| File name: | b9f4c09b3ee233eea8a09b70ab3e6c4e.exe |
| Full analysis: | https://app.any.run/tasks/f391dbd1-3d5c-4f4a-823a-63cfc658afe0 |
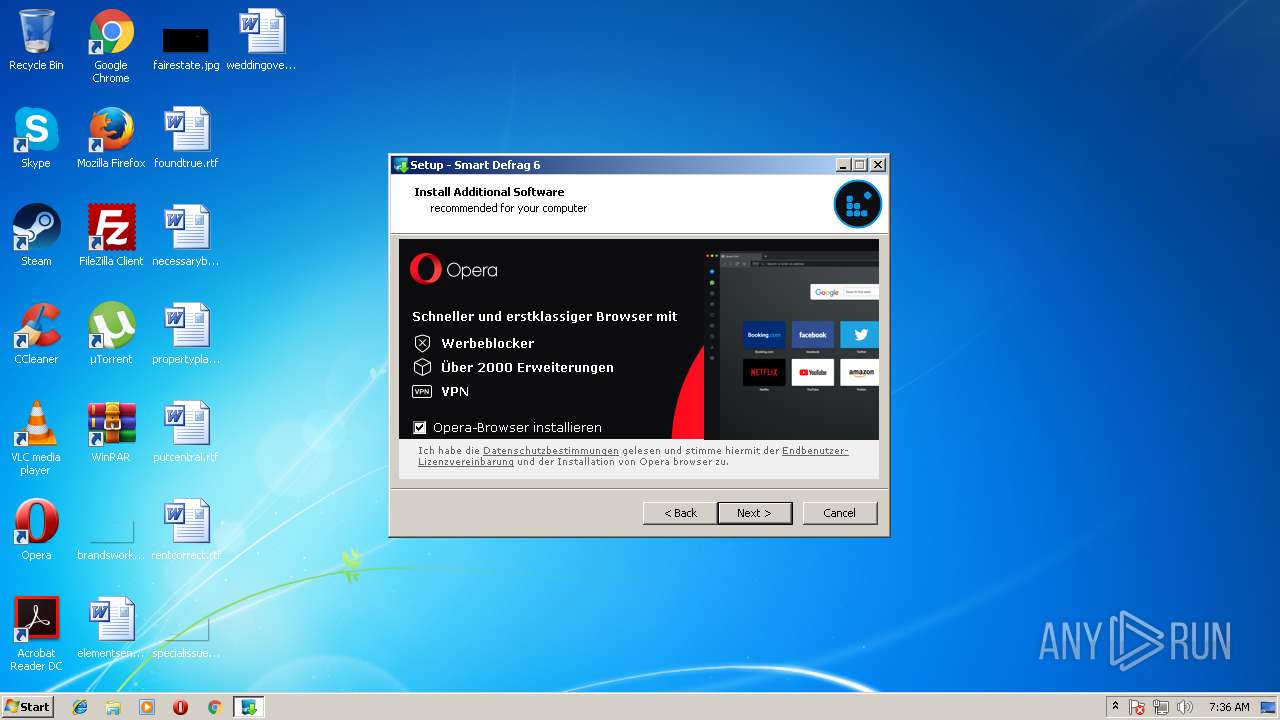
| Verdict: | Malicious activity |
| Analysis date: | September 05, 2018, 06:36:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B9F4C09B3EE233EEA8A09B70AB3E6C4E |
| SHA1: | 2CAD35101951E803F8993D607FBA25C5C6C5E48D |
| SHA256: | 2521920A736F1793FAF71E9DABA47A0E7B6DDDF6953681C955E5F720C0B68279 |
| SSDEEP: | 393216:PzNLub9F5blma8HcfIDc1yHUfOgn4a0v1zDT4q/dh74zs:hubzPvQhDc1yHDPam54KP7Qs |
MALICIOUS
Application was dropped or rewritten from another process
- LocalLang.exe (PID: 3540)
SUSPICIOUS
Executable content was dropped or overwritten
- b9f4c09b3ee233eea8a09b70ab3e6c4e.exe (PID: 2200)
- b9f4c09b3ee233eea8a09b70ab3e6c4e.exe (PID: 2172)
- b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp (PID: 3344)
Reads Windows owner settings
- b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp (PID: 3344)
Reads the Windows organization settings
- b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp (PID: 3344)
Creates files in the user directory
- b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp (PID: 3344)
Reads the machine GUID from the registry
- b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp (PID: 3344)
Reads CPU info
- b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp (PID: 3344)
Reads the date of Windows installation
- b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp (PID: 3344)
Reads internet explorer settings
- b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp (PID: 3344)
Reads productID from registry
- b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp (PID: 3344)
Uses TASKKILL.EXE to kill process
- b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp (PID: 3344)
INFO
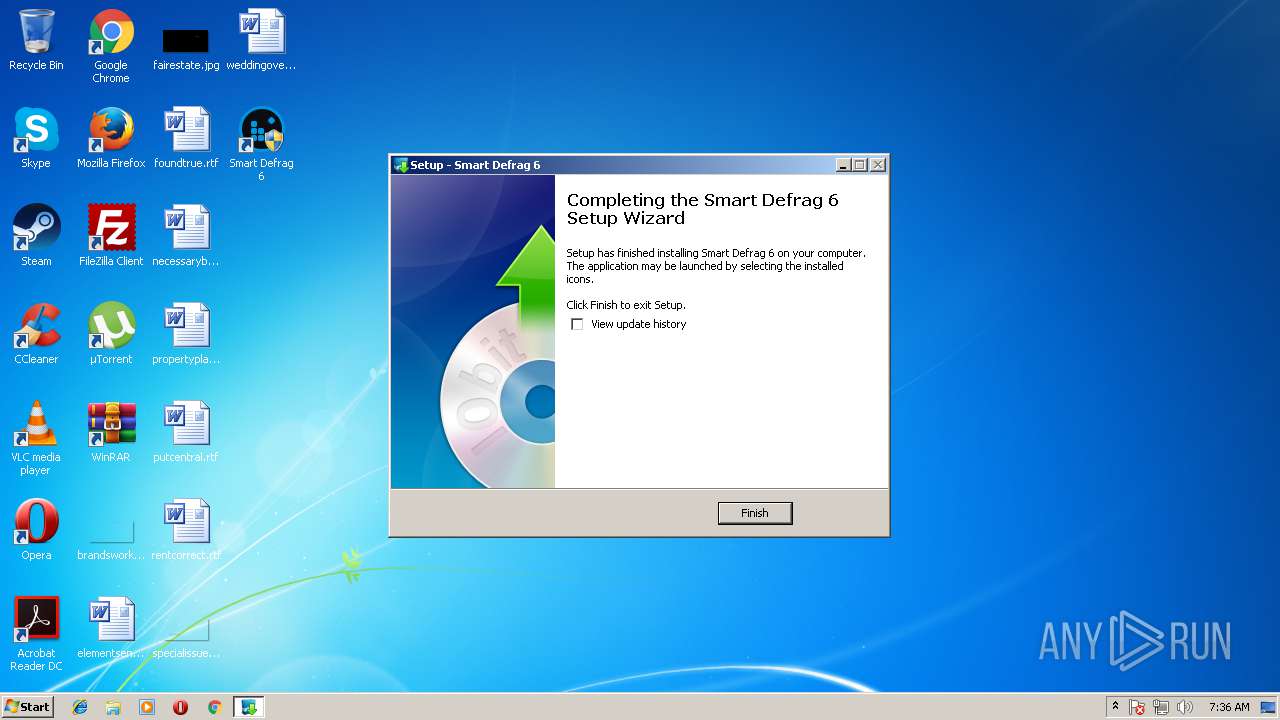
Application was dropped or rewritten from another process
- b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp (PID: 2484)
- b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp (PID: 3344)
Loads dropped or rewritten executable
- b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp (PID: 3344)
Dropped object may contain Bitcoin addresses
- b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp (PID: 3344)
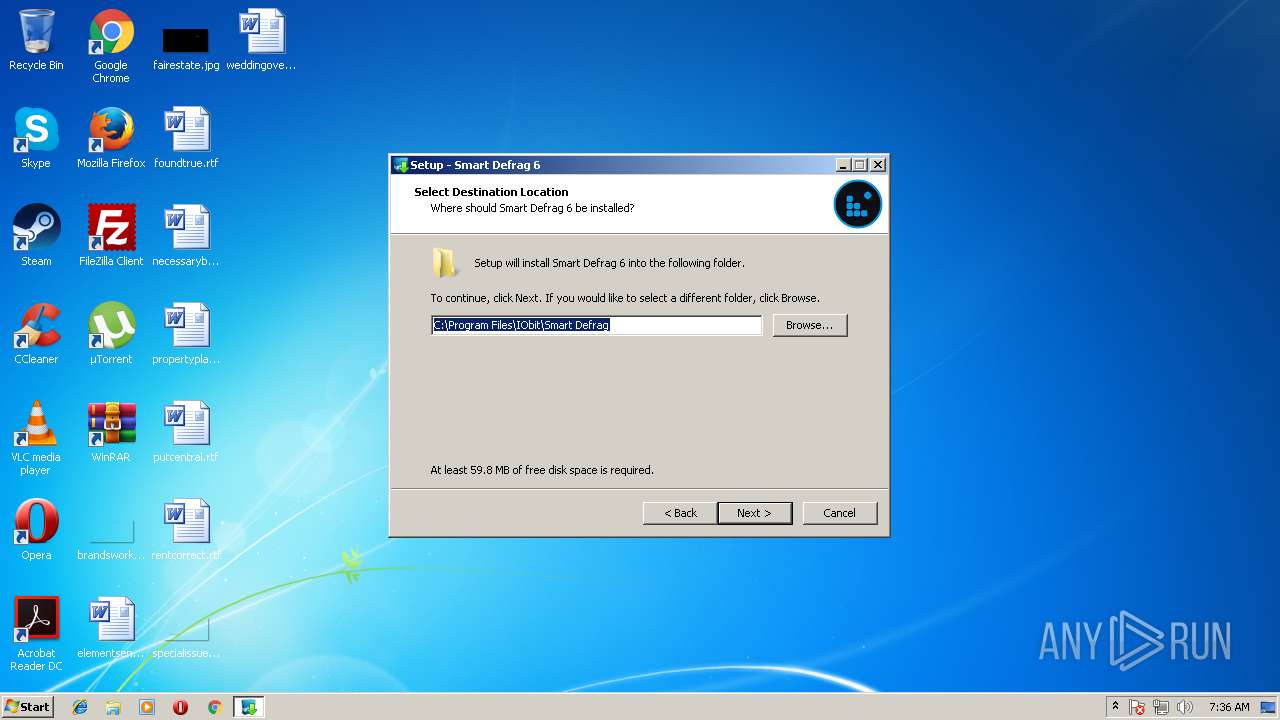
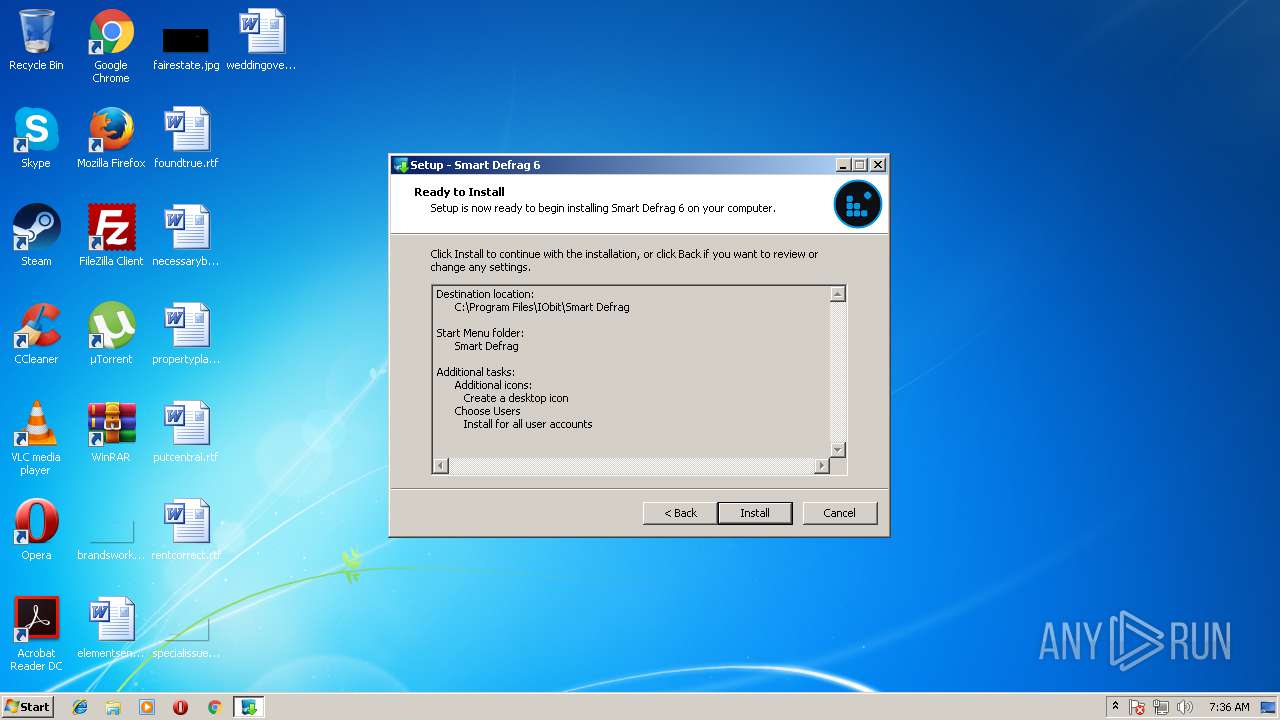
Creates files in the program directory
- b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp (PID: 3344)
Creates a software uninstall entry
- b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp (PID: 3344)
Dropped object may contain URL's
- b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp (PID: 3344)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (45.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (20.9) |
| .exe | | | Win32 Executable (generic) (14.3) |
| .exe | | | Win16/32 Executable Delphi generic (6.6) |
| .exe | | | Generic Win/DOS Executable (6.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:07:16 15:24:20+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 65024 |
| InitializedDataSize: | 71168 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x113bc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.1.116 |
| ProductVersionNumber: | 6.0.1.116 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | IObit |
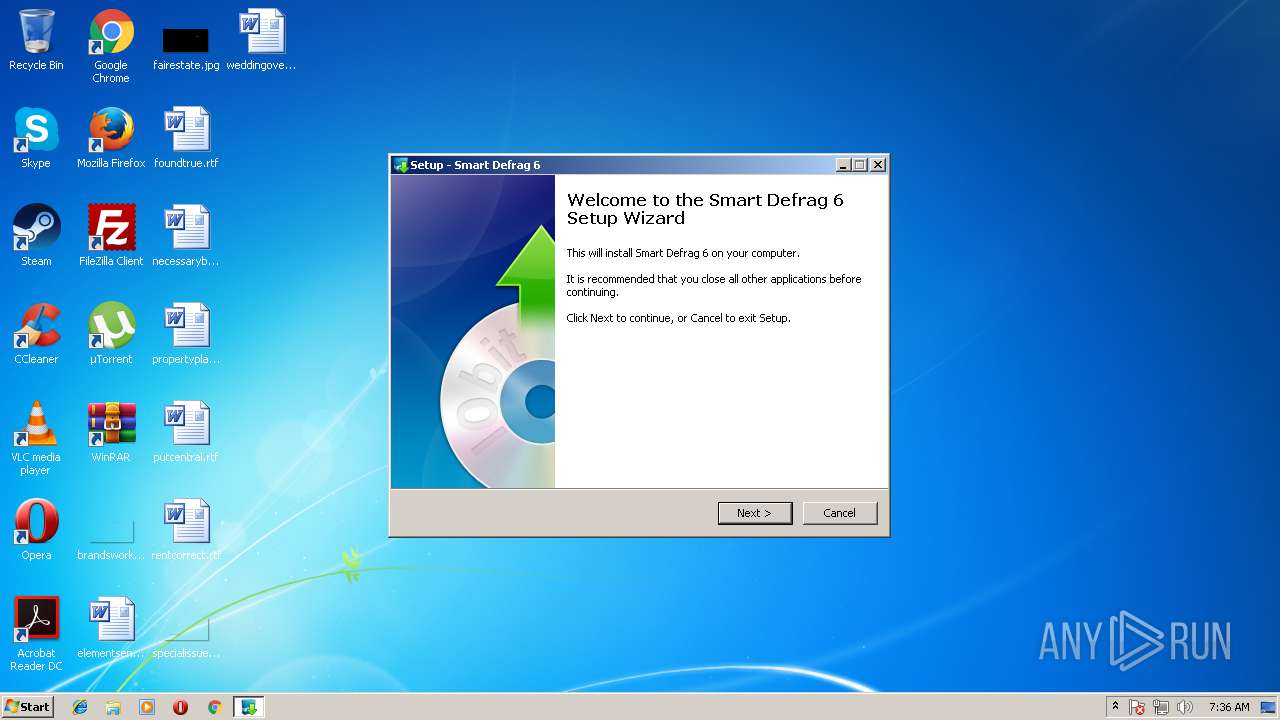
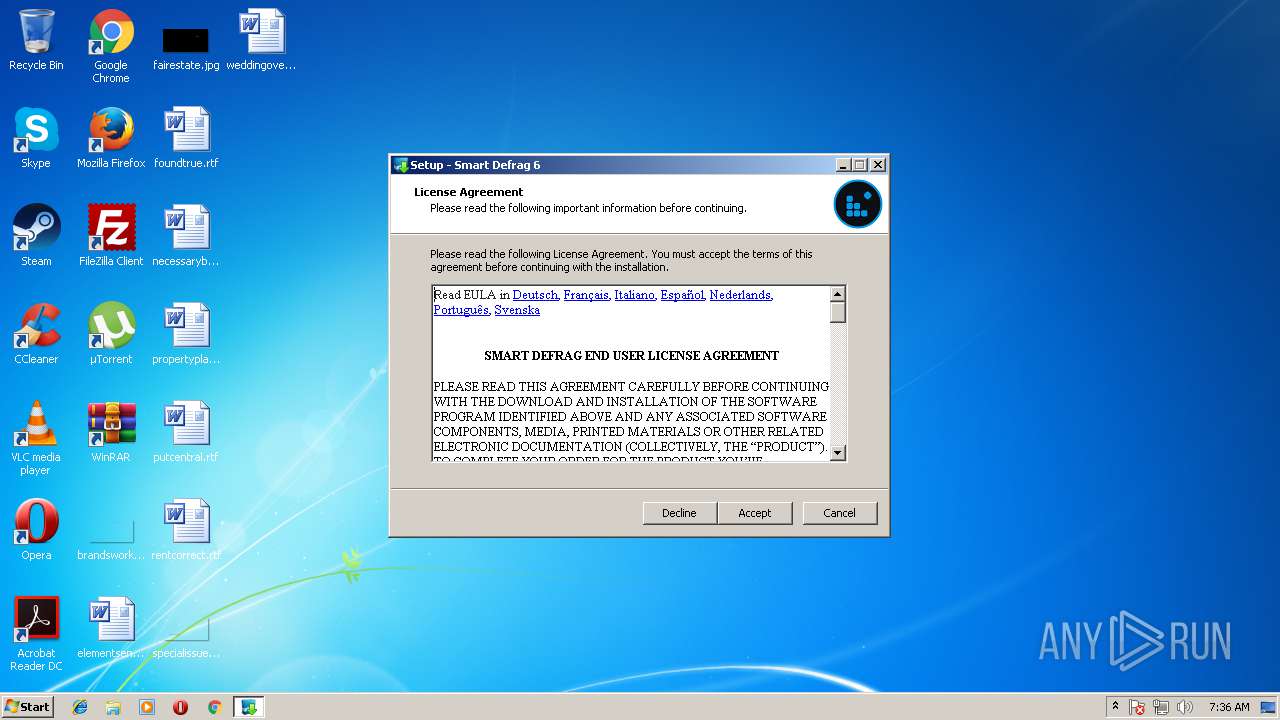
| FileDescription: | Smart Defrag 6 |
| FileVersion: | 6.0.1.116 |
| LegalCopyright: | ©IObit. All rights reserved. |
| ProductName: | Smart Defrag 6 |
| ProductVersion: | 6.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Jul-2015 13:24:20 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | IObit |
| FileDescription: | Smart Defrag 6 |
| FileVersion: | 6.0.1.116 |
| LegalCopyright: | ©IObit. All rights reserved. |
| ProductName: | Smart Defrag 6 |
| ProductVersion: | 6.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 16-Jul-2015 13:24:20 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F134 | 0x0000F200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.39165 |
.itext | 0x00011000 | 0x00000B44 | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.74124 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.24753 |
.bss | 0x00013000 | 0x000056B8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000DD0 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.97188 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0000F648 | 0x0000F800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.24005 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 6.60033 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.62731 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.96326 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 6.48717 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.99451 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
50
Monitored processes
9
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1888 | "C:\Windows\System32\taskkill.exe" -f -im sdproxy.exe | C:\Windows\System32\taskkill.exe | — | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2172 | "C:\Users\admin\AppData\Local\Temp\b9f4c09b3ee233eea8a09b70ab3e6c4e.exe" | C:\Users\admin\AppData\Local\Temp\b9f4c09b3ee233eea8a09b70ab3e6c4e.exe | explorer.exe | ||||||||||||
User: admin Company: IObit Integrity Level: MEDIUM Description: Smart Defrag 6 Exit code: 0 Version: 6.0.1.116 Modules
| |||||||||||||||
| 2200 | "C:\Users\admin\AppData\Local\Temp\b9f4c09b3ee233eea8a09b70ab3e6c4e.exe" /SPAWNWND=$180260 /NOTIFYWND=$220210 | C:\Users\admin\AppData\Local\Temp\b9f4c09b3ee233eea8a09b70ab3e6c4e.exe | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | ||||||||||||
User: admin Company: IObit Integrity Level: HIGH Description: Smart Defrag 6 Exit code: 0 Version: 6.0.1.116 Modules
| |||||||||||||||
| 2372 | "C:\Windows\System32\taskkill.exe" -f -im SDInit.exe | C:\Windows\System32\taskkill.exe | — | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2484 | "C:\Users\admin\AppData\Local\Temp\is-DNCGB.tmp\b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp" /SL5="$220210,14121325,137216,C:\Users\admin\AppData\Local\Temp\b9f4c09b3ee233eea8a09b70ab3e6c4e.exe" | C:\Users\admin\AppData\Local\Temp\is-DNCGB.tmp\b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | — | b9f4c09b3ee233eea8a09b70ab3e6c4e.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2888 | "C:\Windows\System32\taskkill.exe" -f -im SmartDefrag.exe | C:\Windows\System32\taskkill.exe | — | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3344 | "C:\Users\admin\AppData\Local\Temp\is-9IM19.tmp\b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp" /SL5="$3101A2,14121325,137216,C:\Users\admin\AppData\Local\Temp\b9f4c09b3ee233eea8a09b70ab3e6c4e.exe" /SPAWNWND=$180260 /NOTIFYWND=$220210 | C:\Users\admin\AppData\Local\Temp\is-9IM19.tmp\b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | b9f4c09b3ee233eea8a09b70ab3e6c4e.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3540 | "C:\Program Files\IObit\Smart Defrag\LocalLang.exe" | C:\Program Files\IObit\Smart Defrag\LocalLang.exe | — | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | |||||||||||
User: admin Company: IObit Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3772 | "C:\Windows\System32\taskkill.exe" -f -im AutoUpdate.exe | C:\Windows\System32\taskkill.exe | — | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
739
Read events
684
Write events
55
Delete events
0
Modification events
| (PID) Process: | (3344) b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\59\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3344) b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3344) b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3344) b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\b9f4c09b3ee233eea8a09b70ab3e6c4e_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3344) b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\b9f4c09b3ee233eea8a09b70ab3e6c4e_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3344) b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\b9f4c09b3ee233eea8a09b70ab3e6c4e_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3344) b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\b9f4c09b3ee233eea8a09b70ab3e6c4e_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3344) b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\b9f4c09b3ee233eea8a09b70ab3e6c4e_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3344) b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\b9f4c09b3ee233eea8a09b70ab3e6c4e_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3344) b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\b9f4c09b3ee233eea8a09b70ab3e6c4e_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
69
Suspicious files
5
Text files
138
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3344 | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | C:\Users\admin\AppData\Local\Temp\004C83A5.log | — | |
MD5:— | SHA256:— | |||
| 3344 | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | C:\Users\admin\AppData\Local\Temp\is-G2ON7.tmp\SsmbKBVMRa.dll | executable | |
MD5:— | SHA256:— | |||
| 3344 | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | C:\Users\admin\AppData\Roaming\IObit\Smart Defrag\Config.ini | text | |
MD5:— | SHA256:— | |||
| 2172 | b9f4c09b3ee233eea8a09b70ab3e6c4e.exe | C:\Users\admin\AppData\Local\Temp\is-DNCGB.tmp\b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | executable | |
MD5:F32661784543DCEFDC2132B9211A852E | SHA256:951518CE2AC94B078EA959152F0551365F86520F49E3AB840B44FDB035214632 | |||
| 3344 | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | C:\Users\admin\AppData\Local\Temp\is-G2ON7.tmp\Inno_English.lng | text | |
MD5:7994F562A0D36D1A8CB7EE0E59CB97E2 | SHA256:085436D644BFBA34440AA7DB7A358C276EF22D44C6672FB9A374878BA9B4876A | |||
| 2200 | b9f4c09b3ee233eea8a09b70ab3e6c4e.exe | C:\Users\admin\AppData\Local\Temp\is-9IM19.tmp\b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | executable | |
MD5:F32661784543DCEFDC2132B9211A852E | SHA256:951518CE2AC94B078EA959152F0551365F86520F49E3AB840B44FDB035214632 | |||
| 3344 | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | C:\Users\admin\AppData\Local\Temp\nsd501443749480\css\sdk-ui\browse.css | text | |
MD5:6009D6E864F60AEA980A9DF94C1F7E1C | SHA256:5EF48A8C8C3771B4F233314D50DD3B5AFDCD99DD4B74A9745C8FE7B22207056D | |||
| 3344 | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | C:\Users\admin\AppData\Local\Temp\nsd501443749480\csshover3.htc | html | |
MD5:52FA0DA50BF4B27EE625C80D36C67941 | SHA256:E37E99DDFC73AC7BA774E23736B2EF429D9A0CB8C906453C75B14C029BDD5493 | |||
| 3344 | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | C:\Users\admin\AppData\Local\Temp\nsd501443749480\css\sdk-ui\images\button-bg.png | image | |
MD5:98B1DE48DFA64DC2AA1E52FACFBEE3B0 | SHA256:2693930C474FE640E2FE8D6EF98ABE2ECD303D2392C3D8B2E006E8942BA8F534 | |||
| 3344 | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | C:\Users\admin\AppData\Local\Temp\nsd501443749480\css\main.css | text | |
MD5:9B27E2A266FE15A3AABFE635C29E8923 | SHA256:166AA42BC5216C5791388847AE114EC0671A0D97B9952D14F29419B8BE3FB23F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
4
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3344 | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | POST | 200 | 52.31.104.117:80 | http://portal.nusoddtih-zeneb.com/ | IE | — | — | malicious |
3344 | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | POST | 200 | 52.31.104.117:80 | http://portal.nusoddtih-zeneb.com/ | IE | — | — | malicious |
3344 | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | GET | 200 | 199.201.110.78:80 | http://img.nusoddtih-zeneb.com/img/Rowabobeso/icon2.png | US | image | 422 b | malicious |
3344 | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | GET | 200 | 199.201.110.78:80 | http://img.nusoddtih-zeneb.com/img/Rowabobeso/icon1.png | US | image | 481 b | malicious |
3344 | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | GET | 200 | 199.201.110.78:80 | http://img.nusoddtih-zeneb.com/img/Rowabobeso/icon3.png | US | image | 351 b | malicious |
3344 | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | POST | 200 | 52.213.172.218:80 | http://ww3.nusoddtih-zeneb.com/FusionIObit/ | IE | binary | 328 Kb | malicious |
3344 | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | POST | 200 | 52.31.104.117:80 | http://portal.nusoddtih-zeneb.com/ | IE | — | — | malicious |
3344 | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | POST | 200 | 52.31.104.117:80 | http://portal.nusoddtih-zeneb.com/ | IE | — | — | malicious |
3344 | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | GET | 200 | 199.201.110.78:80 | http://img.nusoddtih-zeneb.com/img/Rowabobeso/b2_fus_clean.png | US | image | 33.6 Kb | malicious |
3344 | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | POST | 200 | 52.31.104.117:80 | http://portal.nusoddtih-zeneb.com/ | IE | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3344 | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | 52.213.172.218:80 | ww3.nusoddtih-zeneb.com | Amazon.com, Inc. | IE | whitelisted |
3344 | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | 199.201.110.78:80 | img.nusoddtih-zeneb.com | Namecheap, Inc. | US | malicious |
3344 | b9f4c09b3ee233eea8a09b70ab3e6c4e.tmp | 52.31.104.117:80 | portal.nusoddtih-zeneb.com | Amazon.com, Inc. | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
portal.nusoddtih-zeneb.com |
| malicious |
ww3.nusoddtih-zeneb.com |
| malicious |
img.nusoddtih-zeneb.com |
| malicious |