| File name: | NtfsFreeSetup.exe |
| Full analysis: | https://app.any.run/tasks/d57a0823-3221-473b-9900-90a5caa637db |
| Verdict: | Malicious activity |
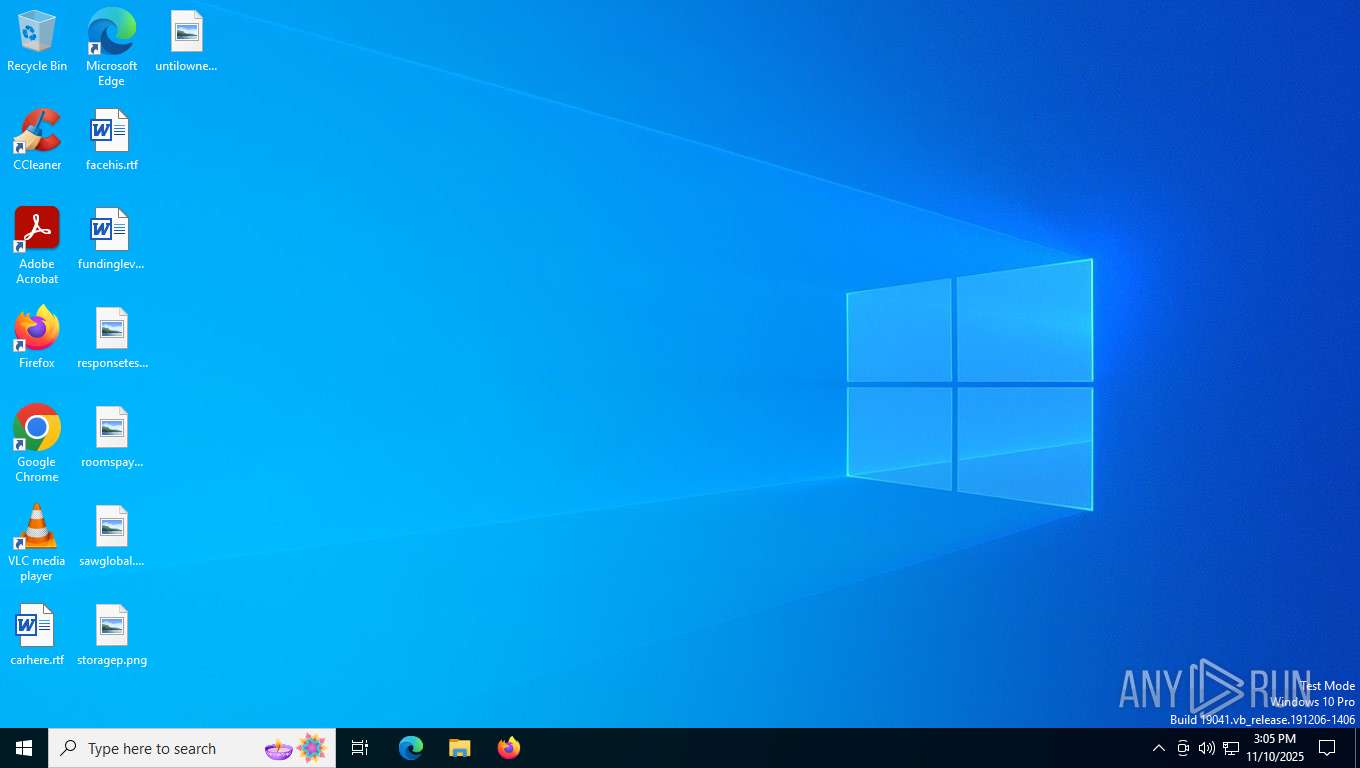
| Analysis date: | November 10, 2025, 15:05:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | F391DF13BED4D43A44523DA1F5C7039A |
| SHA1: | EC63C0EA56809666CA3D320FE3791AA3316FEC00 |
| SHA256: | 25B7E16F72D21070A4BA41D06C7536E54BF33E152035367EE543C3401C3E8AA4 |
| SSDEEP: | 98304:dVCDS2MRMaURIvrmM8URIvjyOV5n4gy9j0FSU7fl7b7PIiUzL/FV7rvHiupjIUsK:PW+9 |
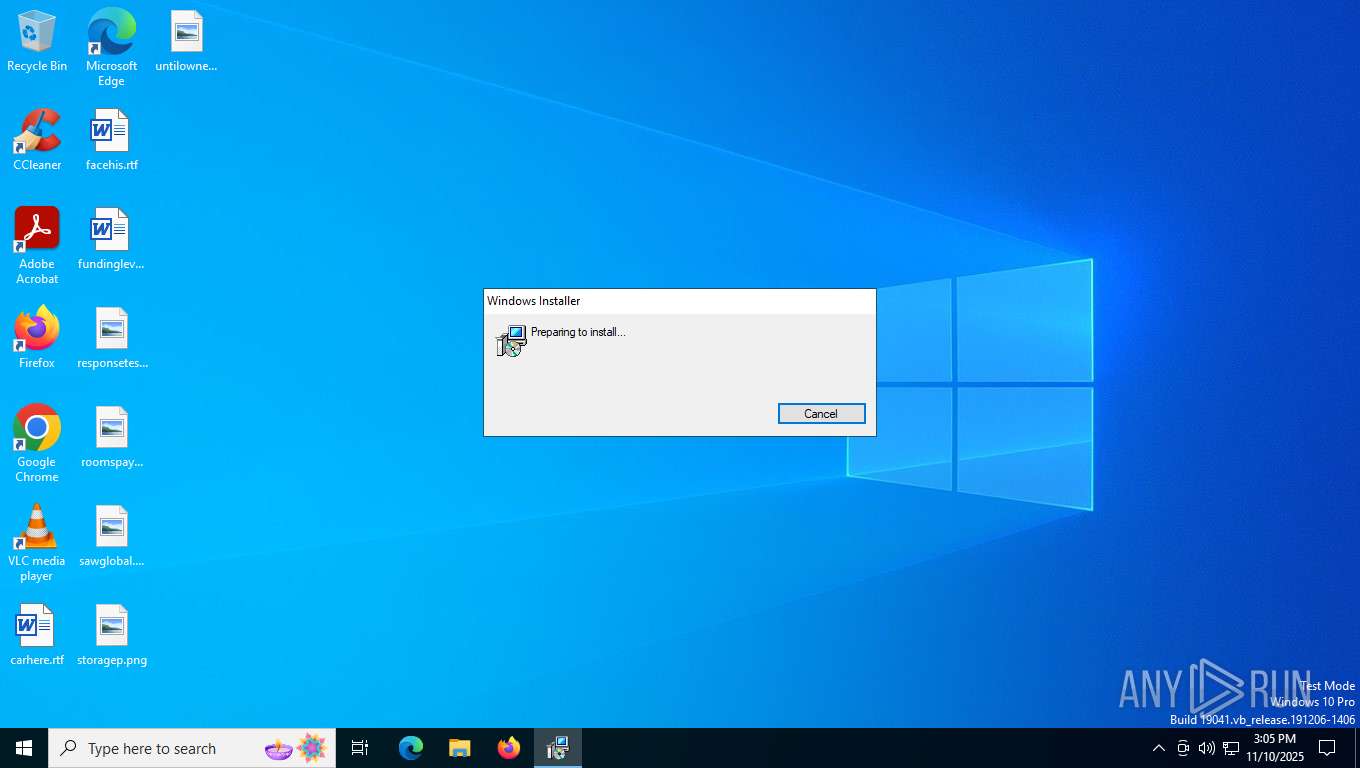
MALICIOUS
Executing a file with an untrusted certificate
- NtfsFreeSetup.exe (PID: 5900)
SUSPICIOUS
Executable content was dropped or overwritten
- NtfsFreeSetup.exe (PID: 5900)
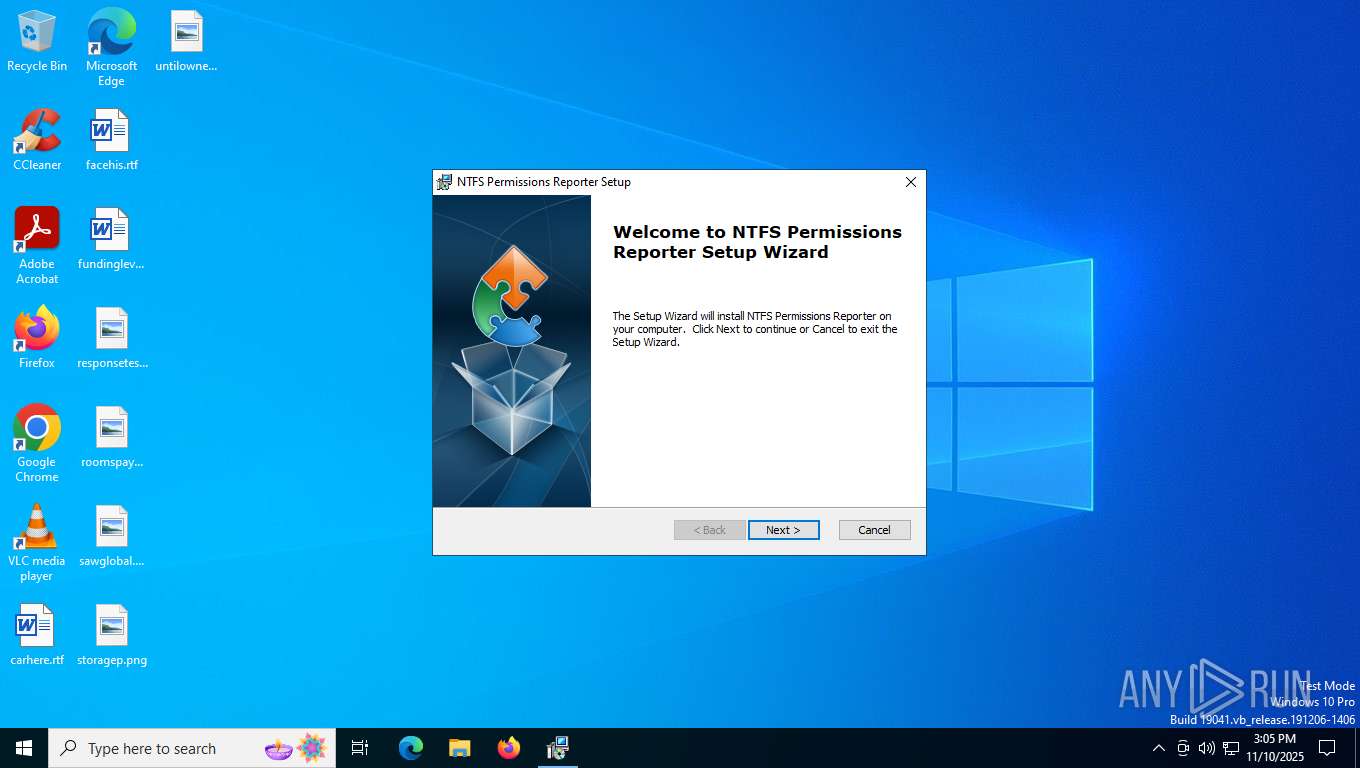
Detects AdvancedInstaller (YARA)
- NtfsFreeSetup.exe (PID: 5900)
There is functionality for taking screenshot (YARA)
- NtfsFreeSetup.exe (PID: 5900)
ADVANCEDINSTALLER mutex has been found
- NtfsFreeSetup.exe (PID: 5900)
INFO
Creates files or folders in the user directory
- NtfsFreeSetup.exe (PID: 5900)
- msiexec.exe (PID: 4084)
Reads the computer name
- NtfsFreeSetup.exe (PID: 5900)
- msiexec.exe (PID: 7344)
- msiexec.exe (PID: 7444)
Checks supported languages
- msiexec.exe (PID: 7344)
- msiexec.exe (PID: 7444)
- NtfsFreeSetup.exe (PID: 5900)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4084)
Reads the software policy settings
- msiexec.exe (PID: 4084)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 4084)
The sample compiled with english language support
- NtfsFreeSetup.exe (PID: 5900)
Checks proxy server information
- msiexec.exe (PID: 4084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:05:27 14:19:09+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 277504 |
| InitializedDataSize: | 171520 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2ff27 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.0.0 |
| ProductVersionNumber: | 2.2.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| CompanyName: | Cjwdev |
| FileDescription: | This installer database contains the logic and data required to install NTFS Permissions Reporter. |
| FileVersion: | 2.2.0 |
| InternalName: | NtfsFreeSetup |
| LegalCopyright: | Copyright (C) Cjwdev |
| OriginalFileName: | NtfsFreeSetup.exe |
| ProductName: | NTFS Permissions Reporter |
| ProductVersion: | 2.2.0 |
Total processes
151
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4084 | /i "C:\Users\admin\AppData\Roaming\Cjwdev\NTFS Permissions Reporter 2.2.0\install\NtfsFreeSetup.x64.msi" AI_SETUPEXEPATH="C:\Users\admin\AppData\Local\Temp\NtfsFreeSetup.exe" SETUPEXEDIR="C:\Users\admin\AppData\Local\Temp\" EXE_CMD_LINE="/exenoupdates /exelang 0 /noprereqs " | C:\Windows\System32\msiexec.exe | NtfsFreeSetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5900 | "C:\Users\admin\AppData\Local\Temp\NtfsFreeSetup.exe" | C:\Users\admin\AppData\Local\Temp\NtfsFreeSetup.exe | explorer.exe | ||||||||||||
User: admin Company: Cjwdev Integrity Level: MEDIUM Description: This installer database contains the logic and data required to install NTFS Permissions Reporter. Version: 2.2.0 Modules
| |||||||||||||||
| 7344 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7444 | C:\Windows\syswow64\MsiExec.exe -Embedding A8D826049681205A31CBD5D8D6969A62 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8184 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 133
Read events
4 133
Write events
0
Delete events
0
Modification events
Executable files
6
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4084 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI2669.tmp | executable | |
MD5:7452F56AF87D0912C3A06206DC77C0A6 | SHA256:19989417F3F411C8A02AA09F1DD51A7FEBC530F0F27C8D3F7DD195BA224E6FBA | |||
| 4084 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI26D7.tmp | executable | |
MD5:7452F56AF87D0912C3A06206DC77C0A6 | SHA256:19989417F3F411C8A02AA09F1DD51A7FEBC530F0F27C8D3F7DD195BA224E6FBA | |||
| 4084 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI2785.tmp | executable | |
MD5:7452F56AF87D0912C3A06206DC77C0A6 | SHA256:19989417F3F411C8A02AA09F1DD51A7FEBC530F0F27C8D3F7DD195BA224E6FBA | |||
| 4084 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\248DDD9FCF61002E219645695E3FFC98_6D438EAF986CF8B7C4ED7E3B62B57F9D | binary | |
MD5:9DAC35104B2CCDBB9085E330B3153AB9 | SHA256:621F2B90EA6B46402219D2D1EDAED0F67D4BA446F2845FC14432DEC32F809B70 | |||
| 4084 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\248DDD9FCF61002E219645695E3FFC98_6D438EAF986CF8B7C4ED7E3B62B57F9D | binary | |
MD5:C813339EC4773823296F4251A89EF939 | SHA256:4BC324FED128C57314C5BE3B6AF66516AC2E0738D891D882310372D08DF47A31 | |||
| 4084 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI2765.tmp | executable | |
MD5:50A3D9C4C3B6AFDA98BD6B0C60363175 | SHA256:4337CDFE01A45F6691CF883B57D5663788FDA9A368A1EAC989CB16E31F049AC0 | |||
| 5900 | NtfsFreeSetup.exe | C:\Users\admin\AppData\Roaming\Cjwdev\NTFS Permissions Reporter 2.2.0\install\NtfsFreeSetup.x64.msi | executable | |
MD5:D54FB728778609E0ACCC15D09A103664 | SHA256:A03316373EB257101EA0476E63424D95393C1781E61F958B4D99DA038B6289F7 | |||
| 4084 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\FE17BEC2A573BC9AE36869D0274FFA19_6DA81F04C5F9EAD2CD0268808FCE61E1 | binary | |
MD5:6D72F082BAC7C20B3C2D95C53756F271 | SHA256:C03ECEFBE987CA0209041E876A31C281E8B7E8A2F85A4C6927CFBA0BC8A67886 | |||
| 4084 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\FE17BEC2A573BC9AE36869D0274FFA19_6DA81F04C5F9EAD2CD0268808FCE61E1 | binary | |
MD5:61D90F82A2F0EDC98BF60883A590A982 | SHA256:C1FA44B85833E428B10CA18485E42C34C1DBC516CB999865CF8BEC1271B97D54 | |||
| 5900 | NtfsFreeSetup.exe | C:\Users\admin\AppData\Roaming\Cjwdev\NTFS Permissions Reporter 2.2.0\install\NtfsFreeSetup.msi | executable | |
MD5:A56EDDEF77989827345E2EC7E34FA3A5 | SHA256:5870134B27142258D617FF5975842A062A00348895C60CA068CC3F6D49C1A5F8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
22
DNS requests
15
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1384 | svchost.exe | GET | 200 | 95.101.35.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8024 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
4084 | msiexec.exe | GET | 200 | 18.173.205.43:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQg3SSkKA74hABkhmlBtJTz8w3hlAQU%2BWC71OPVNPa49QaAJadz20ZpqJ4CEEJLalPOx2YUHCpjsaUcQQQ%3D | unknown | — | — | whitelisted |
4084 | msiexec.exe | GET | 200 | 18.173.205.43:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSoEwb5tith0jIBy9frSyNGB1lsAAQUNr1J%2FzEs669qQP6ZwBbtuvxI3V8CEGZqXAfgn1Lr2XPtpAT0Sz4%3D | unknown | — | — | whitelisted |
8024 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
8024 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
4048 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8024 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1384 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2792 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4084 | msiexec.exe | 18.173.205.43:80 | ocsps.ssl.com | — | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4048 | svchost.exe | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4048 | svchost.exe | 23.63.118.230:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1384 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1384 | svchost.exe | 95.101.35.35:80 | crl.microsoft.com | Orange | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsps.ssl.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |