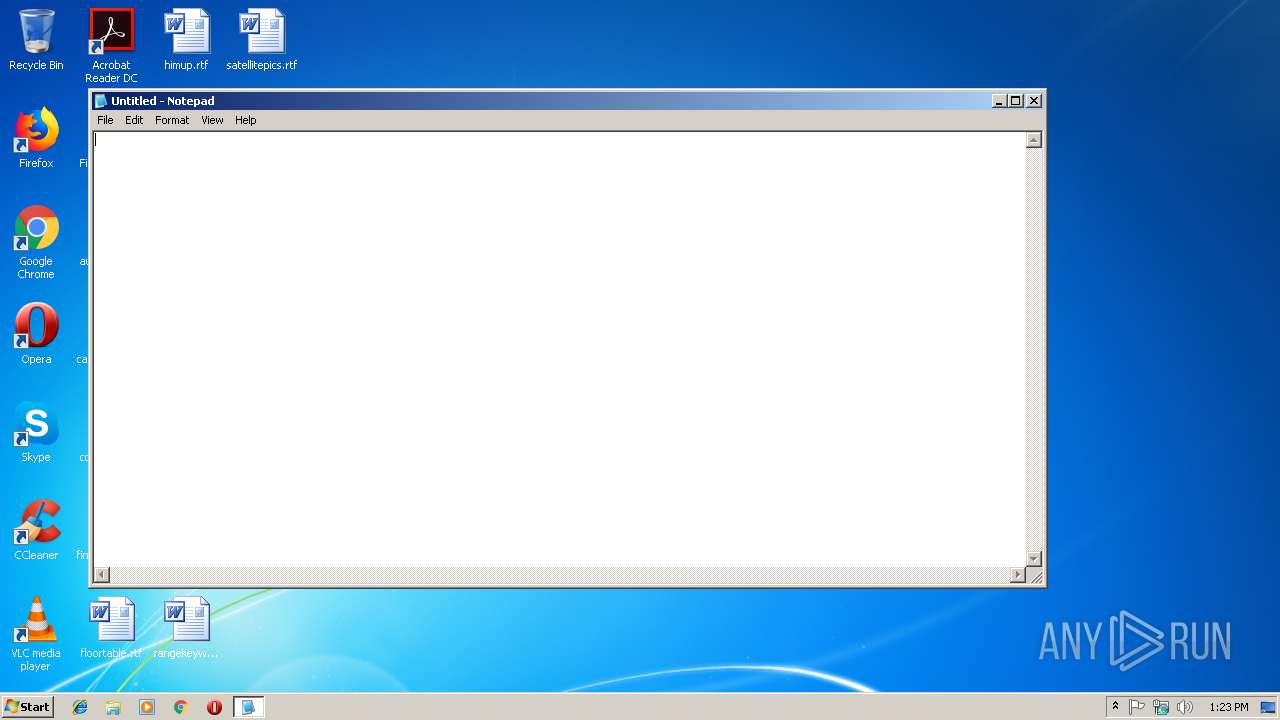
| File name: | notepad.exe |
| Full analysis: | https://app.any.run/tasks/295158da-b60a-4e64-8269-15bb29e45e4a |
| Verdict: | Malicious activity |
| Analysis date: | February 28, 2019, 13:23:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | C3EB07BA4196377E4C7A6B68B78AD378 |
| SHA1: | 7BC68D7FA613C043AC42FE4899F8770FC3C18907 |
| SHA256: | 25BAC42A8BF1CBB9D14132DB95728231992843949A38A91F7608AC9D713C2C79 |
| SSDEEP: | 6144:yxKj8Ot6aF+JhdWE+/CnIIdm8O5TNSDyDRO1thpn:Bj8OGhUE+/NIdNO5SDyo1tjn |
MALICIOUS
Application was dropped or rewritten from another process
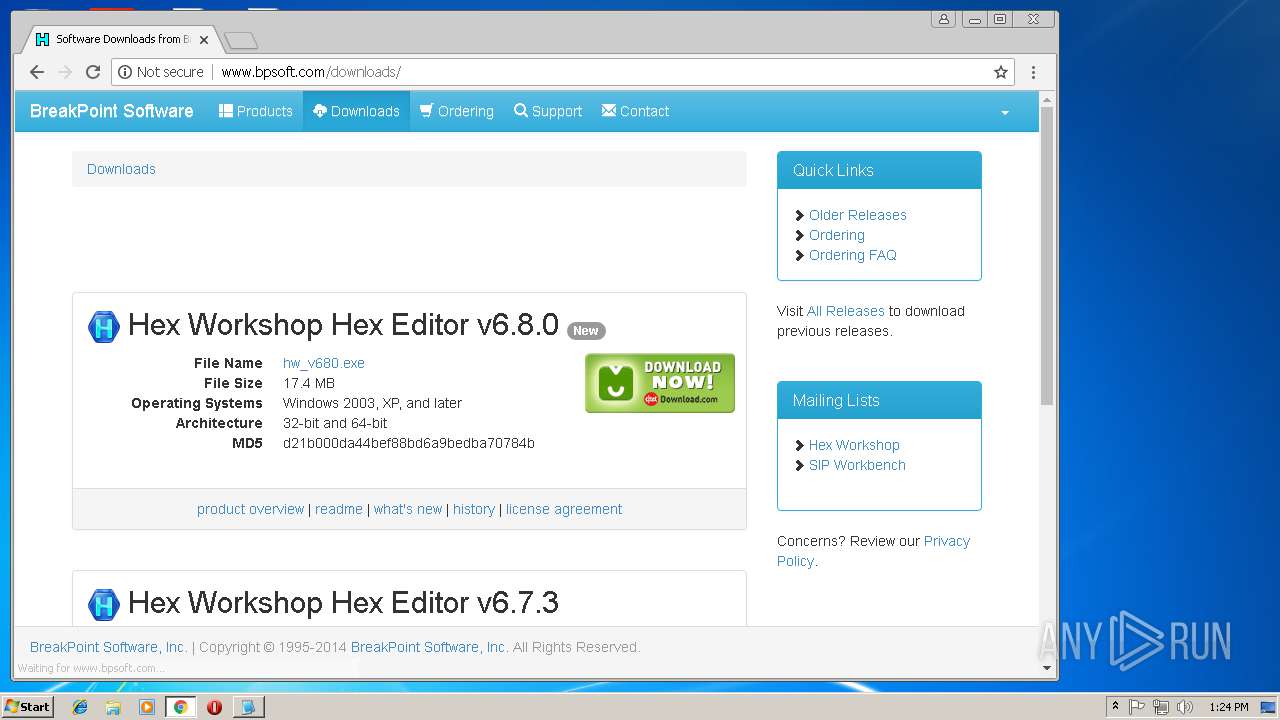
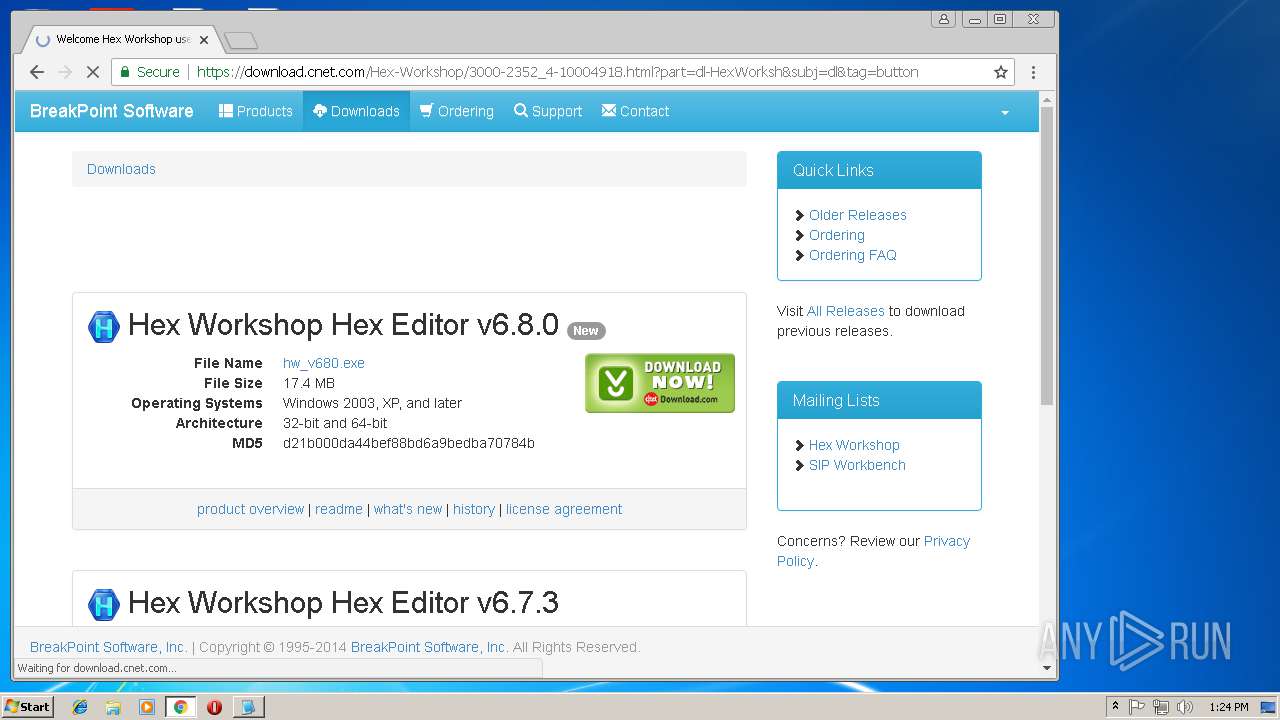
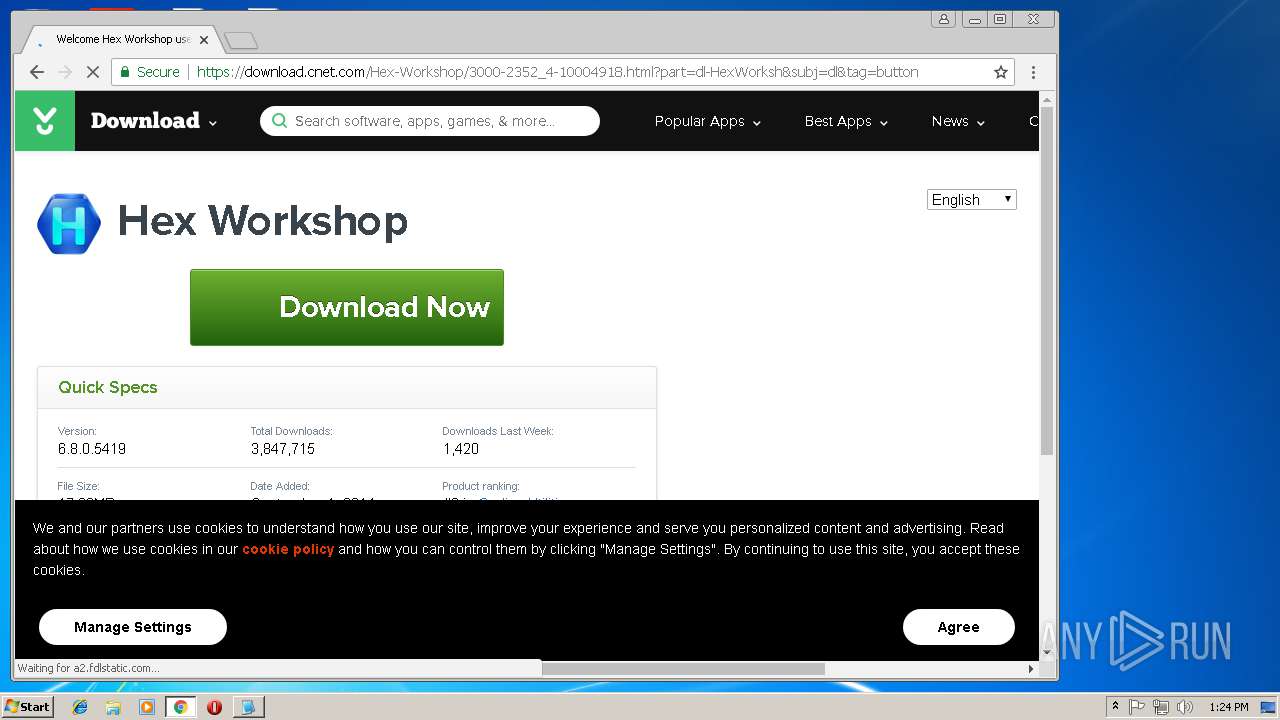
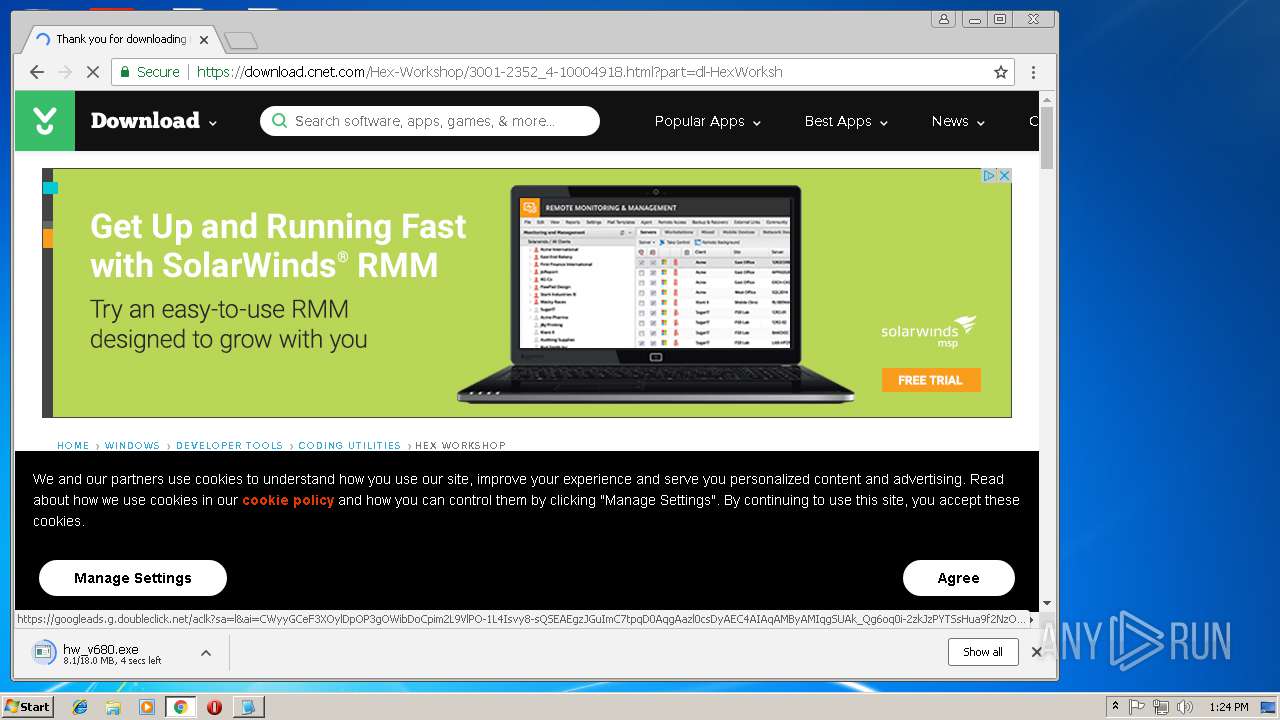
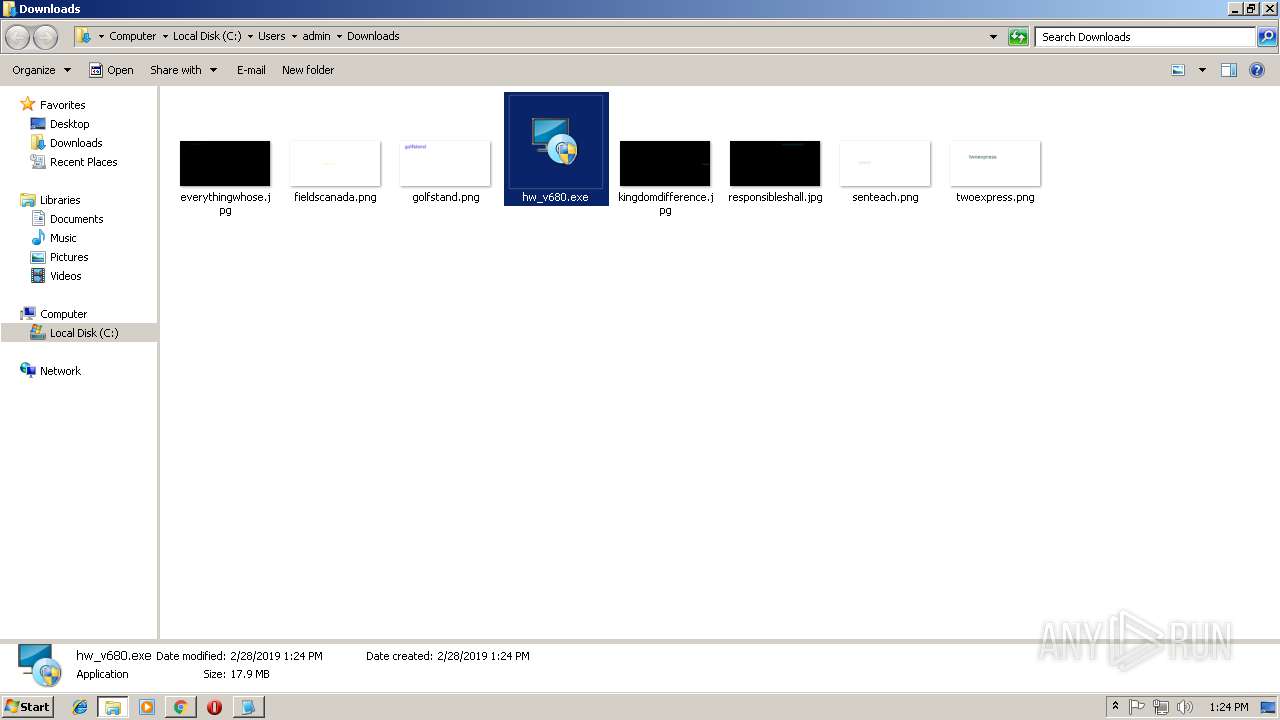
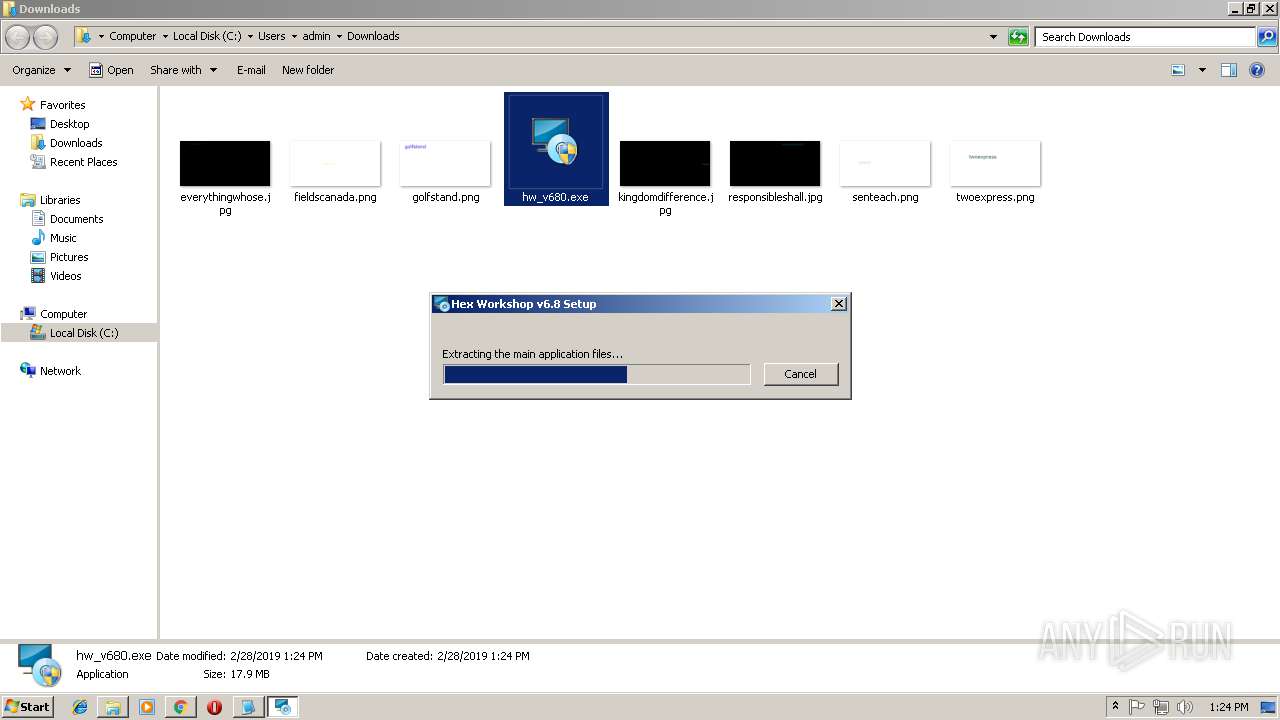
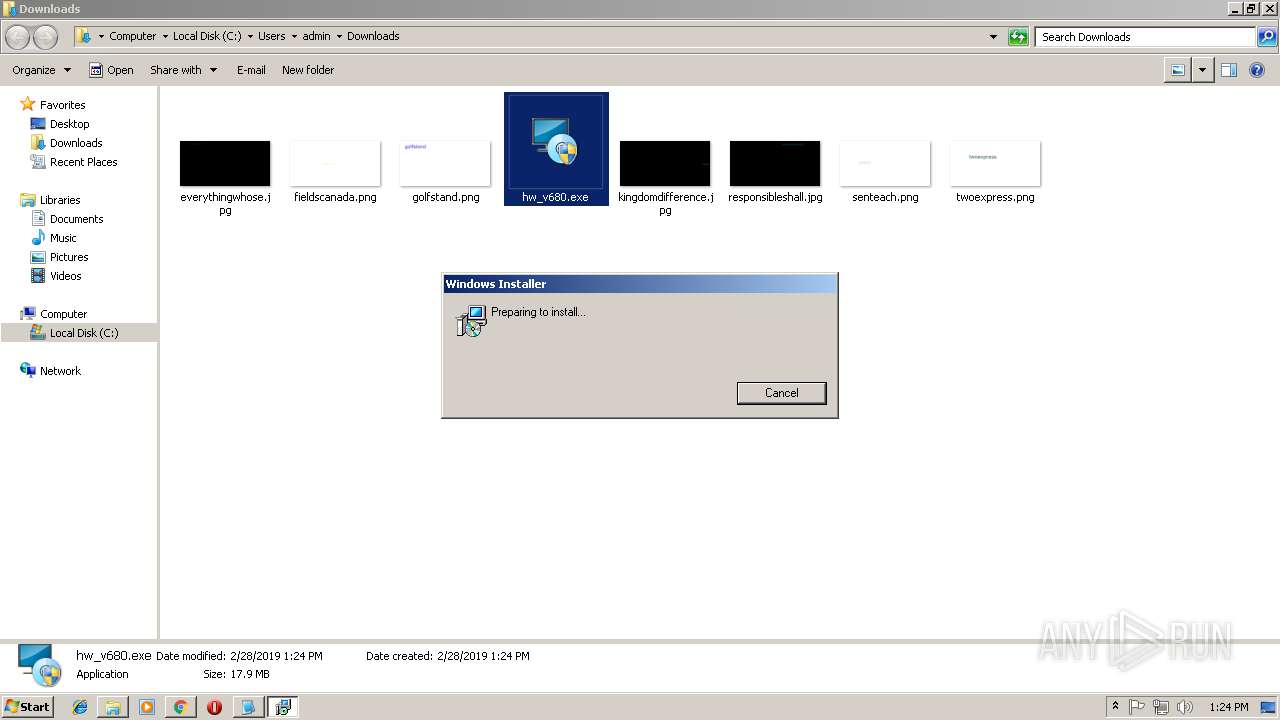
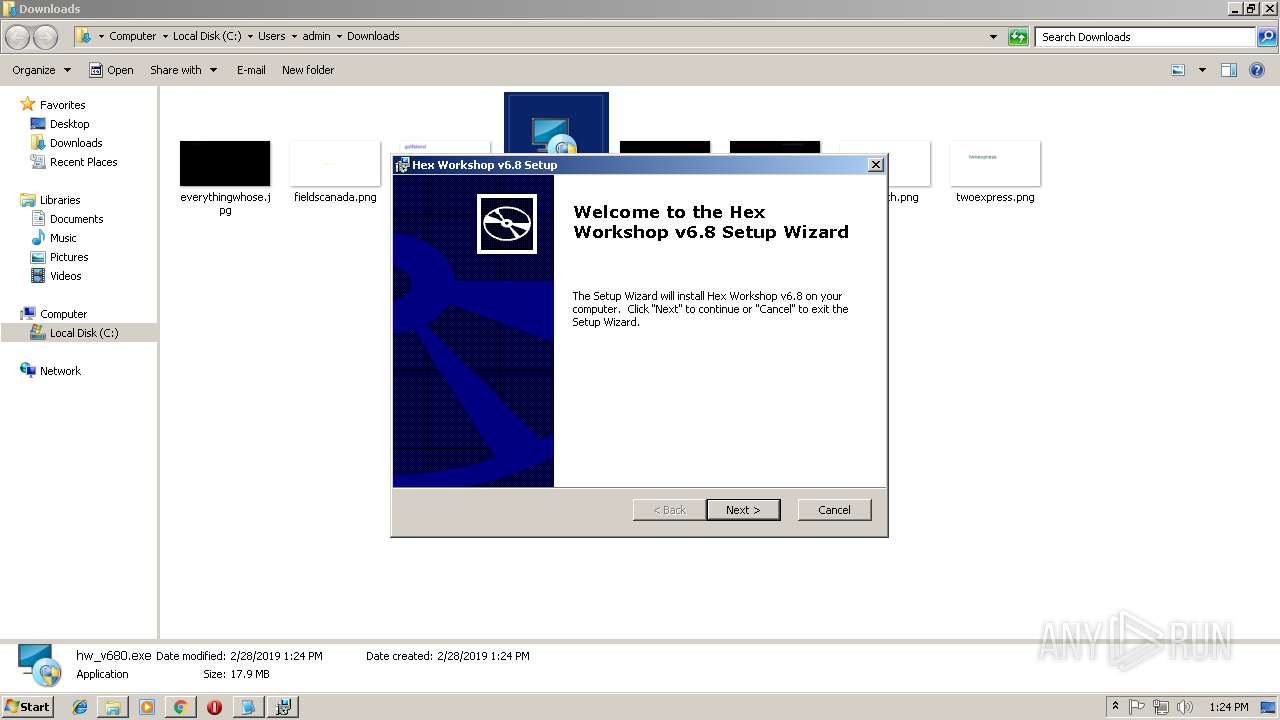
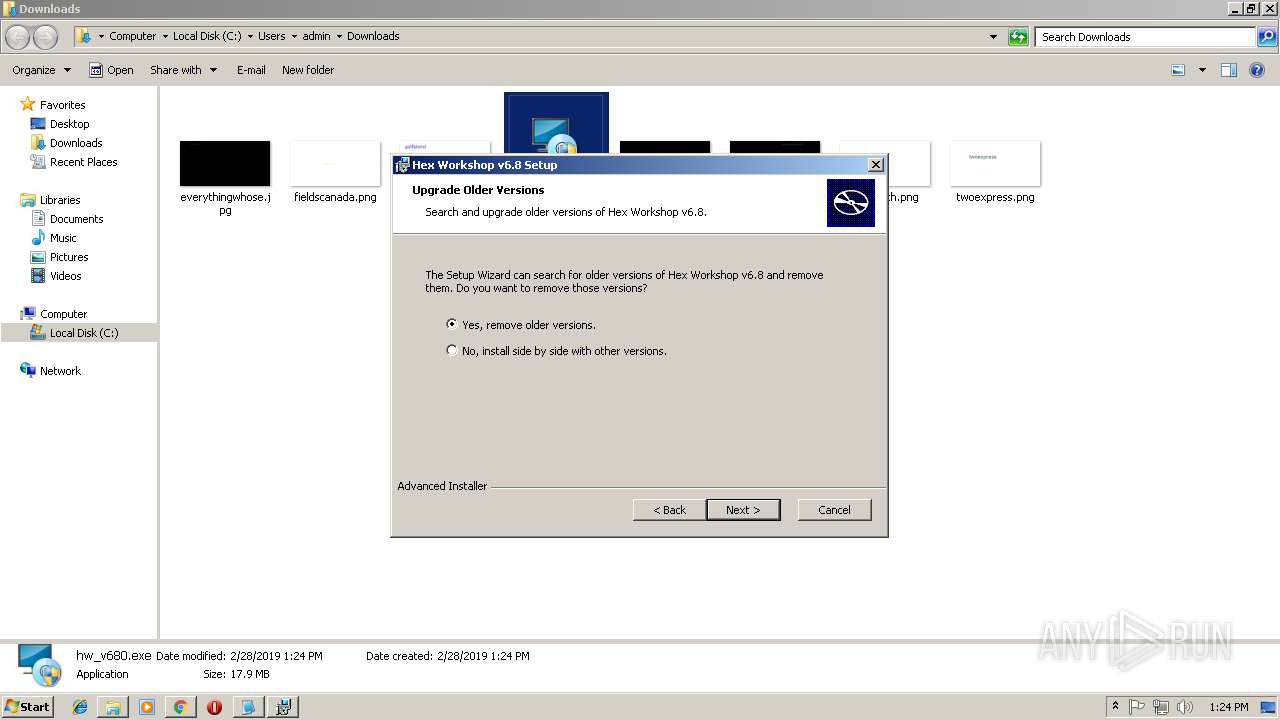
- hw_v680.exe (PID: 3192)
- NTPD32.BIN (PID: 3800)
- hw_v680.exe (PID: 3240)
Changes the autorun value in the registry
- notepad.exe (PID: 3116)
Changes settings of System certificates
- msiexec.exe (PID: 2716)
Loads dropped or rewritten executable
- hw_v680.exe (PID: 3240)
SUSPICIOUS
Starts itself from another location
- notepad.exe (PID: 3116)
Connects to unusual port
- notepad.exe (PID: 3116)
Executable content was dropped or overwritten
- chrome.exe (PID: 3292)
- notepad.exe (PID: 3116)
- hw_v680.exe (PID: 3240)
Creates executable files which already exist in Windows
- notepad.exe (PID: 3116)
Starts application with an unusual extension
- notepad.exe (PID: 3116)
Adds / modifies Windows certificates
- msiexec.exe (PID: 2716)
Creates files in the user directory
- hw_v680.exe (PID: 3240)
INFO
Application launched itself
- msiexec.exe (PID: 3088)
- chrome.exe (PID: 3292)
Reads settings of System Certificates
- chrome.exe (PID: 3292)
Reads Internet Cache Settings
- chrome.exe (PID: 3292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (37.8) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (23.7) |
| .exe | | | Win32 EXE Yoda's Crypter (23.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.7) |
| .exe | | | Win32 Executable (generic) (3.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 49152 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 102400 |
| EntryPoint: | 0x24f70 |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00019000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0001A000 | 0x0000C000 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.89684 |
.rsrc | 0x00026000 | 0x0002F0BA | 0x0002EC18 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.39555 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 7.67396 | 1032 | UNKNOWN | UNKNOWN | RT_STRING |
2 | 7.10169 | 254 | UNKNOWN | UNKNOWN | RT_STRING |
3 | 7.1505 | 304 | UNKNOWN | UNKNOWN | RT_STRING |
4 | 7.27011 | 328 | UNKNOWN | UNKNOWN | RT_STRING |
5 | 6.43979 | 140 | UNKNOWN | UNKNOWN | RT_STRING |
6 | 6.80017 | 198 | UNKNOWN | UNKNOWN | RT_STRING |
7 | 6.92772 | 216 | UNKNOWN | UNKNOWN | RT_STRING |
8 | 6.25648 | 116 | UNKNOWN | UNKNOWN | RT_STRING |
9 | 7.30067 | 364 | UNKNOWN | UNKNOWN | RT_STRING |
10 | 6.50976 | 138 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
KERNEL32.DLL |
advapi32.dll |
gdi32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
winmm.dll |
wsock32.dll |
Total processes
56
Monitored processes
22
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2160 | C:\Windows\system32\MsiExec.exe -Embedding A49F15713CA722A842C729DFAD051824 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,2461013689410946899,7884783509130630210,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=8FDD2902F407A4DCC235F2D89A01E46C --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8FDD2902F407A4DCC235F2D89A01E46C --renderer-client-id=8 --mojo-platform-channel-handle=3960 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,2461013689410946899,7884783509130630210,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=A30EFFF70AAB45DE670F39ABA8BD5F67 --mojo-platform-channel-handle=3840 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,2461013689410946899,7884783509130630210,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7A59026C4148948771E31D238535E408 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7A59026C4148948771E31D238535E408 --renderer-client-id=6 --mojo-platform-channel-handle=3572 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2448 | C:\USERS\ADMIN\APPDATA\LOCAL\TEMP\SVCHOST.EXE RST | C:\USERS\ADMIN\APPDATA\LOCAL\TEMP\SVCHOST.EXE | — | notepad.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,2461013689410946899,7884783509130630210,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=73C30412C7093EB87CC76667EA00C98A --mojo-platform-channel-handle=1020 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,2461013689410946899,7884783509130630210,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=9973B1AC4FB92A3B03DD2153D4AC303B --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9973B1AC4FB92A3B03DD2153D4AC303B --renderer-client-id=9 --mojo-platform-channel-handle=1668 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
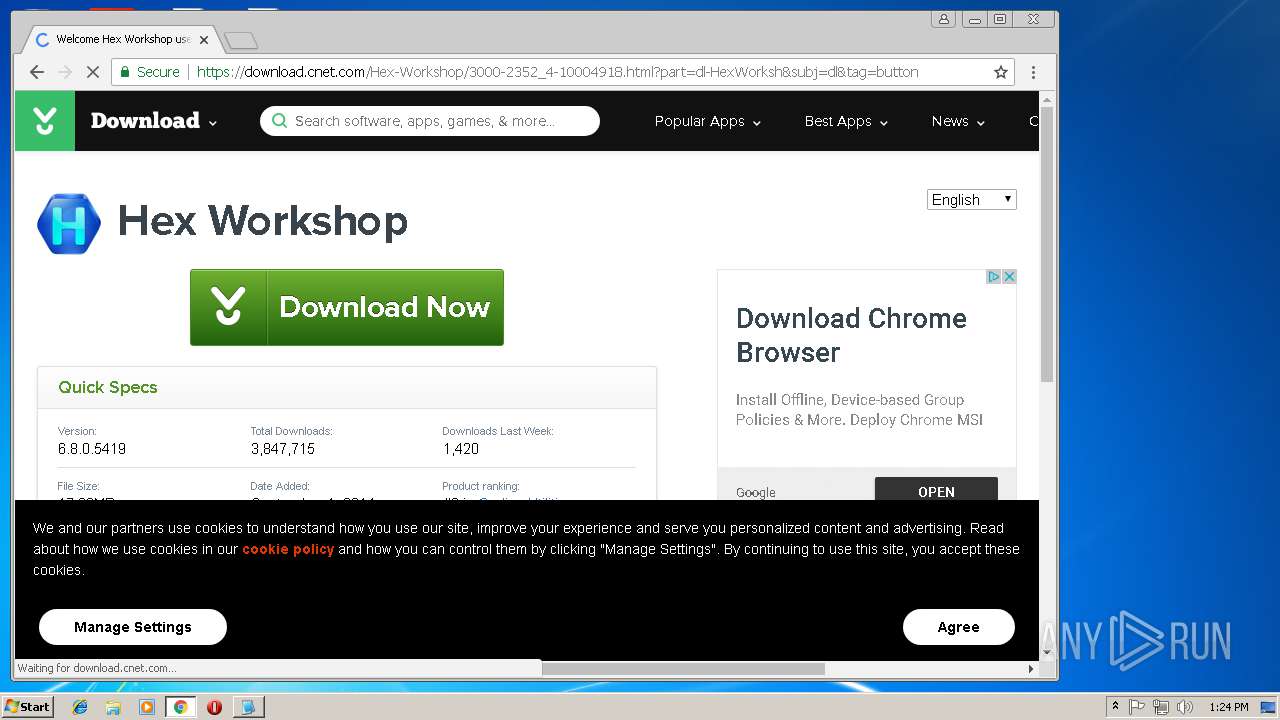
| 2716 | /i "C:\Users\admin\AppData\Roaming\BreakPoint Software\Hex Workshop v6.8\install\1DE165D\HexWorkshop.msi" TRANSFORMS="C:\Users\admin\AppData\Roaming\BreakPoint Software\Hex Workshop v6.8\install\1DE165D\HexWorkshop.mst" AI_SETUPEXEPATH="C:\Users\admin\Downloads\hw_v680.exe" SETUPEXEDIR="C:\Users\admin\Downloads\" | C:\Windows\system32\msiexec.exe | — | hw_v680.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,2461013689410946899,7884783509130630210,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=B4701B5AD7D44A7A4C707B76563CBB93 --mojo-platform-channel-handle=5884 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,2461013689410946899,7884783509130630210,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4DC69406A8CAA85F5ADAFC9ED7A797A2 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4DC69406A8CAA85F5ADAFC9ED7A797A2 --renderer-client-id=10 --mojo-platform-channel-handle=4276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
475
Read events
382
Write events
90
Delete events
3
Modification events
| (PID) Process: | (3116) notepad.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\notepad_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3116) notepad.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\notepad_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3116) notepad.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\notepad_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3116) notepad.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\notepad_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3116) notepad.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\notepad_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3116) notepad.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\notepad_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3116) notepad.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\notepad_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3116) notepad.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\notepad_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3116) notepad.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\notepad_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3116) notepad.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\notepad_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
29
Suspicious files
155
Text files
136
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4b6c960e-077d-46cb-8076-d9d7839f12b0.tmp | — | |
MD5:— | SHA256:— | |||
| 3292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3116 | notepad.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\System32\TRACERT.BIN | binary | |
MD5:— | SHA256:— | |||
| 3292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\728f1406-6b07-42a0-a5a9-7198d5740081.tmp | — | |
MD5:— | SHA256:— | |||
| 3292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1b1a99.TMP | text | |
MD5:— | SHA256:— | |||
| 3292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 3292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
254
DNS requests
166
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3292 | chrome.exe | GET | 302 | 157.240.1.35:80 | http://www.facebook.com/plugins/like.php?app_id=213908491992252&href=https%3A%2F%2Fwww.facebook.com%2Fpages%2FHex-Workshop%2F229114507133108&send=false&layout=button_count&show_faces=false&action=like&colorscheme=light&font&height=21&width=150 | US | — | — | whitelisted |
3292 | chrome.exe | GET | 200 | 18.217.251.91:80 | http://www.hexworkshop.com/images/ss_v65/tn2_ss_hworks_compare.gif | US | image | 17.4 Kb | unknown |
3292 | chrome.exe | GET | 200 | 18.217.251.91:80 | http://www.hexworkshop.com/images/download3K-award.gif | US | image | 3.12 Kb | unknown |
3292 | chrome.exe | GET | 200 | 18.217.251.91:80 | http://www.hexworkshop.com/history/6_72/tn_structviewer_bitfield_enum.gif | US | image | 11.8 Kb | unknown |
3292 | chrome.exe | GET | 200 | 18.217.251.91:80 | http://www.hexworkshop.com/js/bpsoft.js | US | text | 867 b | unknown |
3292 | chrome.exe | GET | 200 | 18.217.251.91:80 | http://www.hexworkshop.com/js/bootstrap.min.js | US | text | 27.1 Kb | unknown |
3292 | chrome.exe | GET | 200 | 18.217.251.91:80 | http://www.hexworkshop.com/images/downloadpipe_5star.gif | US | image | 6.51 Kb | unknown |
3292 | chrome.exe | GET | 200 | 18.217.251.91:80 | http://www.hexworkshop.com/fonts/glyphicons-halflings-regular.woff | US | woff | 22.7 Kb | unknown |
3292 | chrome.exe | GET | 200 | 18.217.251.91:80 | http://www.hexworkshop.com/images/softpedia_pick_award_b.gif | US | image | 5.90 Kb | unknown |
3292 | chrome.exe | GET | 200 | 18.217.251.91:80 | http://www.hexworkshop.com/ | US | html | 13.1 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3116 | notepad.exe | 89.108.116.192:6667 | irc.wenet.ru | Domain names registrar REG.RU, Ltd | RU | unknown |
3292 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3292 | chrome.exe | 172.217.16.163:443 | www.google.de | Google Inc. | US | whitelisted |
3292 | chrome.exe | 172.217.21.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3292 | chrome.exe | 172.217.16.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3292 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3292 | chrome.exe | 172.217.16.196:443 | www.google.com | Google Inc. | US | whitelisted |
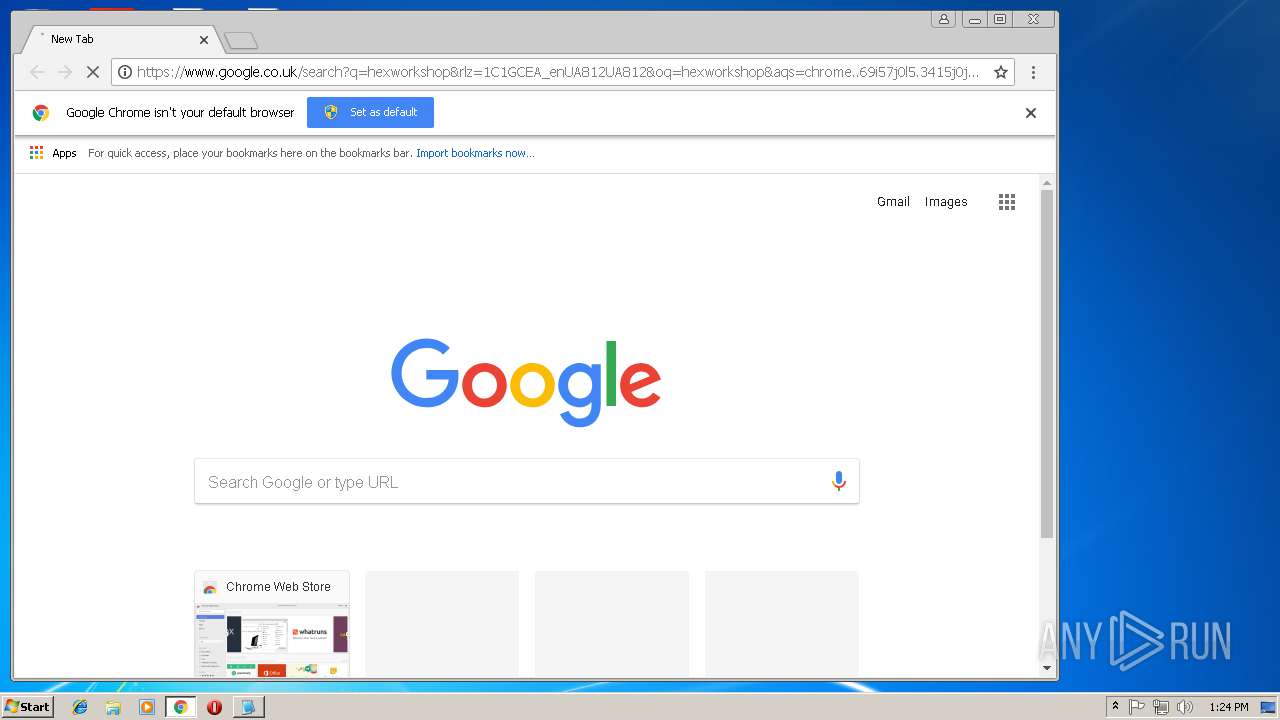
3292 | chrome.exe | 216.58.208.35:443 | www.google.co.uk | Google Inc. | US | whitelisted |
3292 | chrome.exe | 18.217.251.91:80 | www.hexworkshop.com | Amazon.com, Inc. | US | unknown |
3292 | chrome.exe | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
irc.wenet.ru |
| unknown |
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.co.uk |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3116 | notepad.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3116 | notepad.exe | Misc activity | ET CHAT IRC authorization message |