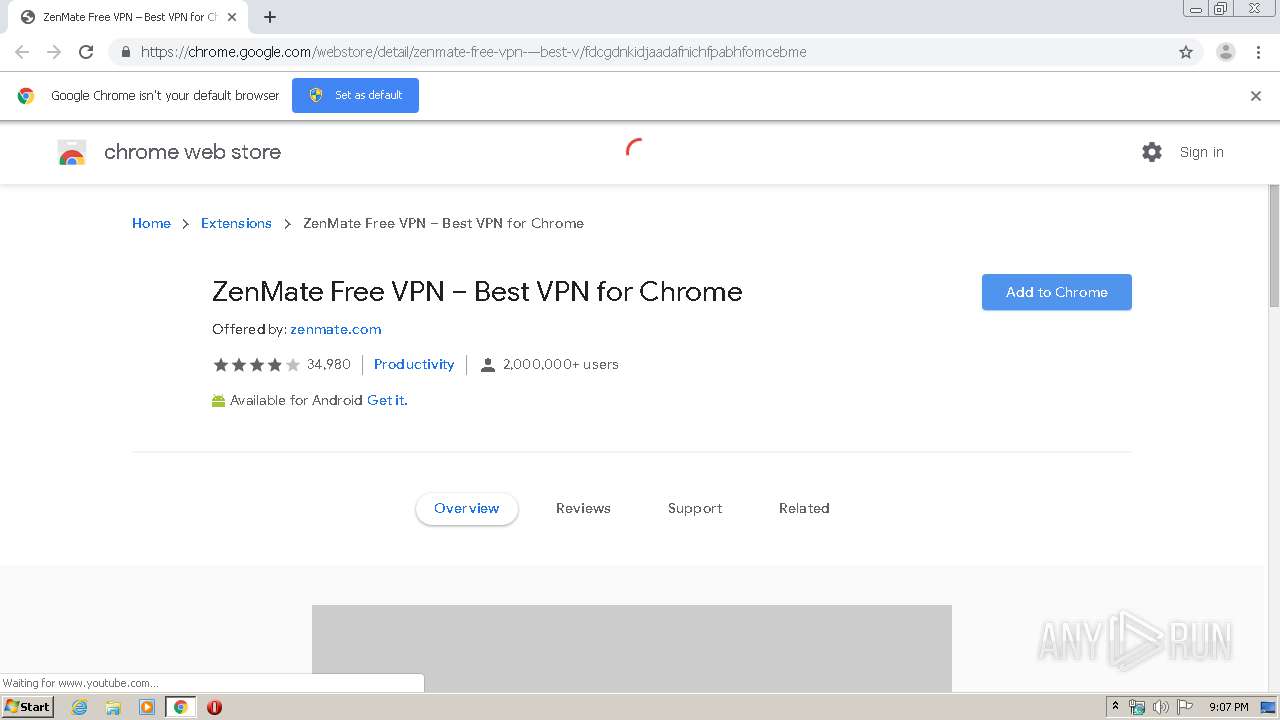
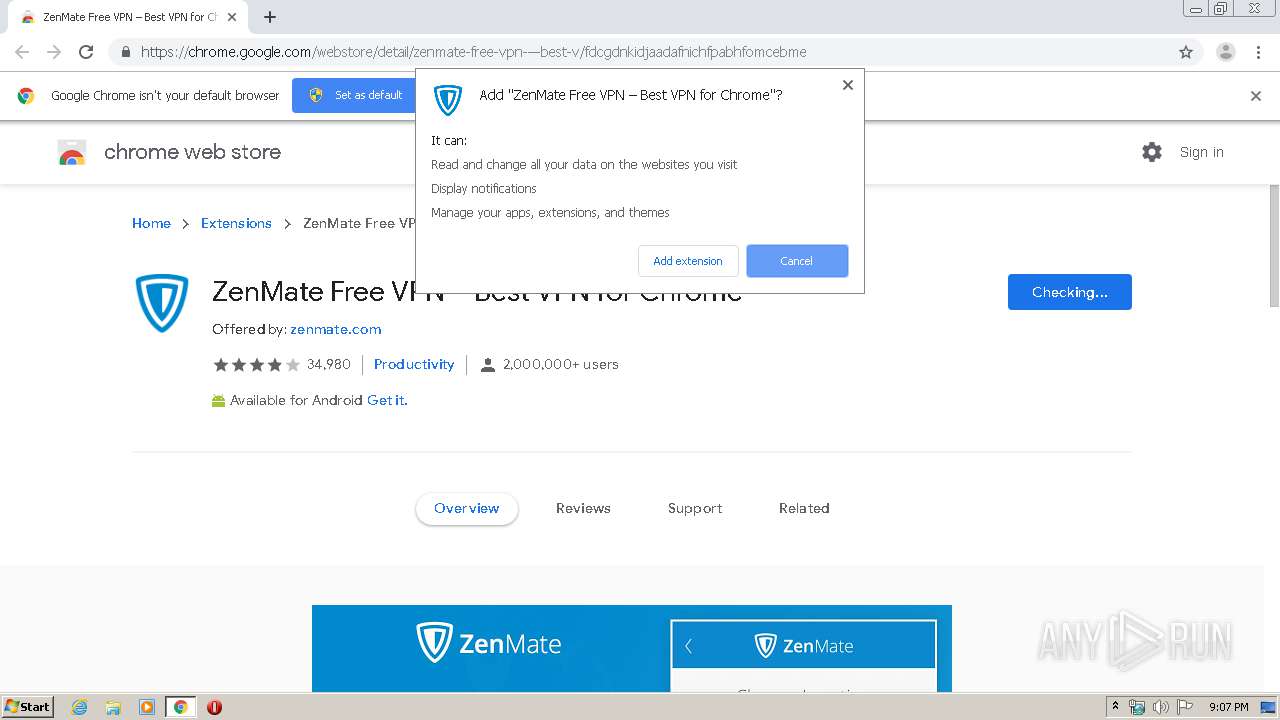
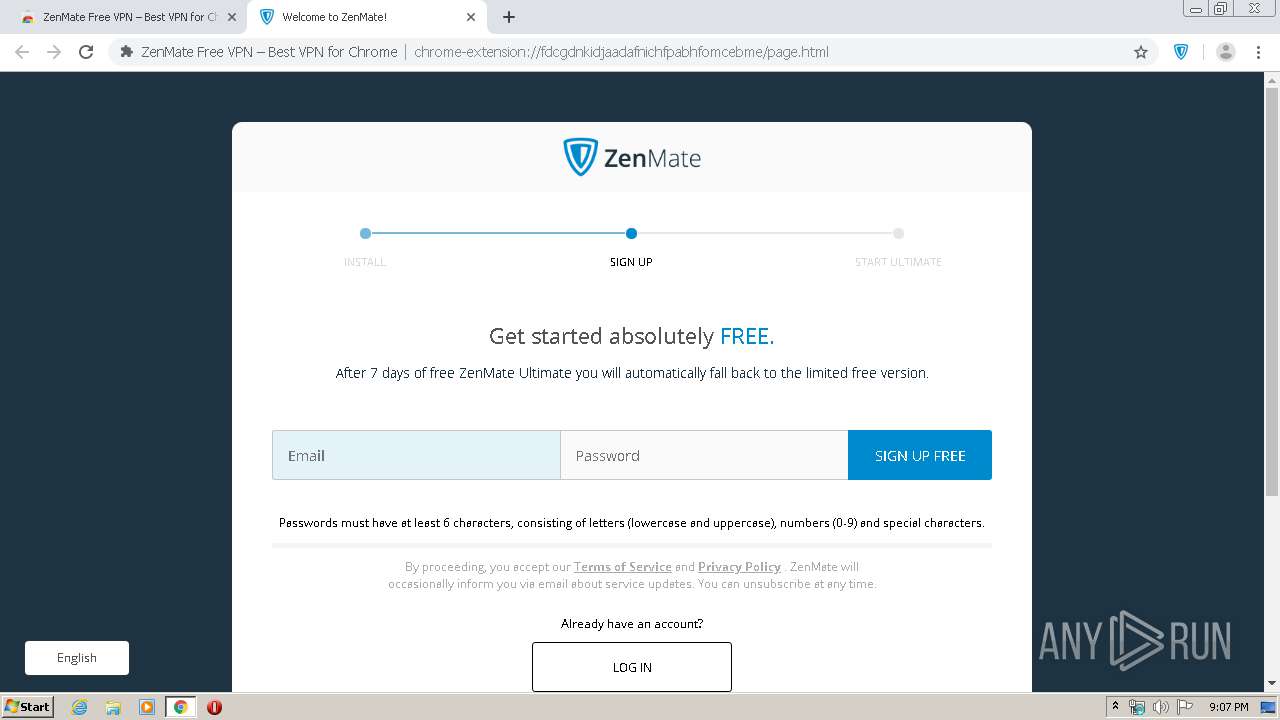
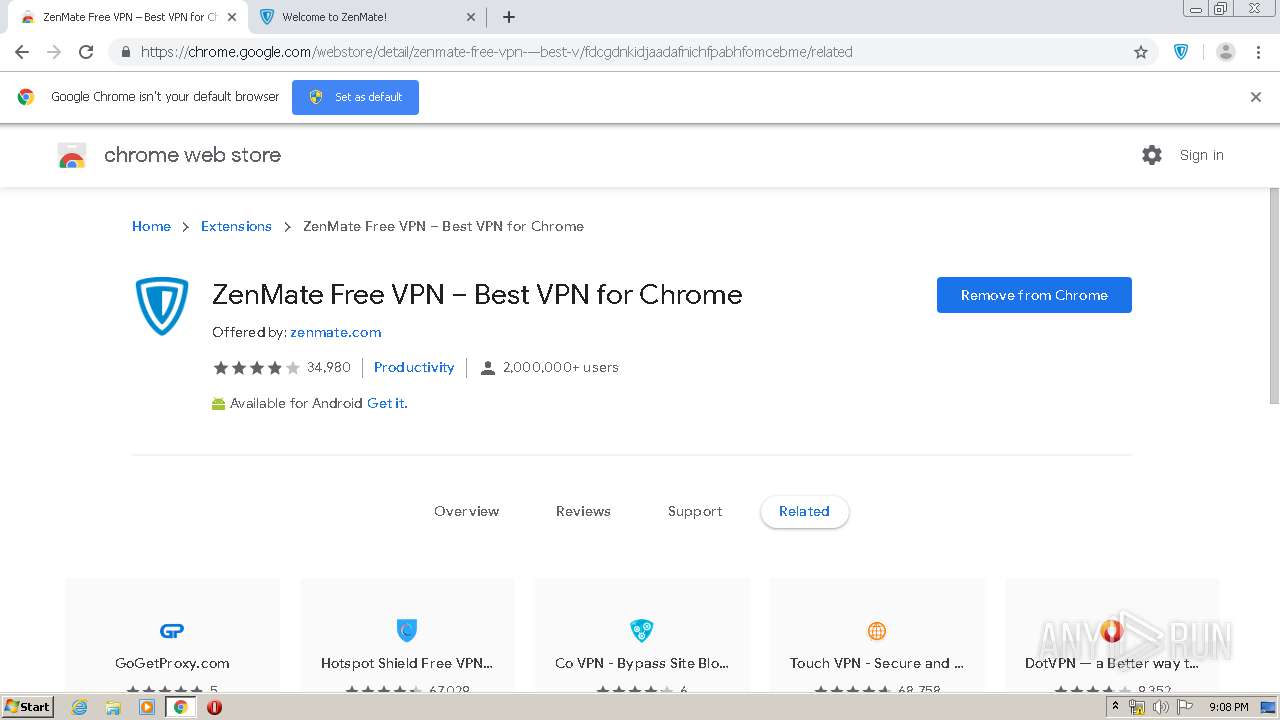
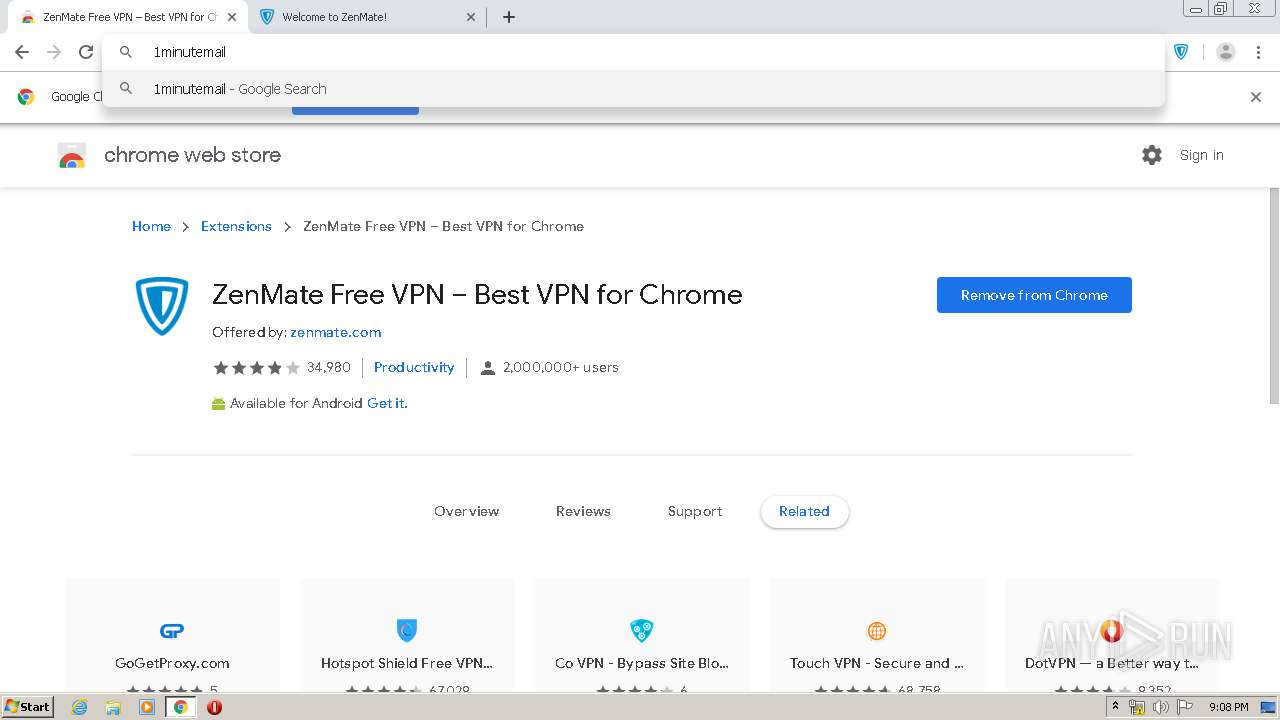
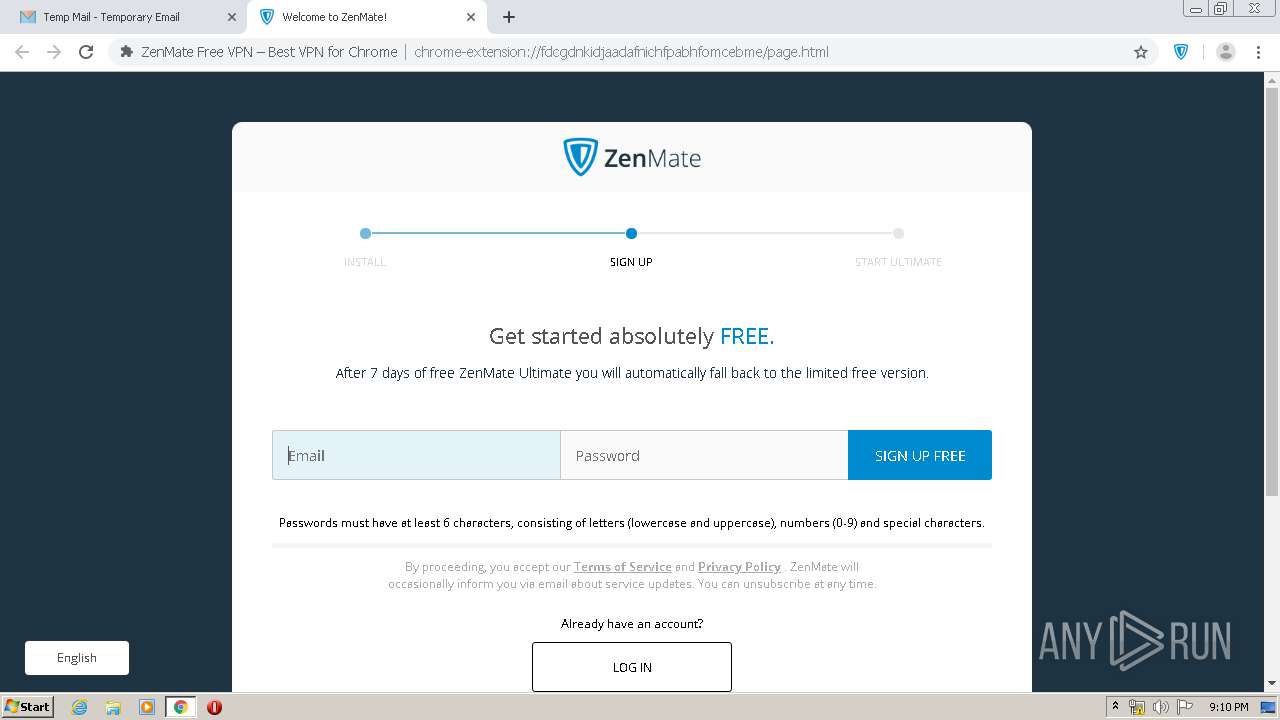
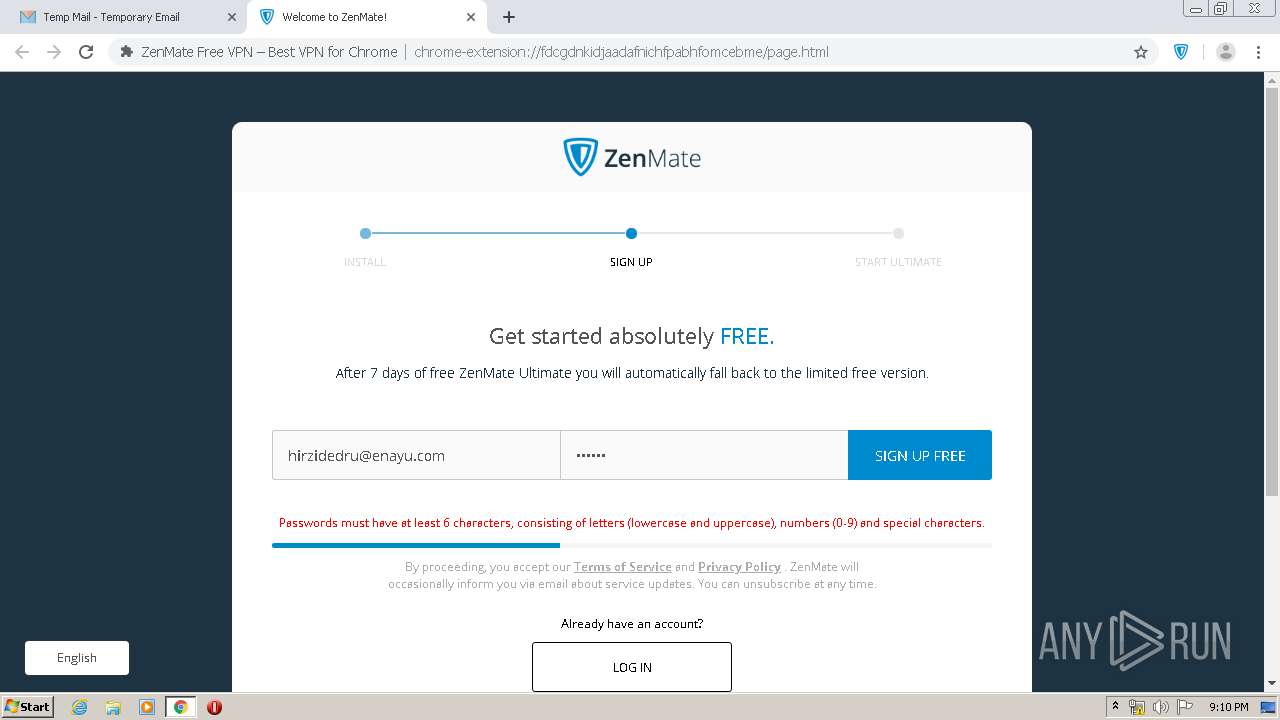
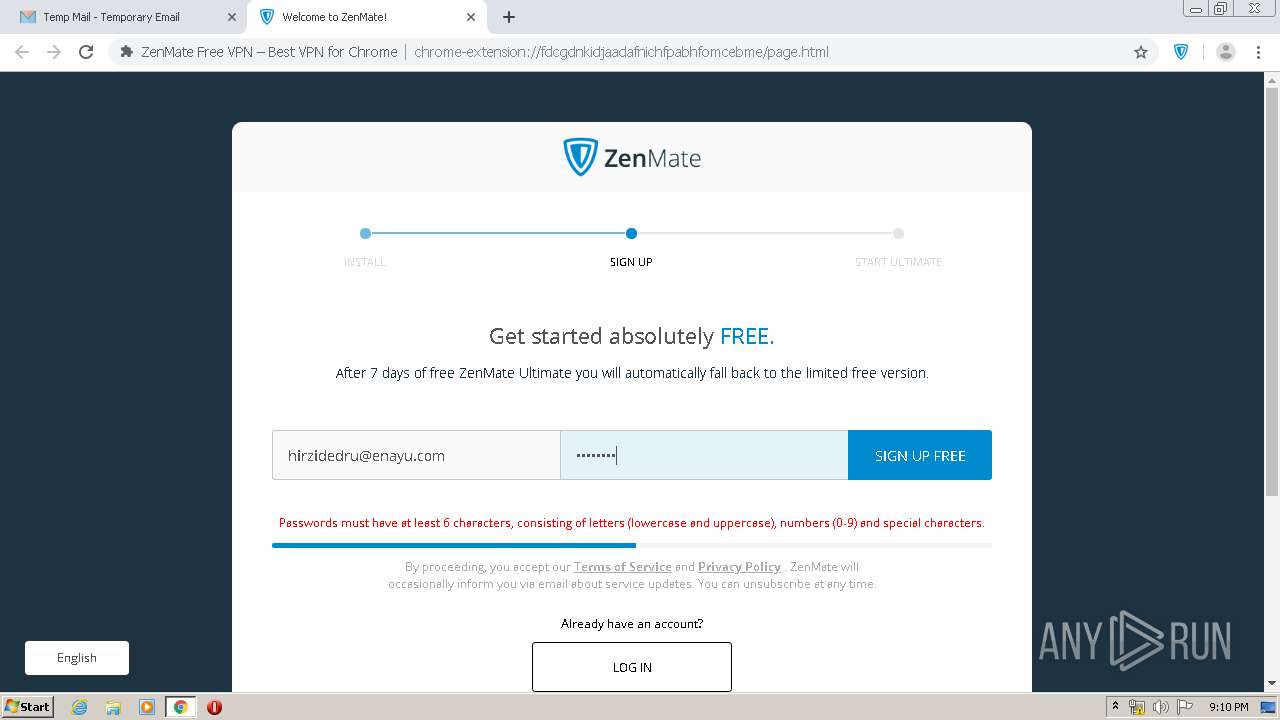
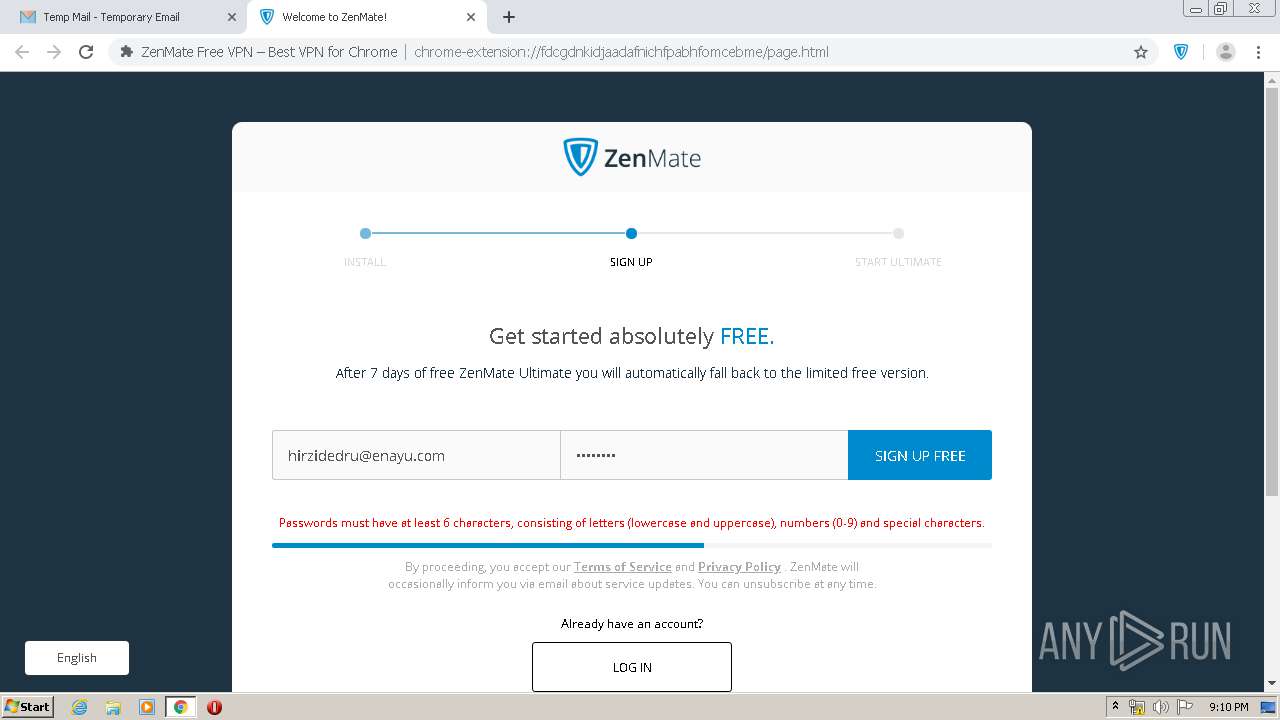
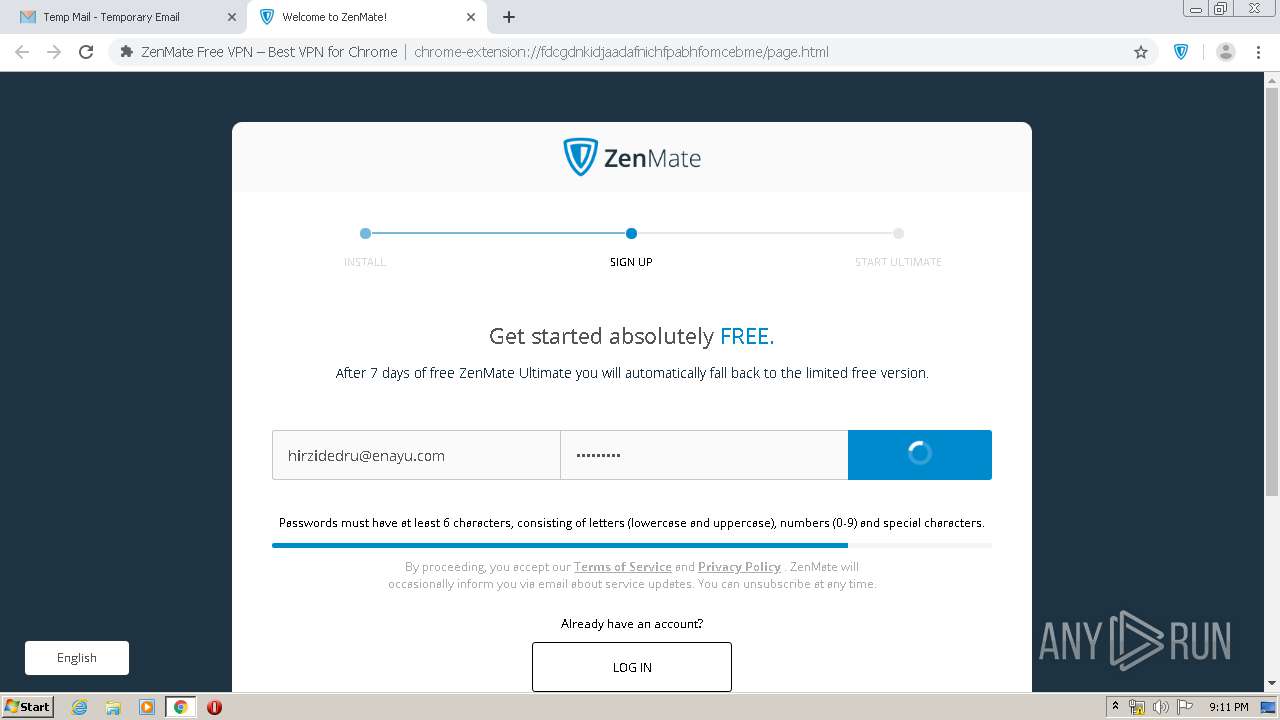
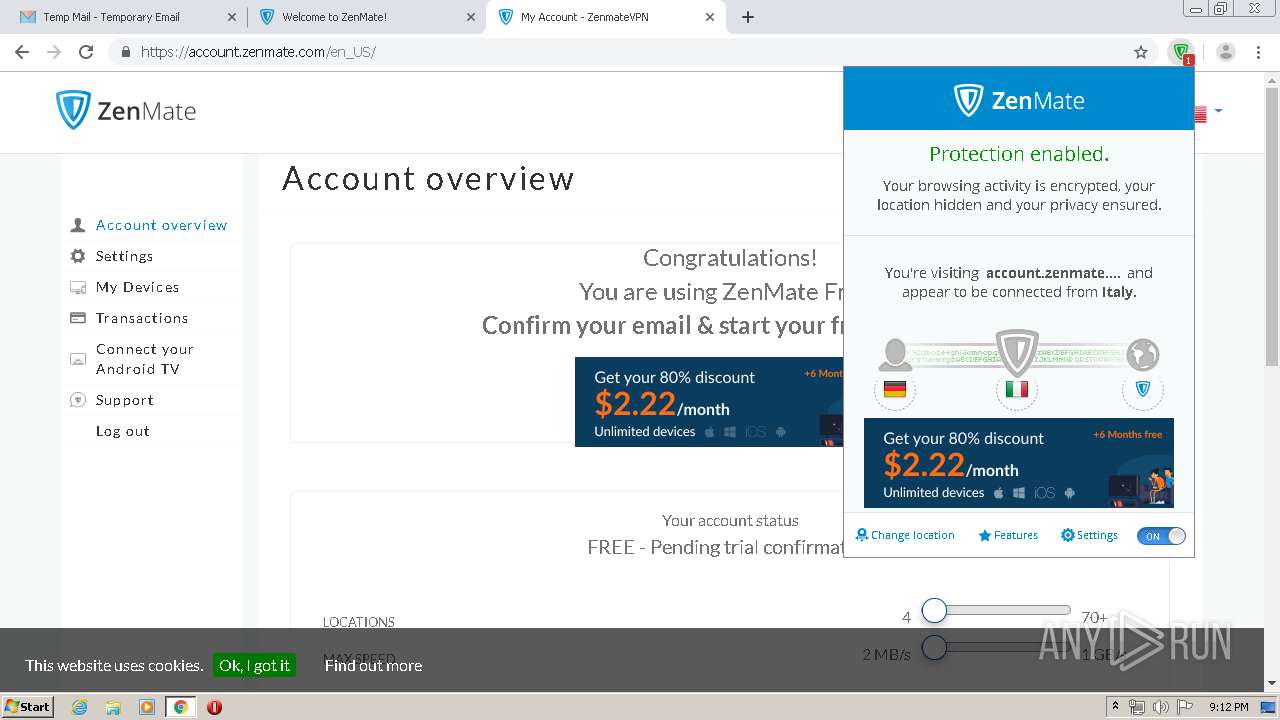
| URL: | https://chrome.google.com/webstore/detail/zenmate-free-vpn-%E2%80%93-best-v/fdcgdnkidjaadafnichfpabhfomcebme |
| Full analysis: | https://app.any.run/tasks/055f0316-1eae-4577-b44d-62ed2de926e4 |
| Verdict: | Malicious activity |
| Analysis date: | April 09, 2020, 20:06:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 84713D2DA4175E2F0C3B17101EEAECE0 |
| SHA1: | CFE2189A3EB13A60F2279AC0D9C766ADA483B0FF |
| SHA256: | 2541BC144CCF84C5FD8F238DF3228D239F8A2ADD01AEAF1F4A62B2AFA36DDD27 |
| SSDEEP: | 3:N8Qa9t3u0A2RKelJl5ch9StIdITsrL9rqLIx0An:2Qa9c01RnlKMIKcy00A |
MALICIOUS
Changes the autorun value in the registry
- chrome.exe (PID: 2904)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2904)
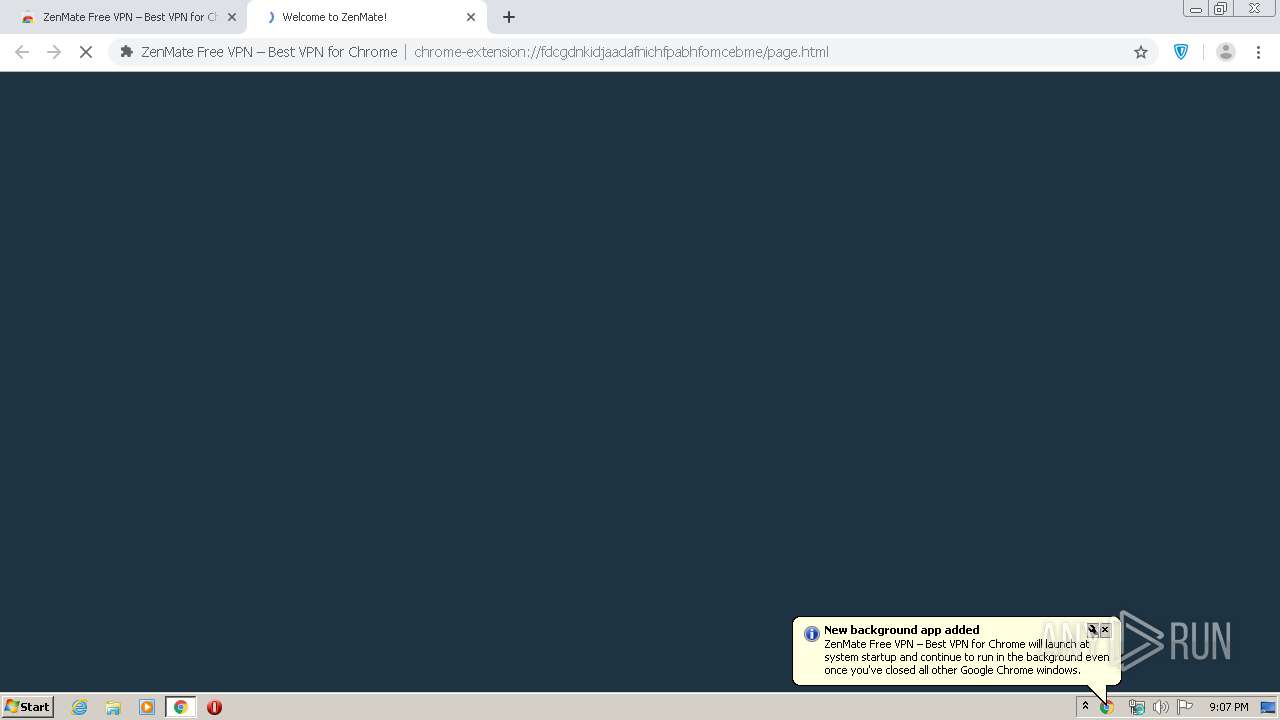
INFO
Reads the hosts file
- chrome.exe (PID: 3960)
- chrome.exe (PID: 2904)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2904)
Connects to unusual port
- chrome.exe (PID: 3960)
Application launched itself
- chrome.exe (PID: 2904)
Reads Internet Cache Settings
- chrome.exe (PID: 2904)
Creates files in the user directory
- chrome.exe (PID: 2904)
Reads settings of System Certificates
- chrome.exe (PID: 3960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
87
Monitored processes
50
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,434577453908771259,4024415327924761098,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1450249473308116996 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2520 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,434577453908771259,4024415327924761098,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8764486374044608596 --mojo-platform-channel-handle=4528 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,434577453908771259,4024415327924761098,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8781224491628120989 --renderer-client-id=37 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3456 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,434577453908771259,4024415327924761098,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14734965112537003345 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4744 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,434577453908771259,4024415327924761098,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13760852120840123391 --mojo-platform-channel-handle=4772 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,434577453908771259,4024415327924761098,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9326456321232658673 --renderer-client-id=41 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,434577453908771259,4024415327924761098,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=535104921025251647 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3884 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,434577453908771259,4024415327924761098,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7197660229284643555 --mojo-platform-channel-handle=4000 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,434577453908771259,4024415327924761098,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=524988369057063231 --mojo-platform-channel-handle=2988 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,434577453908771259,4024415327924761098,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11854425848084835278 --renderer-client-id=48 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4808 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
869
Read events
728
Write events
134
Delete events
7
Modification events
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2904-13230936440361125 |
Value: 259 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
150
Text files
753
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E8F8079-B58.pma | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ae55cf31-0c13-4c2e-af69-a97ed3df1d69.tmp | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RFa6f44b.TMP | text | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa6f296.TMP | text | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa6f574.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
127
DNS requests
63
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
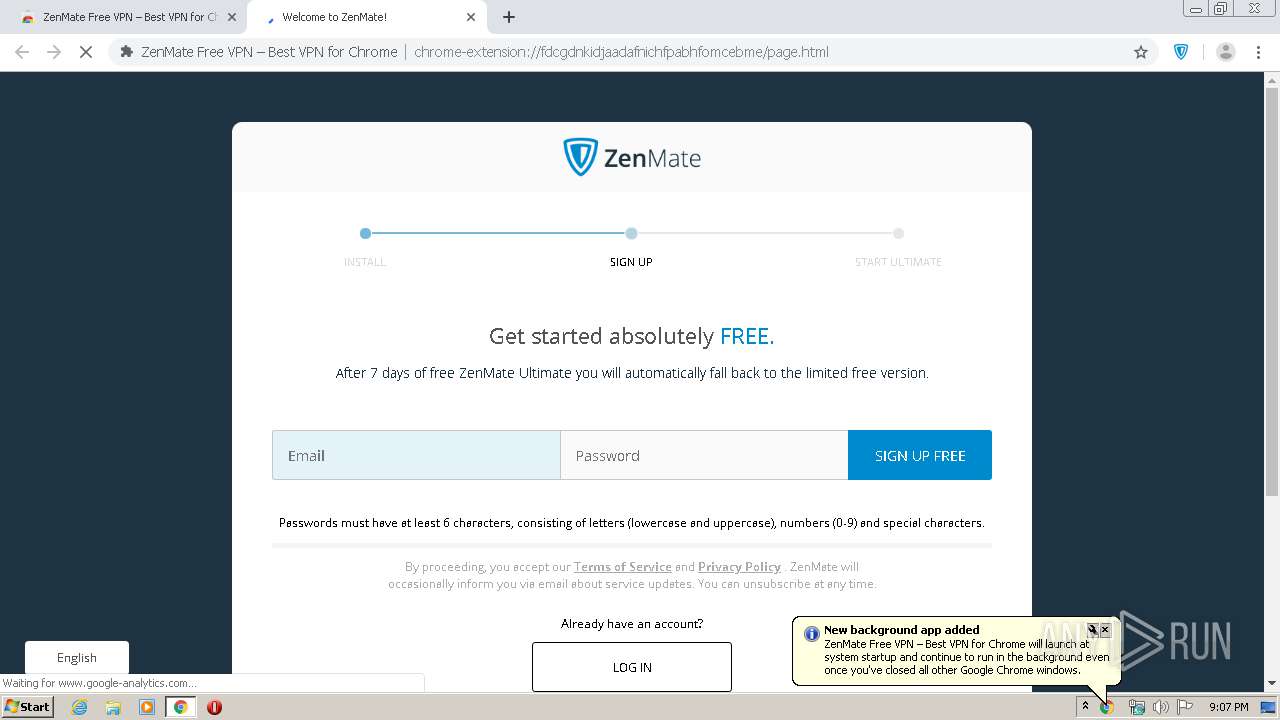
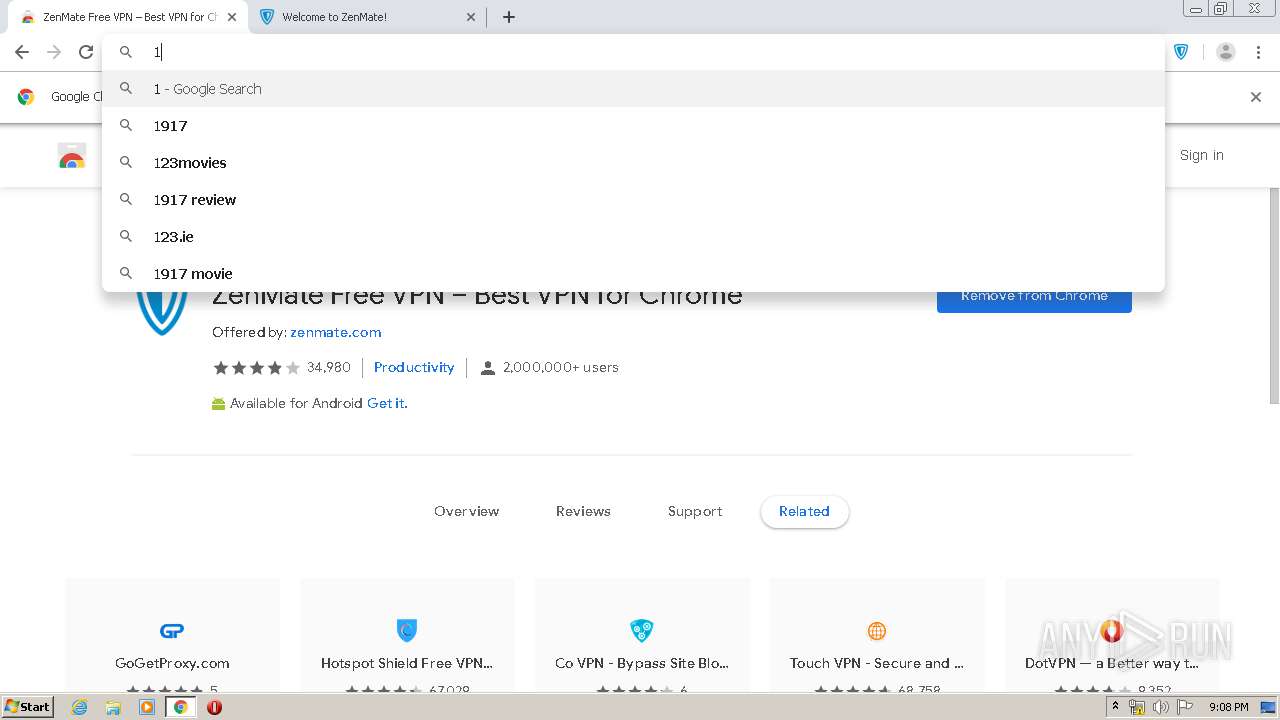
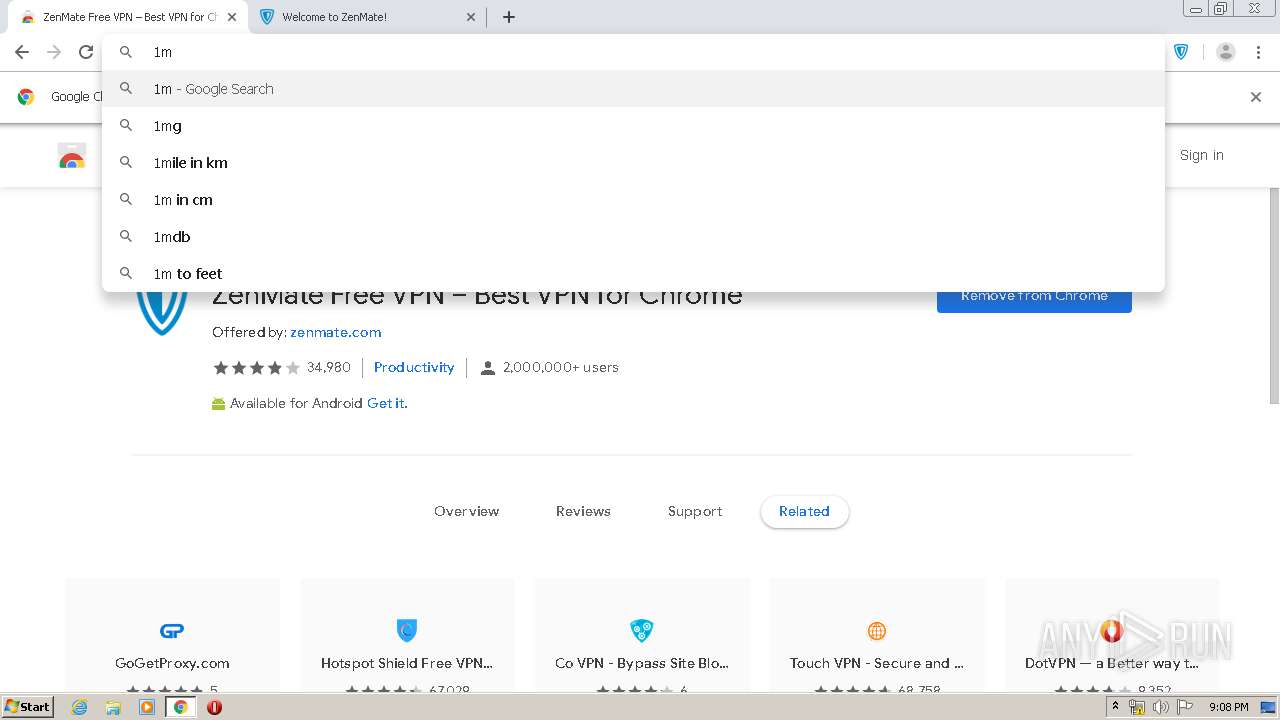
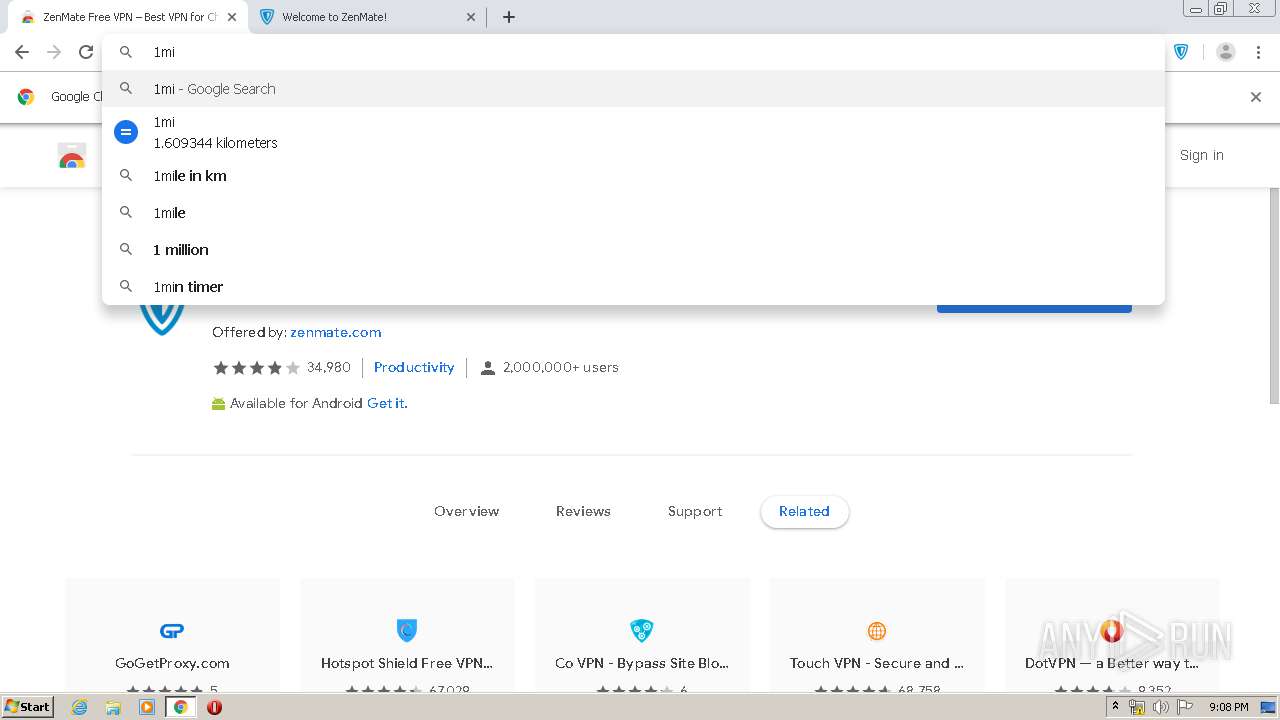
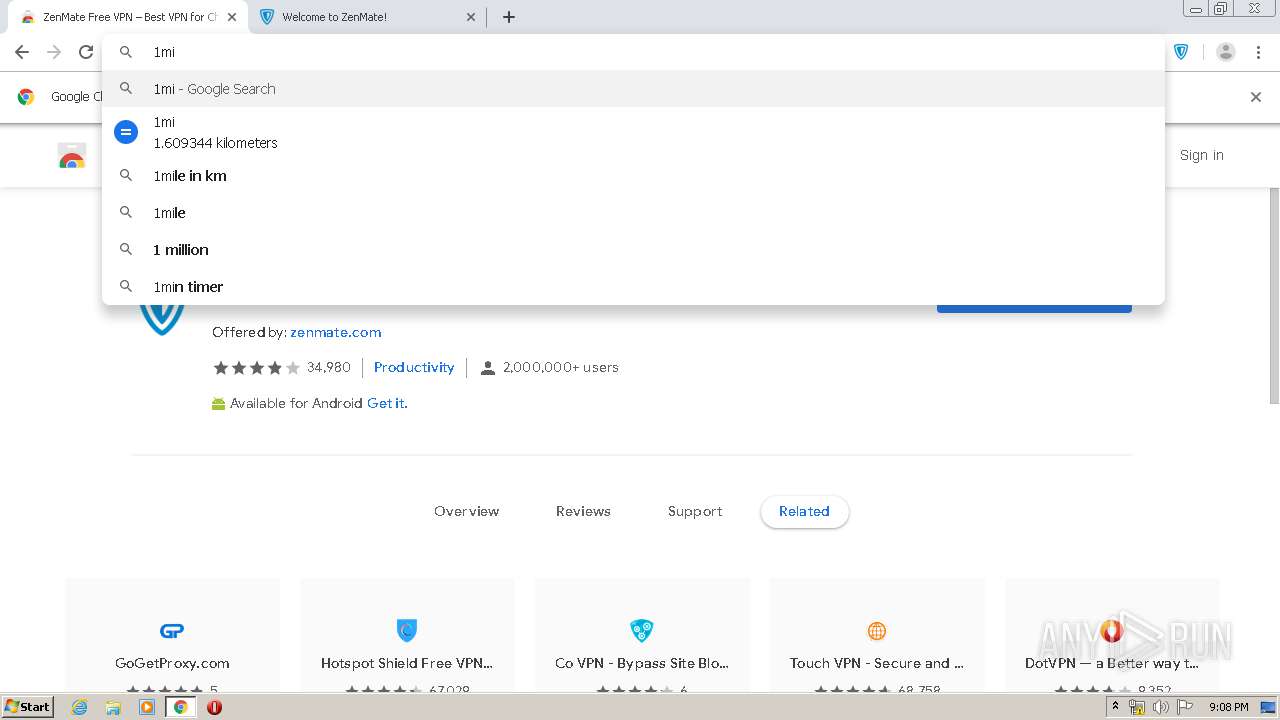
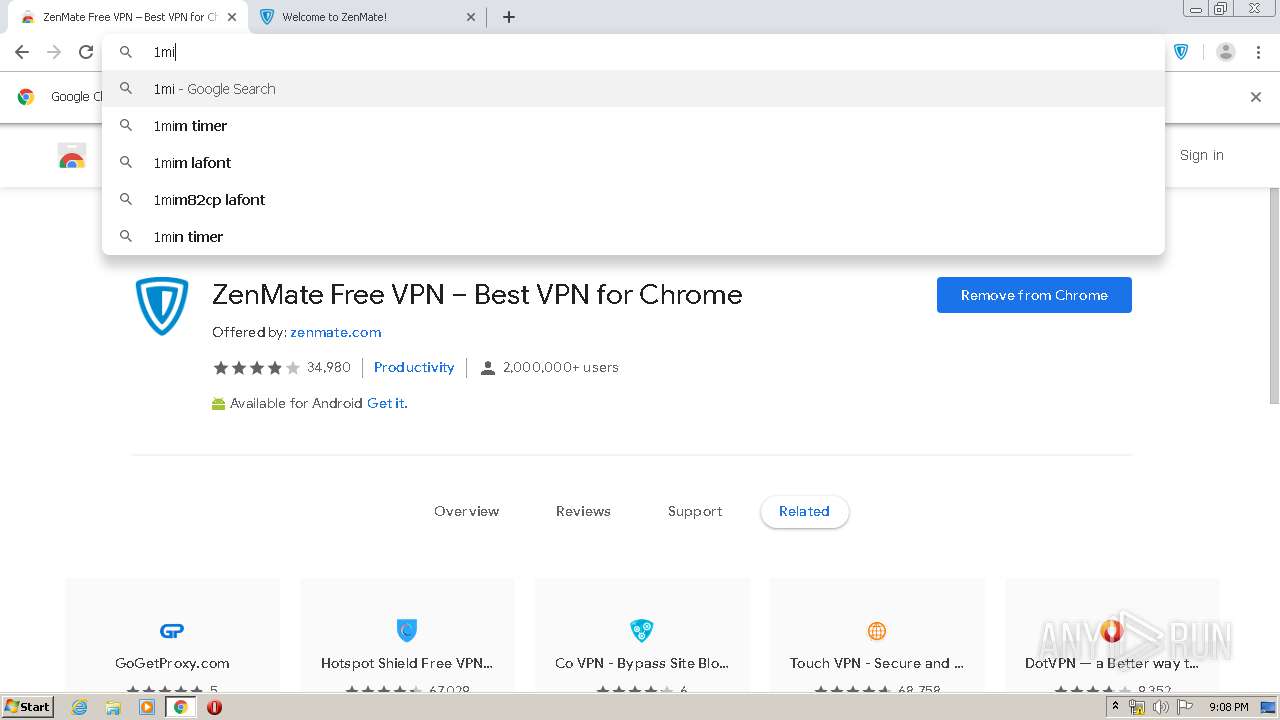
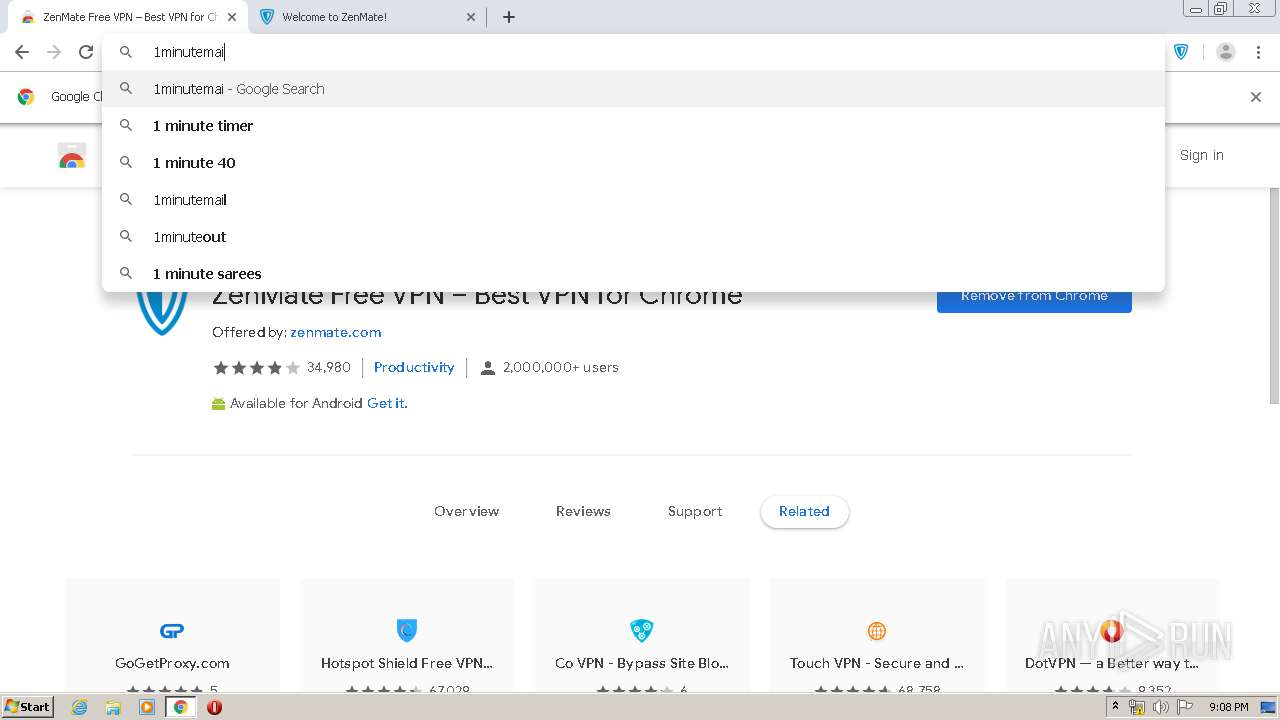
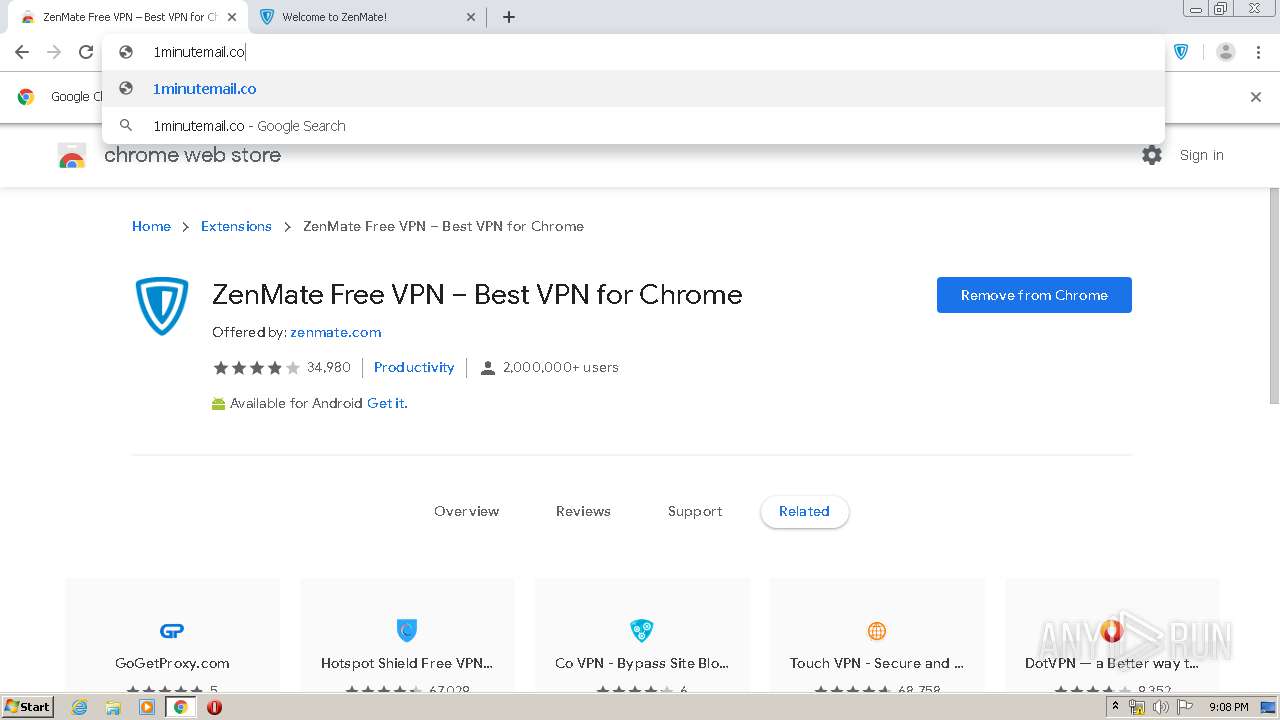
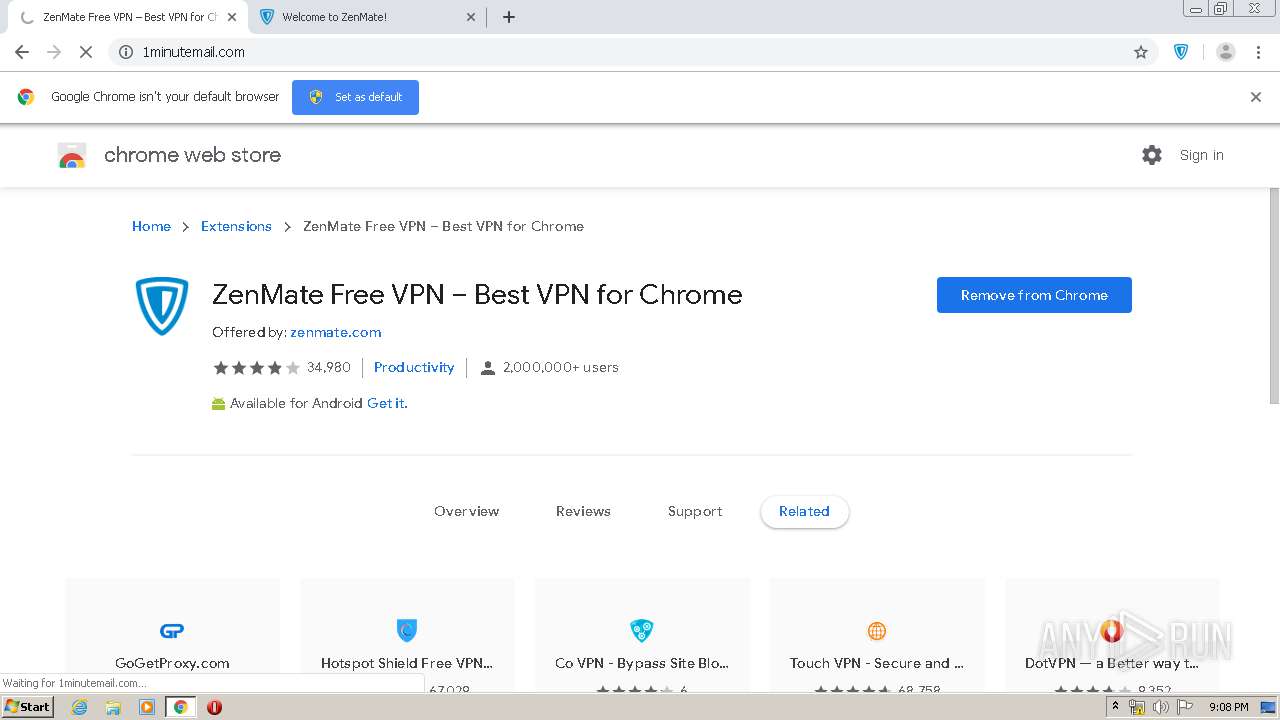
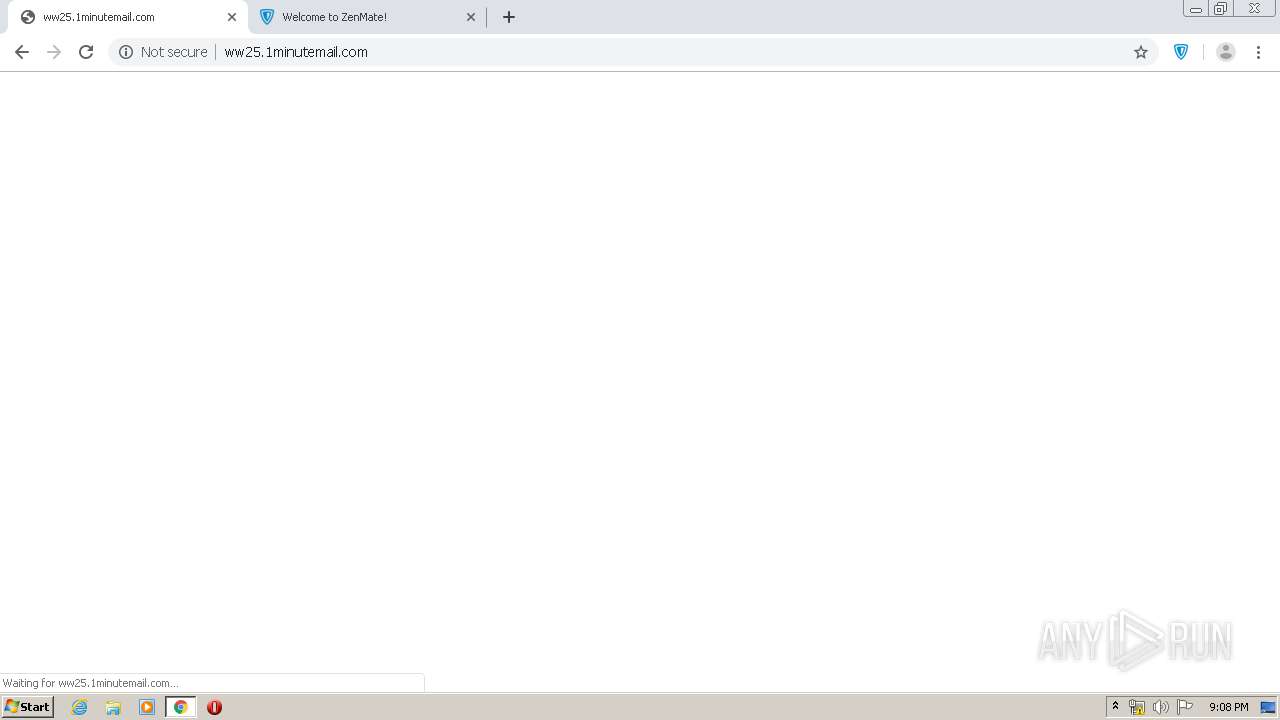
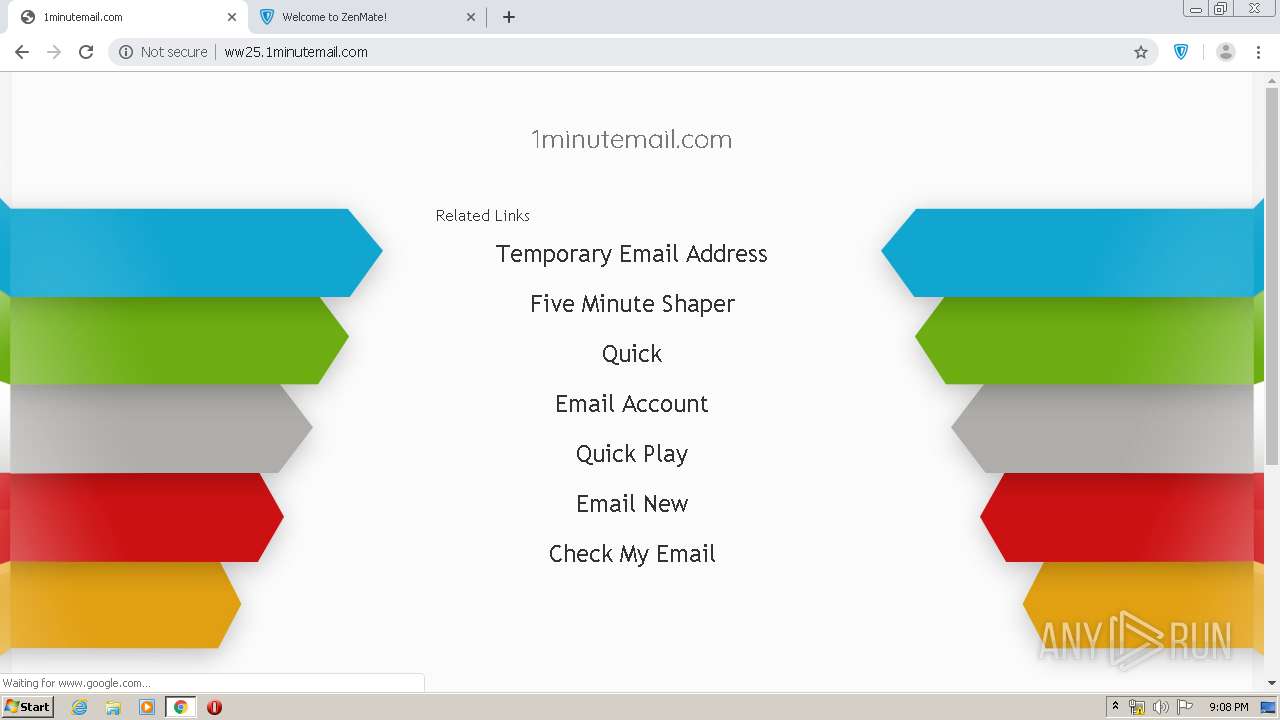
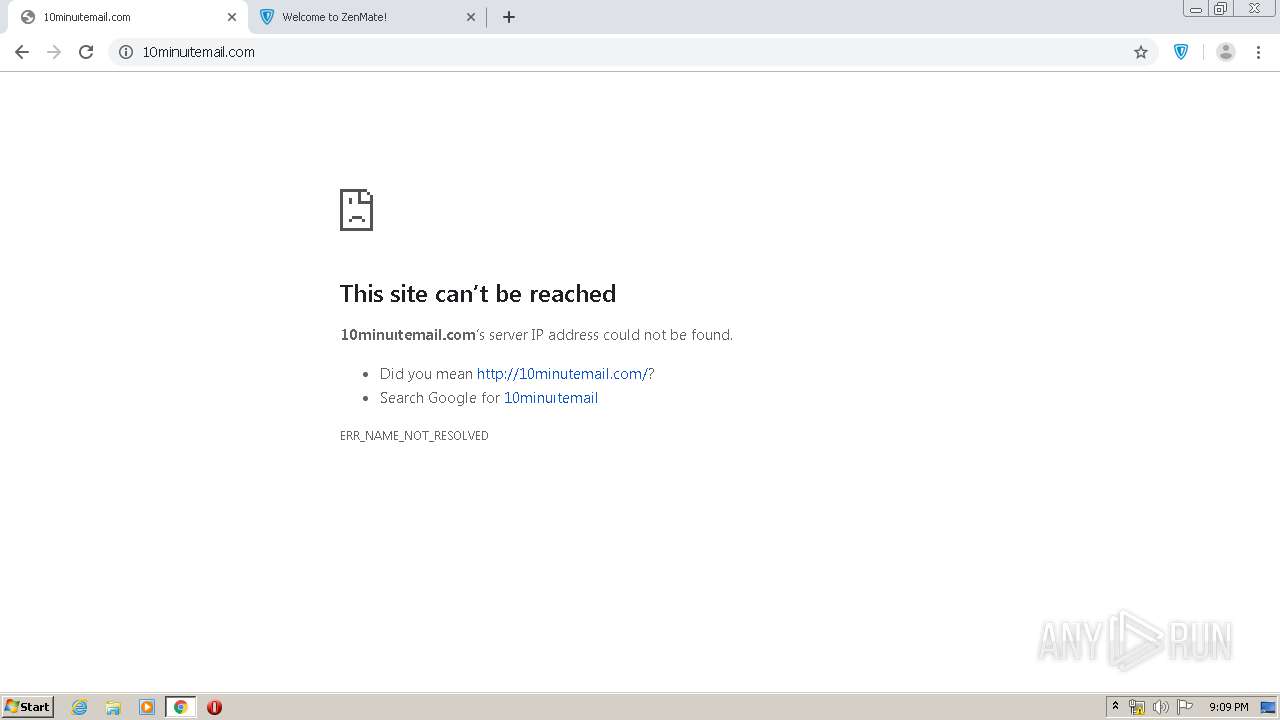
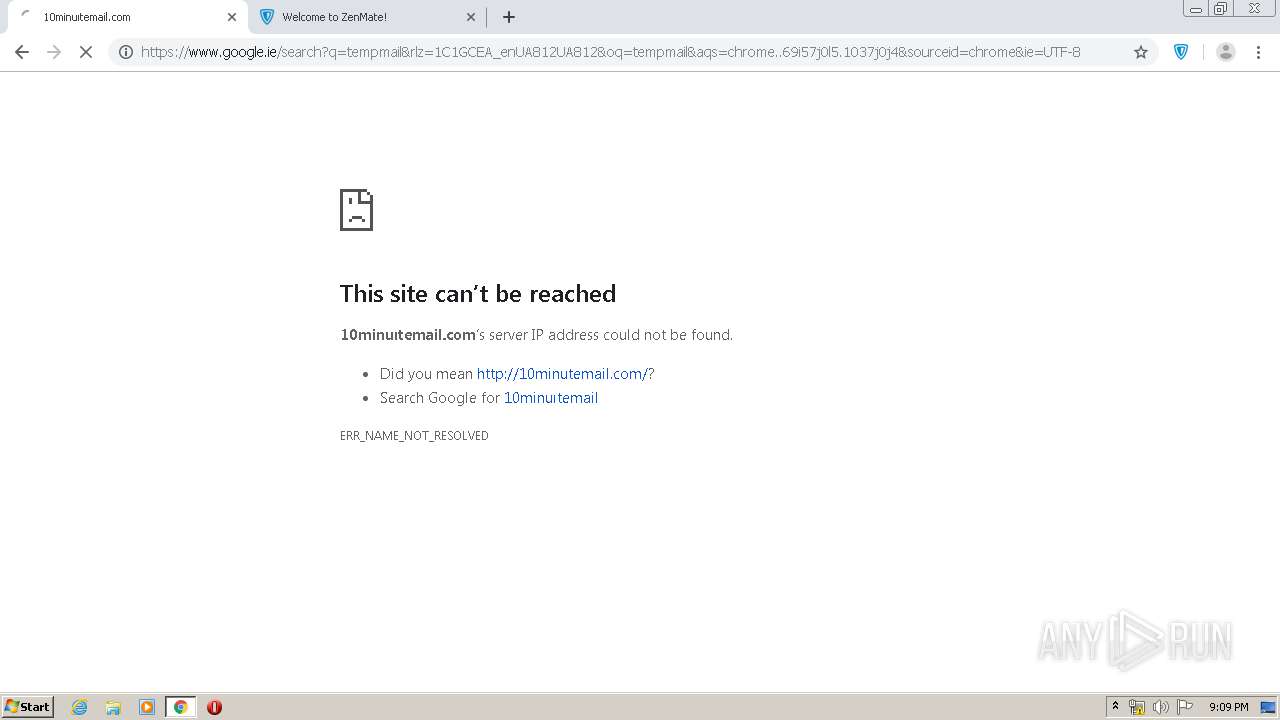
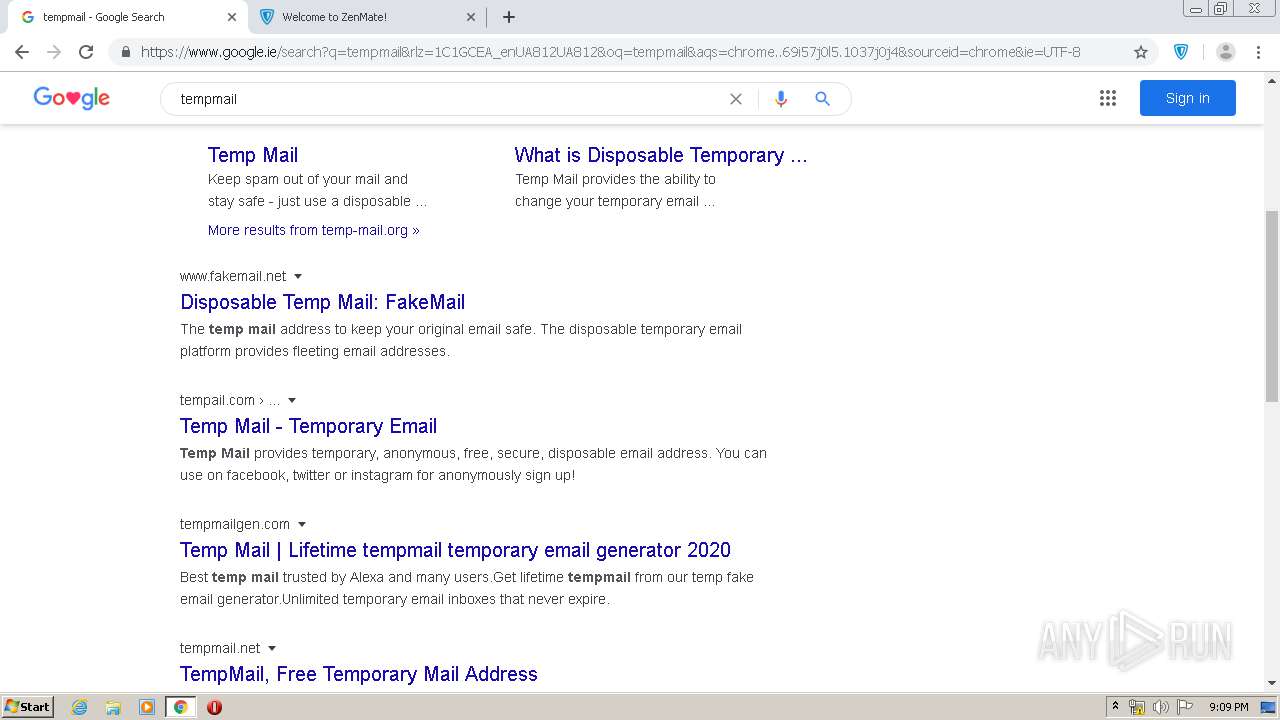
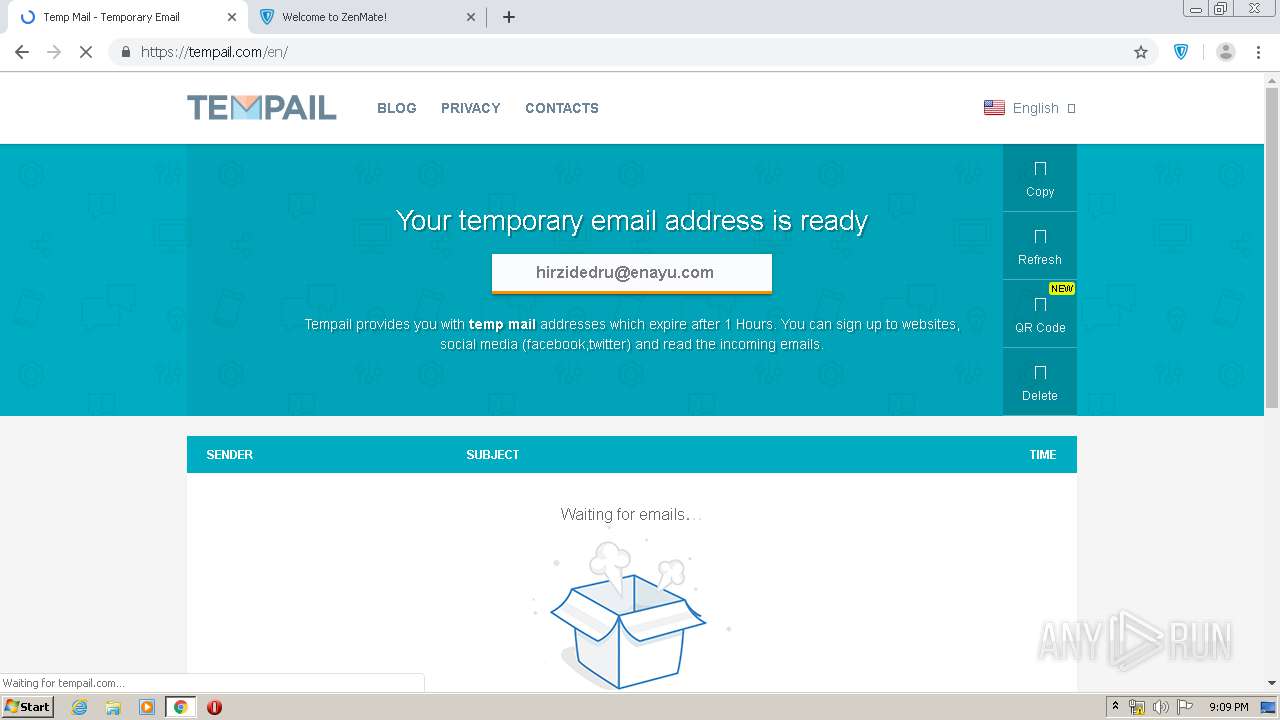
3960 | chrome.exe | GET | 302 | 103.224.212.222:80 | http://1minutemail.com/ | AU | — | — | malicious |
3960 | chrome.exe | GET | 200 | 199.59.242.155:80 | http://tracking.bodis.com/tlpv?d=eyJkb21haW5fbmFtZSI6IjFtaW51dGVtYWlsLmNvbSIsInNlcnZlciI6OTEsInRlcm1zIjpbXSwiVVJMIjoiaHR0cDpcL1wvd3cyNS4xbWludXRlbWFpbC5jb21cLyIsInJlZmVycmVyIjoiIiwiZHciOjEyODAsImRoIjo1NjksInJ3IjoxMjgwLCJyaCI6NzIwfQ&t=1586462922&abp=0 | US | — | — | whitelisted |
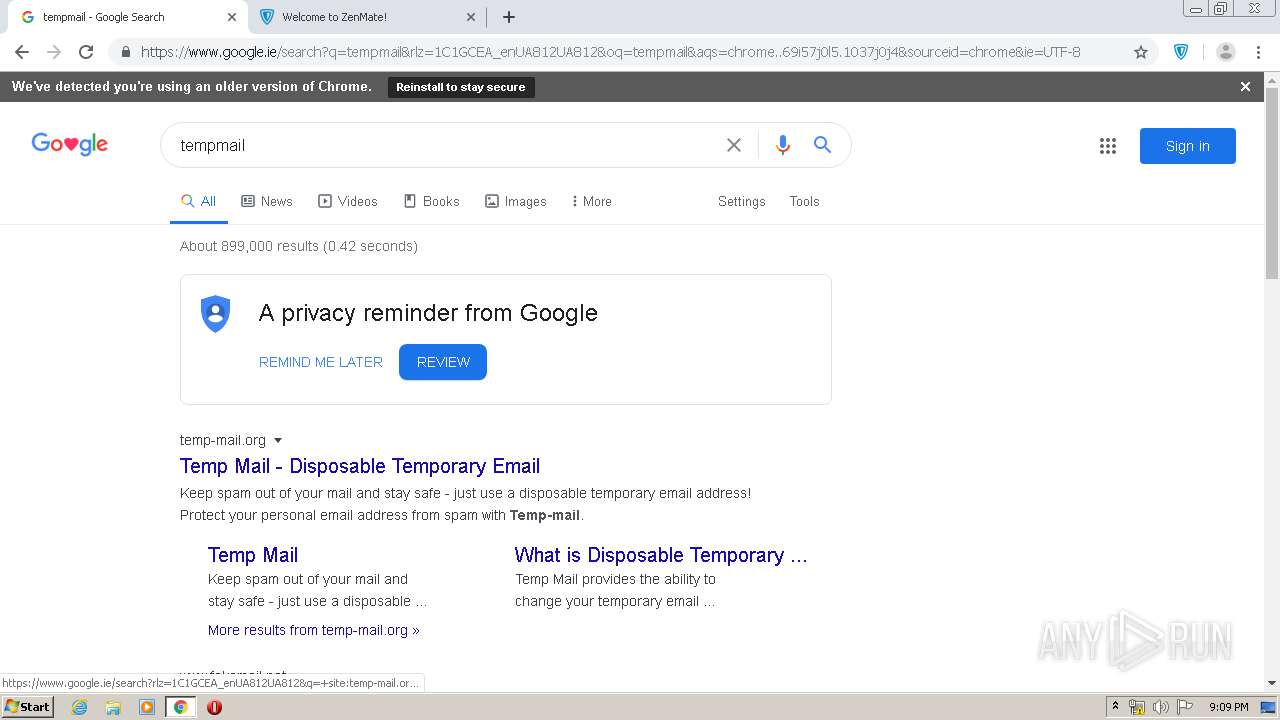
3960 | chrome.exe | GET | 301 | 104.26.6.95:80 | http://temp-mail.org/ | US | — | — | suspicious |
3960 | chrome.exe | GET | 404 | 199.59.242.153:80 | http://ww25.1minutemail.com/favicon.ico | US | html | 3.93 Kb | malicious |
3960 | chrome.exe | GET | 302 | 172.217.22.78:80 | http://www.google-analytics.com/r/__utm.gif?utmwv=5.7.2&utms=1&utmn=878710656&utmhn=fdcgdnkidjaadafnichfpabhfomcebme&utmcs=UTF-8&utmsr=1280x720&utmvp=1264x620&utmsc=24-bit&utmul=en-us&utmje=0&utmfl=-&utmdt=Welcome%20to%20ZenMate!&utmhid=2045334522&utmr=-&utmp=%2Fextension-welcome&utmht=1586462868870&utmac=UA-40329910-24&utmcc=__utma%3D194824314.1438832662.1586462869.1586462869.1586462869.1%3B%2B__utmz%3D194824314.1586462869.1.1.utmcsr%3D(direct)%7Cutmccn%3D(direct)%7Cutmcmd%3D(none)%3B&utmjid=230564186&utmredir=1&utmu=qACAAAAAAAAAAAAAAAAAAAAE~ | US | html | 370 b | whitelisted |
3960 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww25.1minutemail.com/public/legacy/10352/resources/arrows-bg.jpg | US | image | 93.6 Kb | malicious |
3960 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww25.1minutemail.com/ | US | html | 3.93 Kb | malicious |
3960 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww25.1minutemail.com/public/legacy/10352/resources/arrows-bg-ext.png | US | image | 1.12 Kb | malicious |
3960 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
3960 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 524 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3960 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 172.217.16.174:443 | chrome.google.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 172.217.23.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 216.58.206.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 172.217.23.182:443 | i.ytimg.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 74.125.133.155:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
3960 | chrome.exe | 172.217.22.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 172.217.22.40:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 172.217.16.142:443 | www.youtube.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
chrome.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.gstatic.com |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
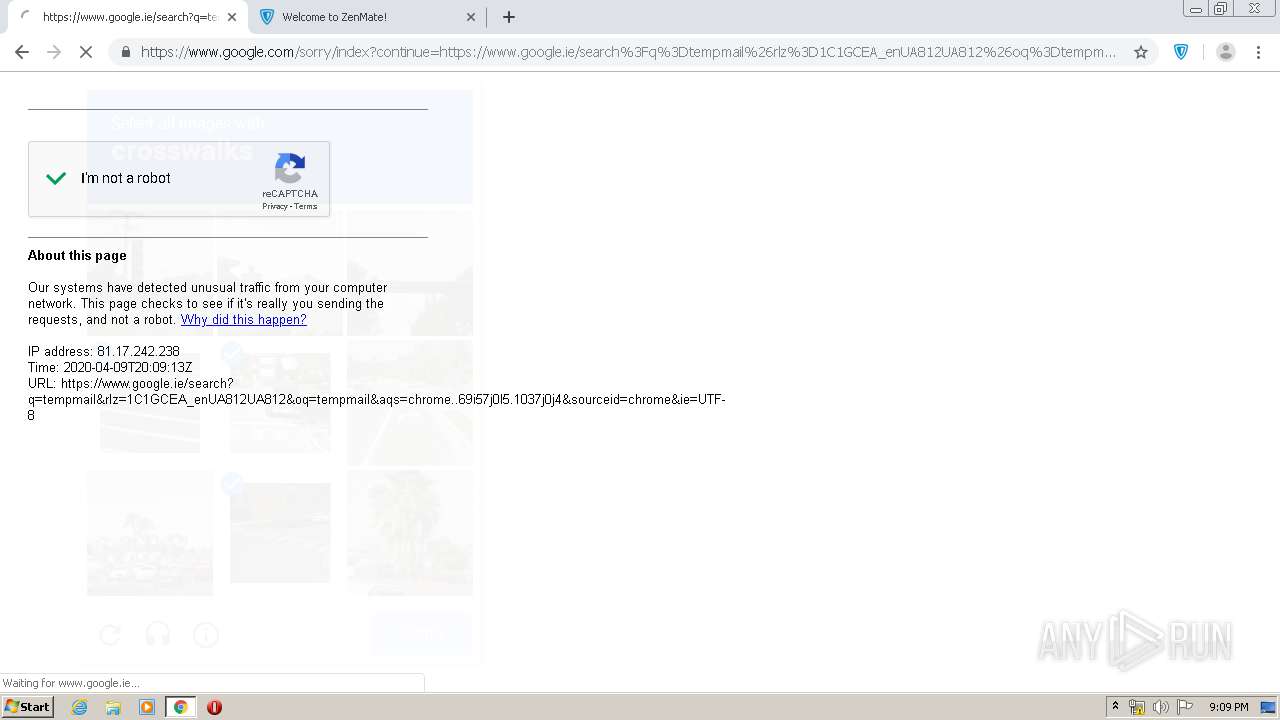
3960 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
3960 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |