| File name: | tmpok8nalu9 |
| Full analysis: | https://app.any.run/tasks/7d0a2d68-c2be-4768-b8d5-f3d9d2a5c13f |
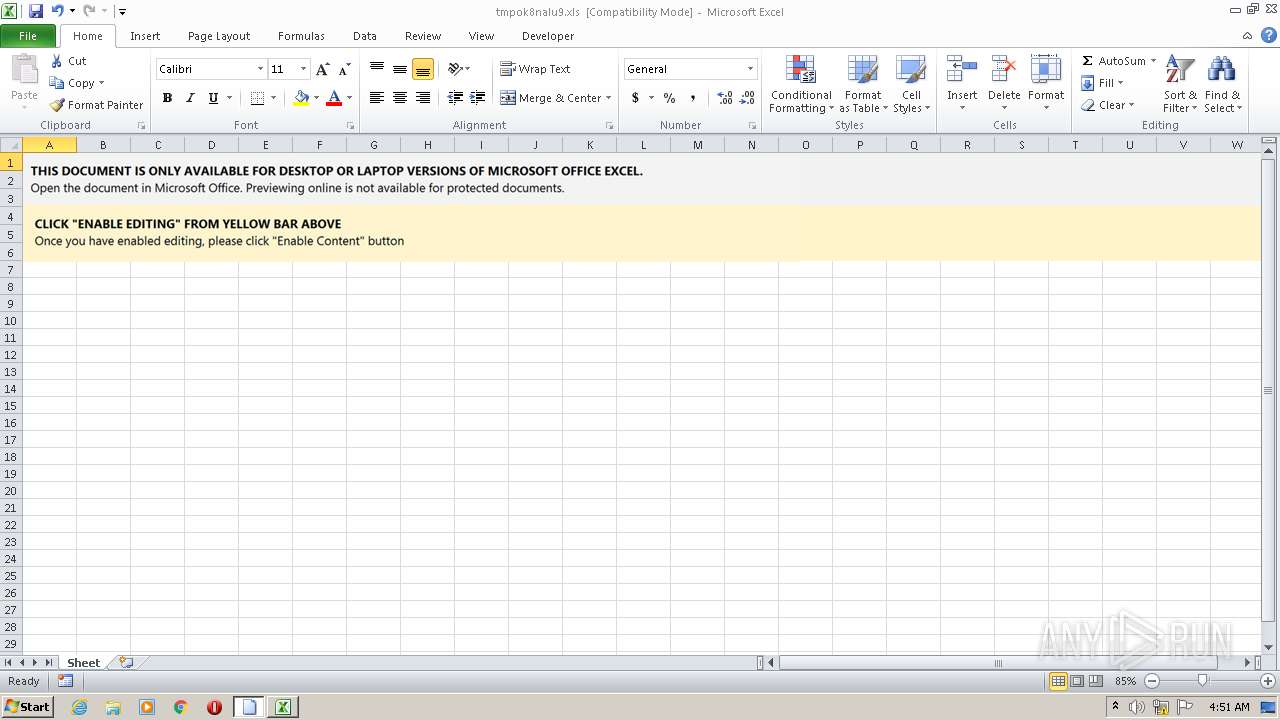
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | March 07, 2022, 04:50:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1251, Author: Admin, Last Saved By: Admin, Name of Creating Application: Microsoft Excel, Create Time/Date: Fri Jun 5 19:19:34 2015, Last Saved Time/Date: Wed Feb 2 19:04:39 2022, Security: 0 |
| MD5: | 907DD480FA4E5ED747B69D0CFDDA55D3 |
| SHA1: | 75DA2AF312AC8E8010A2081054E1649D66FAA3D6 |
| SHA256: | 251AD0658CF434FCAB41FED2C5E801683ABF289D9CC72B0F271D46610F7B932D |
| SSDEEP: | 3072:yWKpbdrHYrMue8q7QPX+5xtekEdi8/dg1JcdOpsHgGOqd4Z4:nKpbdrHYrMue8q7QPX+5xtFEdi8/dg14 |
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 1220)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- EXCEL.EXE (PID: 1220)
INFO
Checks supported languages
- EXCEL.EXE (PID: 1220)
- rundll32.exe (PID: 3592)
Reads the computer name
- EXCEL.EXE (PID: 1220)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 1220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (78.9) |
|---|
EXIF
FlashPix
| HeadingPairs: |
|
|---|---|
| TitleOfParts: |
|
| HyperlinksChanged: | No |
| SharedDoc: | No |
| LinksUpToDate: | No |
| ScaleCrop: | No |
| AppVersion: | 16 |
| Company: | - |
| CodePage: | Windows Cyrillic |
| Security: | None |
| ModifyDate: | 2022:02:02 19:04:39 |
| CreateDate: | 2015:06:05 18:19:34 |
| Software: | Microsoft Excel |
| LastModifiedBy: | Admin |
| Author: | Admin |
Total processes
36
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1220 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3592 | C:\Windows\SysWow64\rundll32.exe ..\iix.ocx,D"&"l"&"lR"&"egister"&"Serve"&"r | C:\Windows\SysWow64\rundll32.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 609
Read events
1 535
Write events
63
Delete events
11
Modification events
| (PID) Process: | (1220) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | z66 |
Value: 7A363600C4040000010000000000000000000000 | |||
| (PID) Process: | (1220) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1220) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1220) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1220) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1220) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1220) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1220) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1220) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1220) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1220 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVREE7A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1220 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\PA0rBwFszIpy[1].htm | html | |
MD5:DDE72AE232DC63298465861482D7BB93 | SHA256:0032588B8D93A807CF0F48A806CCF125677503A6FABE4105A6DC69E81ACE6091 | |||
| 1220 | EXCEL.EXE | C:\Users\admin\iix.ocx | html | |
MD5:DDE72AE232DC63298465861482D7BB93 | SHA256:0032588B8D93A807CF0F48A806CCF125677503A6FABE4105A6DC69E81ACE6091 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1220 | EXCEL.EXE | GET | 403 | 74.208.236.252:80 | http://cableequipmentmanagementreturns.com/wp-admin/JPivizxmiwo9A5Owys/ | US | html | 569 b | suspicious |
1220 | EXCEL.EXE | GET | 200 | 45.130.41.31:80 | http://novawedevent.com/tmp/PA0rBwFszIpy/ | unknown | html | 274 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1220 | EXCEL.EXE | 74.208.236.252:80 | cableequipmentmanagementreturns.com | 1&1 Internet SE | US | malicious |
1220 | EXCEL.EXE | 45.130.41.31:80 | novawedevent.com | — | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cableequipmentmanagementreturns.com |
| suspicious |
novawedevent.com |
| suspicious |