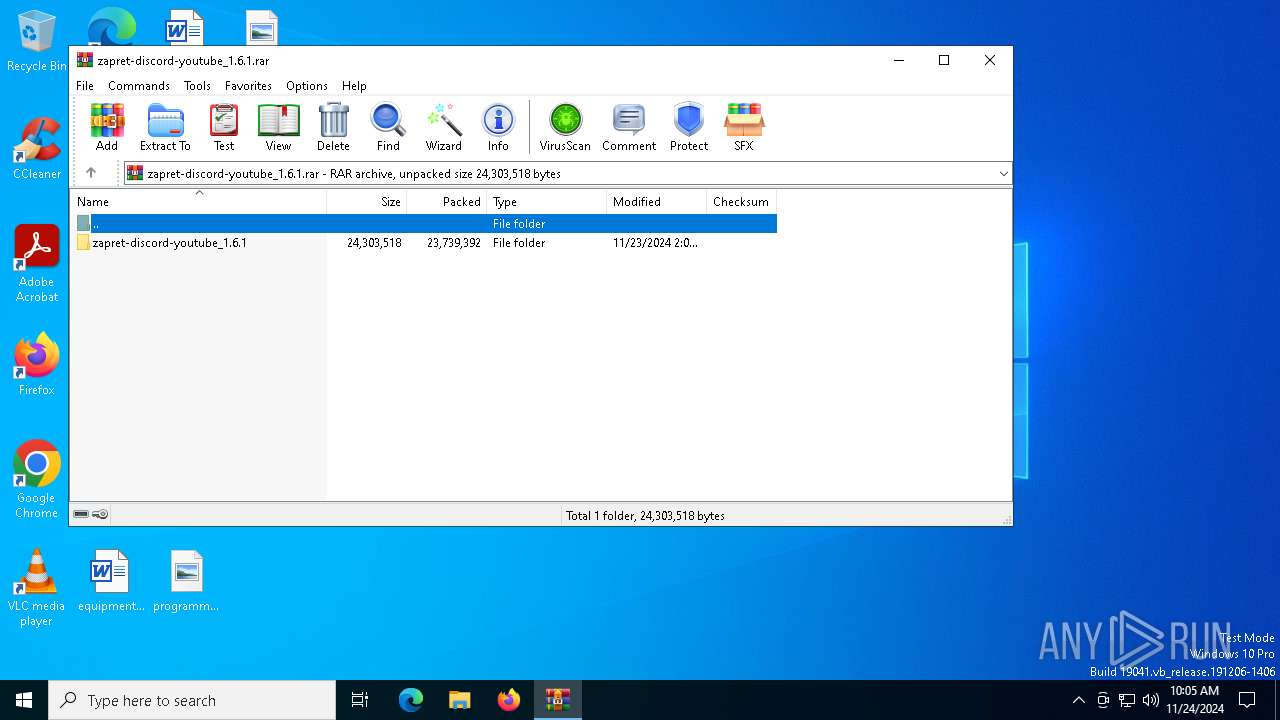
| File name: | zapret-discord-youtube_1.6.1.rar |
| Full analysis: | https://app.any.run/tasks/f2590cdd-e74e-403e-8985-d11ee9d74322 |
| Verdict: | Malicious activity |
| Analysis date: | November 24, 2024, 10:05:09 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 368D40F964ADE0AC2EBC7122D708D282 |
| SHA1: | 04EC87241898B8C4A03B306505AE001B1EB68A4E |
| SHA256: | 2548E395E83105CBAF24BE34AC0FD146A8F7C11D56AB546777336077434F6518 |
| SSDEEP: | 196608:6x6lmul2mSuFTmKbOEGqe00xqpiS47wOmEQP:6oPl/hZsqeqp0wOpA |
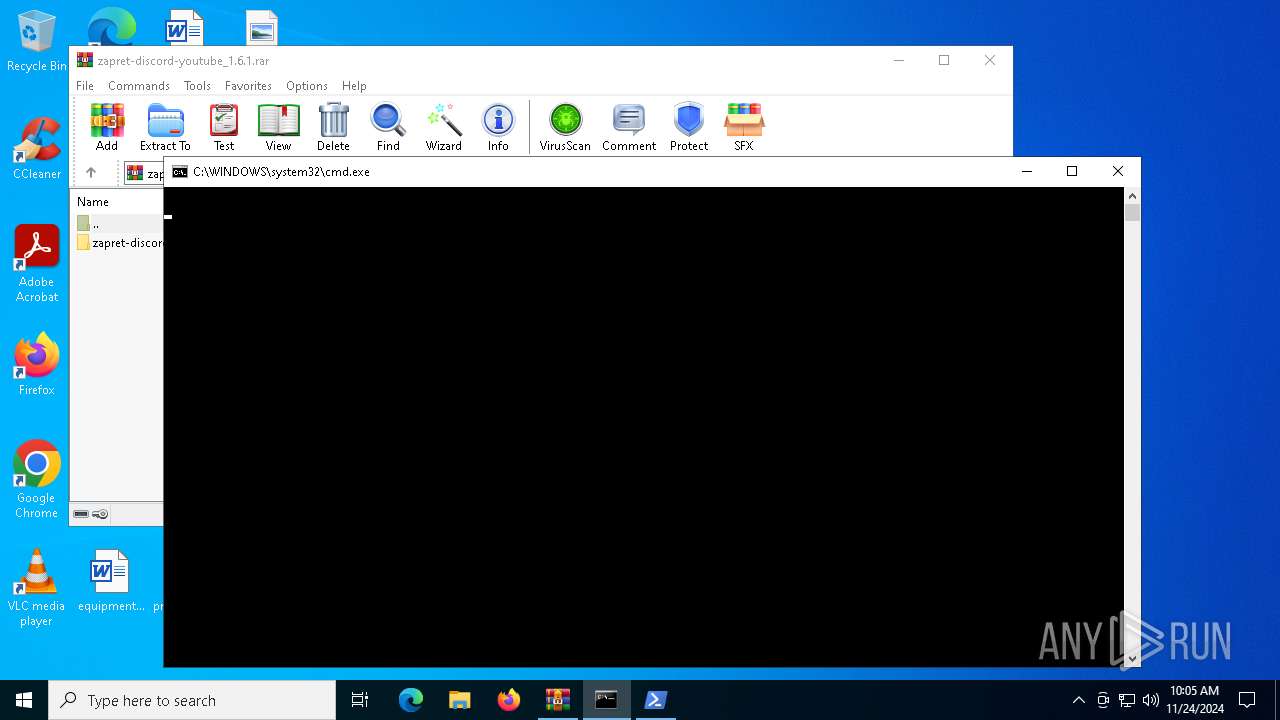
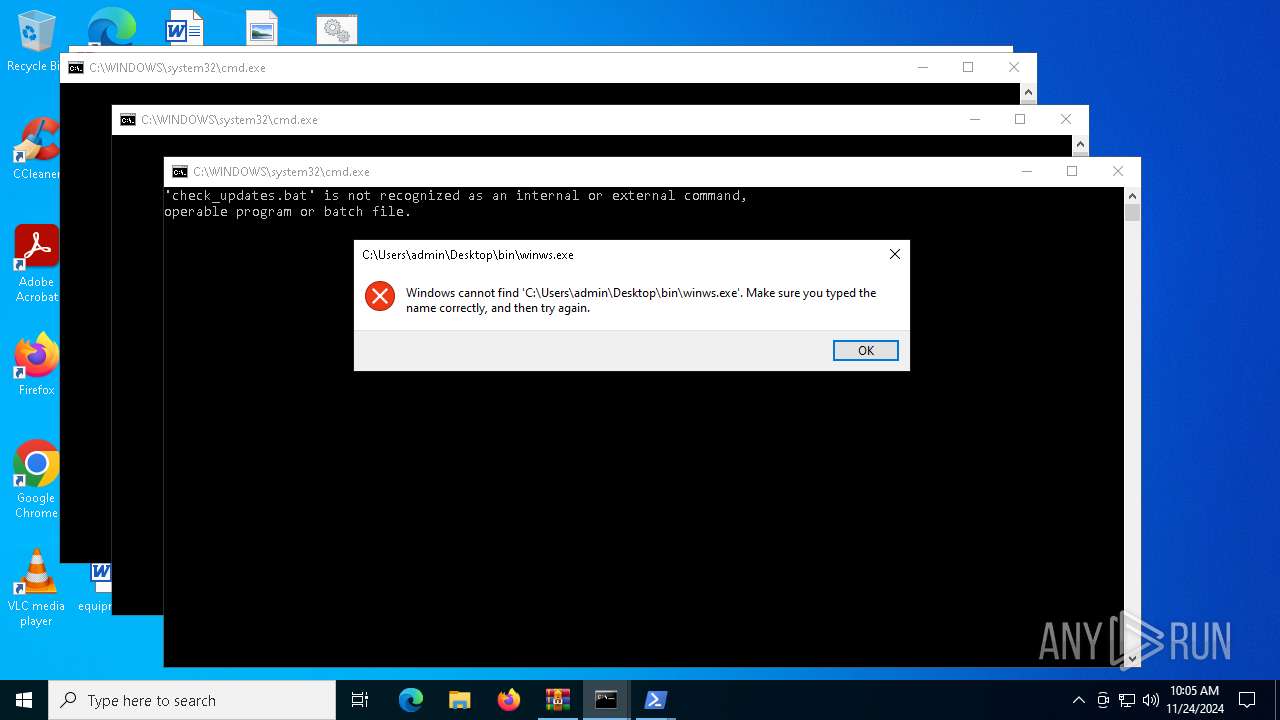
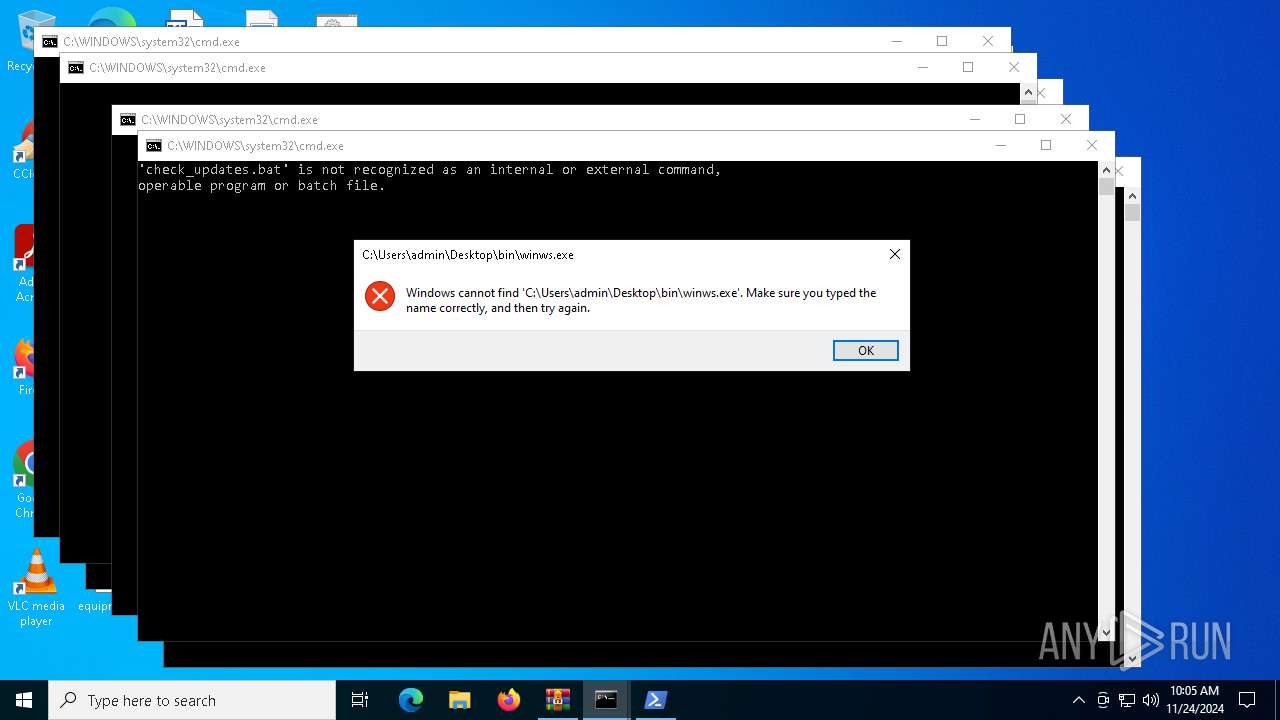
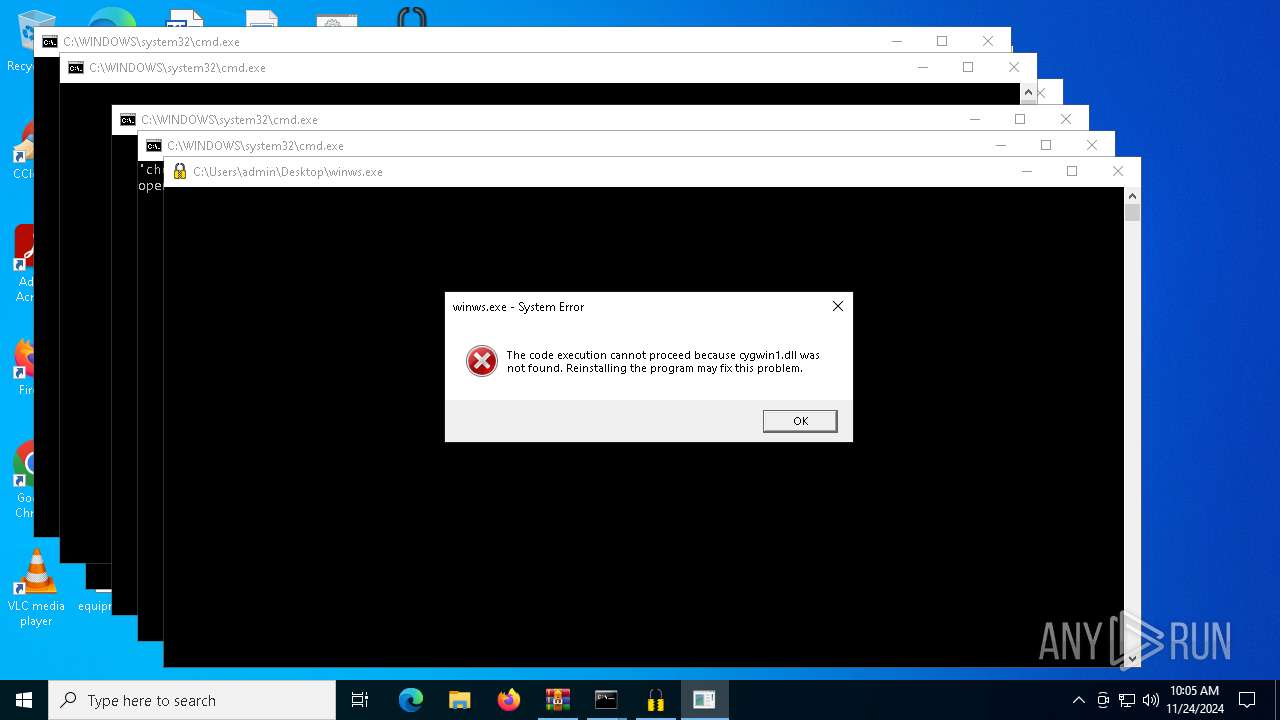
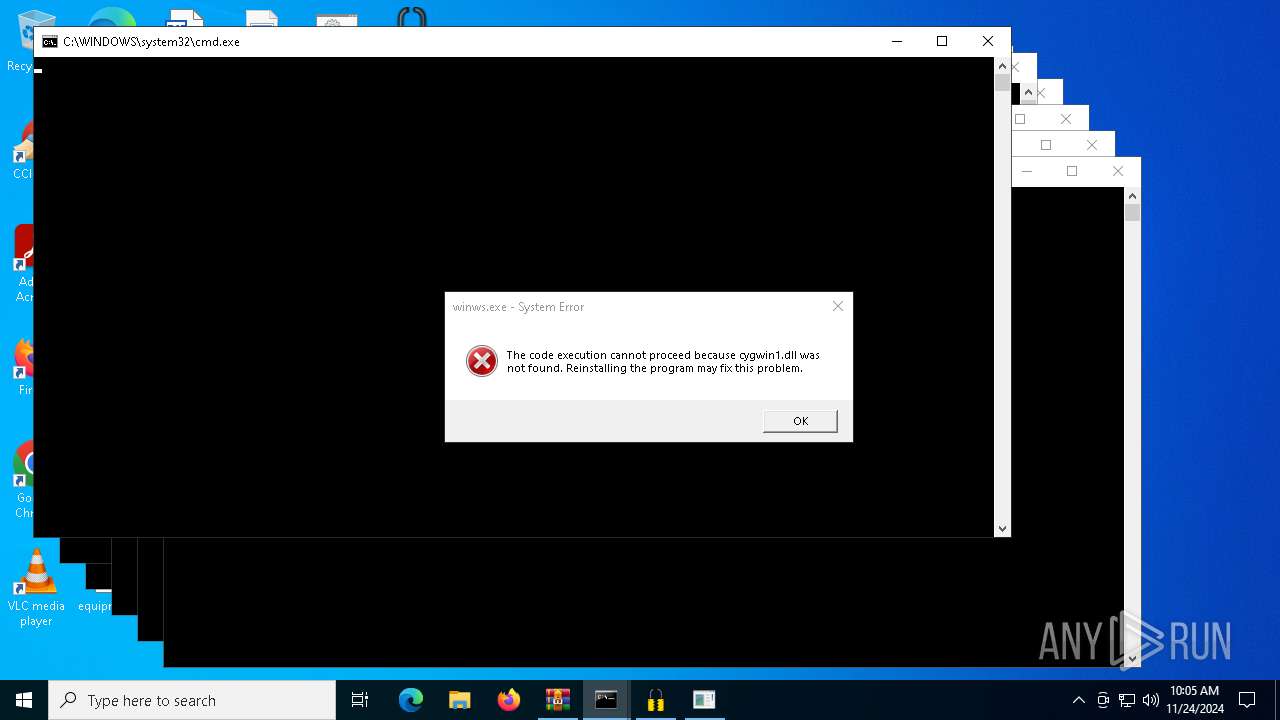
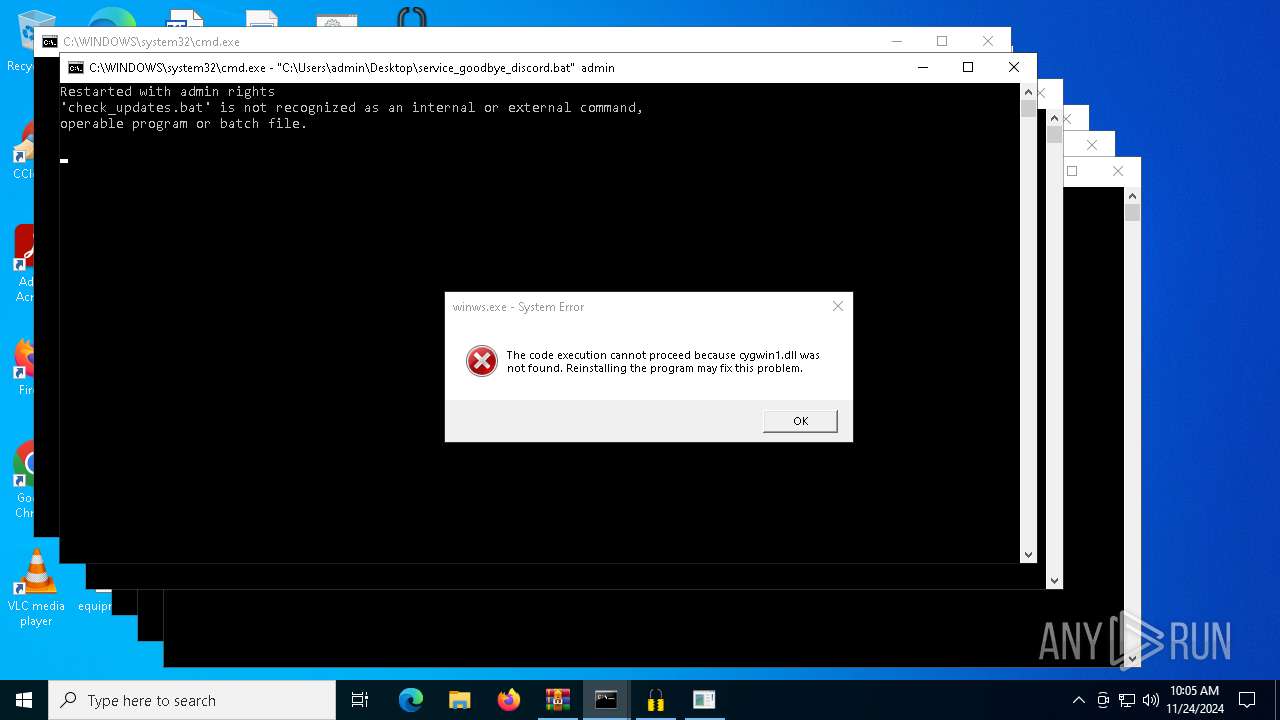
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 5788)
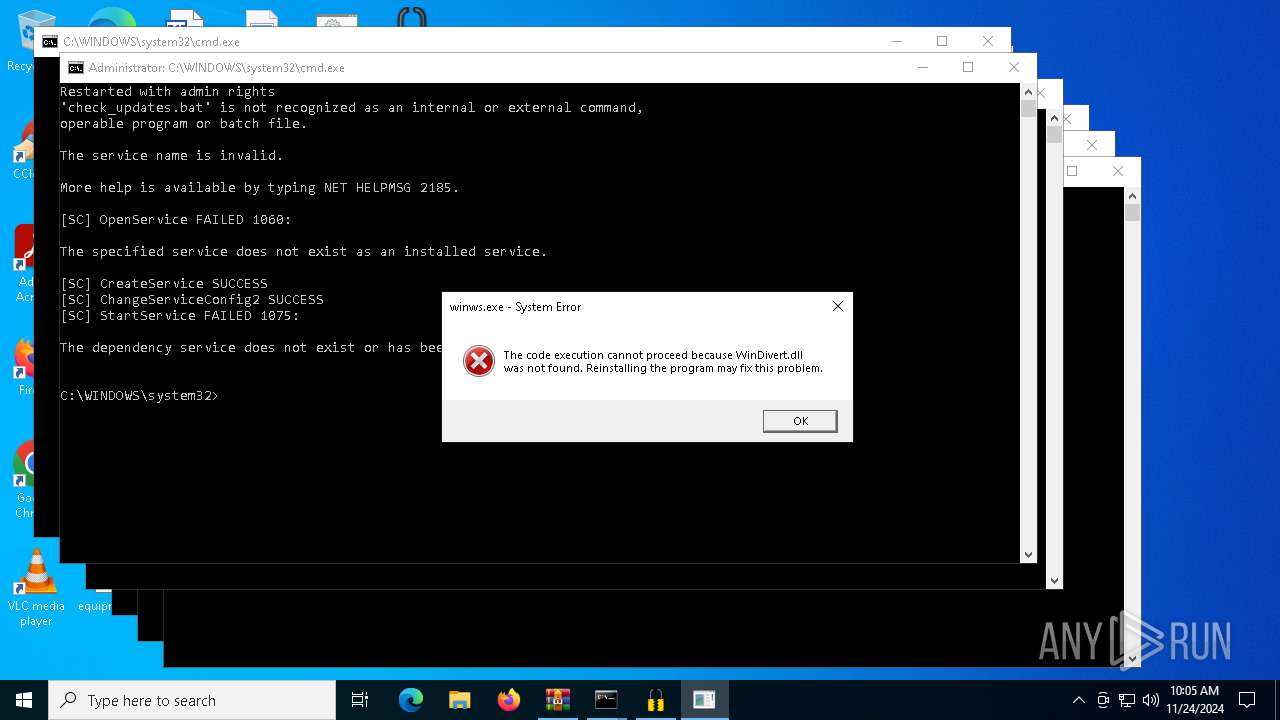
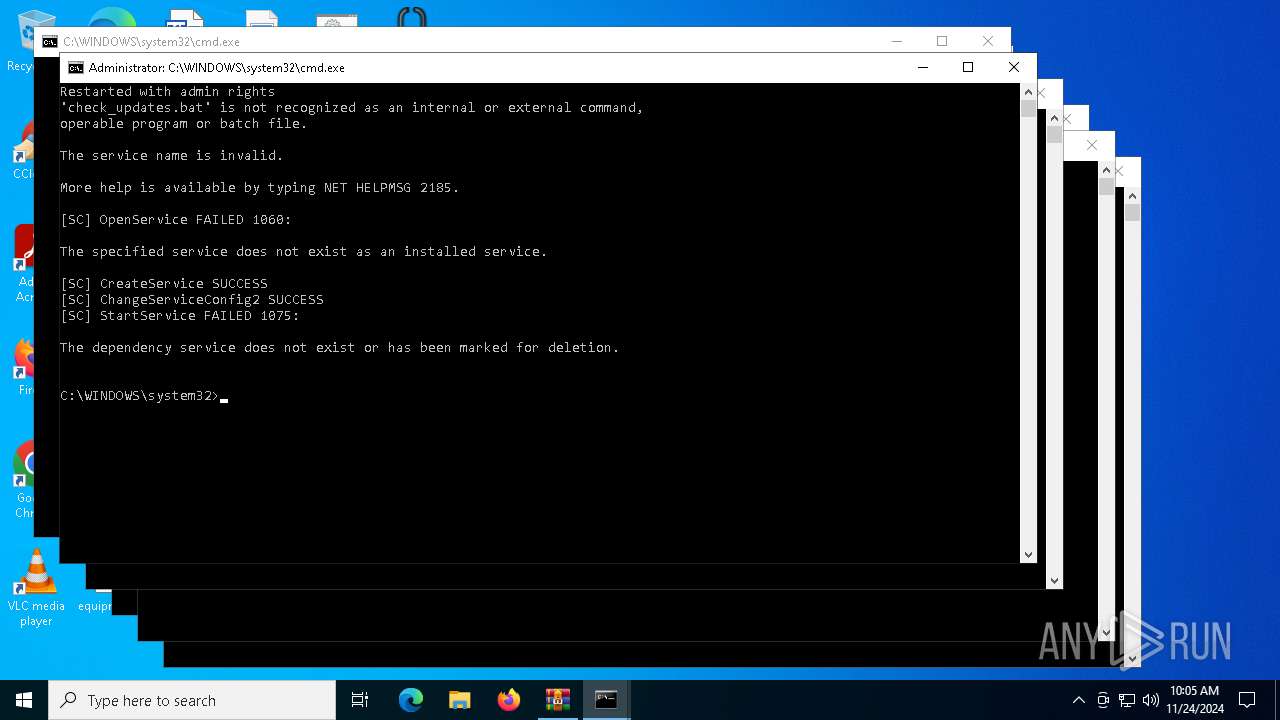
Starts NET.EXE for service management
- cmd.exe (PID: 6568)
- net.exe (PID: 6292)
SUSPICIOUS
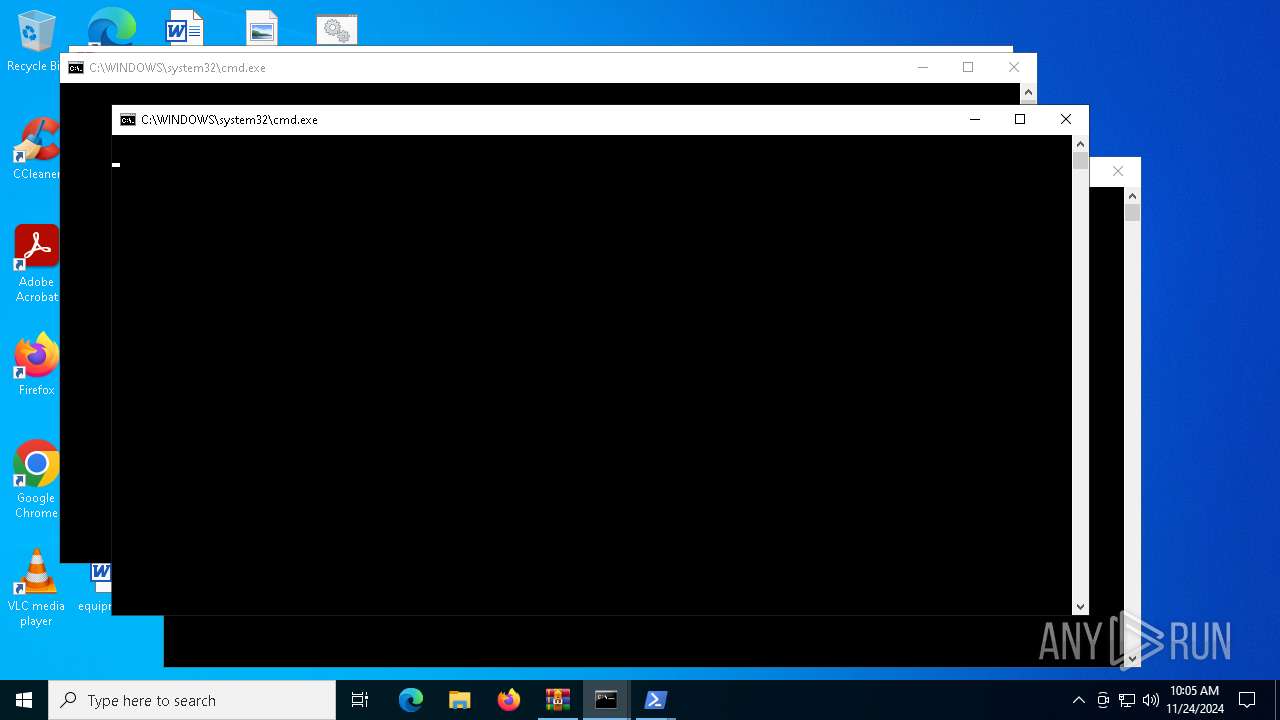
Starts process via Powershell
- powershell.exe (PID: 6168)
- powershell.exe (PID: 6784)
- powershell.exe (PID: 6540)
- powershell.exe (PID: 7140)
- powershell.exe (PID: 5268)
- powershell.exe (PID: 6884)
Starts application with an unusual extension
- cmd.exe (PID: 5028)
- cmd.exe (PID: 6456)
- cmd.exe (PID: 6708)
- cmd.exe (PID: 6932)
- cmd.exe (PID: 7064)
- cmd.exe (PID: 3876)
- cmd.exe (PID: 2008)
- cmd.exe (PID: 6604)
- cmd.exe (PID: 6568)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5028)
- cmd.exe (PID: 6456)
- cmd.exe (PID: 6708)
- cmd.exe (PID: 7064)
- cmd.exe (PID: 3876)
- cmd.exe (PID: 6604)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5028)
- cmd.exe (PID: 6456)
- cmd.exe (PID: 6708)
- cmd.exe (PID: 3876)
- cmd.exe (PID: 7064)
Executing commands from a ".bat" file
- powershell.exe (PID: 6884)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 6884)
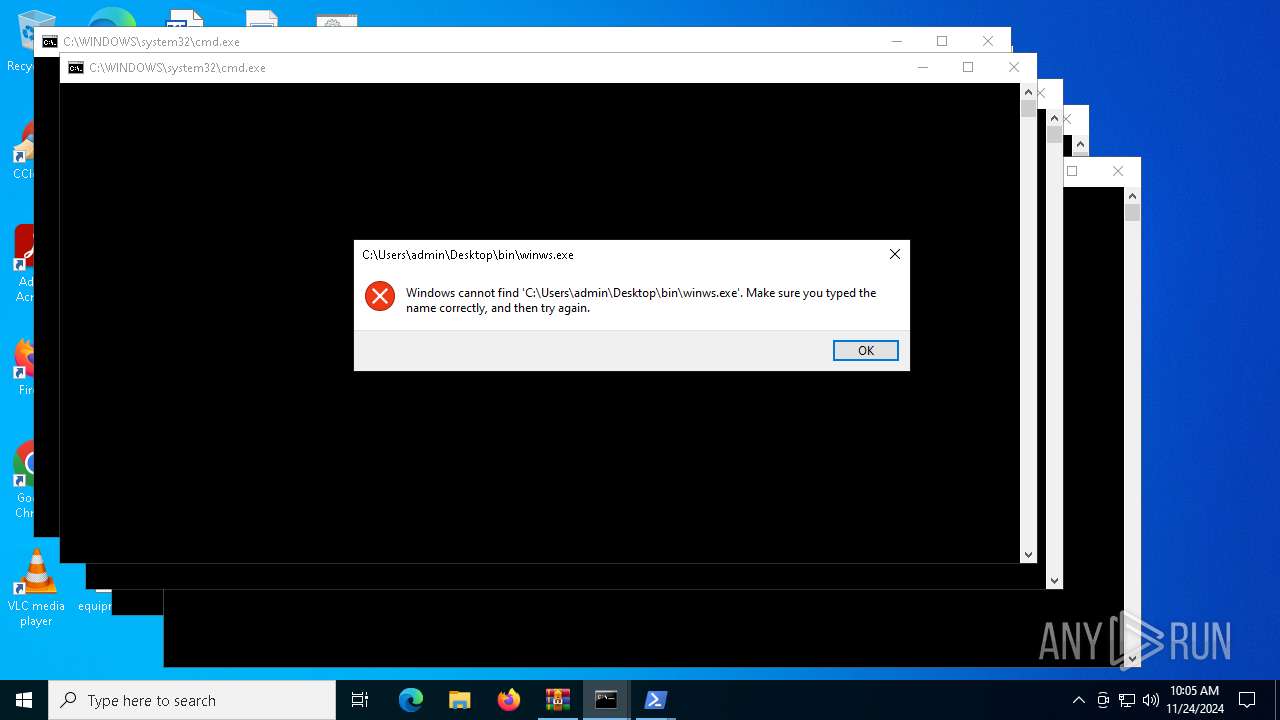
Starts SC.EXE for service management
- cmd.exe (PID: 6568)
INFO
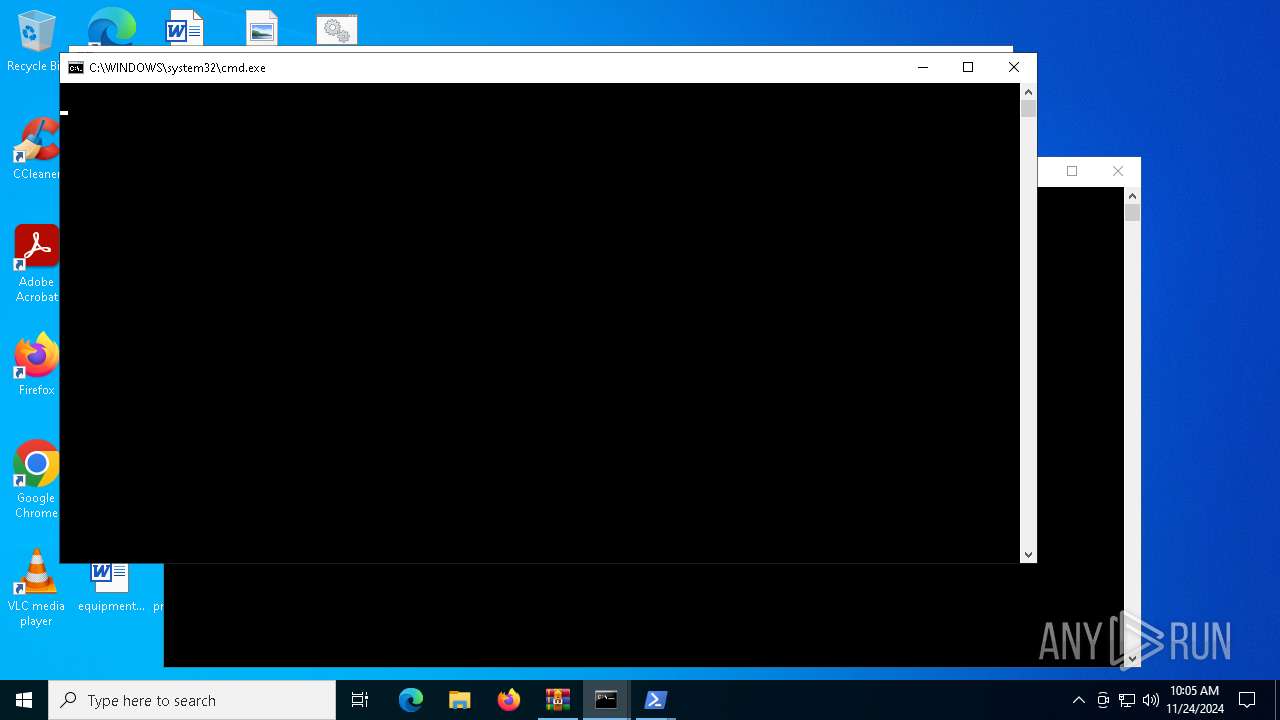
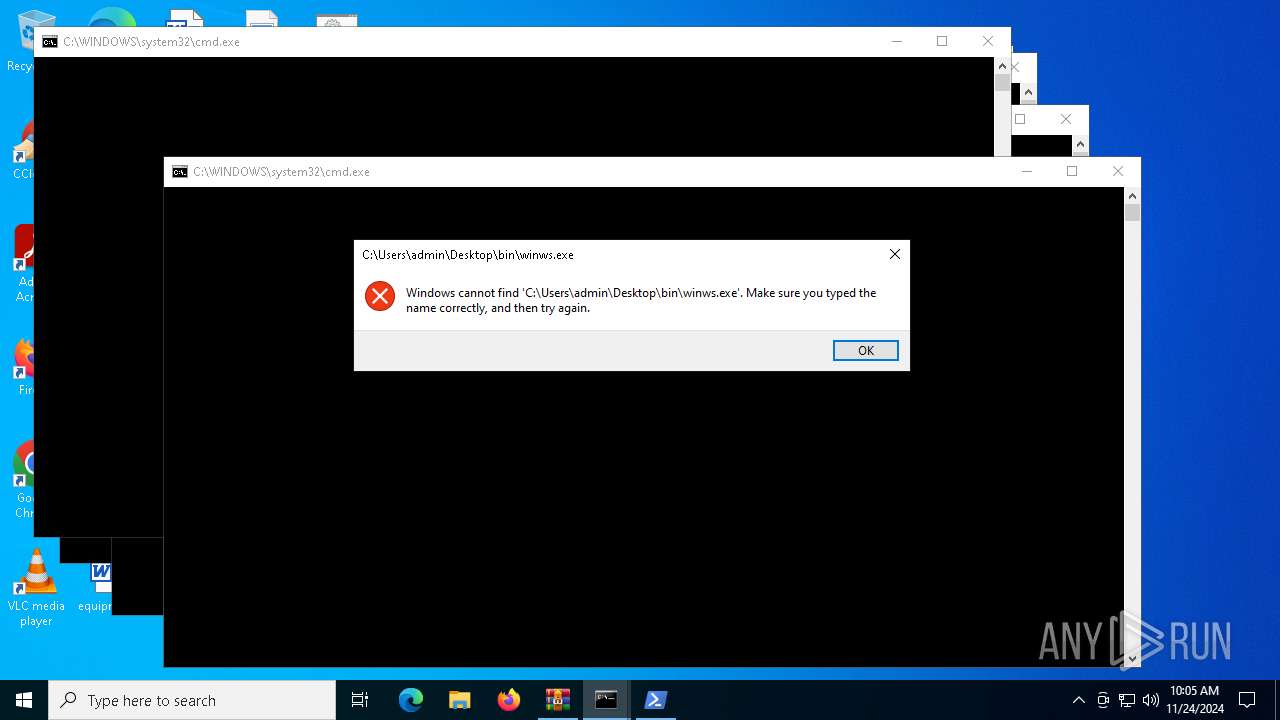
Manual execution by a user
- cmd.exe (PID: 5028)
- cmd.exe (PID: 6456)
- cmd.exe (PID: 6708)
- cmd.exe (PID: 6932)
- cmd.exe (PID: 7064)
- cmd.exe (PID: 2008)
- winws.exe (PID: 6280)
- cmd.exe (PID: 3876)
- cmd.exe (PID: 6604)
- winws.exe (PID: 6624)
Changes the display of characters in the console
- cmd.exe (PID: 5028)
- cmd.exe (PID: 6456)
- cmd.exe (PID: 6708)
- cmd.exe (PID: 6932)
- cmd.exe (PID: 3876)
- cmd.exe (PID: 7064)
- cmd.exe (PID: 2008)
- cmd.exe (PID: 6604)
- cmd.exe (PID: 6568)
Checks supported languages
- chcp.com (PID: 6148)
- chcp.com (PID: 6516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 981664 |
| UncompressedSize: | 1022005 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | zapret-discord-youtube_1.6.1/bin/cygwin1.dll |
Total processes
179
Monitored processes
53
Malicious processes
3
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 556 | C:\WINDOWS\system32\net1 stop zapret | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1016 | timeout /t 5 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1296 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2008 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\general (ALT5).bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2076 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3144 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3608 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3876 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\discord.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3988 | sc delete zapret | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
28 300
Read events
28 292
Write events
8
Delete events
0
Modification events
| (PID) Process: | (5788) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5788) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5788) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5788) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\zapret-discord-youtube_1.6.1.rar | |||
| (PID) Process: | (5788) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5788) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5788) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5788) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
0
Suspicious files
16
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6540 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF13690e.TMP | binary | |
MD5:B457BD2D89ED0FE6ACFBF95ACF80E6D3 | SHA256:1EB3B0F83643A8B2BD5C1C4ABB943493DCB17177072C1580C9958A4284E9EDDD | |||
| 6540 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PB9K5L2B8KRVUDSN1JZK.temp | binary | |
MD5:035A9C09062262253D88507EABF2BA40 | SHA256:BC1F8A35D505FC6AF03A47479F6B7514B40BB7B8226179C30C10641F03DE1859 | |||
| 7140 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\RCRV6HXCJH3Z8JKG8TET.temp | binary | |
MD5:26ADFD41C9D3D7F6FCC4C69ECB224E8A | SHA256:93879D8A6913EB6796C089A06B5F14BBF7D5A7F4D904EF34FED65DD65A48D94D | |||
| 6168 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:179D2B4AC5777F664E18348AE92EEAAA | SHA256:071C548C86C162C99B3357FA64FBD20C40C0237F2D82A6FF3017533C70123548 | |||
| 6784 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\FBYBZ5JGL7Z7WFPBN191.temp | binary | |
MD5:67D61748A365925AA7E92D189D47F3A2 | SHA256:3F951ED12BF79ABECF01F6A633ED94CE13FEEC0188FB2CA8F3AFC7EBD1A9E460 | |||
| 6540 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_evupaujq.kum.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6540 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qzzkzijx.4pr.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6784 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_etivnvay.pqq.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6784 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:67D61748A365925AA7E92D189D47F3A2 | SHA256:3F951ED12BF79ABECF01F6A633ED94CE13FEEC0188FB2CA8F3AFC7EBD1A9E460 | |||
| 6168 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:B457BD2D89ED0FE6ACFBF95ACF80E6D3 | SHA256:1EB3B0F83643A8B2BD5C1C4ABB943493DCB17177072C1580C9958A4284E9EDDD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
32
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
716 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
716 | svchost.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7028 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3080 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7028 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
904 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.110.171:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
716 | svchost.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
716 | svchost.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |