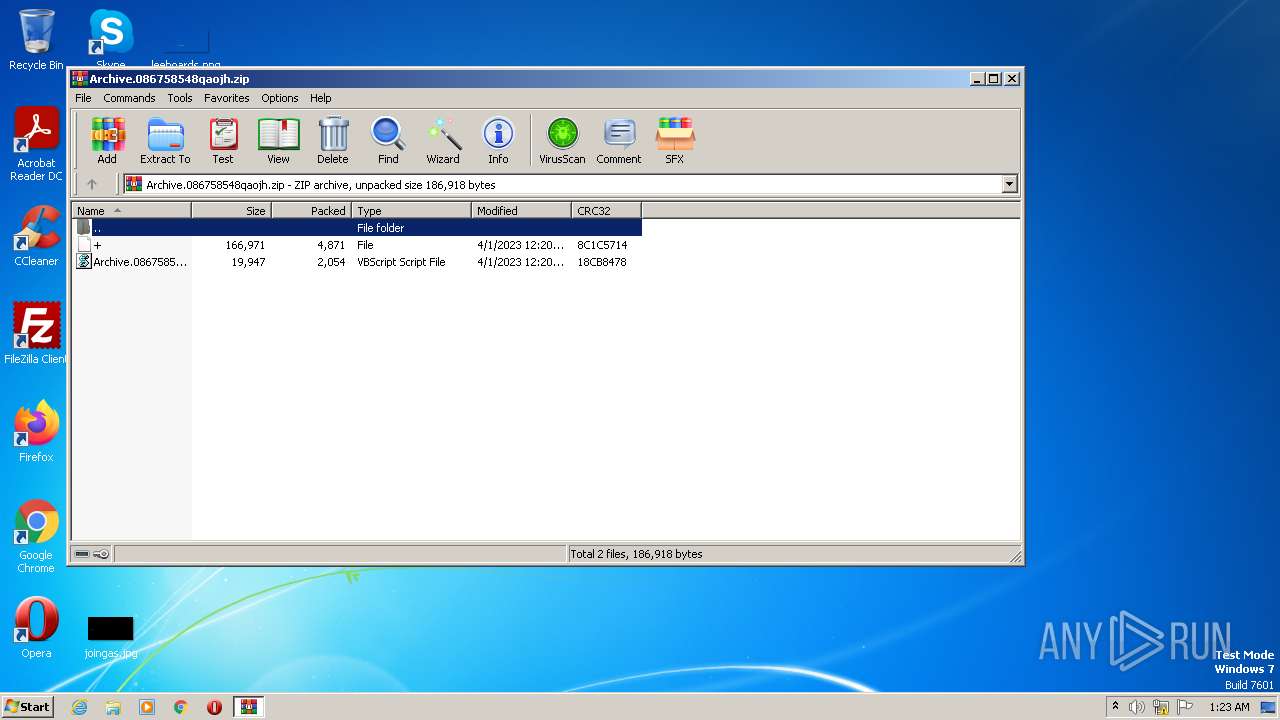
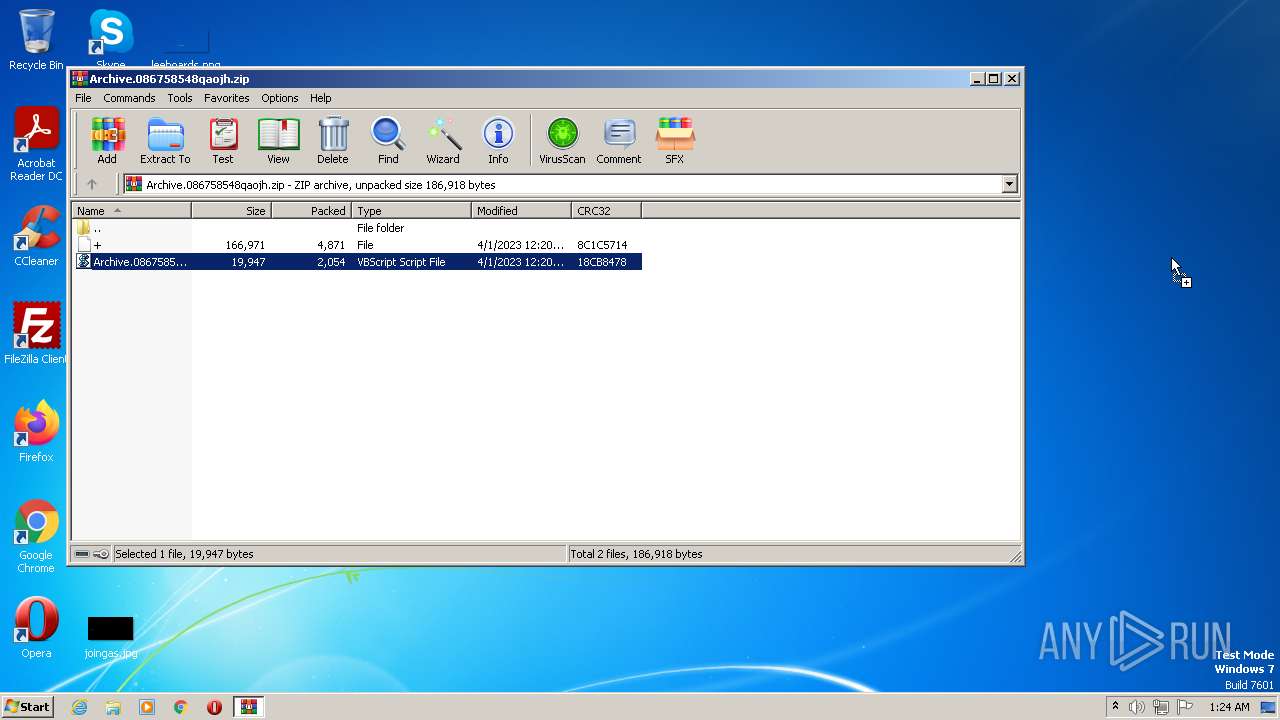
| File name: | Archive.086758548qaojh.zip |
| Full analysis: | https://app.any.run/tasks/3c7b0421-4e33-4372-9231-35a399396ef6 |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 00:23:42 |
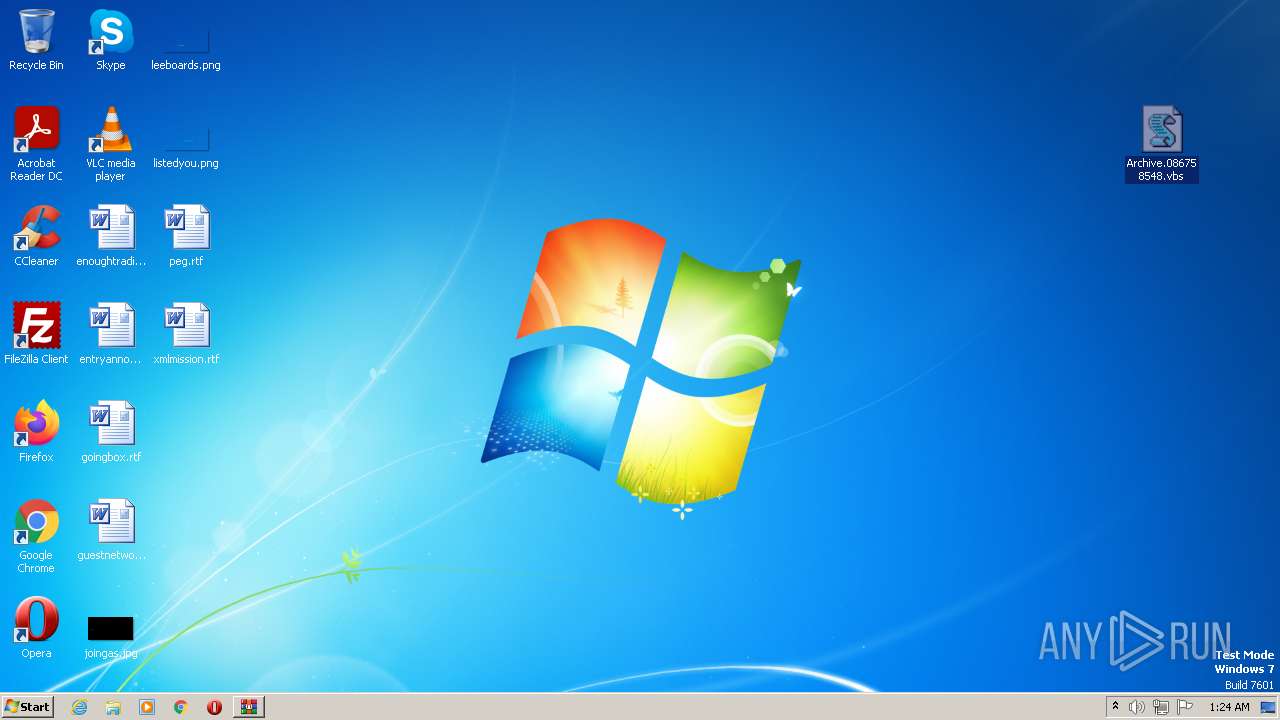
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 1C58C35CB58A4F2B0138CA0232FB3BD1 |
| SHA1: | 00EE9128696B59644D310B7387A338C317A40B5C |
| SHA256: | 254192A864D234870EA94384411C5599E49D5A5649BA0E9CDE9CF245196DA924 |
| SSDEEP: | 192:r2gvMepAjr+idrF6ZZwf/kUKn57TTK+4KJg:L0ep0+XZZPfn9PlJg |
MALICIOUS
Unusual connection from system programs
- wscript.exe (PID: 3660)
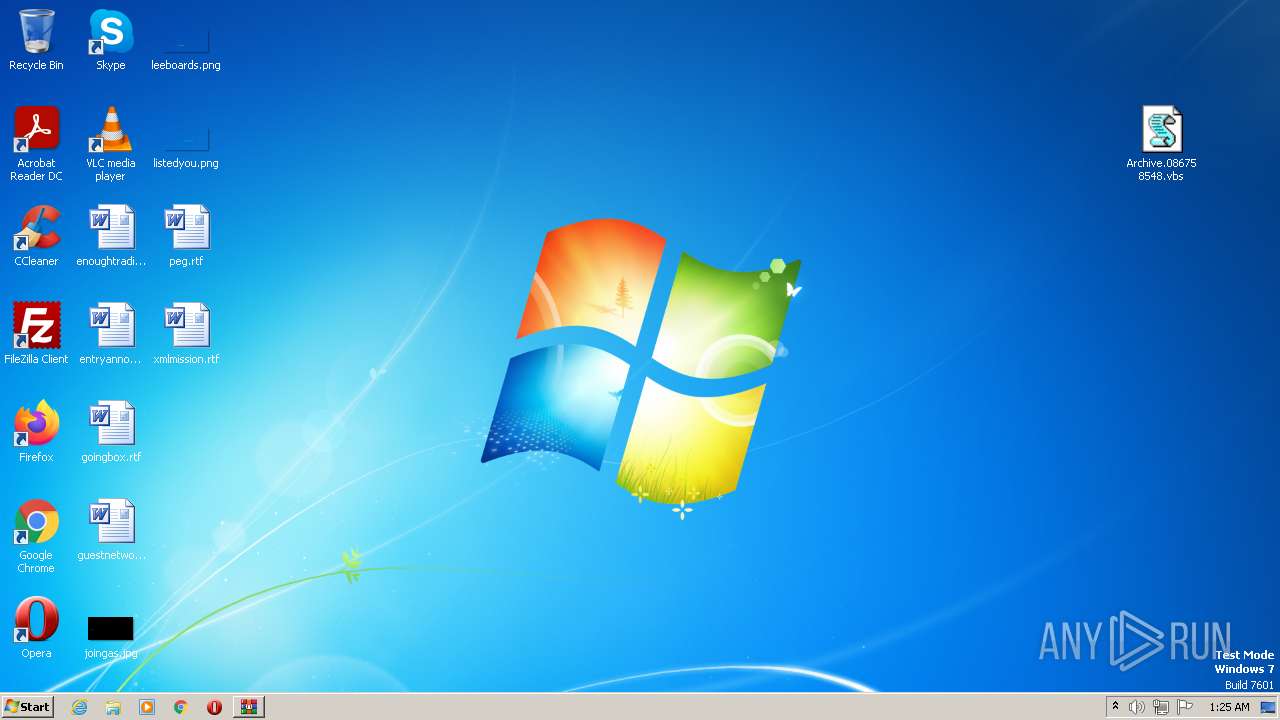
Application was dropped or rewritten from another process
- HostFx.exe (PID: 2740)
SUSPICIOUS
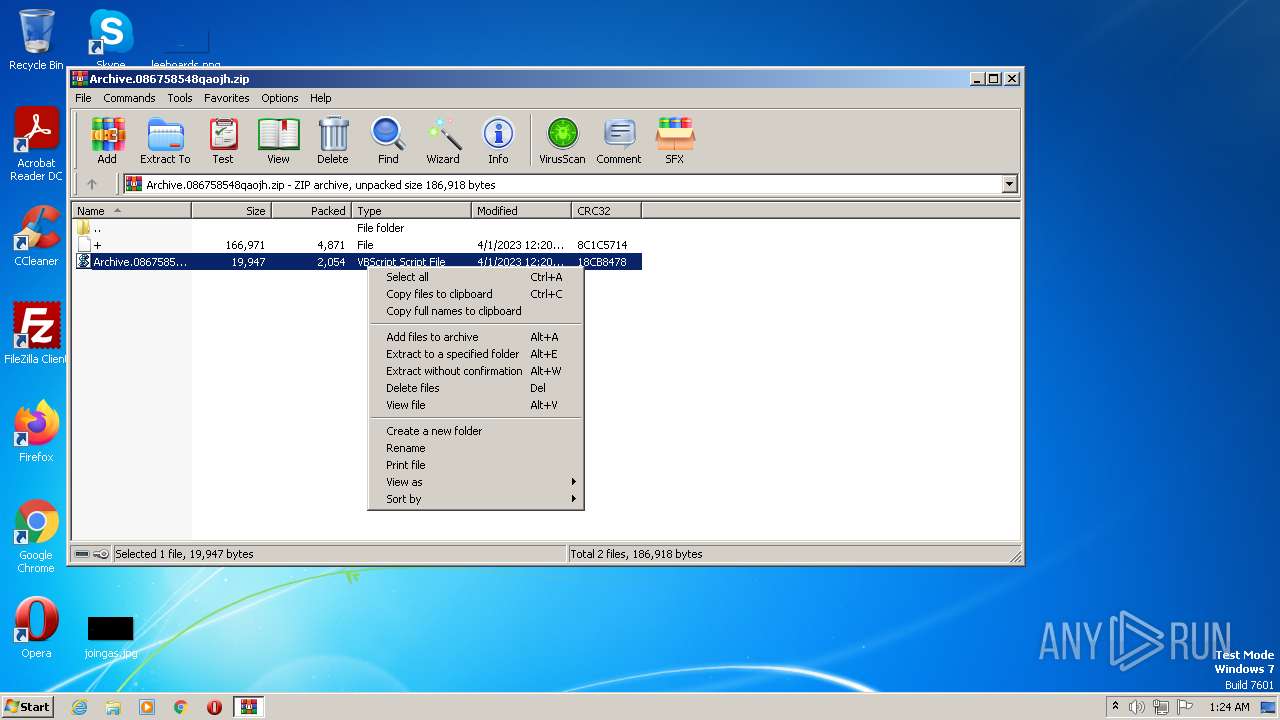
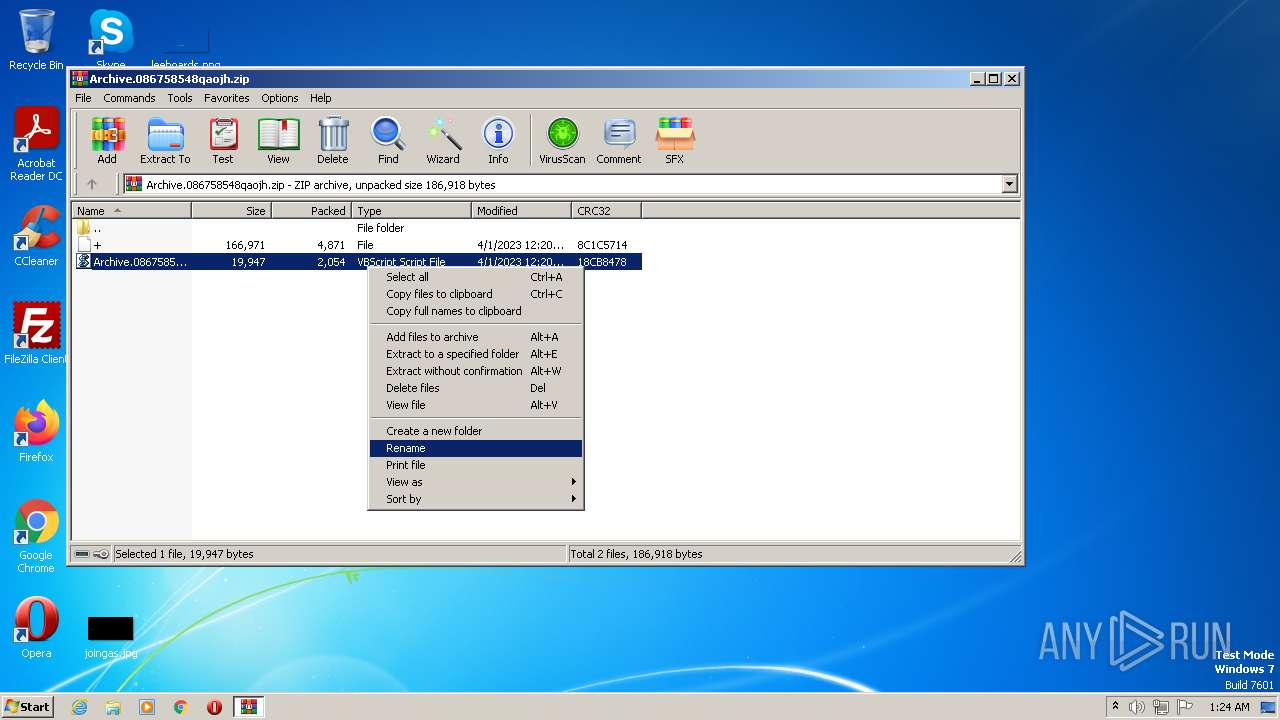
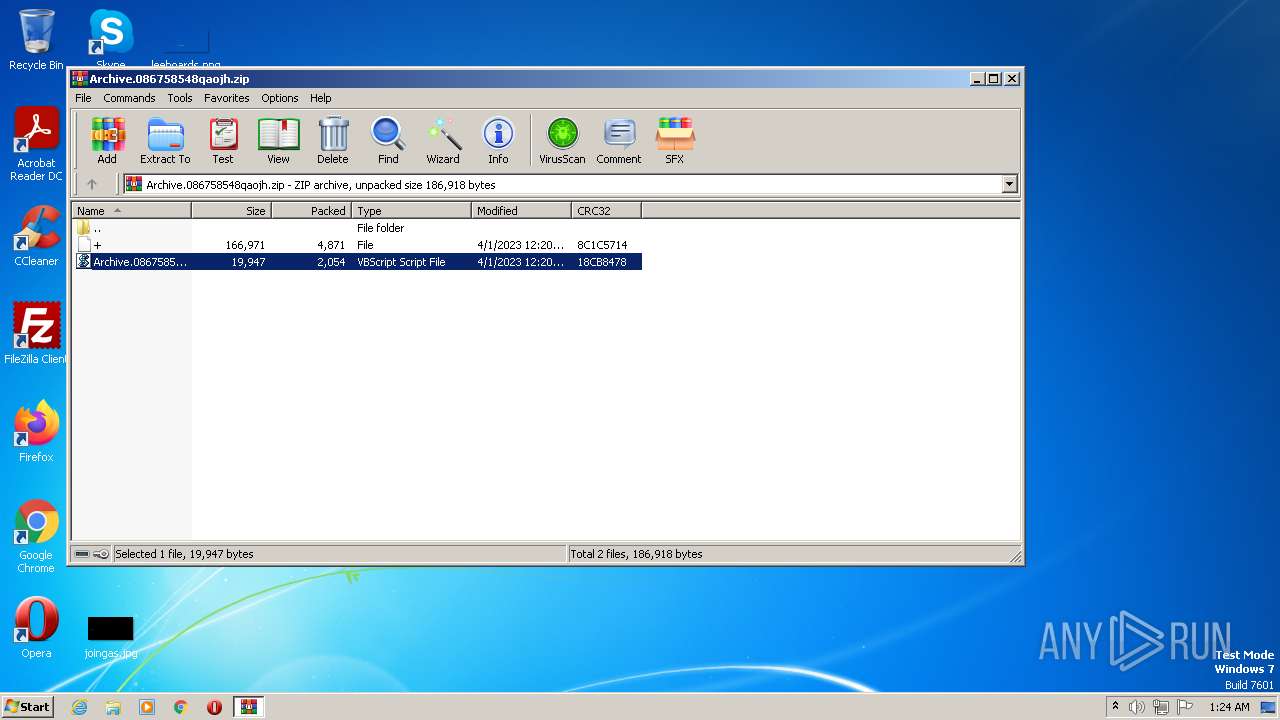
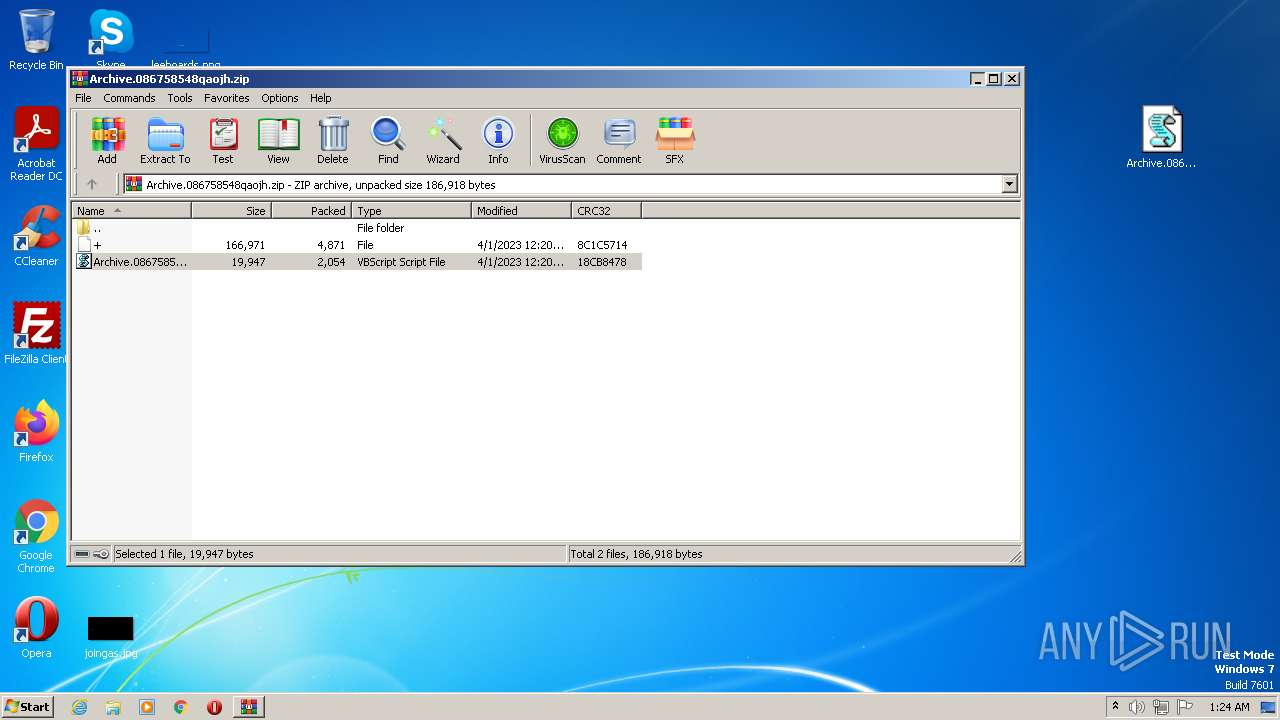
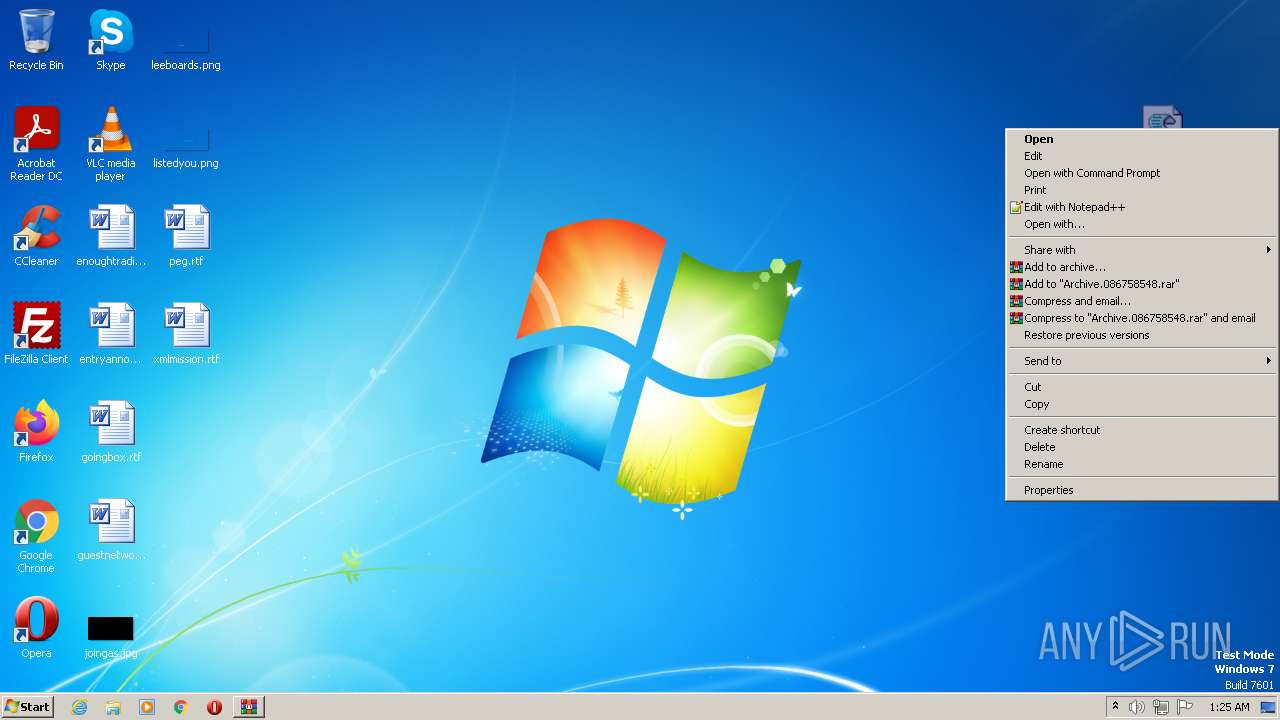
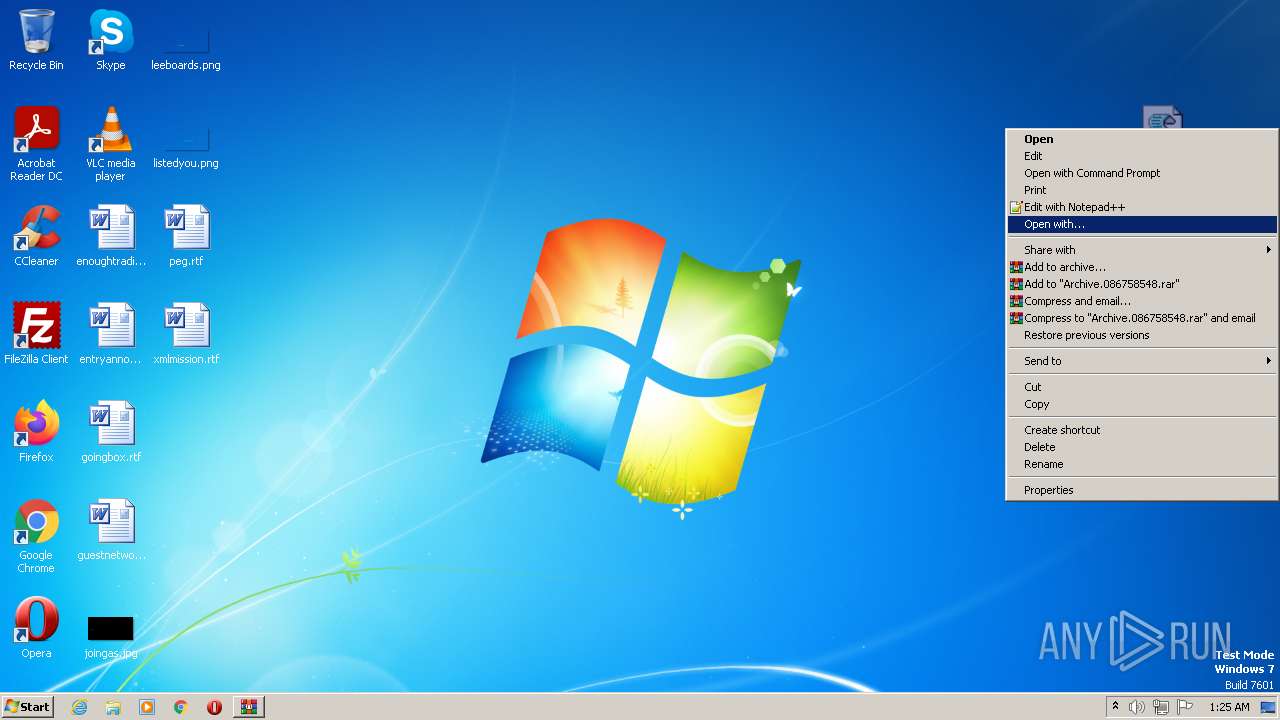
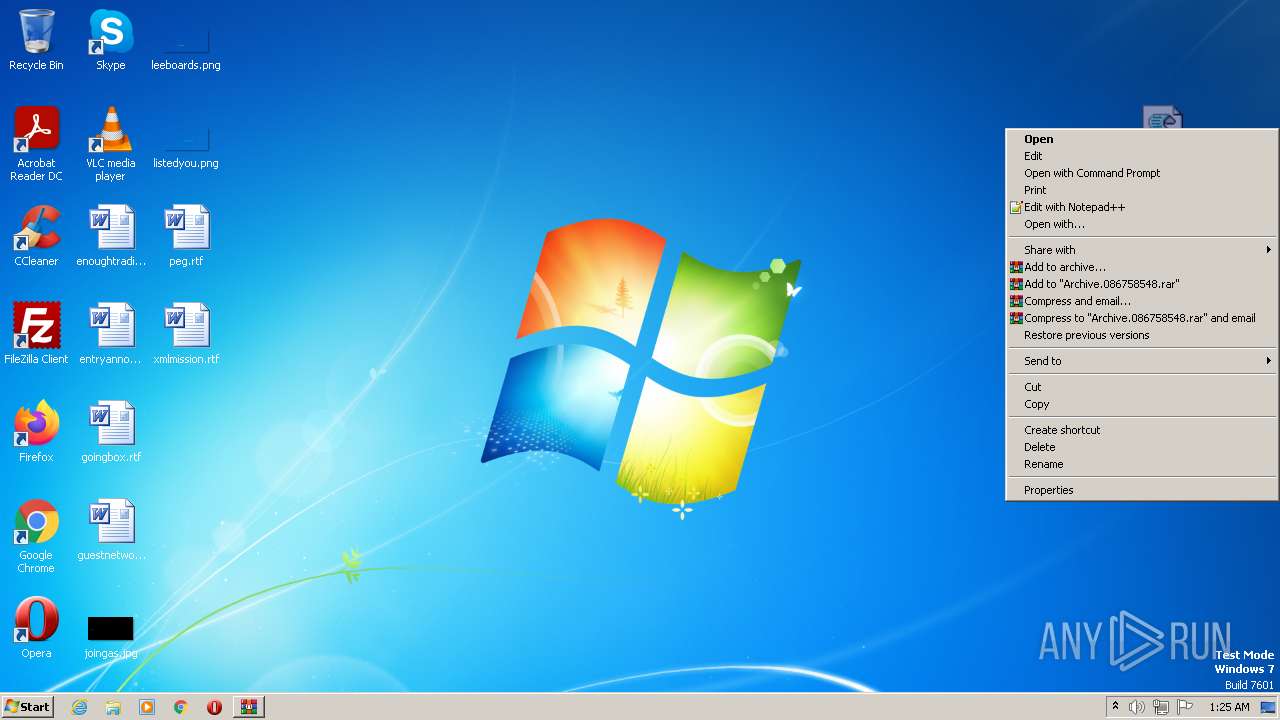
The process executes VB scripts
- WinRAR.exe (PID: 2512)
Connects to unusual port
- wscript.exe (PID: 3660)
Reads the Internet Settings
- wscript.exe (PID: 3660)
Executable content was dropped or overwritten
- wscript.exe (PID: 3660)
INFO
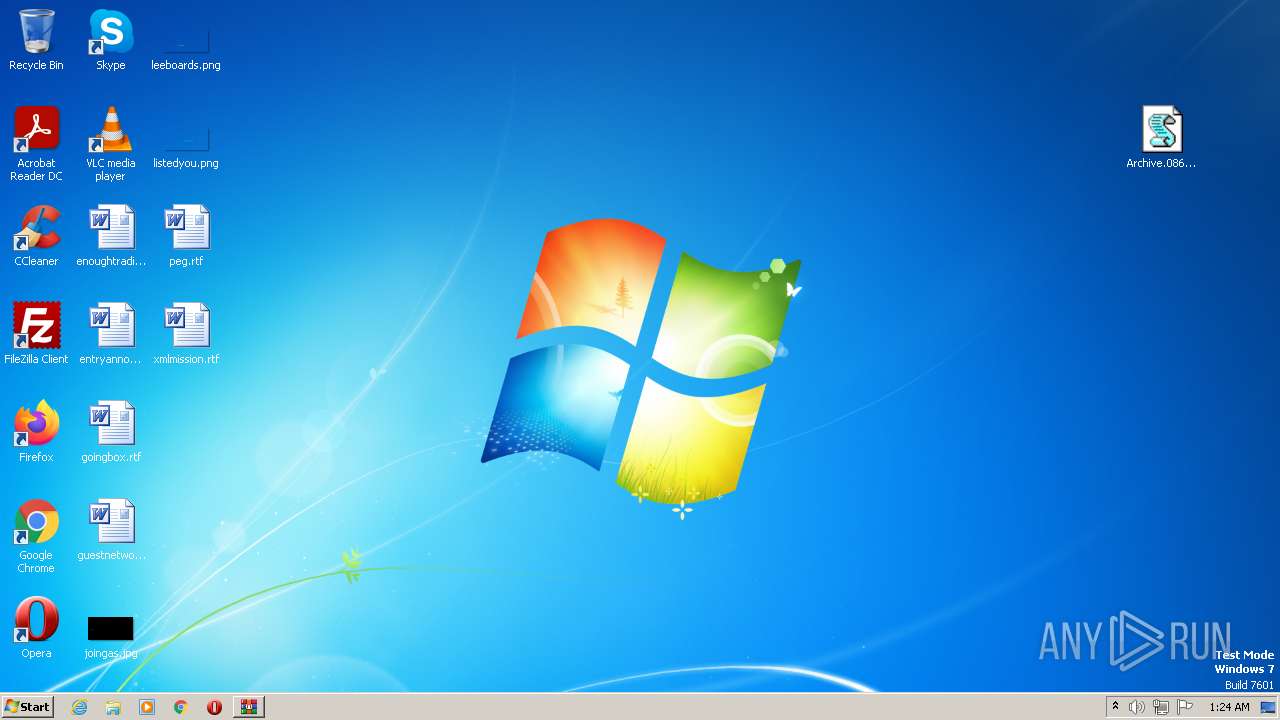
Manual execution by a user
- wmpnscfg.exe (PID: 2764)
- wscript.exe (PID: 2348)
- wscript.exe (PID: 2924)
- wscript.exe (PID: 2436)
Checks supported languages
- wmpnscfg.exe (PID: 2764)
- HostFx.exe (PID: 2740)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 2764)
Reads the computer name
- wmpnscfg.exe (PID: 2764)
The process checks LSA protection
- wmpnscfg.exe (PID: 2764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | + |
|---|---|
| ZipUncompressedSize: | 166971 |
| ZipCompressedSize: | 4871 |
| ZipCRC: | 0x8c1c5714 |
| ZipModifyDate: | 2023:04:01 00:20:44 |
| ZipCompression: | Deflated |
| ZipBitFlag: | 0x0800 |
| ZipRequiredVersion: | 20 |
Total processes
46
Monitored processes
9
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa2512.13547\Archive.086758548.vbs" | C:\Windows\System32\wscript.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 964 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa2512.15229\Archive.086758548.vbs" | C:\Windows\System32\wscript.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2348 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\Archive.086758548.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2436 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\Archive.086758548.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2512 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Archive.086758548qaojh.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2740 | "C:\pastajh\HostFx.exe" | C:\pastajh\HostFx.exe | — | wscript.exe | |||||||||||
User: admin Company: Caphyon LTD Integrity Level: MEDIUM Description: Advanced Installer SCCM Tool Exit code: 0 Version: 19.9.0.0 Modules
| |||||||||||||||
| 2764 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2924 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\Archive.086758548.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3660 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa2512.13396\Archive.086758548.vbs" | C:\Windows\System32\wscript.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
3 346
Read events
3 286
Write events
54
Delete events
6
Modification events
| (PID) Process: | (2512) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
8
Suspicious files
2
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2512.13396\Archive.086758548.vbs | text | |
MD5:— | SHA256:— | |||
| 2512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2512.13547\Archive.086758548.vbs | text | |
MD5:— | SHA256:— | |||
| 3660 | wscript.exe | C:\pastajh\Test.Zip | compressed | |
MD5:— | SHA256:— | |||
| 2512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2512.16682\Archive.086758548.vbs | text | |
MD5:— | SHA256:— | |||
| 3660 | wscript.exe | C:\pastajh\zlibai.dll | executable | |
MD5:— | SHA256:— | |||
| 2512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2512.15229\Archive.086758548.vbs | text | |
MD5:— | SHA256:— | |||
| 3660 | wscript.exe | C:\pastajh\HostFx.exe | executable | |
MD5:B5485D229F8078575D639FB903B4FCA7 | SHA256:9625E775E955281732270B7A0FC468BEF83B468BE85E82E0659973AEFA369782 | |||
| 3660 | wscript.exe | C:\pastajh\dbghelp.dll | executable | |
MD5:4003E34416EBD25E4C115D49DC15E1A7 | SHA256:C06430B8CB025BE506BE50A756488E1BCC3827C4F45158D93E4E3EEB98CE1E4F | |||
| 3660 | wscript.exe | C:\pastajh\uires.dll | executable | |
MD5:87C7411E05FF159A3707869ADC9D5C01 | SHA256:207D66DAE08CA39065019355802604768B213ED2817E78BEA128F136784AF6A7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
0
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3660 | wscript.exe | GET | 200 | 142.11.237.26:4873 | http://142.11.237.26:4873/ibra.zip? | US | text | 29.9 Mb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3660 | wscript.exe | 142.11.237.26:4873 | — | HOSTWINDS | US | suspicious |