| File name: | Mouse.exe |
| Full analysis: | https://app.any.run/tasks/149230bb-6405-4de8-94d5-0ba318649c9c |
| Verdict: | Malicious activity |
| Analysis date: | June 25, 2023, 23:05:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D19CBFDDCABC13C0D0610B8455B8690D |
| SHA1: | BDC63E914DBAFBD5315FC82ABE536F8FB25D0307 |
| SHA256: | 2531CD97D7C80DF3C848305C1CED69589B4D23C48F300FE9FBFDBC90C4374DA5 |
| SSDEEP: | 98304:uuYQRUPI/RIHb+njgXvB9SAMlyzLQj1UGhj8DvQxER4mzEDjUt39NXzxnH8JNvV/:uurR1AjGhj8cOzNLcJNvVkTKxM0zh |
MALICIOUS
Application was dropped or rewritten from another process
- hefF098.exe (PID: 3616)
- hefF098.exe (PID: 1148)
- hefF098.exe (PID: 2436)
- hefF098.exe (PID: 2100)
- hefF098.exe (PID: 3276)
- hefF098.exe (PID: 3960)
- hefF098.exe (PID: 2716)
SUSPICIOUS
Executable content was dropped or overwritten
- Mouse.exe (PID: 3140)
Reads the Internet Settings
- Mouse.exe (PID: 3140)
- runonce.exe (PID: 1892)
- hefF098.exe (PID: 3616)
- hefF098.exe (PID: 1148)
- runonce.exe (PID: 3084)
- hefF098.exe (PID: 2436)
- runonce.exe (PID: 752)
- hefF098.exe (PID: 2100)
- runonce.exe (PID: 1024)
- hefF098.exe (PID: 3276)
- runonce.exe (PID: 1280)
- hefF098.exe (PID: 3960)
- runonce.exe (PID: 3412)
- hefF098.exe (PID: 2716)
- runonce.exe (PID: 3800)
Uses RUNDLL32.EXE to load library
- runonce.exe (PID: 1016)
- runonce.exe (PID: 3400)
- runonce.exe (PID: 2140)
- runonce.exe (PID: 2884)
- runonce.exe (PID: 3120)
- runonce.exe (PID: 1160)
- runonce.exe (PID: 2120)
Application launched itself
- runonce.exe (PID: 1892)
- runonce.exe (PID: 3084)
- runonce.exe (PID: 752)
- runonce.exe (PID: 1024)
- runonce.exe (PID: 1280)
- runonce.exe (PID: 3412)
- runonce.exe (PID: 3800)
Reads the Windows owner or organization settings
- Mouse.exe (PID: 3140)
INFO
Checks supported languages
- Mouse.exe (PID: 3140)
- hefF098.exe (PID: 3616)
- hefF098.exe (PID: 1148)
- hefF098.exe (PID: 2436)
- hefF098.exe (PID: 2100)
- hefF098.exe (PID: 3276)
- hefF098.exe (PID: 3960)
- hefF098.exe (PID: 2716)
The process checks LSA protection
- Mouse.exe (PID: 3140)
- runonce.exe (PID: 1892)
- hefF098.exe (PID: 3616)
- hefF098.exe (PID: 1148)
- runonce.exe (PID: 3084)
- hefF098.exe (PID: 2436)
- runonce.exe (PID: 752)
- hefF098.exe (PID: 2100)
- runonce.exe (PID: 1024)
- hefF098.exe (PID: 3276)
- runonce.exe (PID: 1280)
- hefF098.exe (PID: 3960)
- runonce.exe (PID: 3412)
- hefF098.exe (PID: 2716)
- runonce.exe (PID: 3800)
Reads the computer name
- hefF098.exe (PID: 3616)
- Mouse.exe (PID: 3140)
- hefF098.exe (PID: 1148)
- hefF098.exe (PID: 2436)
- hefF098.exe (PID: 2100)
- hefF098.exe (PID: 3276)
- hefF098.exe (PID: 3960)
- hefF098.exe (PID: 2716)
Reads the time zone
- runonce.exe (PID: 1892)
- runonce.exe (PID: 3084)
- runonce.exe (PID: 752)
- runonce.exe (PID: 1024)
- runonce.exe (PID: 1280)
- runonce.exe (PID: 3412)
- runonce.exe (PID: 3800)
Create files in a temporary directory
- Mouse.exe (PID: 3140)
- hefF098.exe (PID: 3616)
- hefF098.exe (PID: 1148)
- hefF098.exe (PID: 2436)
- hefF098.exe (PID: 2100)
- hefF098.exe (PID: 3276)
- hefF098.exe (PID: 3960)
- hefF098.exe (PID: 2716)
Reads the machine GUID from the registry
- hefF098.exe (PID: 3616)
- hefF098.exe (PID: 1148)
- hefF098.exe (PID: 2436)
- hefF098.exe (PID: 2100)
- hefF098.exe (PID: 3276)
- hefF098.exe (PID: 3960)
- hefF098.exe (PID: 2716)
Creates files or folders in the user directory
- Mouse.exe (PID: 3140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (45.2) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (43.6) |
| .exe | | | Win32 Executable (generic) (4.7) |
| .exe | | | Win16/32 Executable Delphi generic (2.1) |
| .exe | | | Generic Win/DOS Executable (2.1) |
EXIF
EXE
| Email: | skystars@hanmail.net |
|---|---|
| Web: | http://www.hdwallpaper.kr |
| Comments: | Built with HTML Executable, http://www.htmlexe.com |
| ProductVersion: | 1.0.0.0 |
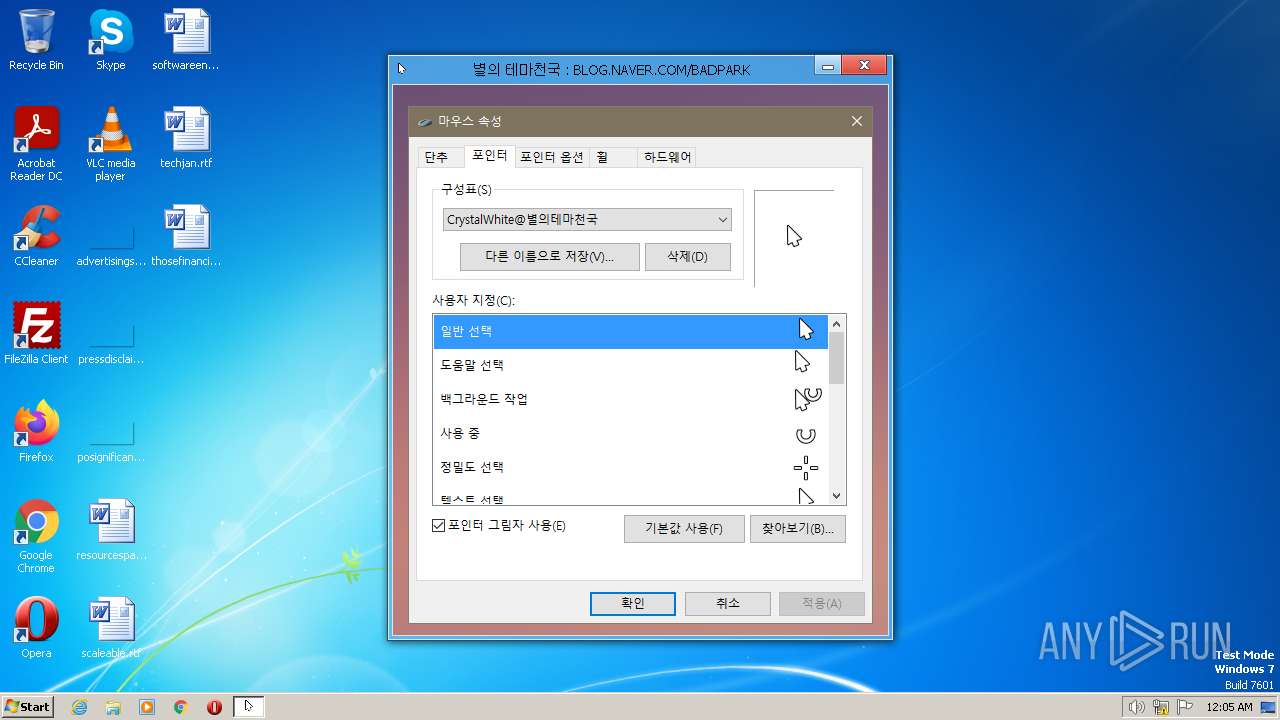
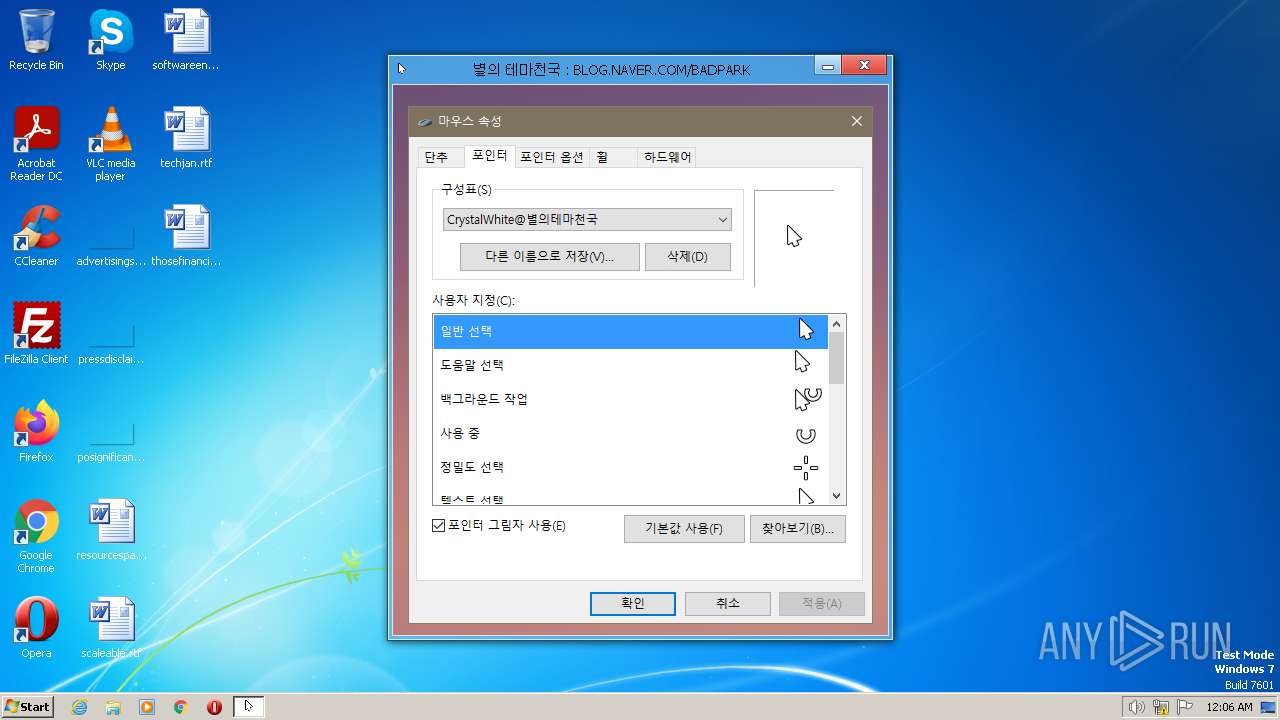
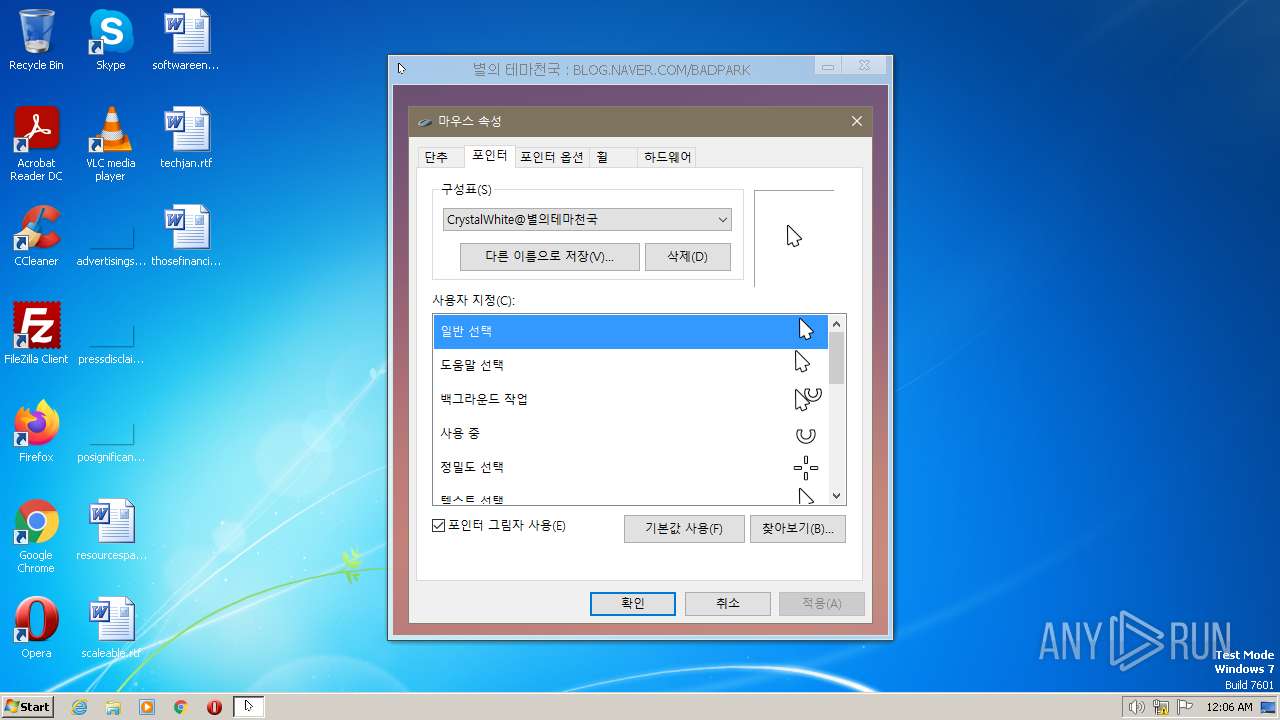
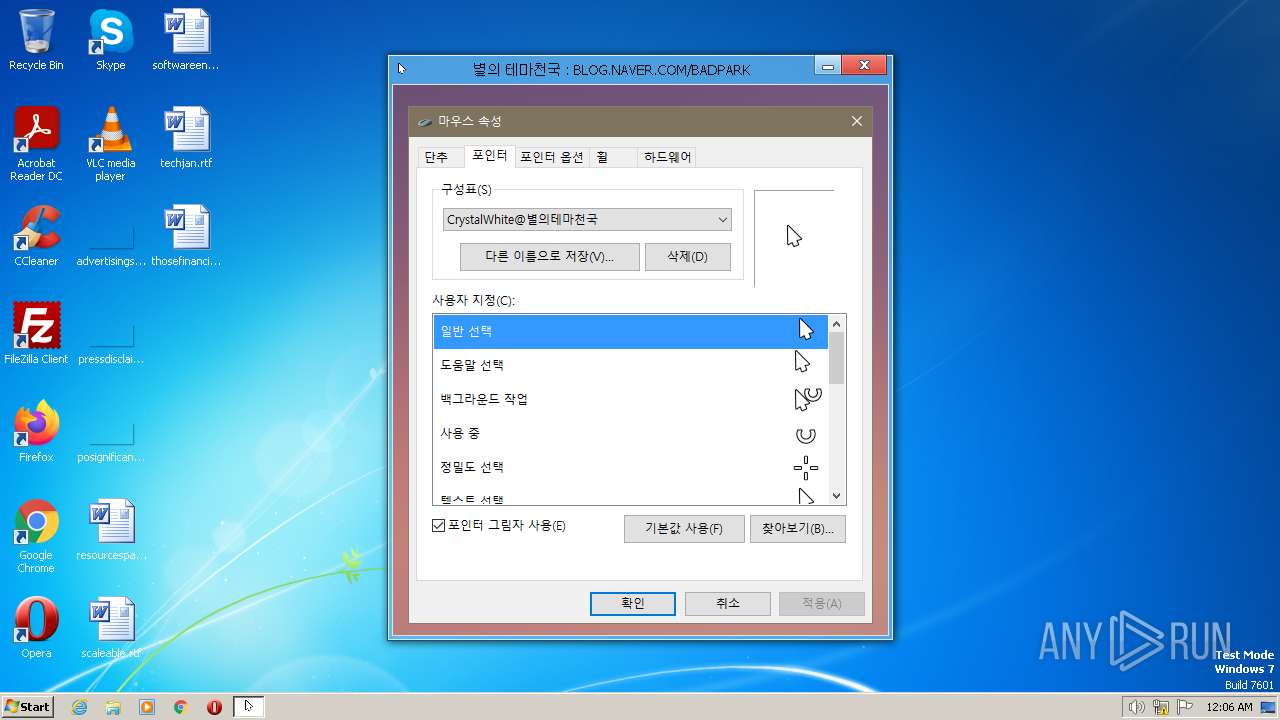
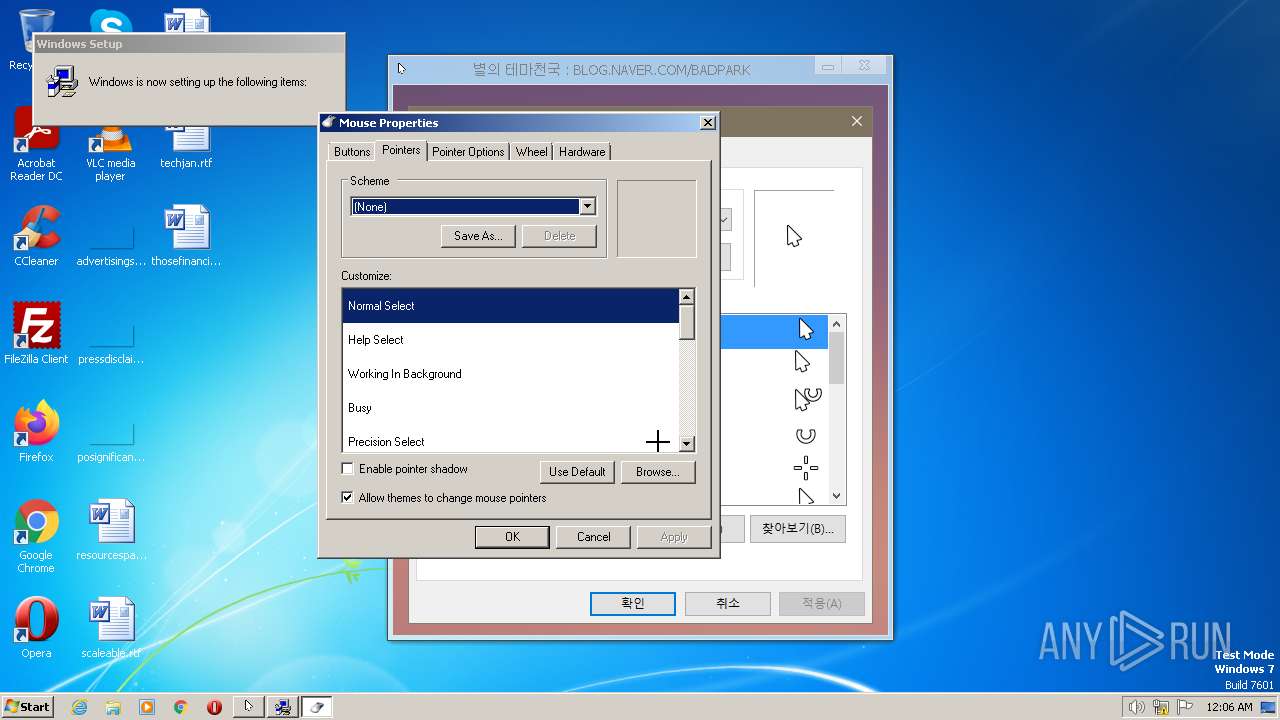
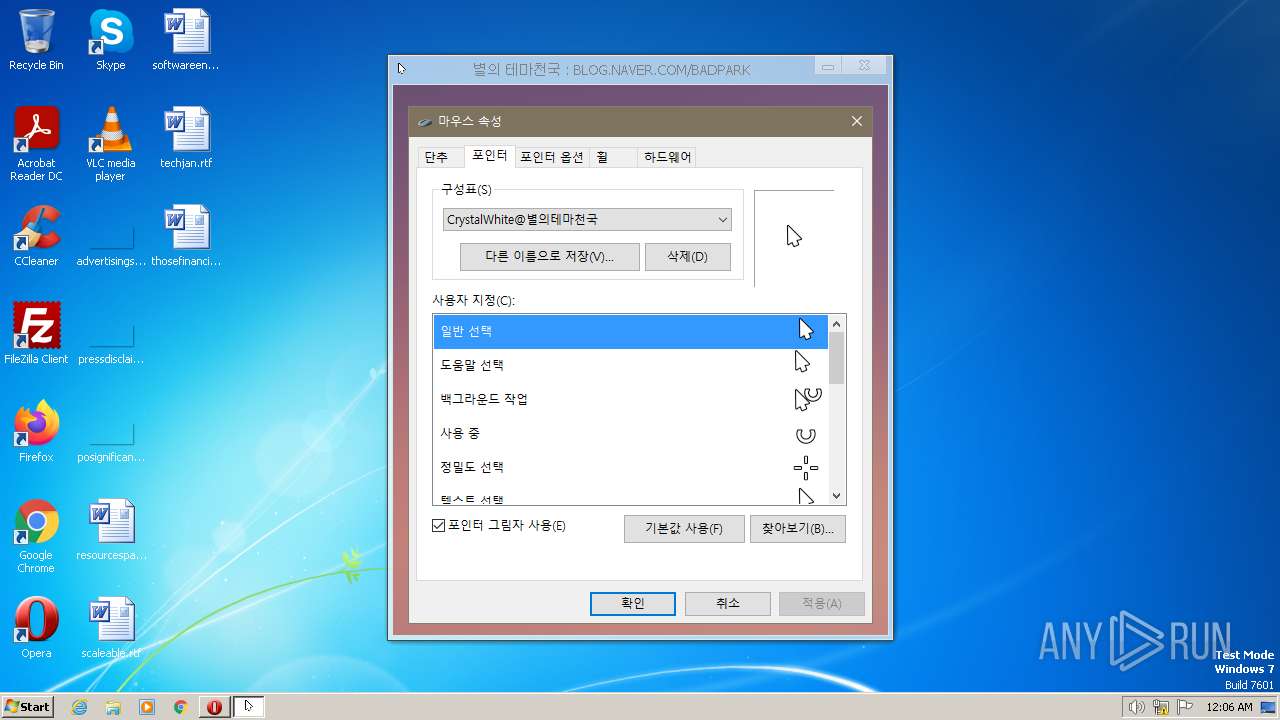
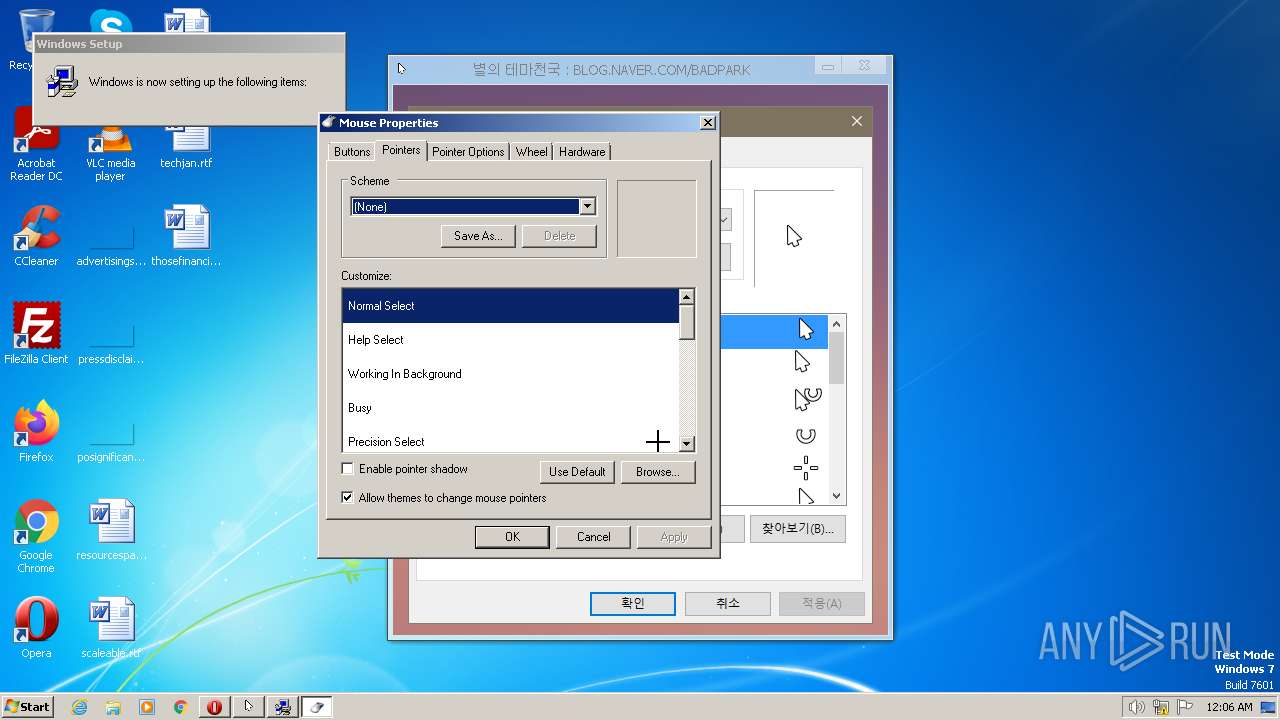
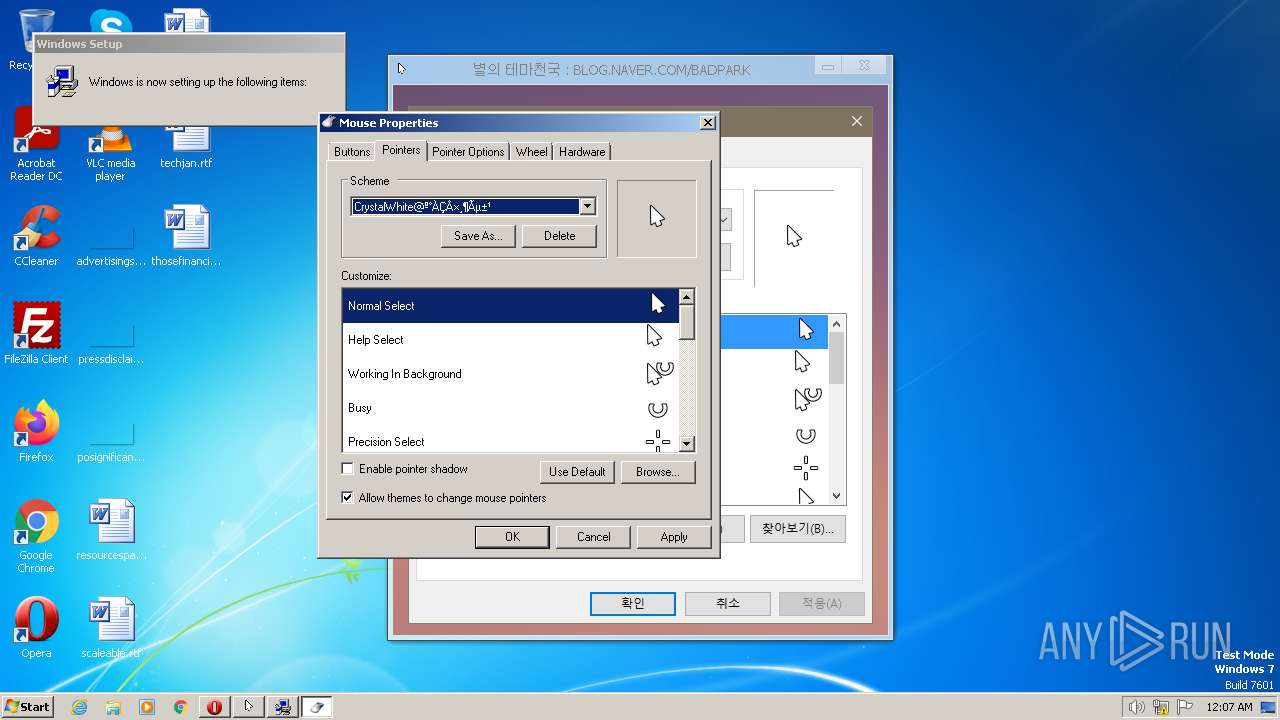
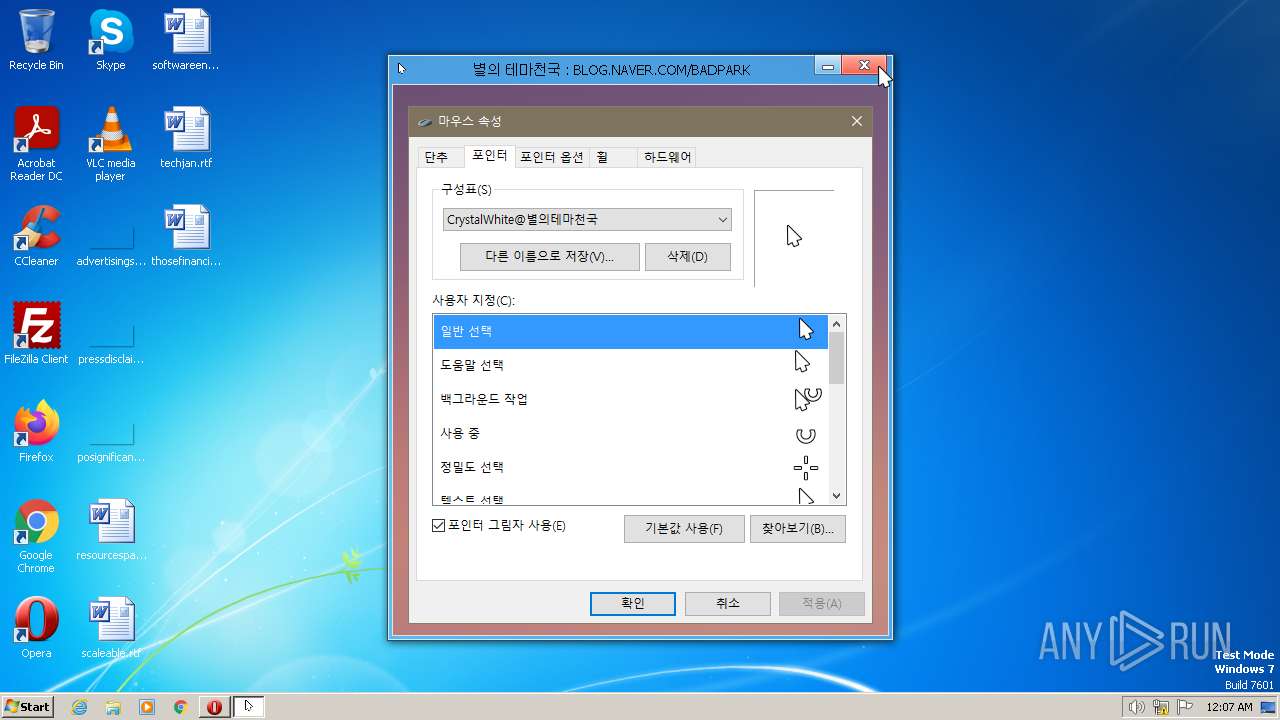
| ProductName: | 별의 테마천국 :: BLOG.NAVER.COM/BADPARK |
| LegalCopyright: | 2013 |
| FileVersion: | 1.0.0.0 |
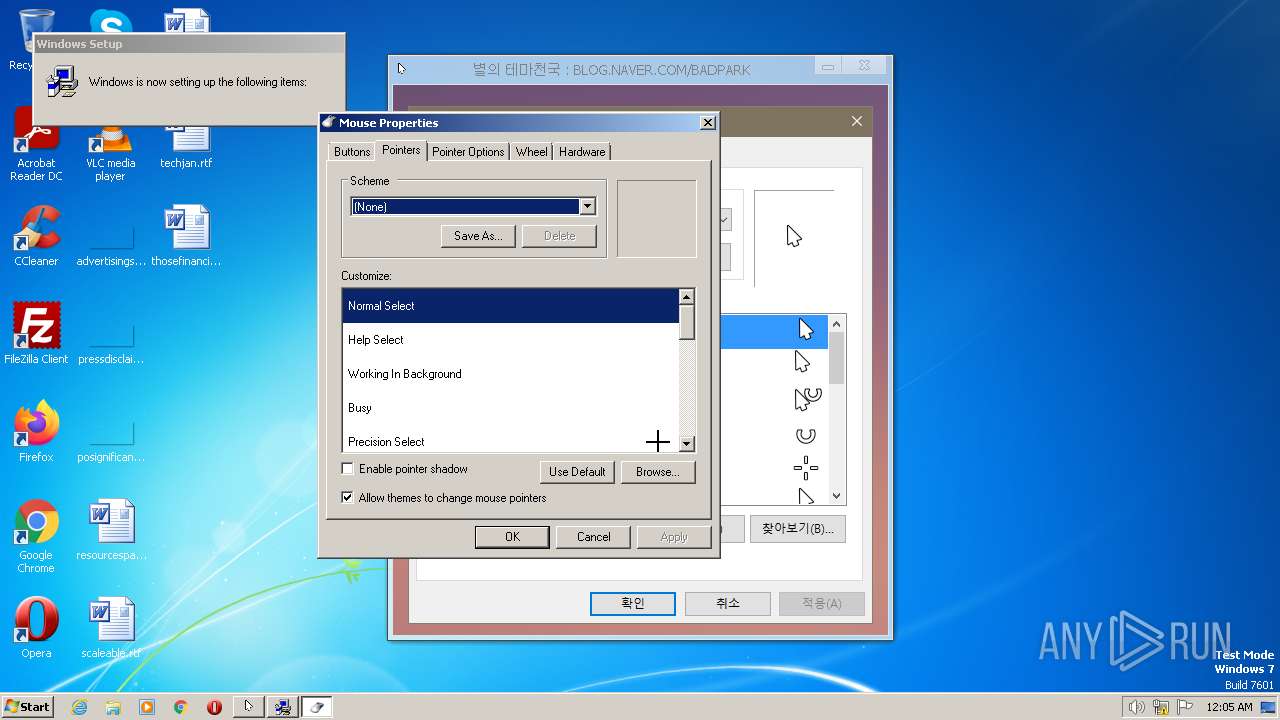
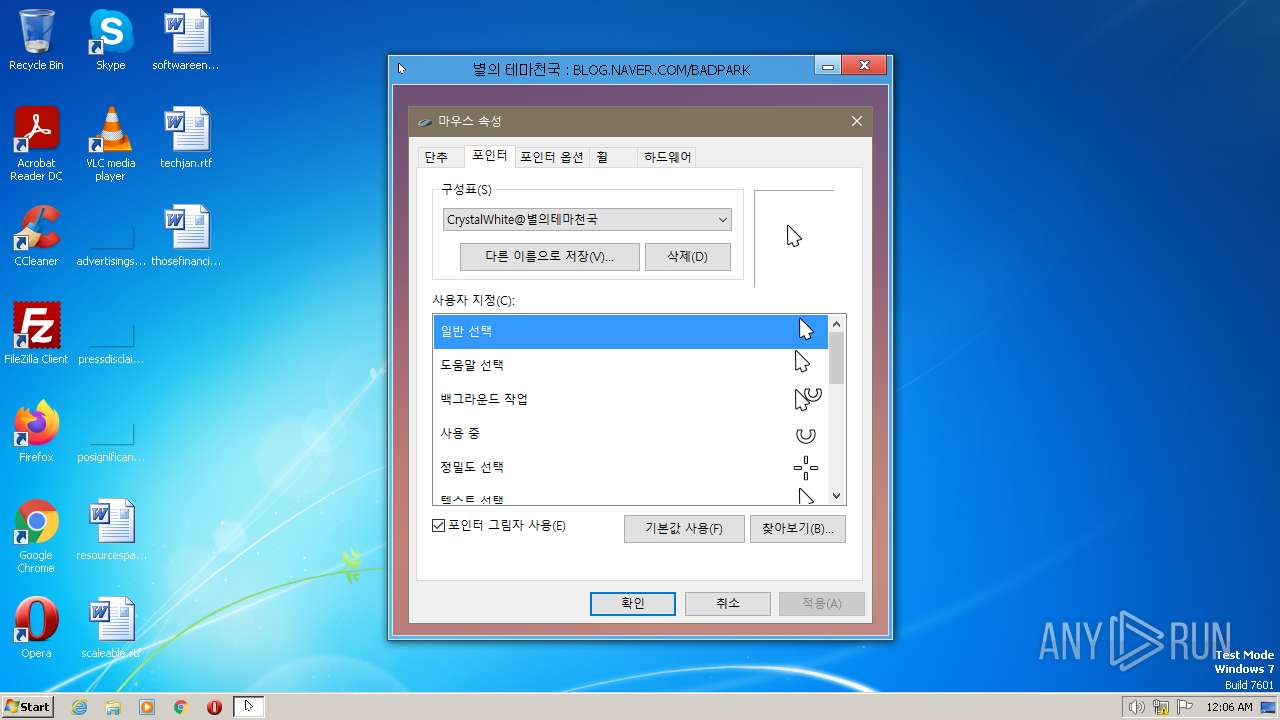
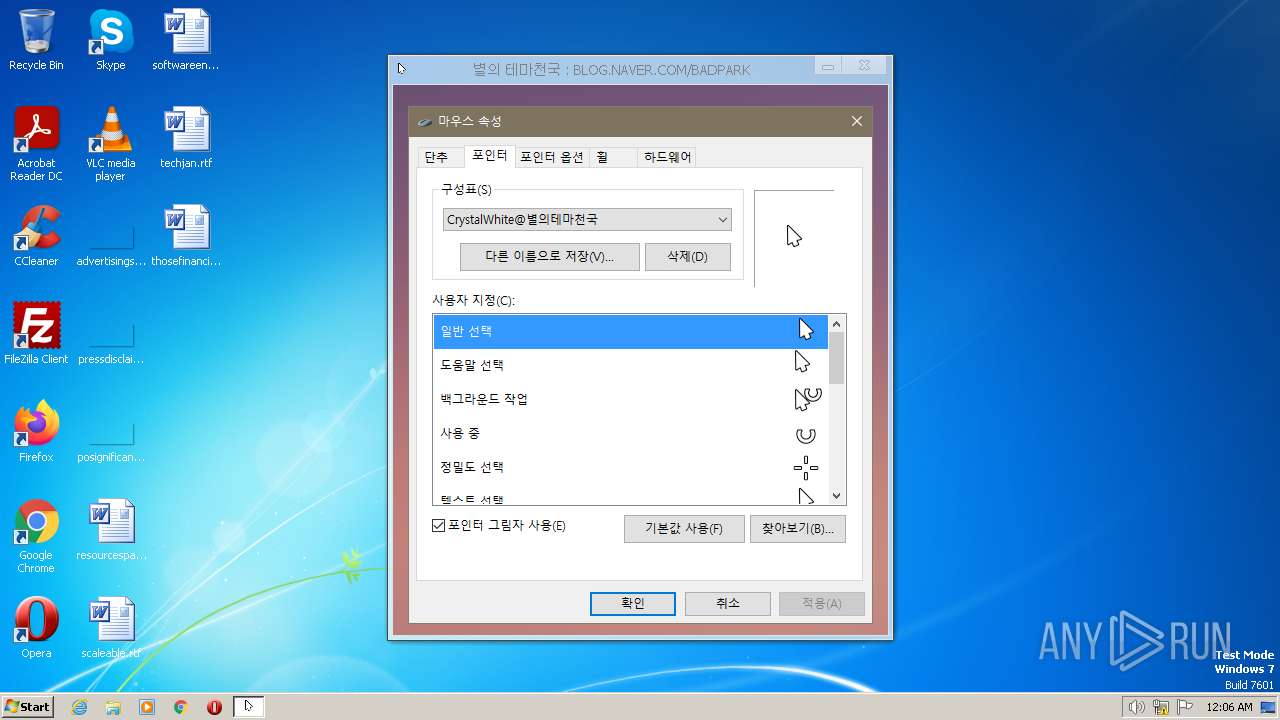
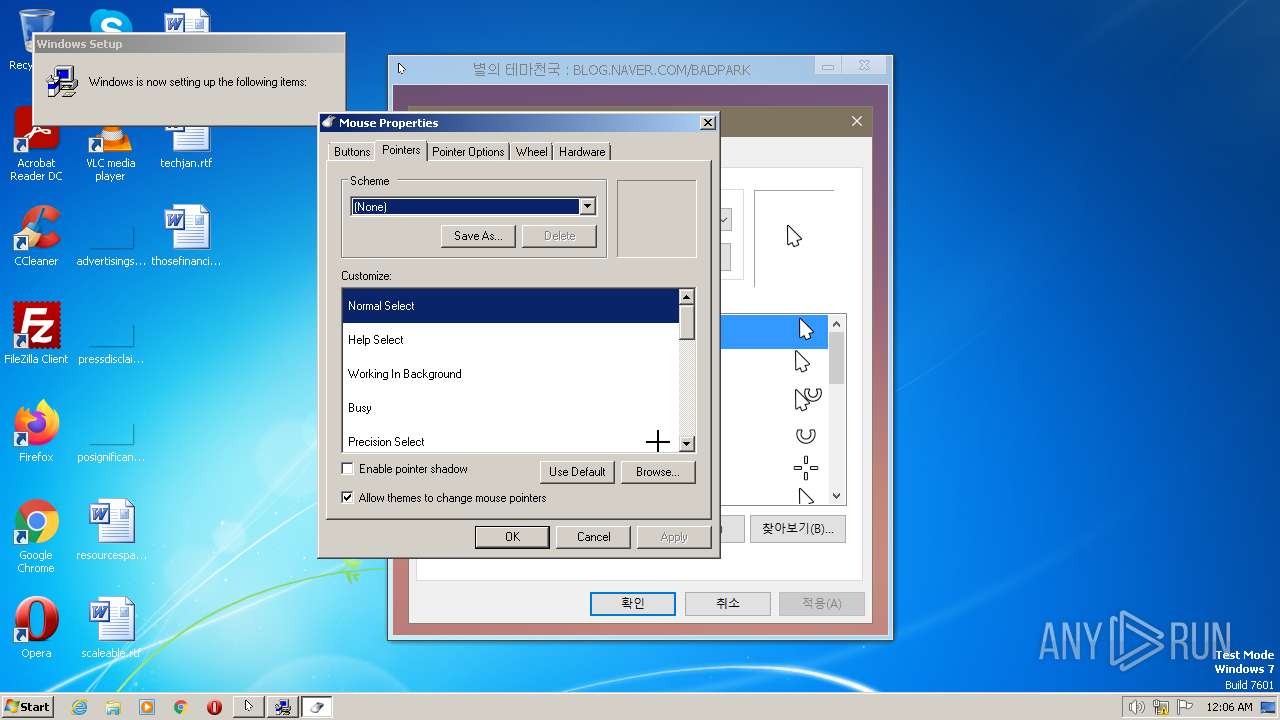
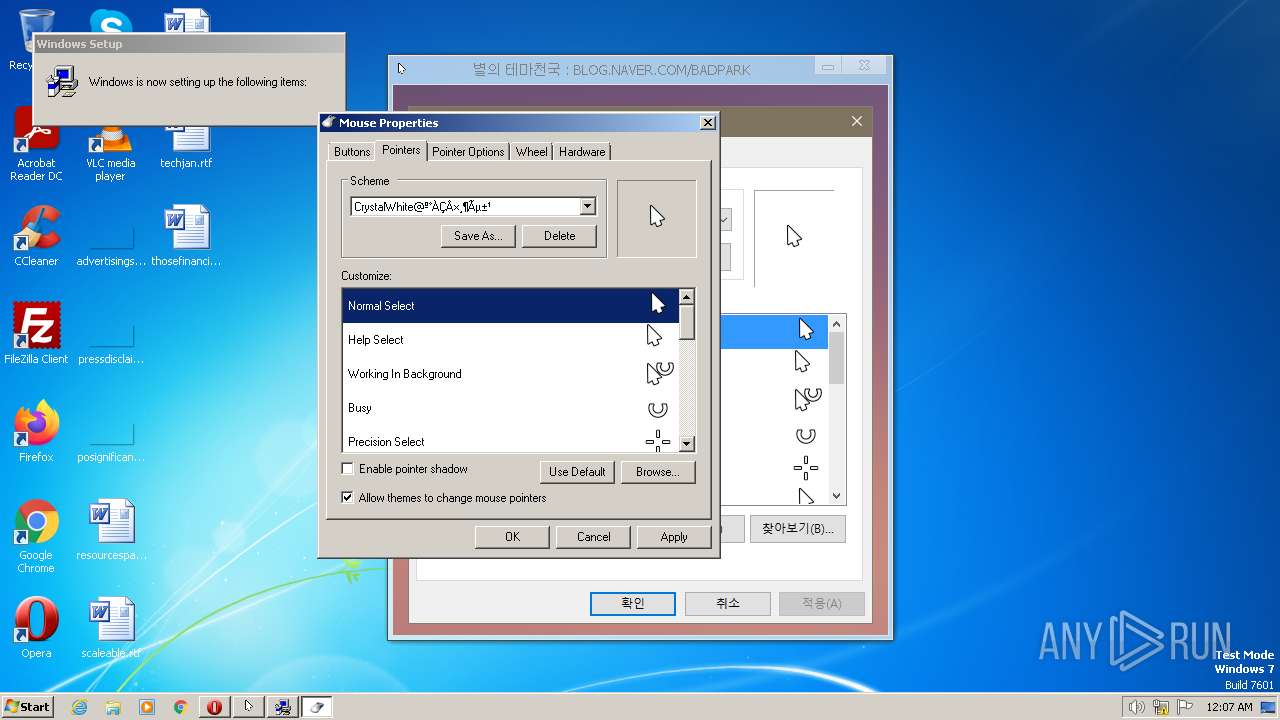
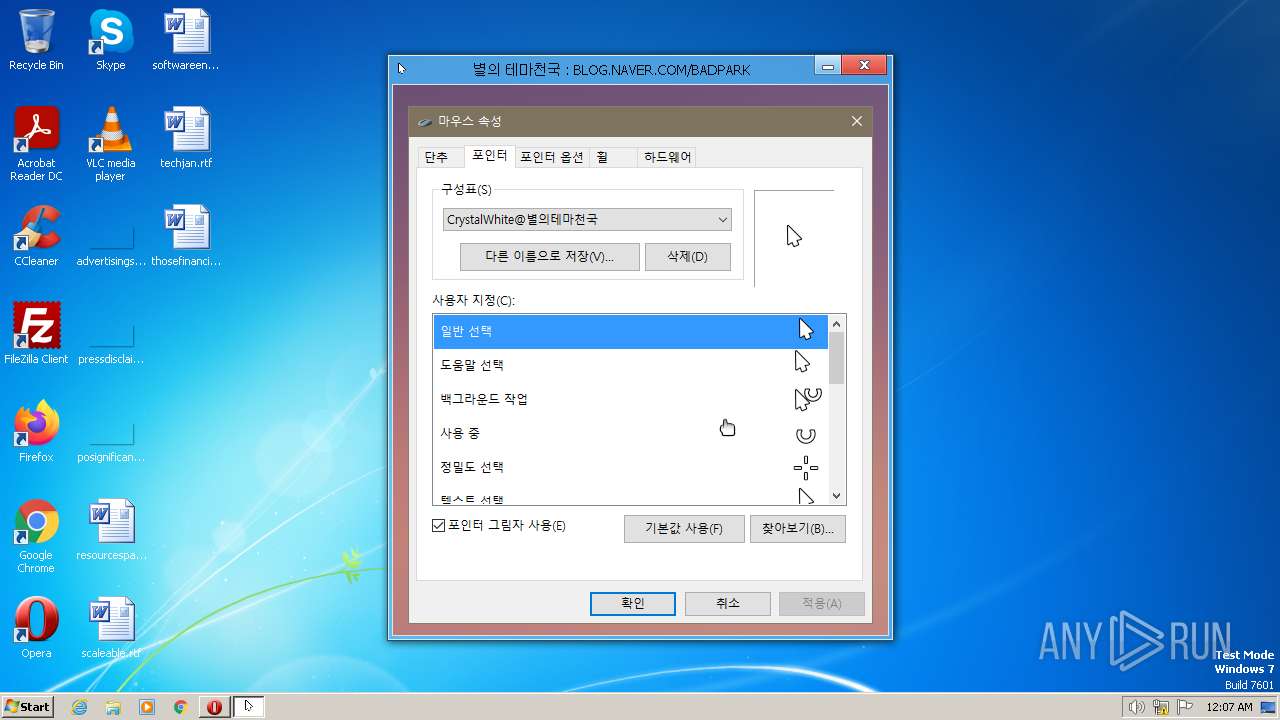
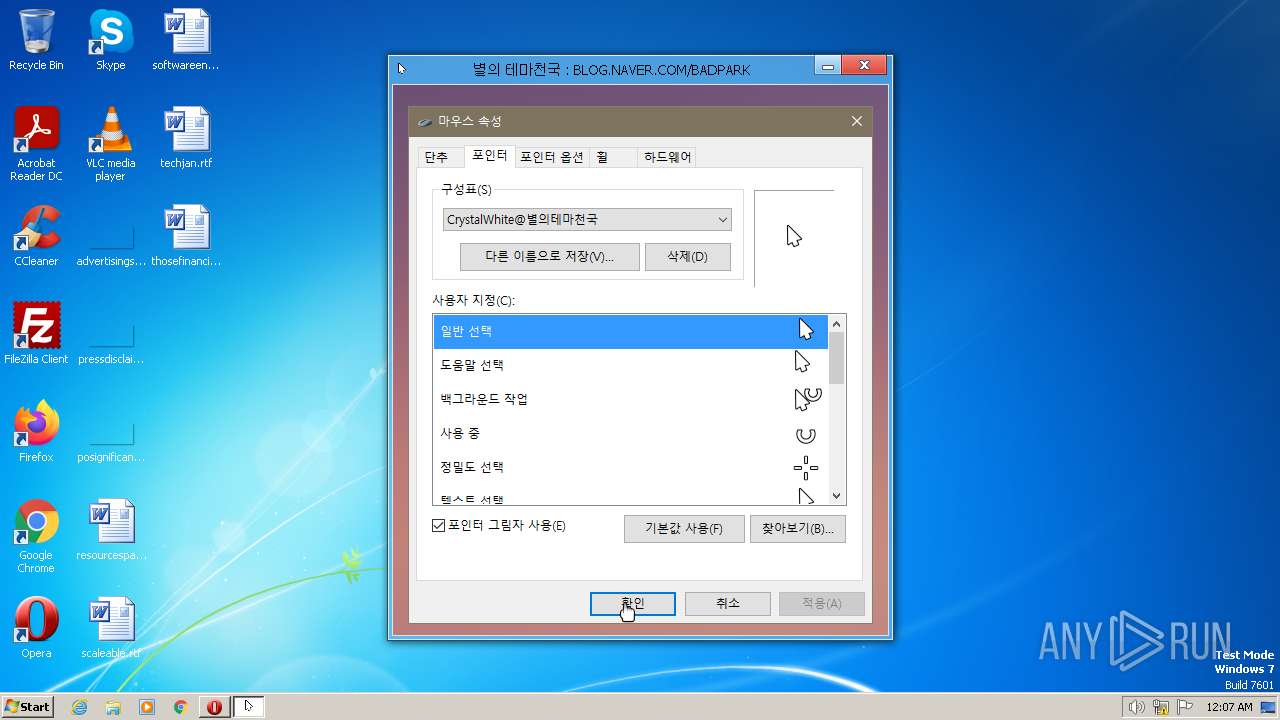
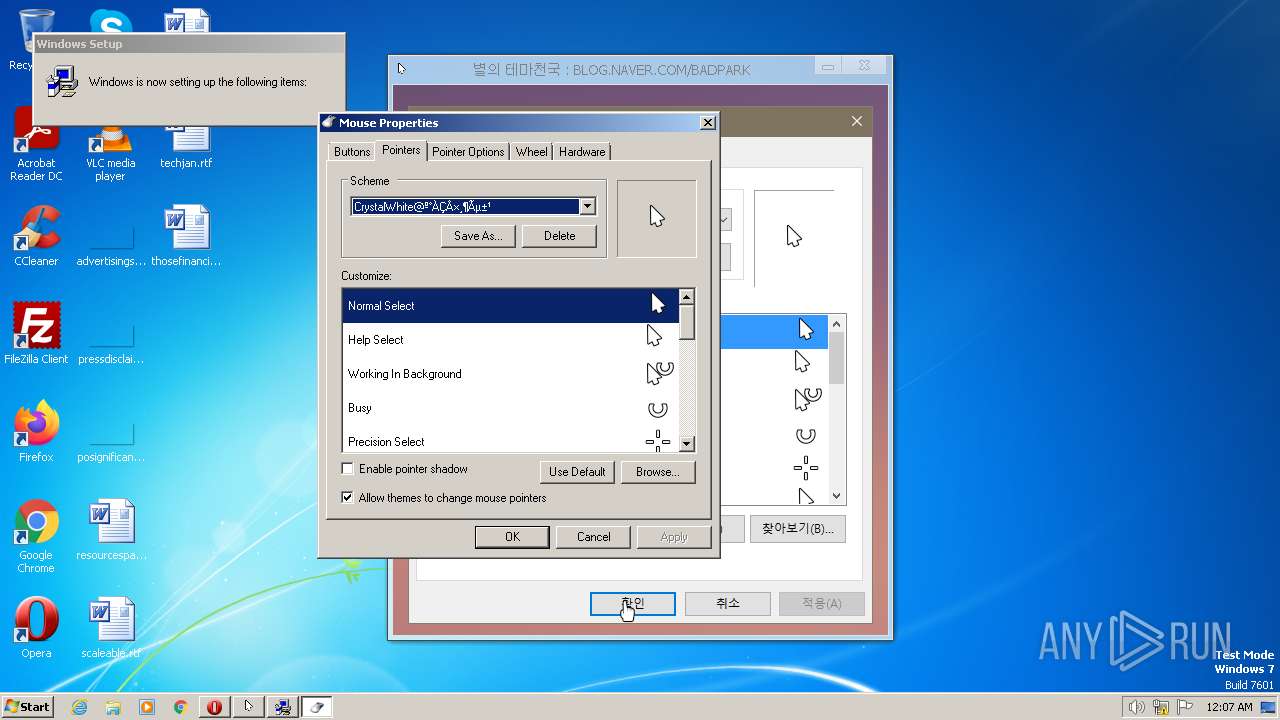
| FileDescription: | Fashion Mouse Cursor |
| CompanyName: | 바탕화면 천국 |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x4be334 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 3136512 |
| CodeSize: | 5349888 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| TimeStamp: | 2013:03:26 21:28:15+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Mar-2013 21:28:15 |
| Detected languages: |
|
| CompanyName: | 바탕화면 천국 |
| FileDescription: | Fashion Mouse Cursor |
| FileVersion: | 1.0.0.0 |
| LegalCopyright: | 2013 |
| ProductName: | 별의 테마천국 :: BLOG.NAVER.COM/BADPARK |
| ProductVersion: | 1.0.0.0 |
| Comments: | Built with HTML Executable, http://www.htmlexe.com |
| Web: | http://www.hdwallpaper.kr |
| Email: | skystars@hanmail.net |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 12 |
| Time date stamp: | 26-Mar-2013 21:28:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x004BAB94 | 0x004BAC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.38786 |
.itext | 0x004BC000 | 0x0000235C | 0x00002400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.33845 |
.data | 0x004BF000 | 0x0012A5FC | 0x0012A600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.44523 |
.bss | 0x005EA000 | 0x0000B084 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x005F6000 | 0x000052D0 | 0x00005400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.24176 |
.didata | 0x005FC000 | 0x0000104C | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.29872 |
.tls | 0x005FE000 | 0x00000044 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x005FF000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.210826 |
.reloc | 0x00600000 | 0x00051F28 | 0x00052000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.69837 |
.res1 | 0x00652000 | 0x00000003 | 0x00000200 | 0.0611629 | |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.14607 | 1459 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 2.31836 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
3 | 3.00046 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4 | 2.56318 | 308 | UNKNOWN | English - United States | RT_CURSOR |
5 | 2.6949 | 308 | UNKNOWN | English - United States | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | English - United States | RT_CURSOR |
8 | 2.86115 | 308 | UNKNOWN | English - United States | RT_CURSOR |
9 | 2.77296 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
10 | 2.34875 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
Imports
IMAGEHLP.DLL |
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
gdiplus.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
mpr.dll |
msvcrt.dll |
Total processes
113
Monitored processes
50
Malicious processes
1
Suspicious processes
13
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Windows\System32\InfDefaultInstall.exe" "C:\Users\admin\AppData\Local\Temp\RarSFX1\install.inf" | C:\Windows\System32\InfDefaultInstall.exe | hefF098.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: INF Default Install Exit code: 0 Version: 5.2.3668.0 Modules
| |||||||||||||||
| 752 | "C:\Windows\system32\runonce.exe" -r | C:\Windows\System32\runonce.exe | — | InfDefaultInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1016 | "C:\Windows\System32\runonce.exe" | C:\Windows\System32\runonce.exe | — | runonce.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1024 | "C:\Windows\system32\runonce.exe" -r | C:\Windows\System32\runonce.exe | — | InfDefaultInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1148 | "C:\Users\admin\AppData\Local\Temp\hegC8FA\hefF098.exe" | C:\Users\admin\AppData\Local\Temp\hegC8FA\hefF098.exe | — | Mouse.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1148 | "C:\Windows\System32\grpconv.exe" -o | C:\Windows\System32\grpconv.exe | — | runonce.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1160 | "C:\Windows\System32\runonce.exe" | C:\Windows\System32\runonce.exe | — | runonce.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
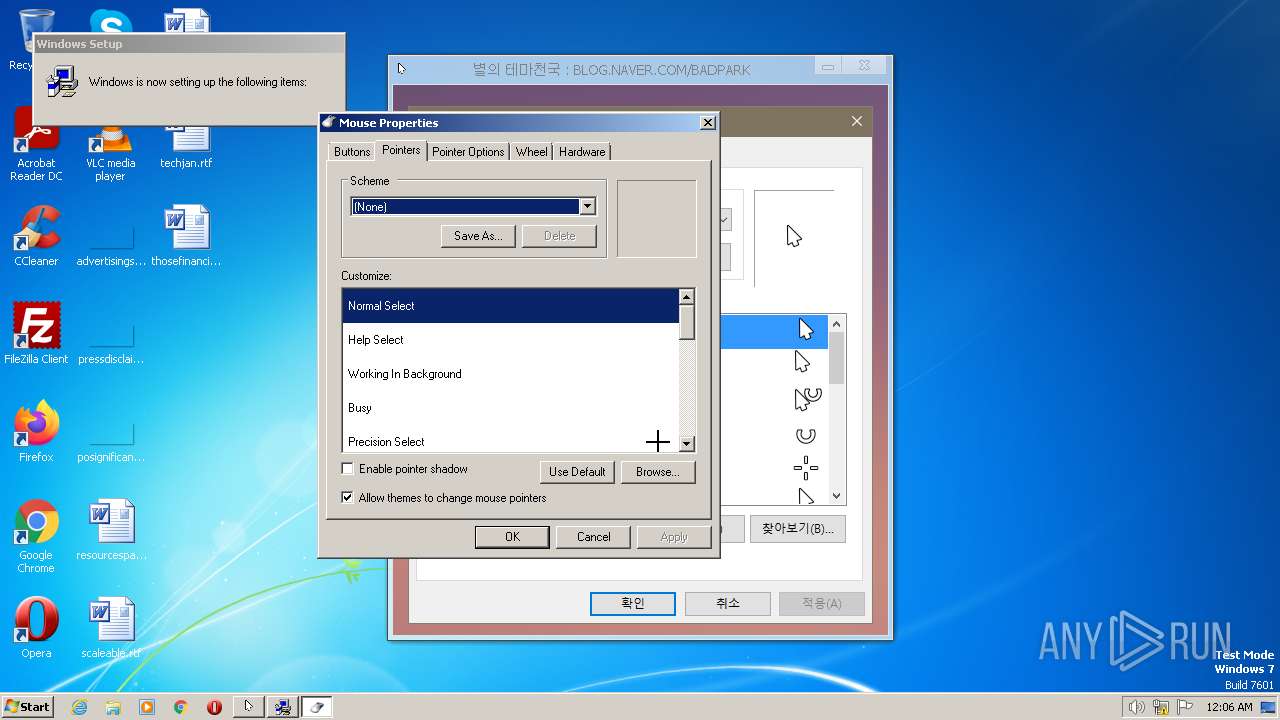
| 1216 | rundll32.exe shell32.dll,Control_RunDLL main.cpl @0,1 | C:\Windows\System32\rundll32.exe | — | runonce.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1276 | "C:\Windows\System32\InfDefaultInstall.exe" "C:\Users\admin\AppData\Local\Temp\RarSFX0\install.inf" | C:\Windows\System32\InfDefaultInstall.exe | — | hefF098.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: INF Default Install Exit code: 3221226540 Version: 5.2.3668.0 Modules
| |||||||||||||||
| 1280 | "C:\Windows\system32\runonce.exe" -r | C:\Windows\System32\runonce.exe | — | InfDefaultInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
8 537
Read events
8 258
Write events
258
Delete events
21
Modification events
| (PID) Process: | (3140) Mouse.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3140) Mouse.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3140) Mouse.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3140) Mouse.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3616) hefF098.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3616) hefF098.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3616) hefF098.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3616) hefF098.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3616) hefF098.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
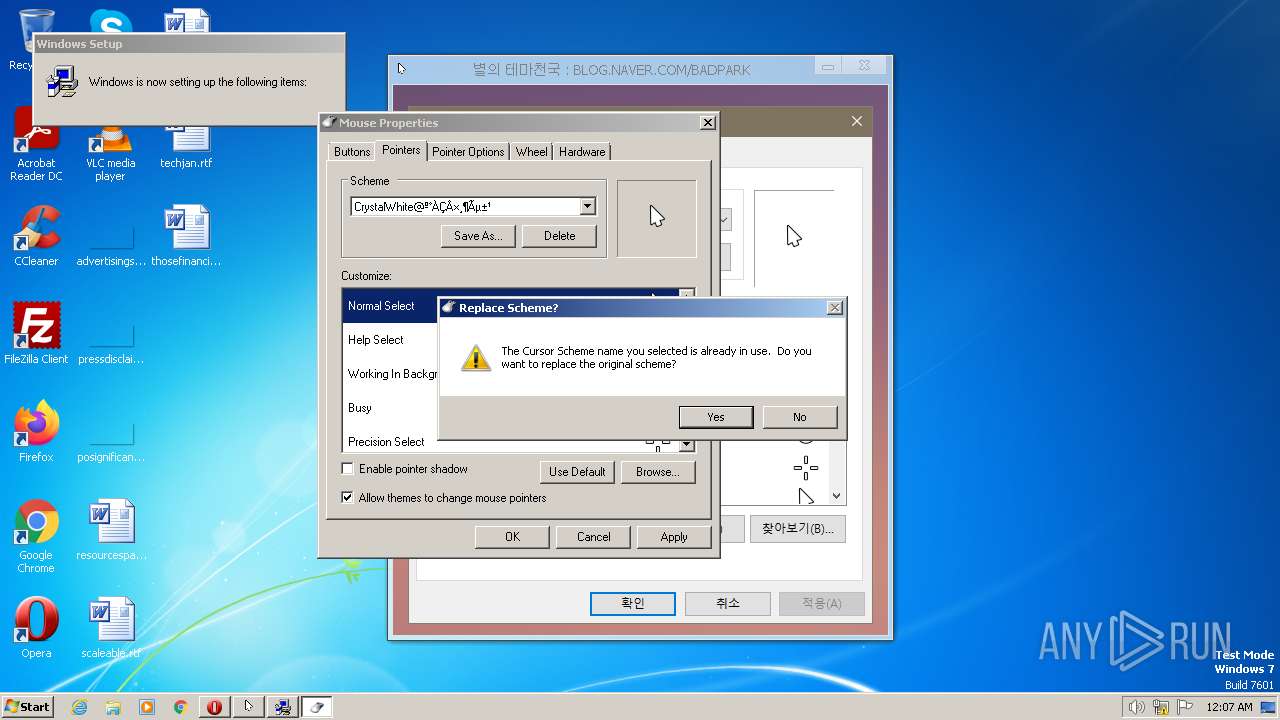
| (PID) Process: | (1892) runonce.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | delete value | Name: | Wrapper |
Value: runonce | |||
Executable files
2
Suspicious files
390
Text files
2
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
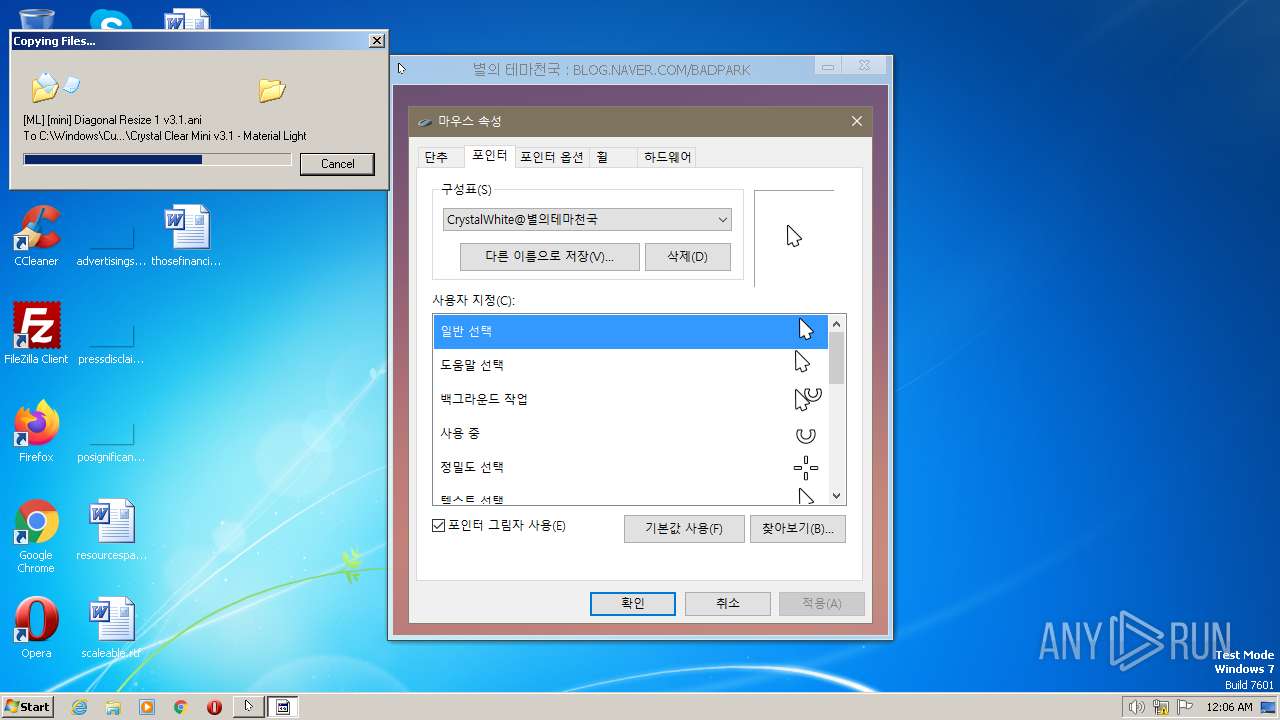
| 3616 | hefF098.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\[ML] [mini] Help Select v3.1.ani | binary | |
MD5:97CCA17CF29326F4F4232C3D6CB95100 | SHA256:21F790AD71CCB88F5771B5E5A5D3536B20967C1DC462AFAE5D6FBDDA6359CCA5 | |||
| 3140 | Mouse.exe | C:\Users\admin\AppData\Local\Temp\hegC8FA\hefF098.exe | executable | |
MD5:5E506E0404D8E30F6F55AC79FEE1790C | SHA256:C8353E410EF8A7D8968916AB9218F117693BA5C7D9B92F9CCBC5D115E9C5435E | |||
| 3616 | hefF098.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\[ML] [mini] Move v3.1.ani | binary | |
MD5:055CECCB7F77CFF2C39489B8F9C75CE4 | SHA256:C03AFE10848C9079347F1B953A5DEFCD8DCCFDC59FC1E24E56E899E84BEC67E6 | |||
| 3616 | hefF098.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\[ML] [mini] Diagonal Resize 2 v3.1.ani | binary | |
MD5:3C2B2A9DACAEE0D2027B94812EA20384 | SHA256:8F19D8118D5700BFEB4FD6666FF4DF4BFC7E311A7E80FE0C386F5E90DCE36C20 | |||
| 3616 | hefF098.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\[ML] [mini] Handwriting v3.1.ani | binary | |
MD5:076DE33FC2BDDEEDCCC382966400825E | SHA256:EB72C723ABF1EBE587C97DBF04B3FDCF720C98CADE1BDC242B5986D337273E14 | |||
| 3616 | hefF098.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\[ML] [mini] Normal Select v3.1.cur | binary | |
MD5:AF3A79482990AD1C6B6E1BFC5A30DAA6 | SHA256:2B862DFE6AC8688FA5FDC09EFCF8501B3CD35DC9A9C683600D8EEE80063344B6 | |||
| 3616 | hefF098.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\[ML] [mini] Unavailable v3.1.ani | binary | |
MD5:0FD5F2D5F5A66E54F3B2B294937A4B1F | SHA256:376F07BFE7D130E677B06F7E6A92B015FCA6971FEFA3ABC4BF437C308D74296B | |||
| 3616 | hefF098.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\[ML] [mini] Text Select v3.1.ani | binary | |
MD5:BA342ADBA814B7B2B413B64F19AA1E7D | SHA256:EC3872C099E22F3A33313E1DD2CED567C7C9FF643711567F6D790DBEAAFC620F | |||
| 3616 | hefF098.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\[ML] [mini] Working In Background v3.1.ani | binary | |
MD5:FE4D57D7449C7C0B84B3344DEA83FD97 | SHA256:F099981A8D6A76082DF38EA42707119217A8AFE91F61B58A562C7C3CF830C5B0 | |||
| 3616 | hefF098.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\install.inf | binary | |
MD5:7E5C579C172C139EF31C31A5AD0E7865 | SHA256:113E1C5490831835D53CA4ECB6632DBD475151FDF989412B63CA6E1BDD716E93 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2624 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |