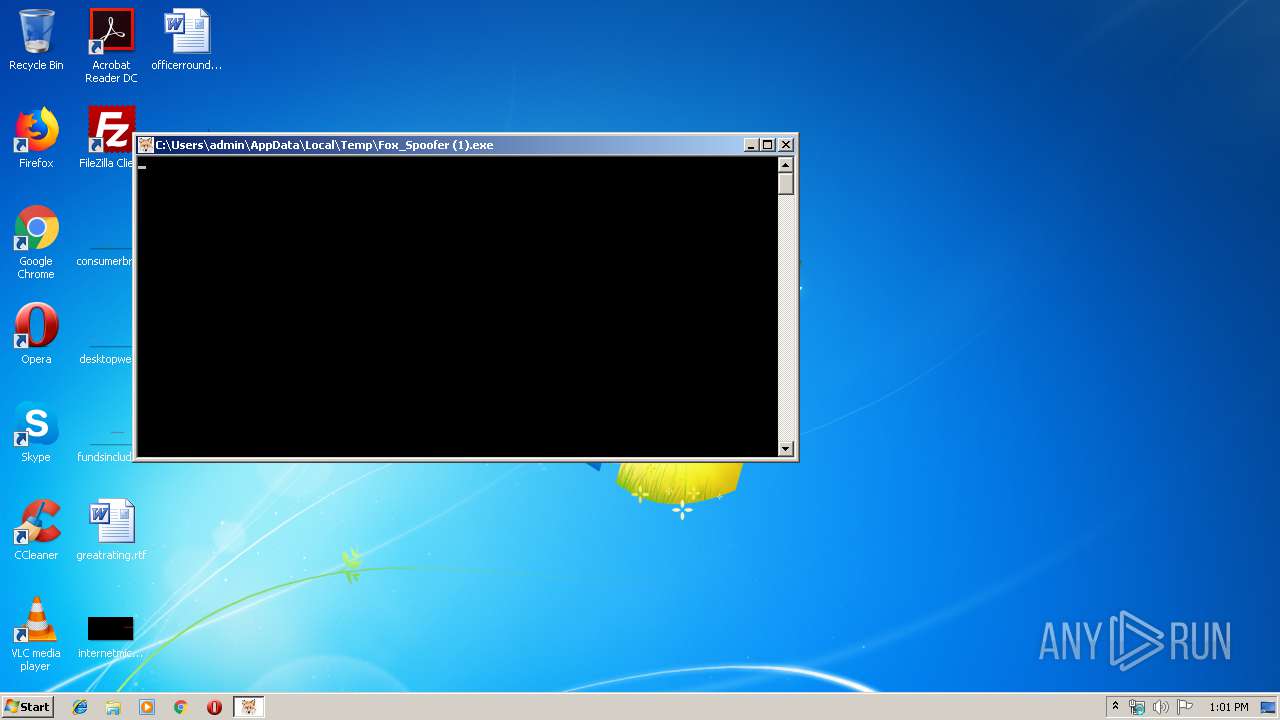
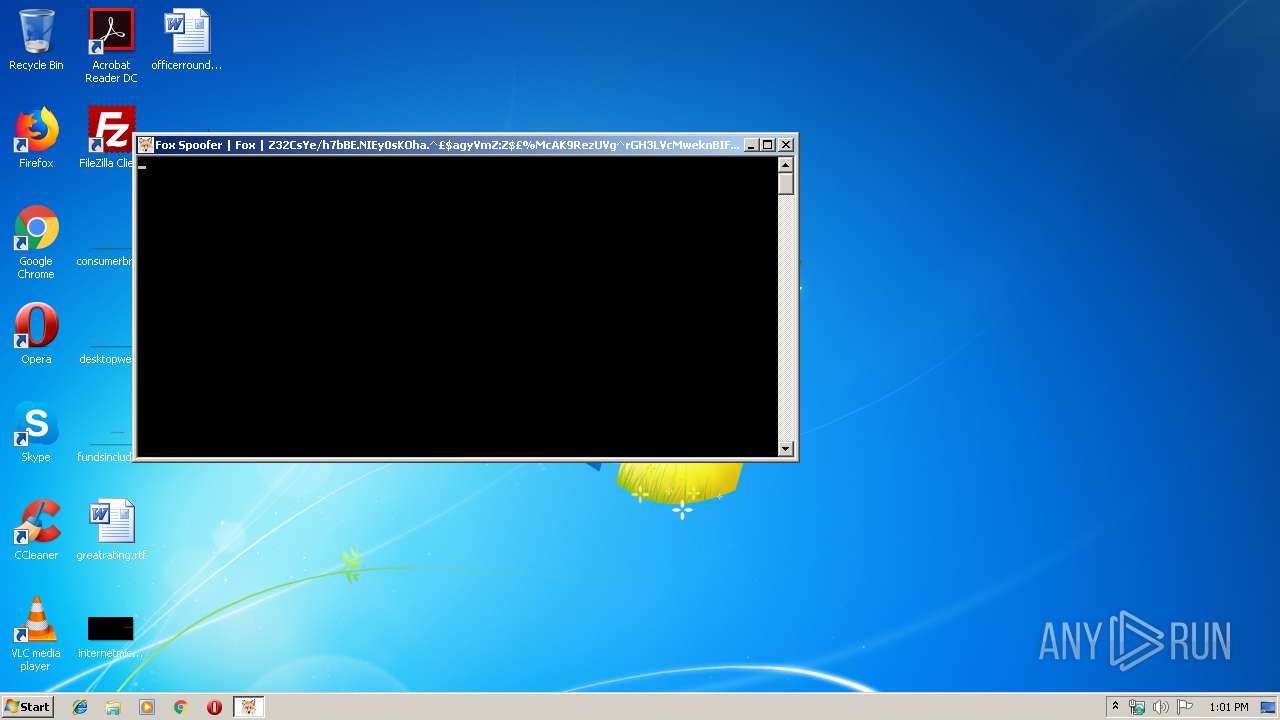
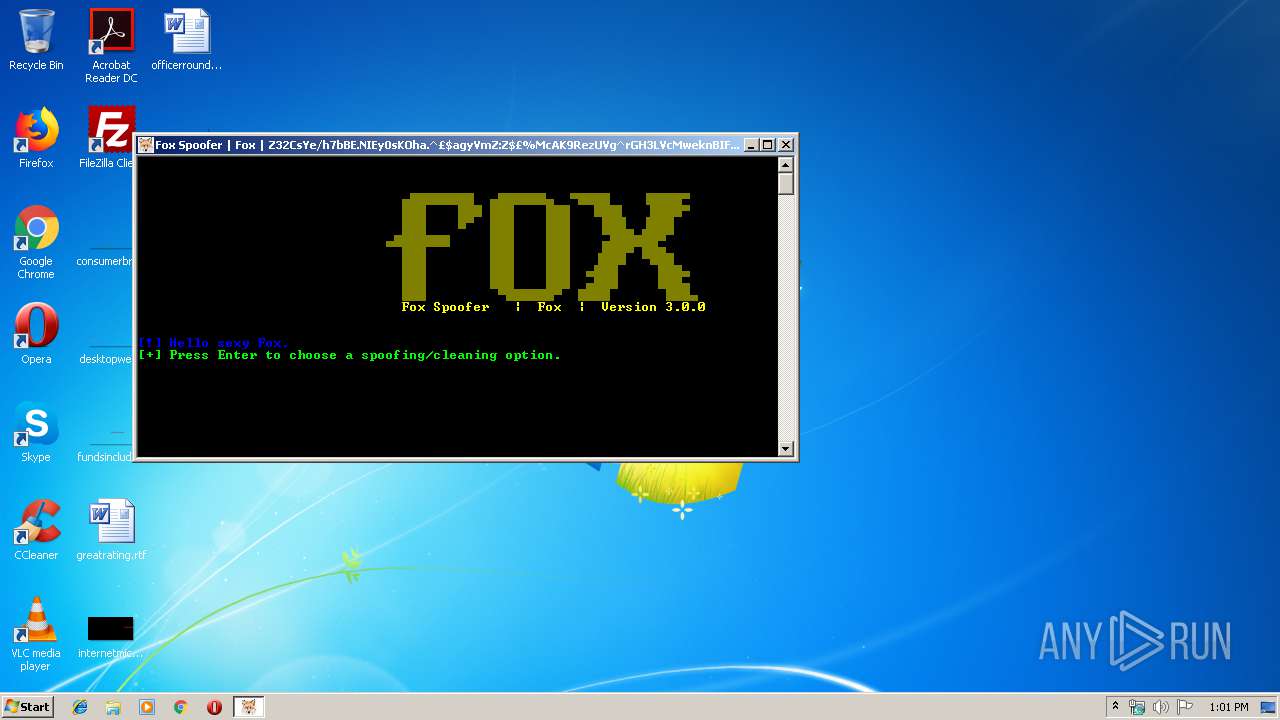
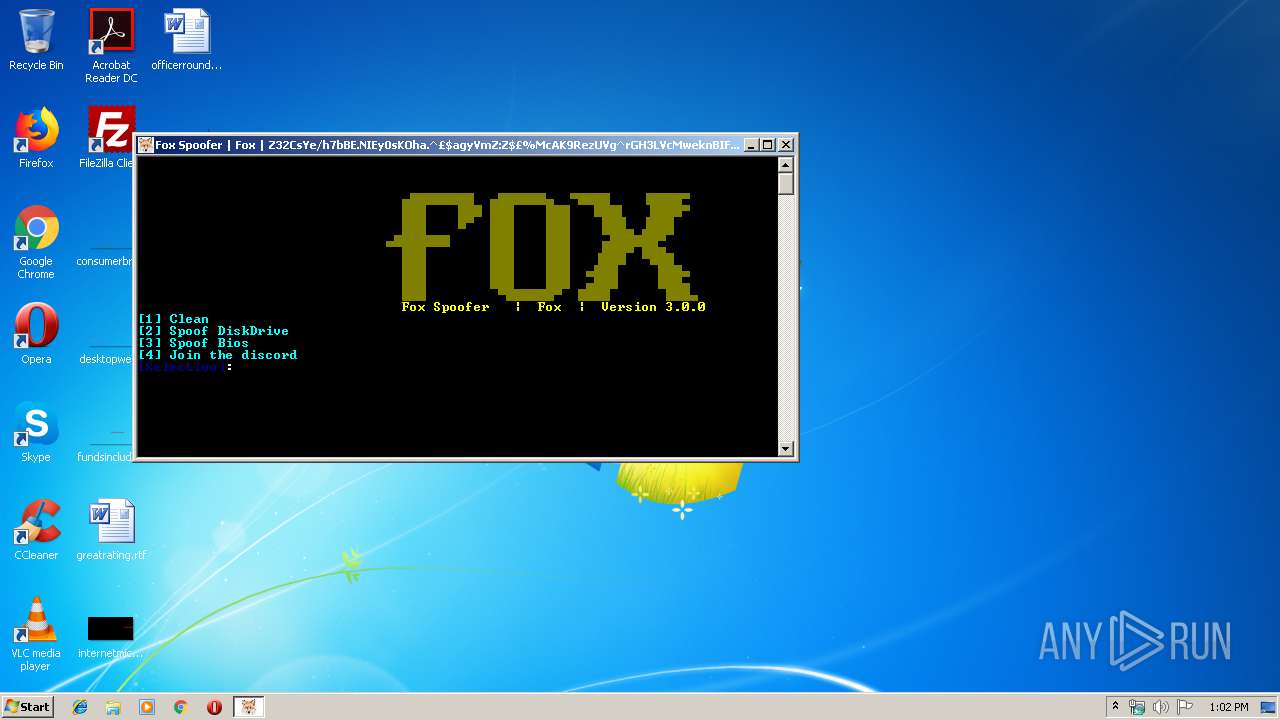
| File name: | Fox_Spoofer (1).exe |
| Full analysis: | https://app.any.run/tasks/378e5ec8-fa1b-4755-8d97-c7eaaa0f58a8 |
| Verdict: | Malicious activity |
| Analysis date: | November 16, 2019, 13:01:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 1975BCCC0E66C6664C8C70FE6157D59A |
| SHA1: | 0C2256862BBC32CF22784A8006EC2DFD635C459A |
| SHA256: | 252578CB5198D5444A7D02B628B1CFF525158FFE76EDC7602ADE6BB3199B58EC |
| SSDEEP: | 98304:c2yfksiI4IHjw1MGR1eWs0EPNZeCgkG4TdzelXD:XIksfDStR1C0A+4Tdz2D |
MALICIOUS
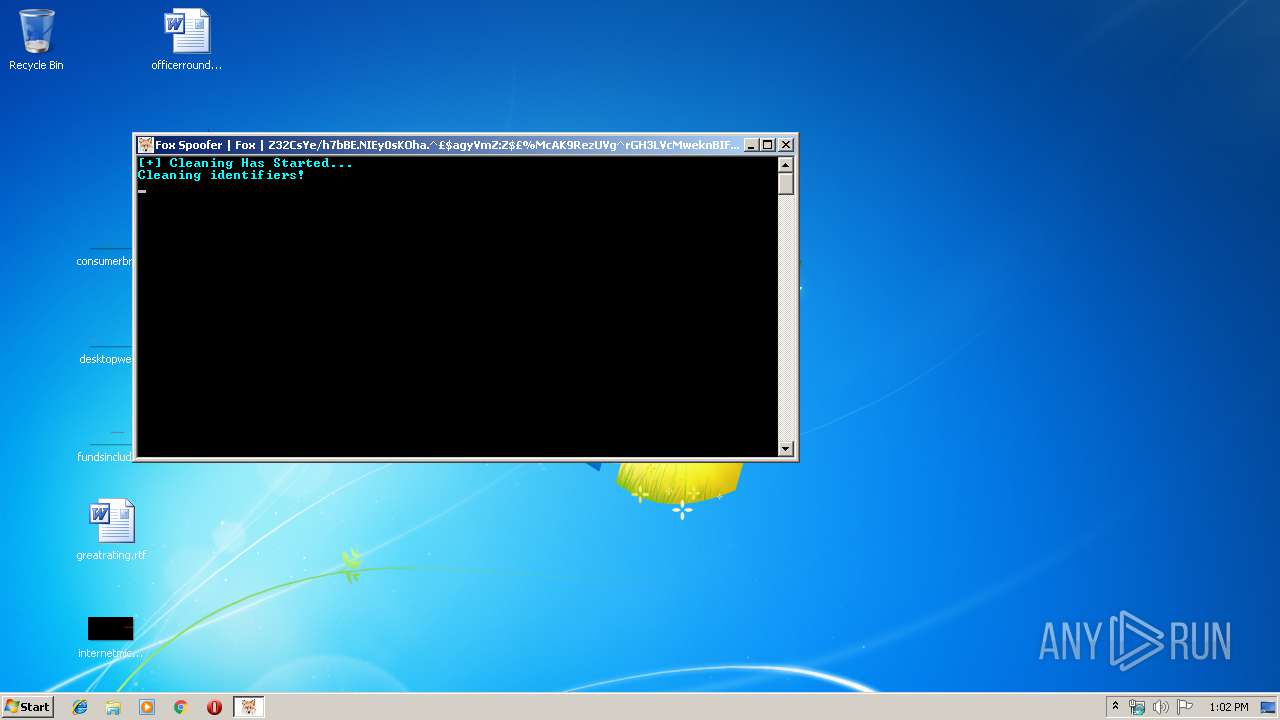
Loads dropped or rewritten executable
- Fox_Spoofer (1).exe (PID: 3984)
SUSPICIOUS
Starts CMD.EXE for commands execution
- Fox_Spoofer (1).exe (PID: 3984)
Executable content was dropped or overwritten
- Fox_Spoofer (1).exe (PID: 3984)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1416)
- cmd.exe (PID: 1648)
- cmd.exe (PID: 2912)
- cmd.exe (PID: 2620)
INFO
Reads the hosts file
- Fox_Spoofer (1).exe (PID: 3984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:11:16 13:07:58+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 5046784 |
| InitializedDataSize: | 5261312 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7be000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 4.0.0.0 |
| ProductVersionNumber: | 4.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
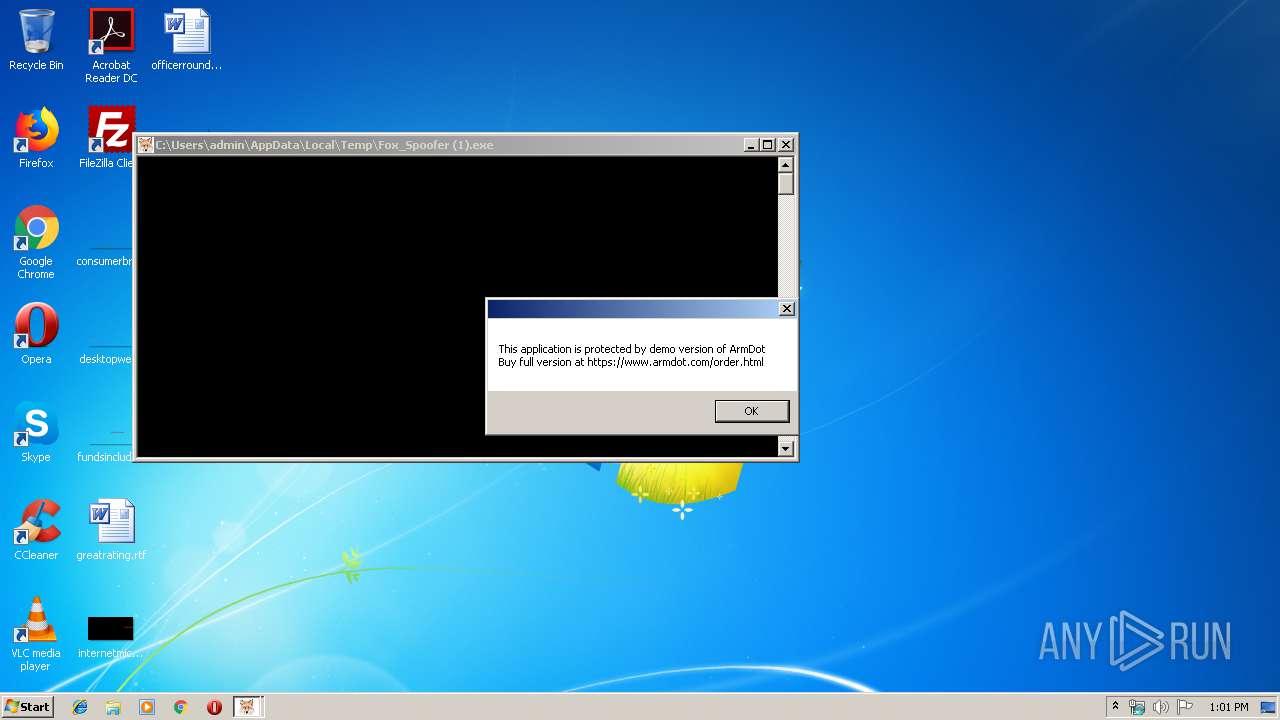
| Comments: | Spoofer |
| CompanyName: | ElysiumCheats.XYZ |
| FileDescription: | Elysium Spoofer |
| FileVersion: | 4.0.0.0 |
| InternalName: | Fox Spoofer.exe |
| LegalCopyright: | Copyright © Elysium |
| LegalTrademarks: | - |
| OriginalFileName: | Fox Spoofer.exe |
| ProductName: | Elysium Spoofer | Apex | Fortnite | R6S | Rust | H1Z1 | CSGO | Face-It |
| ProductVersion: | 4.0.0.0 |
| AssemblyVersion: | 4.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 16-Nov-2019 12:07:58 |
| Comments: | Spoofer |
| CompanyName: | ElysiumCheats.XYZ |
| FileDescription: | Elysium Spoofer |
| FileVersion: | 4.0.0.0 |
| InternalName: | Fox Spoofer.exe |
| LegalCopyright: | Copyright © Elysium |
| LegalTrademarks: | - |
| OriginalFilename: | Fox Spoofer.exe |
| ProductName: | Elysium Spoofer | Apex | Fortnite | R6S | Rust | H1Z1 | CSGO | Face-It |
| ProductVersion: | 4.0.0.0 |
| Assembly Version: | 4.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x867A |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 16-Nov-2019 12:07:58 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00002000 | 0x004D2000 | 0x0026EE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.95987 | |
.rsrc | 0x004D4000 | 0x000344CC | 0x0001DA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99447 |
.idata | 0x0050A000 | 0x00002000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.30872 |
pxxhlmtp | 0x0050C000 | 0x002B2000 | 0x002B0200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.48976 |
orpukwss | 0x007BE000 | 0x00002000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.17689 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00772 | 3168 | UNKNOWN | UNKNOWN | RT_MANIFEST |
32512 | 2.16096 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
comctl32.dll |
kernel32.dll |
Total processes
52
Monitored processes
10
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | taskkill /F /IM Razer Synapse Service.exe /T | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 436 | taskkill /F /IM IPROSetMonitor.exe /T | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1028 | "C:\Users\admin\AppData\Local\Temp\Fox_Spoofer (1).exe" | C:\Users\admin\AppData\Local\Temp\Fox_Spoofer (1).exe | — | explorer.exe | |||||||||||
User: admin Company: ElysiumCheats.XYZ Integrity Level: MEDIUM Description: Elysium Spoofer Exit code: 3221226540 Version: 4.0.0.0 Modules
| |||||||||||||||
| 1416 | "C:\Windows\System32\cmd.exe" /c taskkill /F /IM RazerCentralService /T | C:\Windows\System32\cmd.exe | — | Fox_Spoofer (1).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1648 | "C:\Windows\System32\cmd.exe" /c taskkill /F /IM Razer Synapse Service.exe /T | C:\Windows\System32\cmd.exe | — | Fox_Spoofer (1).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2620 | "C:\Windows\System32\cmd.exe" /c taskkill /F /IM Razer Synapse Service Process.exe /T | C:\Windows\System32\cmd.exe | — | Fox_Spoofer (1).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2912 | "C:\Windows\System32\cmd.exe" /c taskkill /F /IM IPROSetMonitor.exe /T | C:\Windows\System32\cmd.exe | — | Fox_Spoofer (1).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3032 | taskkill /F /IM RazerCentralService /T | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3984 | "C:\Users\admin\AppData\Local\Temp\Fox_Spoofer (1).exe" | C:\Users\admin\AppData\Local\Temp\Fox_Spoofer (1).exe | explorer.exe | ||||||||||||
User: admin Company: ElysiumCheats.XYZ Integrity Level: HIGH Description: Elysium Spoofer Exit code: 0 Version: 4.0.0.0 Modules
| |||||||||||||||
| 4020 | taskkill /F /IM Razer Synapse Service Process.exe /T | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
159
Read events
133
Write events
26
Delete events
0
Modification events
| (PID) Process: | (3984) Fox_Spoofer (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3984) Fox_Spoofer (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3984) Fox_Spoofer (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Fox_Spoofer (1)_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3984) Fox_Spoofer (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Fox_Spoofer (1)_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3984) Fox_Spoofer (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Fox_Spoofer (1)_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3984) Fox_Spoofer (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Fox_Spoofer (1)_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3984) Fox_Spoofer (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Fox_Spoofer (1)_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3984) Fox_Spoofer (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Fox_Spoofer (1)_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3984) Fox_Spoofer (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Fox_Spoofer (1)_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3984) Fox_Spoofer (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Fox_Spoofer (1)_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3984 | Fox_Spoofer (1).exe | C:\Windows\Fonts\registery.bat | text | |
MD5:— | SHA256:— | |||
| 3984 | Fox_Spoofer (1).exe | C:\Users\admin\AppData\Local\Temp\4d7ee5a6-9d64-43ad-9e58-015bbc6167b9\AgileDotNetRT.dll | executable | |
MD5:14FF402962AD21B78AE0B4C43CD1F194 | SHA256:FB9646CB956945BDC503E69645F6B5316D3826B780D3C36738D6B944E884D15B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3984 | Fox_Spoofer (1).exe | 216.58.206.14:443 | google.com | Google Inc. | US | whitelisted |
3984 | Fox_Spoofer (1).exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
— | — | 162.159.135.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| malicious |
www.google.com |
| malicious |
cdn.discordapp.com |
| shared |
Threats
Process | Message |
|---|---|
Fox_Spoofer (1).exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
Fox_Spoofer (1).exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |