| File name: | aa1abf98e7e54c5eaf2239a6da1c7bb1.exe |
| Full analysis: | https://app.any.run/tasks/cd9f21e0-054e-4978-8f23-292434bd2707 |
| Verdict: | No threats detected |
| Analysis date: | September 11, 2018, 06:54:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AA1ABF98E7E54C5EAF2239A6DA1C7BB1 |
| SHA1: | 7B2E39EA8030FC59EFB110B1D9532B78100E0FFA |
| SHA256: | 2554E569E2F915A9A8D7EC1FB2979C984A09D702381AB81EEF59064C8EC2E5EC |
| SSDEEP: | 98304:cFmv0eoxDoV01bci68Mja4+9R0TnS/X3Ro4+YZnviNIO8c4LcGNJR7n7R5HmgnJQ:cRxeObRYa3eTnSX3+4/Zv/RR7n7HQ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Application launched itself
- aa1abf98e7e54c5eaf2239a6da1c7bb1.exe (PID: 2036)
Executable content was dropped or overwritten
- aa1abf98e7e54c5eaf2239a6da1c7bb1.exe (PID: 3256)
Creates files in the Windows directory
- aa1abf98e7e54c5eaf2239a6da1c7bb1.exe (PID: 3256)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.3) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
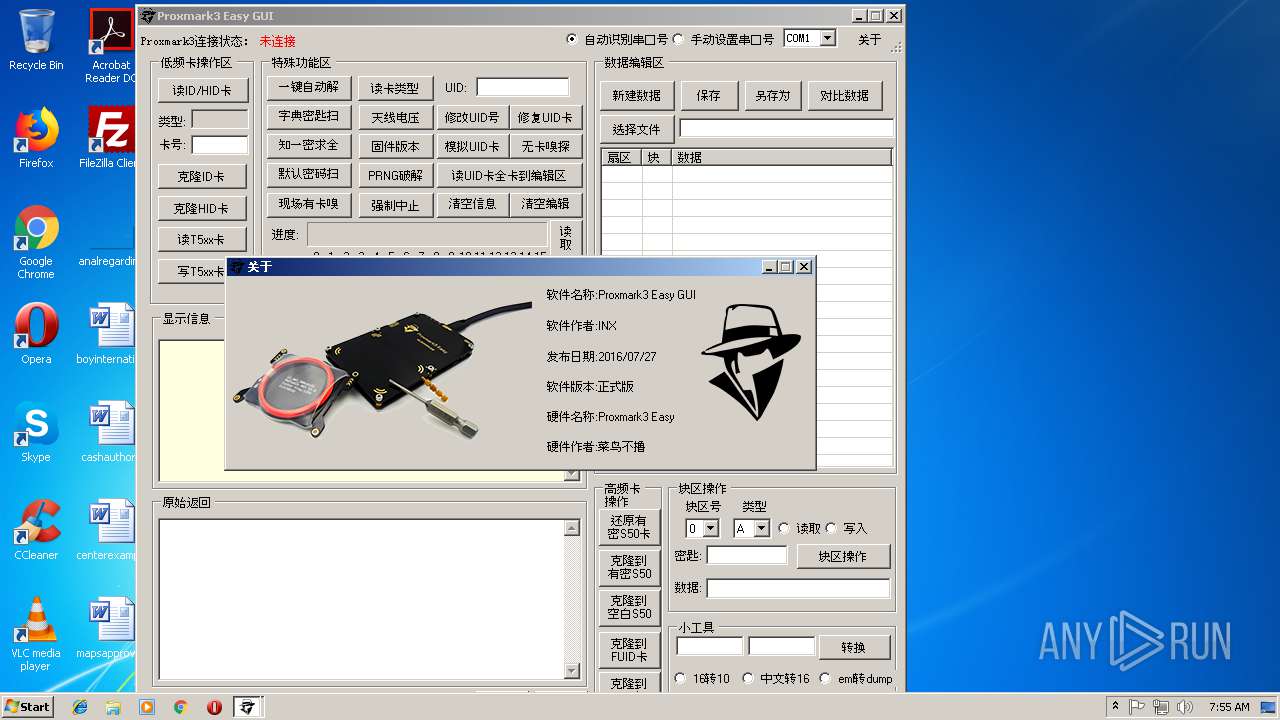
| TimeStamp: | 2016:07:27 18:36:43+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | - |
| InitializedDataSize: | - |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5d01f5 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | CHINA |
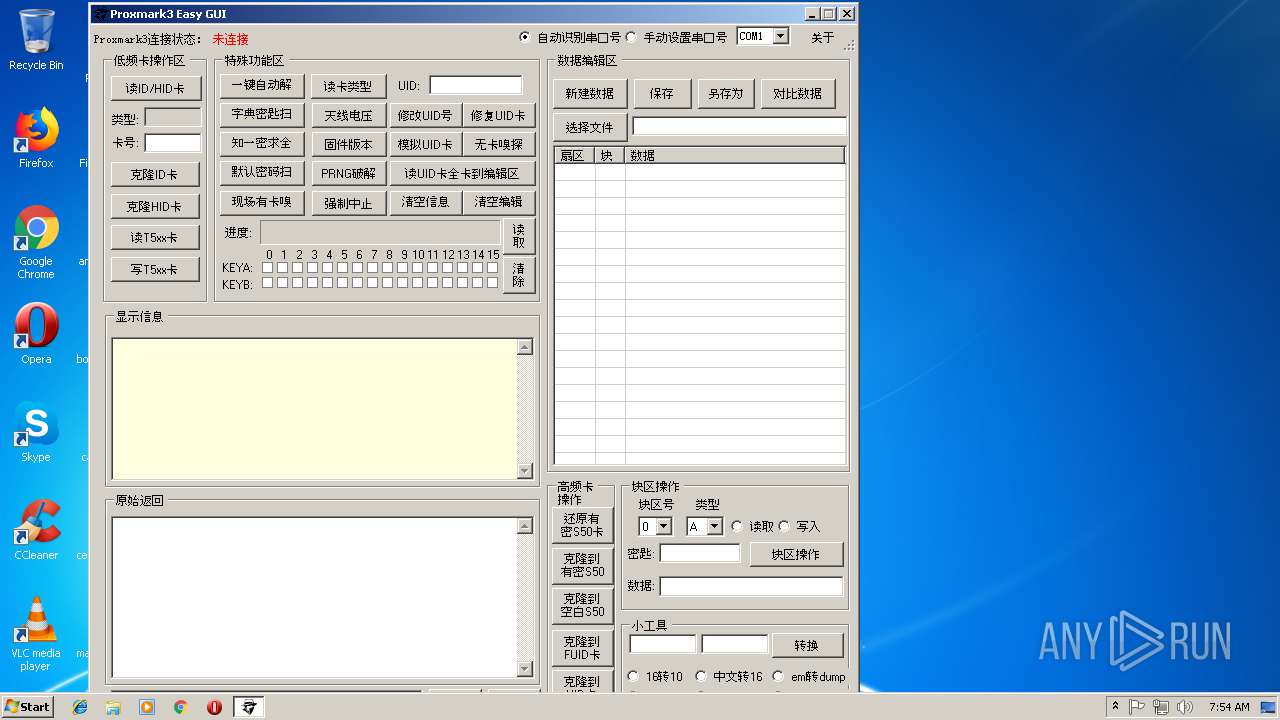
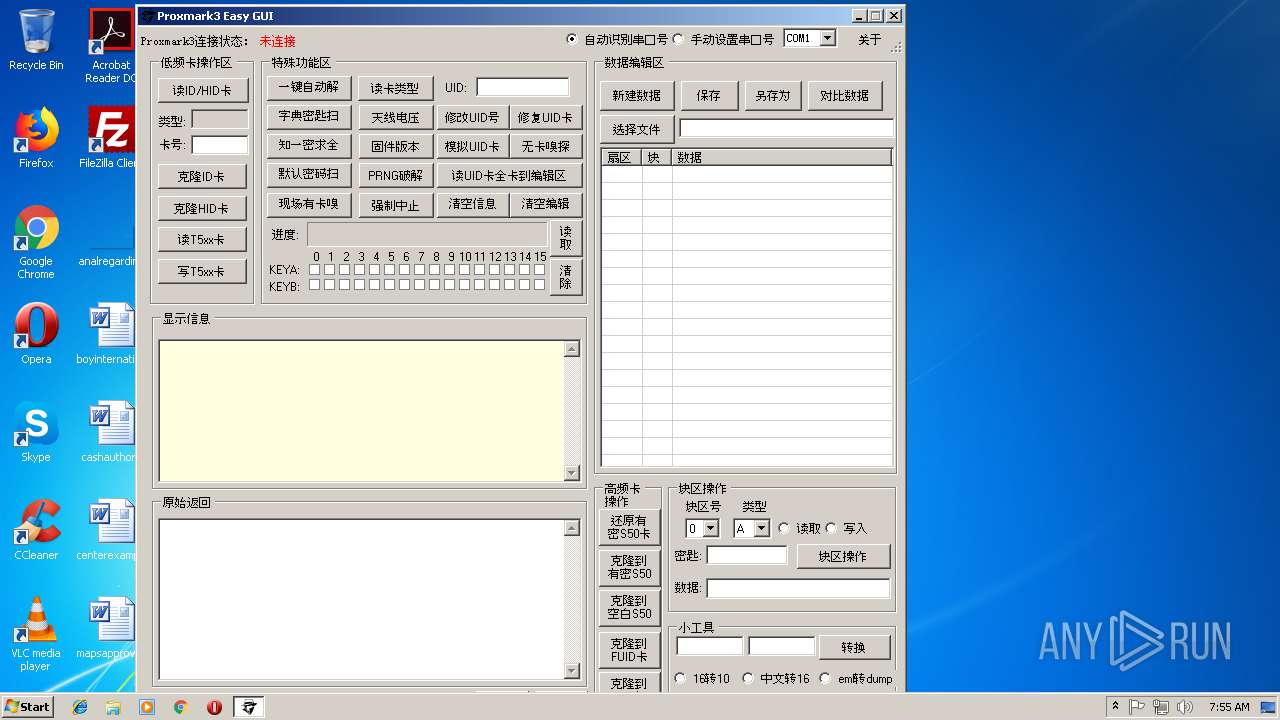
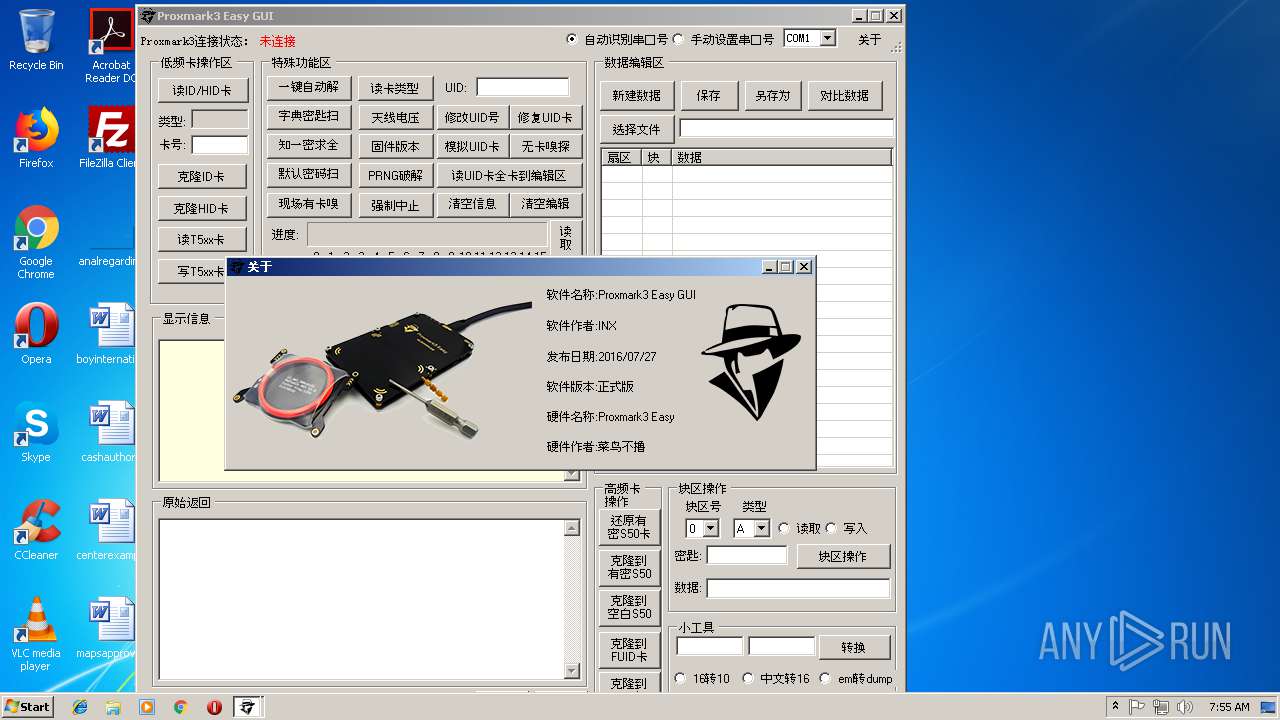
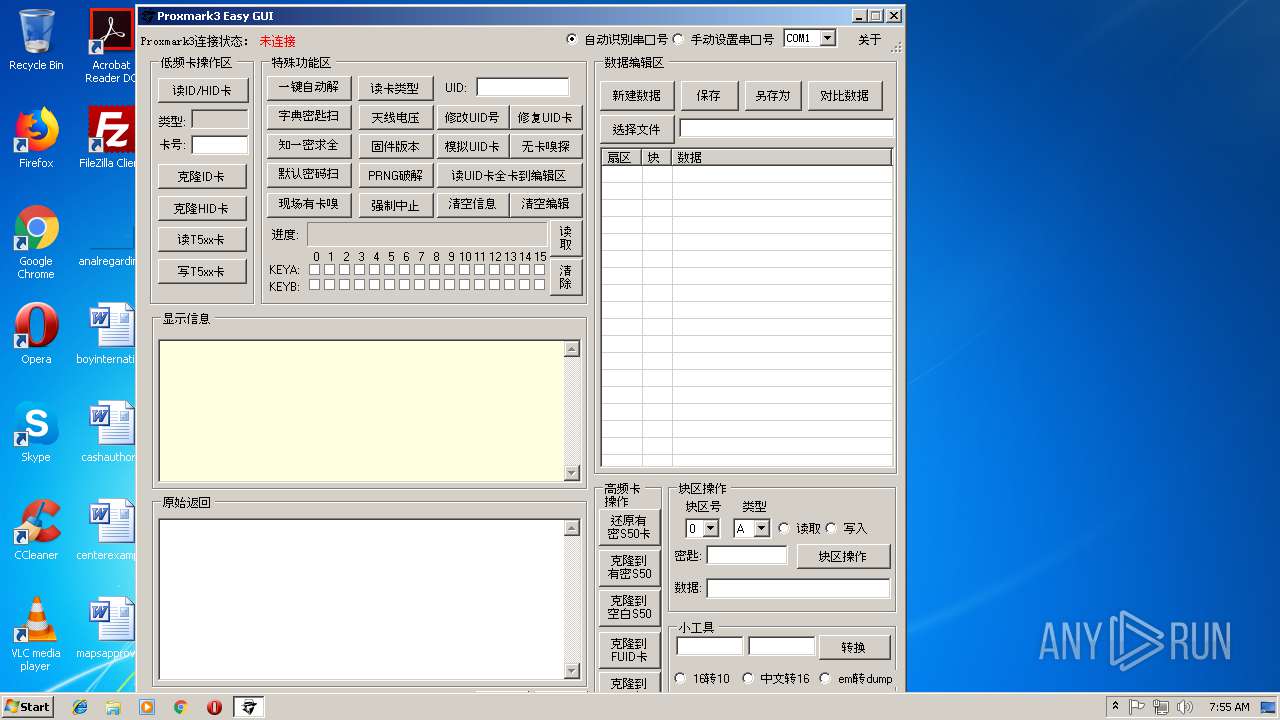
| FileDescription: | Proxmark3GUI |
| FileVersion: | 1.0.0.0 |
| InternalName: | Proxmark3GUI.exe |
| LegalCopyright: | Copyright © CHINA 2016 |
| OriginalFileName: | Proxmark3GUI.exe |
| ProductName: | Proxmark3GUI |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Jul-2016 16:36:43 |
| CompanyName: | CHINA |
| FileDescription: | Proxmark3GUI |
| FileVersion: | 1.0.0.0 |
| InternalName: | Proxmark3GUI.exe |
| LegalCopyright: | Copyright © CHINA 2016 |
| OriginalFilename: | Proxmark3GUI.exe |
| ProductName: | Proxmark3GUI |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 27-Jul-2016 16:36:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0051A000 | 0x0051A000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.97481 |
.data | 0x005E6000 | 0x00002000 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99331 |
.idata | 0x005D2000 | 0x00002000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_NOT_PAGED, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.212 |
.rsrc | 0x005D4000 | 0x00012000 | 0x00010E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.52304 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.33788 | 776 | UNKNOWN | UNKNOWN | RT_VERSION |
2 | 1.48638 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.16096 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MSVCRT.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
mscoree.dll |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2036 | "C:\Users\admin\AppData\Local\Temp\aa1abf98e7e54c5eaf2239a6da1c7bb1.exe" | C:\Users\admin\AppData\Local\Temp\aa1abf98e7e54c5eaf2239a6da1c7bb1.exe | — | explorer.exe | |||||||||||
User: admin Company: CHINA Integrity Level: MEDIUM Description: Proxmark3GUI Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3256 | "C:\Users\admin\AppData\Local\Temp\aa1abf98e7e54c5eaf2239a6da1c7bb1.exe" | C:\Users\admin\AppData\Local\Temp\aa1abf98e7e54c5eaf2239a6da1c7bb1.exe | aa1abf98e7e54c5eaf2239a6da1c7bb1.exe | ||||||||||||
User: admin Company: CHINA Integrity Level: HIGH Description: Proxmark3GUI Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
374
Read events
370
Write events
4
Delete events
0
Modification events
| (PID) Process: | (2036) aa1abf98e7e54c5eaf2239a6da1c7bb1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2036) aa1abf98e7e54c5eaf2239a6da1c7bb1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
8
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3256 | aa1abf98e7e54c5eaf2239a6da1c7bb1.exe | C:\Windows\System32\crypto1.dll | executable | |
MD5:— | SHA256:— | |||
| 3256 | aa1abf98e7e54c5eaf2239a6da1c7bb1.exe | C:\Users\admin\AppData\Local\Temp\proxmark3.exe | executable | |
MD5:— | SHA256:— | |||
| 3256 | aa1abf98e7e54c5eaf2239a6da1c7bb1.exe | C:\Users\admin\AppData\Local\Temp\libgcc_s_dw2-1.dll | executable | |
MD5:000ABDF5D3E31514801B44B954E1CF91 | SHA256:63843B68B9887080C6D6ABE74ABD4382312C2082D92B5F527BA13FD90EA5C956 | |||
| 3256 | aa1abf98e7e54c5eaf2239a6da1c7bb1.exe | C:\Users\admin\AppData\Local\Temp\pthreadGC2.dll | executable | |
MD5:AC05FBBA61F939CD90133032F2595C69 | SHA256:C271F42DA9F1483DE15869914D216A8EF44CA80C0D5907789B6E9873E3AA245F | |||
| 3256 | aa1abf98e7e54c5eaf2239a6da1c7bb1.exe | C:\Users\admin\AppData\Local\Temp\readline5.dll | executable | |
MD5:DF20019AAA0CE3525735EB206CD907BF | SHA256:B652B96D07641DBC986B5A5B7819411BA2B96E19FF8727D3F2C54076F5FF3CD0 | |||
| 3256 | aa1abf98e7e54c5eaf2239a6da1c7bb1.exe | C:\Users\admin\AppData\Local\Temp\QtCore4.dll | executable | |
MD5:— | SHA256:— | |||
| 3256 | aa1abf98e7e54c5eaf2239a6da1c7bb1.exe | C:\Users\admin\AppData\Local\Temp\libstdc++-6.dll | executable | |
MD5:13A00917B6BBE4CC11ACFCEEFBC3F4C5 | SHA256:A3514BD7B77166E7B9FEE429A59DE8BDA528BBF1DE2E7749E7CF682FE8CEC967 | |||
| 3256 | aa1abf98e7e54c5eaf2239a6da1c7bb1.exe | C:\Users\admin\AppData\Local\Temp\QtGui4.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report