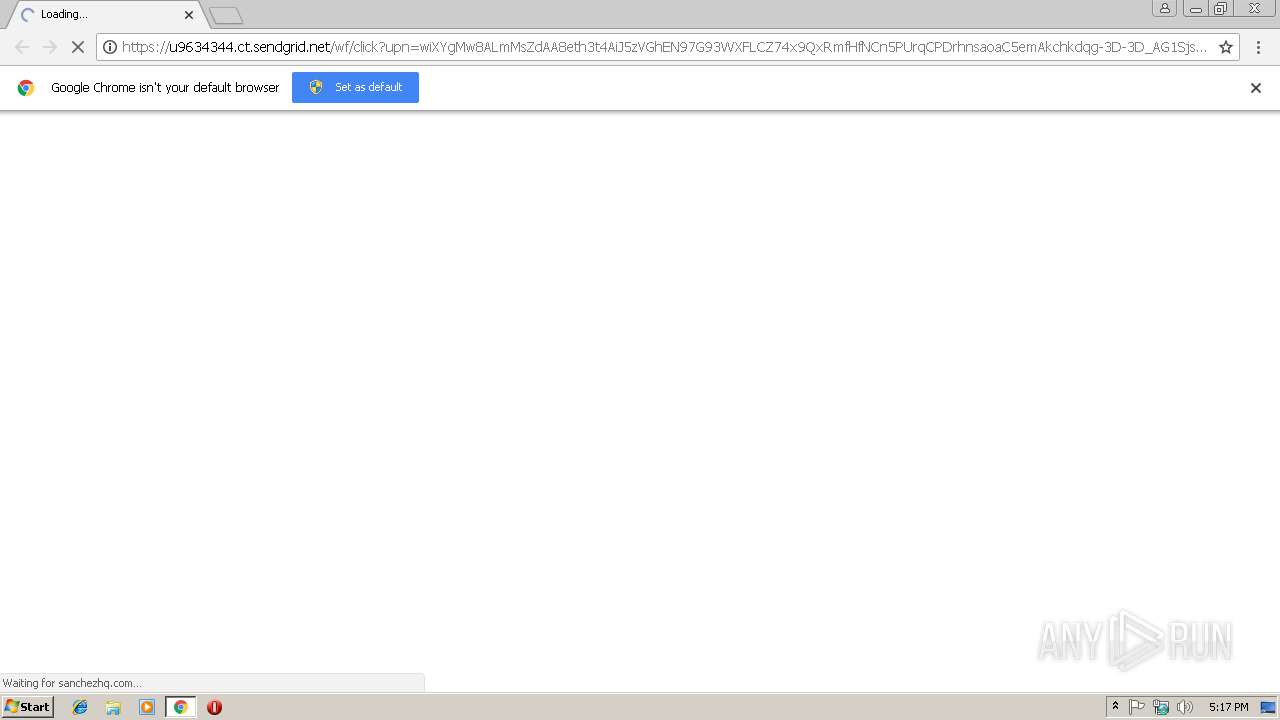
| URL: | https://u9634344.ct.sendgrid.net/wf/click?upn=wiXYgMw8ALmMsZdAA8eth3t4AiJ5zVGhEN97G93WXFLCZ74x9QxRmfHfNCn5PUrqCPDrhnsaoaC5emAkchkdqg-3D-3D_AG1SjsNIqD754Em6BVCQNBo4lagZlgpiJQgCWslQt1RVJND-2FehCoqTBrypej-2B3eLfT-2BmHEieZm1-2BKxxW-2FSXpaJjs1XumUiqHRh-2BHSyJ2OEVi-2FD0WaSMnb8XoIrv4nkGqvMZRfNV-2BQgx36NNxtZQMfMmhIzsErTzcDFhE6uFLXljFKU-2F5Lb3CMl3etbDv1ajLhyhIO2pDeUy9Y03zSWq-2BYQ-3D-3D |
| Full analysis: | https://app.any.run/tasks/8cd8a3ec-7c8b-4b64-b9c2-95a56eeff440 |
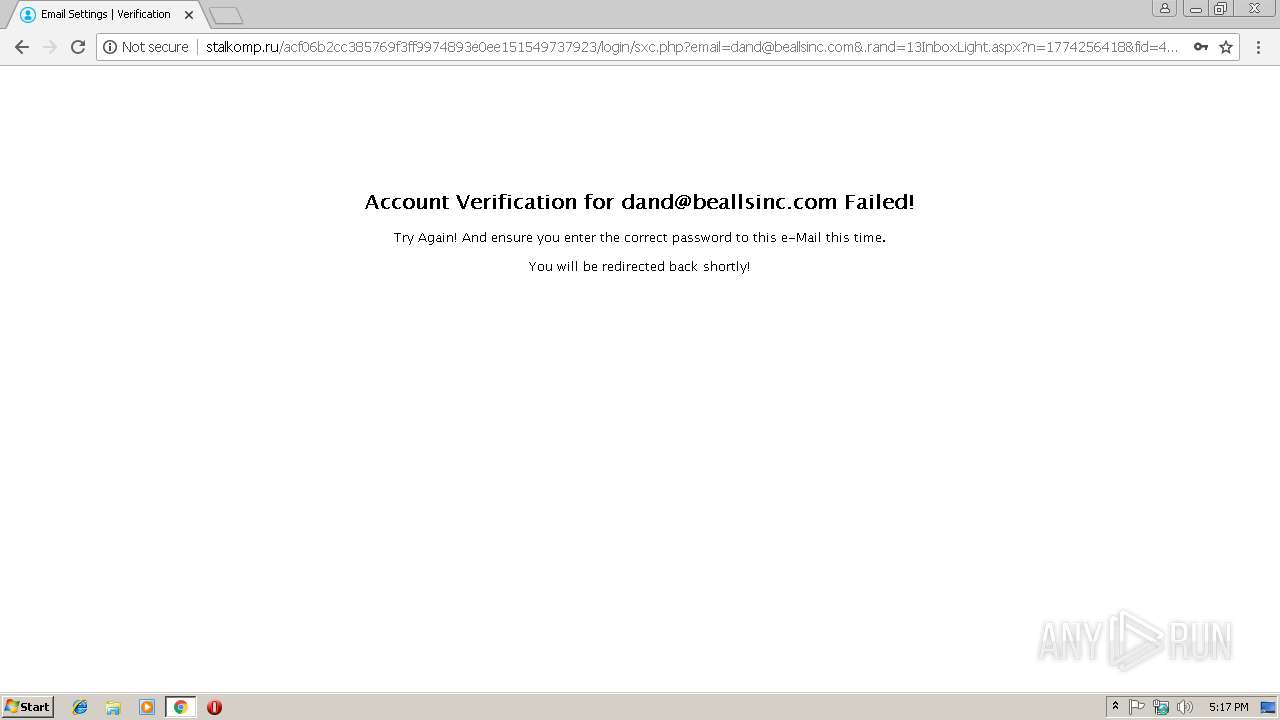
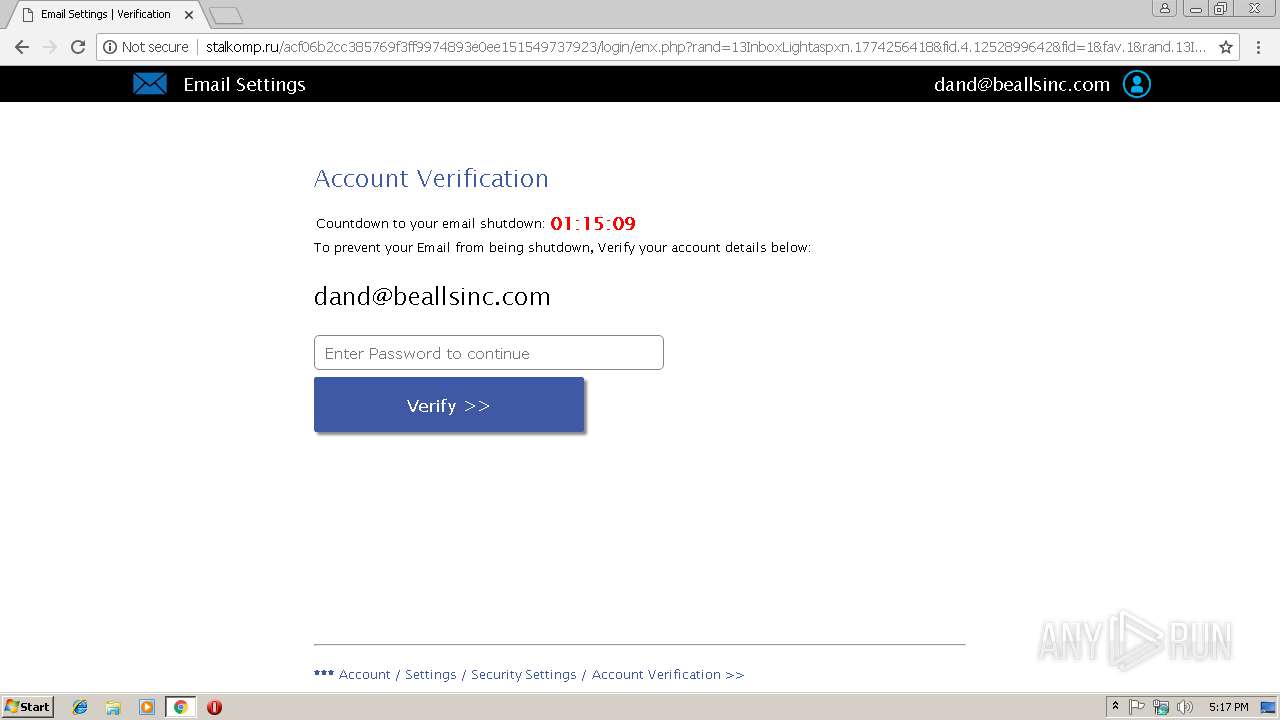
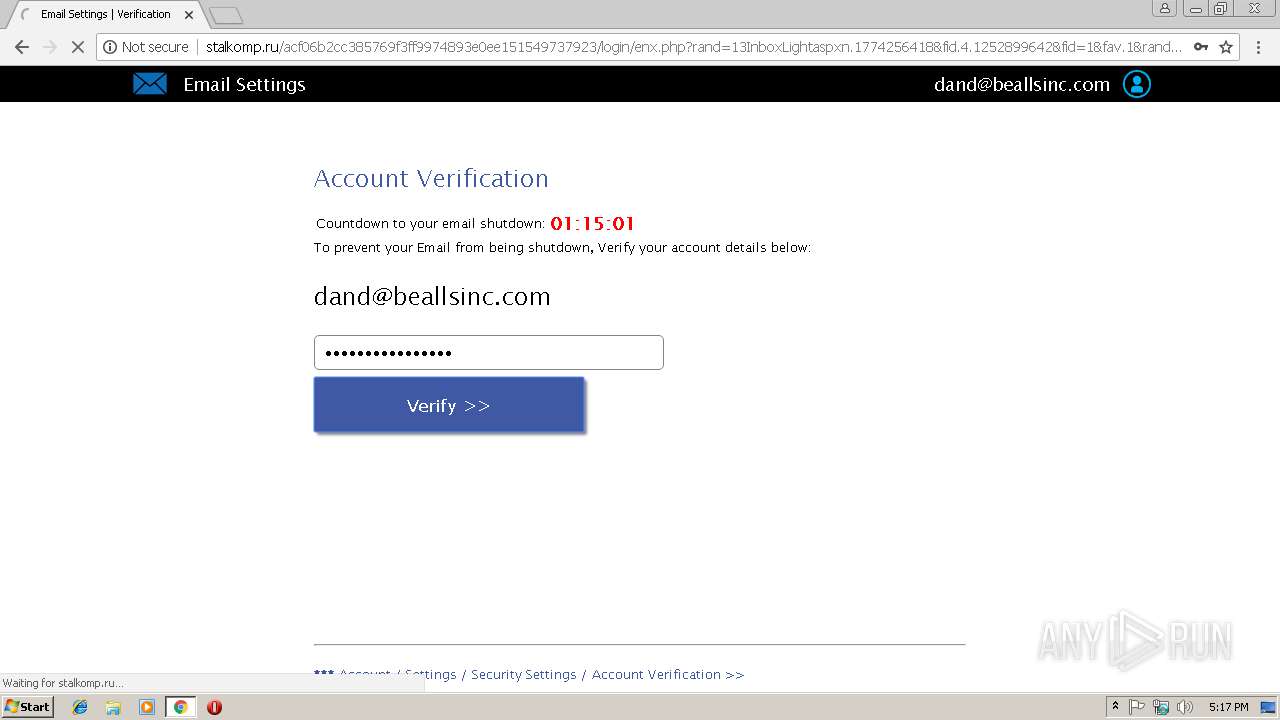
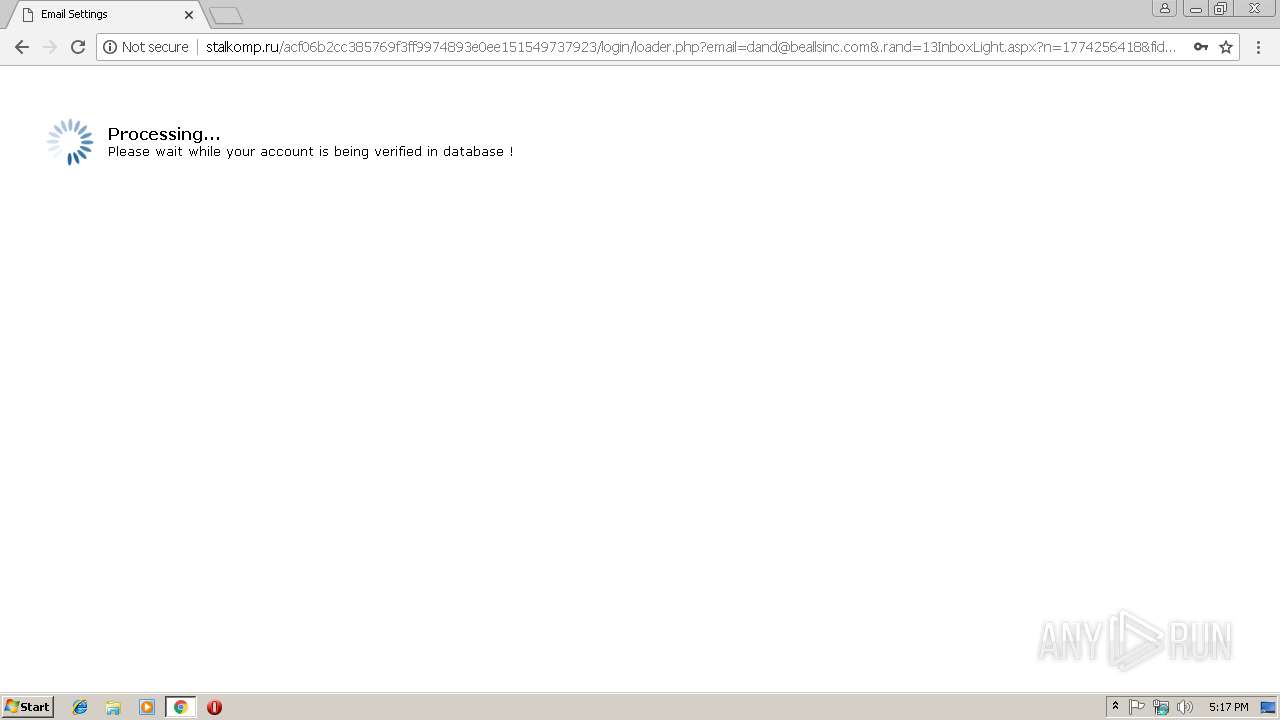
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 17:16:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C41BDE00F5A9678CF8D080CF65A3064E |
| SHA1: | 8C9F976039205E11E5B7E2D9201E5638CDDA4F3A |
| SHA256: | 25B1765A0D40B128459965160DF7AF409C56C156871E6C3947D46E165E74038B |
| SSDEEP: | 6:2ORzSDSzMUO6uHDYQ6JfmD9kivOjrzSyqs9on4fRVMrDVl5Dq8OkX0l7SXL71v:2pDSgX6uHR6RmaivOjvkpkRQDNsyYmfh |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads settings of System Certificates
- chrome.exe (PID: 2992)
Application launched itself
- chrome.exe (PID: 2992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
9
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=884,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --service-pipe-token=9A0EAD4AFD8AFA7516EDF6E549A9802B --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9A0EAD4AFD8AFA7516EDF6E549A9802B --renderer-client-id=4 --mojo-platform-channel-handle=1900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=884,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=95C298D4CBA1F20CBDBD3538705138B6 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=95C298D4CBA1F20CBDBD3538705138B6 --renderer-client-id=5 --mojo-platform-channel-handle=3364 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2996 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://u9634344.ct.sendgrid.net/wf/click?upn=wiXYgMw8ALmMsZdAA8eth3t4AiJ5zVGhEN97G93WXFLCZ74x9QxRmfHfNCn5PUrqCPDrhnsaoaC5emAkchkdqg-3D-3D_AG1SjsNIqD754Em6BVCQNBo4lagZlgpiJQgCWslQt1RVJND-2FehCoqTBrypej-2B3eLfT-2BmHEieZm1-2BKxxW-2FSXpaJjs1XumUiqHRh-2BHSyJ2OEVi-2FD0WaSMnb8XoIrv4nkGqvMZRfNV-2BQgx36NNxtZQMfMmhIzsErTzcDFhE6uFLXljFKU-2F5Lb3CMl3etbDv1ajLhyhIO2pDeUy9Y03zSWq-2BYQ-3D-3D | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=884,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5FF347CEDC66FF0C09262B8C888C6DE1 --mojo-platform-channel-handle=2536 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=884,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=DAC8E5C8FC45F92C8EABF8810E0D22FA --mojo-platform-channel-handle=2900 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x701500b0,0x701500c0,0x701500cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=884,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --service-pipe-token=D98078C2AB2F37394DB98912B6D15B63 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=D98078C2AB2F37394DB98912B6D15B63 --renderer-client-id=3 --mojo-platform-channel-handle=2160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 4064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=884,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=11BFF5CE3237868FC9DA1CE0606B0AEB --mojo-platform-channel-handle=980 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
501
Read events
456
Write events
42
Delete events
3
Modification events
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2992-13194983826619750 |
Value: 259 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
0
Suspicious files
32
Text files
60
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e3c0b8fa-974f-4119-bfc5-557d9f0be6d2.tmp | — | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9c7069f5-8f50-4ef6-be23-ae4e8400a05e.tmp | — | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old~RF20e8dd.TMP | text | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
42
DNS requests
22
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
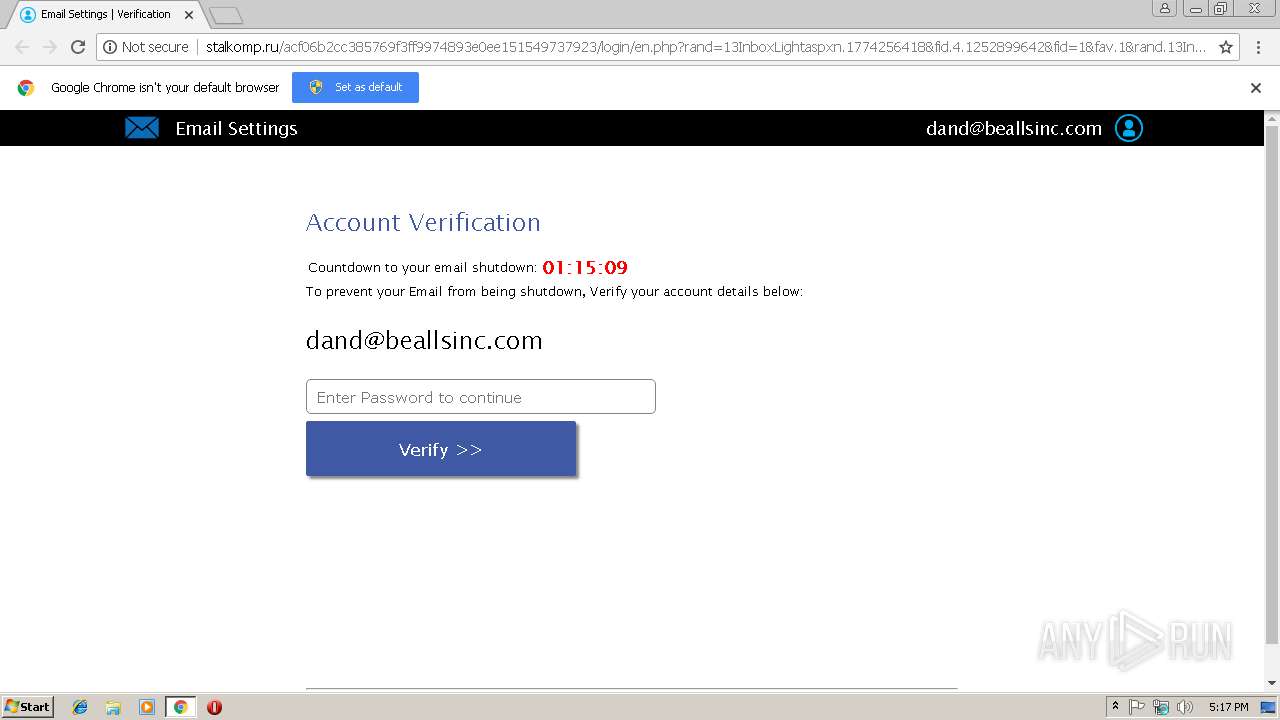
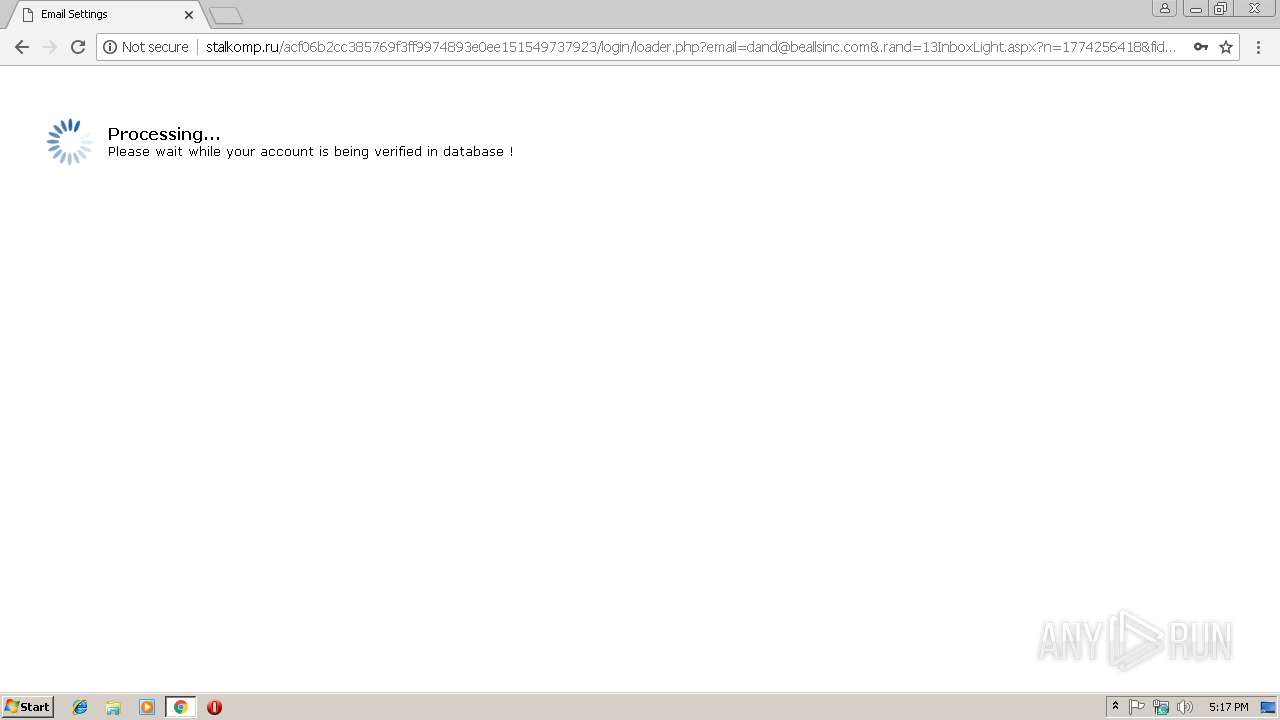
2992 | chrome.exe | GET | 200 | 78.110.50.154:80 | http://stalkomp.ru/acf06b2cc385769f3ff9974893e0ee151549737923/login/index.php?email=dand@beallsinc.com | RU | text | 273 b | malicious |
2992 | chrome.exe | GET | 200 | 78.110.50.154:80 | http://stalkomp.ru/acf06b2cc385769f3ff9974893e0ee151549737923/login/en.php?rand=13InboxLightaspxn.1774256418&fid.4.1252899642&fid=1&fav.1&rand.13InboxLight.aspxn.1774256418&fid.1252899642&fid.1&fav.1&email=ZGFuZEBiZWFsbHNpbmMuY29t&.rand=13InboxLight.aspx?n=1774256418&fid=4 | RU | html | 11.7 Kb | malicious |
2992 | chrome.exe | GET | 200 | 78.110.50.154:80 | http://stalkomp.ru/acf06b2cc385769f3ff9974893e0ee151549737923/login/enx.php?rand=13InboxLightaspxn.1774256418&fid.4.1252899642&fid=1&fav.1&rand.13InboxLight.aspxn.1774256418&fid.1252899642&fid.1&fav.1&email=dand@beallsinc.com&.rand=13InboxLight.aspx?n=1774256418&fid=4 | RU | html | 11.7 Kb | malicious |
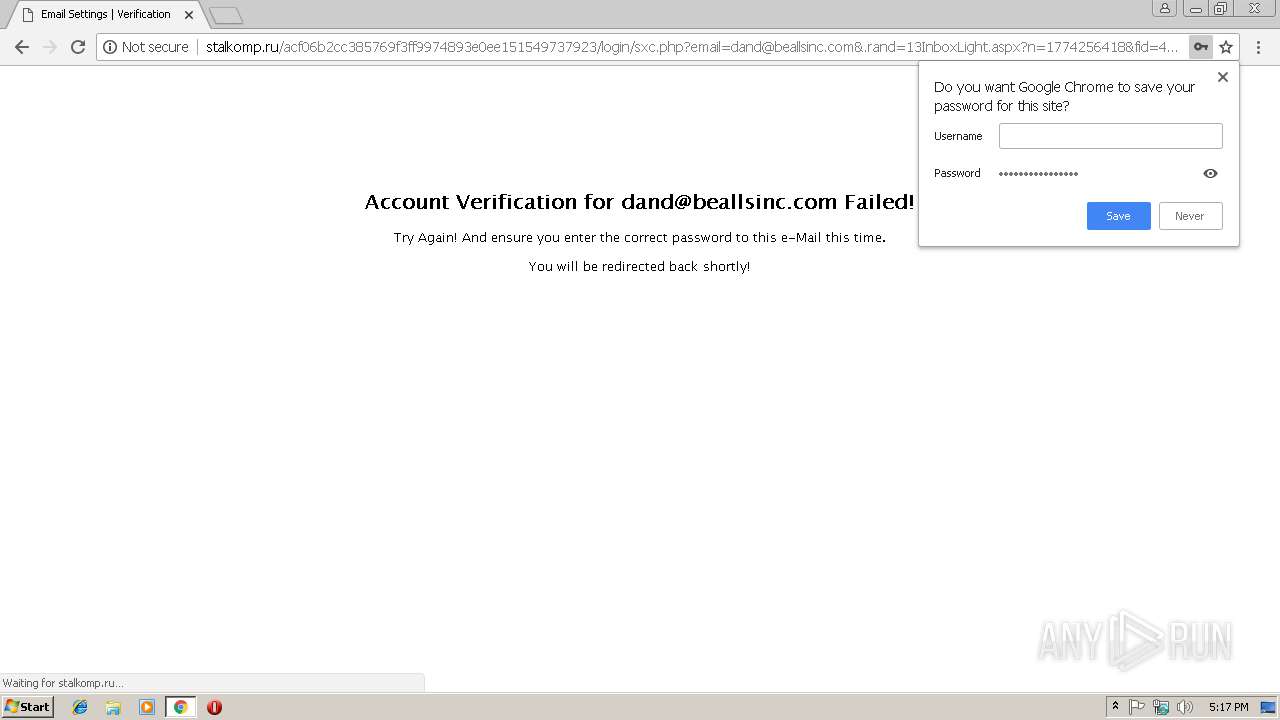
2992 | chrome.exe | GET | 200 | 78.110.50.154:80 | http://stalkomp.ru/acf06b2cc385769f3ff9974893e0ee151549737923/login/sxc.php?email=dand@beallsinc.com&.rand=13InboxLight.aspx?n=1774256418&fid=4 | RU | html | 1.12 Kb | malicious |
2992 | chrome.exe | GET | 404 | 78.110.50.154:80 | http://stalkomp.ru/favicon.ico | RU | html | 311 b | malicious |
2992 | chrome.exe | GET | 404 | 78.110.50.154:80 | http://stalkomp.ru/acf06b2cc385769f3ff9974893e0ee151549737923/login/files/errors.css | RU | html | 365 b | malicious |
2992 | chrome.exe | GET | 404 | 78.110.50.154:80 | http://stalkomp.ru/acf06b2cc385769f3ff9974893e0ee151549737923/login/files/signin.css | RU | html | 365 b | malicious |
2992 | chrome.exe | GET | 404 | 78.110.50.154:80 | http://stalkomp.ru/acf06b2cc385769f3ff9974893e0ee151549737923/login/files/i.css | RU | html | 360 b | malicious |
2992 | chrome.exe | GET | 404 | 78.110.50.154:80 | http://stalkomp.ru/acf06b2cc385769f3ff9974893e0ee151549737923/login/files/element.js?cb=googleTranslateElementInit | RU | html | 365 b | malicious |
2992 | chrome.exe | GET | 404 | 78.110.50.154:80 | http://stalkomp.ru/acf06b2cc385769f3ff9974893e0ee151549737923/login/files/bootstrap.css | RU | html | 368 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2992 | chrome.exe | 78.110.50.154:80 | stalkomp.ru | ZAO Hosting Telesystems | RU | malicious |
2992 | chrome.exe | 50.87.35.176:443 | sanchezhq.com | Unified Layer | US | unknown |
2992 | chrome.exe | 23.236.62.147:80 | beallsinc.com | Google Inc. | US | whitelisted |
2992 | chrome.exe | 35.246.12.233:443 | www.beallsinc.com | — | US | malicious |
2992 | chrome.exe | 35.244.177.48:443 | static.wixstatic.com | — | US | unknown |
2992 | chrome.exe | 13.32.158.173:443 | static.parastorage.com | Amazon.com, Inc. | US | whitelisted |
2992 | chrome.exe | 34.236.27.14:443 | ecom.wix.com | Amazon.com, Inc. | US | unknown |
2992 | chrome.exe | 52.3.155.93:443 | ecom.wix.com | Amazon.com, Inc. | US | unknown |
2992 | chrome.exe | 34.194.96.135:443 | frog.wix.com | Amazon.com, Inc. | US | unknown |
2992 | chrome.exe | 151.101.122.109:443 | f.vimeocdn.com | Fastly | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
u9634344.ct.sendgrid.net |
| malicious |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
sanchezhq.com |
| unknown |
stalkomp.ru |
| malicious |
ssl.gstatic.com |
| whitelisted |
beallsinc.com |
| whitelisted |
www.beallsinc.com |
| malicious |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2992 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT Hex Obfuscation of Script Tag % Encoding |
2992 | chrome.exe | Potentially Bad Traffic | ET INFO Multiple Javascript Unescapes - Common Obfuscation Observed in Phish Landing |
2992 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT Hex Obfuscation of Script Tag % Encoding |
2992 | chrome.exe | Potentially Bad Traffic | ET INFO Multiple Javascript Unescapes - Common Obfuscation Observed in Phish Landing |
9 ETPRO signatures available at the full report