (PID: 2108)
Low-level read access rights to disk partition
- vssvc.exe (PID: 184)
Creates files in the program directory
- msiexec.exe (PID: 2108)
Creates a software uninstall entry
- msiexec.exe (PID: 2108)
Reads settings of System Certificates
- nsepa.exe (PID: 3508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
93
Monitored processes
49
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,6147491286848509495,8471258549834483080,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3128123617786533343 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3972 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,6147491286848509495,8471258549834483080,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15947858595197677601 --mojo-platform-channel-handle=3772 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 532 | "C:\Windows\System32\grpconv.exe" -o | C:\Windows\System32\grpconv.exe | — | runonce.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,6147491286848509495,8471258549834483080,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8229856355413904054 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2128 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,6147491286848509495,8471258549834483080,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=2008232226569853939 --mojo-platform-channel-handle=1524 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,6147491286848509495,8471258549834483080,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9673797398793383093 --mojo-platform-channel-handle=2968 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,6147491286848509495,8471258549834483080,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1625051428149544693 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,6147491286848509495,8471258549834483080,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2308397981303471381 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4200 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://8.34.168.21/123131/index.php" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 511
Read events
2 028
Write events
460
Delete events
23
Modification events
| (PID) Process: | (996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 996-13215289904363500 |
Value: 259 | |||
| (PID) Process: | (996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (996) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
27
Suspicious files
82
Text files
245
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b4383791-45e2-456b-a9ce-faaaf368fbdf.tmp | — | |
MD5:— | SHA256:— | |||
| 996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a504.TMP | text | |
MD5:— | SHA256:— | |||
| 996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
41
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
656 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 529 b | whitelisted |
3508 | nsepa.exe | GET | 200 | 23.37.43.27:80 | http://s2.symcb.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCED141%2Fl2SWCyYX308B7Khio%3D | NL | der | 1.71 Kb | whitelisted |
656 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 534 b | whitelisted |
3508 | nsepa.exe | GET | 200 | 23.37.43.27:80 | http://sv.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQe6LNDJdqx%2BJOp7hVgTeaGFJ%2FCQgQUljtT8Hkzl699g%2B8uK8zKt4YecmYCEFFKududa8IHFUo6FSNdvx4%3D | NL | der | 1.57 Kb | shared |
3508 | nsepa.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT5hgD4pKvs0jFFLEKNQ1CjblLIPQQU9LbhIB3%2BKa7S5GGlsqIlssgXNW4CEAqSXSRVgDYm4YegBXCaJZA%3D | US | der | 471 b | whitelisted |
3508 | nsepa.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEAqhJdbWMht%2BQeQF2jaXwhU%3D | US | der | 471 b | whitelisted |
656 | chrome.exe | GET | 200 | 92.122.213.201:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 57.0 Kb | whitelisted |
656 | chrome.exe | GET | 200 | 185.180.12.142:80 | http://r3---sn-n02xgoxufvg3-8pxe.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.183.107.236&mm=28&mn=sn-n02xgoxufvg3-8pxe&ms=nvh&mt=1570816215&mv=m&mvi=2&pl=24&shardbypass=yes | AT | crx | 293 Kb | whitelisted |
656 | chrome.exe | GET | 200 | 185.180.12.140:80 | http://r1---sn-n02xgoxufvg3-8pxe.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.183.107.236&mm=28&mn=sn-n02xgoxufvg3-8pxe&ms=nvh&mt=1570816215&mv=m&mvi=0&pl=24&shardbypass=yes | AT | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
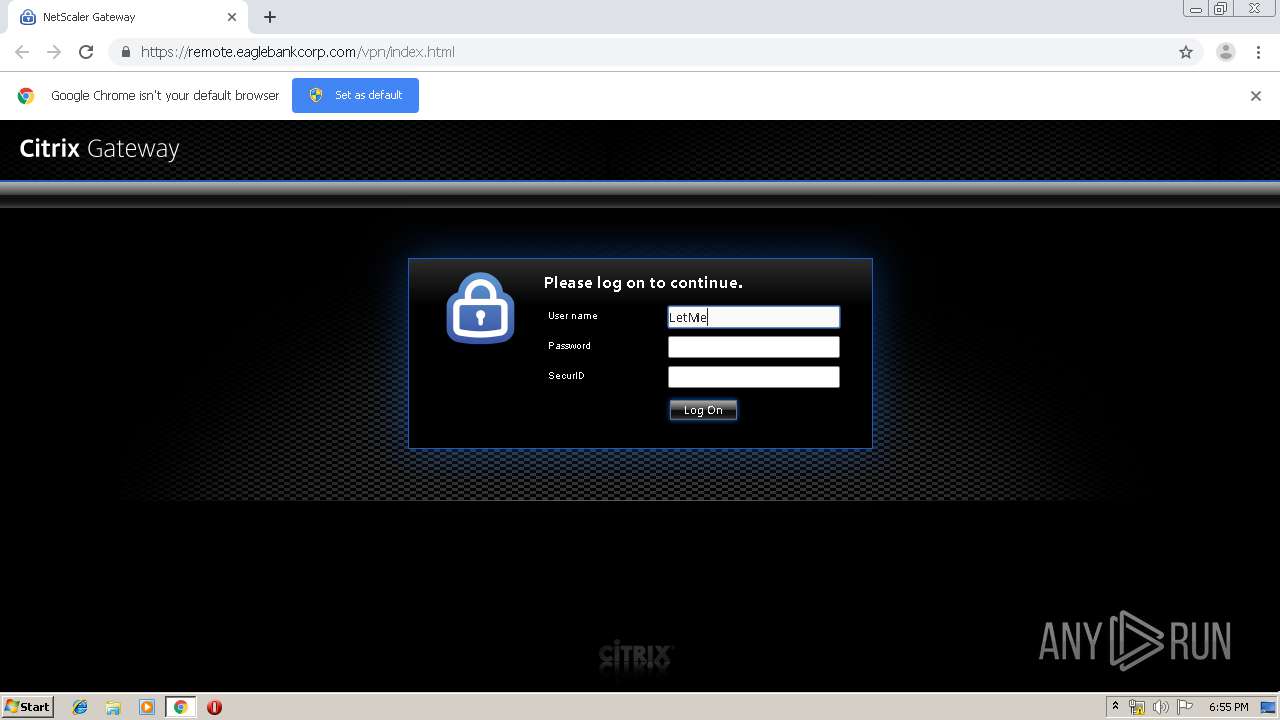
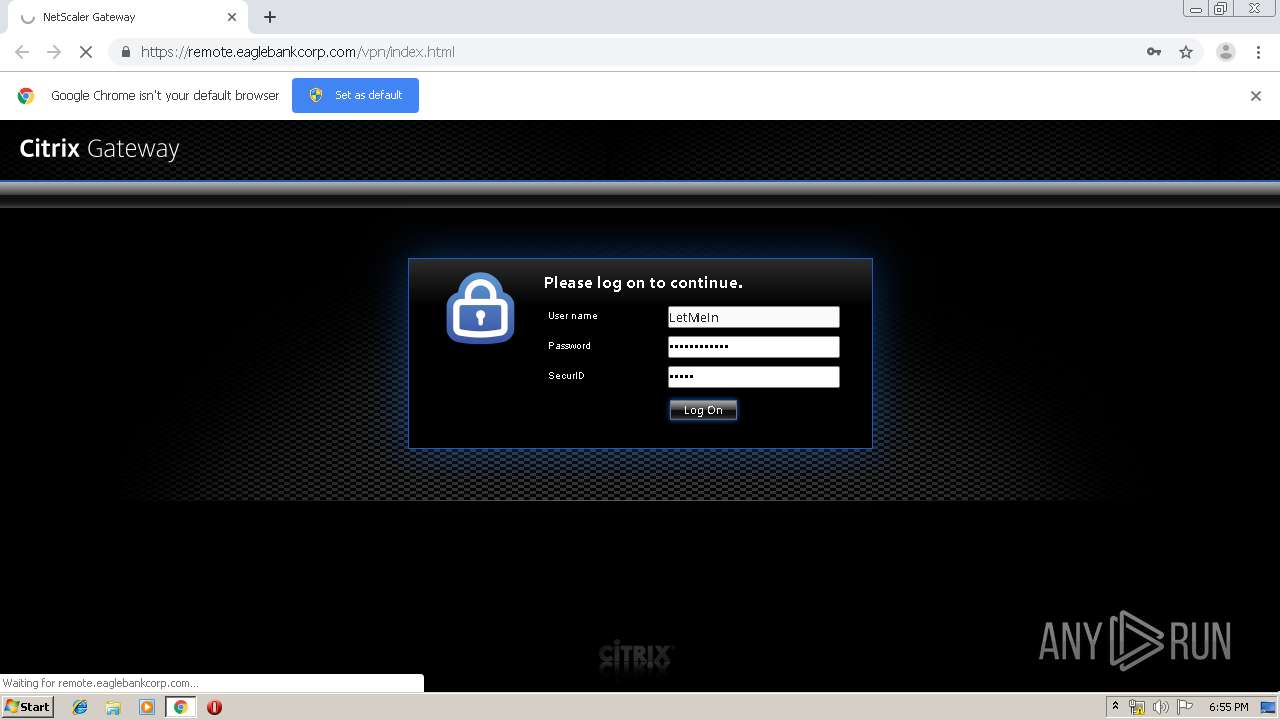
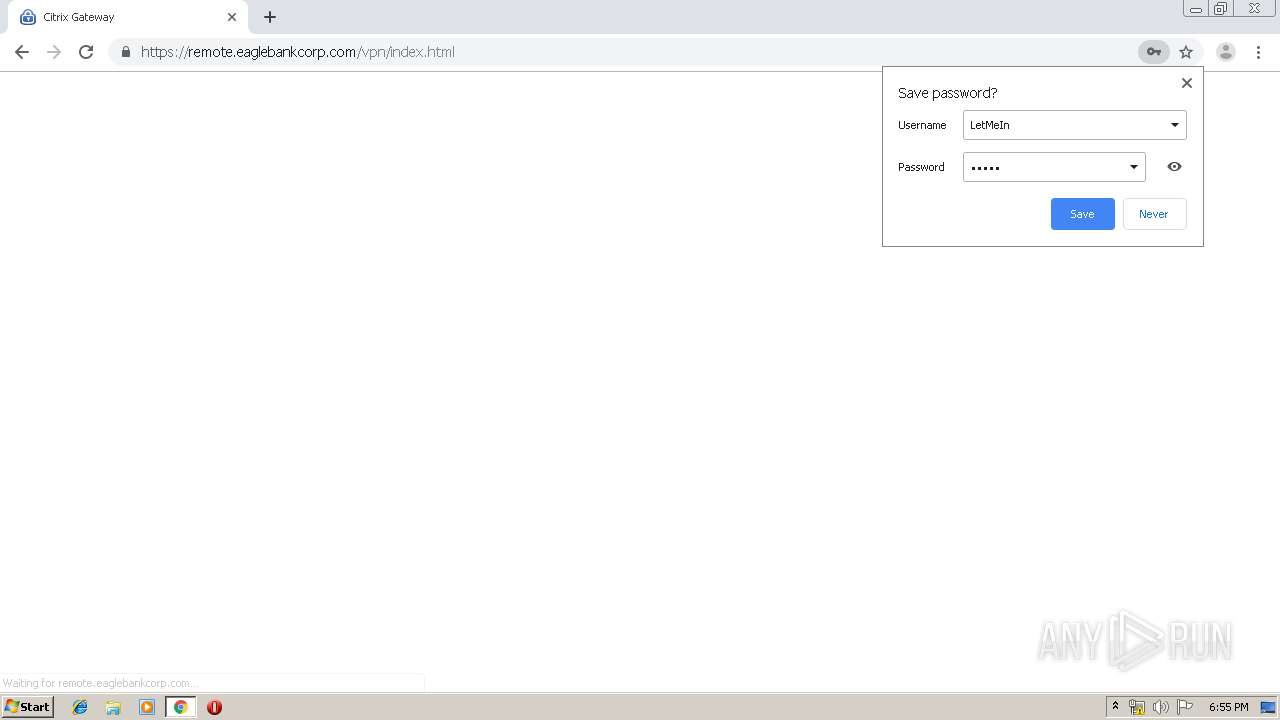
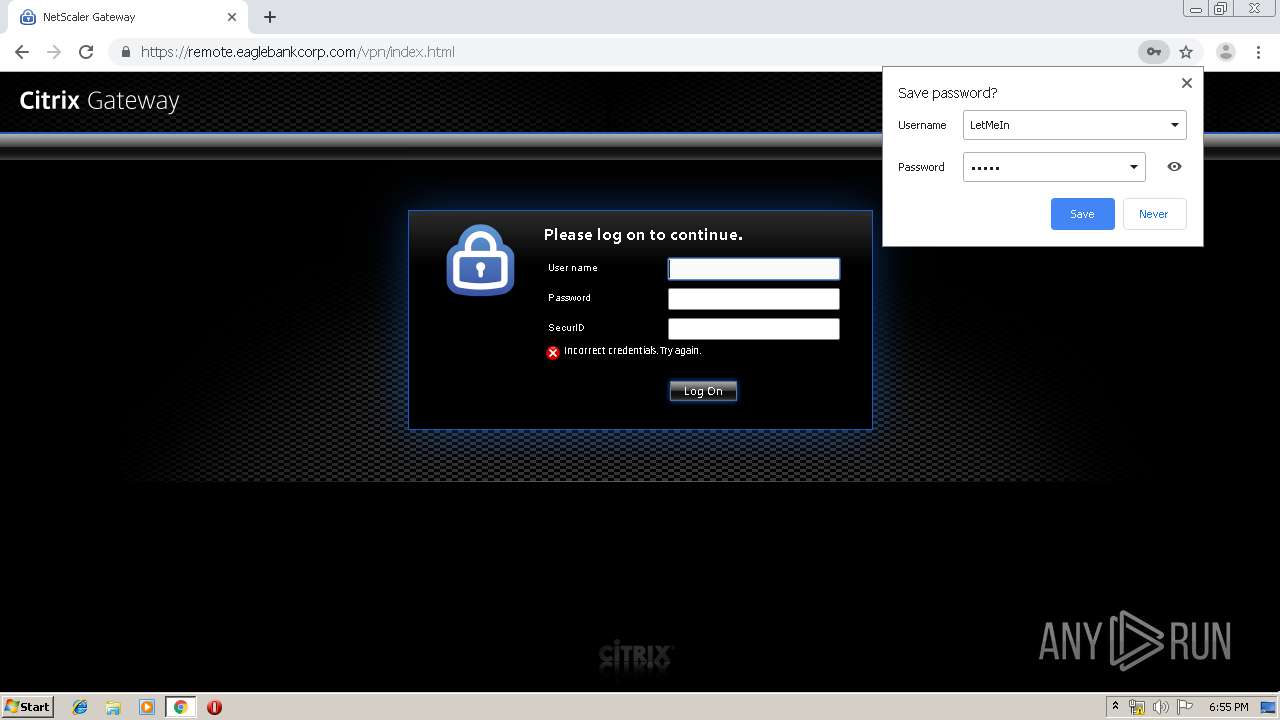
656 | chrome.exe | 8.34.168.21:80 | — | Level 3 Communications, Inc. | US | unknown |
656 | chrome.exe | 216.58.210.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
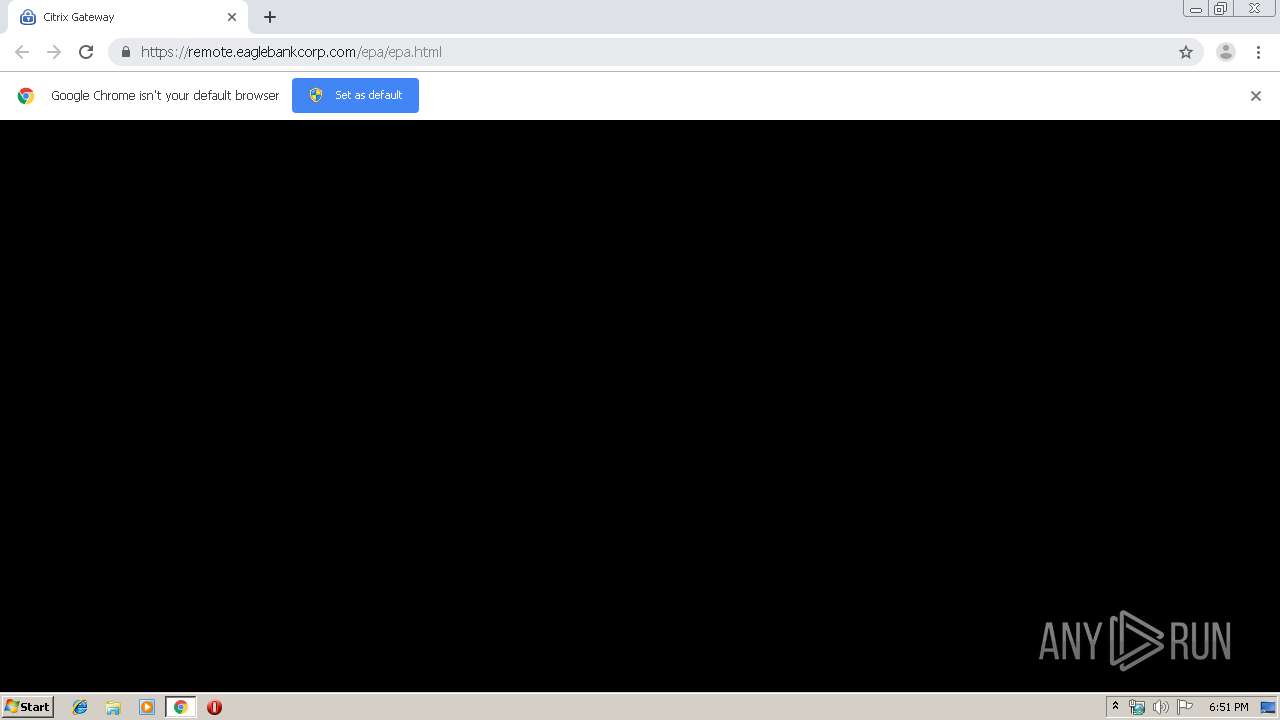
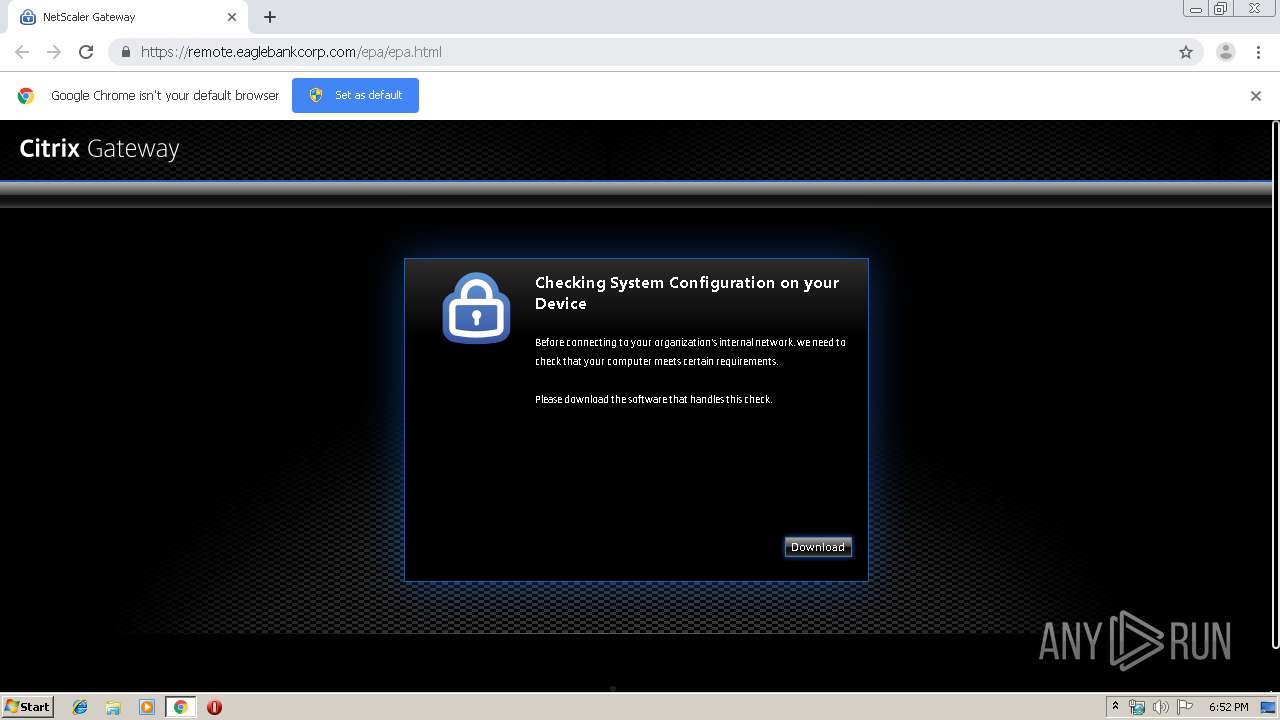
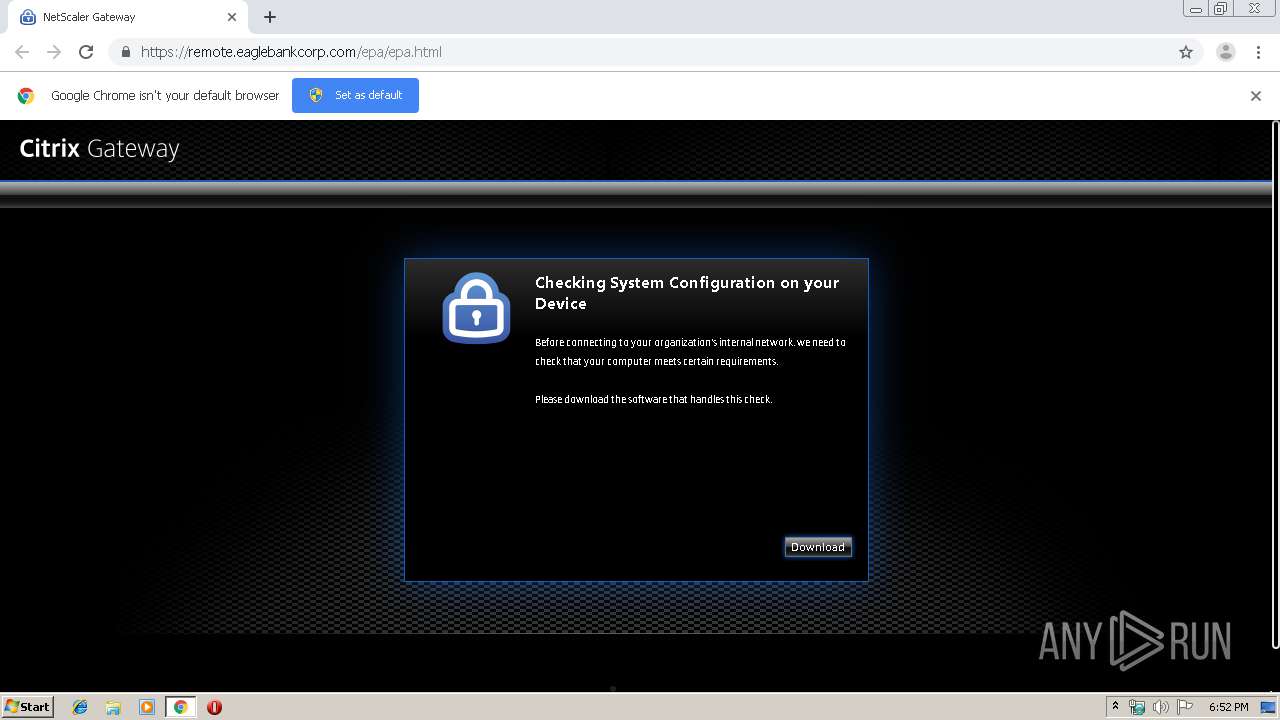
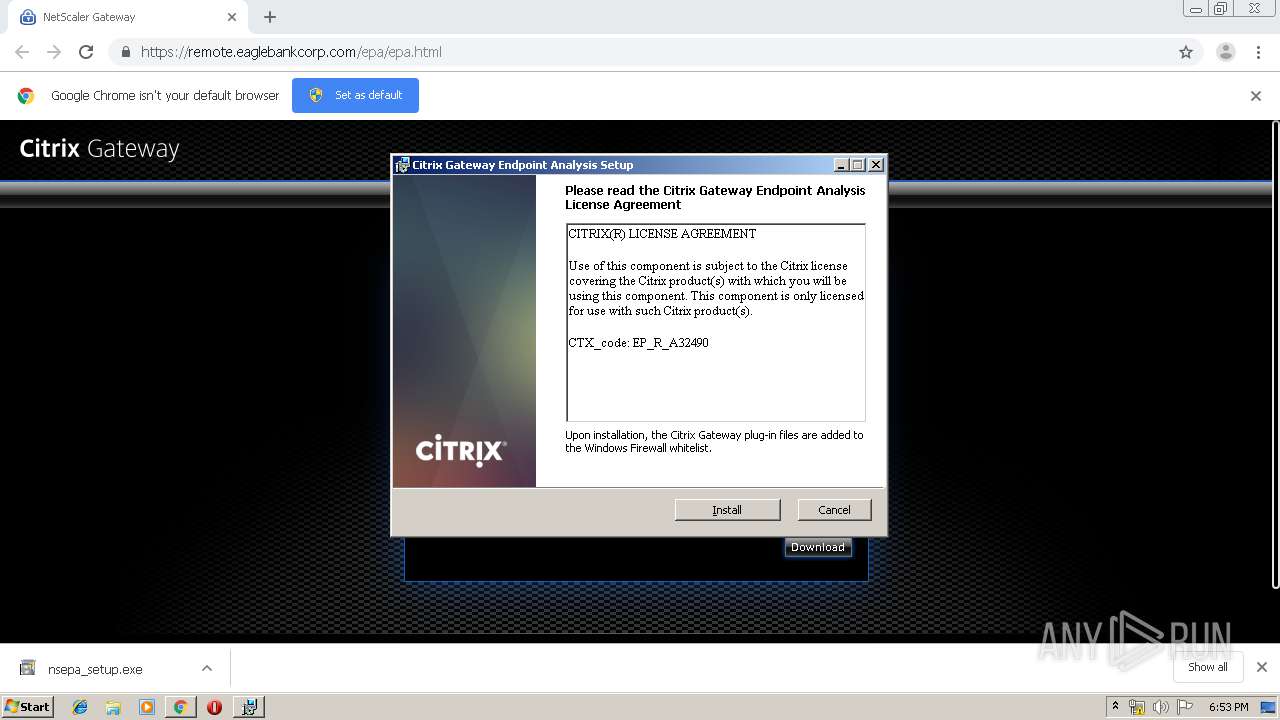
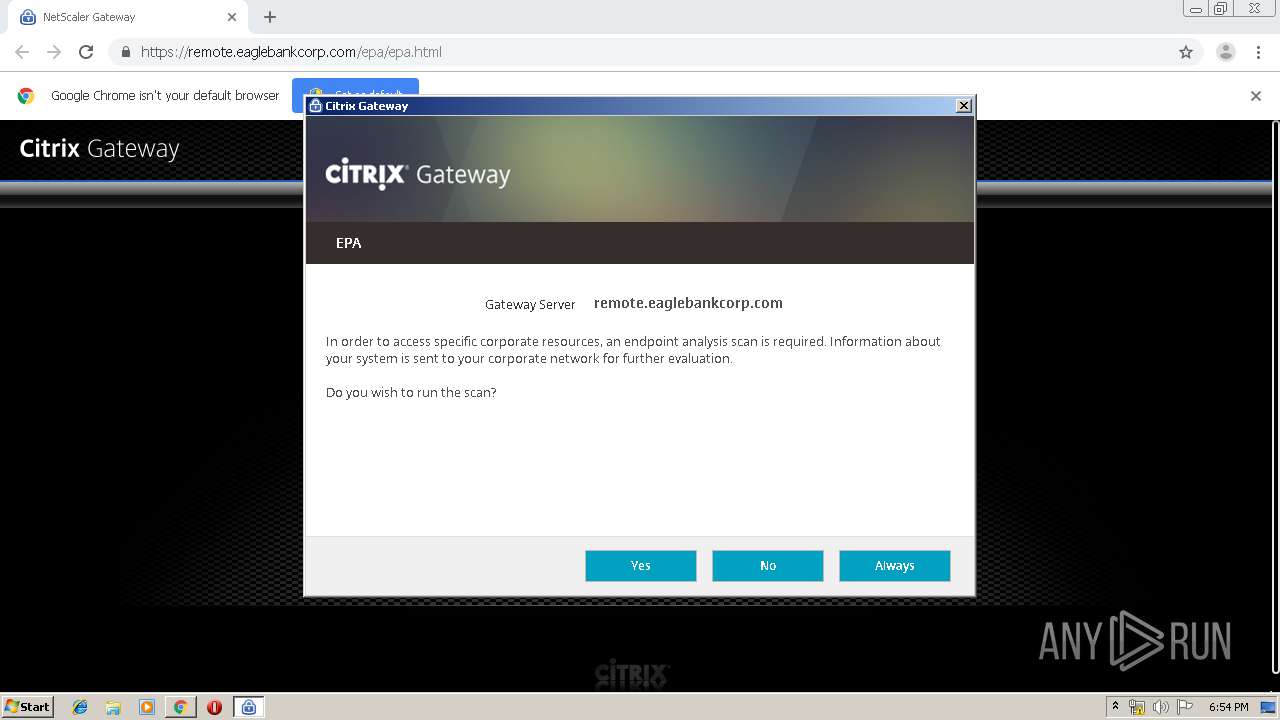
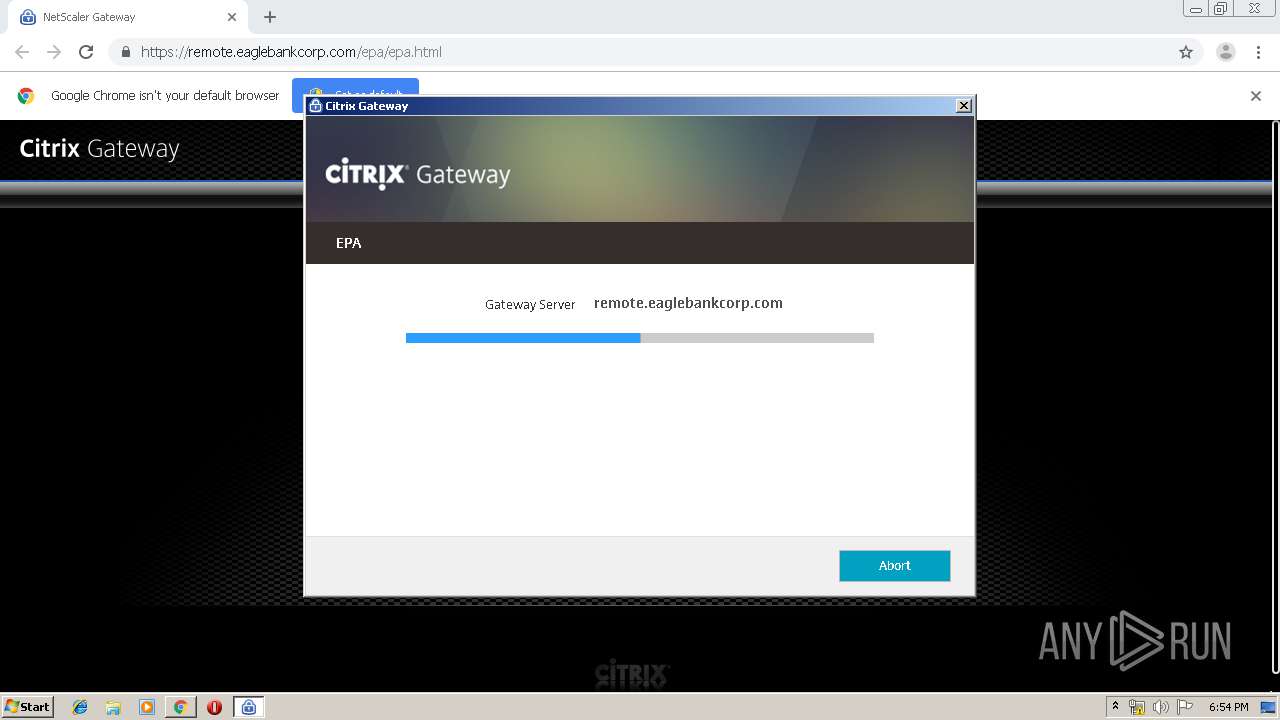
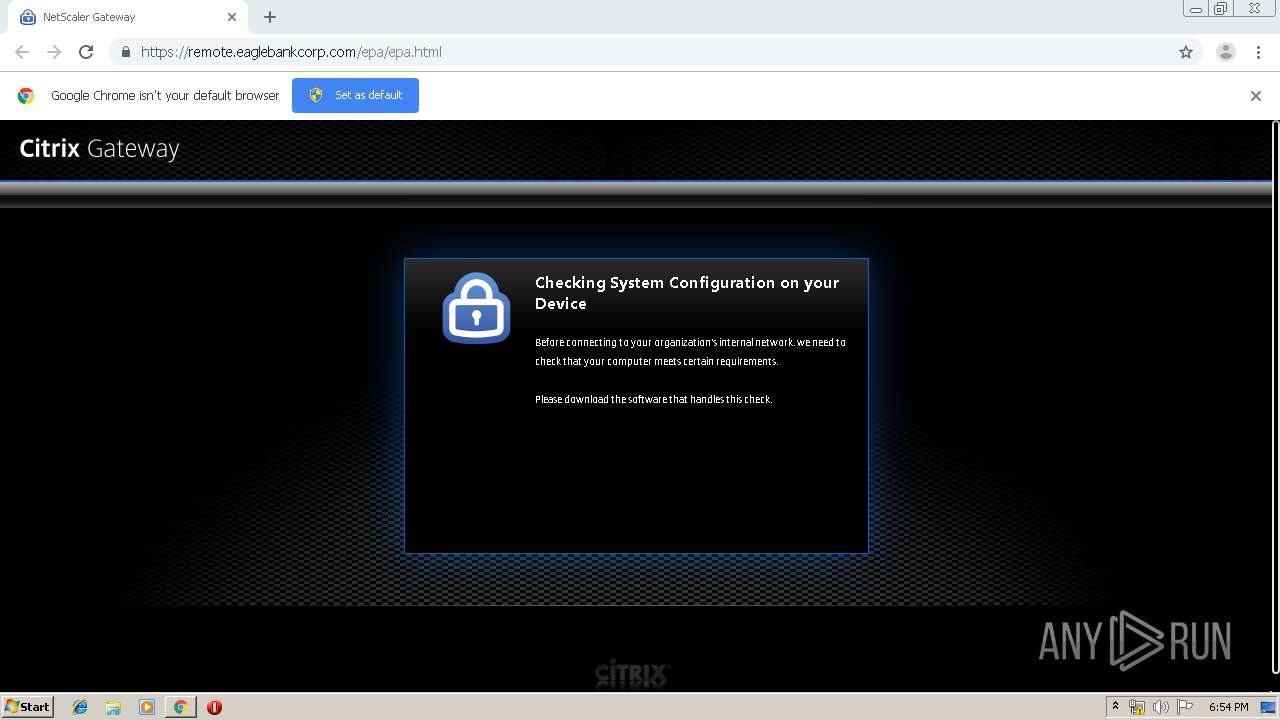
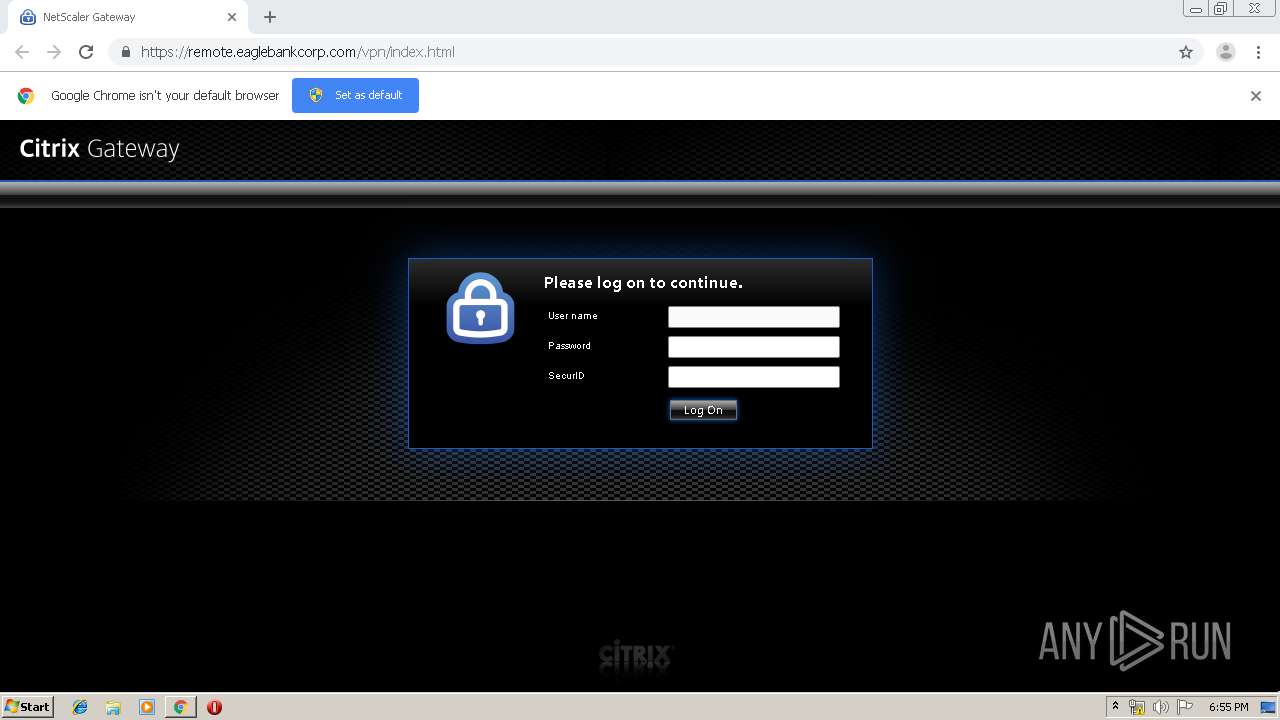
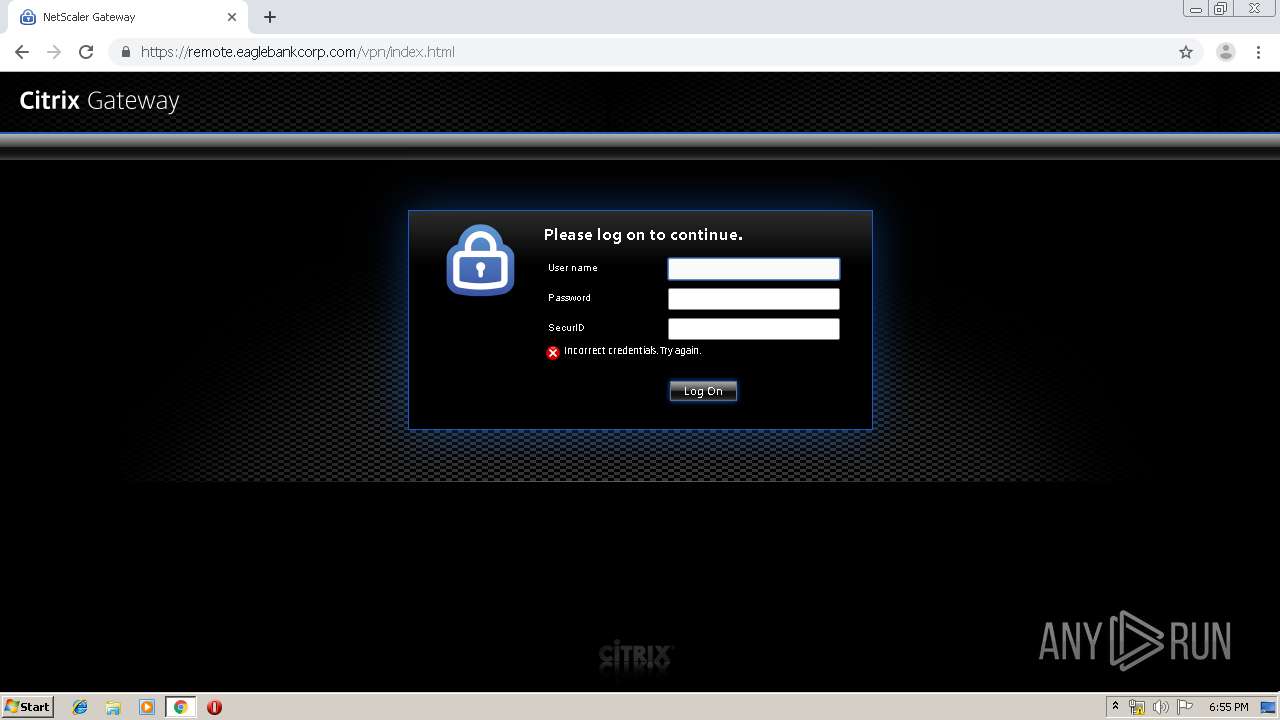
656 | chrome.exe | 4.79.229.24:443 | remote.eaglebankcorp.com | Level 3 Communications, Inc. | US | unknown |
656 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
656 | chrome.exe | 172.217.22.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
656 | chrome.exe | 172.217.22.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
656 | chrome.exe | 185.180.12.142:80 | r3---sn-n02xgoxufvg3-8pxe.gvt1.com | Datacamp Limited | AT | whitelisted |
656 | chrome.exe | 172.217.18.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
656 | chrome.exe | 172.217.22.110:443 | redirector.gvt1.com | Google Inc. | US | whitelisted |
656 | chrome.exe | 172.217.16.206:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
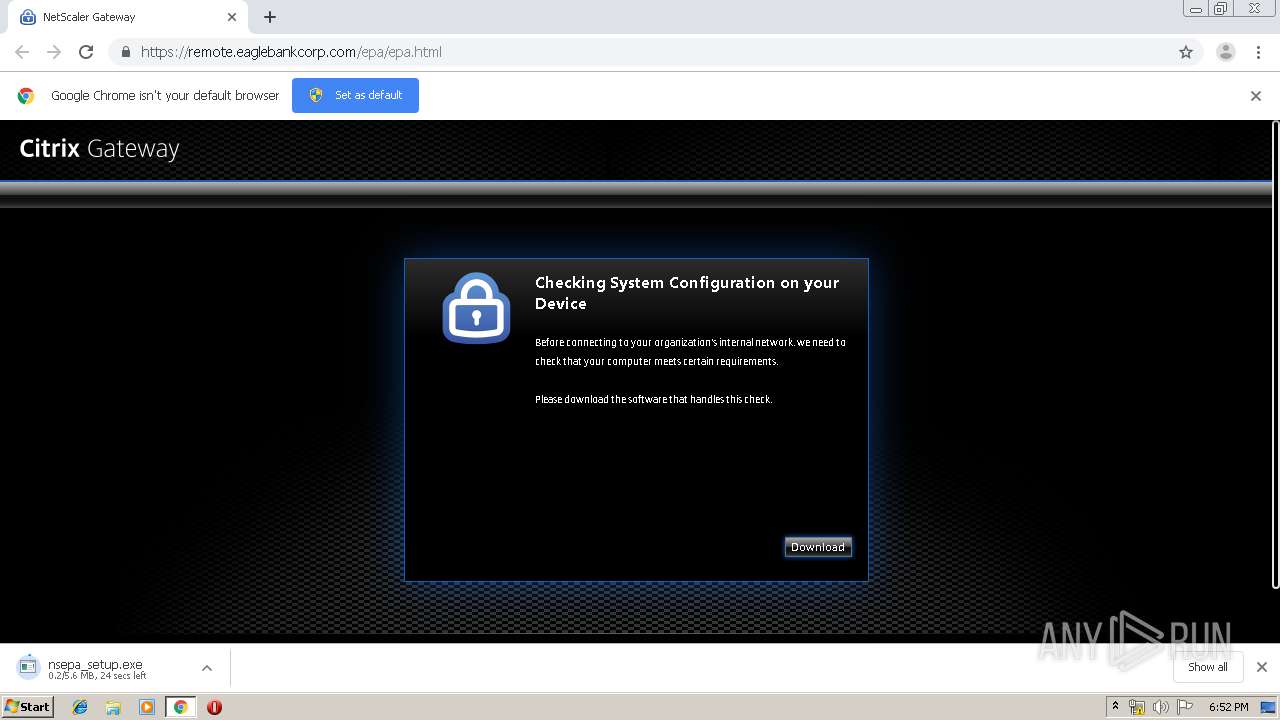
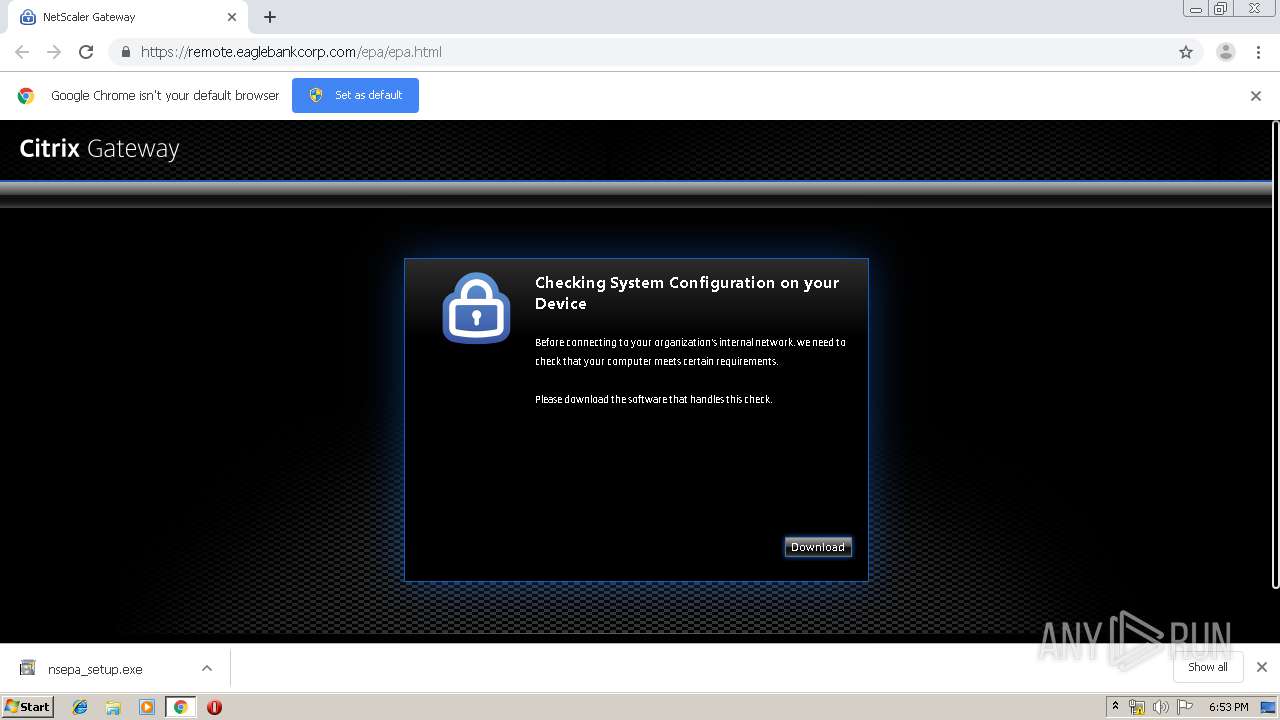
remote.eaglebankcorp.com |
| unknown |
www.download.windowsupdate.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r3---sn-n02xgoxufvg3-8pxe.gvt1.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |