| File name: | skynews-roblox-gaming_4353396.jpg |
| Full analysis: | https://app.any.run/tasks/b36bf99e-65d8-4ad9-a669-cf83ed29e199 |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 19:01:52 |
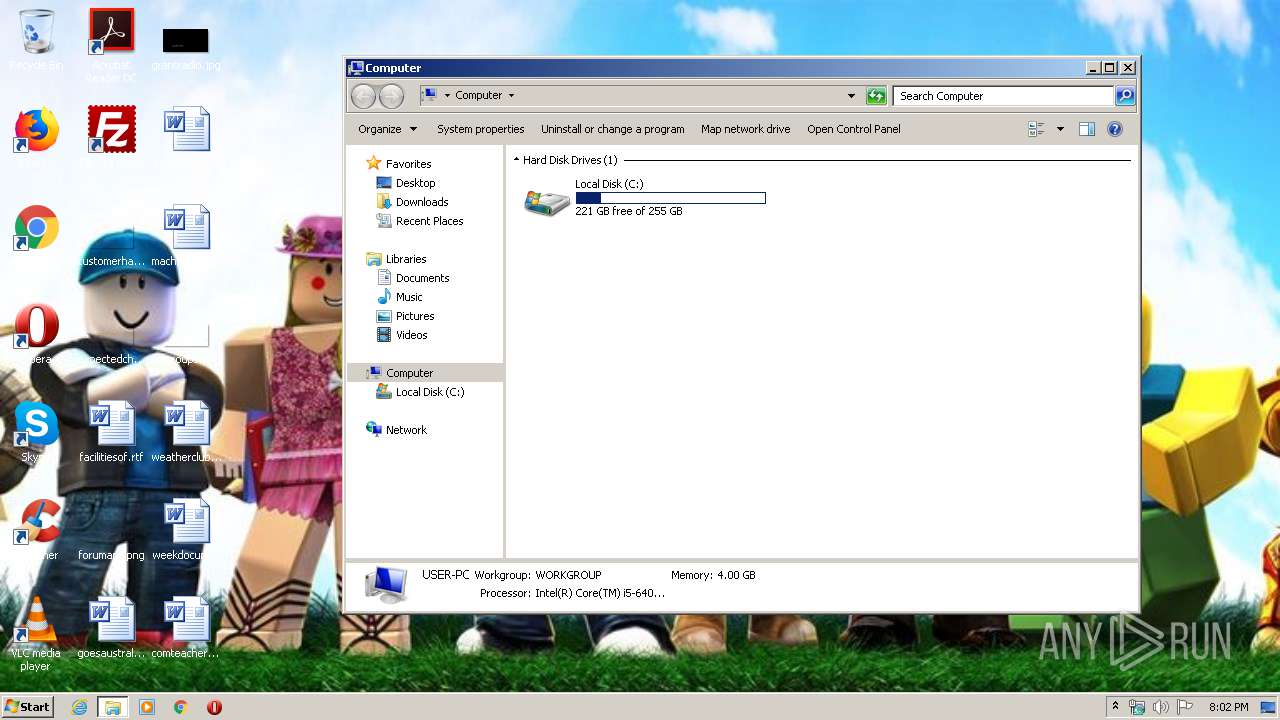
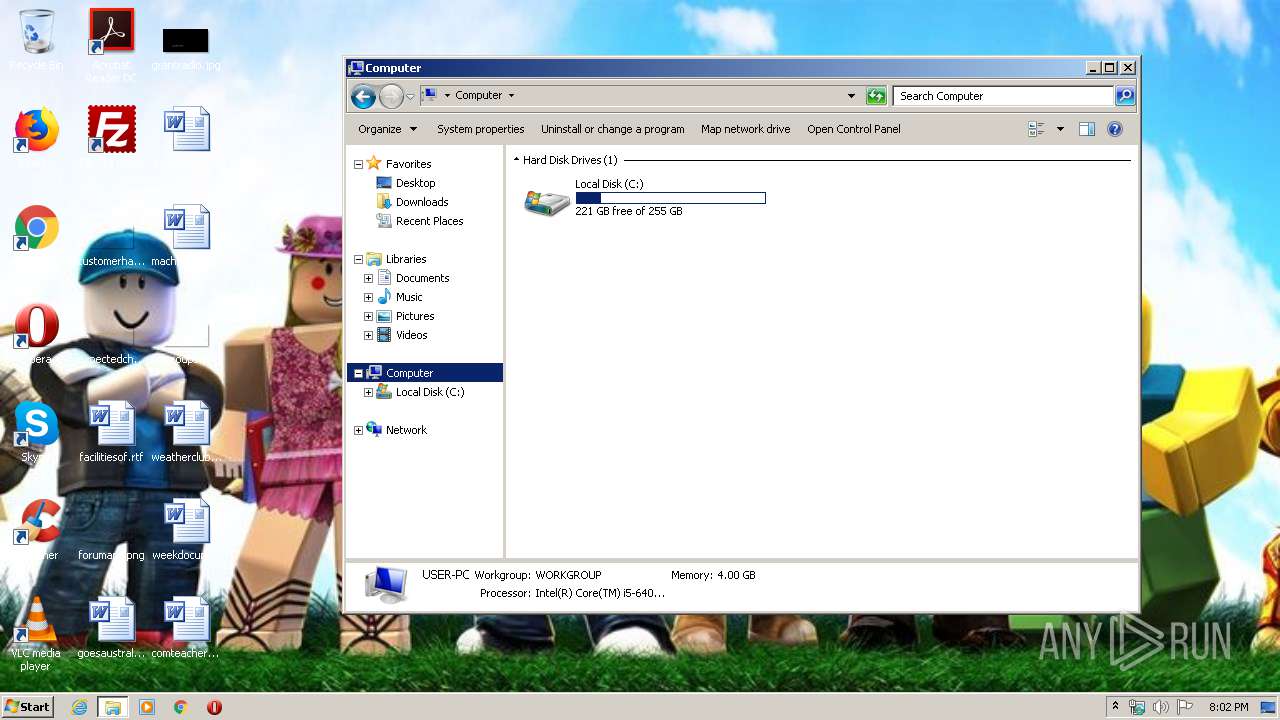
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | image/jpeg |
| File info: | JPEG image data, progressive, precision 8, 768x432, frames 3 |
| MD5: | E6B86B6D7F0F25C11CC1256F932DE4C5 |
| SHA1: | 85FE232BE97EA65DECA30ECBFC71114C53944094 |
| SHA256: | 252DB79D916A456855260945DB58CE7287C3F018DE68E7A62B1A3BBDD727EC75 |
| SSDEEP: | 1536:2efBk/ie/56LzvwqgkAVs7kAQfOgip4DjUoUXts1aMJWublo+IK:rfK/h/yvwdk8s7kX2g84DLU9s1xJWubp |
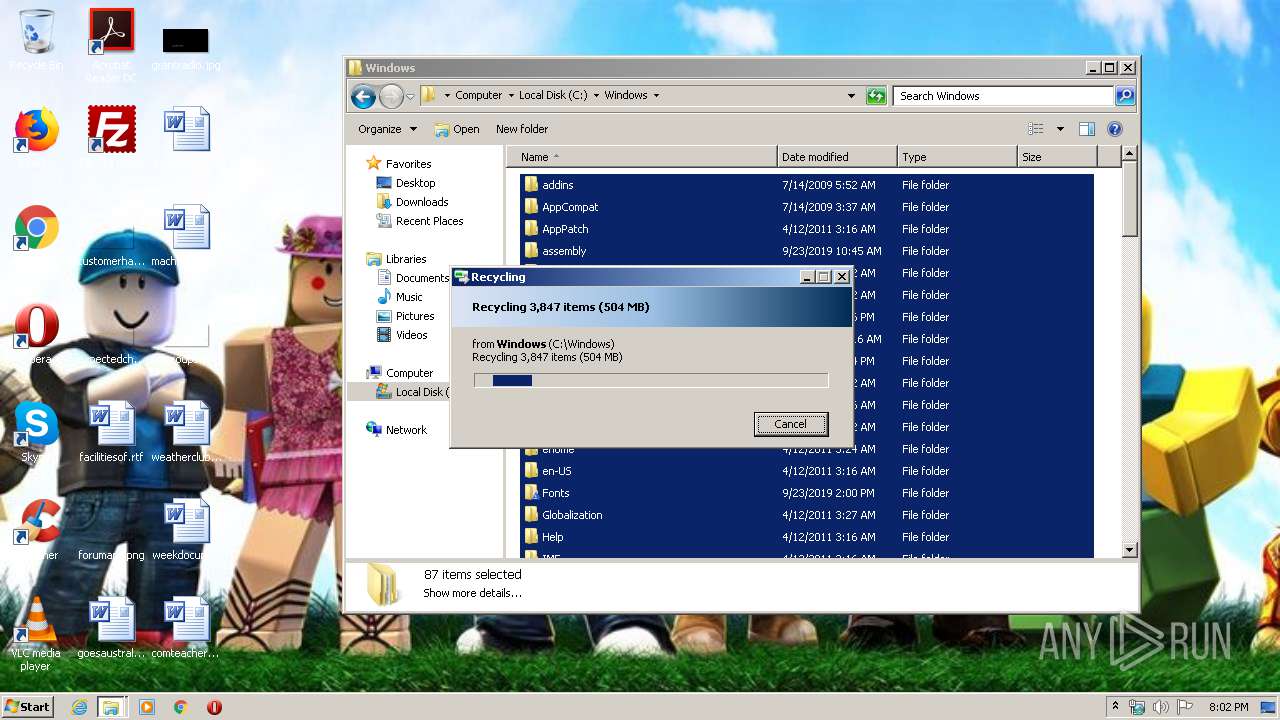
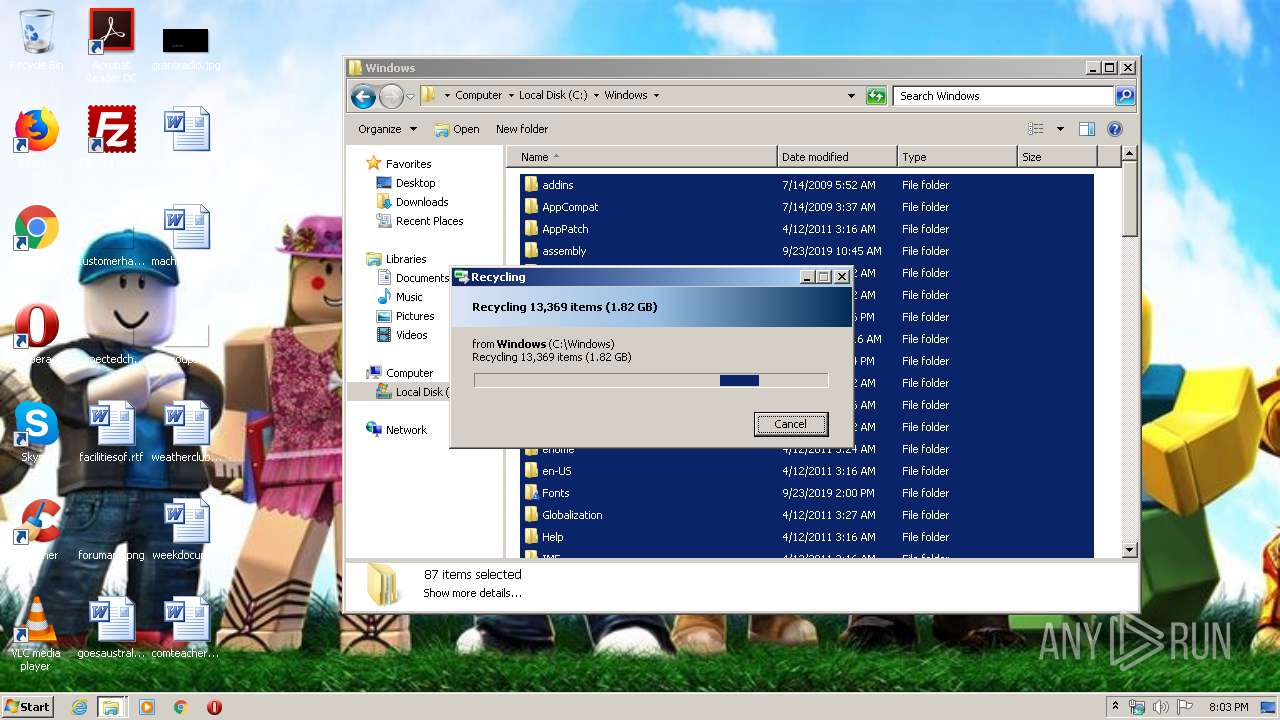
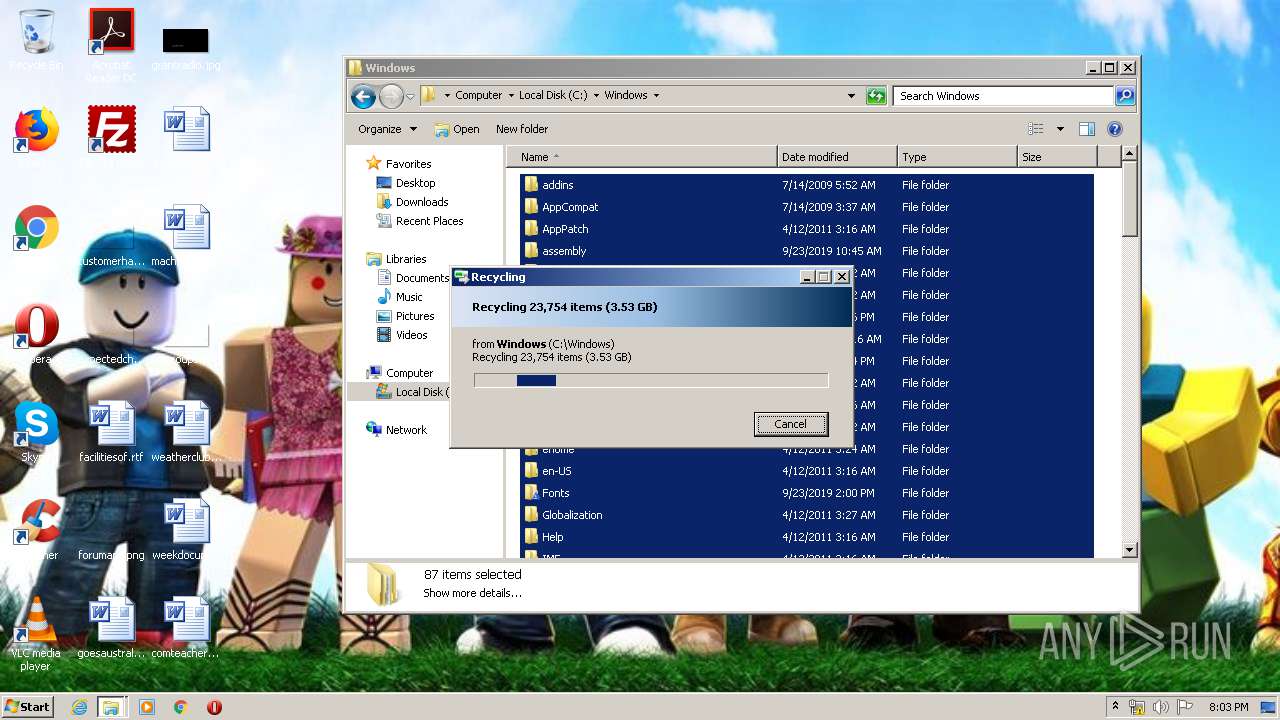
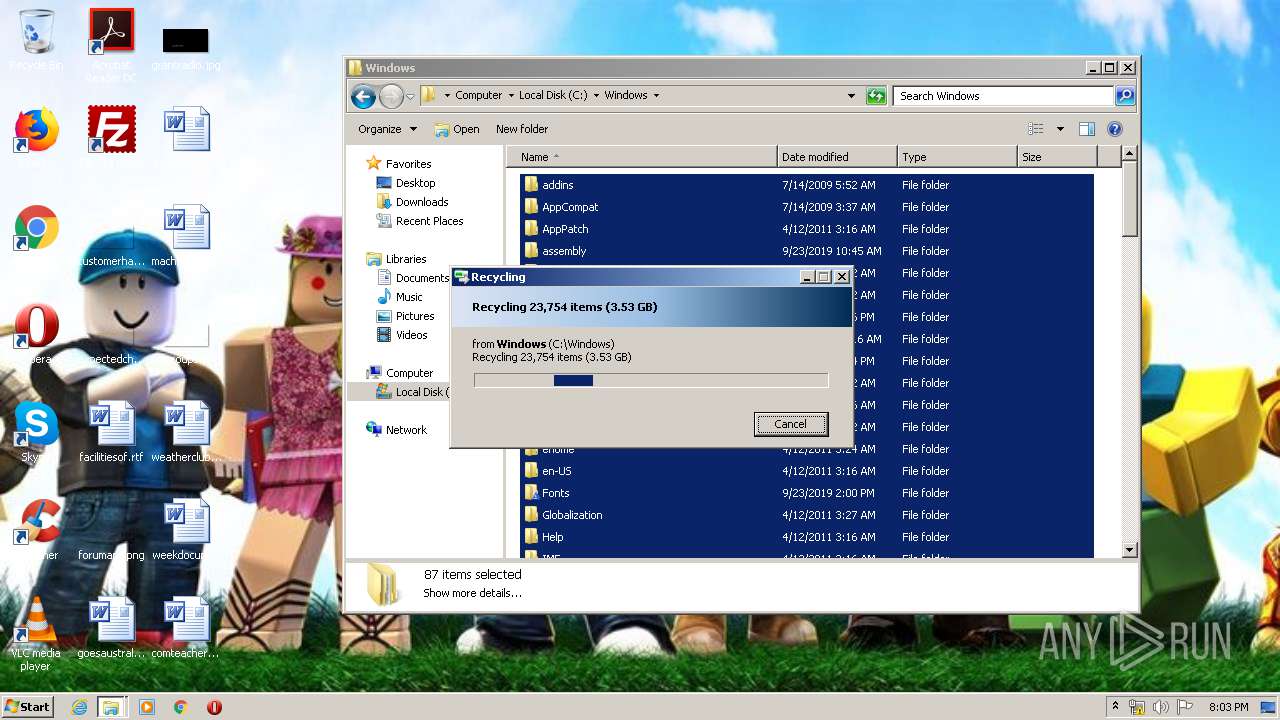
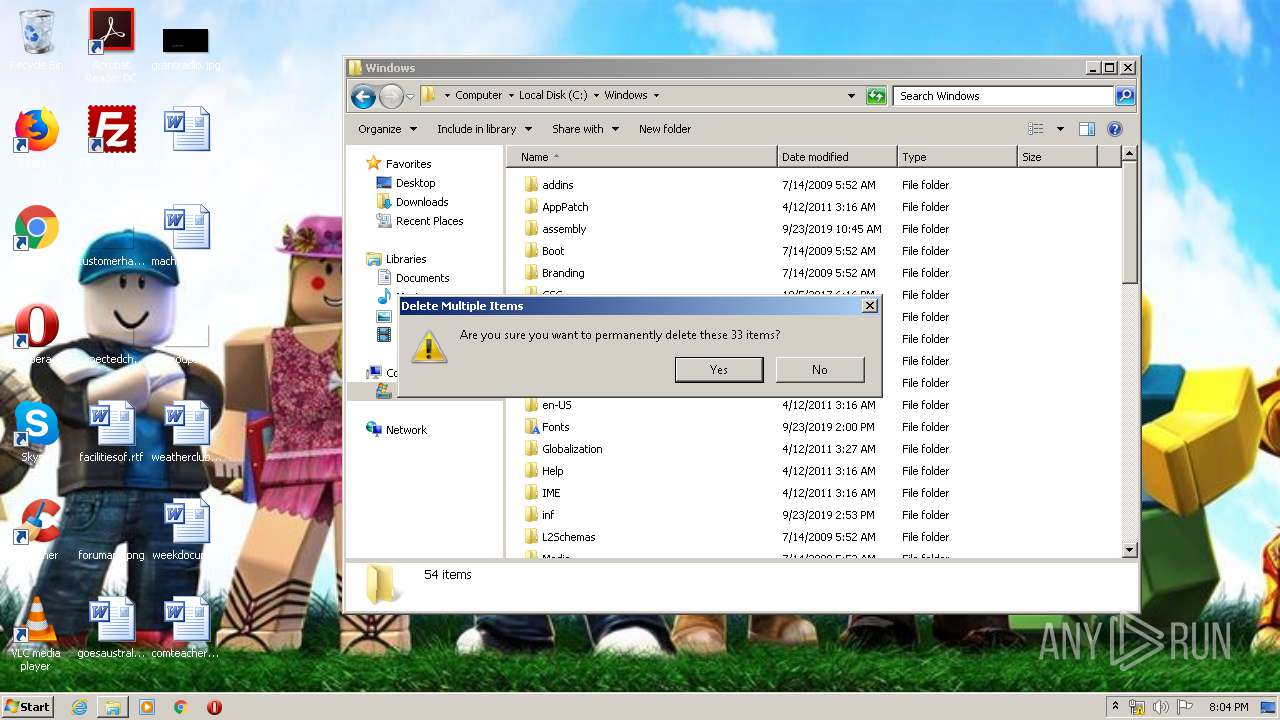
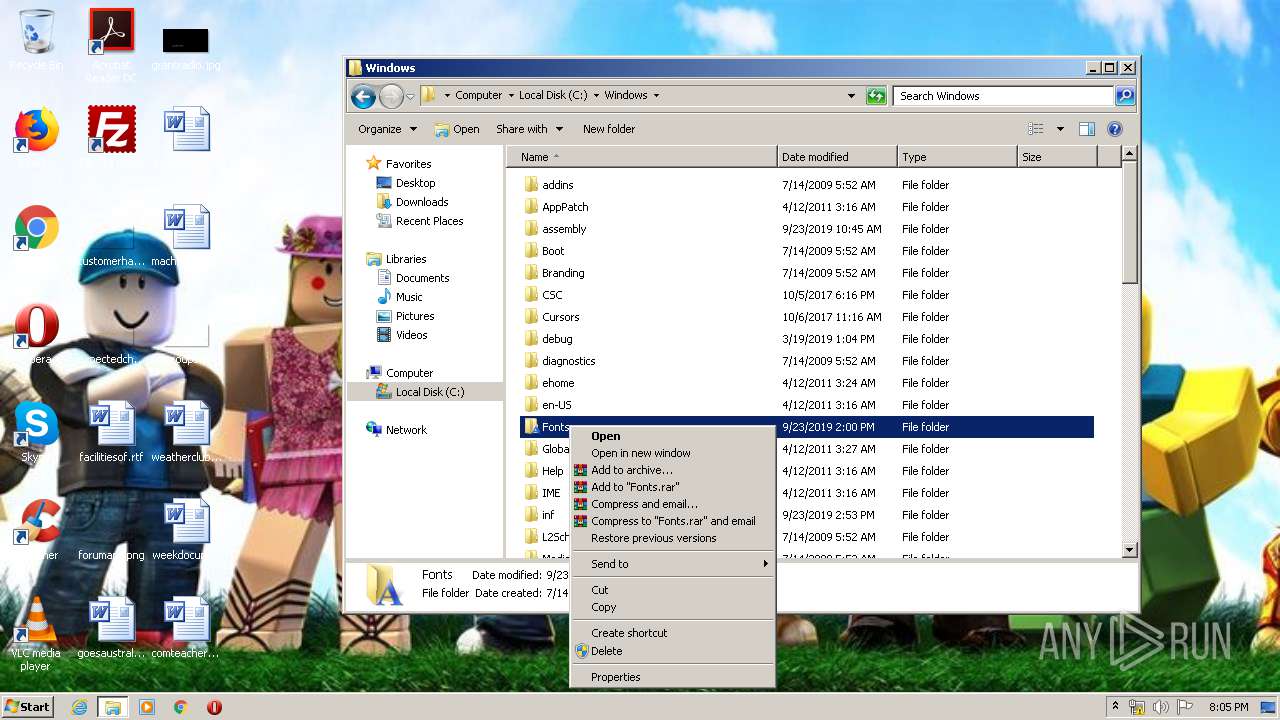
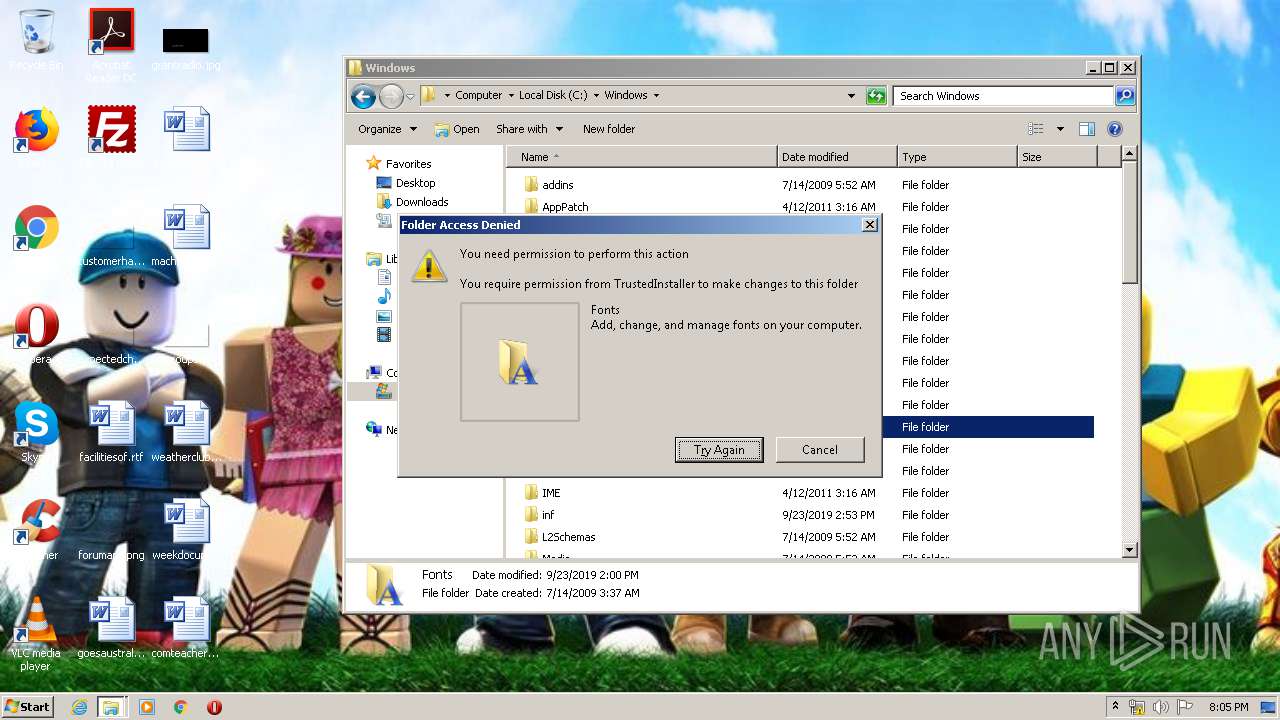
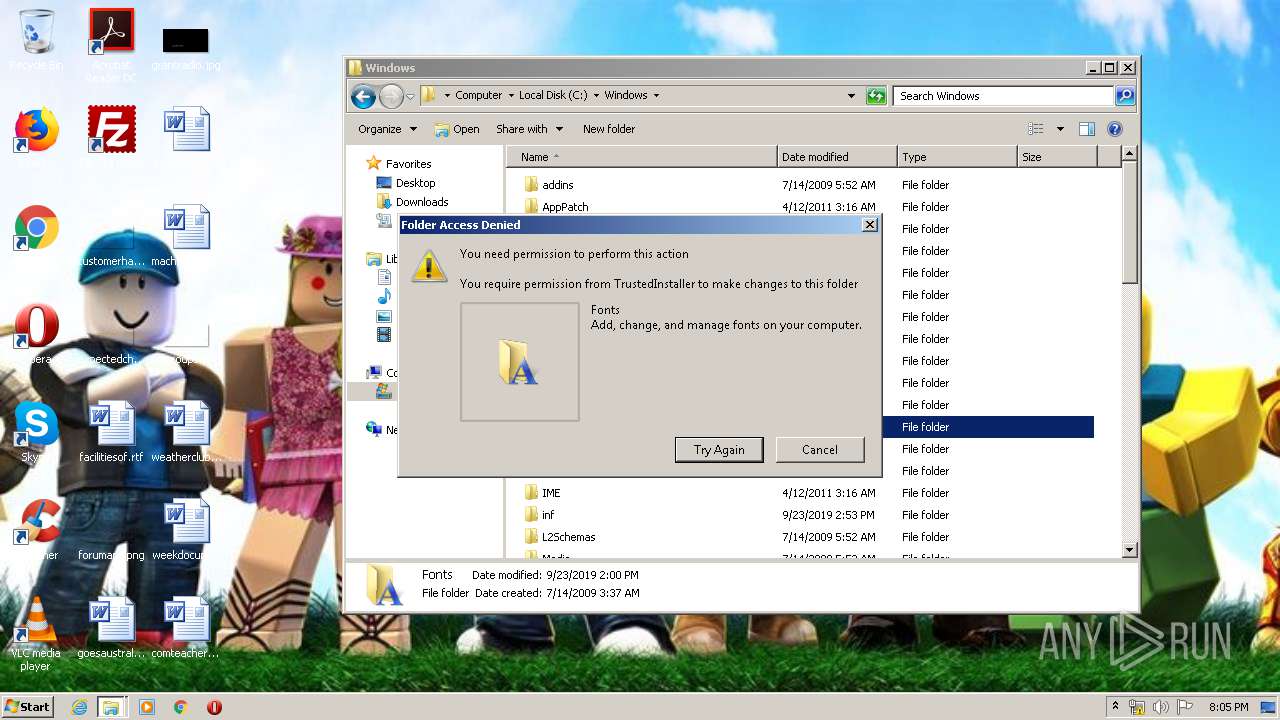
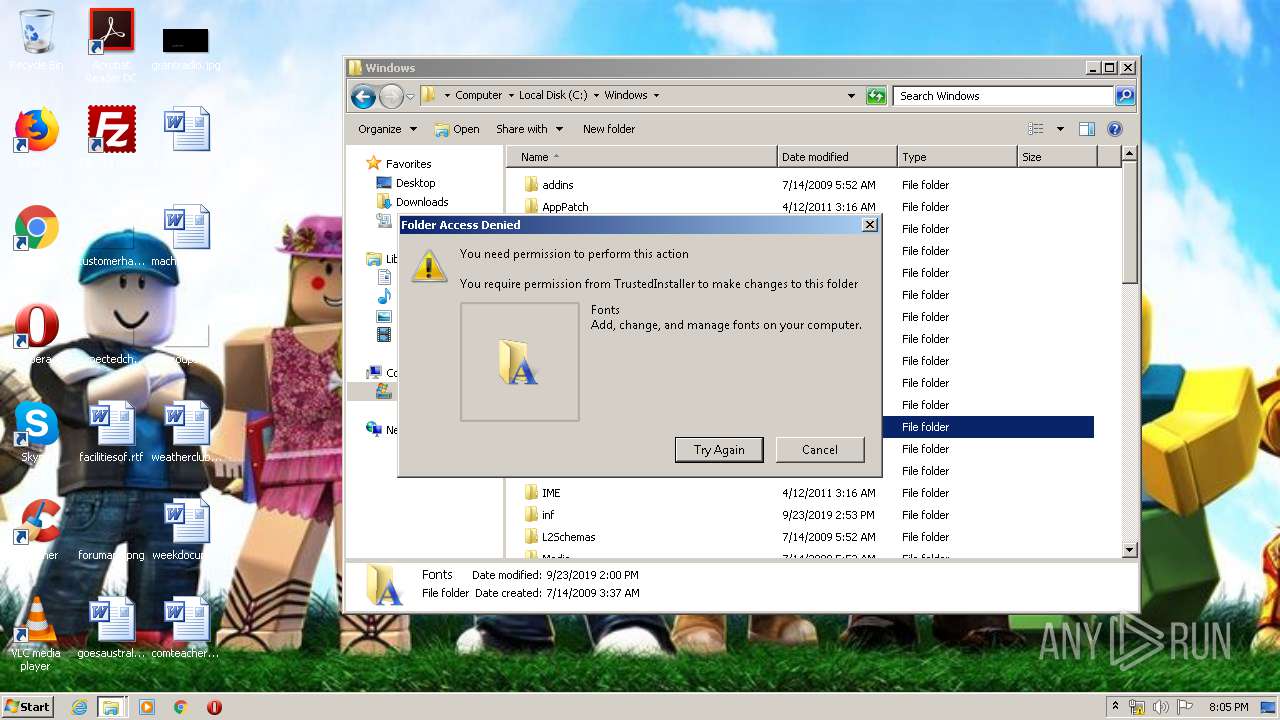
MALICIOUS
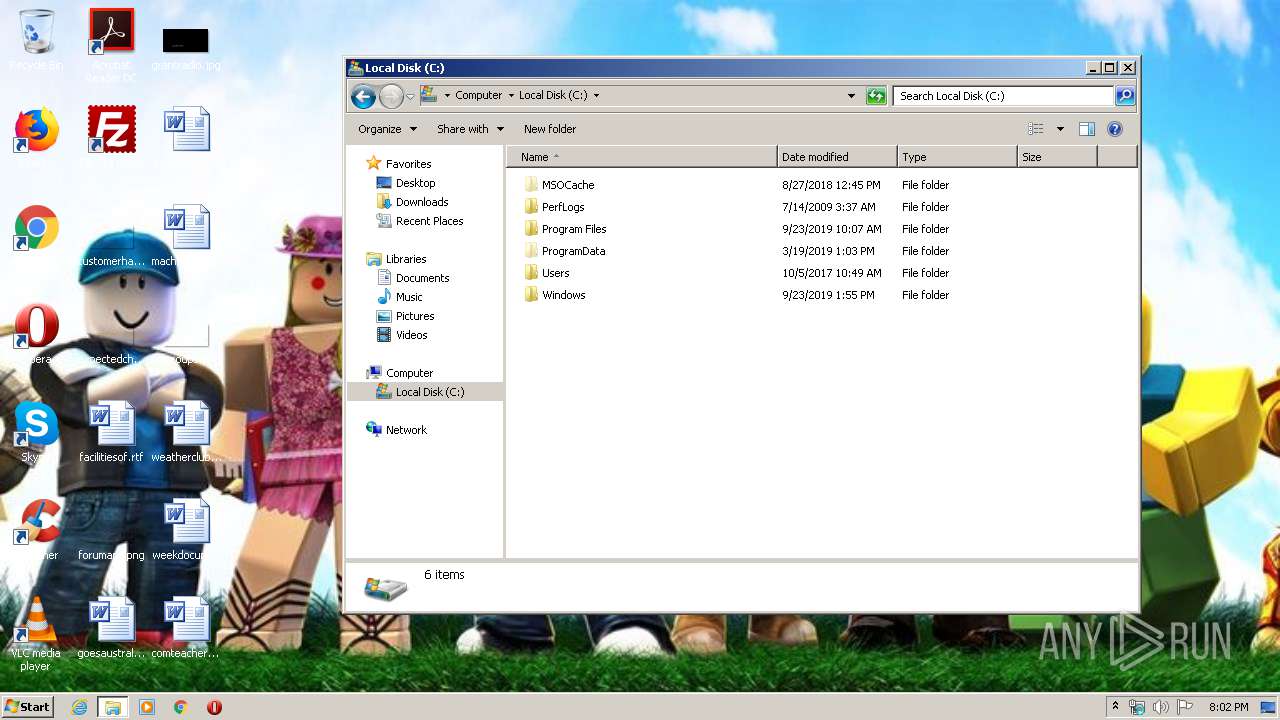
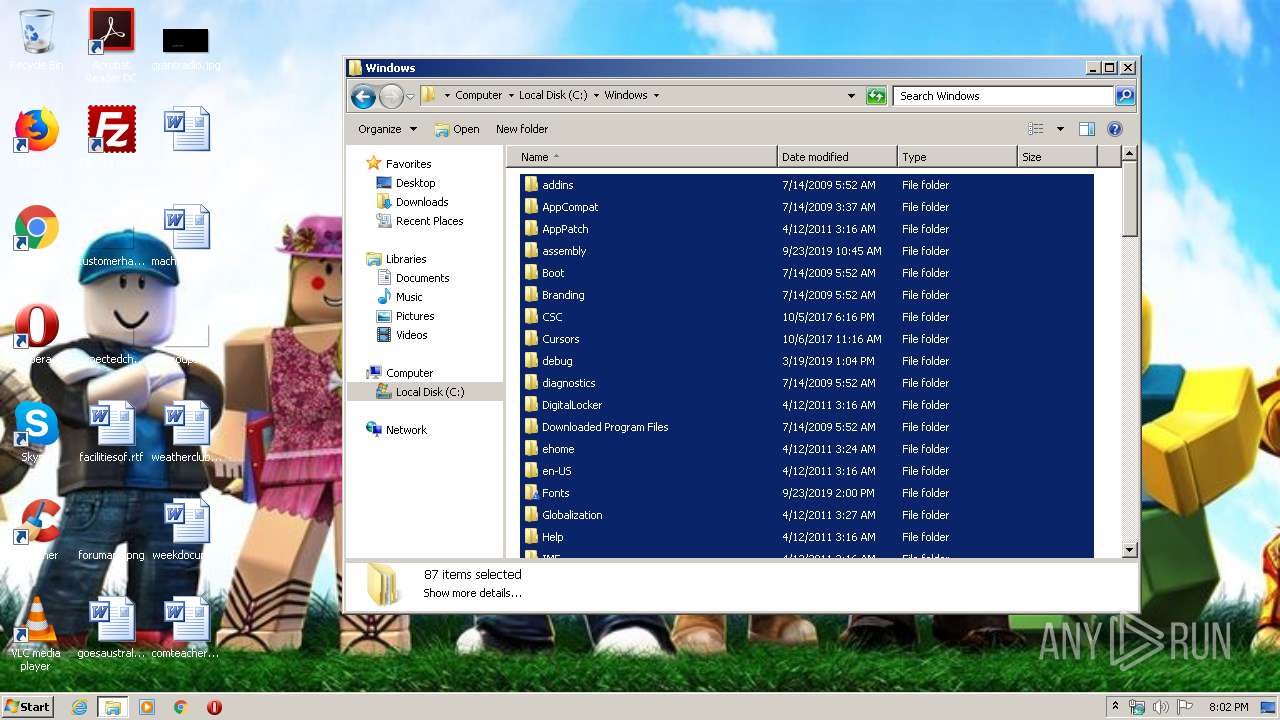
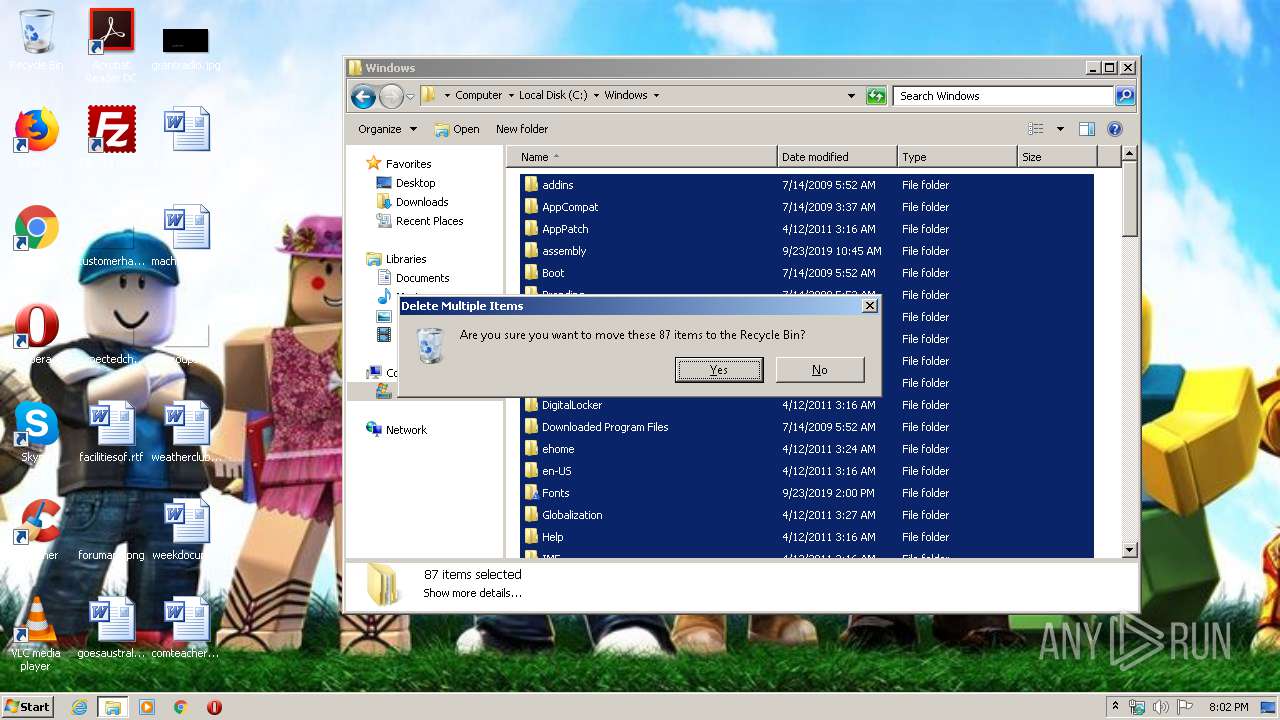
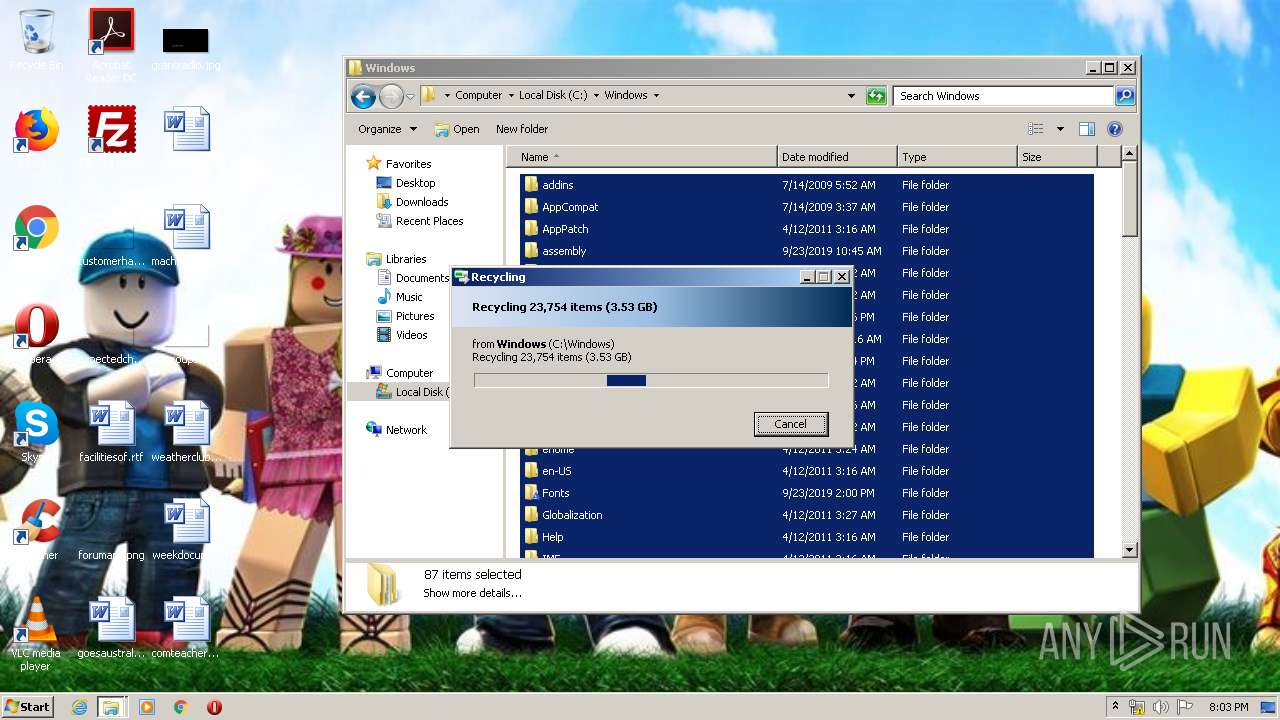
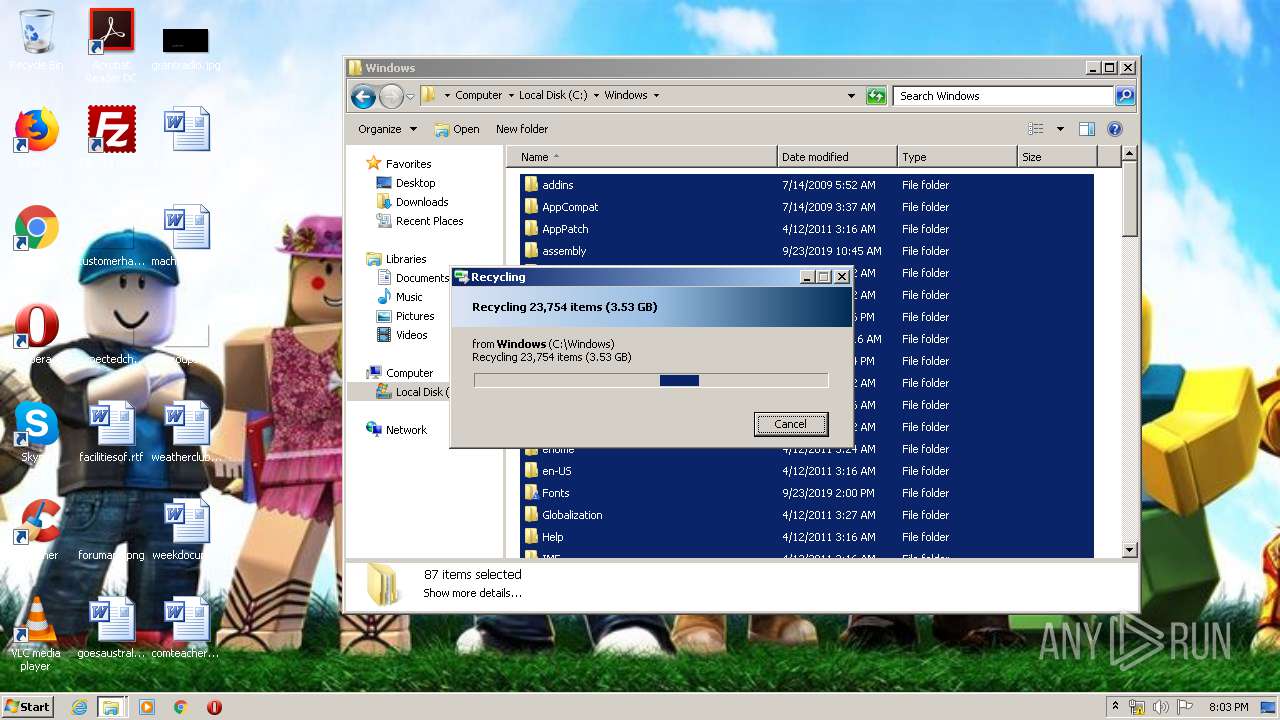
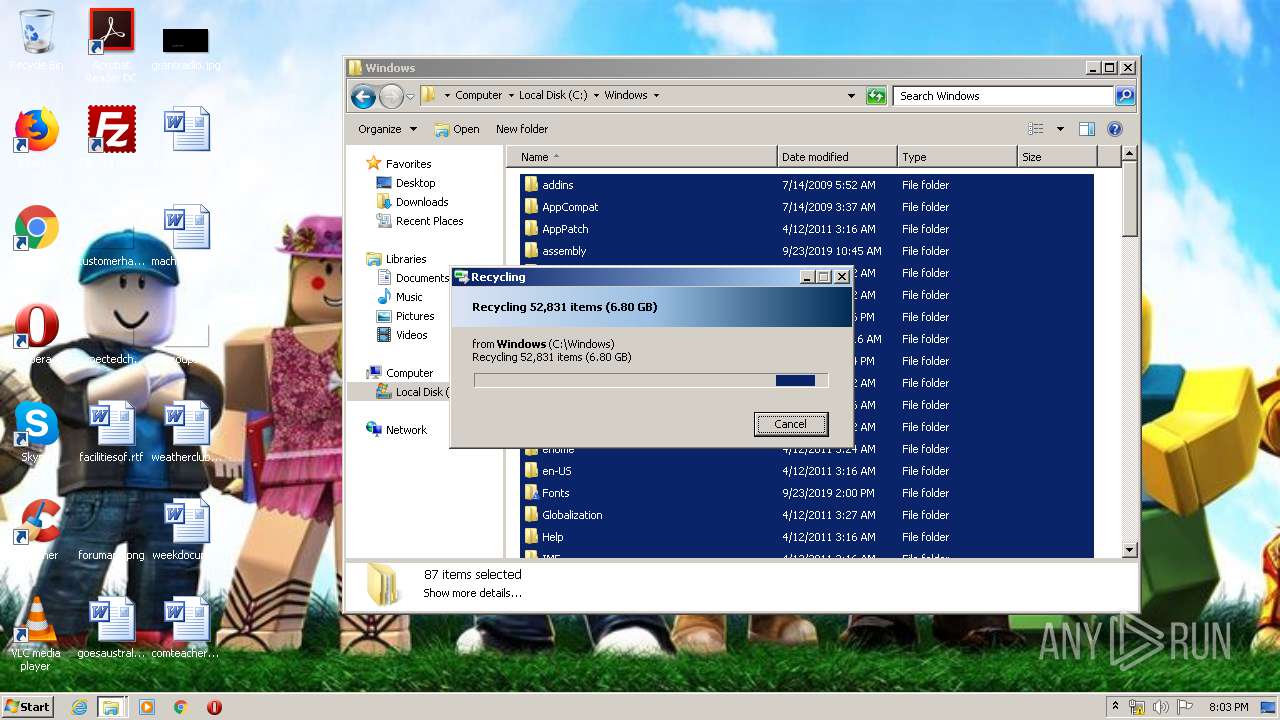
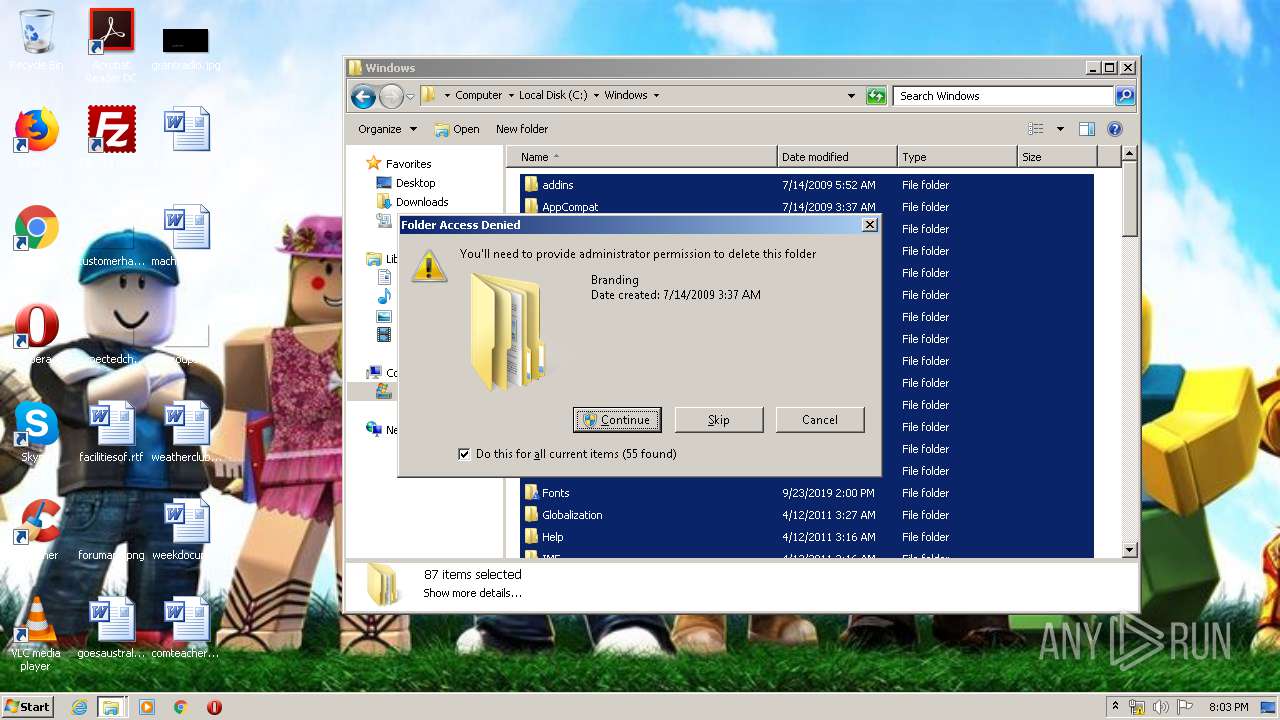
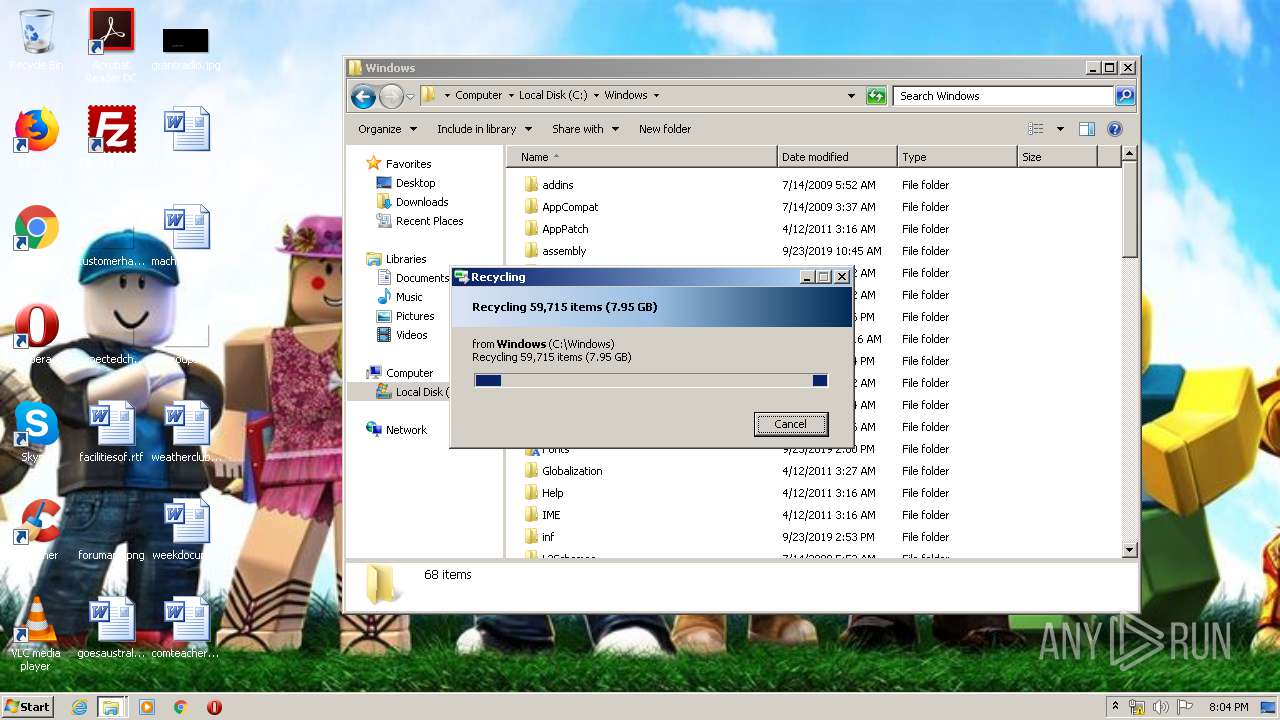
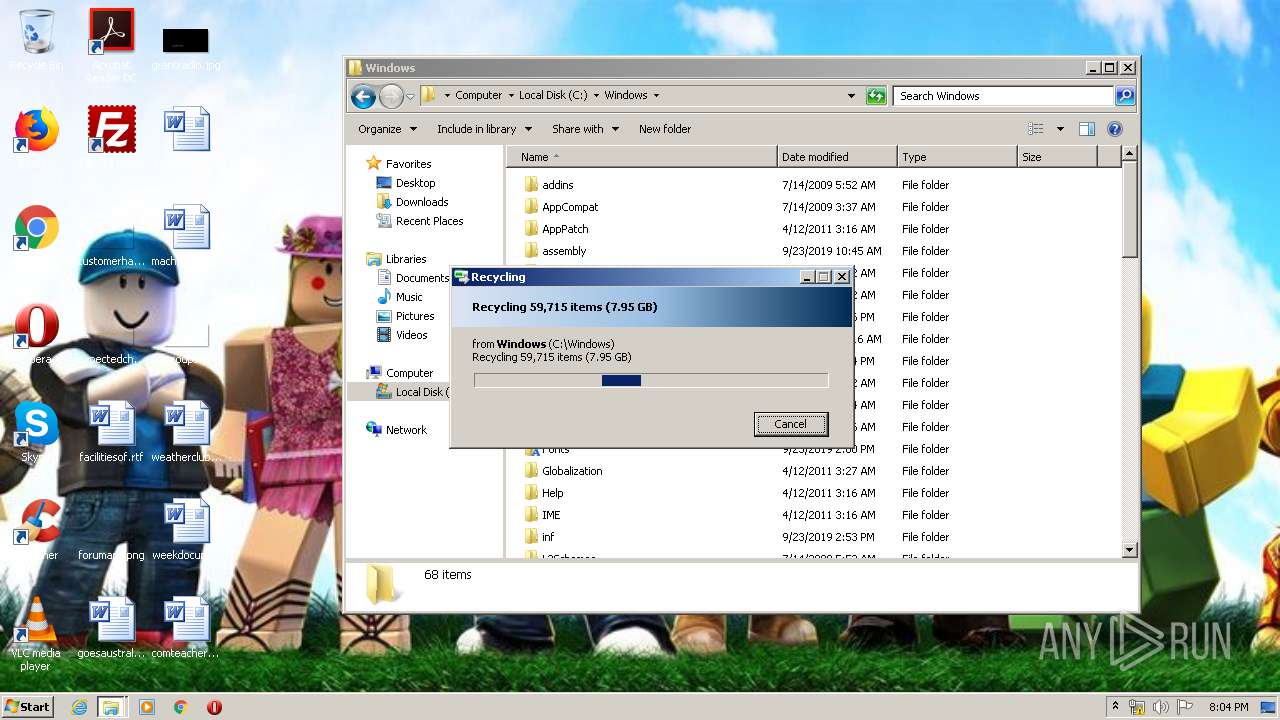
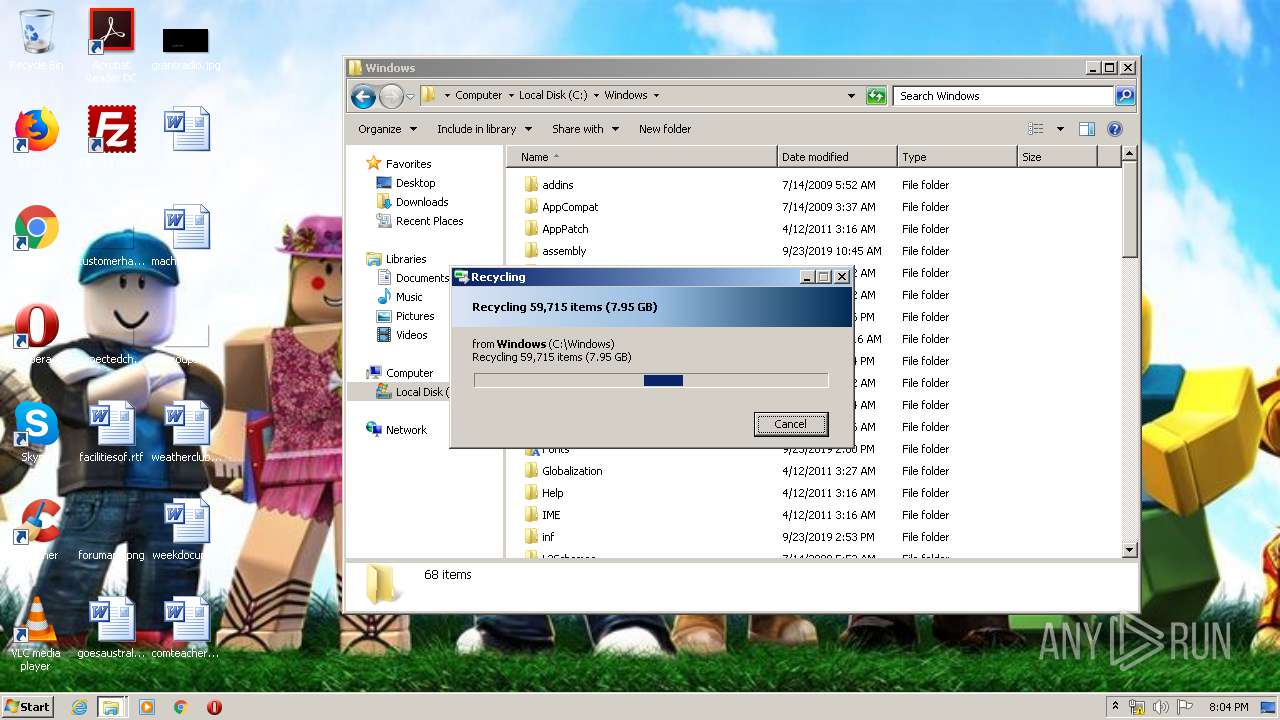
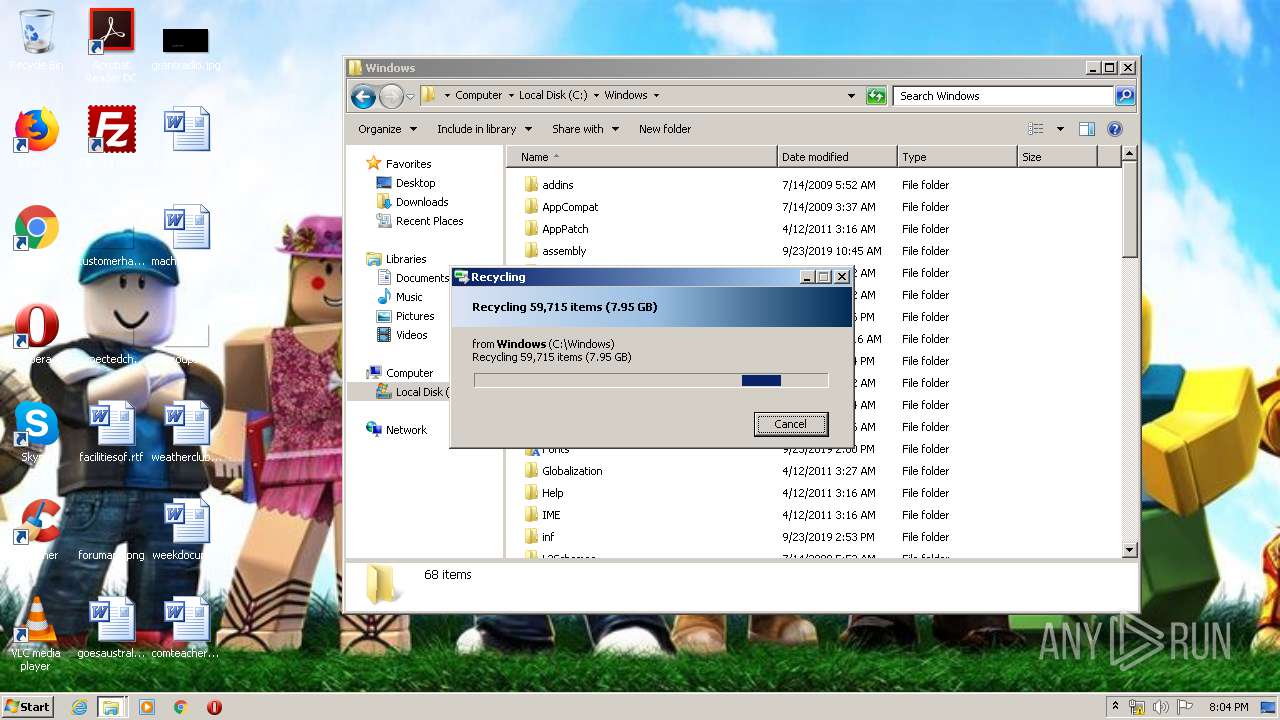
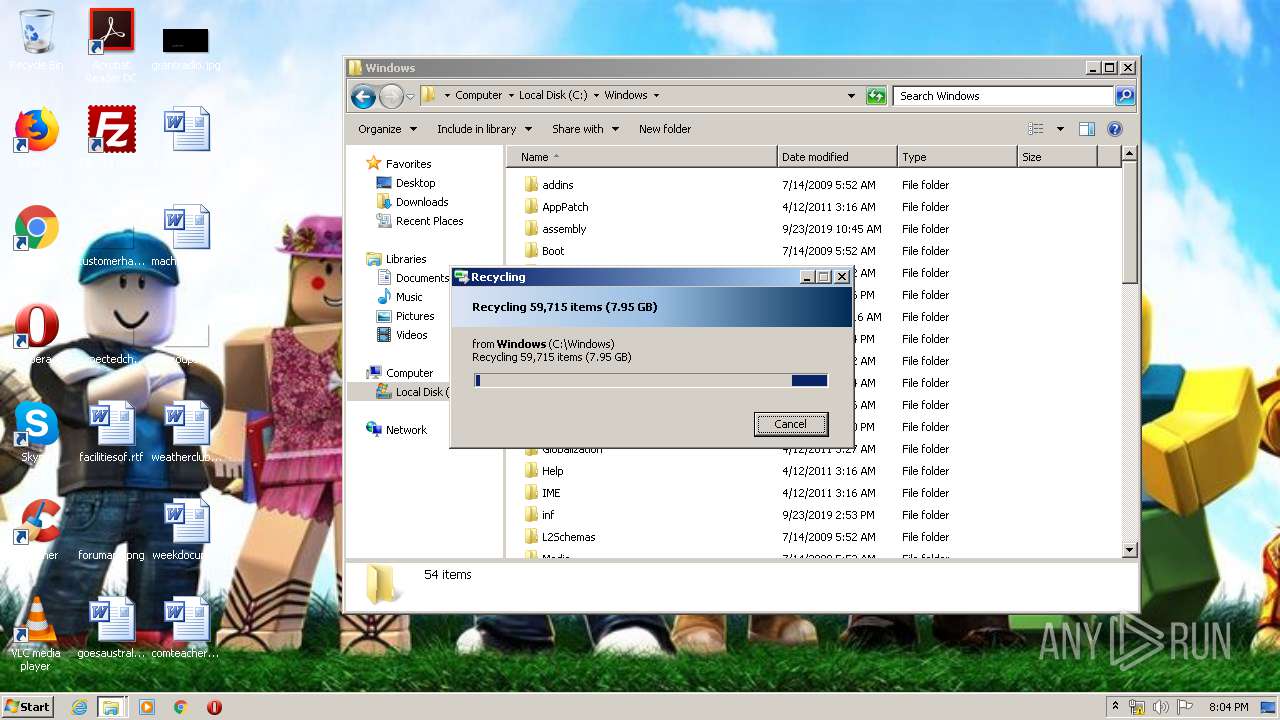
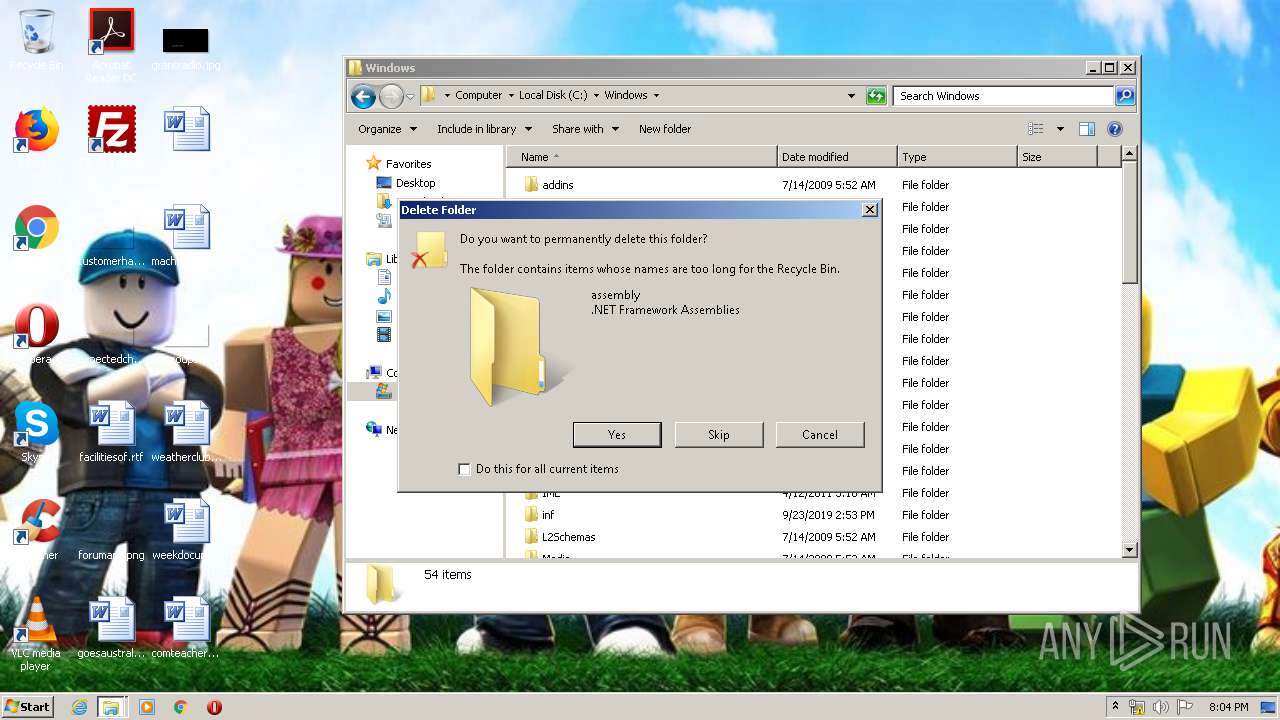
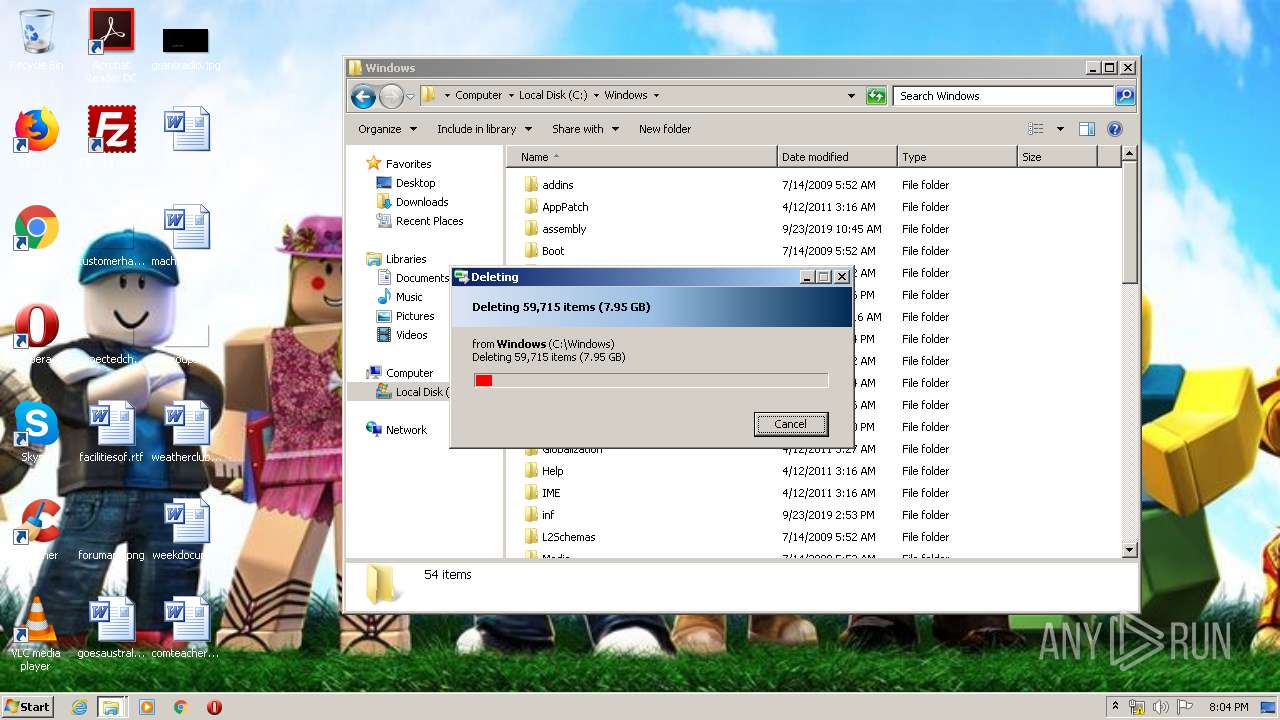
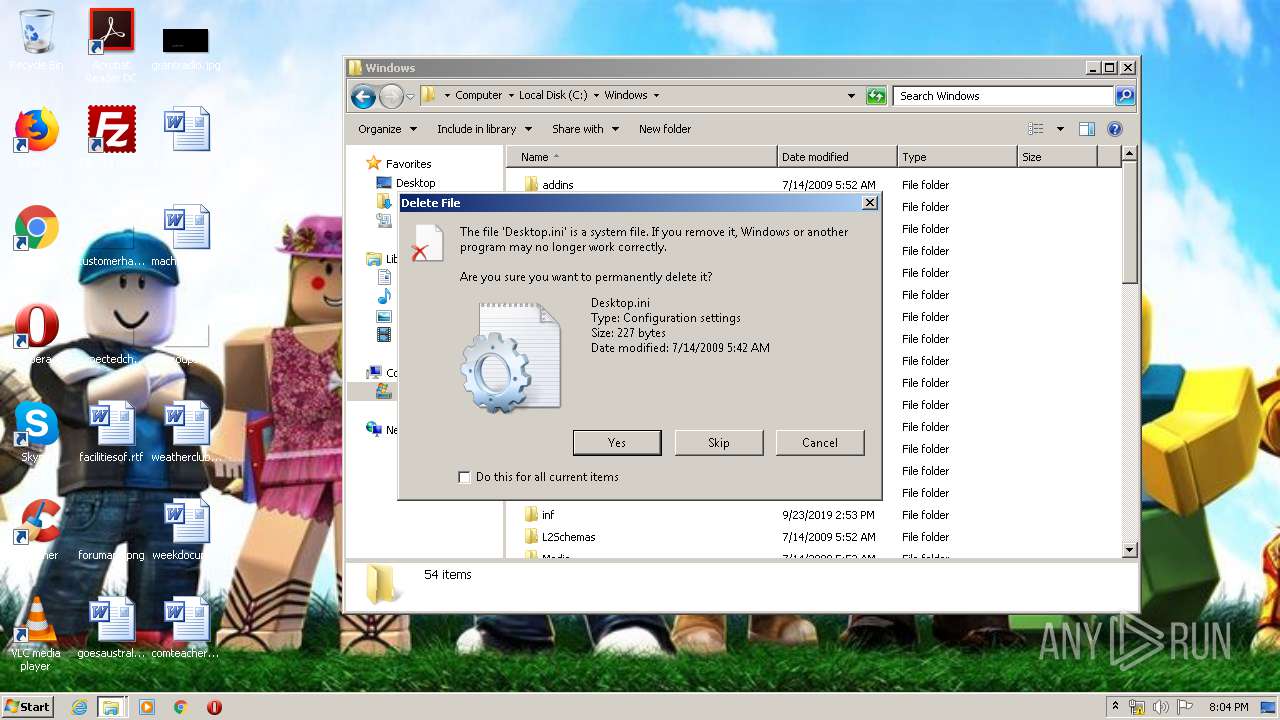
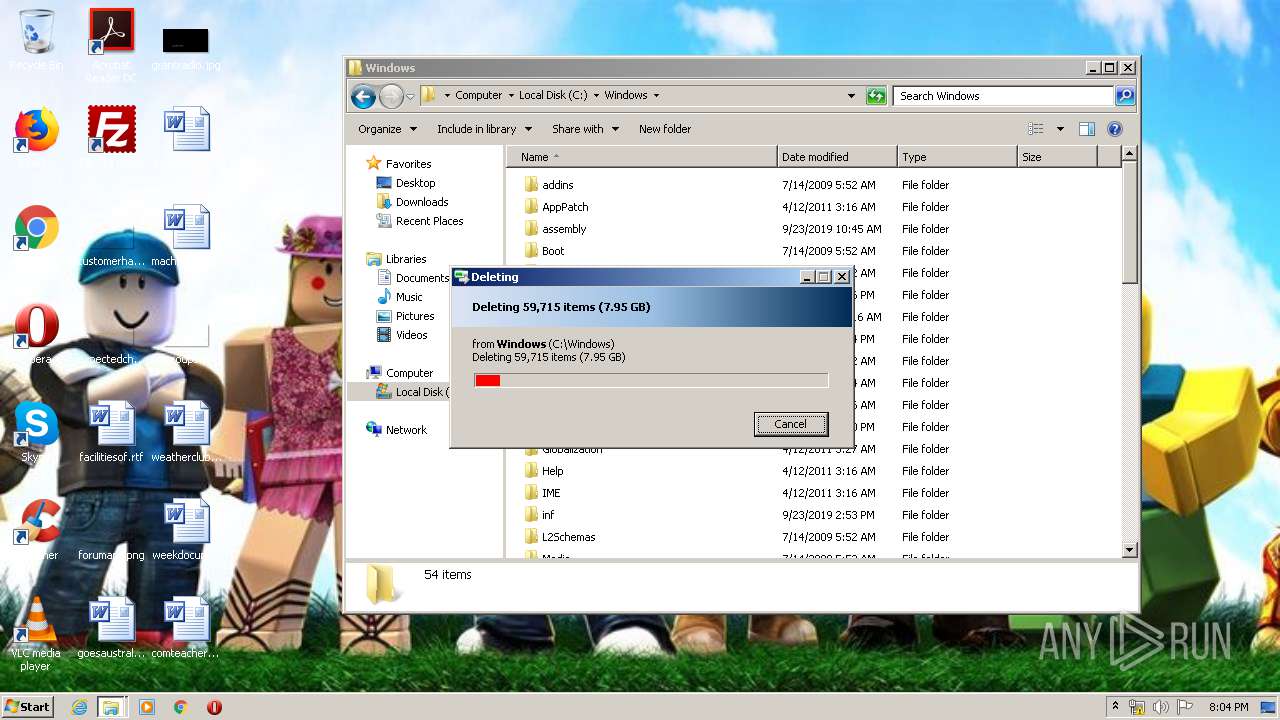
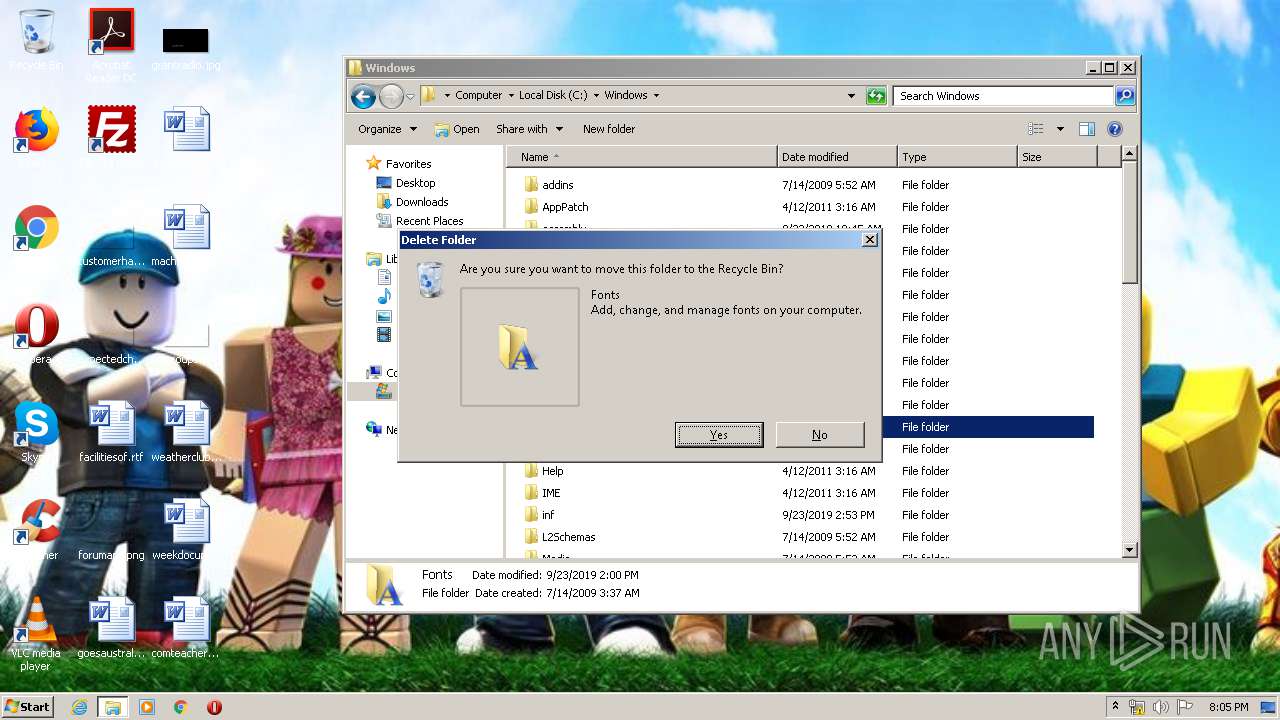
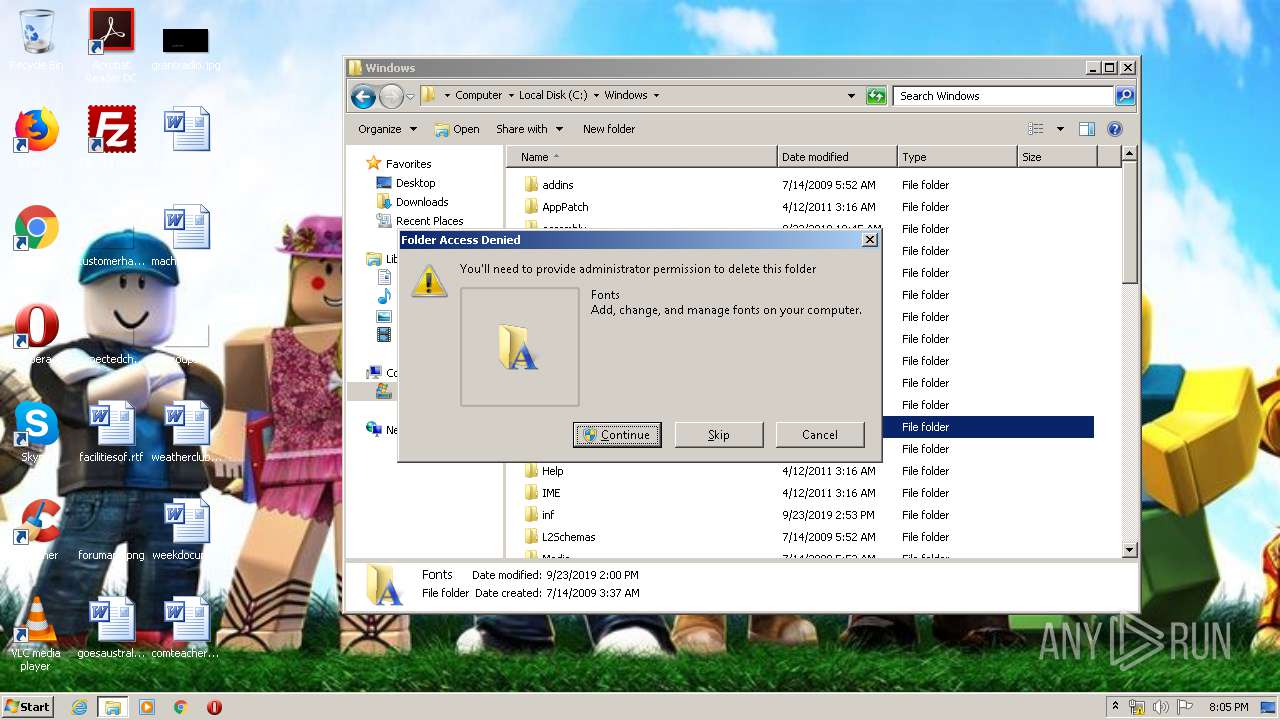
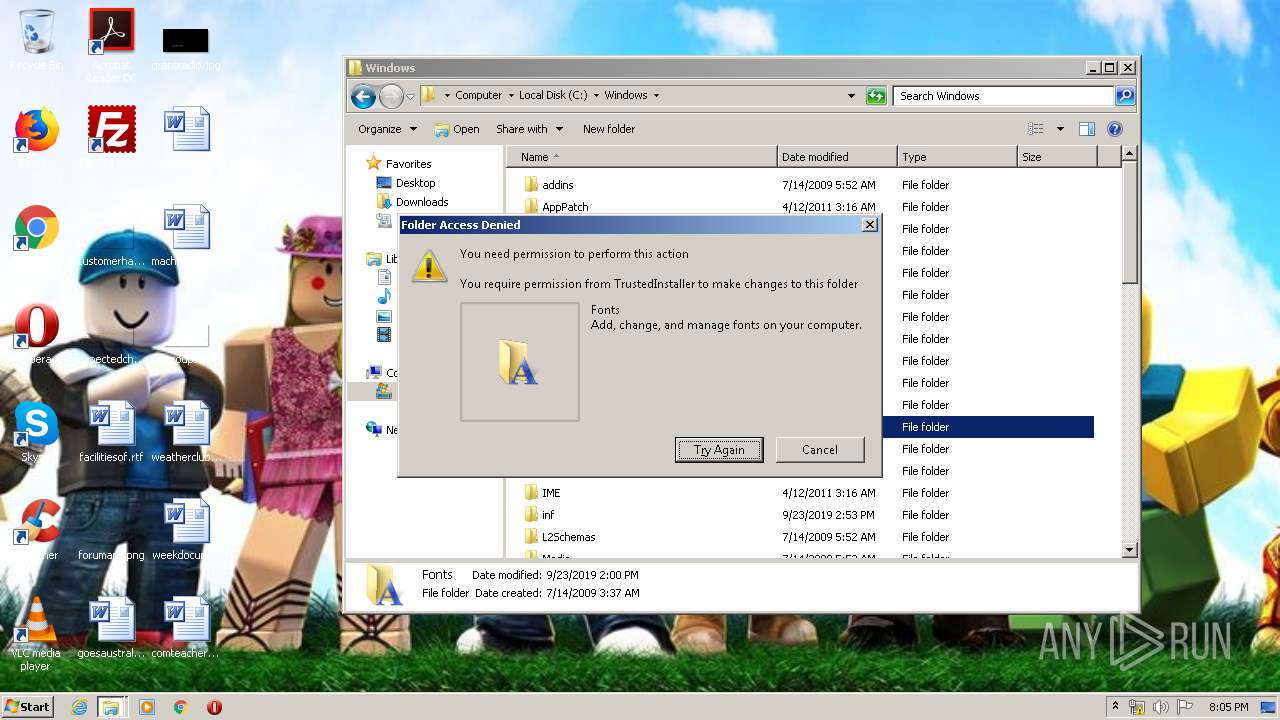
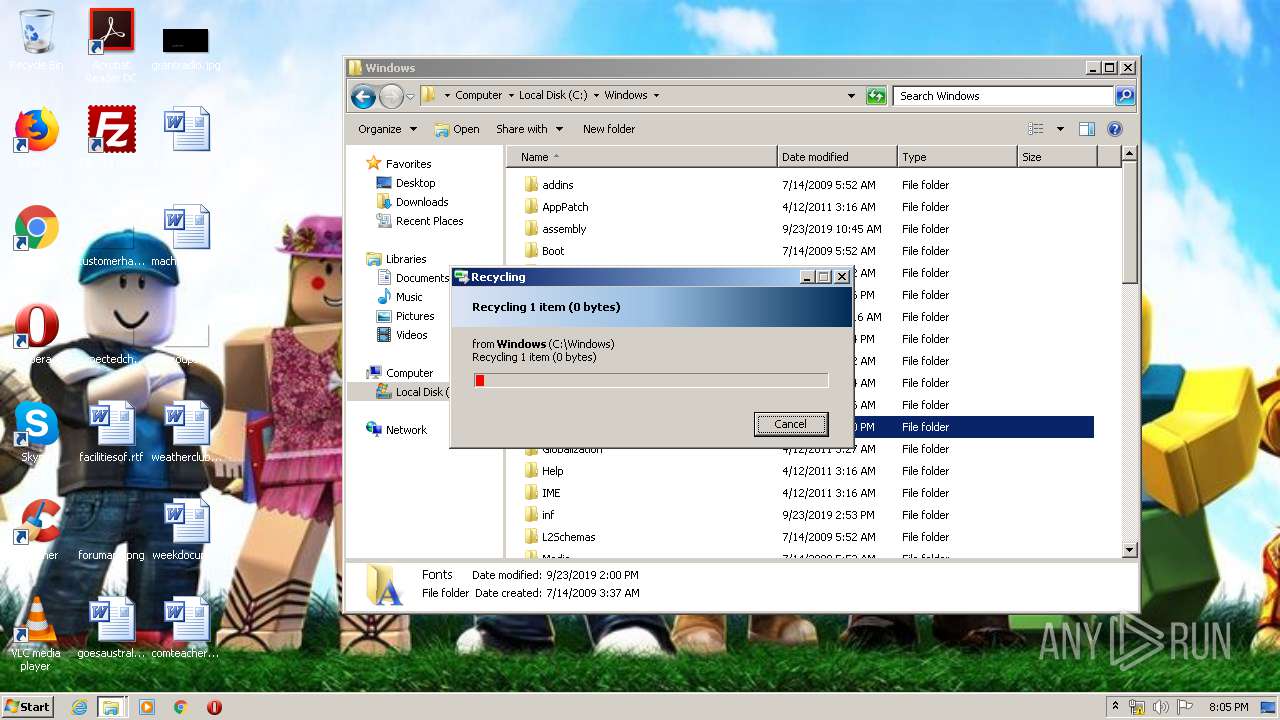
Tries to delete the host file
- DllHost.exe (PID: 4040)
SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 4040)
- DllHost.exe (PID: 2352)
- DllHost.exe (PID: 1024)
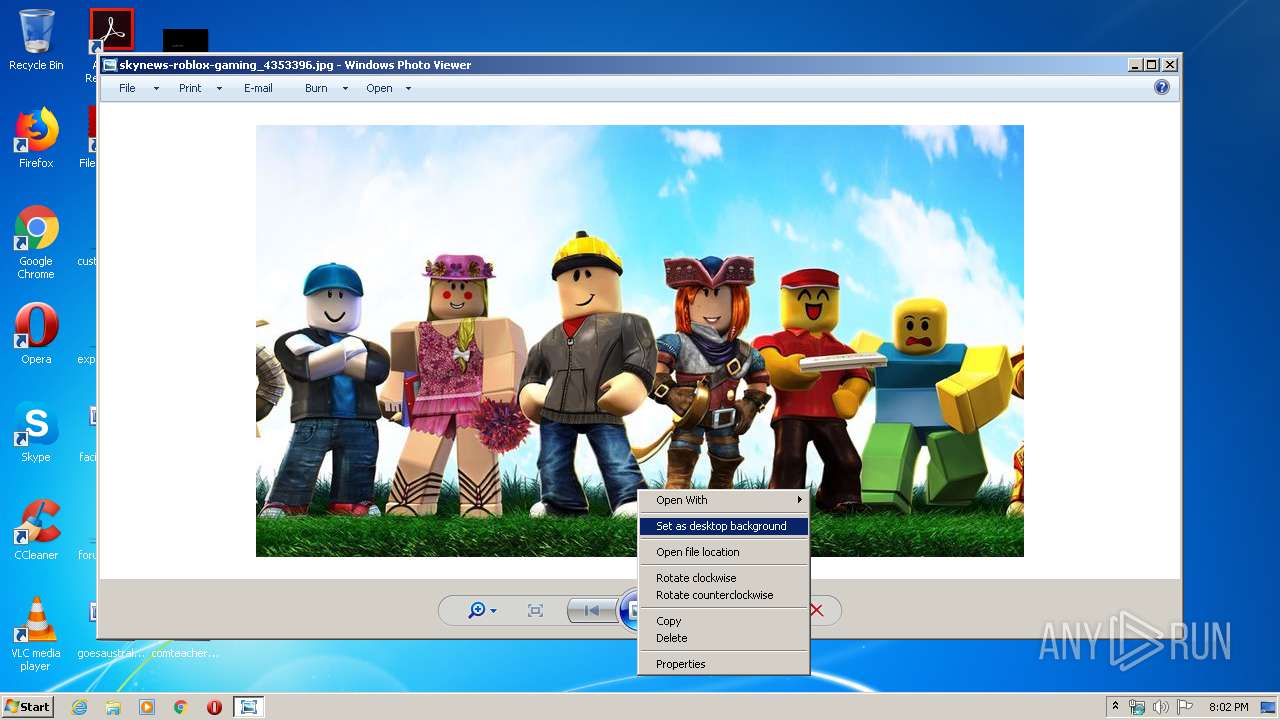
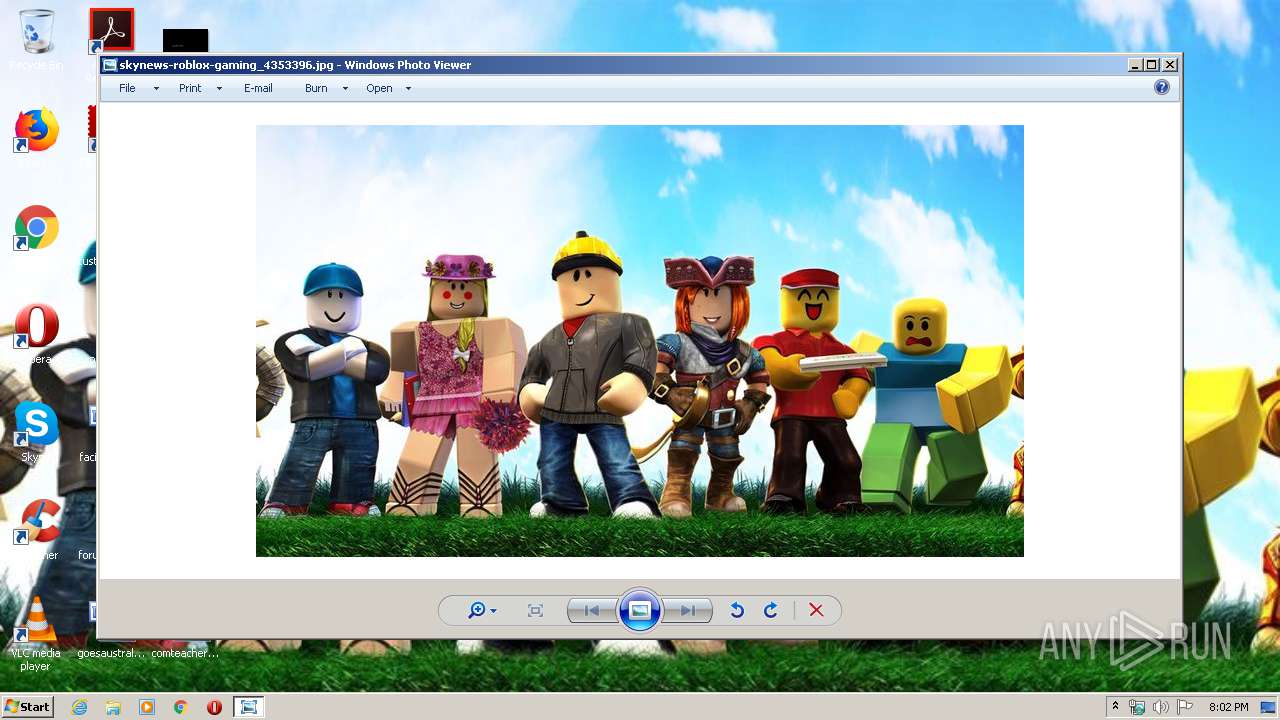
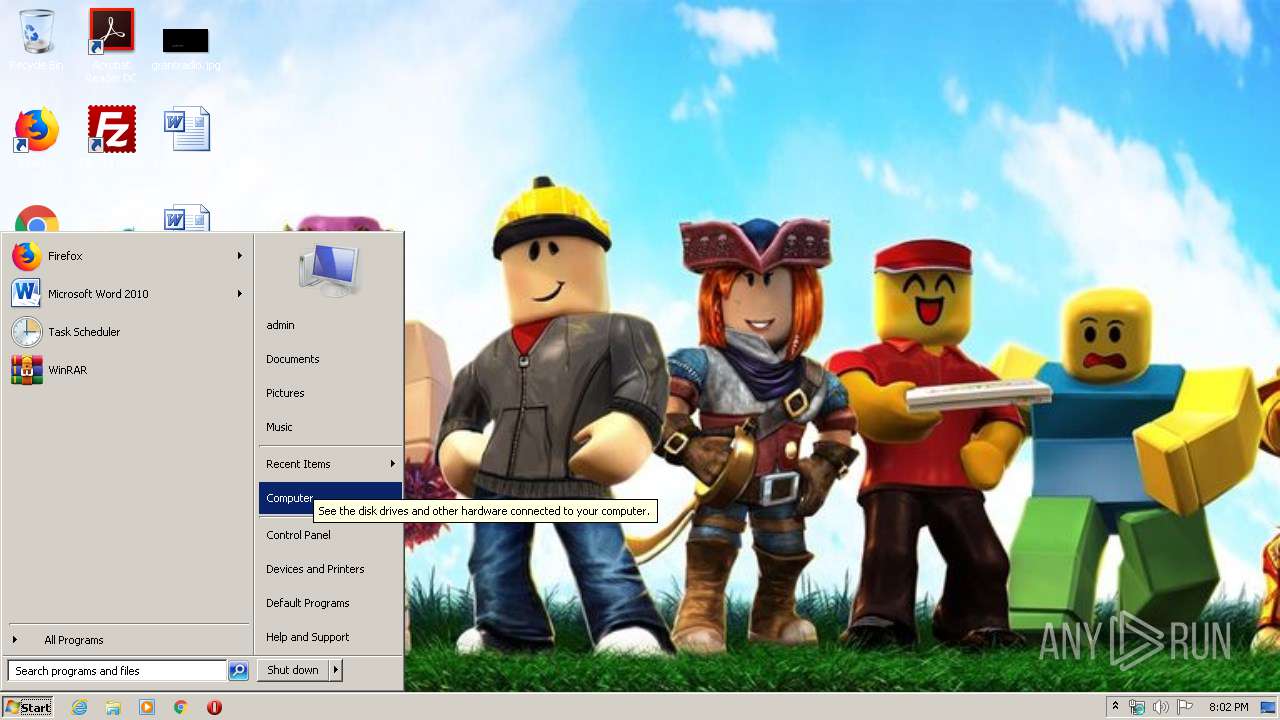
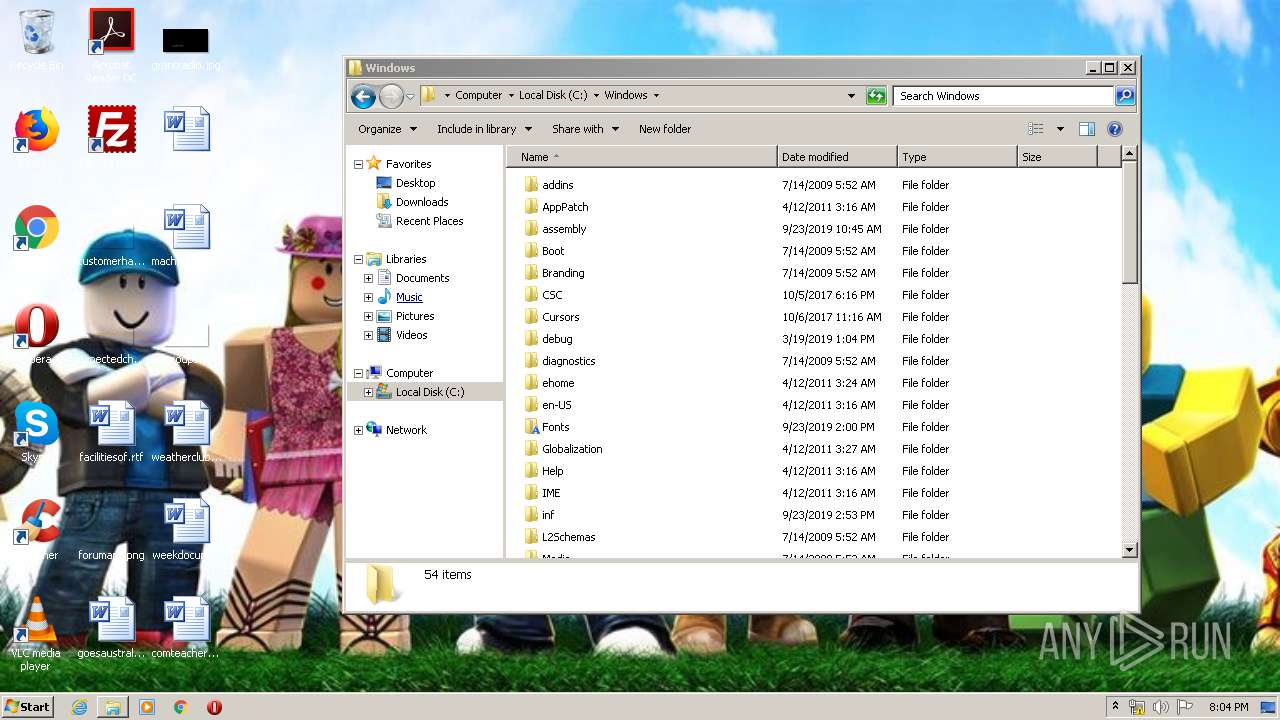
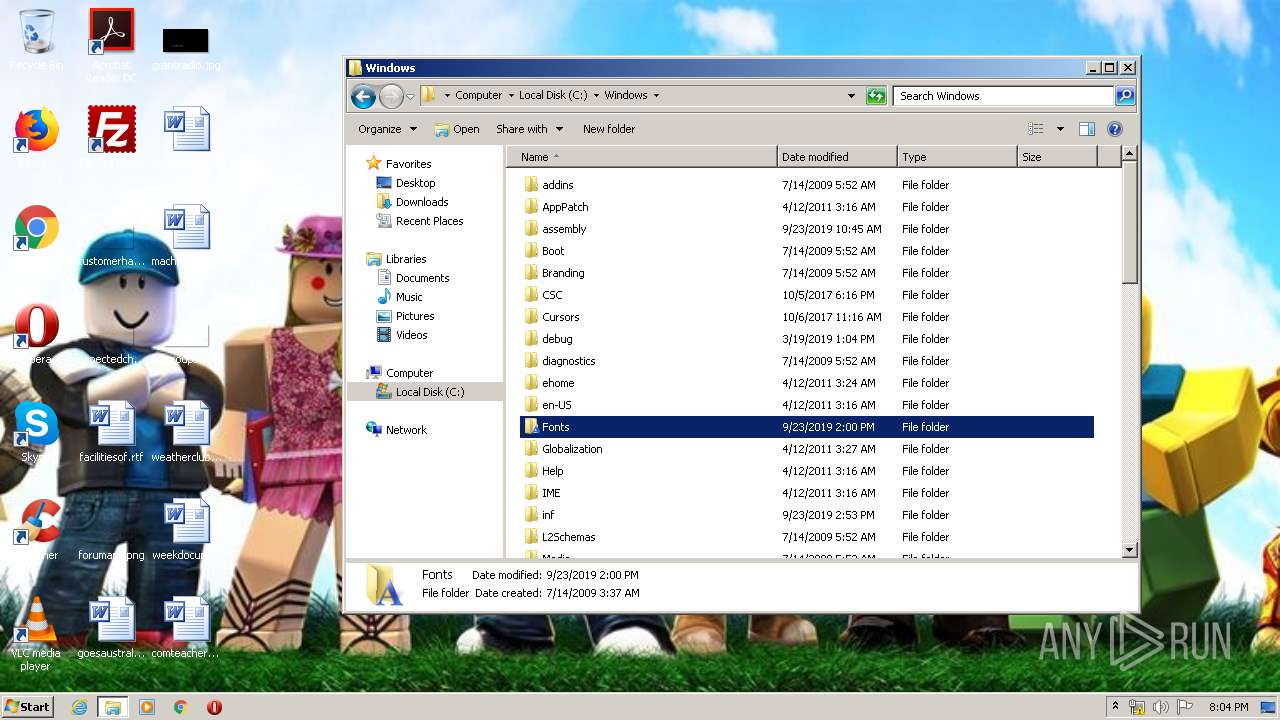
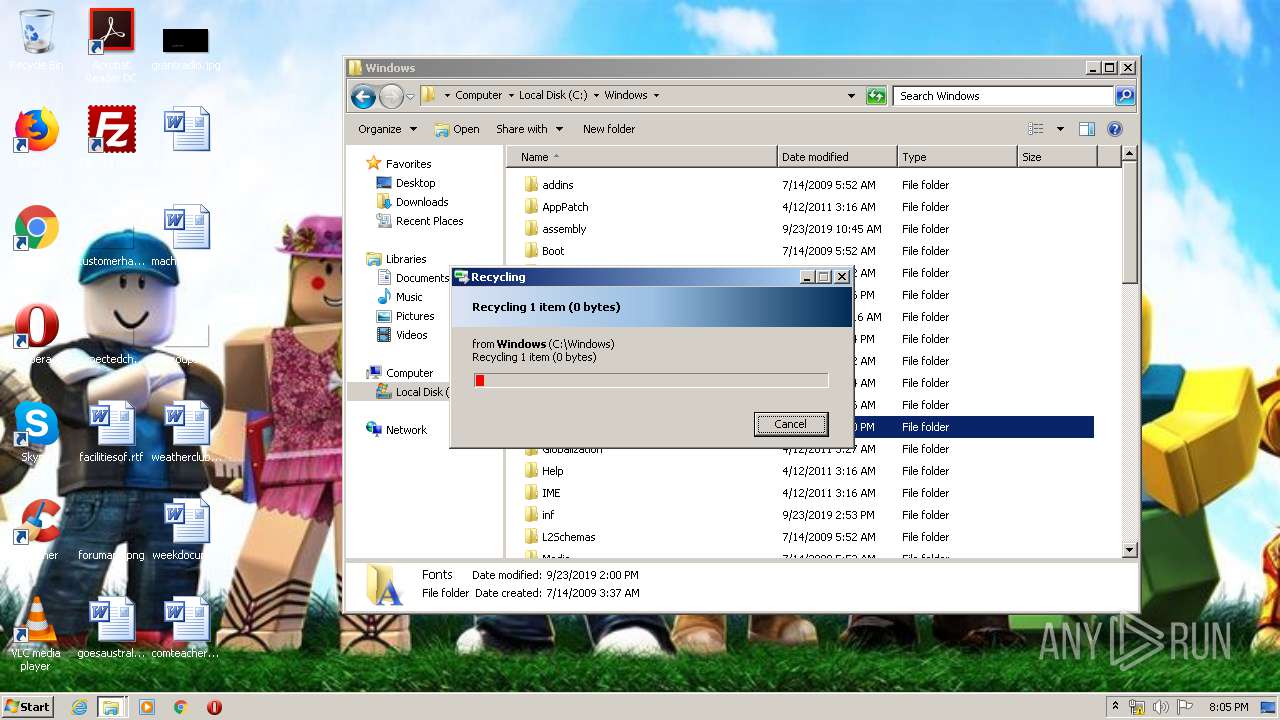
Changes the desktop background image
- rundll32.exe (PID: 2556)
Executable content was dropped or overwritten
- DllHost.exe (PID: 4040)
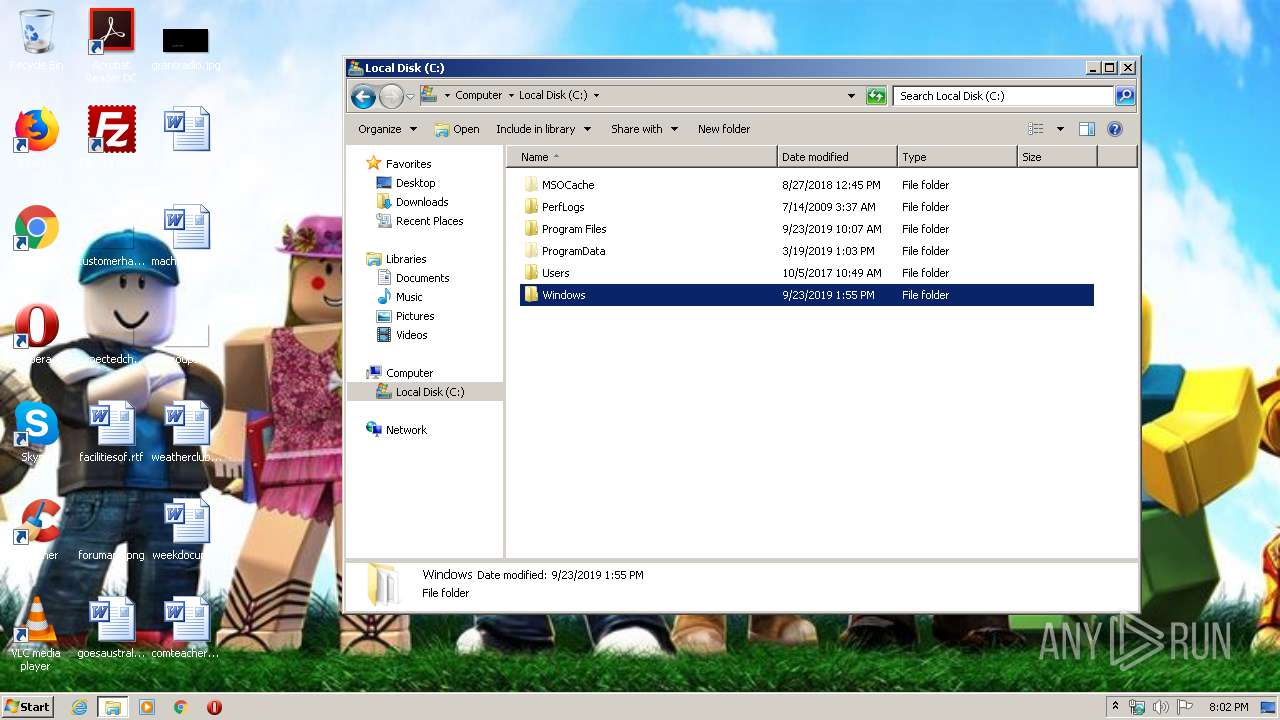
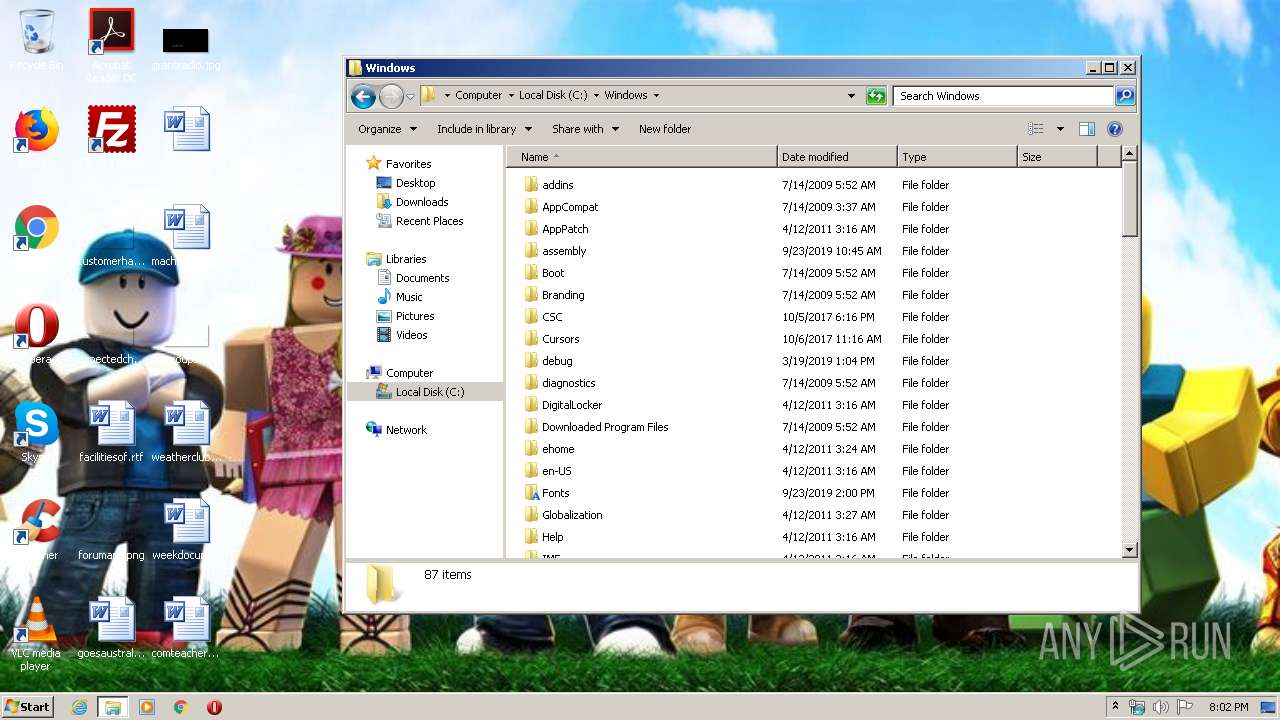
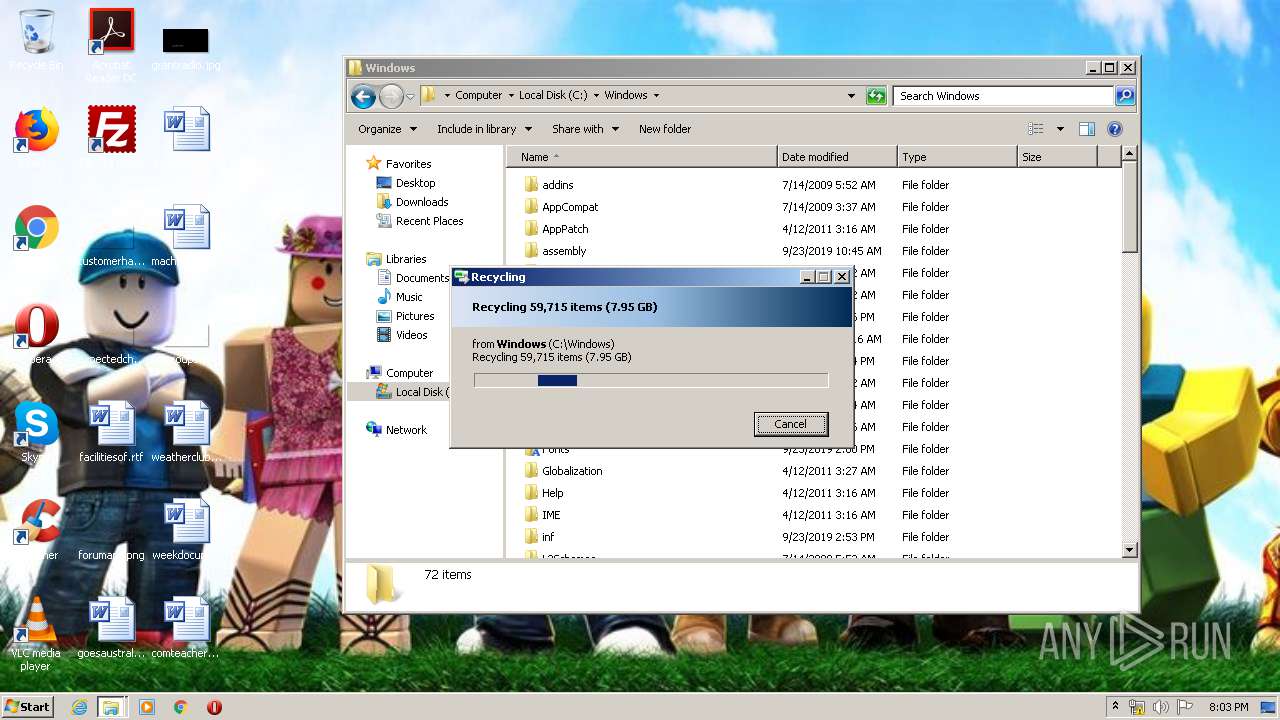
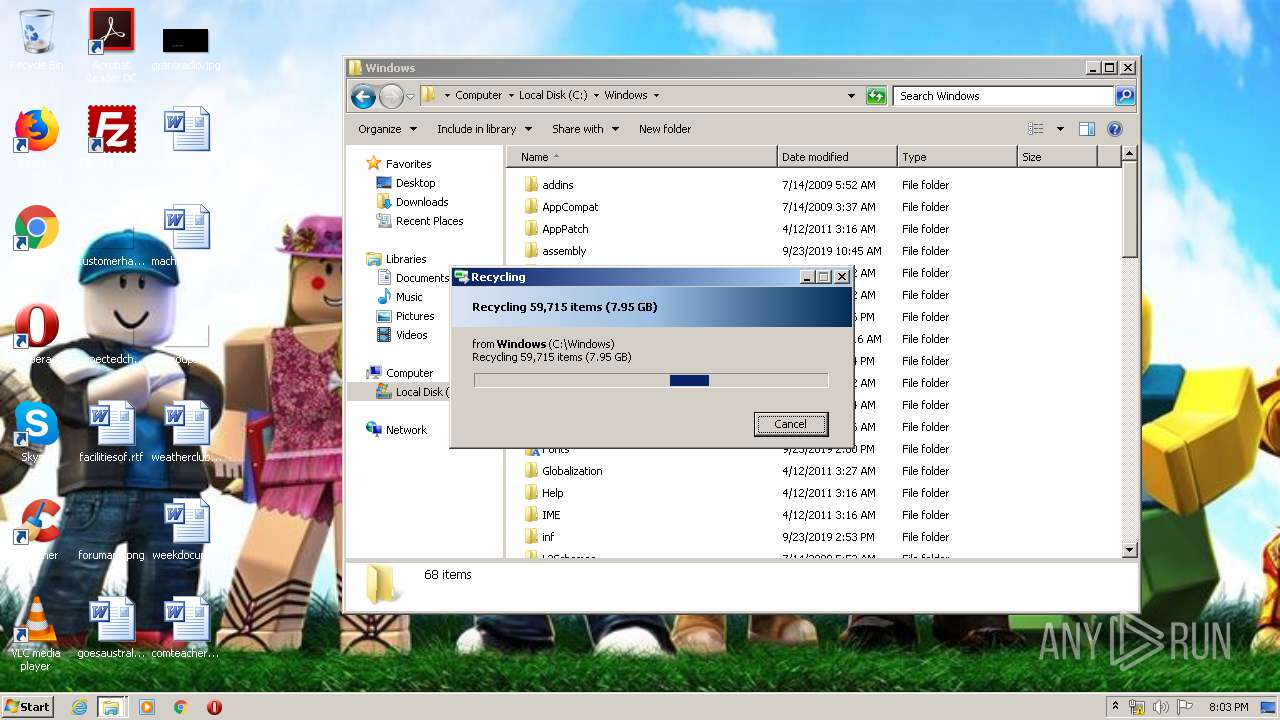
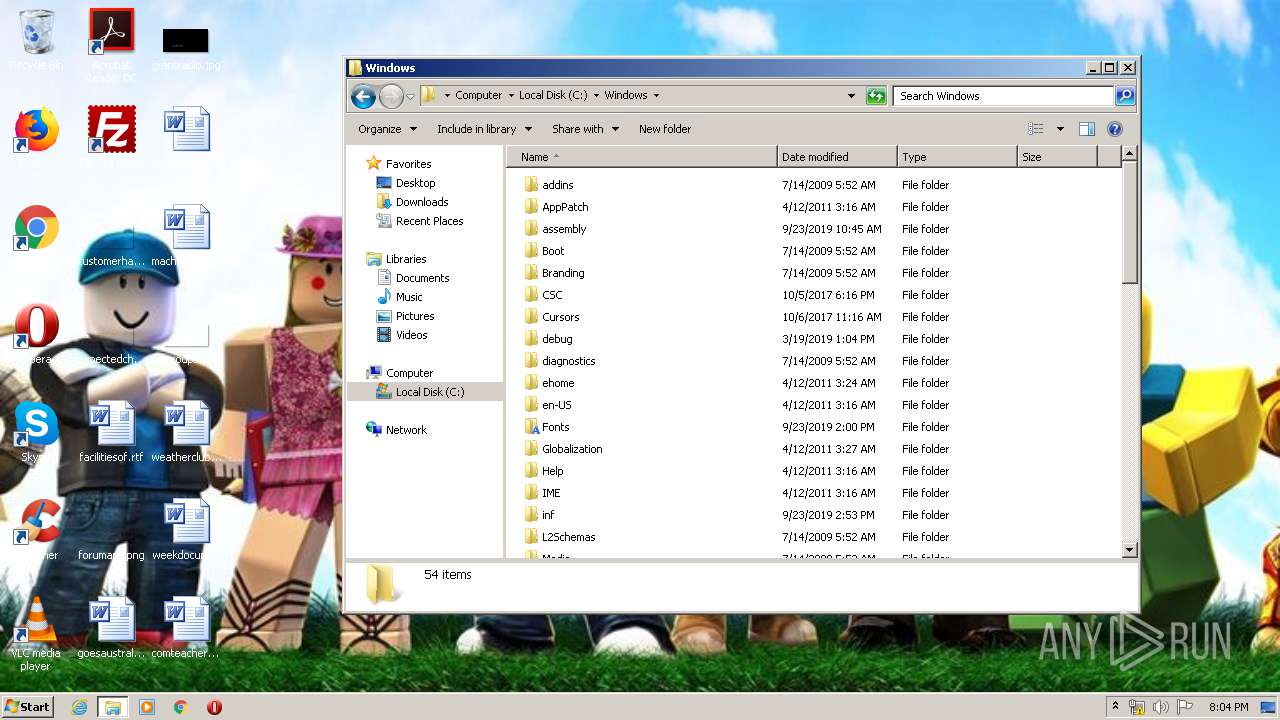
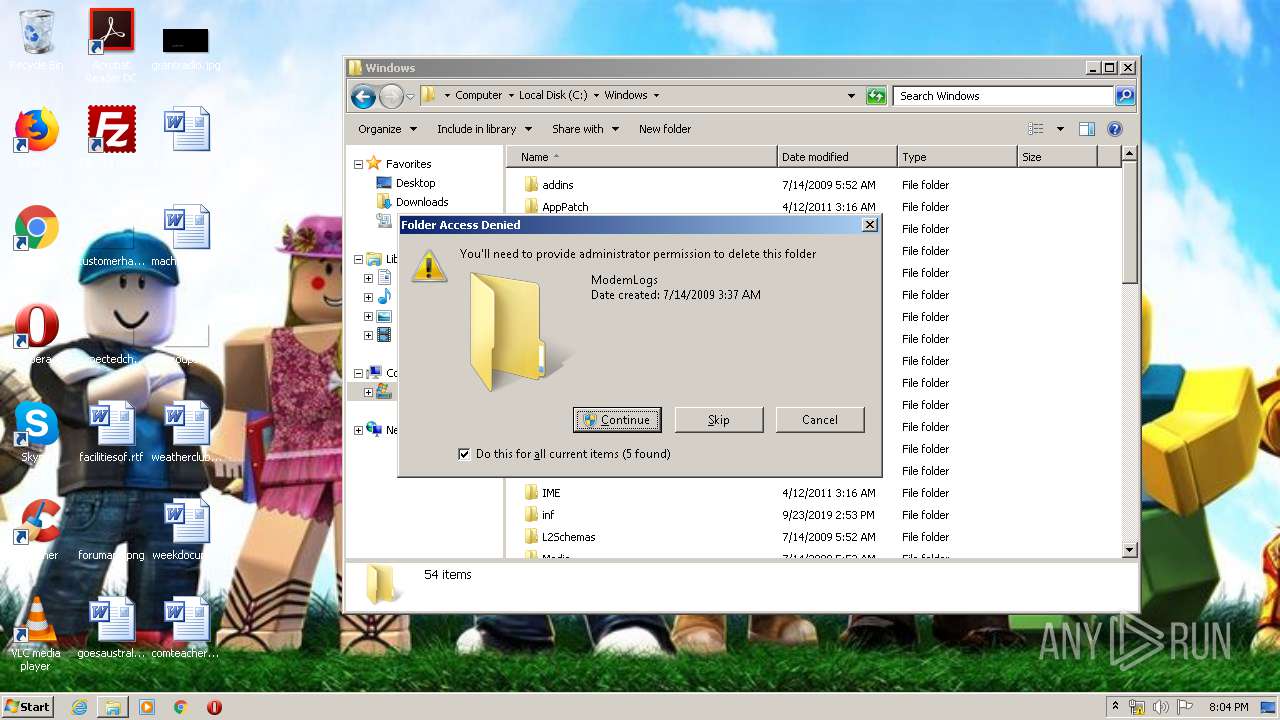
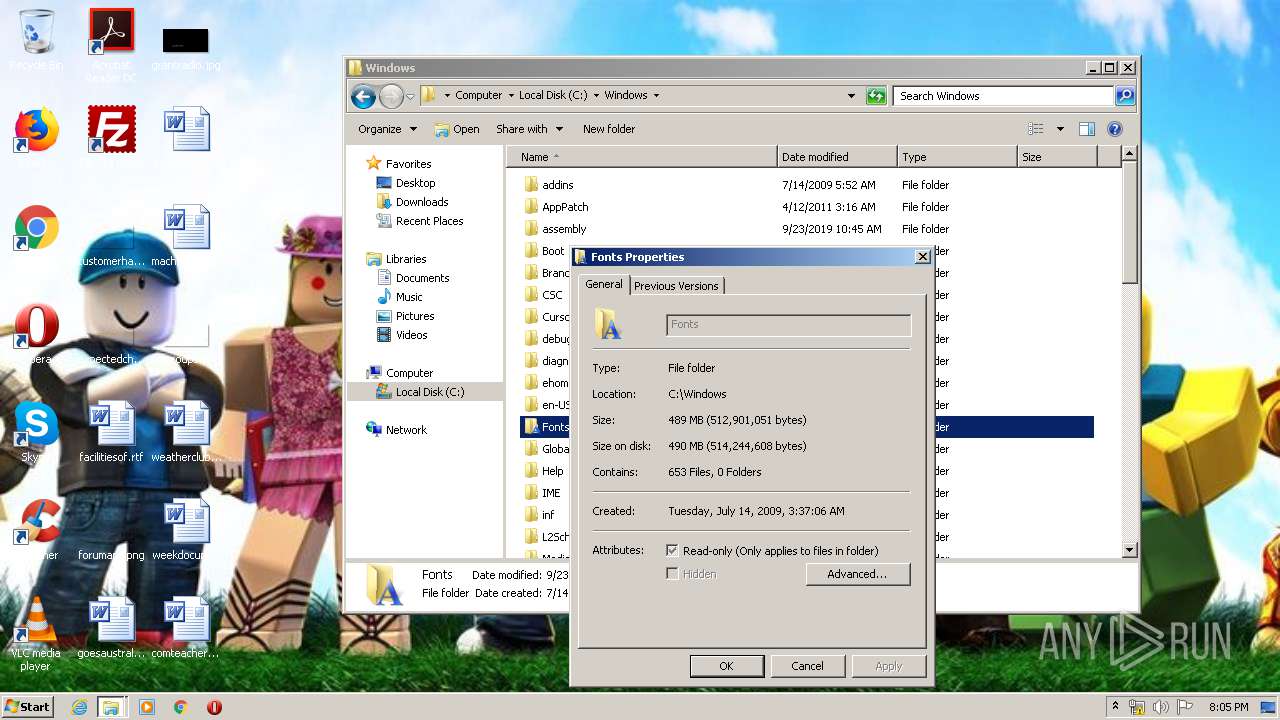
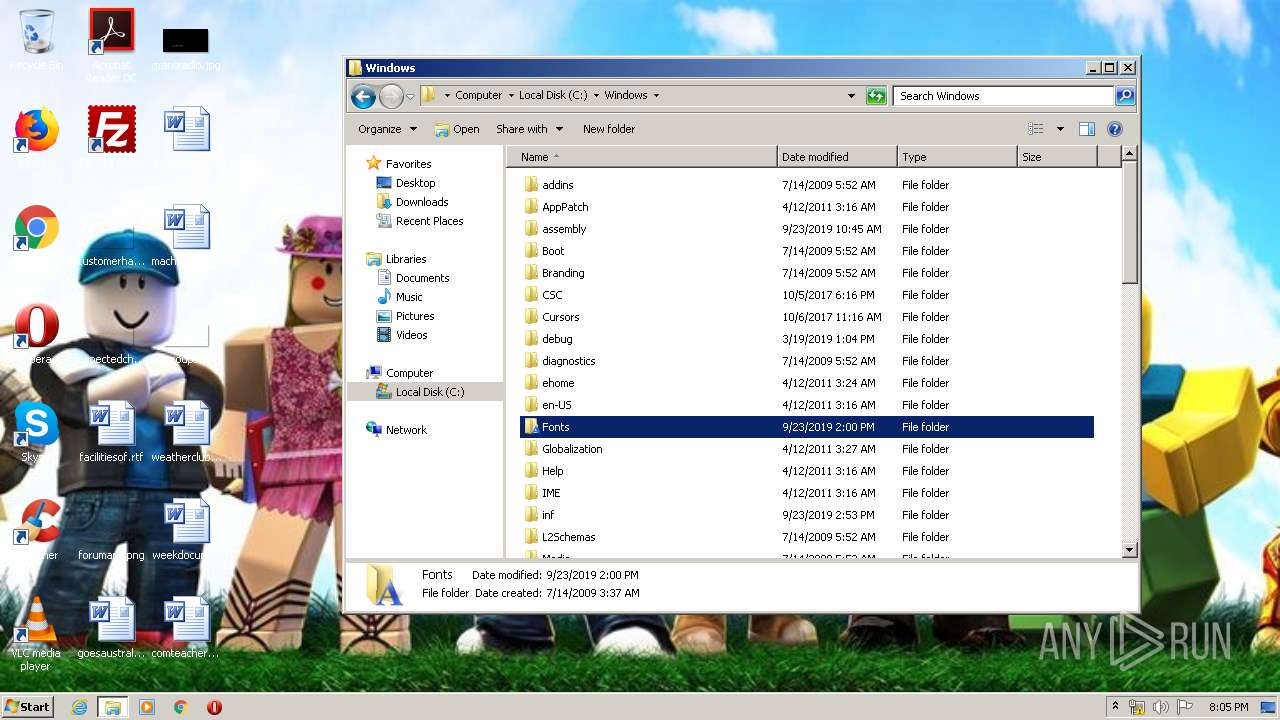
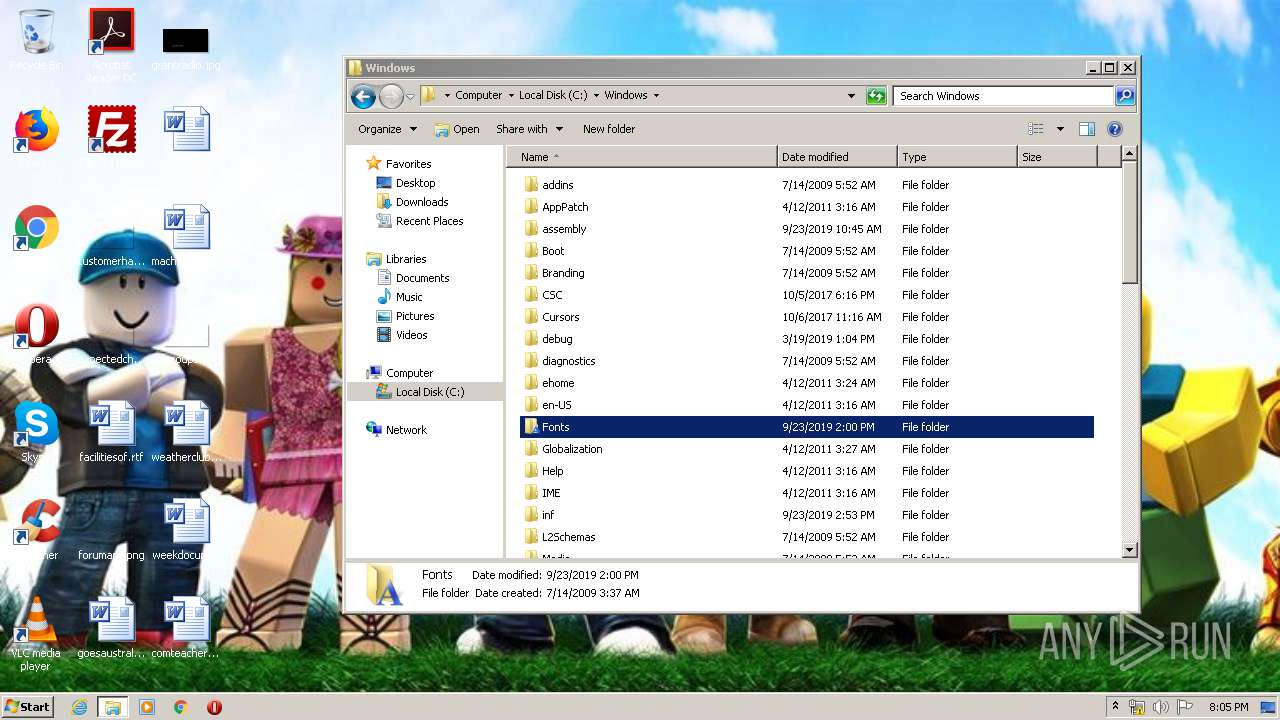
Removes files from Windows directory
- DllHost.exe (PID: 2352)
- DllHost.exe (PID: 4040)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jpg | | | JPEG bitmap (75) |
|---|---|---|
| .mp3 | | | MP3 audio (25) |
EXIF
Composite
| ImageSize: | 768x432 |
|---|---|
| Megapixels: | 0.332 |
Total processes
47
Monitored processes
4
Malicious processes
2
Suspicious processes
0
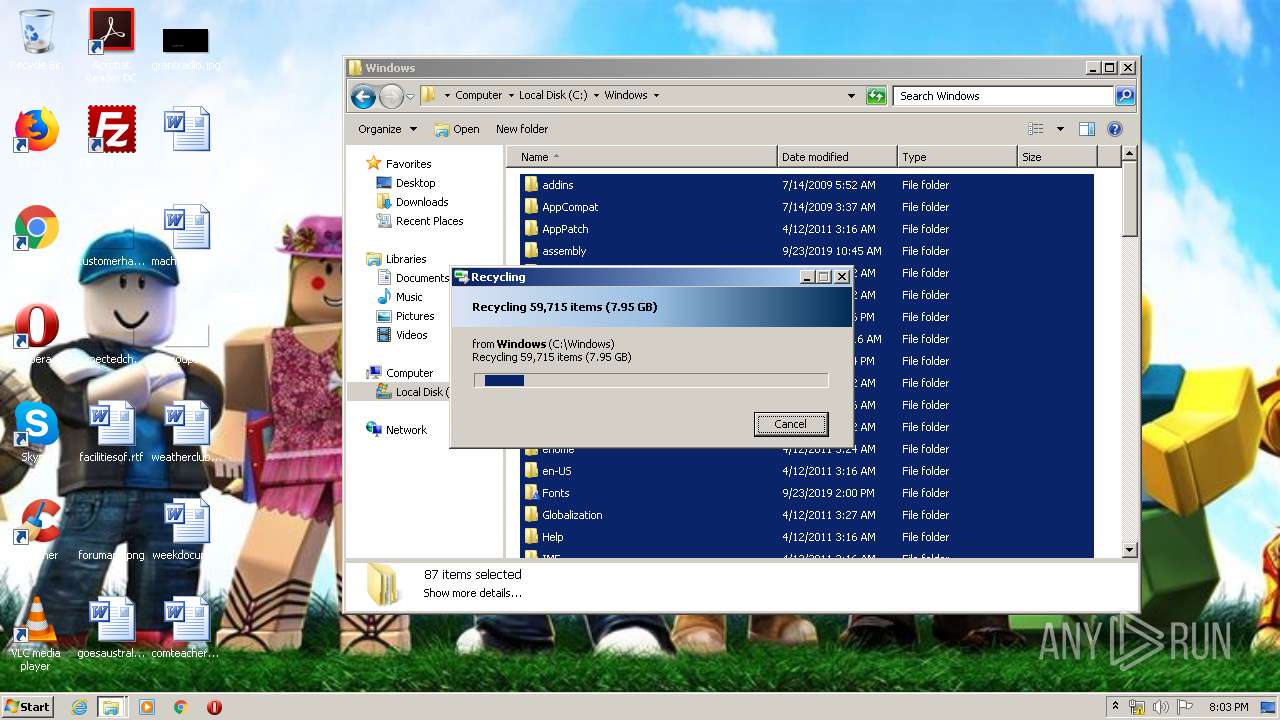
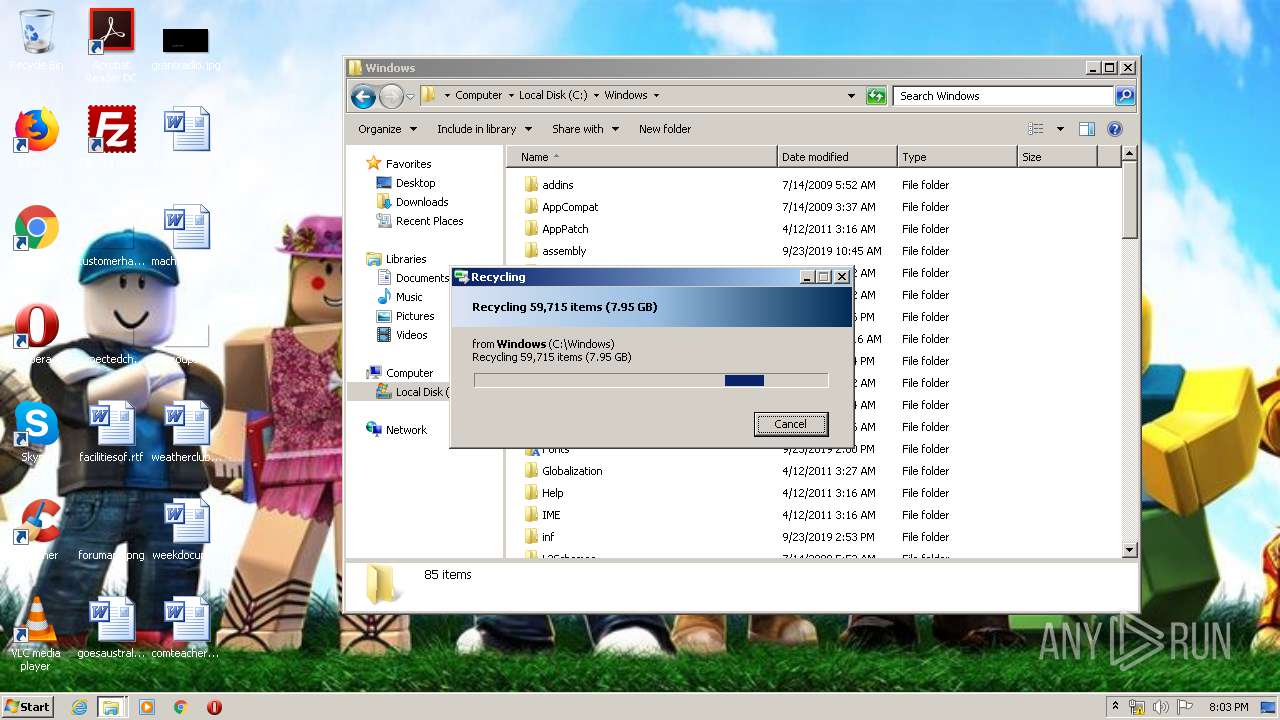
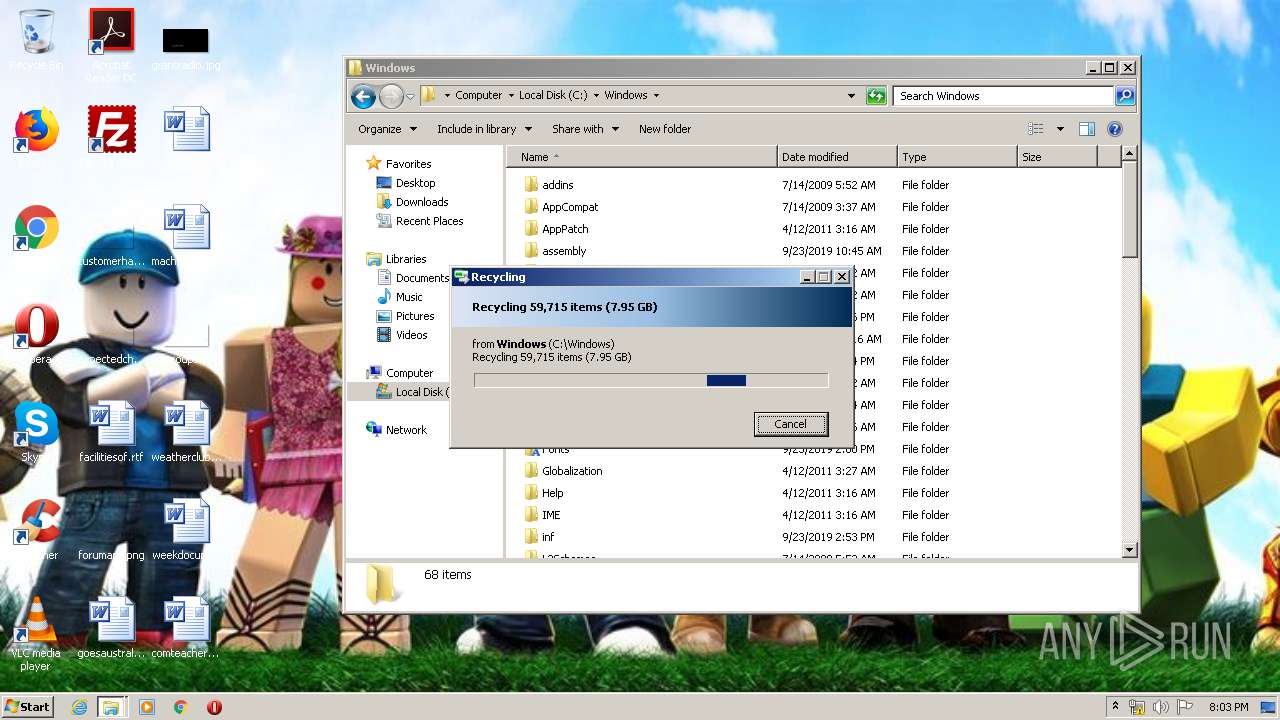
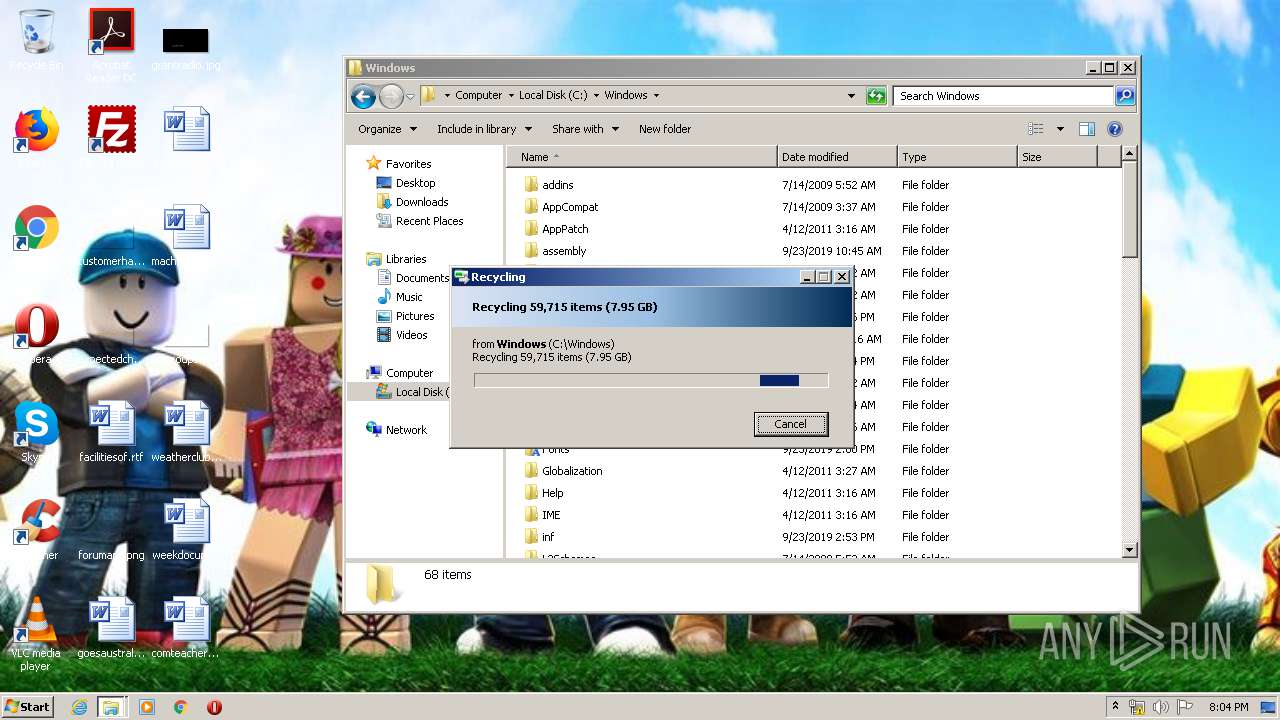
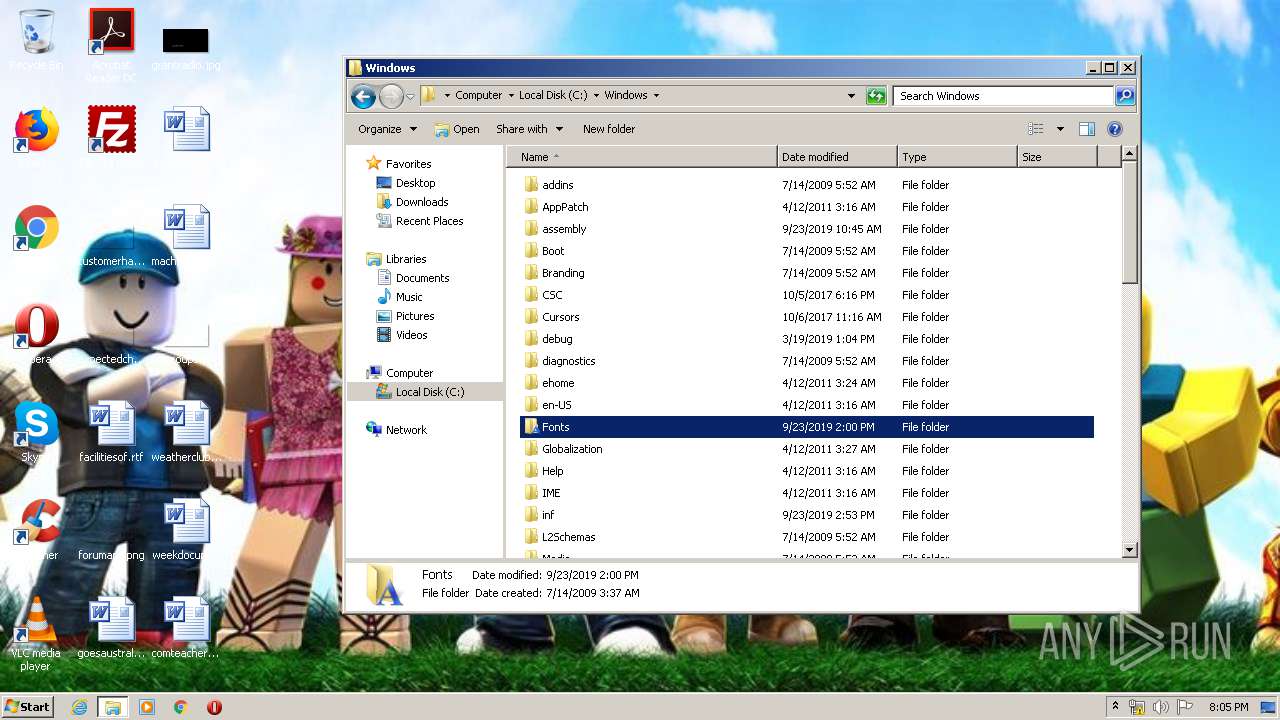
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1024 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2352 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2556 | "C:\Windows\System32\rundll32.exe" "C:\Program Files\Windows Photo Viewer\PhotoViewer.dll", ImageView_Fullscreen C:\Users\admin\AppData\Local\Temp\skynews-roblox-gaming_4353396.jpg | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4040 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
641
Read events
597
Write events
44
Delete events
0
Modification events
| (PID) Process: | (2556) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: rundll32.exe | |||
| (PID) Process: | (2556) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.jpg\OpenWithProgids |
| Operation: | write | Name: | jpegfile |
Value: | |||
| (PID) Process: | (2556) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (2556) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (2556) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (2556) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (2556) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (2556) rundll32.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | TileWallpaper |
Value: 0 | |||
| (PID) Process: | (2556) rundll32.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | WallpaperStyle |
Value: 0 | |||
| (PID) Process: | (2556) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Desktop\General |
| Operation: | write | Name: | WallpaperSource |
Value: C:\Users\admin\AppData\Roaming\Microsoft\Windows Photo Viewer\Windows Photo Viewer Wallpaper.jpg | |||
Executable files
2
Suspicious files
27
Text files
9
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2556 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\~PI8641.tmp | — | |
MD5:— | SHA256:— | |||
| 4040 | DllHost.exe | C:\$RECYCLE.BIN\S-1-5-21-1302019708-1500728564-335382590-1000\$RRMMAQ2 | — | |
MD5:— | SHA256:— | |||
| 4040 | DllHost.exe | C:\$RECYCLE.BIN\S-1-5-21-1302019708-1500728564-335382590-1000\$RF5FU9D | — | |
MD5:— | SHA256:— | |||
| 4040 | DllHost.exe | C:\$RECYCLE.BIN\S-1-5-21-1302019708-1500728564-335382590-1000\$RNNBDRC | — | |
MD5:— | SHA256:— | |||
| 4040 | DllHost.exe | C:\$RECYCLE.BIN\S-1-5-21-1302019708-1500728564-335382590-1000\$RQDSC0H | — | |
MD5:— | SHA256:— | |||
| 4040 | DllHost.exe | C:\$RECYCLE.BIN\S-1-5-21-1302019708-1500728564-335382590-1000\$RYBUSJ2 | — | |
MD5:— | SHA256:— | |||
| 4040 | DllHost.exe | C:\$RECYCLE.BIN\S-1-5-21-1302019708-1500728564-335382590-1000\$R84WW13 | — | |
MD5:— | SHA256:— | |||
| 4040 | DllHost.exe | C:\$RECYCLE.BIN\S-1-5-21-1302019708-1500728564-335382590-1000\$RJ4T75G | — | |
MD5:— | SHA256:— | |||
| 4040 | DllHost.exe | C:\$RECYCLE.BIN\S-1-5-21-1302019708-1500728564-335382590-1000\$R167KD4 | — | |
MD5:— | SHA256:— | |||
| 4040 | DllHost.exe | C:\$RECYCLE.BIN\S-1-5-21-1302019708-1500728564-335382590-1000\$R2JZ8HN | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report