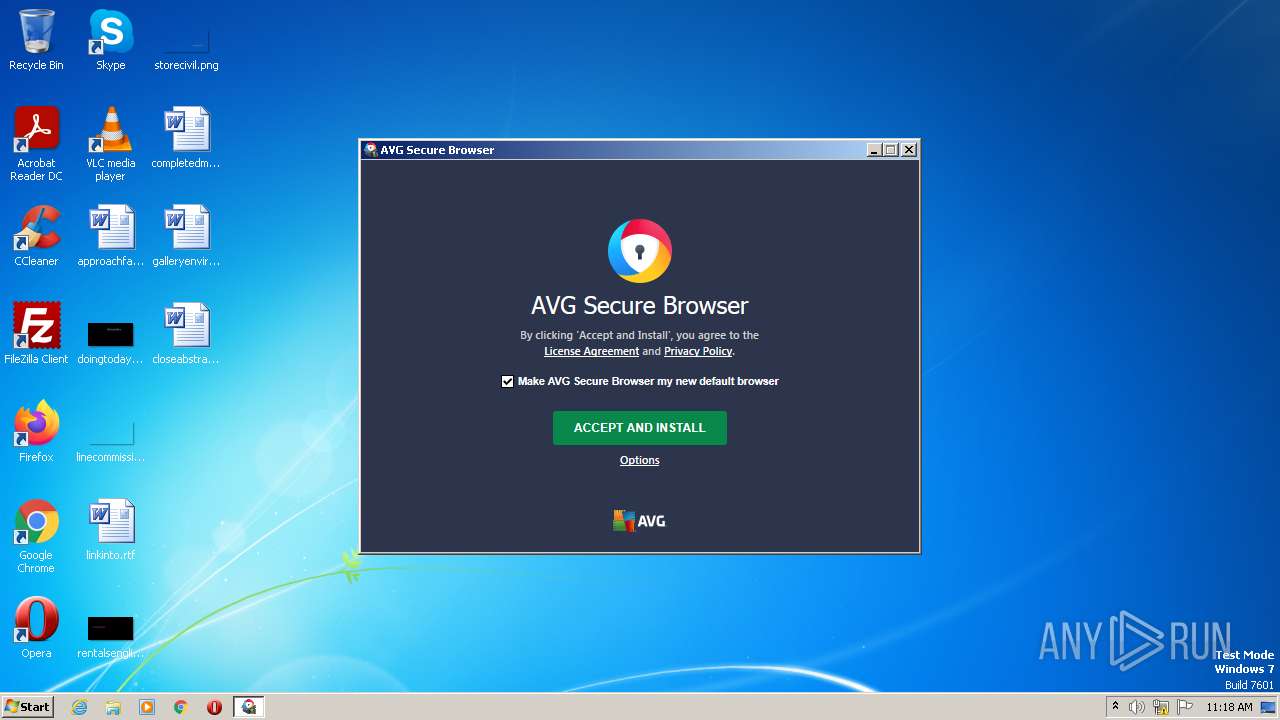
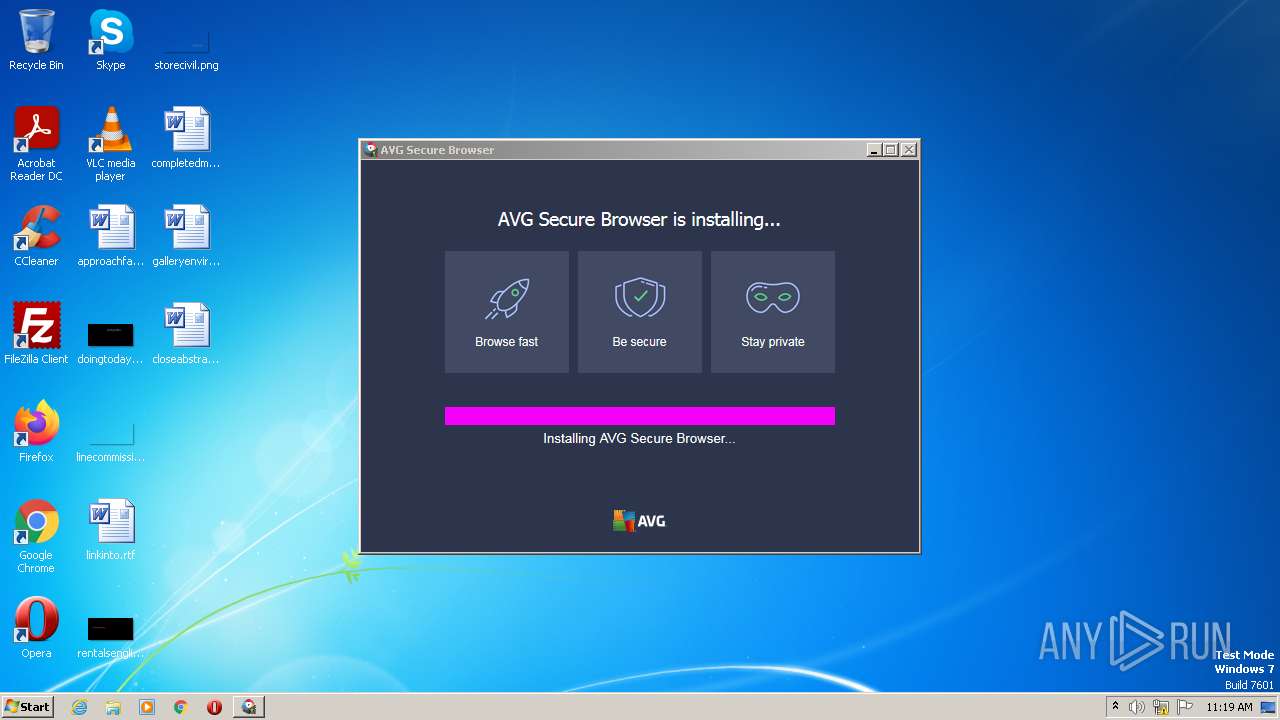
| File name: | avg_secure_browser_setup.exe |
| Full analysis: | https://app.any.run/tasks/fe736e28-8022-4d85-883f-a971c291ff98 |
| Verdict: | Malicious activity |
| Analysis date: | March 27, 2023, 10:17:55 |
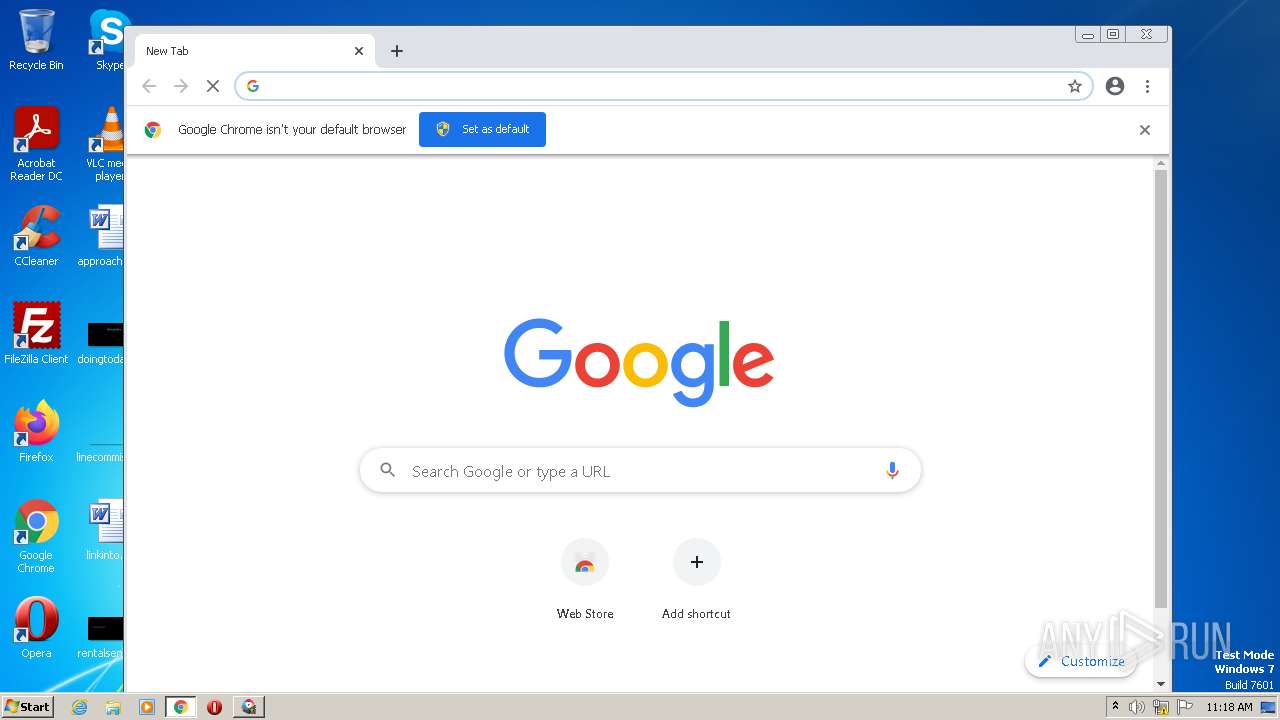
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 775964F0CA9CFE7F12BEE4FA77392E38 |
| SHA1: | 6419EC8D160E30723AF071D6911F6E376400C00A |
| SHA256: | 251AF2D396C5D86B2F02B7E26D01D082B8DD75E99C86C707719FED7F4B02F1D1 |
| SSDEEP: | 98304:ChrFUtI3ZZwvNVTGCLlAL4nI2xR3icXzGVgCFNhmAW2sEZiO//xuGal5vnh3pKe+:U6tI3ZZwvN5vCL2IwRRDx5AJjhivnhf+ |
MALICIOUS
Application was dropped or rewritten from another process
- ajFED.exe (PID: 3388)
- AVGBrowserUpdateSetup.exe (PID: 3036)
- AVGBrowserUpdate.exe (PID: 3076)
- AVGBrowserUpdate.exe (PID: 3304)
- AVGBrowserUpdate.exe (PID: 3408)
- AVGBrowserUpdate.exe (PID: 1796)
- AVGBrowserUpdate.exe (PID: 3636)
Actions looks like stealing of personal data
- ajFED.exe (PID: 3388)
Steals credentials from Web Browsers
- ajFED.exe (PID: 3388)
SUSPICIOUS
The process checks presence of the antivirus software
- avg_secure_browser_setup.exe (PID: 2340)
- ajFED.exe (PID: 3388)
Executable content was dropped or overwritten
- avg_secure_browser_setup.exe (PID: 2340)
- ajFED.exe (PID: 3388)
- AVGBrowserUpdateSetup.exe (PID: 3036)
- AVGBrowserUpdate.exe (PID: 3076)
Reads security settings of Internet Explorer
- ajFED.exe (PID: 3388)
Searches for installed software
- ajFED.exe (PID: 3388)
Checks Windows Trust Settings
- ajFED.exe (PID: 3388)
Reads the Internet Settings
- ajFED.exe (PID: 3388)
- AVGBrowserUpdate.exe (PID: 3408)
- AVGBrowserUpdate.exe (PID: 1796)
Creates/Modifies COM task schedule object
- AVGBrowserUpdate.exe (PID: 3304)
Reads settings of System Certificates
- ajFED.exe (PID: 3388)
- AVGBrowserUpdate.exe (PID: 3408)
- AVGBrowserUpdate.exe (PID: 1796)
Starts itself from another location
- AVGBrowserUpdate.exe (PID: 3076)
Process requests binary or script from the Internet
- AVGBrowserUpdate.exe (PID: 1796)
INFO
Checks supported languages
- avg_secure_browser_setup.exe (PID: 2340)
- ajFED.exe (PID: 3388)
- AVGBrowserUpdateSetup.exe (PID: 3036)
- AVGBrowserUpdate.exe (PID: 3076)
- AVGBrowserUpdate.exe (PID: 3304)
- AVGBrowserUpdate.exe (PID: 1796)
- AVGBrowserUpdate.exe (PID: 3636)
- AVGBrowserUpdate.exe (PID: 3408)
Reads the computer name
- avg_secure_browser_setup.exe (PID: 2340)
- ajFED.exe (PID: 3388)
- AVGBrowserUpdate.exe (PID: 3076)
- AVGBrowserUpdate.exe (PID: 3304)
- AVGBrowserUpdate.exe (PID: 1796)
- AVGBrowserUpdate.exe (PID: 3408)
- AVGBrowserUpdate.exe (PID: 3636)
The process checks LSA protection
- avg_secure_browser_setup.exe (PID: 2340)
- ajFED.exe (PID: 3388)
- AVGBrowserUpdate.exe (PID: 3076)
- AVGBrowserUpdate.exe (PID: 3408)
- AVGBrowserUpdate.exe (PID: 3636)
- AVGBrowserUpdate.exe (PID: 1796)
Create files in a temporary directory
- avg_secure_browser_setup.exe (PID: 2340)
- ajFED.exe (PID: 3388)
- AVGBrowserUpdateSetup.exe (PID: 3036)
- AVGBrowserUpdate.exe (PID: 1796)
- chrome.exe (PID: 2996)
Process checks computer location settings
- avg_secure_browser_setup.exe (PID: 2340)
- ajFED.exe (PID: 3388)
Reads Environment values
- avg_secure_browser_setup.exe (PID: 2340)
- ajFED.exe (PID: 3388)
Reads the machine GUID from the registry
- ajFED.exe (PID: 3388)
- AVGBrowserUpdate.exe (PID: 3076)
- AVGBrowserUpdate.exe (PID: 3636)
- AVGBrowserUpdate.exe (PID: 1796)
- AVGBrowserUpdate.exe (PID: 3408)
Checks proxy server information
- ajFED.exe (PID: 3388)
Creates files or folders in the user directory
- AVGBrowserUpdate.exe (PID: 3076)
Application launched itself
- chrome.exe (PID: 2996)
Manual execution by a user
- chrome.exe (PID: 2996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| ProductVersion: | 8.9.0.6117 |
|---|---|
| ProductName: | إعداد AVG Secure Browser |
| OmahaVersion: | 1.8.1582.3 |
| LegalCopyright: | حقوق الطبع والنشر لعام 2022 لـ AVG Technologies |
| JsisCommit: | bc26fe057328f82c2184a80394770674a7aad8a8 |
| InternalName: | AVG Secure Browser |
| InstallerKeyword: | avg-securebrowser |
| InstallerEdition: | web |
| InstallerCommit: | e8ba9200ad22ea9e3eab4921fb59ea3846132883 |
| FileVersion: | 8.9.0.6117 |
| FileDescription: | إعداد AVG Secure Browser |
| BuildVersion: | 8.9.0.6117 |
| BuildTimestamp: | 1670430887 |
| BuildDate: | 19700120T080030 |
| CharacterSet: | Windows, Arabic |
| LanguageCode: | Arabic |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 8.9.0.6117 |
| FileVersionNumber: | 8.9.0.6117 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x350d |
| UninitializedDataSize: | 2048 |
| InitializedDataSize: | 141824 |
| CodeSize: | 26112 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2019:12:16 00:50:53+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Dec-2019 00:50:53 |
| Detected languages: |
|
| BuildDate: | 19700120T080030 |
| BuildTimestamp: | 1670430887 |
| BuildVersion: | 8.9.0.6117 |
| FileDescription: | Podešavanje programa AVG Secure Browser |
| FileVersion: | 8.9.0.6117 |
| InstallerCommit: | e8ba9200ad22ea9e3eab4921fb59ea3846132883 |
| InstallerEdition: | web |
| InstallerKeyword: | avg-securebrowser |
| InternalName: | AVG Secure Browser |
| JsisCommit: | bc26fe057328f82c2184a80394770674a7aad8a8 |
| LegalCopyright: | (c) 2022 AVG Technologies |
| OmahaVersion: | 1.8.1582.3 |
| ProductName: | Podešavanje programa AVG Secure Browser |
| ProductVersion: | 8.9.0.6117 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 16-Dec-2019 00:50:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000647B | 0x00006600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.42652 |
.rdata | 0x00008000 | 0x00001384 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.13635 |
.data | 0x0000A000 | 0x00020358 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.00585 |
.ndata | 0x0002B000 | 0x0005F000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0008A000 | 0x0001FE30 | 0x00020000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.73406 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29132 | 1020 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.91525 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 5.33705 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 5.11052 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 5.10581 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 3.83709 | 1640 | UNKNOWN | English - United States | RT_ICON |
7 | 4.74131 | 1384 | UNKNOWN | English - United States | RT_ICON |
8 | 6.00508 | 1128 | UNKNOWN | English - United States | RT_ICON |
9 | 4.30117 | 744 | UNKNOWN | English - United States | RT_ICON |
10 | 4.53771 | 296 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
58
Monitored processes
22
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,4023313611510043691,5709943873986516332,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2964 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,4023313611510043691,5709943873986516332,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2900 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,4023313611510043691,5709943873986516332,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1228 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,4023313611510043691,5709943873986516332,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2984 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1040,4023313611510043691,5709943873986516332,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3380 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1796 | "C:\Users\admin\AppData\Local\AVG\Browser\Update\AVGBrowserUpdate.exe" -Embedding | C:\Users\admin\AppData\Local\AVG\Browser\Update\AVGBrowserUpdate.exe | svchost.exe | ||||||||||||
User: admin Company: AVG Technologies Integrity Level: MEDIUM Description: AVG Browser Exit code: 0 Version: 1.8.1582.3 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,4023313611510043691,5709943873986516332,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2340 | "C:\Users\admin\Downloads\avg_secure_browser_setup.exe" | C:\Users\admin\Downloads\avg_secure_browser_setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: AVG Secure Browser Setup Exit code: 0 Version: 8.9.0.6117 Modules
| |||||||||||||||
| 2396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,4023313611510043691,5709943873986516332,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3440 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1040,4023313611510043691,5709943873986516332,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3124 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
45 030
Read events
41 828
Write events
3 180
Delete events
22
Modification events
| (PID) Process: | (3388) ajFED.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3388) ajFED.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3388) ajFED.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3388) ajFED.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003D010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3388) ajFED.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3388) ajFED.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3388) ajFED.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3388) ajFED.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3388) ajFED.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3304) AVGBrowserUpdate.exe | Key: | HKEY_CLASSES_ROOT\CLSID\{C9D22417-34EB-416B-BE82-31D5660097D6}\InprocServer32 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
346
Suspicious files
262
Text files
218
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2340 | avg_secure_browser_setup.exe | C:\Users\admin\AppData\Local\Temp\avg-securebrowser-web-tags | binary | |
MD5:F6C56A9C86DFDDCE90E8ACD7CE436B5B | SHA256:34BDA7D3707629594D773350CD52136B419B3533D0233620E637AE759901712B | |||
| 2340 | avg_secure_browser_setup.exe | C:\Users\admin\AppData\Local\Temp\nsc482.tmp\inetc.dll | executable | |
MD5:7FB1BBFF6382A4D6143C76A5453BEBB7 | SHA256:90B21F42D547E2F1849ABE573A1E87353C9FA534EEFD4576FB6D4ED6B7A449DC | |||
| 2340 | avg_secure_browser_setup.exe | C:\Users\admin\AppData\Local\Temp\nsc482.tmp\nsJSON.dll | executable | |
MD5:18662C1ACB667A9DB5FB9E90AA0F5DC8 | SHA256:608D4AEFD5C5184BC109CBD94A5D4C8883A4AE6CEDF81CFC3028D2570A849A66 | |||
| 2340 | avg_secure_browser_setup.exe | C:\Users\admin\AppData\Local\Temp\nsc482.tmp\ultimateSplash.dll | executable | |
MD5:339AF92CB0C6200309DA266D9B849A46 | SHA256:1ED3510A6FF8D488BF6CF7EEE9ECC5D419843DBF3B3A3BF384AED75C0AFEA7FC | |||
| 2340 | avg_secure_browser_setup.exe | C:\Users\admin\AppData\Local\Temp\nsc482.tmp\jsisdl.dll | executable | |
MD5:9CD0F6895D5160964F5DE813BC81F2A2 | SHA256:3791341A0F4A49AC54C06CC906A024F9A2F97D13CEDC0B0D74B11C7E98928D09 | |||
| 2340 | avg_secure_browser_setup.exe | C:\Users\admin\AppData\Local\Temp\nsc482.tmp\Midex.dll | executable | |
MD5:00FD199D6B8D08446F4862C31B191CA7 | SHA256:1B2A0DE815E288161F0A156B4D1F17F06D2F4840B71D9D1903AD1284192CDE24 | |||
| 2340 | avg_secure_browser_setup.exe | C:\Users\admin\AppData\Local\Temp\nsc482.tmp\thirdparty.dll | executable | |
MD5:080EEA7A54AEB7EA3D016645DEC05BD6 | SHA256:84CAB1C6DF2EDDCED4E60FC1E158B772F7B766D0FAED27E33BD5F0EA69903BF4 | |||
| 2340 | avg_secure_browser_setup.exe | C:\Users\admin\AppData\Local\Temp\ajFED.exe | executable | |
MD5:3D173D31AA79C82A369A3E4F36BDDE7E | SHA256:39ECFADE5B8331D3200F09A41263C4C8CBDC1DB4190D14DE4579EBA4D2EC4656 | |||
| 3388 | ajFED.exe | C:\Users\admin\AppData\Local\Temp\nsc11D0.tmp\FF.places.tmp | — | |
MD5:— | SHA256:— | |||
| 2340 | avg_secure_browser_setup.exe | C:\Users\admin\AppData\Local\Temp\nsc482.tmp\StdUtils.dll | executable | |
MD5:9A44BA9A6E36099D8058FED7FEB1CA5A | SHA256:445A8C41038974BF604CD826E192DA08431E8B0C72F6A8ECB6894F8C5A6C777D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
26
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3712 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
3388 | ajFED.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0ed25029d42cd405 | US | compressed | 4.70 Kb | whitelisted |
1796 | AVGBrowserUpdate.exe | GET | — | 23.48.23.58:80 | http://browser-update.avg.com/browser-avg/win/x86/109.0.19981.121/AVGBrowserInstaller.exe | US | — | — | whitelisted |
3388 | ajFED.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3388 | ajFED.exe | 172.67.5.41:443 | stats.avgbrowser.com | CLOUDFLARENET | US | whitelisted |
3388 | ajFED.exe | 104.22.65.125:443 | stats.avgbrowser.com | CLOUDFLARENET | — | whitelisted |
3388 | ajFED.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3388 | ajFED.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3408 | AVGBrowserUpdate.exe | 172.67.5.41:443 | stats.avgbrowser.com | CLOUDFLARENET | US | whitelisted |
1796 | AVGBrowserUpdate.exe | 172.67.5.41:443 | stats.avgbrowser.com | CLOUDFLARENET | US | whitelisted |
3712 | chrome.exe | 142.250.181.238:443 | clients2.google.com | GOOGLE | US | whitelisted |
3712 | chrome.exe | 142.250.186.100:443 | www.google.com | GOOGLE | US | whitelisted |
3712 | chrome.exe | 142.250.184.195:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
3712 | chrome.exe | 142.250.186.129:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
stats.avgbrowser.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
update.avgbrowser.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
clients2.googleusercontent.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1796 | AVGBrowserUpdate.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |