| File name: | windowsnetservicehelper-1.1.21bt2.exe.NULL |
| Full analysis: | https://app.any.run/tasks/574f7d1a-2b3e-4417-a31b-727ffbbe7a40 |
| Verdict: | Malicious activity |
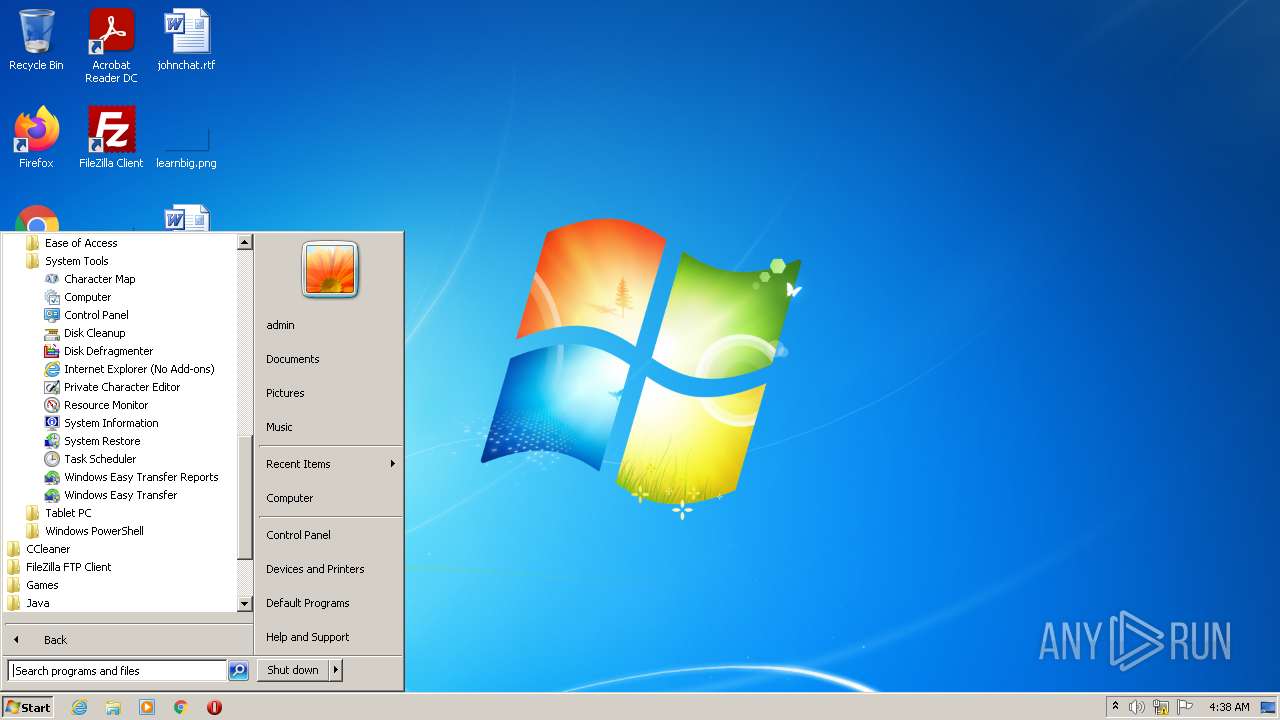
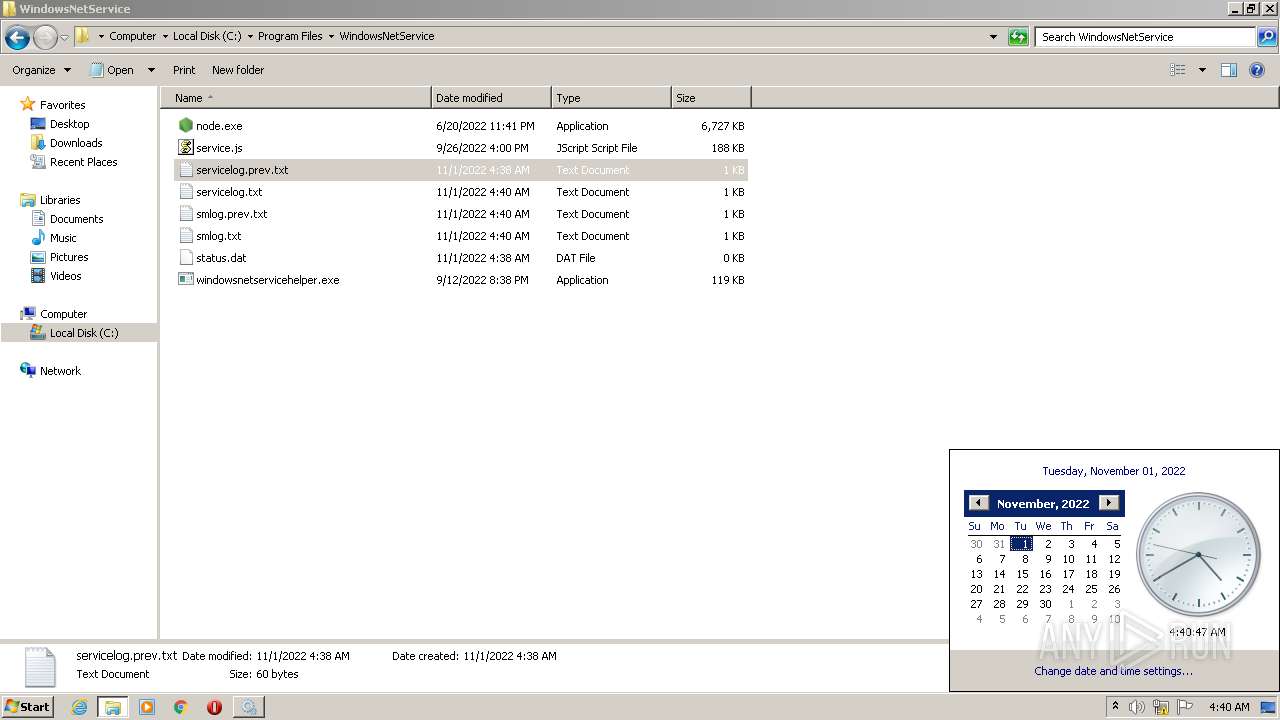
| Analysis date: | November 01, 2022, 04:38:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 455D41020B4A6D23F594D98E1AE80775 |
| SHA1: | ED33649CF74FF162E19D1FFA6793A76BDCE49525 |
| SHA256: | 2535C027E98C8B83C9DA56C45354099D30445DB935B71B38609B93E7CFB5C7F7 |
| SSDEEP: | 196608:Sqzwr5QLUbwOydkc/XQAqNA+0pDrAuOYEPY2+aV:ytiJJqBKOrPv+O |
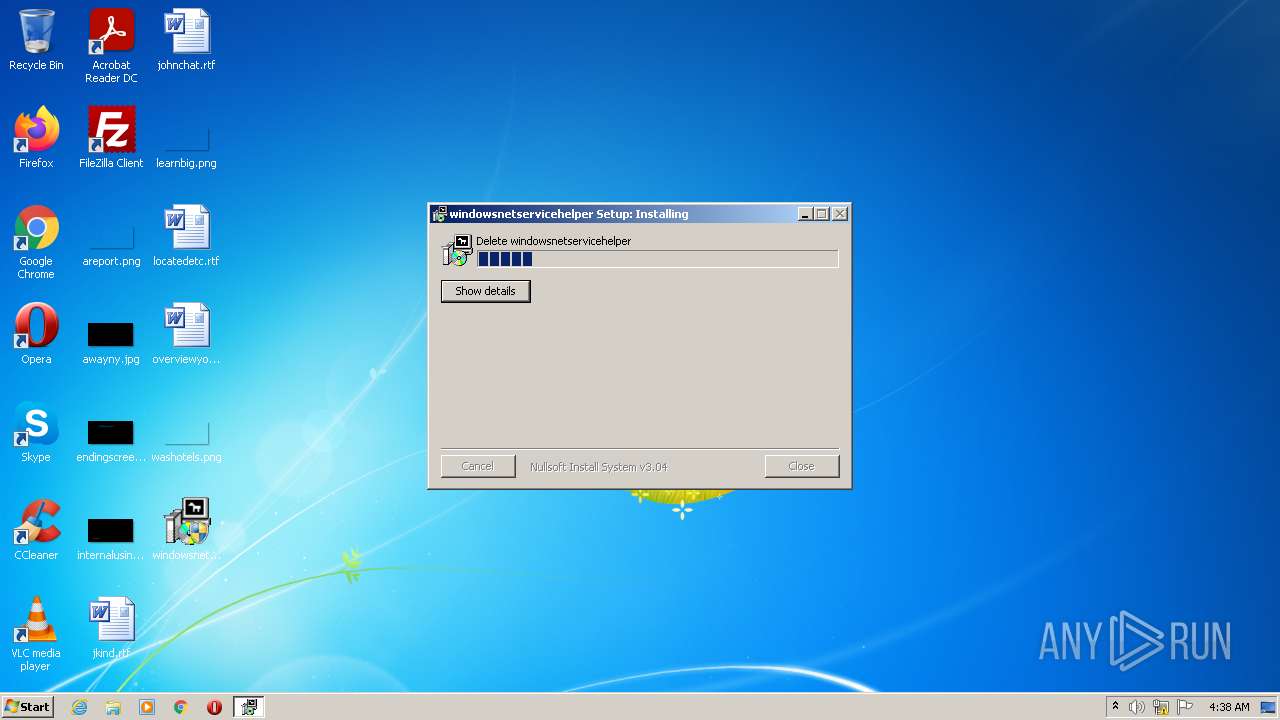
MALICIOUS
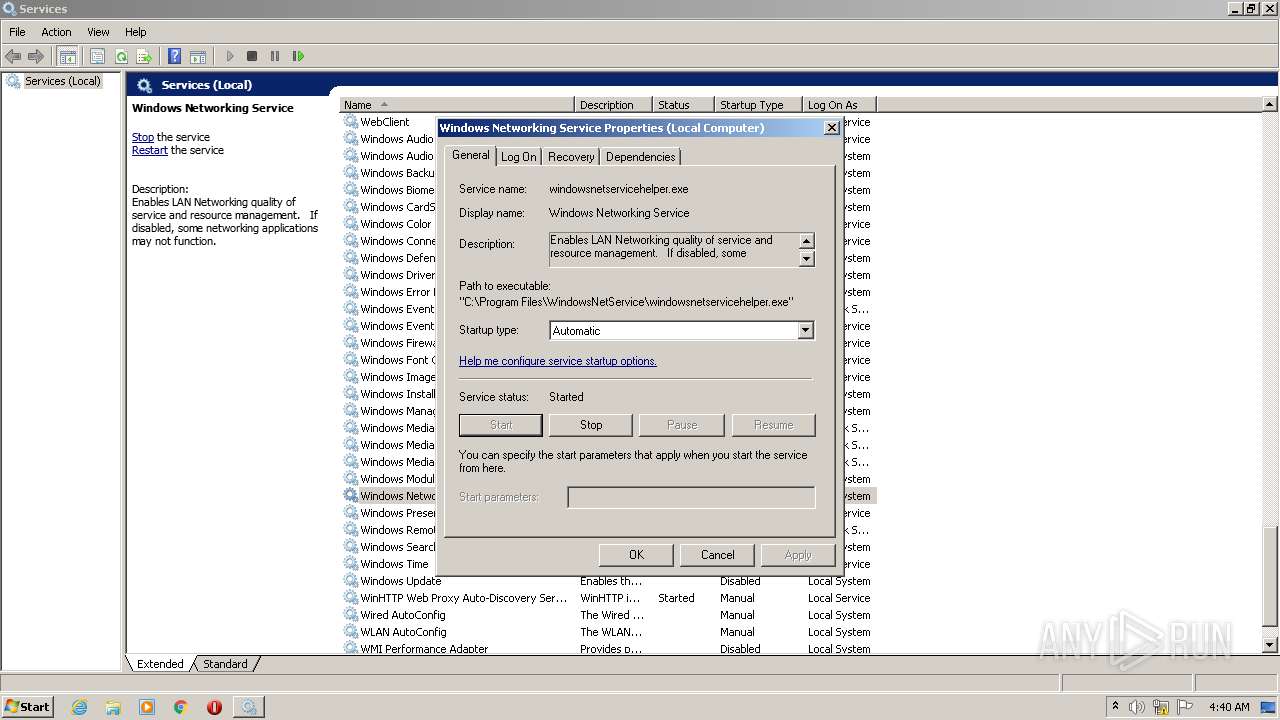
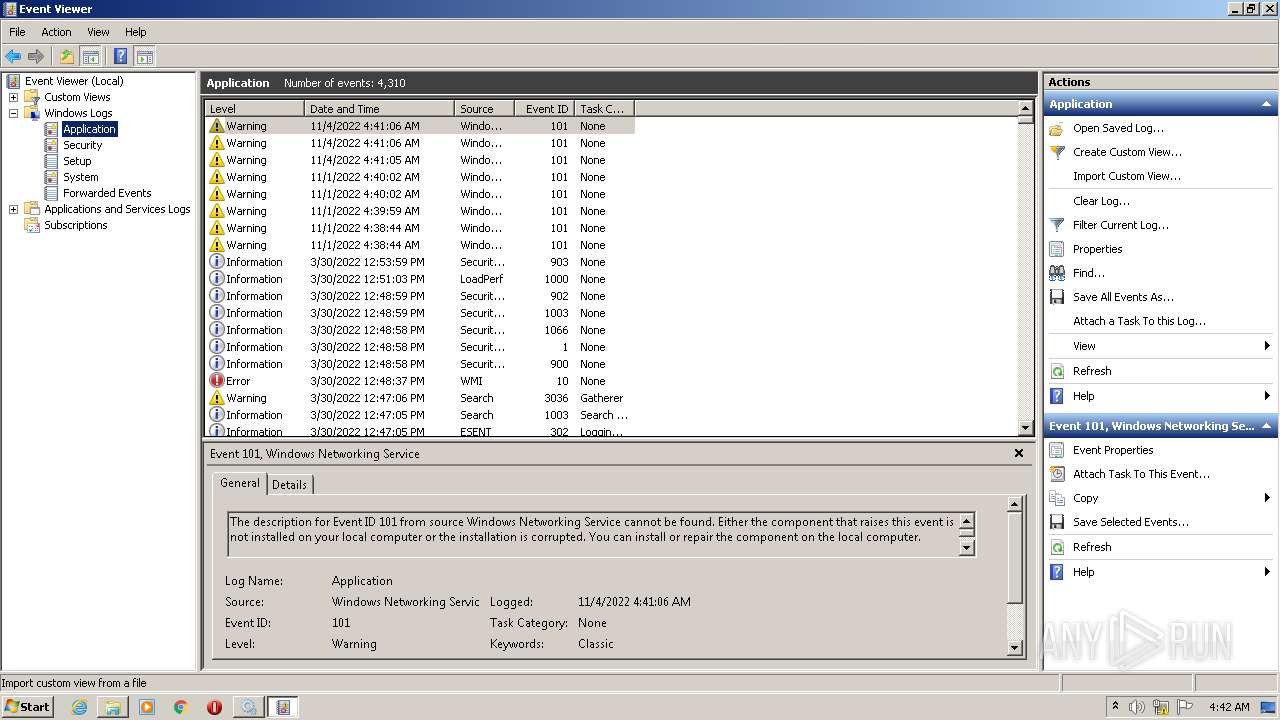
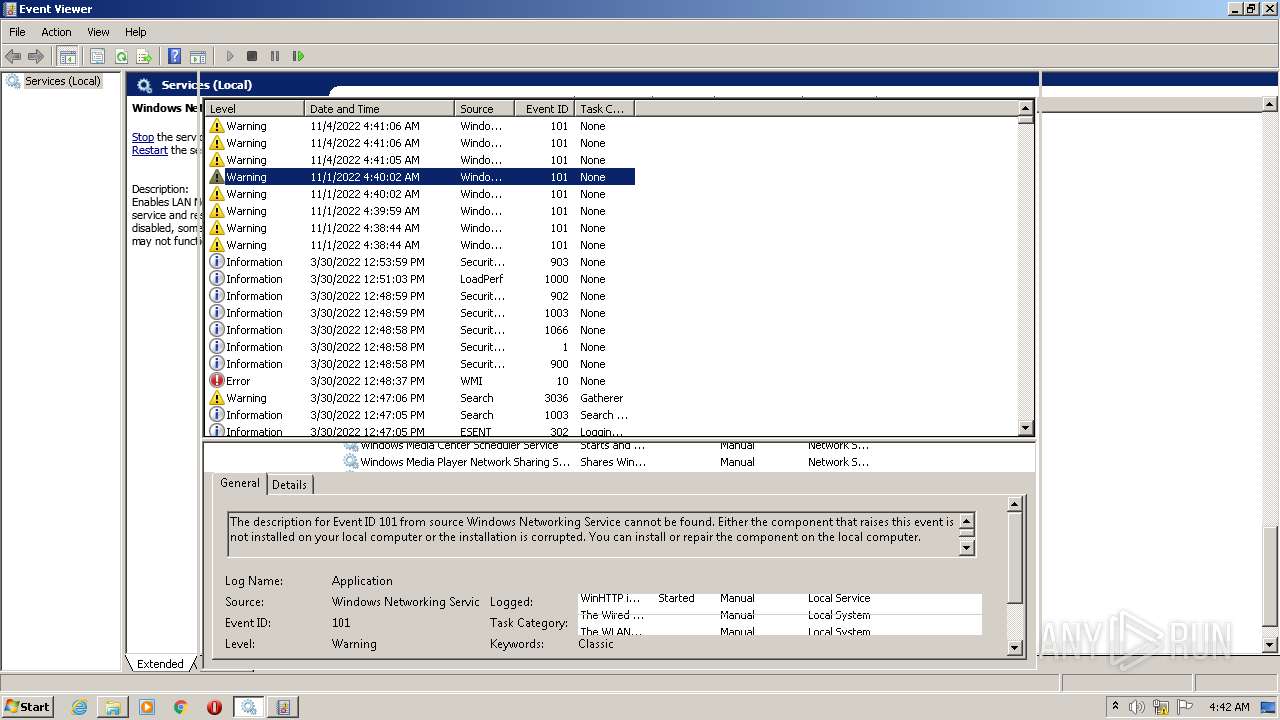
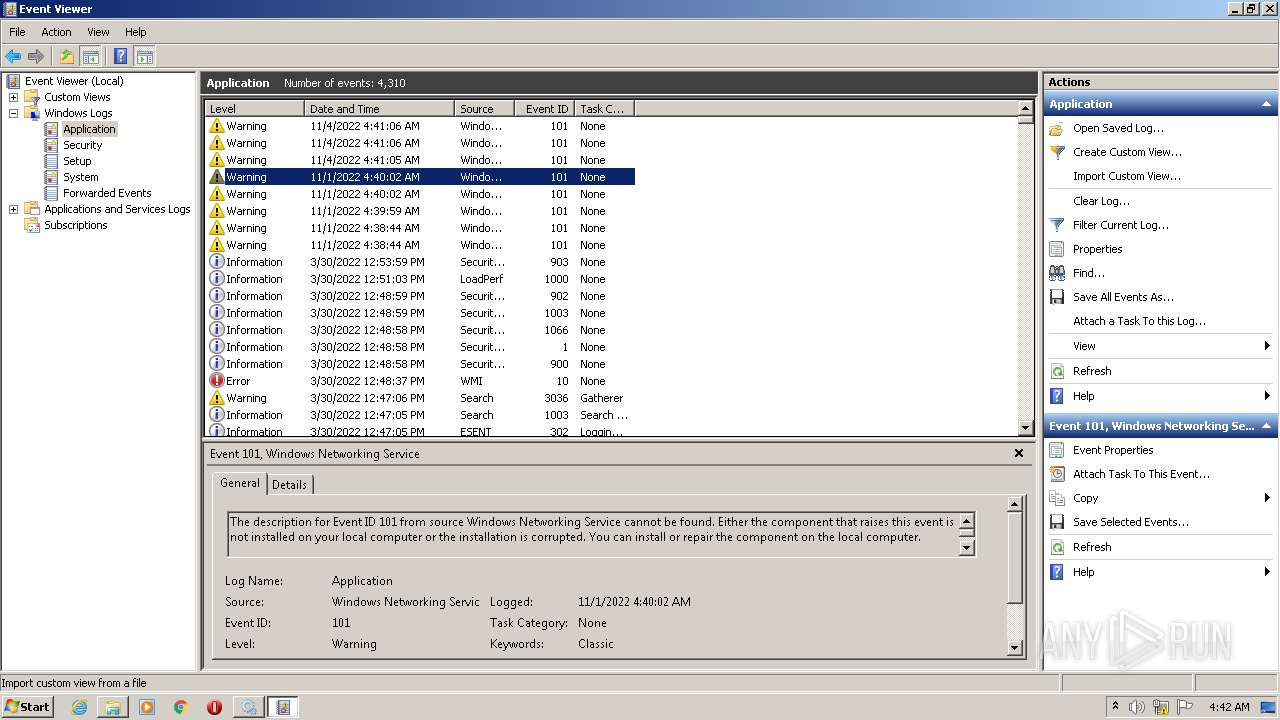
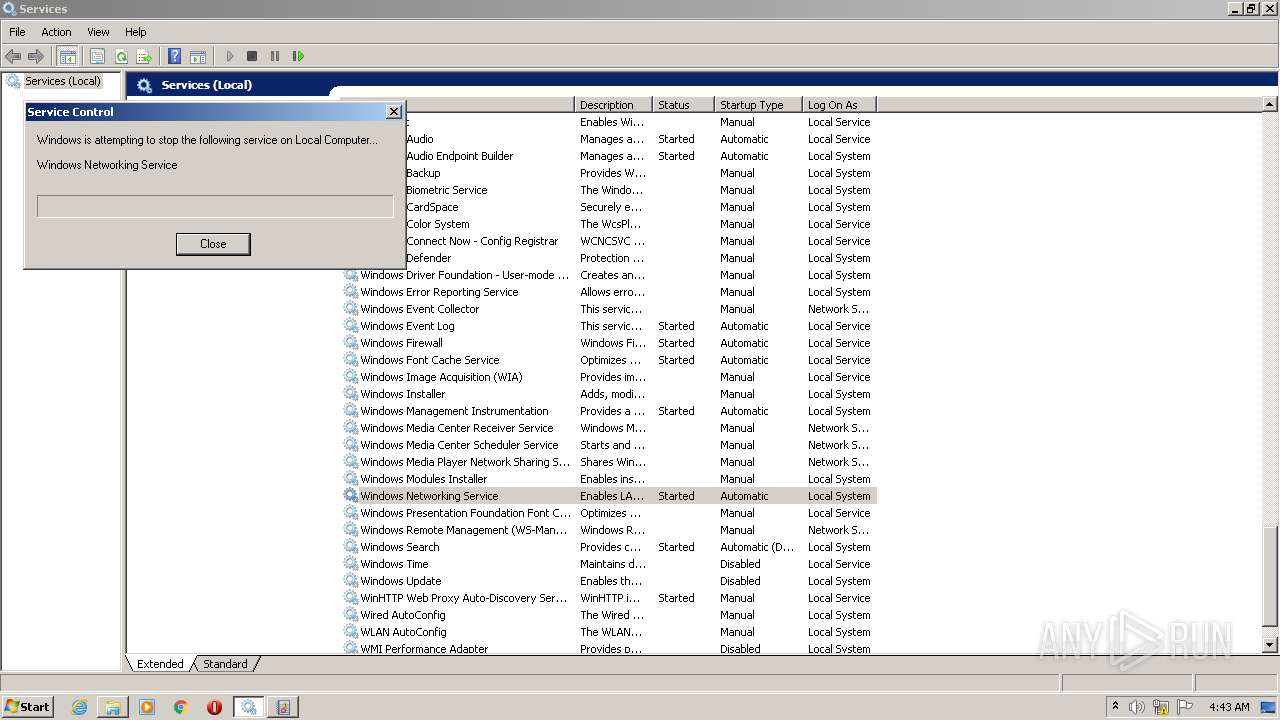
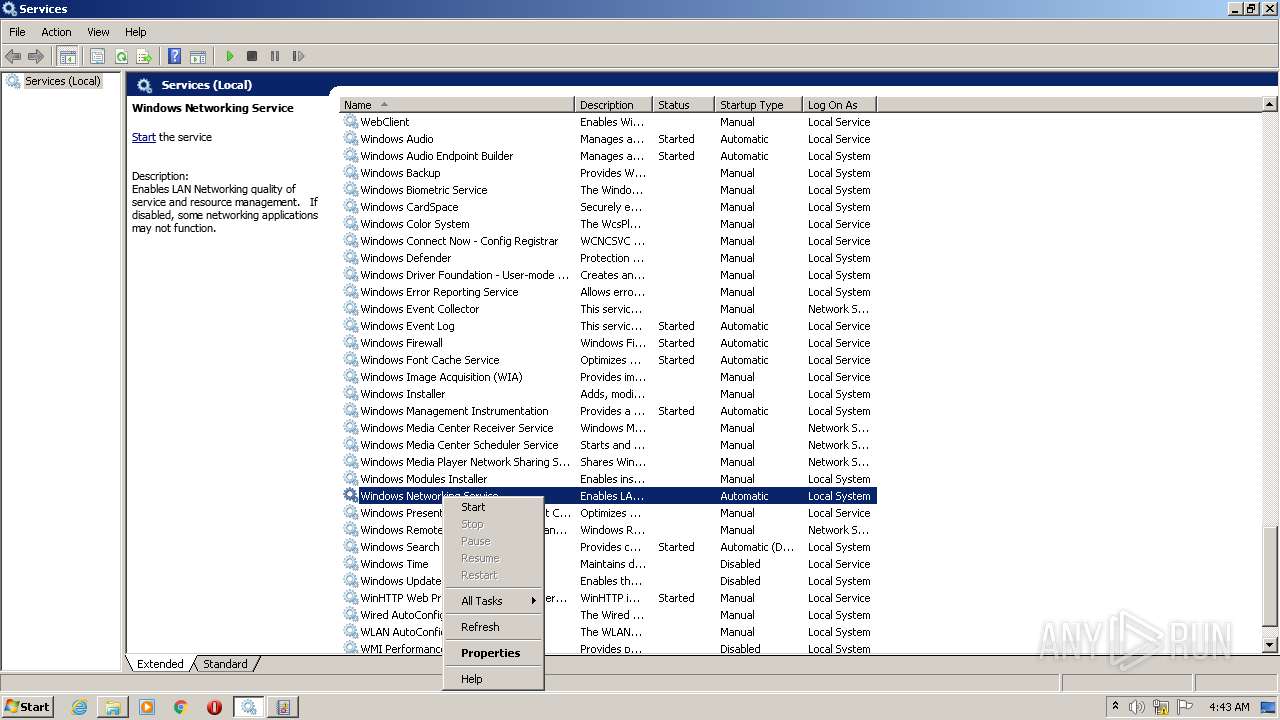
Starts NET.EXE for service management
- nsF53D.tmp (PID: 3272)
Drops the executable file immediately after the start
- windowsnetservicehelper-1.1.21bt2.exe.NULL.exe (PID: 336)
Application was dropped or rewritten from another process
- windowsnetservicehelper.exe (PID: 3972)
- windowsnetservicehelper.exe (PID: 3556)
- windowsnetservicehelper.exe (PID: 3472)
- node.exe (PID: 2412)
- windowsnetservicehelper.exe (PID: 3672)
- node.exe (PID: 3484)
Loads dropped or rewritten executable
- windowsnetservicehelper-1.1.21bt2.exe.NULL.exe (PID: 336)
SUSPICIOUS
Starts application with an unusual extension
- windowsnetservicehelper-1.1.21bt2.exe.NULL.exe (PID: 336)
Uses TASKKILL.EXE to kill process
- nsF5BB.tmp (PID: 2888)
Executable content was dropped or overwritten
- windowsnetservicehelper-1.1.21bt2.exe.NULL.exe (PID: 336)
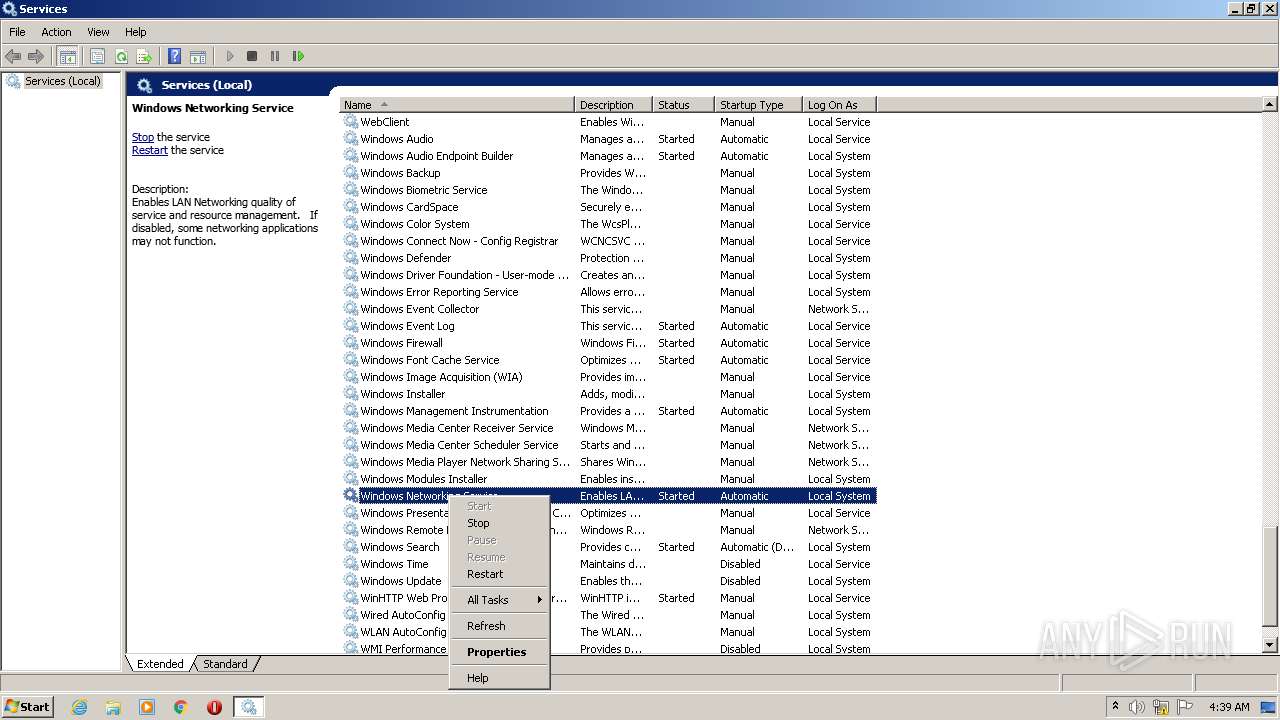
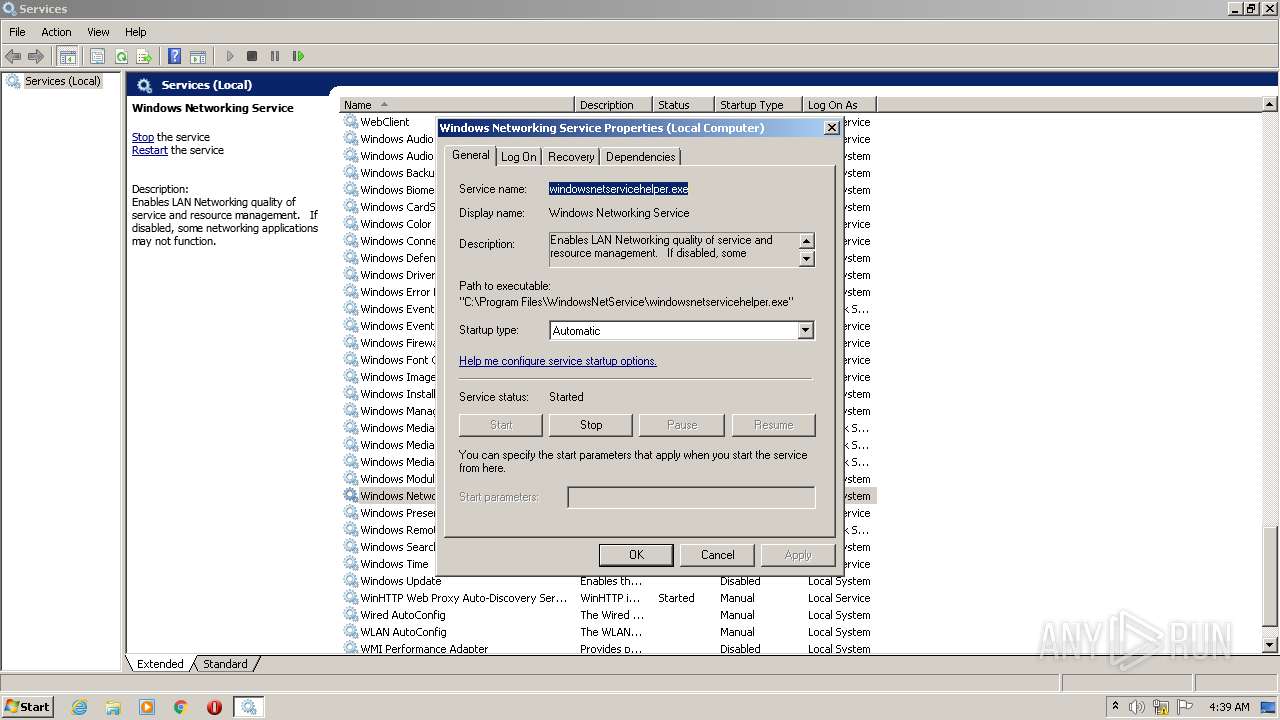
Starts SC.EXE for service management
- nsF697.tmp (PID: 3380)
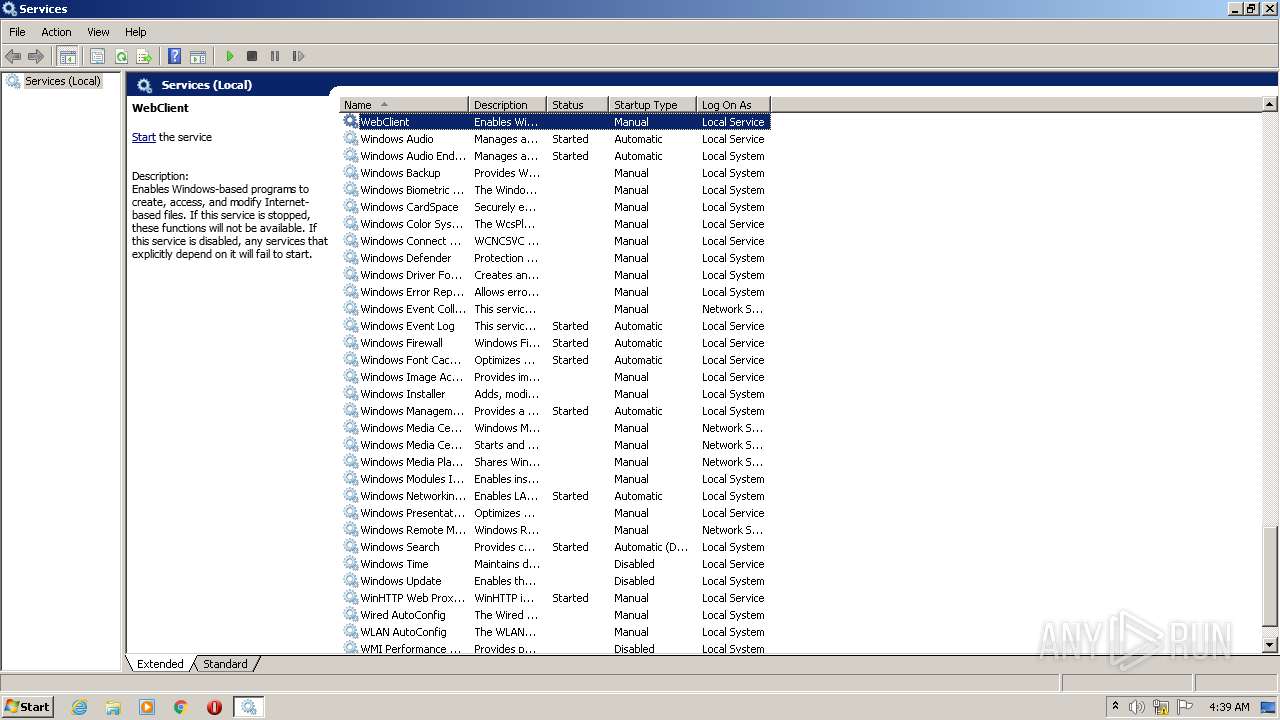
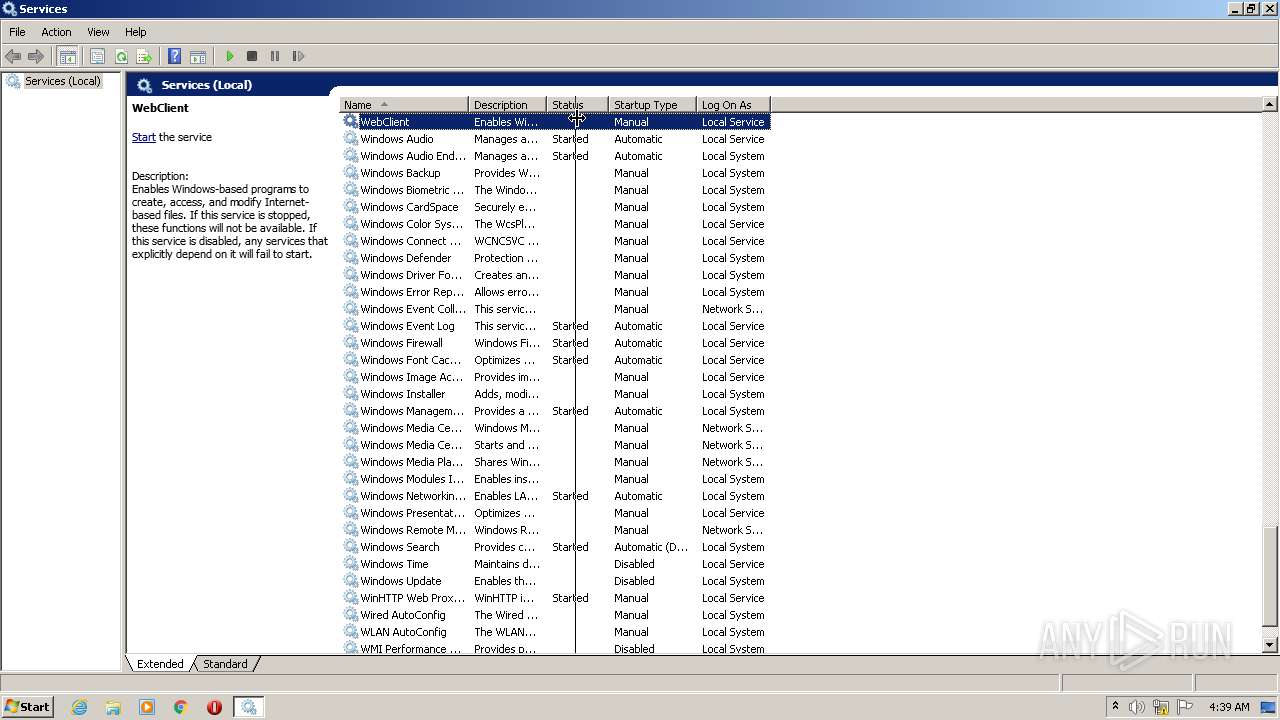
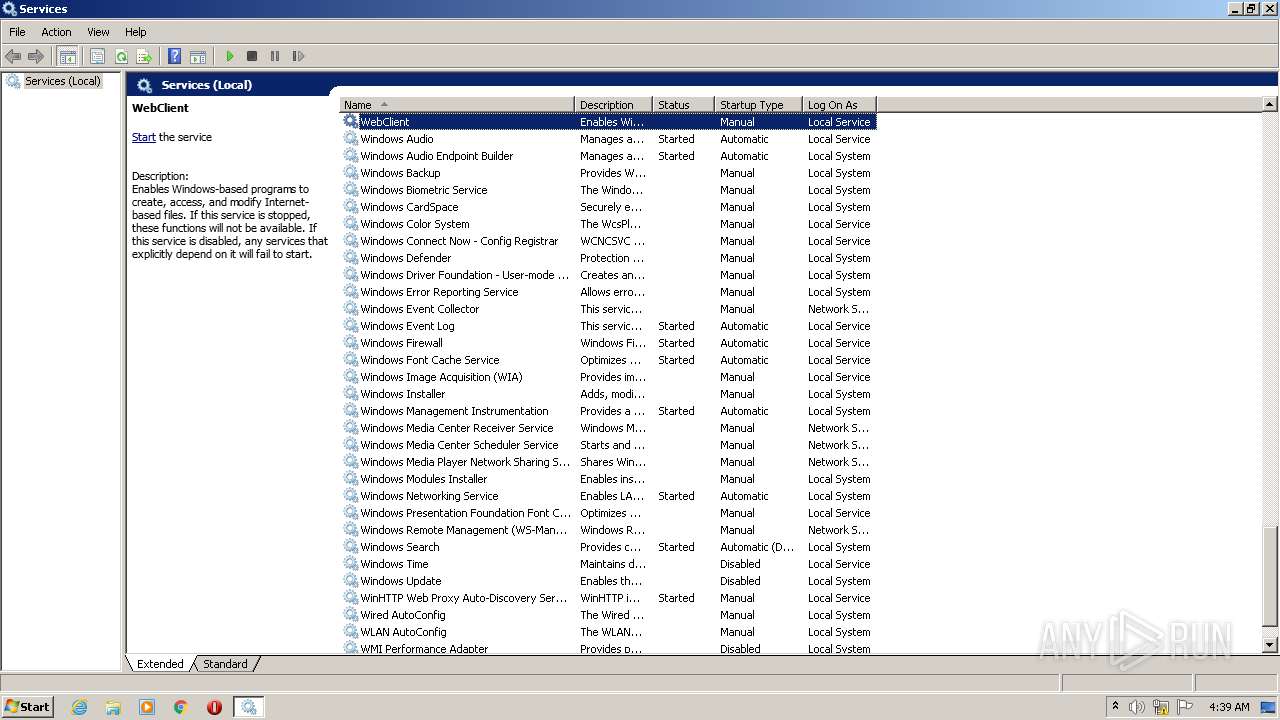
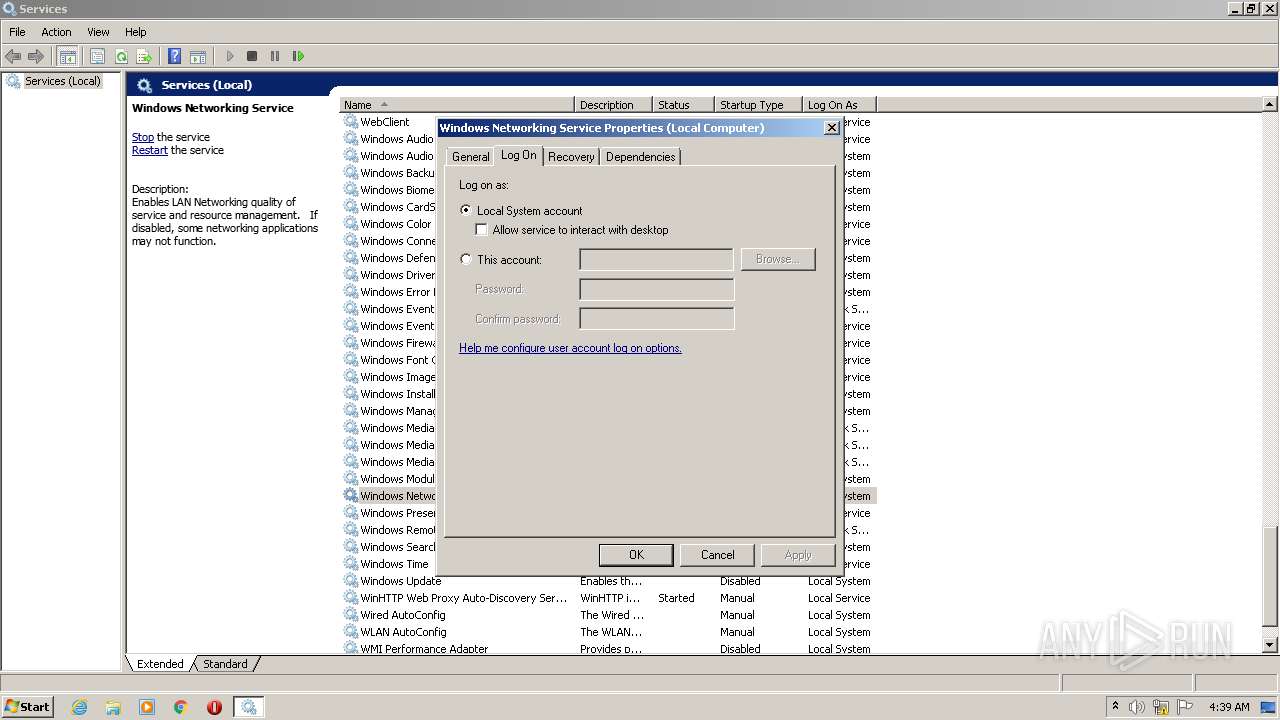
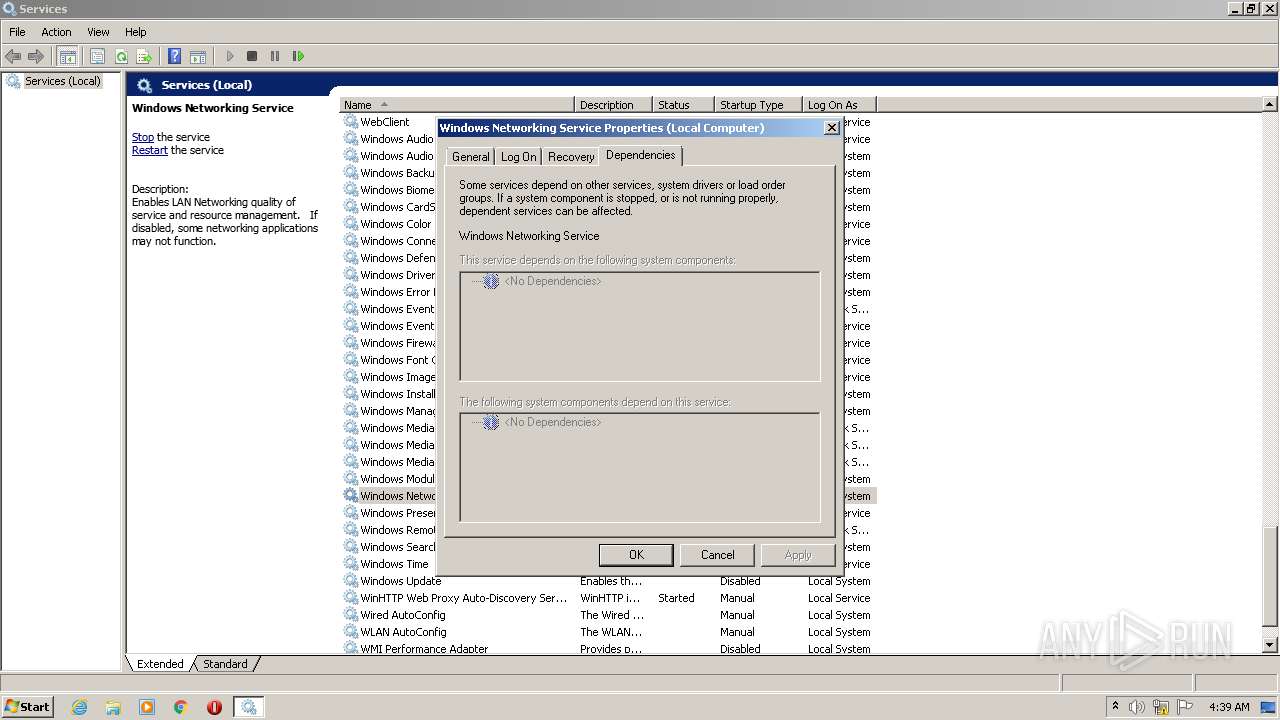
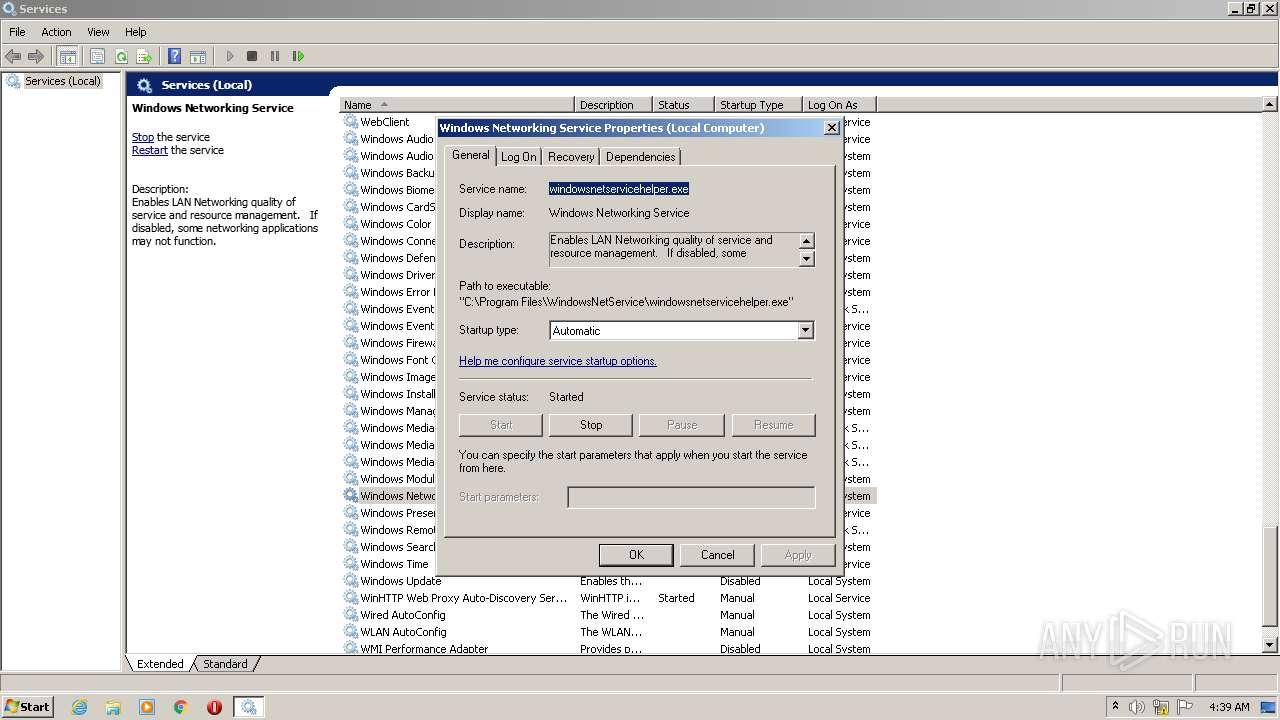
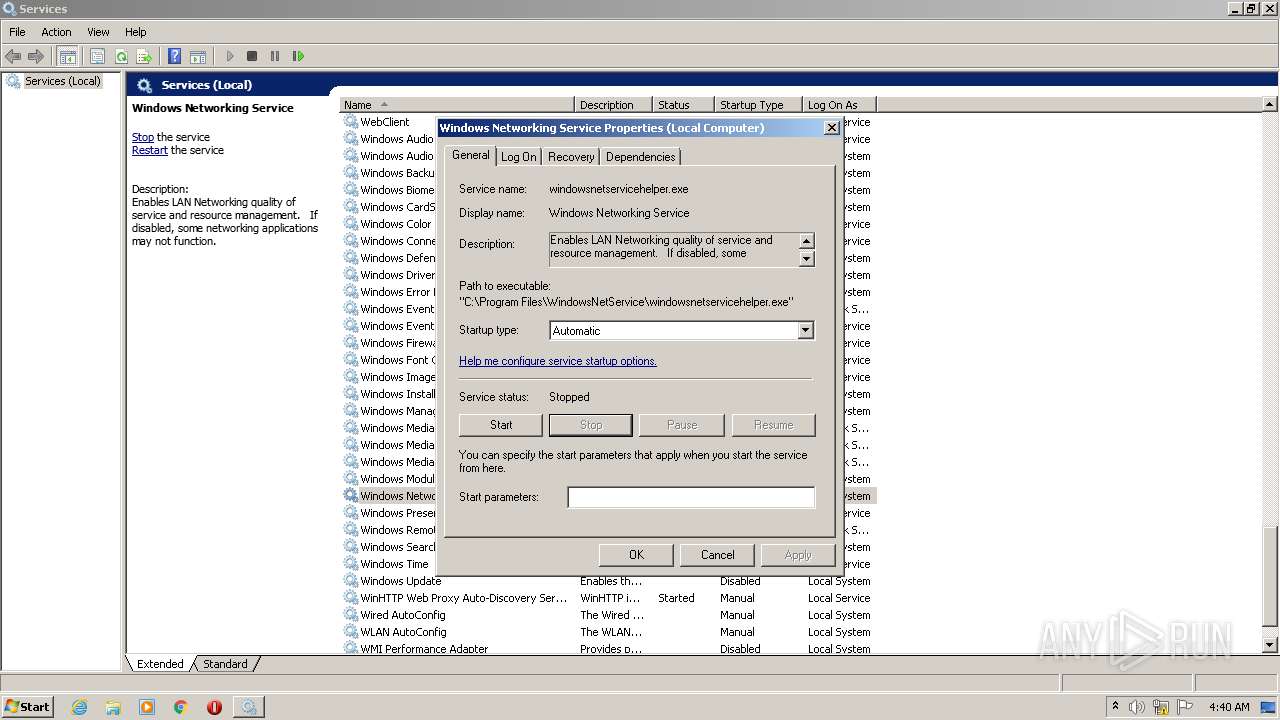
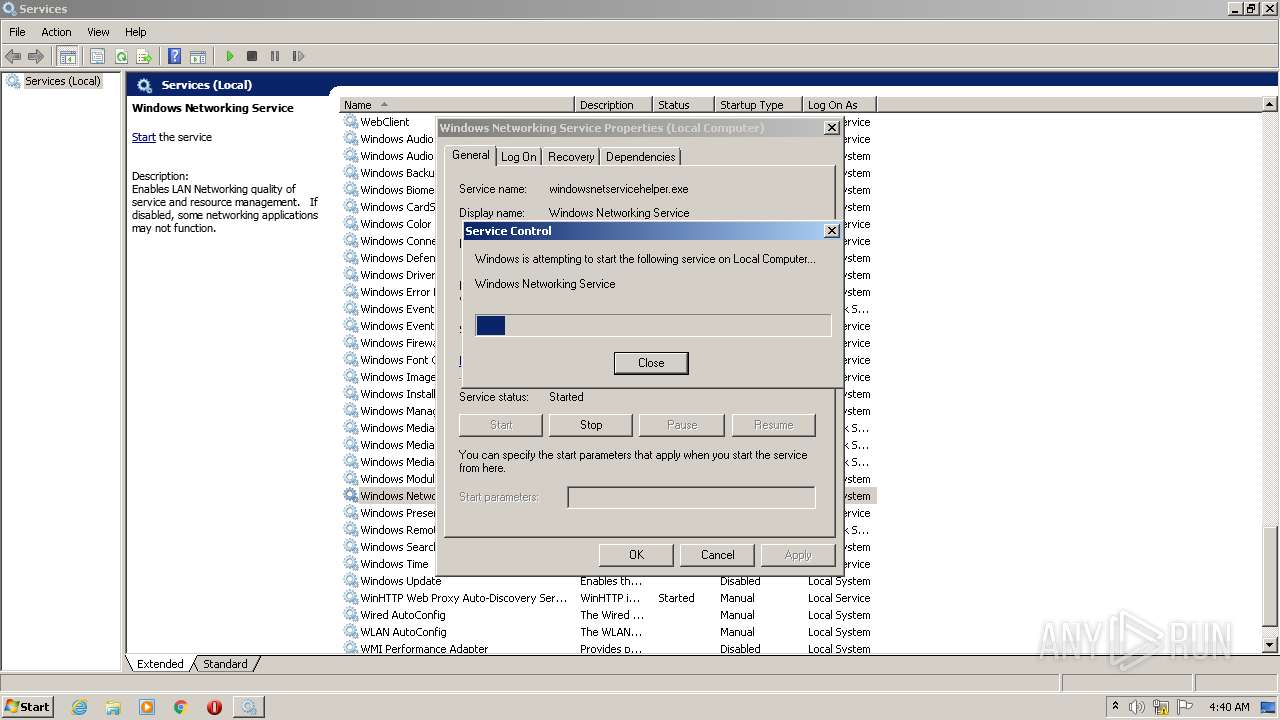
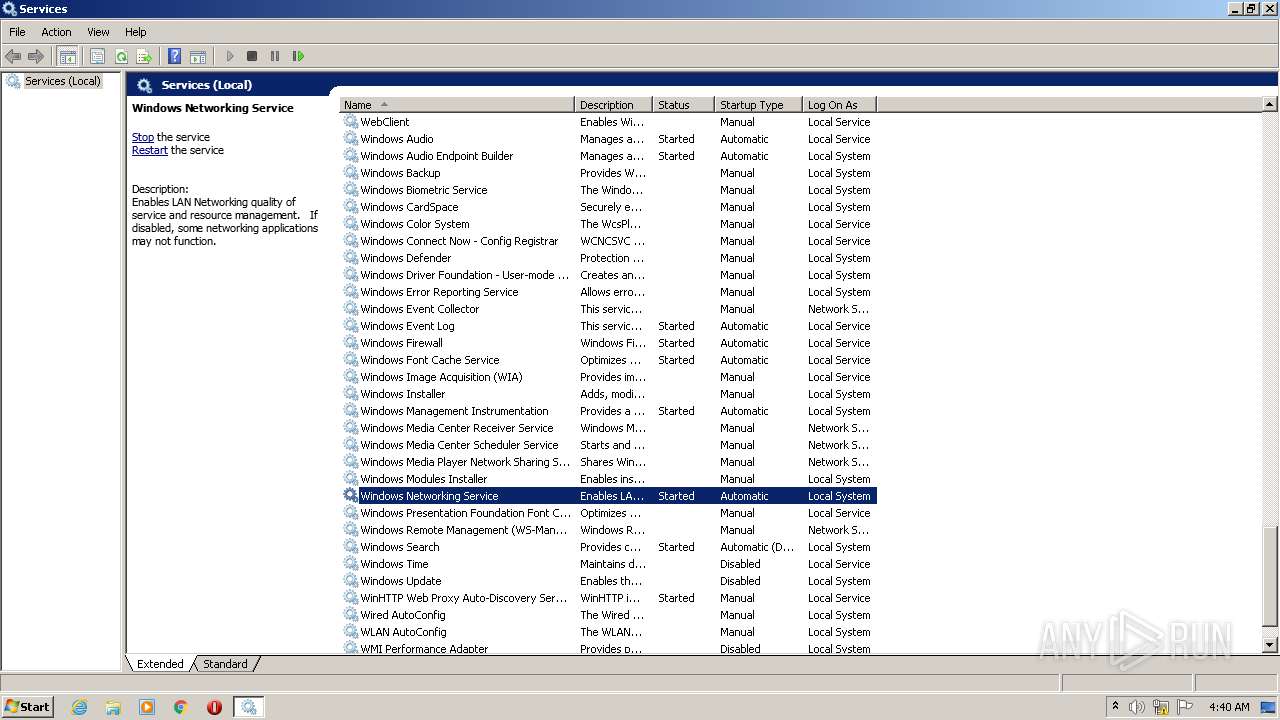
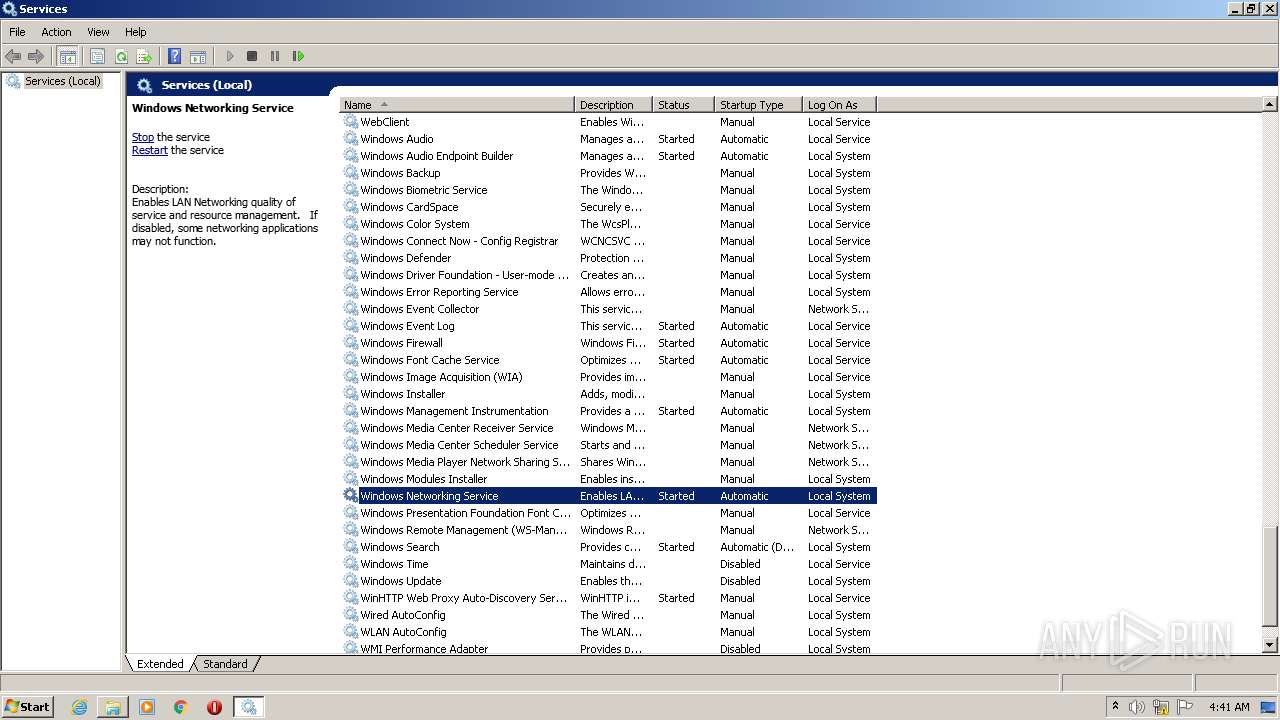
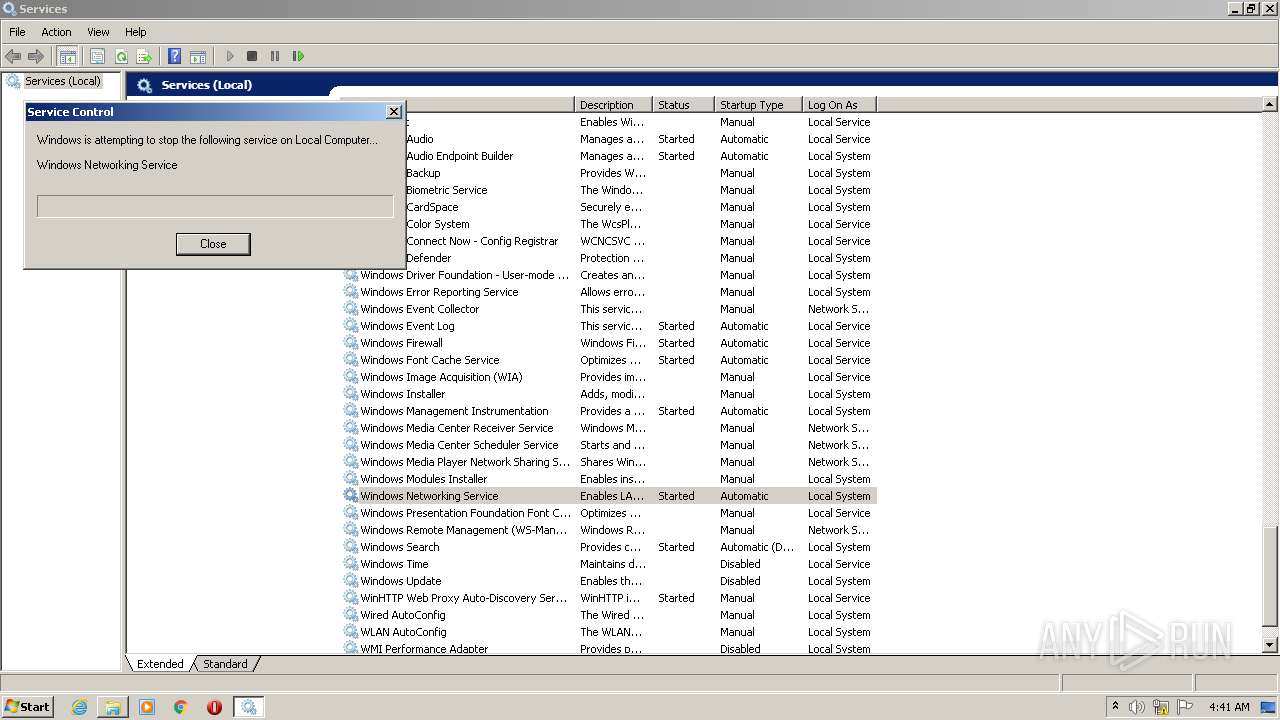
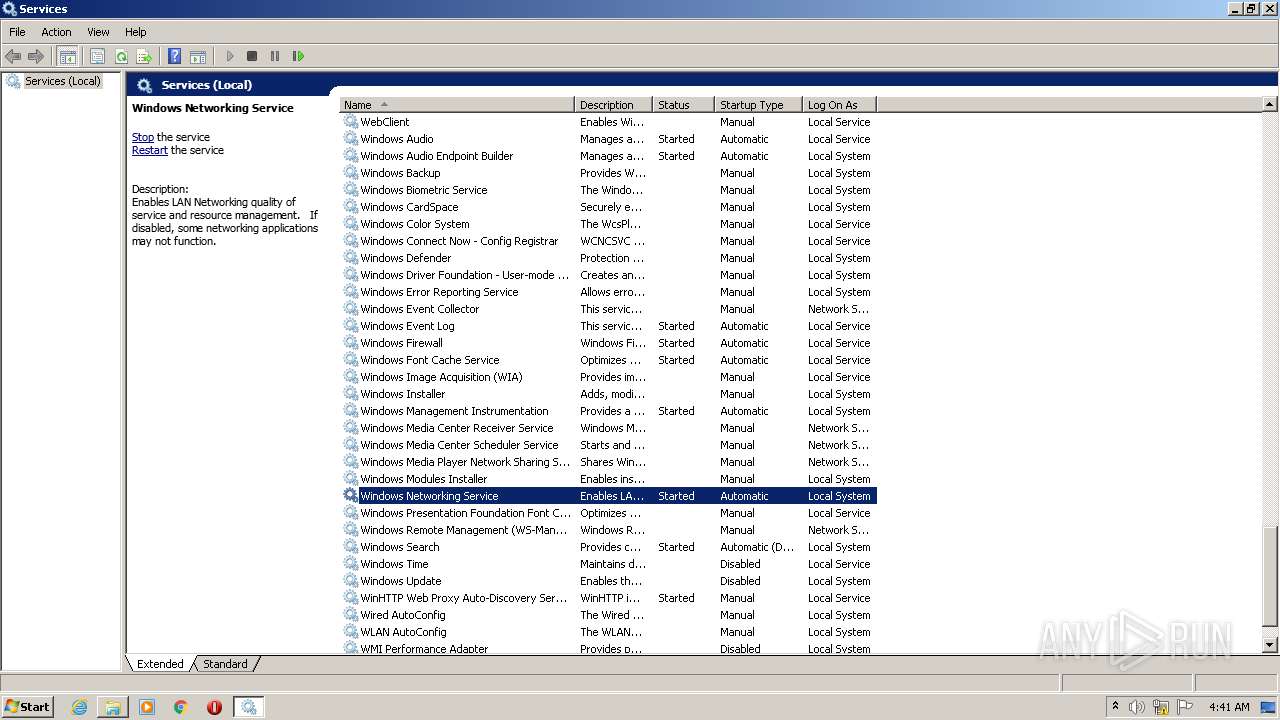
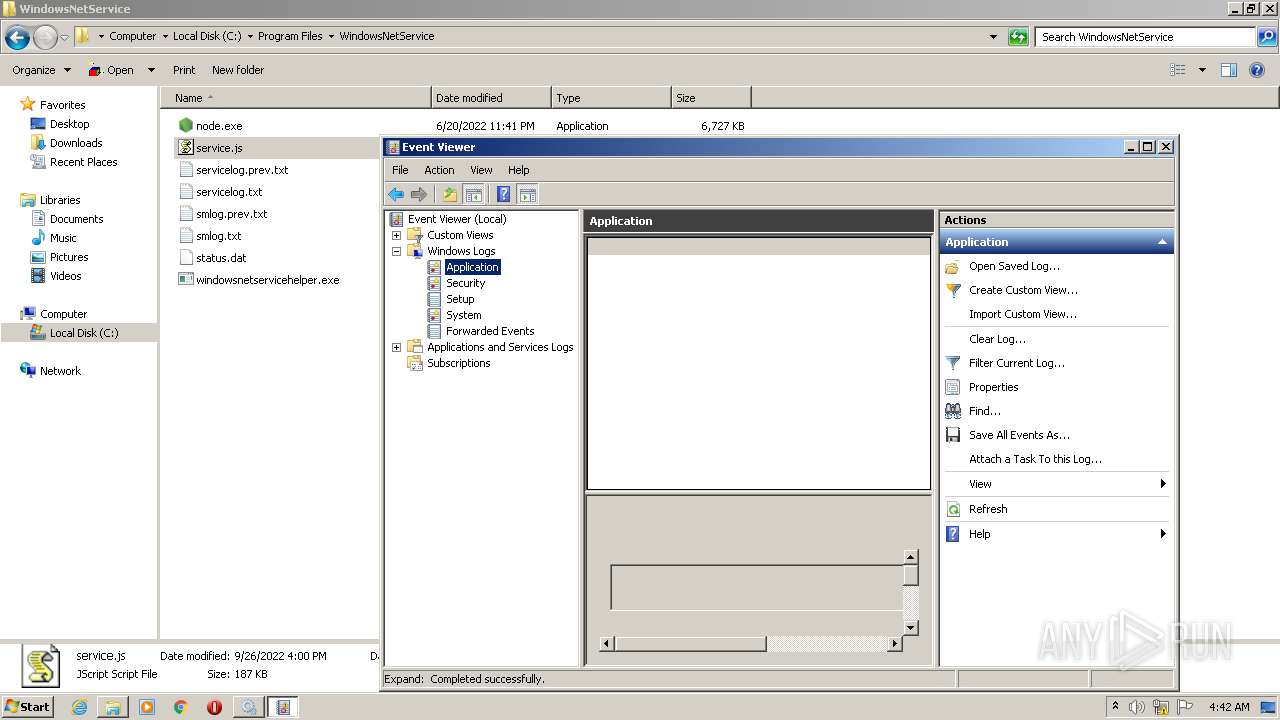
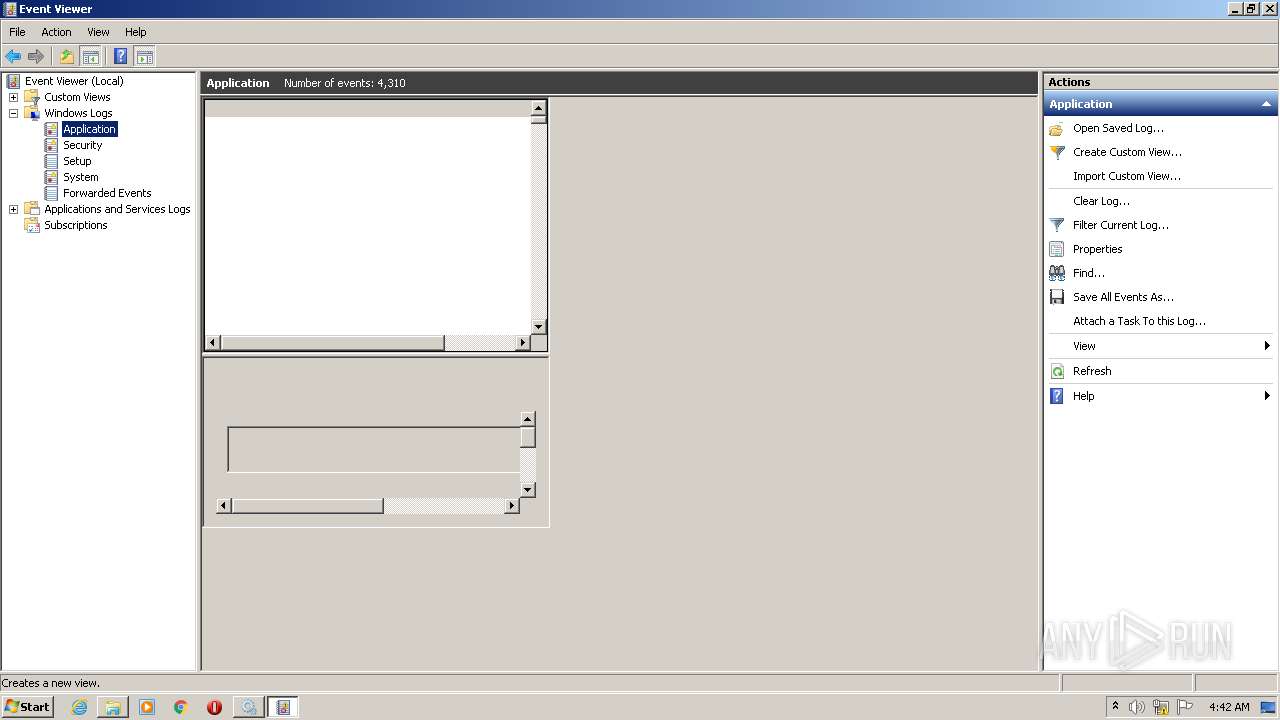
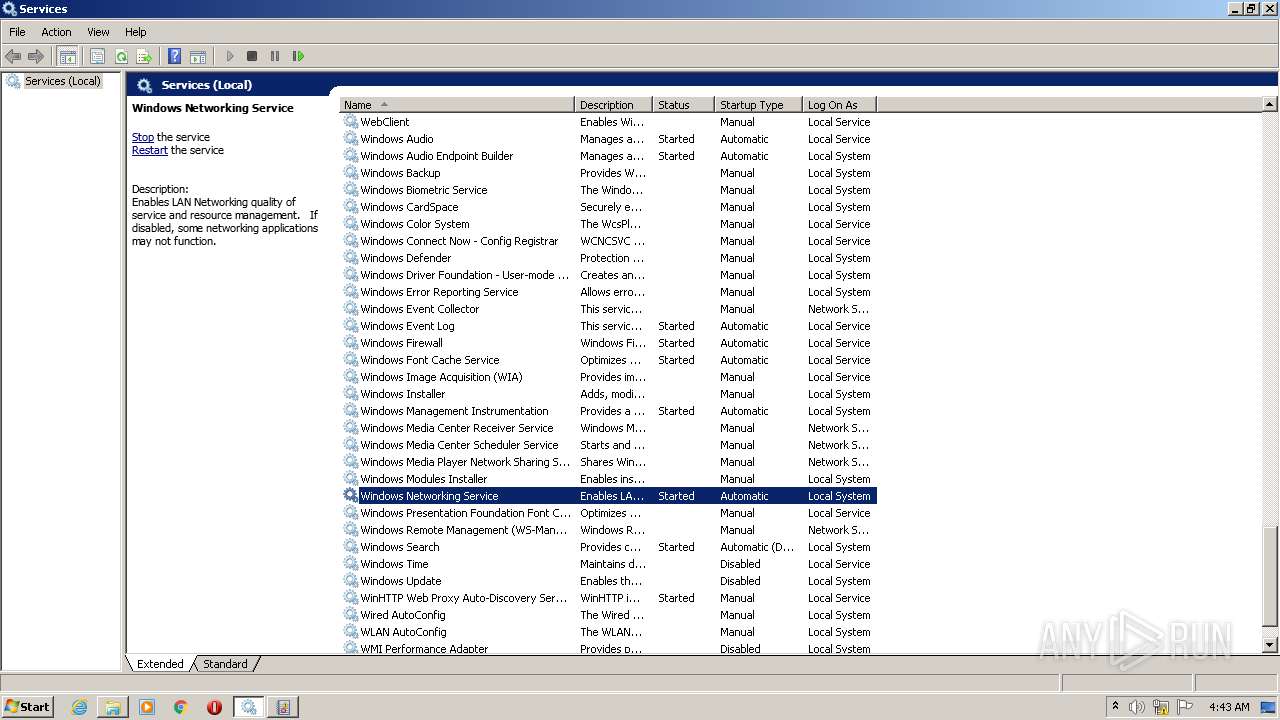
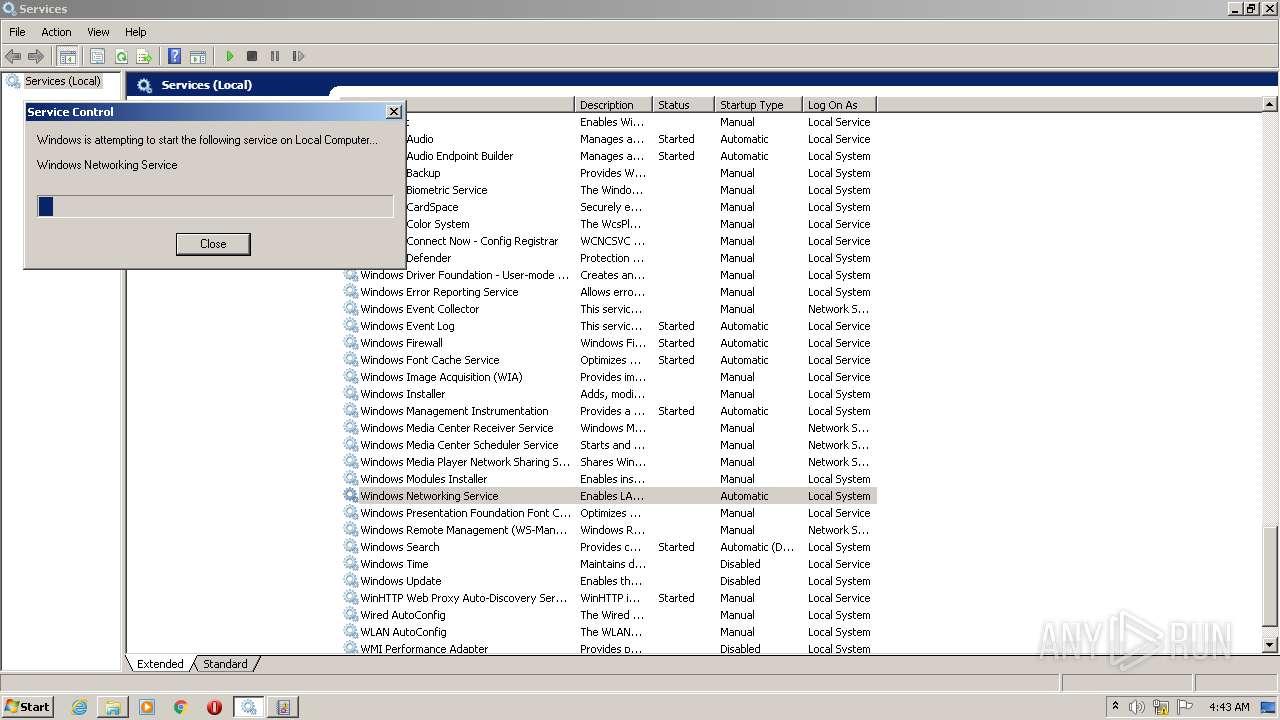
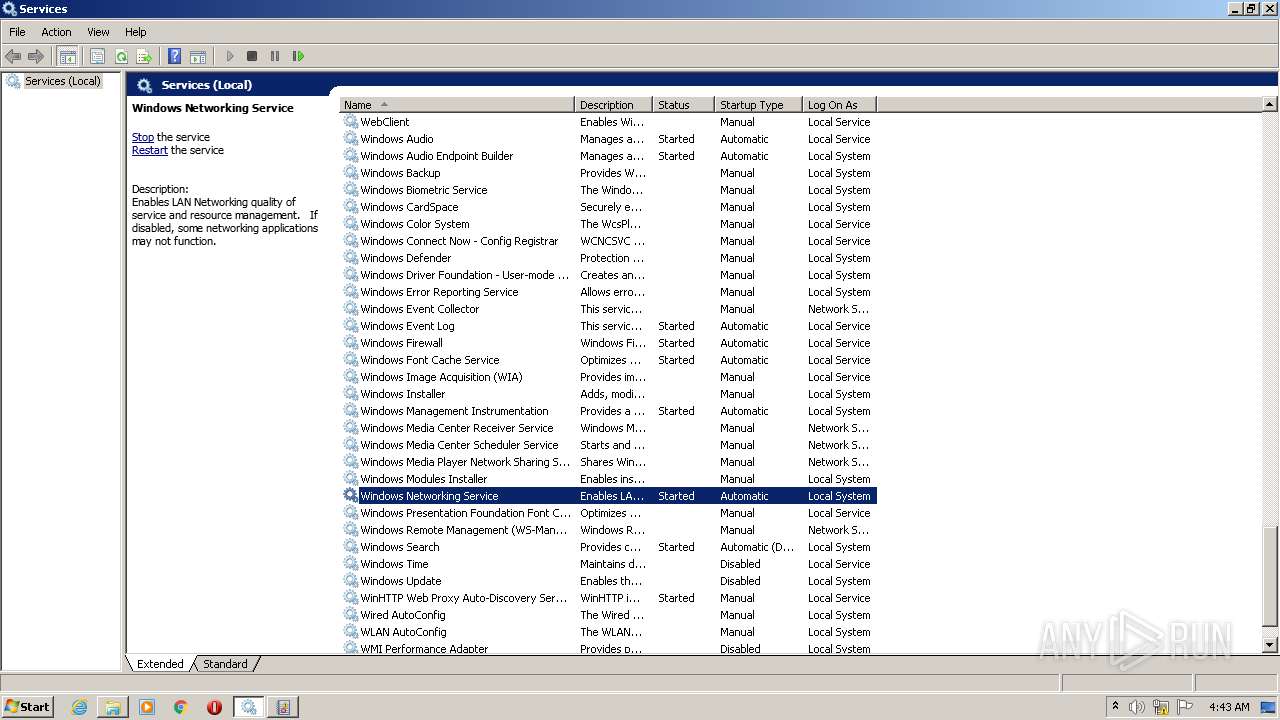
Executes as Windows Service
- windowsnetservicehelper.exe (PID: 3972)
- windowsnetservicehelper.exe (PID: 3672)
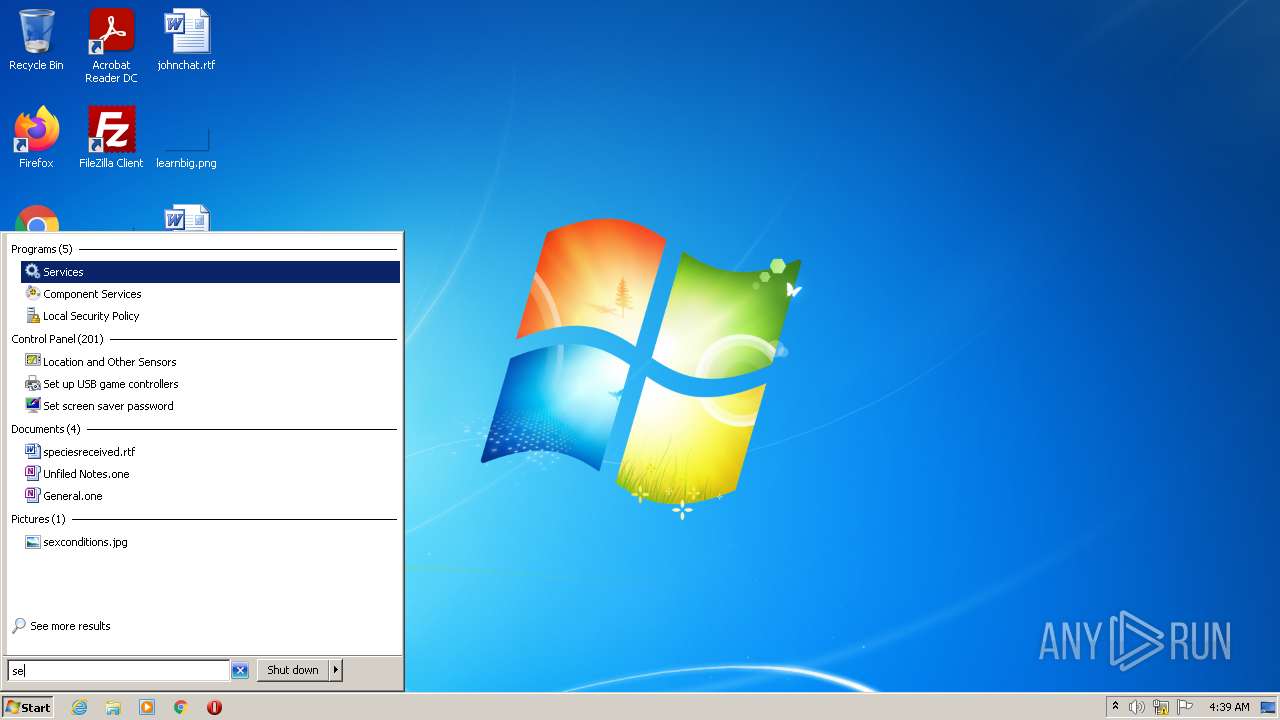
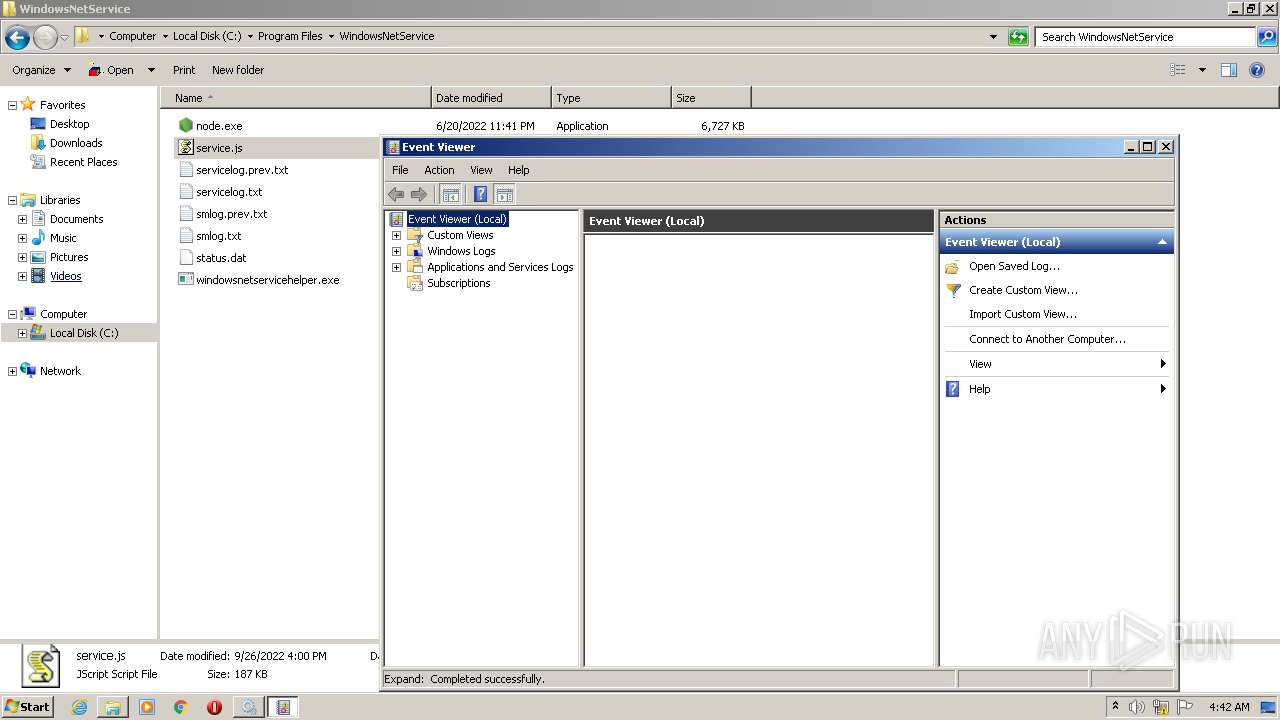
Reads Microsoft Outlook installation path
- mmc.exe (PID: 3592)
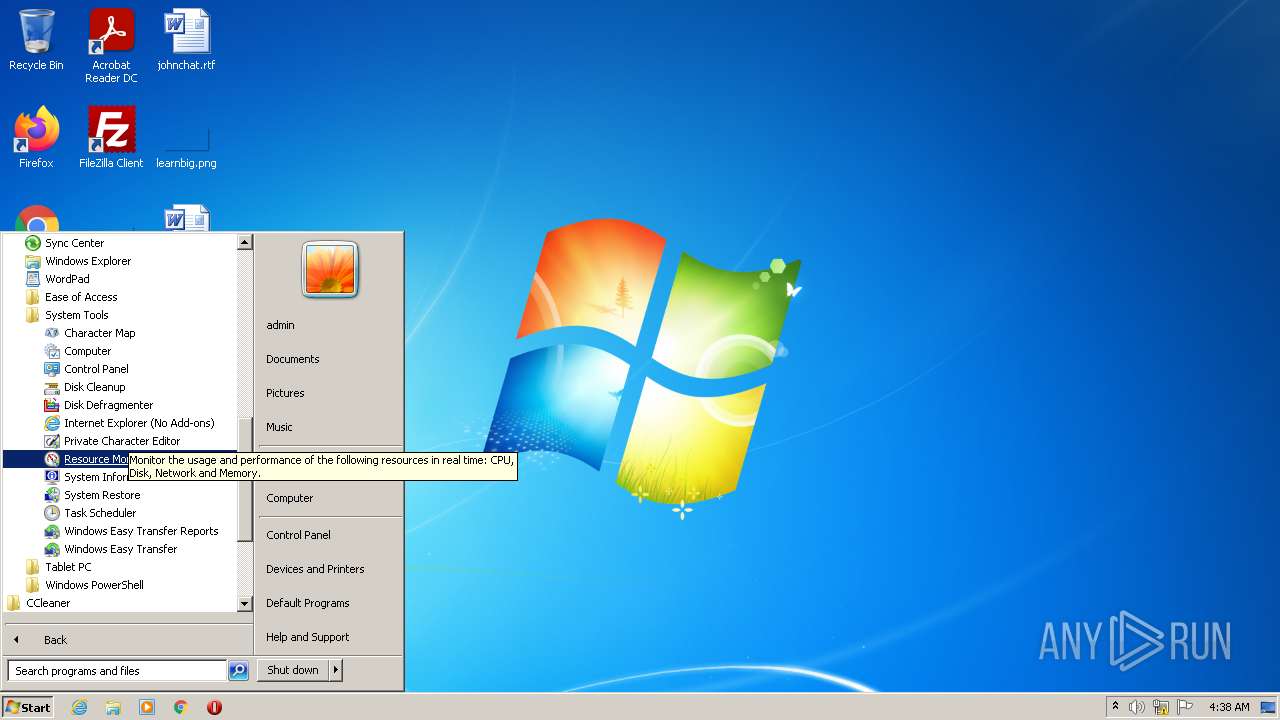
Uses WMIC.EXE to obtain a system information
- node.exe (PID: 2412)
- node.exe (PID: 3484)
Reads Internet Explorer settings
- mmc.exe (PID: 3592)
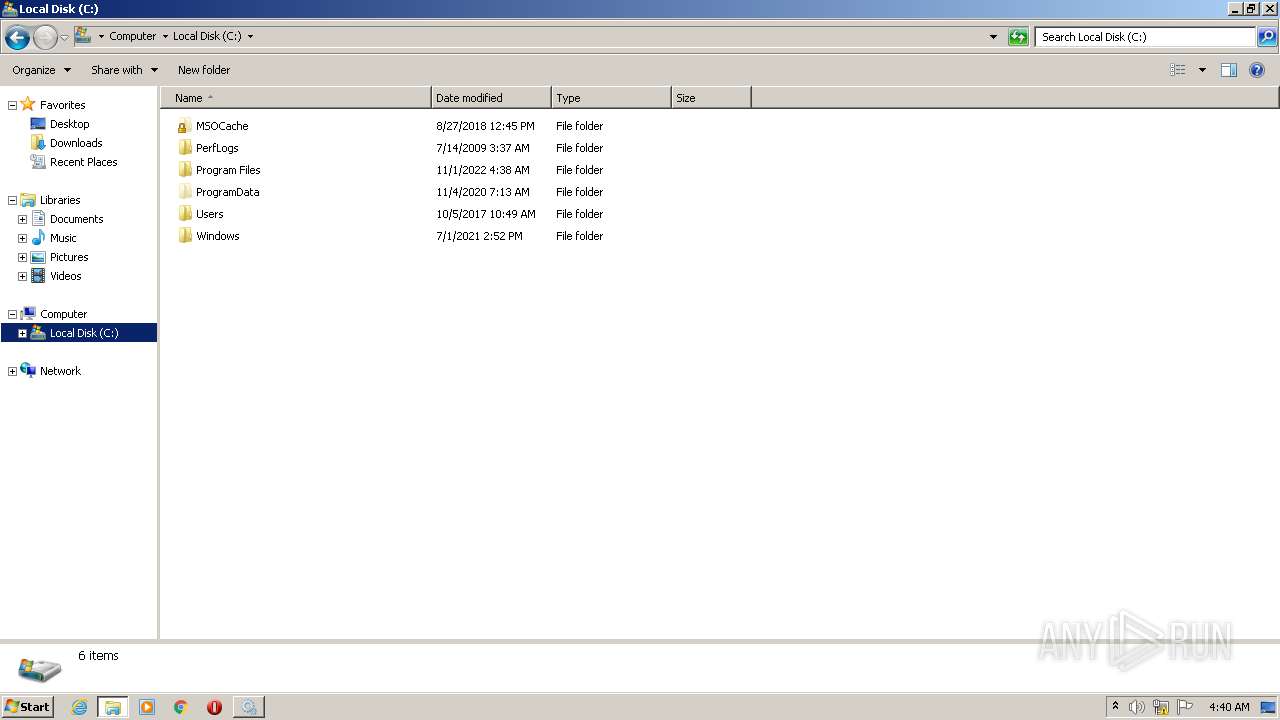
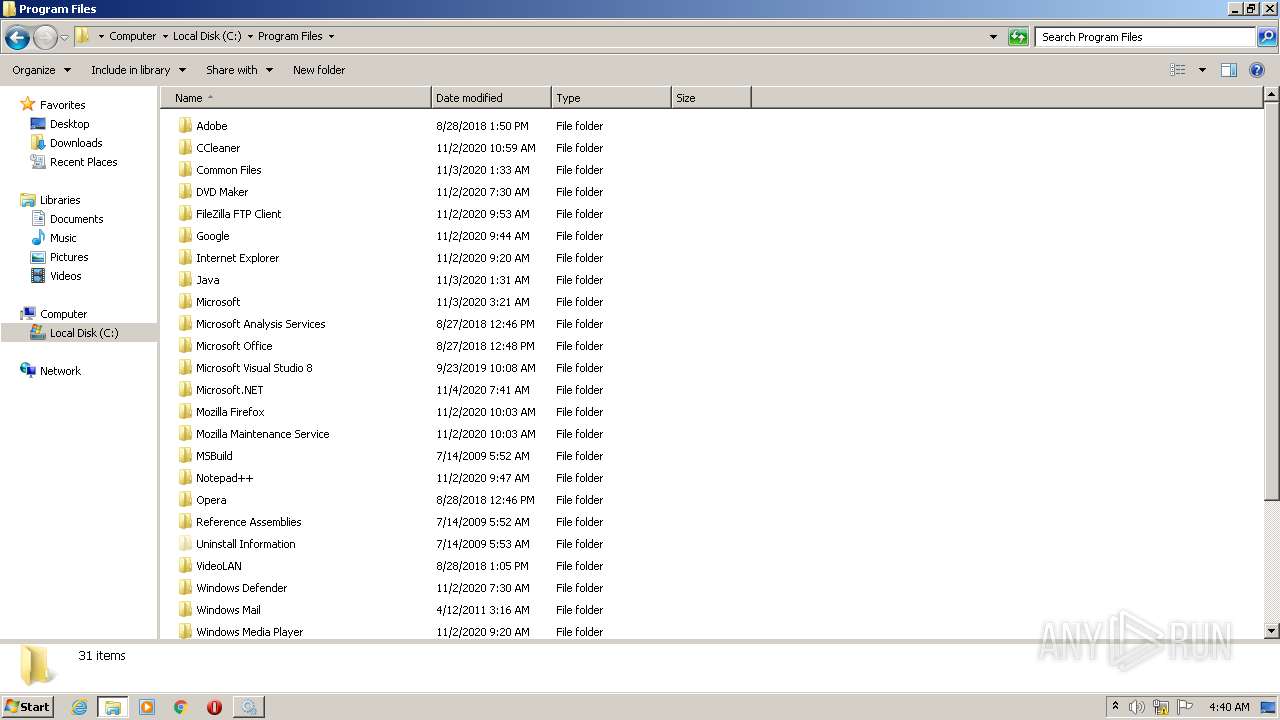
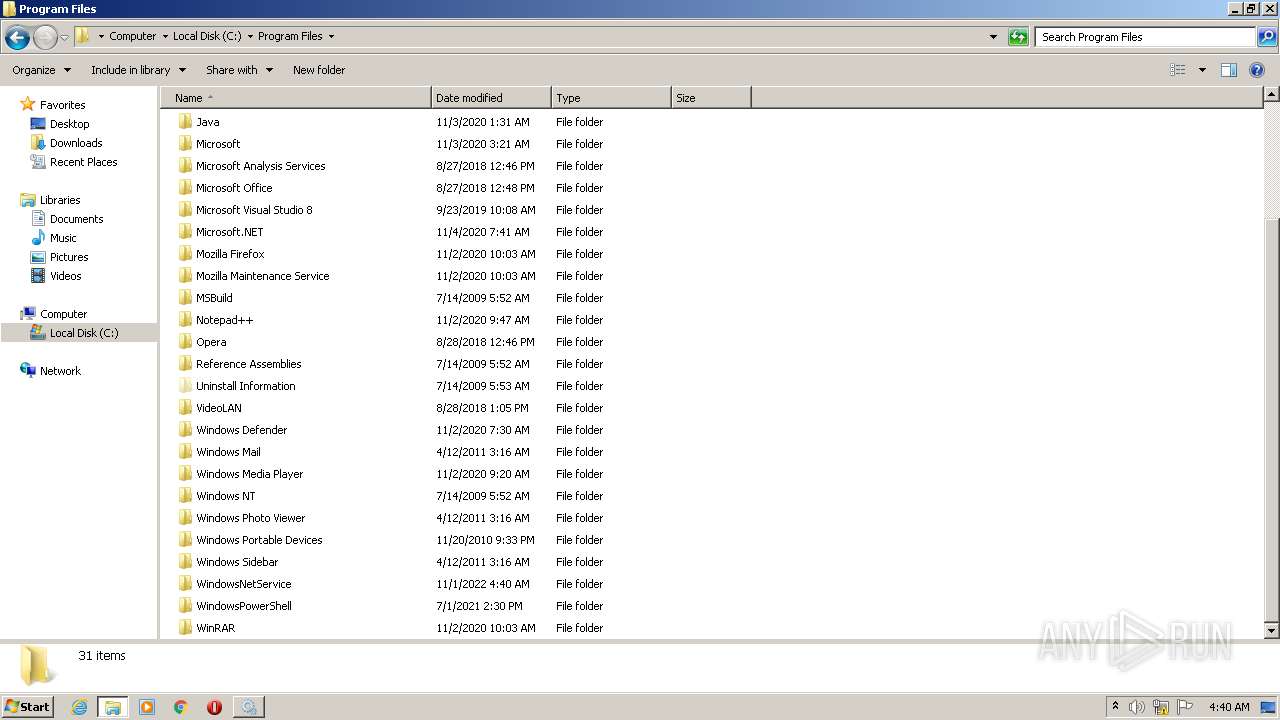
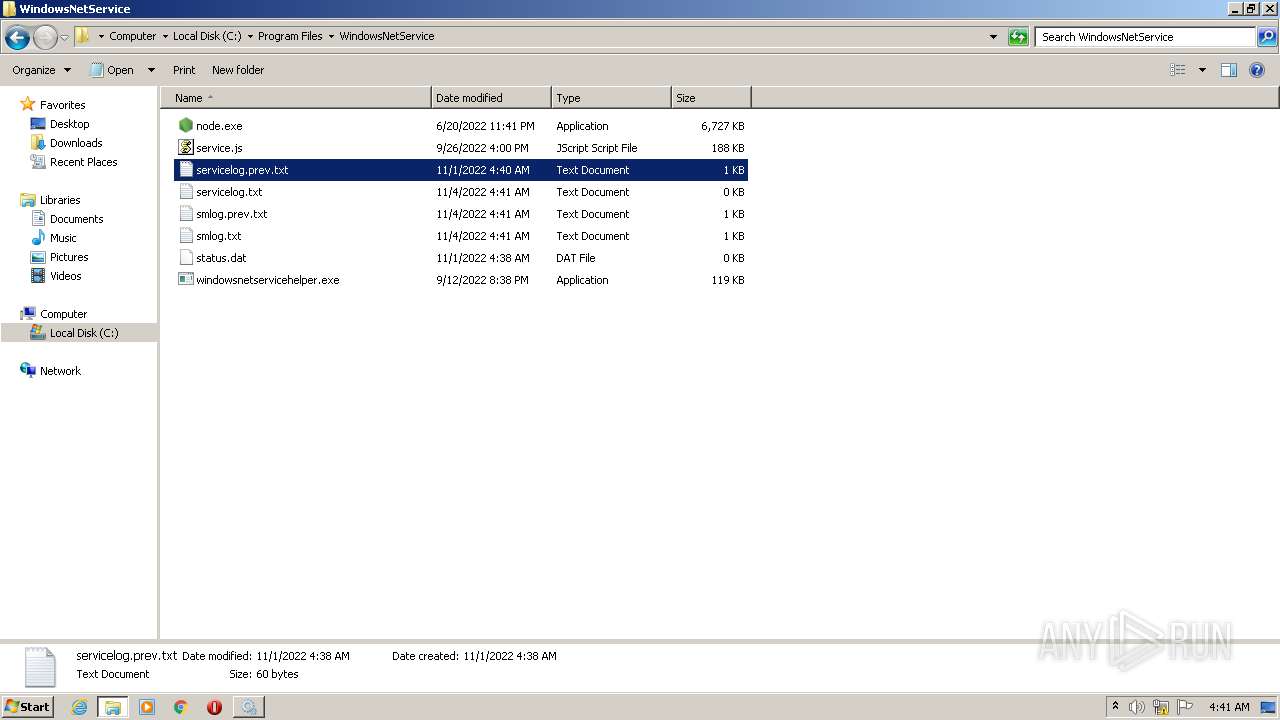
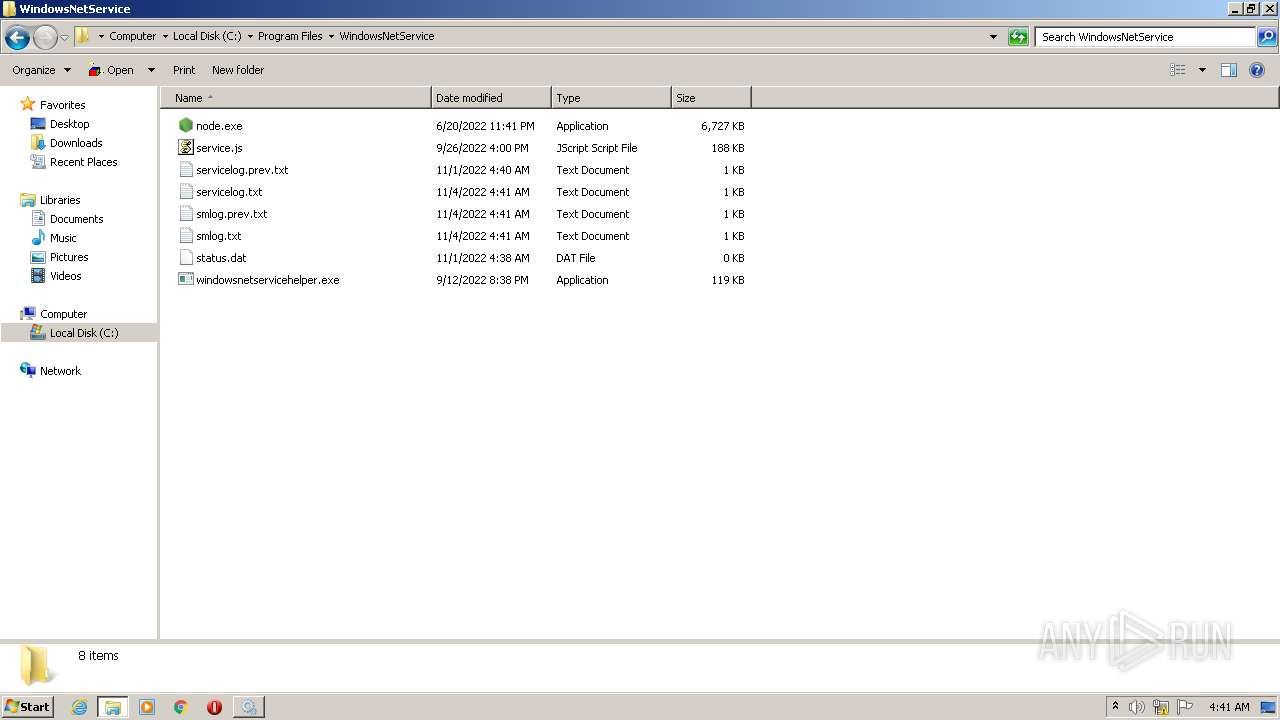
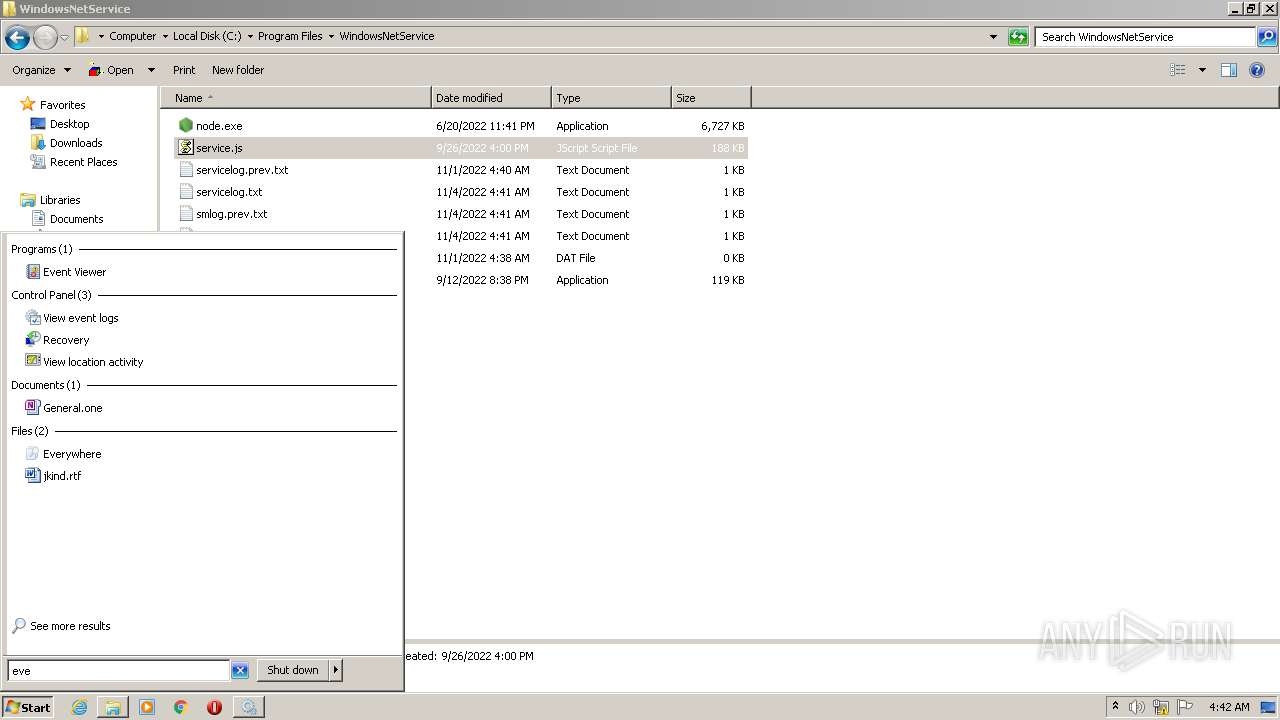
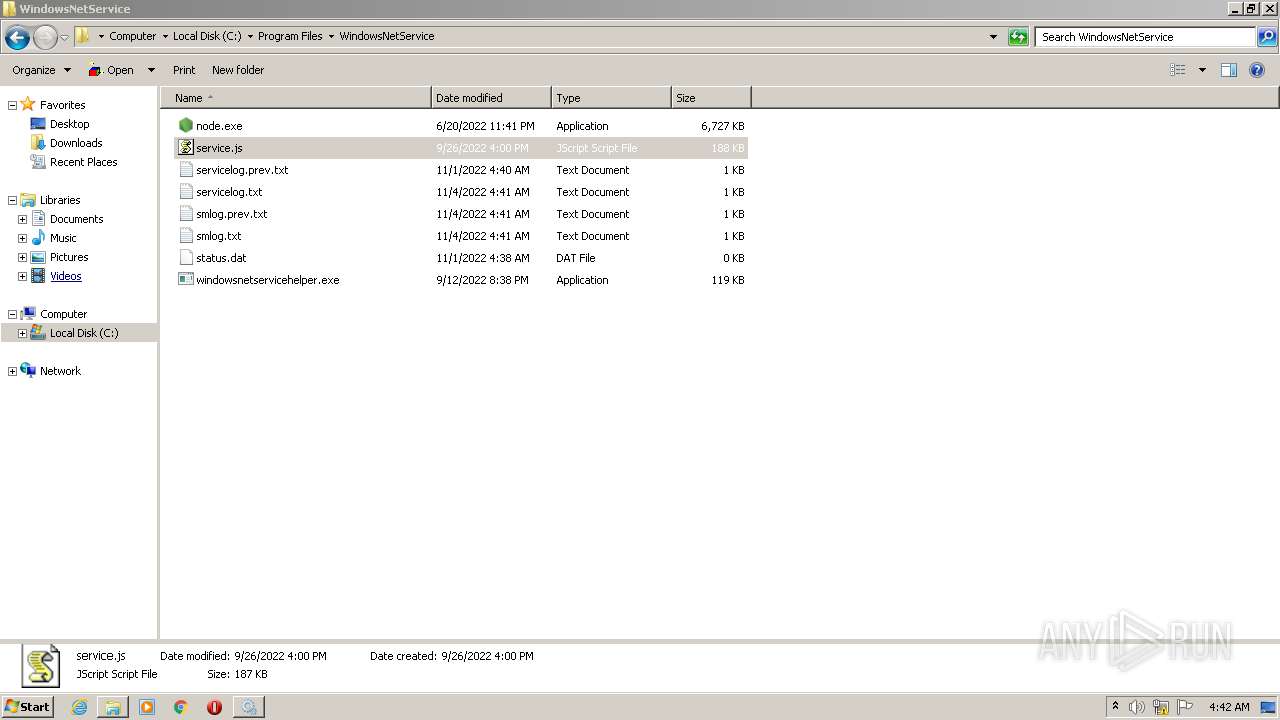
Creates a directory in Program Files
- windowsnetservicehelper-1.1.21bt2.exe.NULL.exe (PID: 336)
INFO
Process checks LSA protection
- windowsnetservicehelper-1.1.21bt2.exe.NULL.exe (PID: 336)
- node.exe (PID: 2412)
- node.exe (PID: 3484)
Reads the computer name
- windowsnetservicehelper-1.1.21bt2.exe.NULL.exe (PID: 336)
- windowsnetservicehelper.exe (PID: 3556)
- windowsnetservicehelper.exe (PID: 3972)
- node.exe (PID: 2412)
- node.exe (PID: 3484)
- windowsnetservicehelper.exe (PID: 3672)
- windowsnetservicehelper.exe (PID: 3472)
Checks supported languages
- windowsnetservicehelper-1.1.21bt2.exe.NULL.exe (PID: 336)
- nsF5BB.tmp (PID: 2888)
- windowsnetservicehelper.exe (PID: 3472)
- nsF53D.tmp (PID: 3272)
- nsF697.tmp (PID: 3380)
- nsFE78.tmp (PID: 3700)
- nsFEE6.tmp (PID: 2604)
- node.exe (PID: 2412)
- windowsnetservicehelper.exe (PID: 3556)
- windowsnetservicehelper.exe (PID: 3972)
- windowsnetservicehelper.exe (PID: 3672)
- node.exe (PID: 3484)
Creates a file in a temporary directory
- windowsnetservicehelper-1.1.21bt2.exe.NULL.exe (PID: 336)
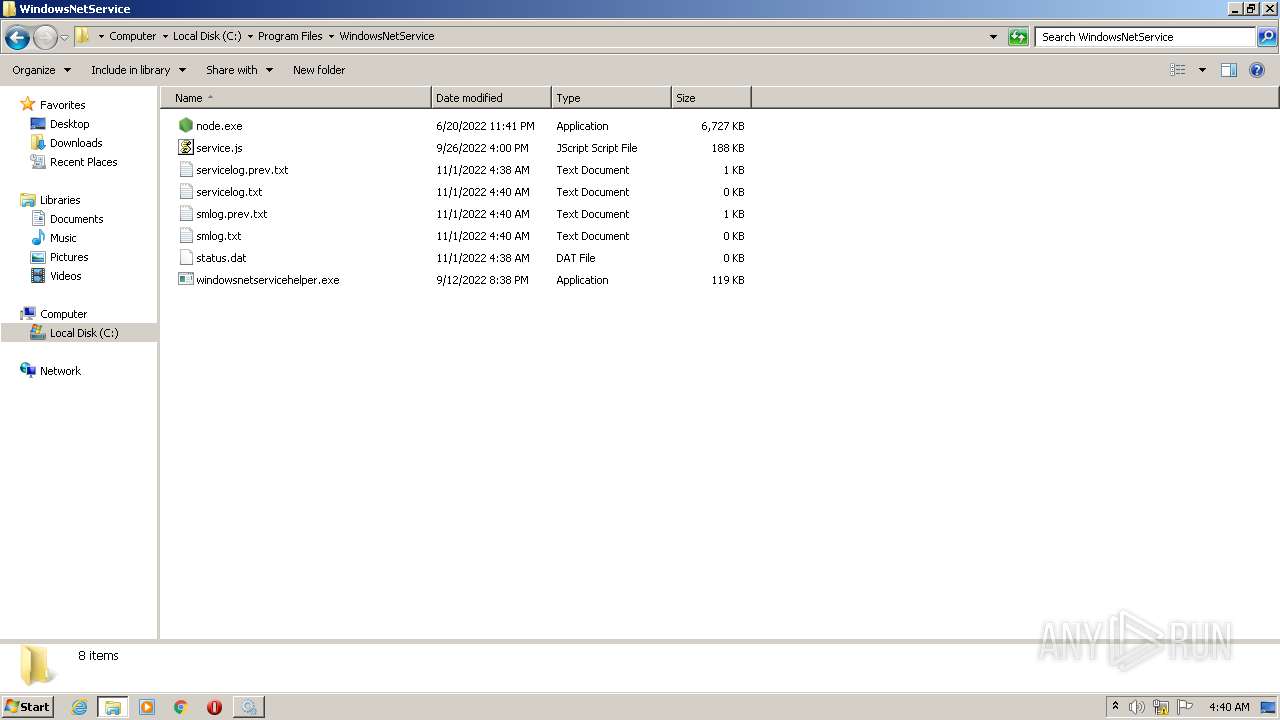
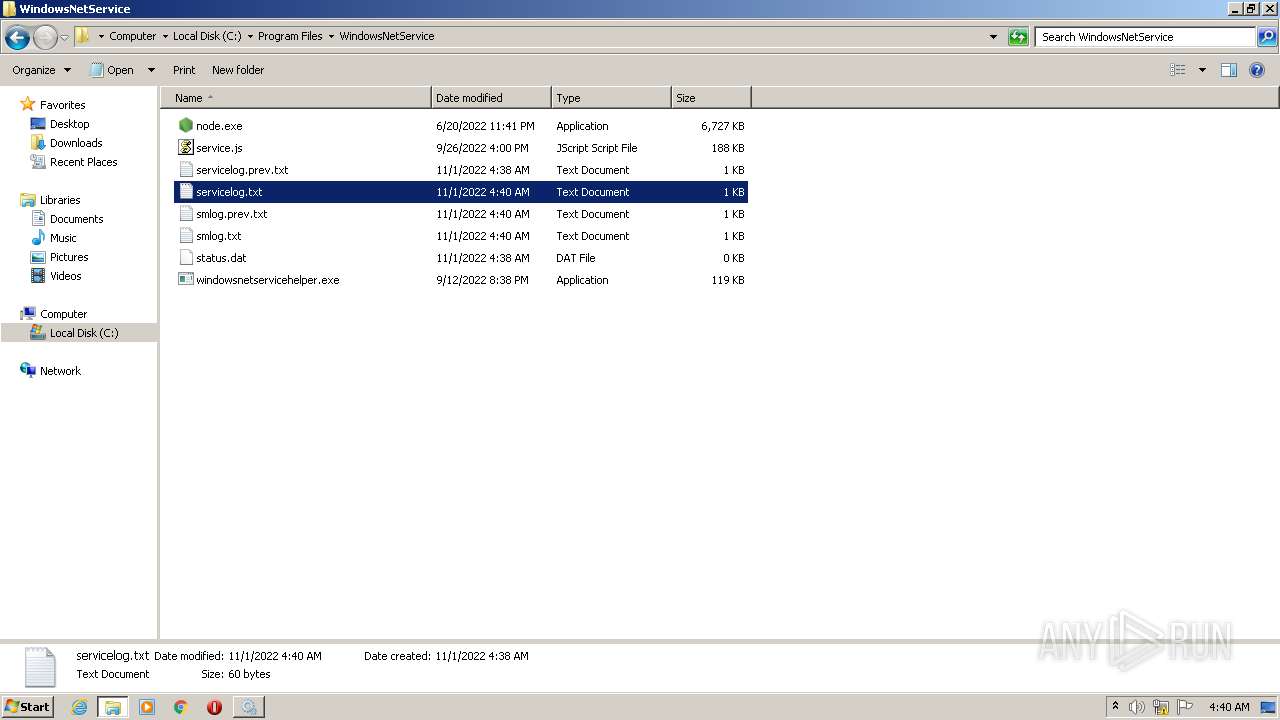
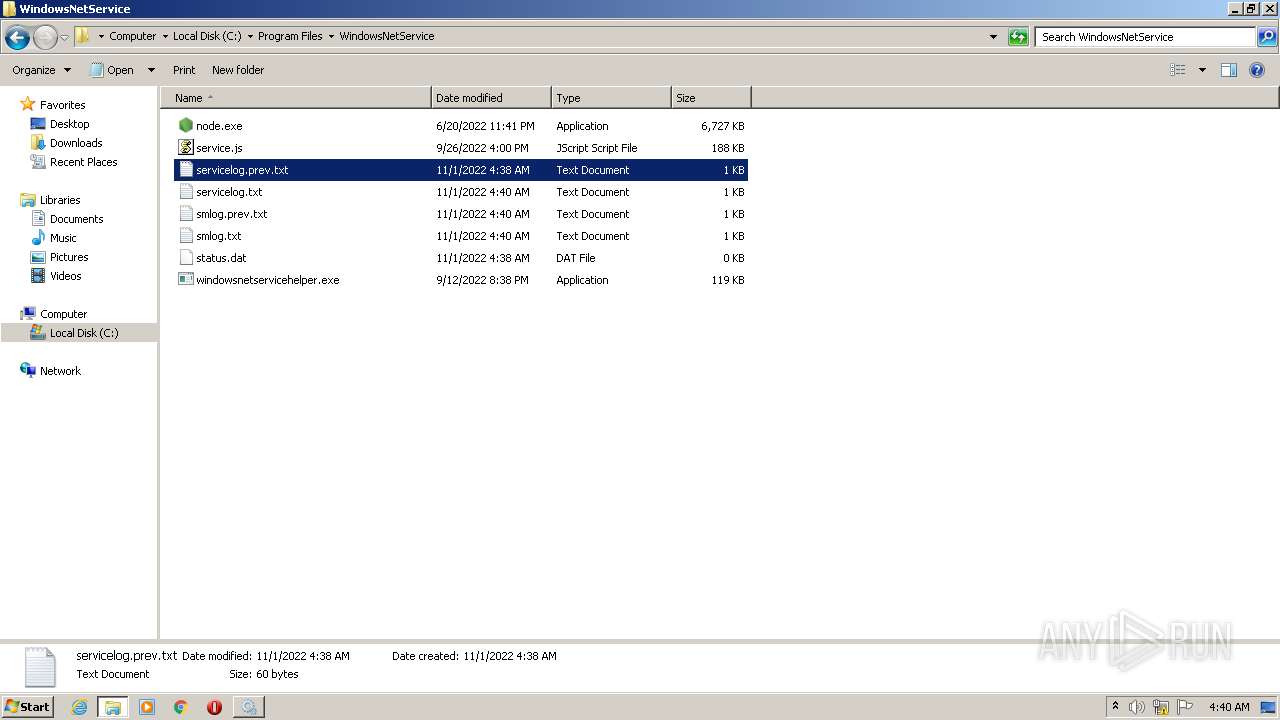
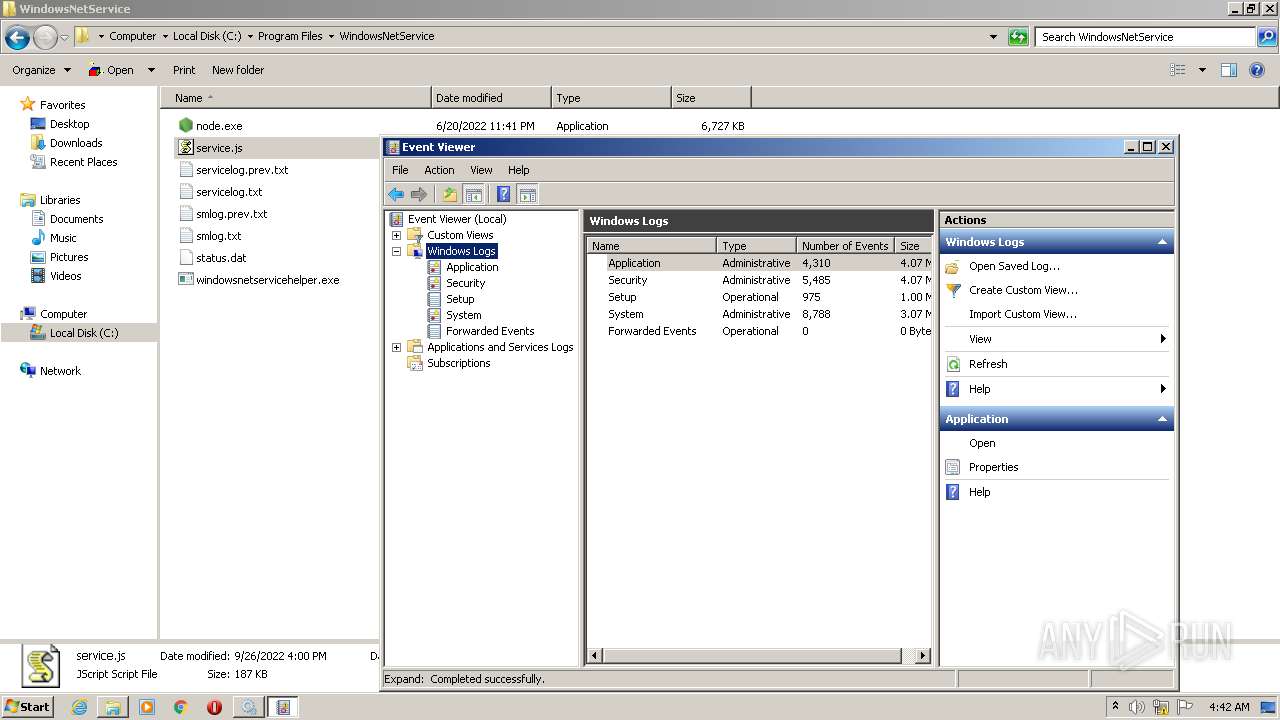
Creates files in the program directory
- windowsnetservicehelper.exe (PID: 3972)
- windowsnetservicehelper.exe (PID: 3672)
- windowsnetservicehelper-1.1.21bt2.exe.NULL.exe (PID: 336)
Reads Environment values
- node.exe (PID: 2412)
- node.exe (PID: 3484)
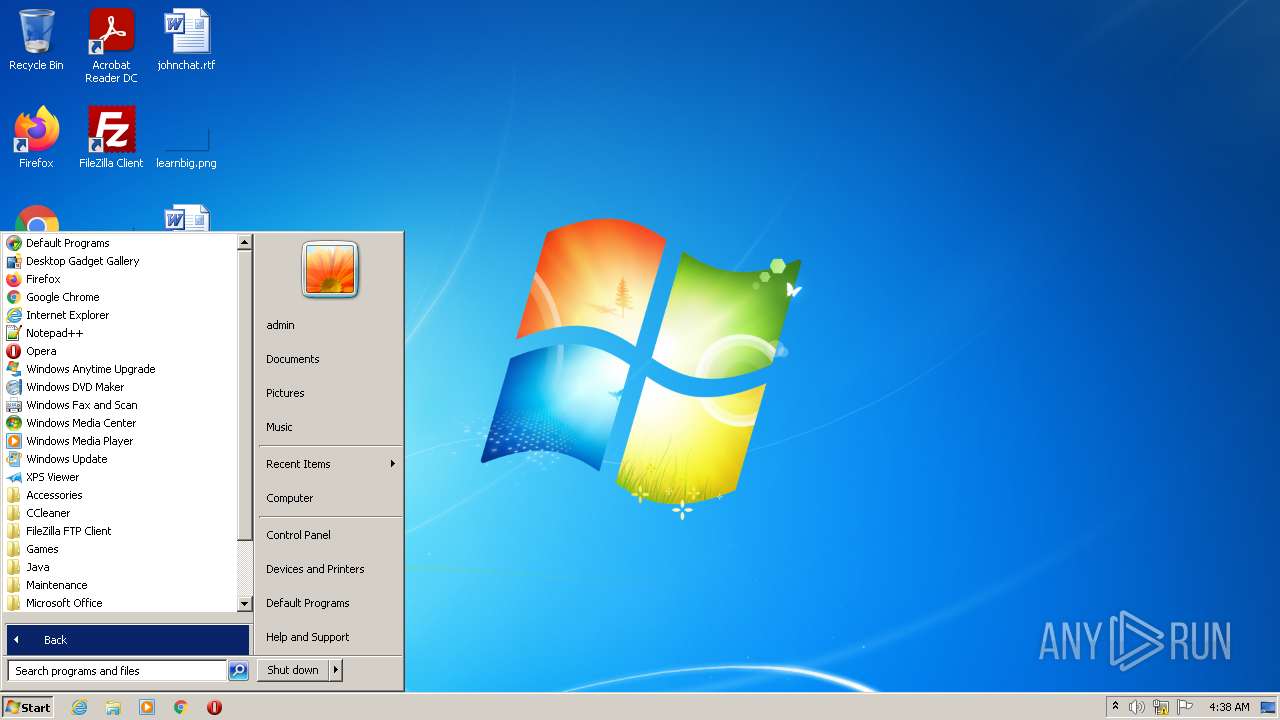
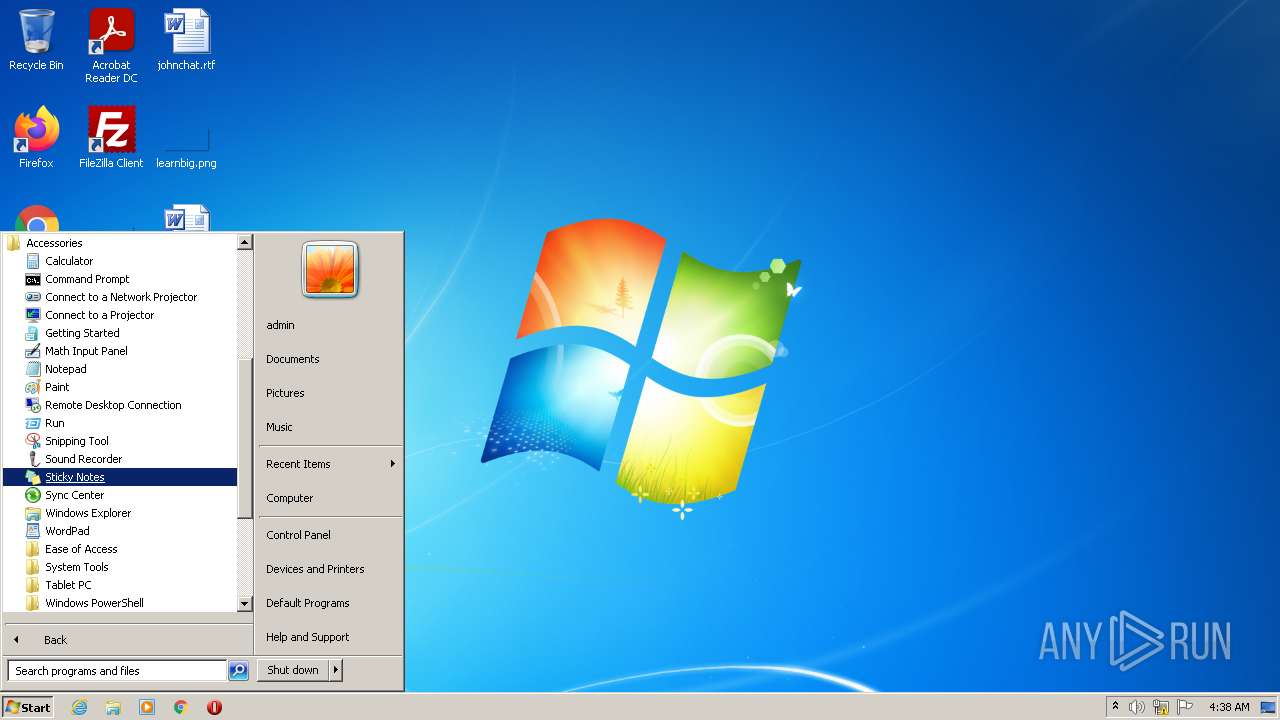
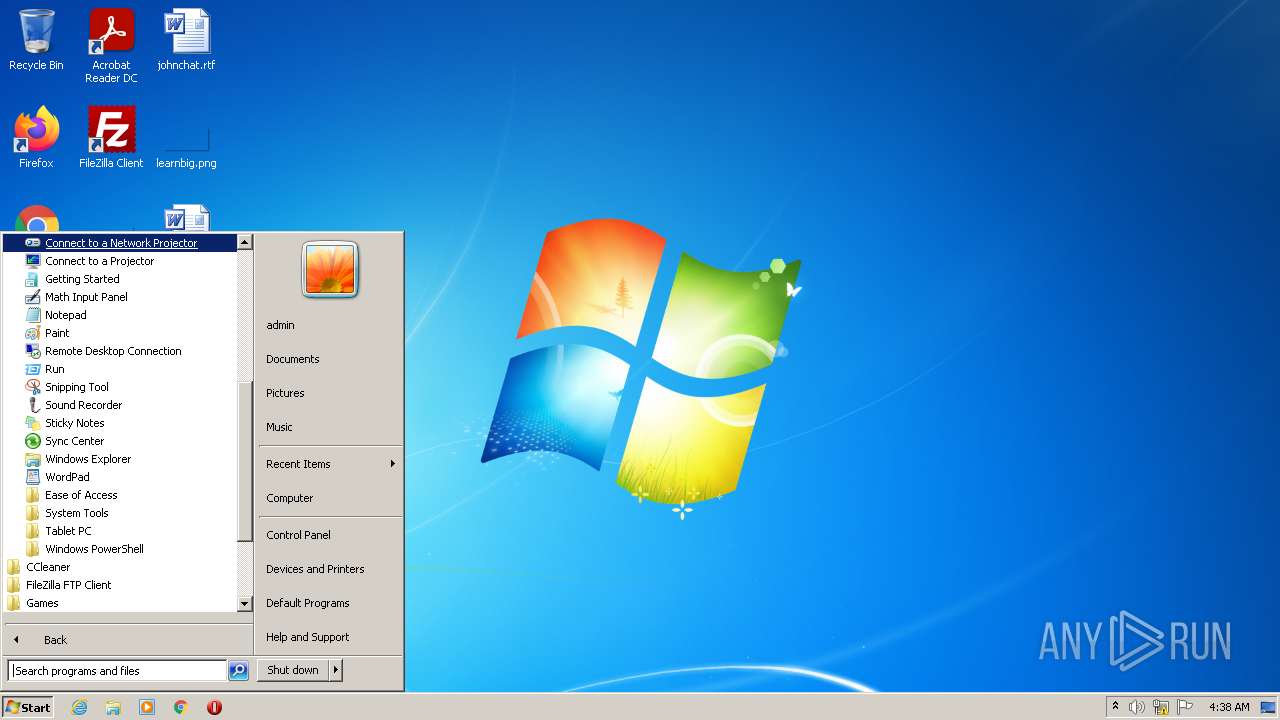
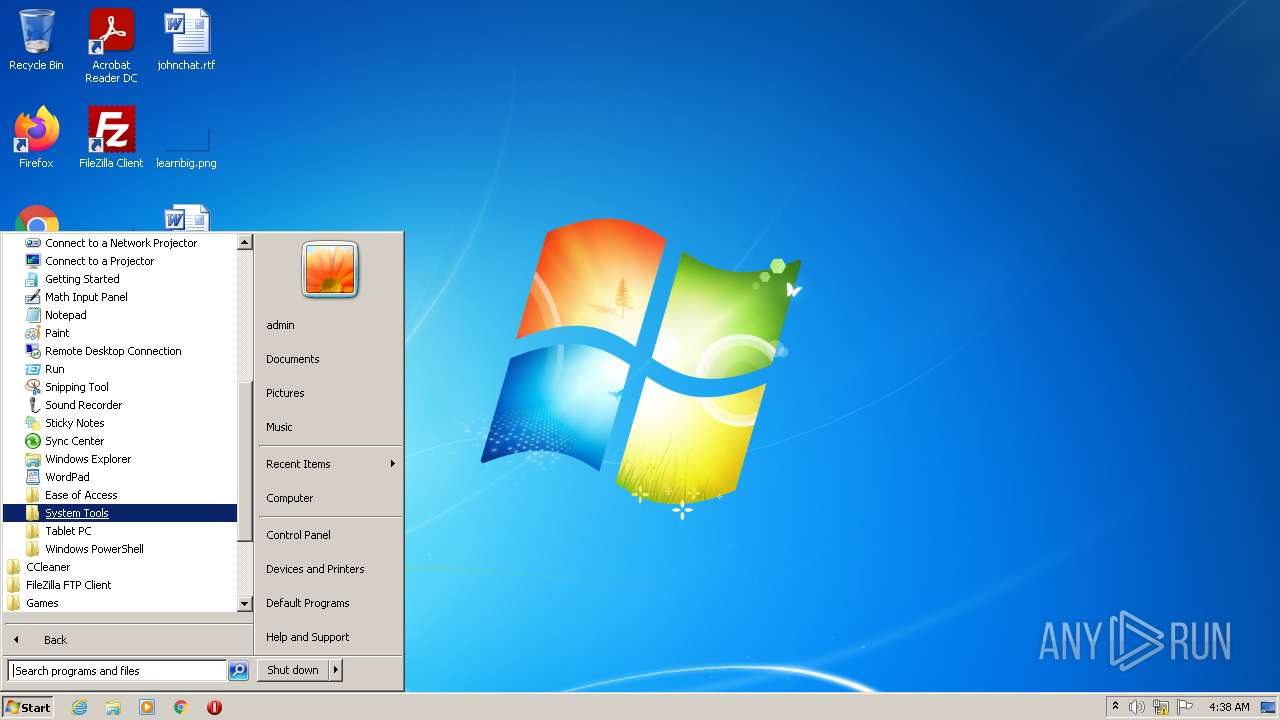
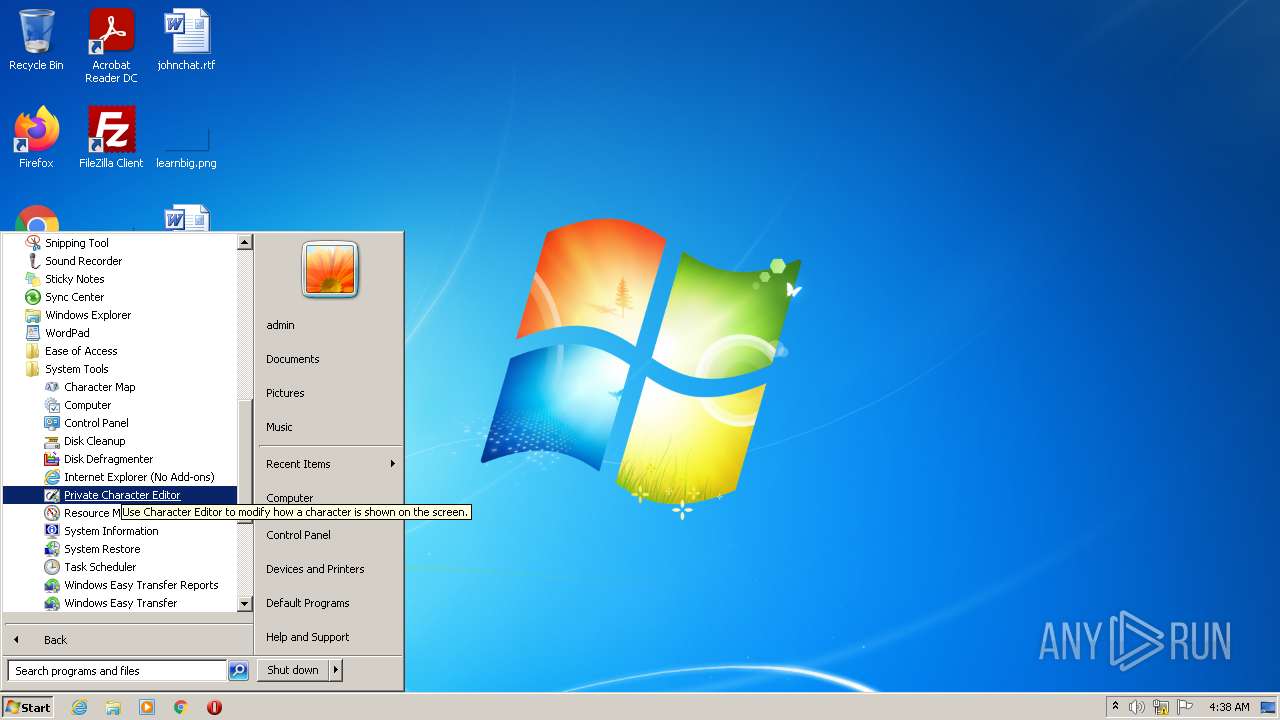
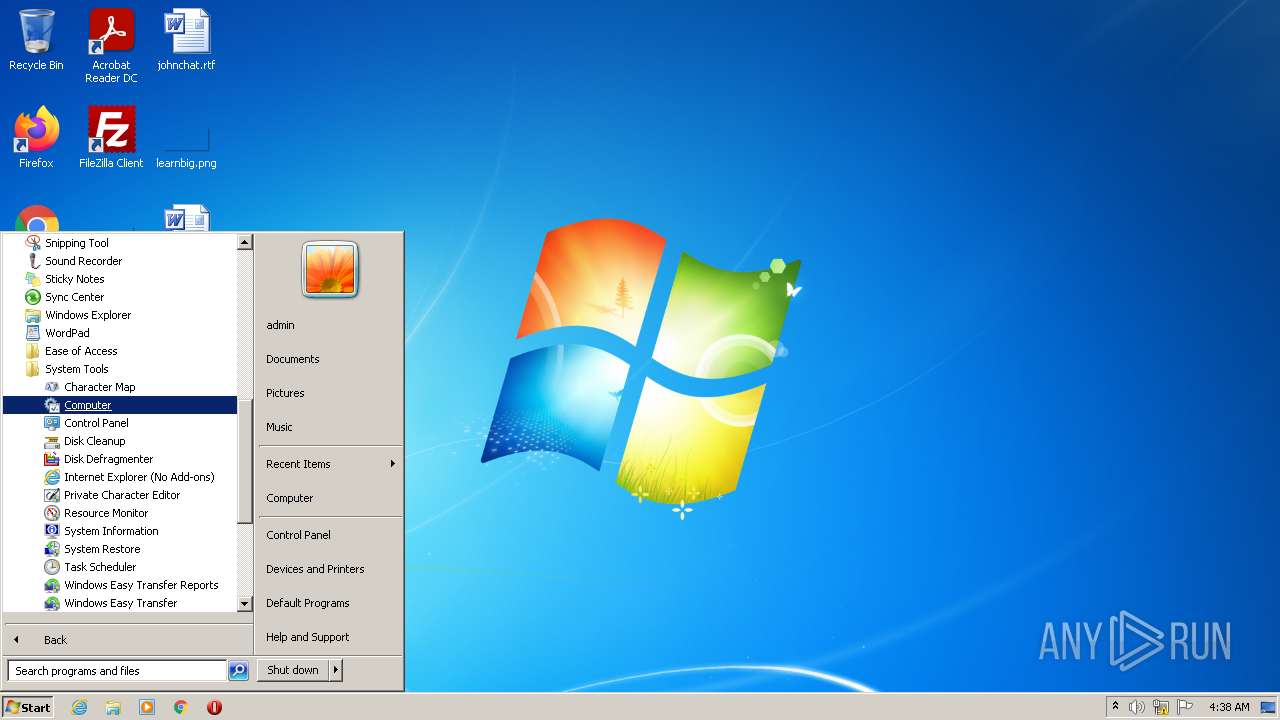
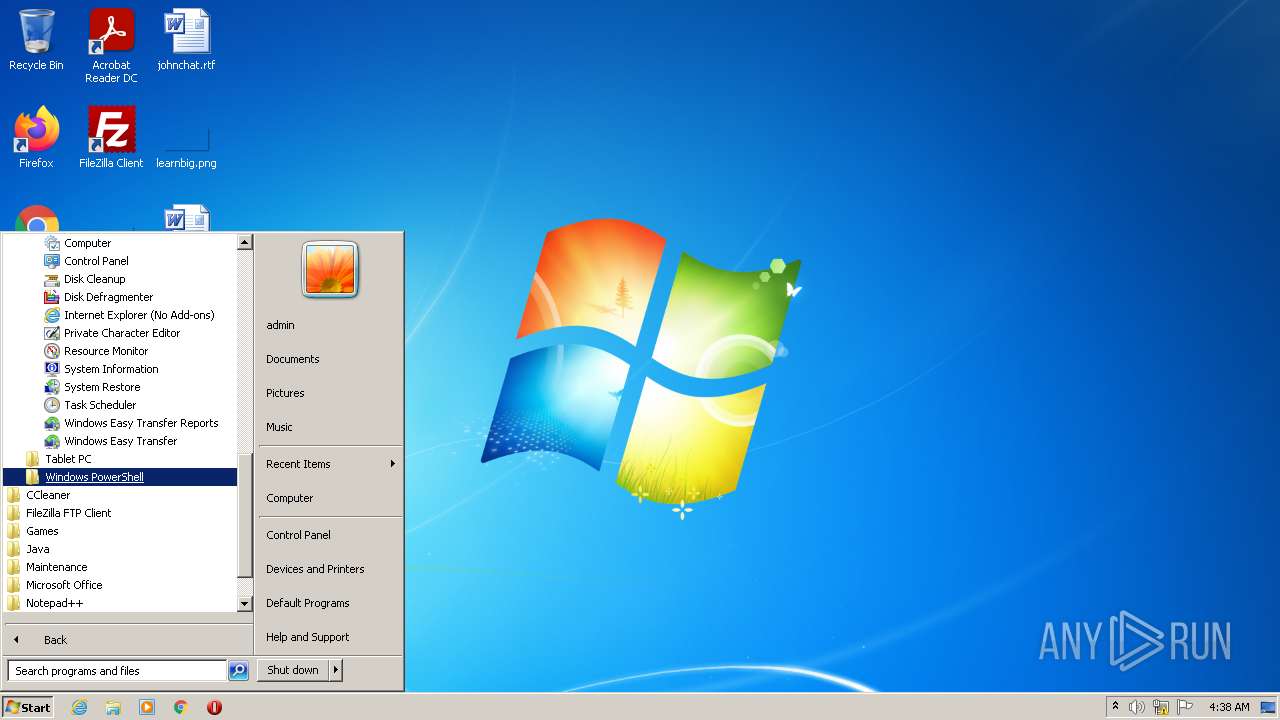
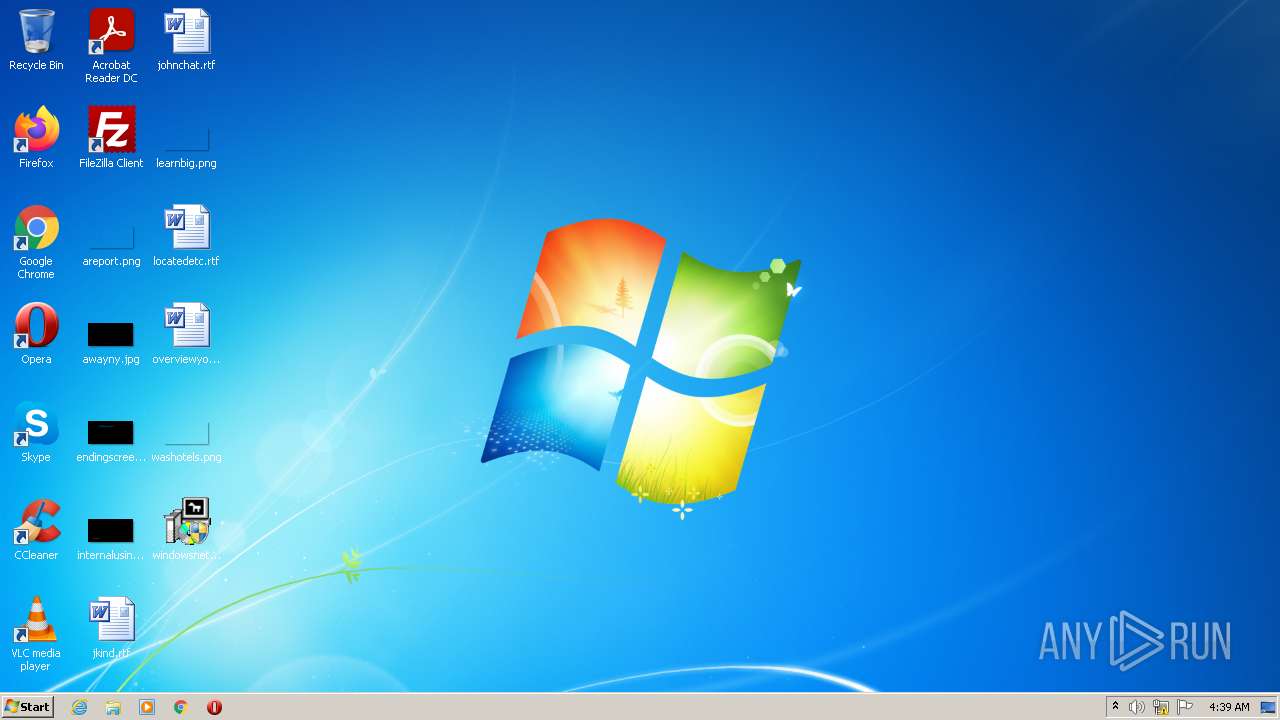
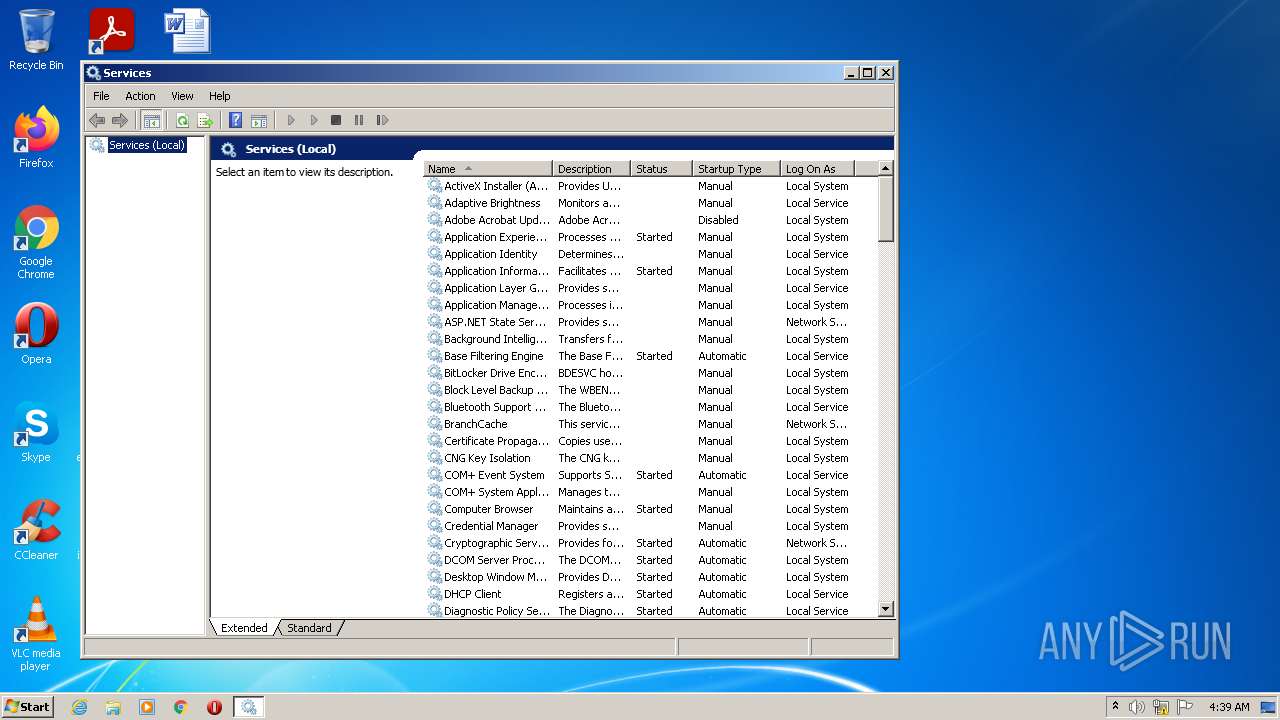
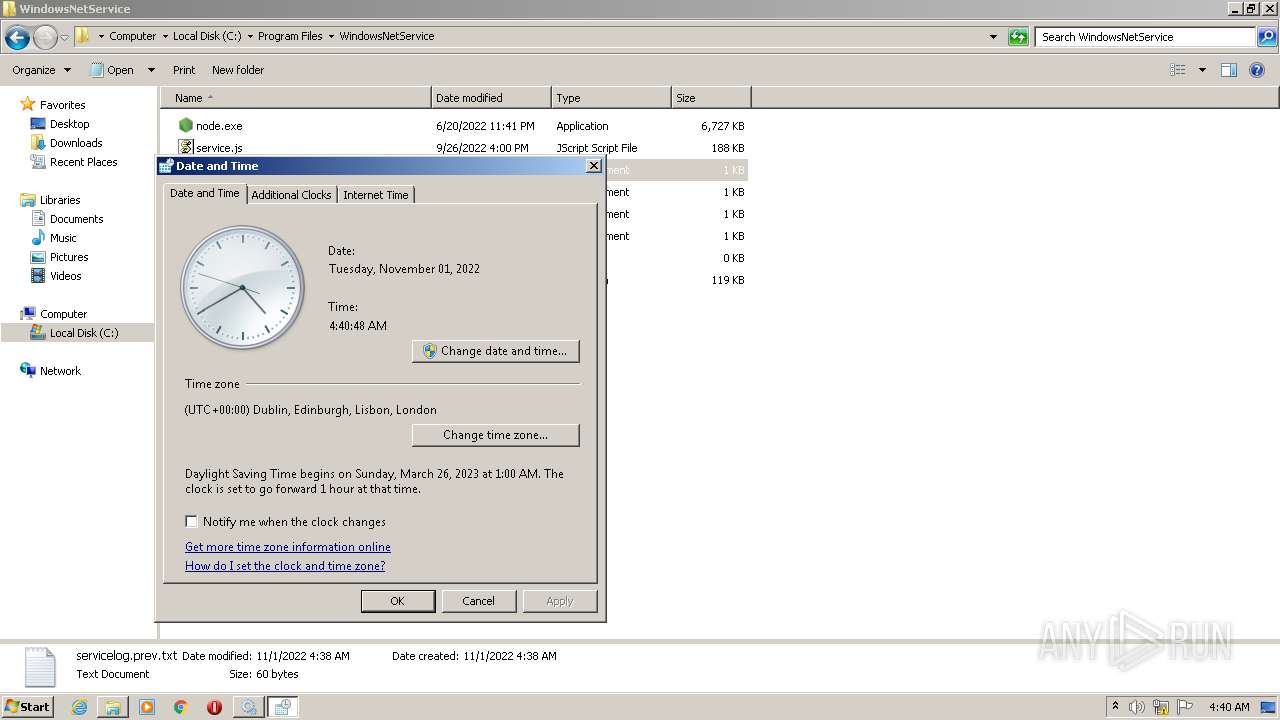
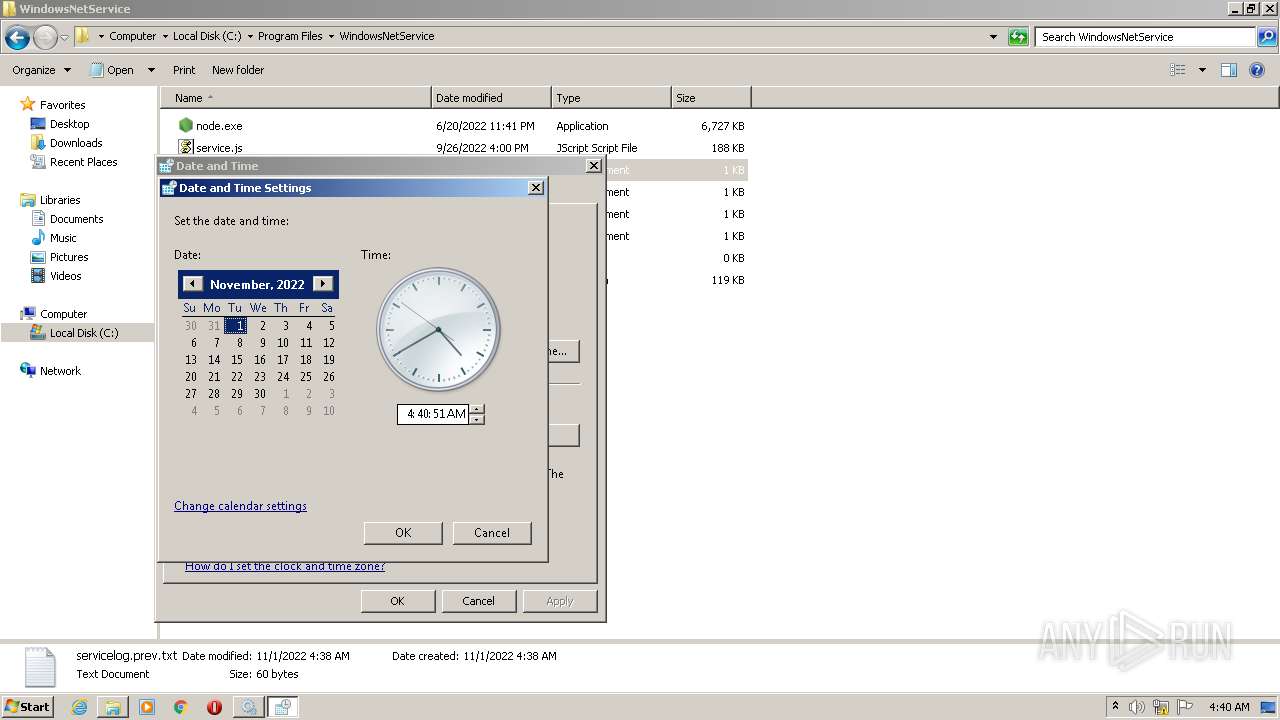
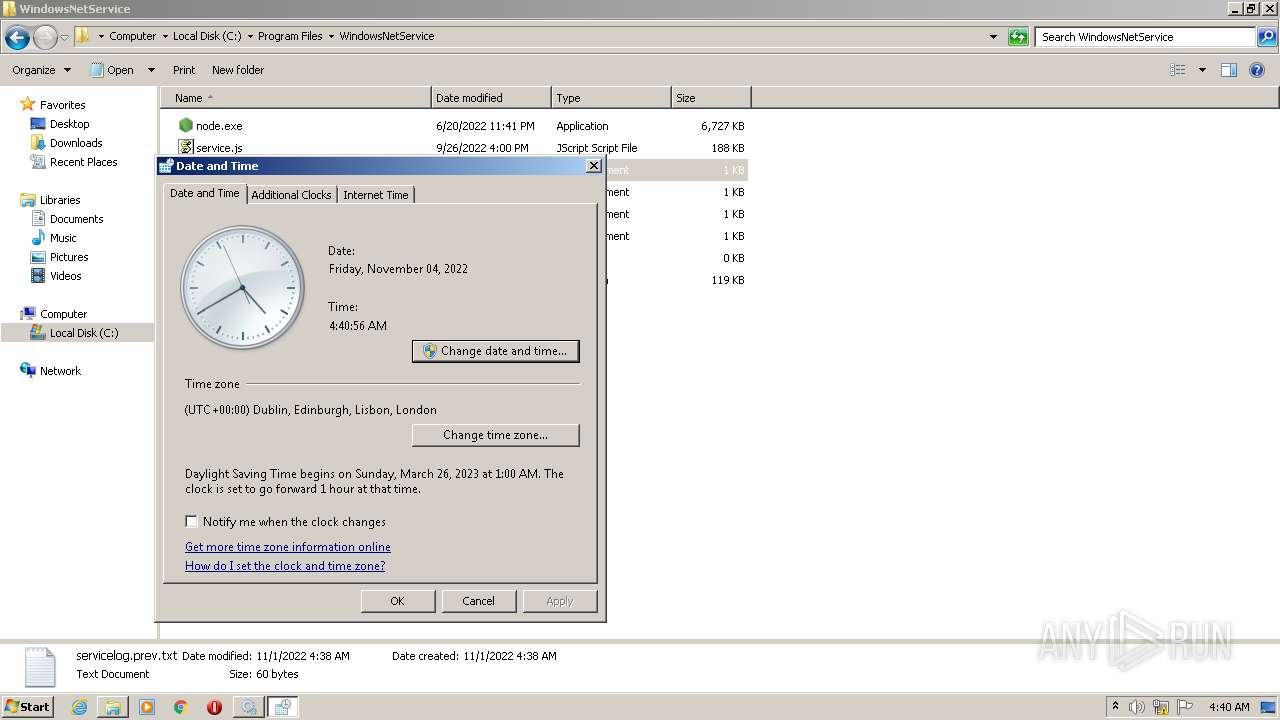
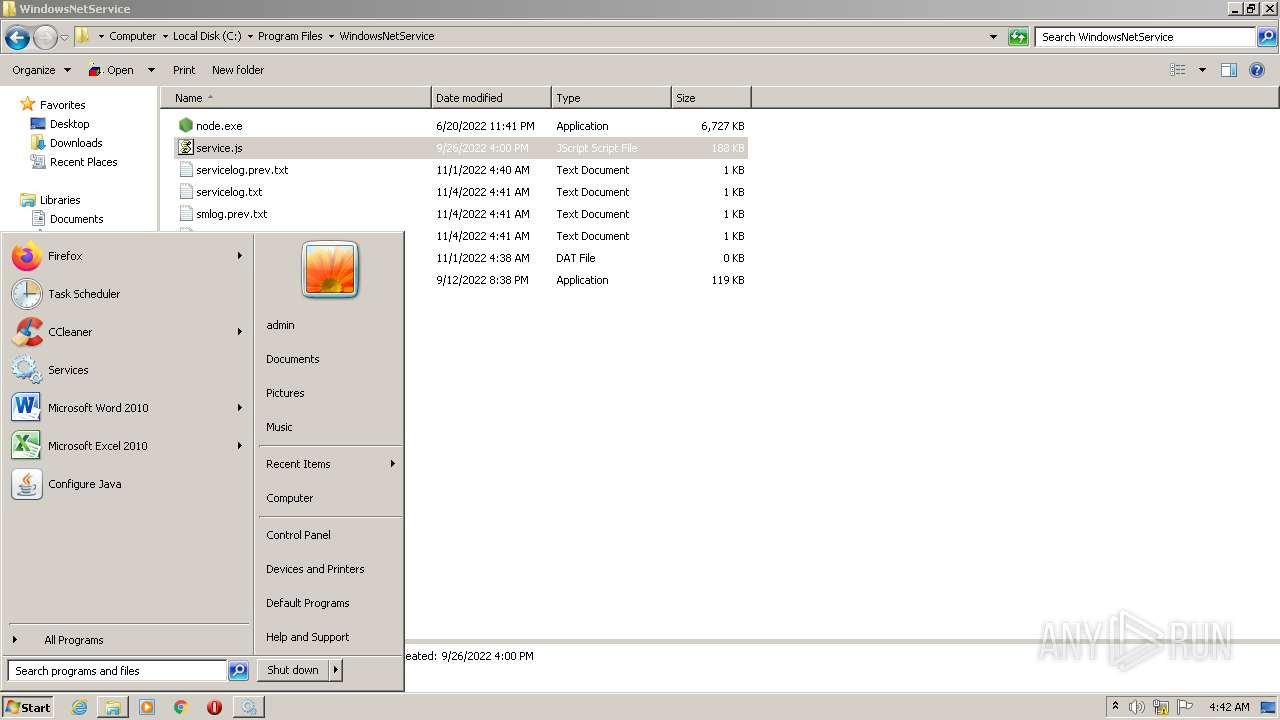
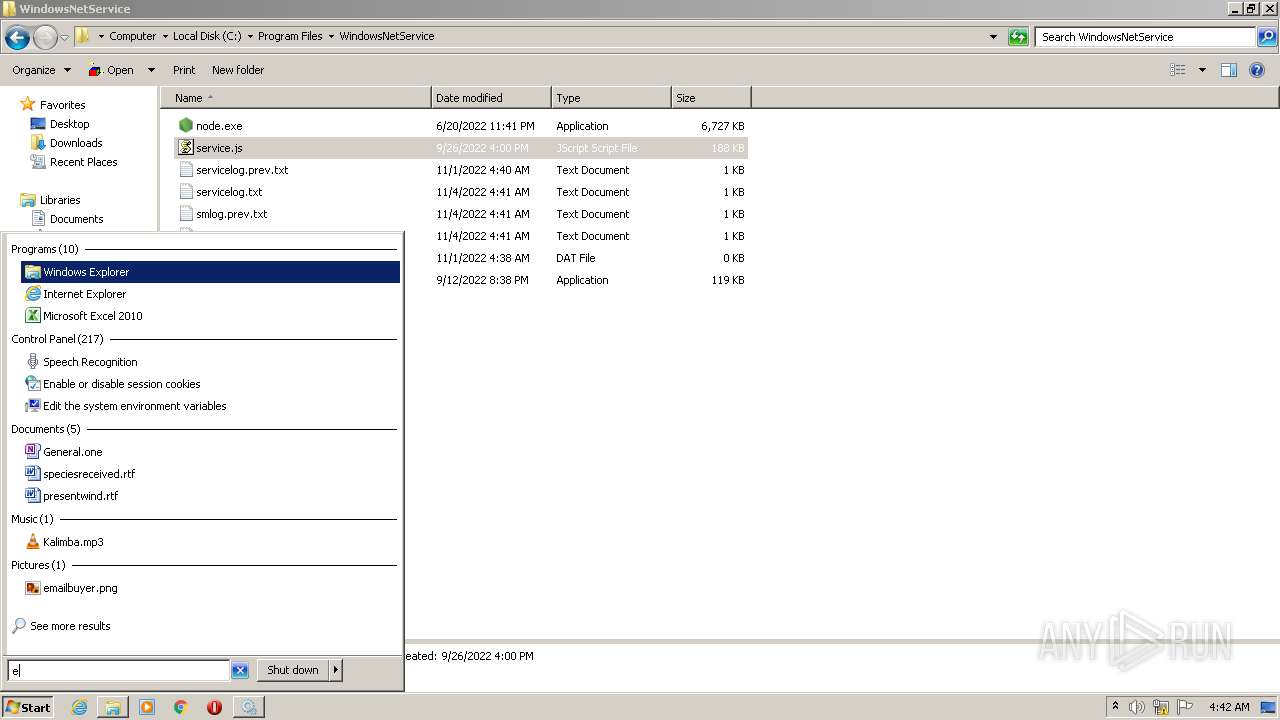
Manual execution by user
- mmc.exe (PID: 3592)
- mmc.exe (PID: 3028)
- NOTEPAD.EXE (PID: 2176)
- explorer.exe (PID: 3340)
- NOTEPAD.EXE (PID: 3072)
- control.exe (PID: 1308)
- NOTEPAD.EXE (PID: 704)
- NOTEPAD.EXE (PID: 3340)
Reads security settings of Internet Explorer
- mmc.exe (PID: 3592)
Reads product name
- node.exe (PID: 2412)
- node.exe (PID: 3484)
Process checks SAM and SYSTEM backups
- node.exe (PID: 2412)
- node.exe (PID: 3484)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2018-Dec-15 22:26:01 |
| Detected languages: |
|
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 216 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 5 |
| TimeDateStamp: | 2018-Dec-15 22:26:01 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 4096 | 25609 | 26112 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.40783 |
.rdata | 32768 | 5014 | 5120 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15491 |
.data | 40960 | 418648 | 1536 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.00056 |
.ndata | 462848 | 524288 | 0 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | |
.rsrc | 987136 | 2656 | 3072 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.20099 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.50665 | 744 | UNKNOWN | English - United States | RT_ICON |
103 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
1 (#2) | 5.28733 | 841 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
88
Monitored processes
31
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 336 | "C:\Users\admin\Desktop\windowsnetservicehelper-1.1.21bt2.exe.NULL.exe" | C:\Users\admin\Desktop\windowsnetservicehelper-1.1.21bt2.exe.NULL.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 400 | "sc" delete windowsnetservicehelper.exe | C:\Windows\system32\sc.exe | — | nsF697.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 680 | C:\Windows\system32\DllHost.exe /Processid:{9DF523B0-A6C0-4EA9-B5F1-F4565C3AC8B8} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
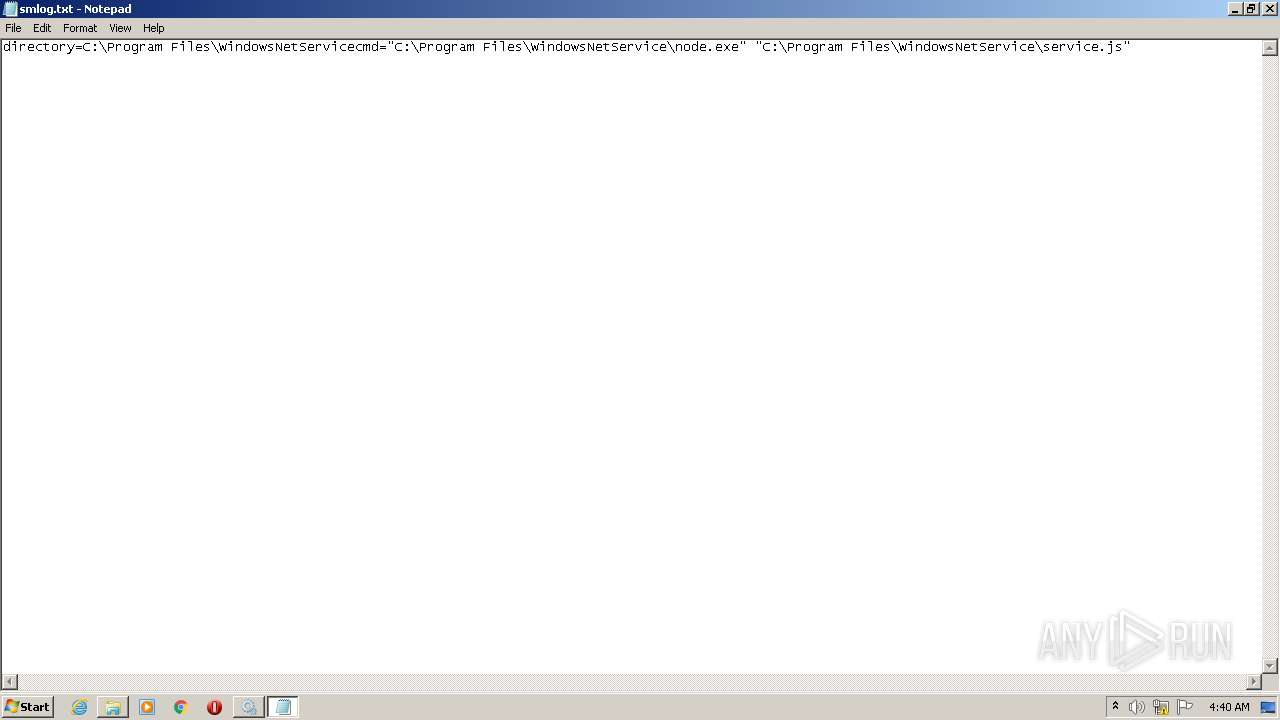
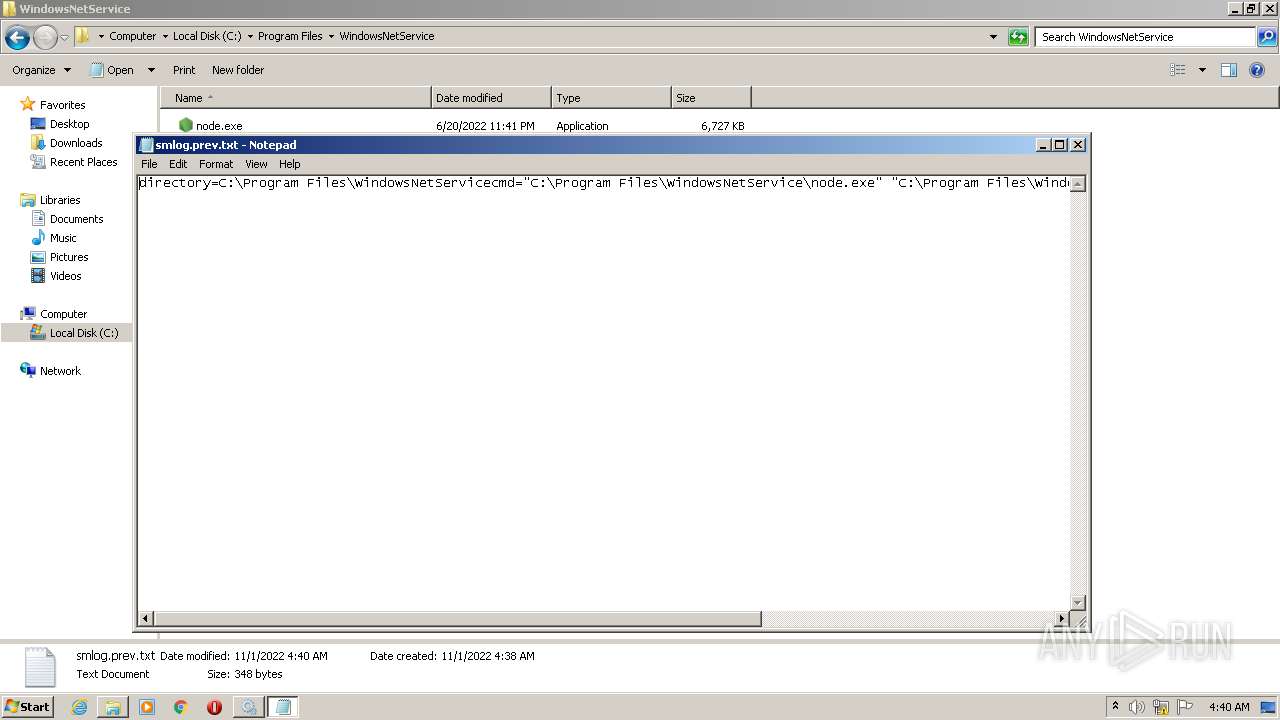
| 704 | "C:\Windows\system32\NOTEPAD.EXE" C:\Program Files\WindowsNetService\smlog.prev.txt | C:\Windows\system32\NOTEPAD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1076 | "C:\Users\admin\Desktop\windowsnetservicehelper-1.1.21bt2.exe.NULL.exe" | C:\Users\admin\Desktop\windowsnetservicehelper-1.1.21bt2.exe.NULL.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1208 | wmic path Win32_NetworkAdapter where Index=7 get NetConnectionID,MACAddress /format:table | C:\Windows\System32\Wbem\wmic.exe | — | node.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1308 | "C:\Windows\System32\control.exe" "C:\Windows\system32\timedate.cpl", | C:\Windows\System32\control.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1320 | wmic path Win32_NetworkAdapterConfiguration where IPEnabled=true get DefaultIPGateway,GatewayCostMetric,IPConnectionMetric,Index /format:table | C:\Windows\System32\Wbem\wmic.exe | — | node.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
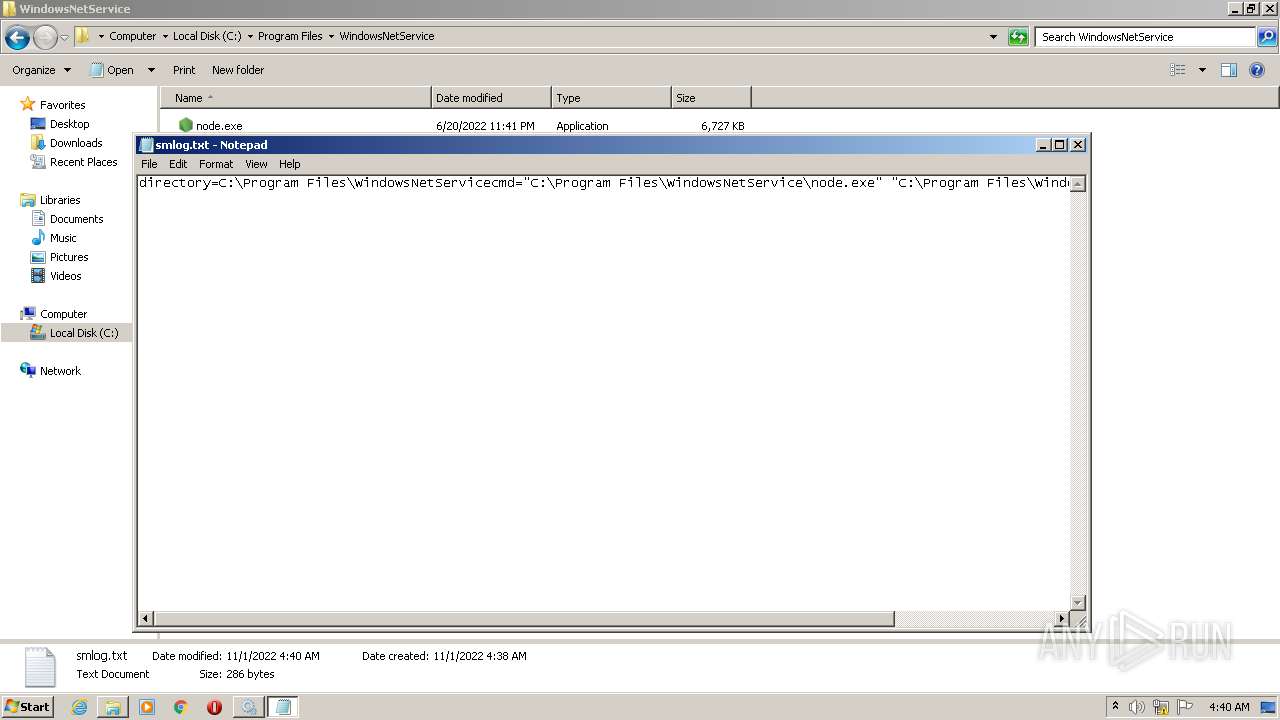
| 2176 | "C:\Windows\system32\NOTEPAD.EXE" C:\Program Files\WindowsNetService\smlog.txt | C:\Windows\system32\NOTEPAD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2412 | "C:\Program Files\WindowsNetService\node.exe" "C:\Program Files\WindowsNetService\service.js" | C:\Program Files\WindowsNetService\node.exe | windowsnetservicehelper.exe | ||||||||||||
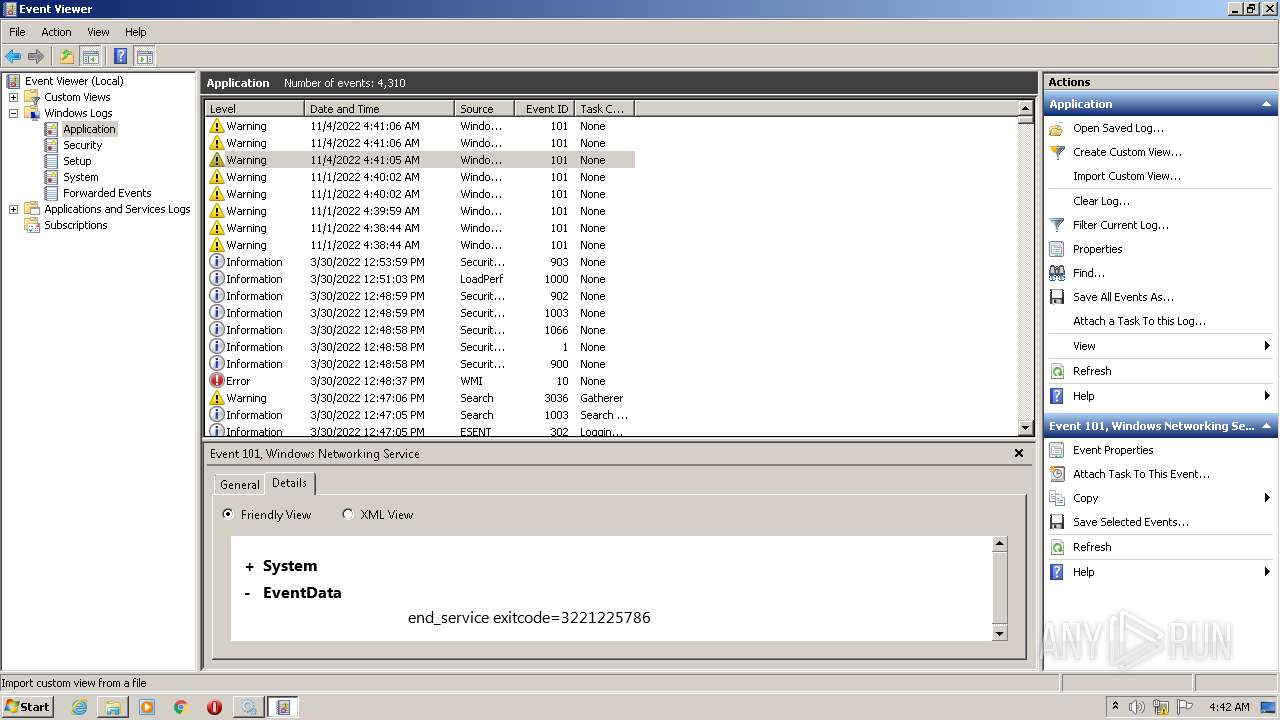
User: SYSTEM Company: Node.js Integrity Level: SYSTEM Description: Node.js: Server-side JavaScript Exit code: 3221225786 Version: 12.22.12 Modules
| |||||||||||||||
Total events
1 767
Read events
1 746
Write events
21
Delete events
0
Modification events
| (PID) Process: | (3592) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3592) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3592) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3592) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3592) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3592) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3592) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3592) mmc.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1308) control.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1308) control.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
8
Suspicious files
2
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
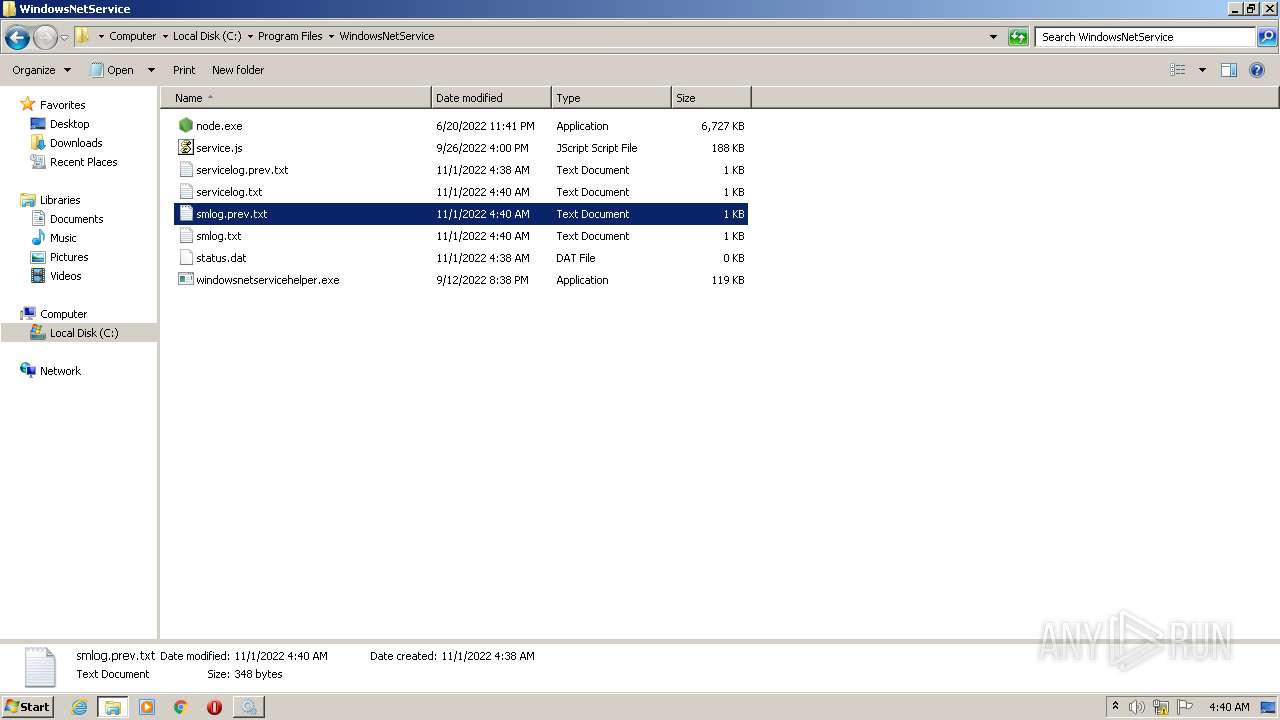
| 336 | windowsnetservicehelper-1.1.21bt2.exe.NULL.exe | C:\Program Files\WindowsNetService\status.dat | — | |
MD5:— | SHA256:— | |||
| 336 | windowsnetservicehelper-1.1.21bt2.exe.NULL.exe | C:\Users\admin\AppData\Local\Temp\nsvF51C.tmp | — | |
MD5:— | SHA256:— | |||
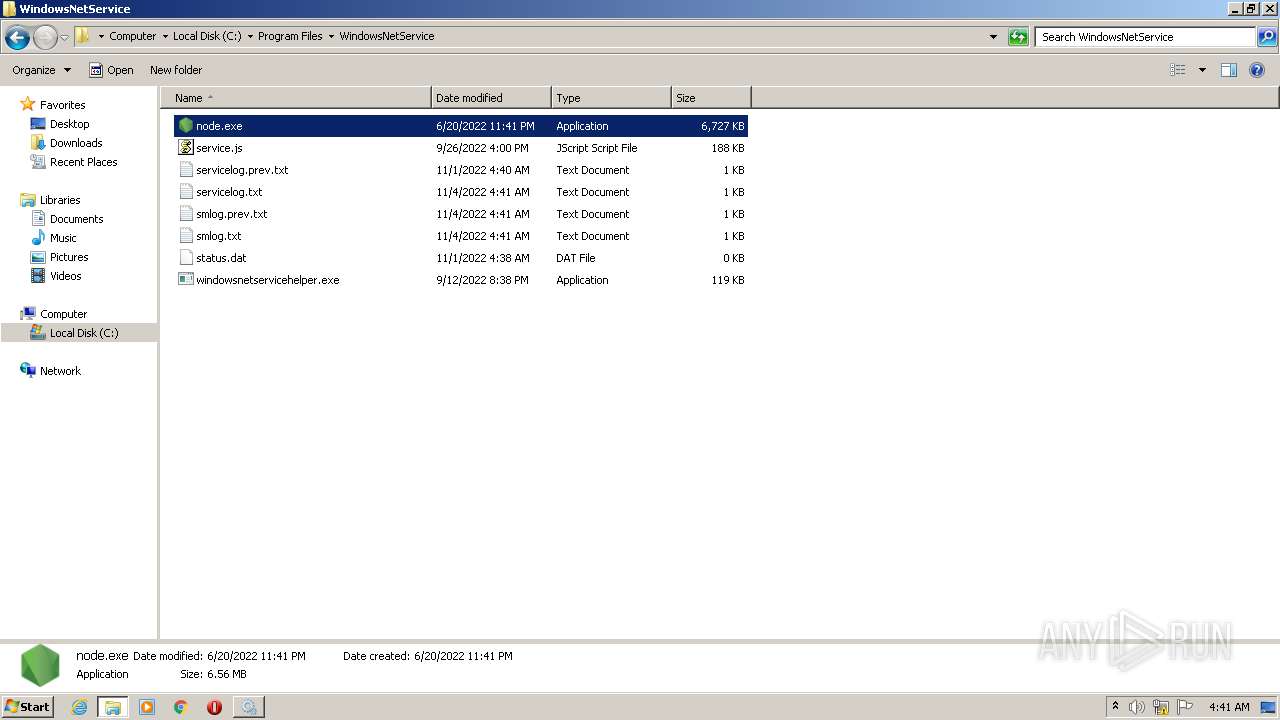
| 336 | windowsnetservicehelper-1.1.21bt2.exe.NULL.exe | C:\Program Files\WindowsNetService\node.exe | executable | |
MD5:5F40521D2E1082FE1C734610C4A83911 | SHA256:79AC7AE94231A392D27F303418E305A60C4194DBBE143C5DEFFC977C7B2E7A78 | |||
| 336 | windowsnetservicehelper-1.1.21bt2.exe.NULL.exe | C:\Program Files\WindowsNetService\windowsnetservicehelper.exe | executable | |
MD5:71363311A899A137B18015888254DECD | SHA256:298E654799DE64E5064D986223E7F08D75527FE528D750B325855CB0C2FEBAAA | |||
| 3672 | windowsnetservicehelper.exe | C:\Program Files\WindowsNetService\smlog.prev.txt | binary | |
MD5:— | SHA256:— | |||
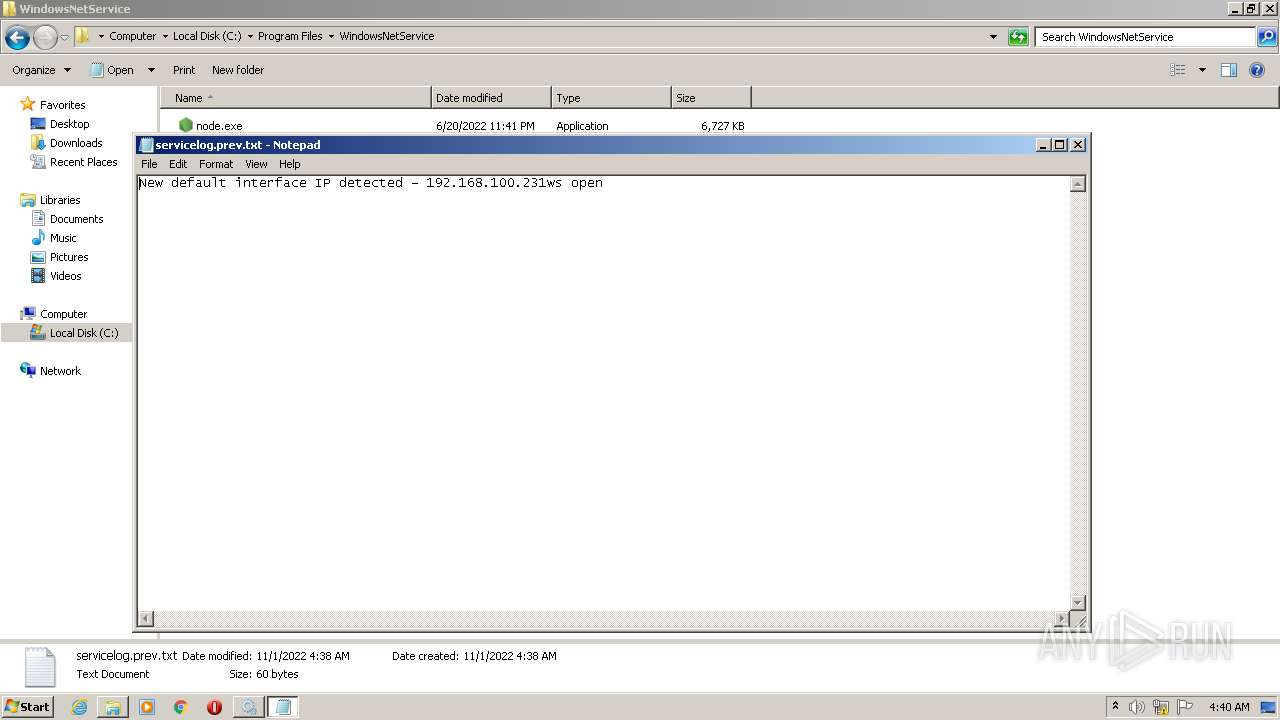
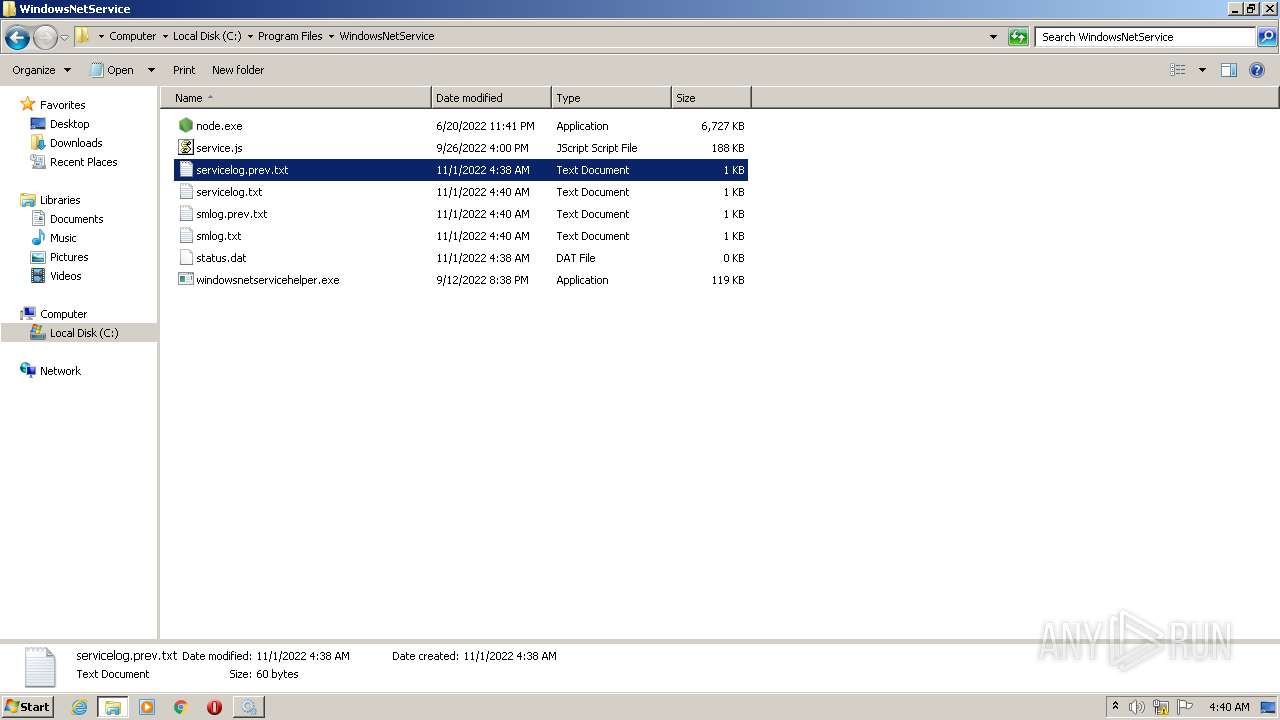
| 3672 | windowsnetservicehelper.exe | C:\Program Files\WindowsNetService\servicelog.prev.txt | text | |
MD5:— | SHA256:— | |||
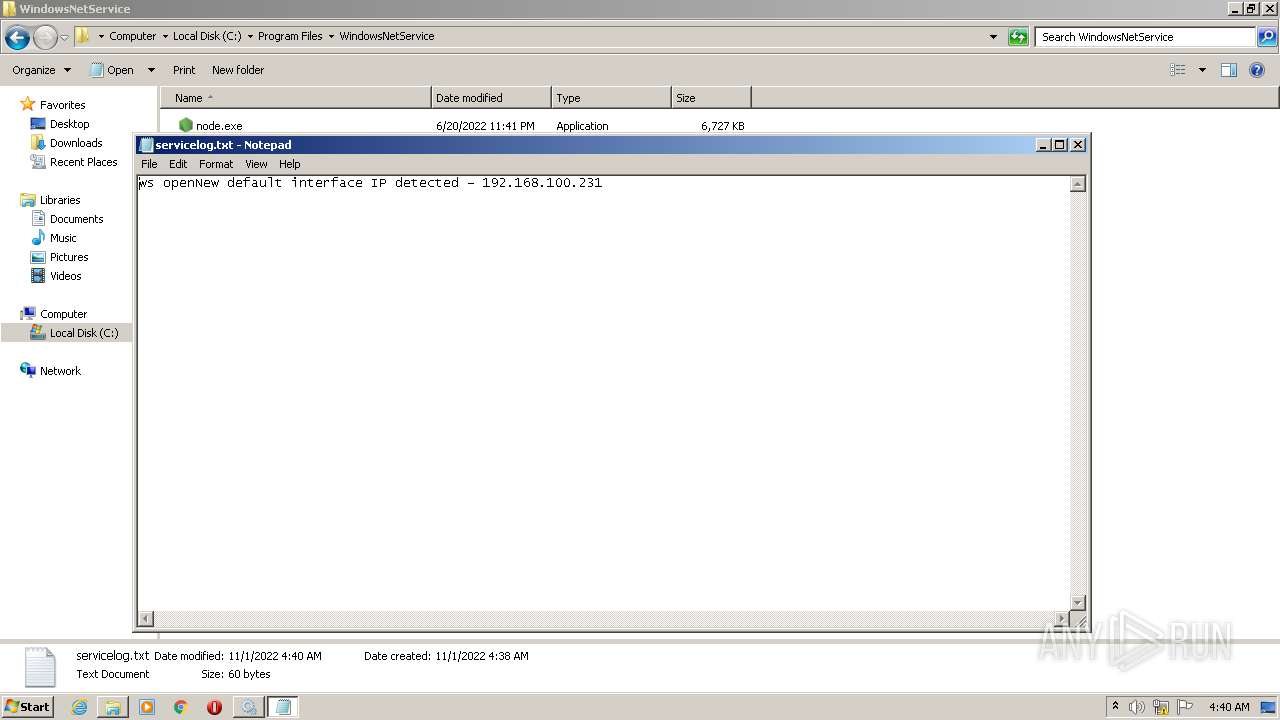
| 2412 | node.exe | C:\Program Files\WindowsNetService\servicelog.txt | text | |
MD5:— | SHA256:— | |||
| 3972 | windowsnetservicehelper.exe | C:\Program Files\WindowsNetService\smlog.txt | binary | |
MD5:— | SHA256:— | |||
| 336 | windowsnetservicehelper-1.1.21bt2.exe.NULL.exe | C:\Users\admin\AppData\Local\Temp\nslF52D.tmp\nsF697.tmp | executable | |
MD5:EC0504E6B8A11D5AAD43B296BEEB84B2 | SHA256:5D9CEB1CE5F35AEA5F9E5A0C0EDEEEC04DFEFE0C77890C80C70E98209B58B962 | |||
| 336 | windowsnetservicehelper-1.1.21bt2.exe.NULL.exe | C:\Users\admin\AppData\Local\Temp\nslF52D.tmp\nsF53D.tmp | executable | |
MD5:EC0504E6B8A11D5AAD43B296BEEB84B2 | SHA256:5D9CEB1CE5F35AEA5F9E5A0C0EDEEEC04DFEFE0C77890C80C70E98209B58B962 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2412 | node.exe | GET | 101 | 142.93.96.73:6101 | http://register.starhome.io:6101/strvn | CA | — | — | unknown |
3484 | node.exe | GET | 101 | 142.93.96.73:6101 | http://register.starhome.io:6101/strvn | CA | — | — | unknown |
— | — | GET | 101 | 142.93.96.73:6101 | http://register.starhome.io:6101/strvn | CA | — | — | unknown |
— | — | GET | 101 | 142.93.96.73:6101 | http://register.starhome.io:6101/strvn | CA | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2412 | node.exe | 142.93.96.73:6101 | register.starhome.io | DIGITALOCEAN-ASN | DE | unknown |
3484 | node.exe | 142.93.96.73:6101 | register.starhome.io | DIGITALOCEAN-ASN | DE | unknown |
— | — | 142.93.96.73:6101 | register.starhome.io | DIGITALOCEAN-ASN | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
register.starhome.io |
| unknown |