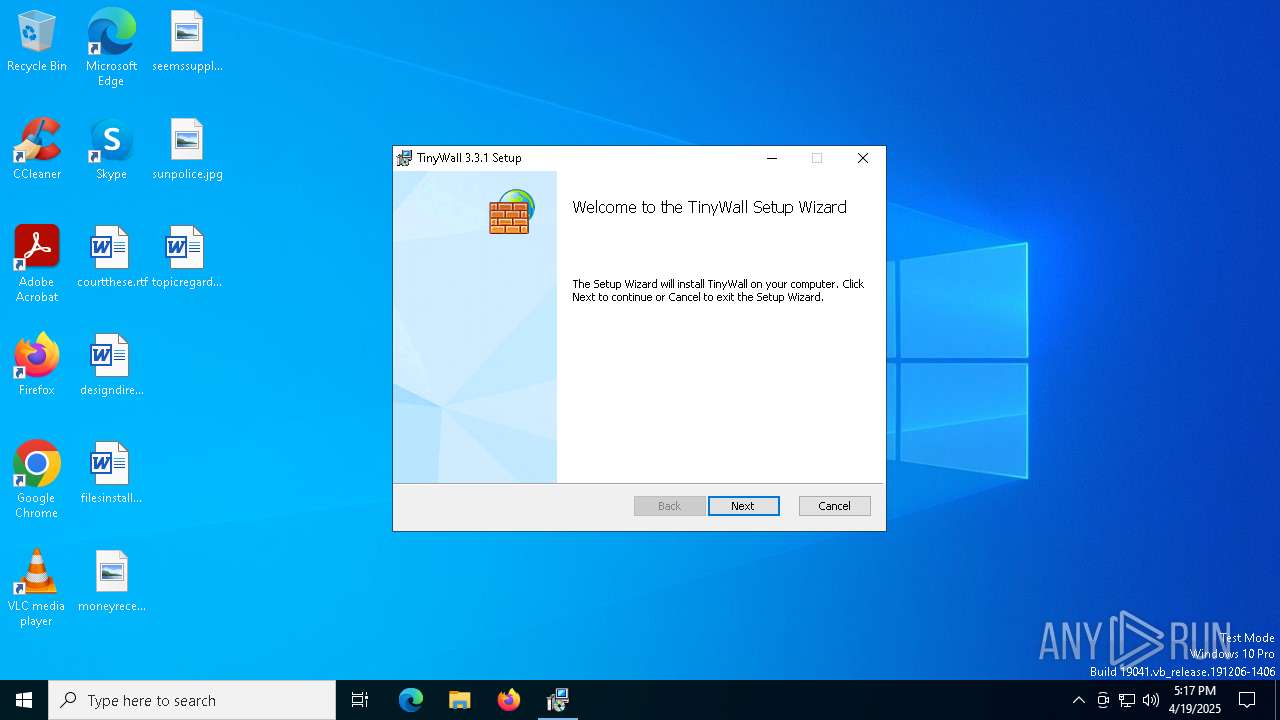
| File name: | TinyWall-v3-Installer (1).msi |
| Full analysis: | https://app.any.run/tasks/17b0a882-96ae-4528-8e48-db47b5bb6050 |
| Verdict: | Malicious activity |
| Analysis date: | April 19, 2025, 17:17:22 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Code page: 1250, Title: Installation Database, Subject: A non-intrusive firewall solution., Author: Kroly Pados, Keywords: Installer, Comments: This installer database contains the logic and data required to install TinyWall., Template: Intel;1033, Revision Number: {B29362A5-AC89-446C-9D15-99D364C13890}, Create Time/Date: Sun Mar 12 17:54:36 2023, Last Saved Time/Date: Sun Mar 12 17:54:36 2023, Number of Pages: 301, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.11.2.4516), Security: 2 |
| MD5: | 792984FCABFDA6BFA2DF1D6975F02DBE |
| SHA1: | 7B14C031514B80FC58E313E1FB9EC2AEE372D874 |
| SHA256: | 250B56EFF2CD5316C6CF8C8B92CB5F29FB3849089E69C8138BF5DD9BD0E9E001 |
| SSDEEP: | 98304:V46A+JoD0NQchKRRcqKjyLb1tGbmGRWpB0d7qsDOu33/naa5ybHnJGT:G |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7636)
Process drops legitimate windows executable
- msiexec.exe (PID: 7636)
Executes as Windows Service
- VSSVC.exe (PID: 8188)
- TinyWall.exe (PID: 7968)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7212)
- msiexec.exe (PID: 5936)
- TinyWall.exe (PID: 7468)
- TinyWall.exe (PID: 7844)
- TinyWall.exe (PID: 7440)
The process checks if it is being run in the virtual environment
- TinyWall.exe (PID: 7844)
- TinyWall.exe (PID: 7440)
Reads Mozilla Firefox installation path
- TinyWall.exe (PID: 7844)
Reads the date of Windows installation
- TinyWall.exe (PID: 7844)
Application launched itself
- TinyWall.exe (PID: 7844)
Reads Internet Explorer settings
- TinyWall.exe (PID: 7440)
INFO
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7528)
Checks proxy server information
- msiexec.exe (PID: 7528)
Checks supported languages
- msiexec.exe (PID: 7636)
- msiexec.exe (PID: 8096)
- msiexec.exe (PID: 5936)
- msiexec.exe (PID: 7212)
- TinyWall.exe (PID: 7468)
- TinyWall.exe (PID: 7968)
- TinyWall.exe (PID: 7844)
- TinyWall.exe (PID: 7440)
Reads the computer name
- msiexec.exe (PID: 7636)
- msiexec.exe (PID: 8096)
- msiexec.exe (PID: 5936)
- TinyWall.exe (PID: 7468)
- msiexec.exe (PID: 7212)
- TinyWall.exe (PID: 7968)
- TinyWall.exe (PID: 7844)
- TinyWall.exe (PID: 7440)
Manages system restore points
- SrTasks.exe (PID: 2236)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7528)
- msiexec.exe (PID: 7636)
Reads the software policy settings
- msiexec.exe (PID: 7636)
- TinyWall.exe (PID: 7844)
- msiexec.exe (PID: 7528)
Reads the machine GUID from the registry
- msiexec.exe (PID: 7636)
- TinyWall.exe (PID: 7468)
- TinyWall.exe (PID: 7968)
- TinyWall.exe (PID: 7844)
- TinyWall.exe (PID: 7440)
Creates a software uninstall entry
- msiexec.exe (PID: 7636)
Reads Environment values
- TinyWall.exe (PID: 7468)
- TinyWall.exe (PID: 7968)
- TinyWall.exe (PID: 7844)
- TinyWall.exe (PID: 7440)
Creates files in the program directory
- TinyWall.exe (PID: 7468)
- TinyWall.exe (PID: 7968)
Reads product name
- TinyWall.exe (PID: 7968)
- TinyWall.exe (PID: 7844)
Process checks computer location settings
- TinyWall.exe (PID: 7844)
An automatically generated document
- msiexec.exe (PID: 7528)
Creates files or folders in the user directory
- msiexec.exe (PID: 7528)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 2 (Central European) |
|---|---|
| Title: | Installation Database |
| Subject: | A non-intrusive firewall solution. |
| Author: | Károly Pados |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install TinyWall. |
| Template: | Intel;1033 |
| RevisionNumber: | {B29362A5-AC89-446C-9D15-99D364C13890} |
| CreateDate: | 2023:03:12 17:54:36 |
| ModifyDate: | 2023:03:12 17:54:36 |
| Pages: | 301 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.11.2.4516) |
| Security: | Read-only recommended |
Total processes
148
Monitored processes
14
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2236 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5936 | C:\Windows\syswow64\MsiExec.exe -Embedding AABB2D758641EB947034195691579D2F E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6564 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7212 | C:\Windows\syswow64\MsiExec.exe -Embedding 3F0556C5DD6C61484D15C90A1E57AE77 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7440 | "C:\Program Files (x86)\TinyWall\TinyWall.exe" | C:\Program Files (x86)\TinyWall\TinyWall.exe | TinyWall.exe | ||||||||||||
User: admin Company: Károly Pados Integrity Level: HIGH Description: TinyWall Version: 3.3.1.0 Modules
| |||||||||||||||
| 7468 | "C:\Program Files (x86)\TinyWall\TinyWall.exe" /install | C:\Program Files (x86)\TinyWall\TinyWall.exe | — | msiexec.exe | |||||||||||
User: admin Company: Károly Pados Integrity Level: MEDIUM Description: TinyWall Exit code: 0 Version: 3.3.1.0 Modules
| |||||||||||||||
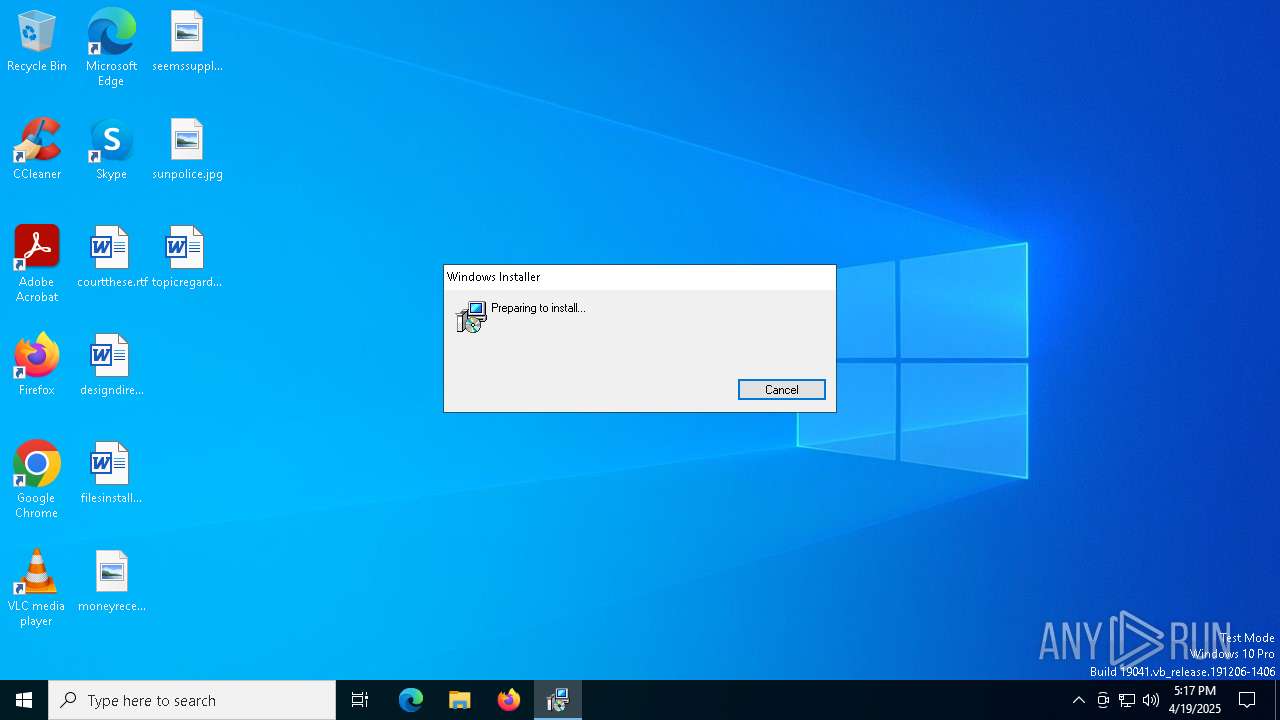
| 7528 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\TinyWall-v3-Installer (1).msi" | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7636 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7724 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7756 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
19 468
Read events
19 107
Write events
348
Delete events
13
Modification events
| (PID) Process: | (7636) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000AB66B5F24EB1DB01D41D0000E81F0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7636) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000AB66B5F24EB1DB01D41D0000E81F0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7636) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000B16231F34EB1DB01D41D0000E81F0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7636) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000B16231F34EB1DB01D41D0000E81F0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7636) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000BBF33AF34EB1DB01D41D0000E81F0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7636) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000B52B36F34EB1DB01D41D0000E81F0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8188) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000009973C0F34EB1DB01FC1F000060030000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8188) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000009973C0F34EB1DB01FC1F0000C01C0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7636) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (7636) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 480000000000000047CEAFF34EB1DB01D41D0000E81F0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
31
Suspicious files
48
Text files
16
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7636 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 7528 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\D682FDDA10064185EC8111DC39DBA8EC | binary | |
MD5:D830CB885D55400E524944D287582DA1 | SHA256:3FC40319370C9C84C81E7966645A71E535F76A844D07A5851D253B026723FBE5 | |||
| 7528 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\54C62B182F5BF07FA8427C07B0A3AAF8_4DBBCB40FA282C06F1543D887F4F4DCC | binary | |
MD5:4C3C17428FA6E6C332AE8CDAE96E946B | SHA256:C2AF2E7C888629FD76A1CDAA1C8E6CC7804109B3D4E119CD2FB15BE679D82BA5 | |||
| 7636 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:D72D52568819E3D385F6D0BE75081A31 | SHA256:80F010C257116F55C94250815CAAA7EC95058A6277F7C570C1C21F93436E97E1 | |||
| 7528 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\D682FDDA10064185EC8111DC39DBA8EC | binary | |
MD5:D4B37E5146529EED34A05A41376072A5 | SHA256:7D6BABED4576D59AC17A40A4AE526323B091DB1B834FF5A705B4AC0846506434 | |||
| 7528 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSID284.tmp | executable | |
MD5:4FDD16752561CF585FED1506914D73E0 | SHA256:AECD2D2FE766F6D439ACC2BBF1346930ECC535012CF5AD7B3273D2875237B7E7 | |||
| 7636 | msiexec.exe | C:\Windows\Installer\MSI20F2.tmp | binary | |
MD5:288B5E2C537E7AAC7E0D0CA1DA44E1F6 | SHA256:A250C1A85F3EAABDC642E14EE8691E380425FE0F7FDB2ED288BF78B6591B33A1 | |||
| 7636 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{8ac11153-b8f2-4c1f-a302-a4b6d5cb4ca0}_OnDiskSnapshotProp | binary | |
MD5:D72D52568819E3D385F6D0BE75081A31 | SHA256:80F010C257116F55C94250815CAAA7EC95058A6277F7C570C1C21F93436E97E1 | |||
| 7636 | msiexec.exe | C:\Windows\Installer\MSI2122.tmp | executable | |
MD5:A3AE5D86ECF38DB9427359EA37A5F646 | SHA256:C8D190D5BE1EFD2D52F72A72AE9DFA3940AB3FACEB626405959349654FE18B74 | |||
| 7636 | msiexec.exe | C:\Windows\Installer\inprogressinstallinfo.ipi | binary | |
MD5:8A58E8C85270FC80F156C6ACFFA33087 | SHA256:ECBBB0F8D7108A6276A50EB7975649889386B64CF56CA91F24EA5E424EF26F1E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
28
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7528 | msiexec.exe | GET | 200 | 18.173.205.113:80 | http://ocsps.ssl.com/MEkwRzBFMEMwQTAJBgUrDgMCGgUABBQMDtATfnJO6JAXDQoHl8pAaJdhTQQU3QQJB6L1en1SUxKSle44gCUNplkCCGQzUdPHOJ8I | unknown | — | — | whitelisted |
7528 | msiexec.exe | GET | 200 | 18.244.18.60:80 | http://crls.ssl.com/SSLcom-SubCA-CodeSigning-RSA-4096-R1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7188 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7188 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.25:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7528 | msiexec.exe | 18.173.205.113:80 | ocsps.ssl.com | — | US | whitelisted |
7528 | msiexec.exe | 18.244.18.60:80 | crls.ssl.com | — | US | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.1:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsps.ssl.com |
| whitelisted |
crls.ssl.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |