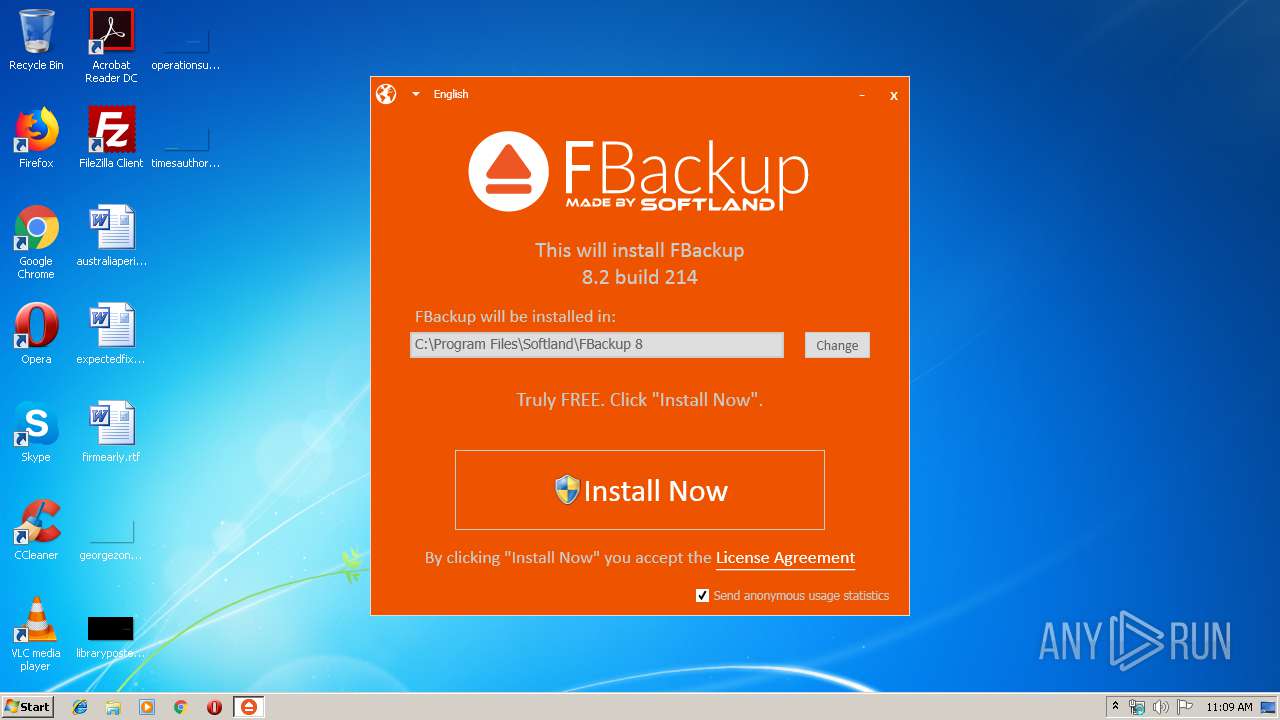
| download: | fbsetup.exe |
| Full analysis: | https://app.any.run/tasks/8b81f37f-cb78-4591-b9b6-5d3d40dc5263 |
| Verdict: | Malicious activity |
| Analysis date: | September 23, 2019, 10:09:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2CB4D594F30E3ACA53C67ABB8FAC3E05 |
| SHA1: | 650DA8F27146A04FDD5E6785F533C148B8DFE0F1 |
| SHA256: | 24FDB147D2E2CC21FC8138B8D1219F4029EF6D3B61739BE3EDBA50A3C0EBC0C8 |
| SSDEEP: | 24576:TgwYgb25FJsqIARMhvltmdwgvyqlzYA06L:igKu8RMhvnmQ76 |
MALICIOUS
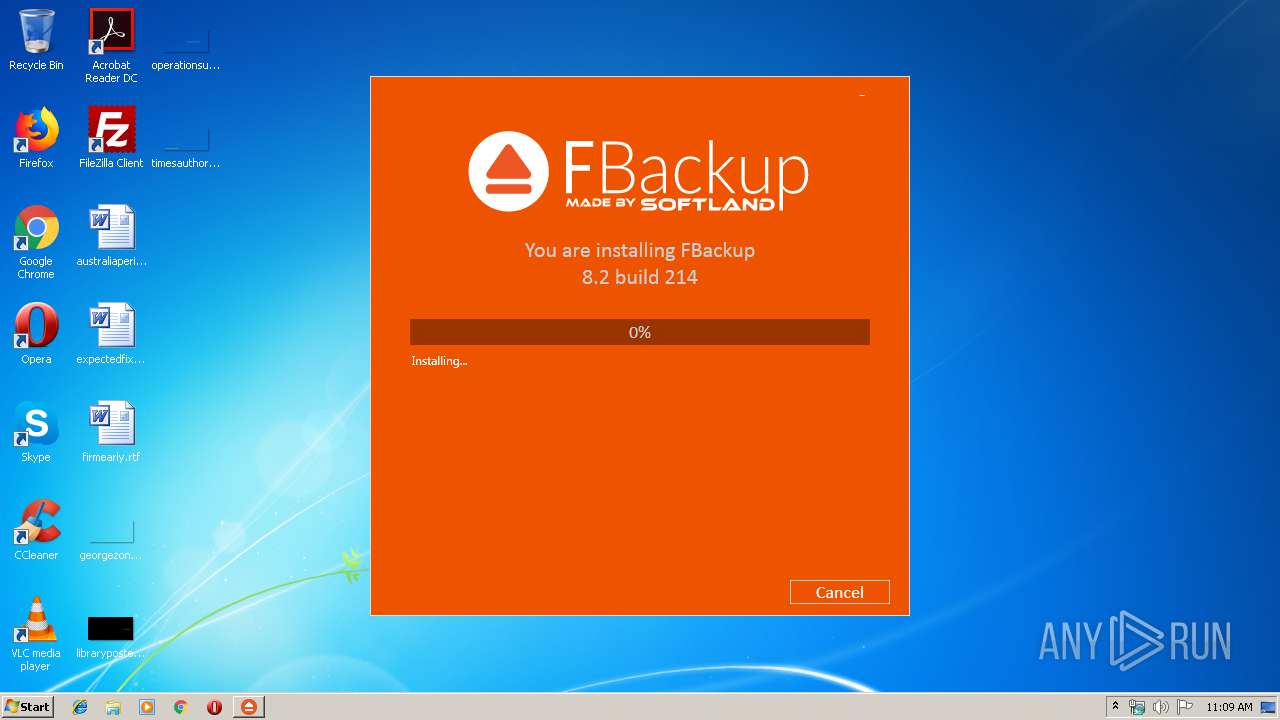
Loads dropped or rewritten executable
- fbsetup.exe (PID: 4048)
Changes the autorun value in the registry
- backupBootstrapper.exe (PID: 3132)
SUSPICIOUS
Executable content was dropped or overwritten
- fbsetup.exe (PID: 4048)
- fbsetup.exe (PID: 3040)
- backupBootstrapper.exe (PID: 3132)
Starts itself from another location
- fbsetup.exe (PID: 4048)
- fbsetup.exe (PID: 3040)
Executed as Windows Service
- vssvc.exe (PID: 2228)
Reads Environment values
- fbsetup.exe (PID: 4048)
Searches for installed software
- backupBootstrapper.exe (PID: 3132)
Executed via COM
- DrvInst.exe (PID: 3176)
Creates files in the program directory
- backupBootstrapper.exe (PID: 3132)
Creates a software uninstall entry
- backupBootstrapper.exe (PID: 3132)
Reads Internet Cache Settings
- fbsetup.exe (PID: 4048)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 2228)
Reads settings of System Certificates
- fbsetup.exe (PID: 4048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:05:01 16:33:52+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.1 |
| CodeSize: | 302080 |
| InitializedDataSize: | 772608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e1fd |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.2.214.0 |
| ProductVersionNumber: | 8.2.214.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Softland |
| FileDescription: | FBackup 8.2 |
| FileVersion: | 8.2.214.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Softland. All rights reserved. |
| OriginalFileName: | backupBootstrapper.exe |
| ProductName: | FBackup 8.2 |
| ProductVersion: | 8.2.214.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-May-2017 14:33:52 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Softland |
| FileDescription: | FBackup 8.2 |
| FileVersion: | 8.2.214.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Softland. All rights reserved. |
| OriginalFilename: | backupBootstrapper.exe |
| ProductName: | FBackup 8.2 |
| ProductVersion: | 8.2.214.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 01-May-2017 14:33:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00049A67 | 0x00049C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56282 |
.rdata | 0x0004B000 | 0x0001EC60 | 0x0001EE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.10841 |
.data | 0x0006A000 | 0x00001730 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.15458 |
.wixburn8 | 0x0006C000 | 0x00000038 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.512776 |
.tls | 0x0006D000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0006E000 | 0x00098F60 | 0x00099000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.22133 |
.reloc | 0x00107000 | 0x00003DEC | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.79026 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30829 | 1234 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.3644 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.40259 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.67974 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 2.63901 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
Cabinet.dll (delay-loaded) |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
41
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2228 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3040 | "C:\Users\admin\AppData\Local\Temp\fbsetup.exe" | C:\Users\admin\AppData\Local\Temp\fbsetup.exe | explorer.exe | ||||||||||||
User: admin Company: Softland Integrity Level: MEDIUM Description: FBackup 8.2 Exit code: 0 Version: 8.2.214.0 Modules
| |||||||||||||||
| 3132 | "C:\Users\admin\AppData\Local\Temp\{CD59C0FB-86A8-45F0-97F3-9907475AE97F}\.be\backupBootstrapper.exe" -q -burn.elevated BurnPipe.{77BAB62A-E7D4-458B-93D8-3CF337517F69} {259E29A2-1E3B-4C7F-84F8-64E5BE3C2BB5} 4048 | C:\Users\admin\AppData\Local\Temp\{CD59C0FB-86A8-45F0-97F3-9907475AE97F}\.be\backupBootstrapper.exe | fbsetup.exe | ||||||||||||
User: admin Company: Softland Integrity Level: HIGH Description: FBackup 8.2 Exit code: 0 Version: 8.2.214.0 Modules
| |||||||||||||||
| 3176 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot22" "" "" "695c3f483" "00000000" "00000390" "000005BC" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4048 | "C:\Users\admin\AppData\Local\Temp\{3425624E-A723-4A54-876F-3A87A920EAA2}\.cr\fbsetup.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\fbsetup.exe" -burn.filehandle.attached=148 -burn.filehandle.self=156 | C:\Users\admin\AppData\Local\Temp\{3425624E-A723-4A54-876F-3A87A920EAA2}\.cr\fbsetup.exe | fbsetup.exe | ||||||||||||
User: admin Company: Softland Integrity Level: MEDIUM Description: FBackup 8.2 Exit code: 0 Version: 8.2.214.0 Modules
| |||||||||||||||
Total events
737
Read events
529
Write events
208
Delete events
0
Modification events
| (PID) Process: | (4048) fbsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\fbsetup_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4048) fbsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\fbsetup_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4048) fbsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\fbsetup_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (4048) fbsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\fbsetup_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (4048) fbsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\fbsetup_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (4048) fbsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\fbsetup_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (4048) fbsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\fbsetup_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4048) fbsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\fbsetup_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4048) fbsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\fbsetup_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (4048) fbsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\fbsetup_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
7
Suspicious files
5
Text files
111
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3040 | fbsetup.exe | C:\Users\admin\AppData\Local\Temp\{3425624E-A723-4A54-876F-3A87A920EAA2}\.cr\fbsetup.exe | executable | |
MD5:— | SHA256:— | |||
| 4048 | fbsetup.exe | C:\Users\admin\AppData\Local\Temp\{CD59C0FB-86A8-45F0-97F3-9907475AE97F}\.ba\1038\mbapreq.wxl | xml | |
MD5:17FB605A2F02DA203DF06F714D1CC6DE | SHA256:55CF62D54EFB79801A9D94B24B3C9BA221C2465417A068950D40A67C52BA66EF | |||
| 4048 | fbsetup.exe | C:\Users\admin\AppData\Local\Temp\{CD59C0FB-86A8-45F0-97F3-9907475AE97F}\.ba\BootstrapperCore.dll | executable | |
MD5:1197872FA5DBF0A9D8C742558812DDE8 | SHA256:C1232F304EC8B3CE1626569AC28C6D1EEEA2EB891FC52D39E56F0D6102AC3D7E | |||
| 4048 | fbsetup.exe | C:\Users\admin\AppData\Local\Temp\{CD59C0FB-86A8-45F0-97F3-9907475AE97F}\.ba\1031\mbapreq.wxl | xml | |
MD5:C8E7E0B4E63B3076047B7F49C76D56E1 | SHA256:631D46CB048FB6CF0B9A1362F8E5A1854C46E9525A0260C7841A04B2316C8295 | |||
| 4048 | fbsetup.exe | C:\Users\admin\AppData\Local\Temp\{CD59C0FB-86A8-45F0-97F3-9907475AE97F}\.ba\1030\mbapreq.wxl | xml | |
MD5:7C6E4CE87870B3B5E71D3EF4555500F8 | SHA256:CAC263E0E90A4087446A290055257B1C39F17E11F065598CB2286DF4332C7696 | |||
| 4048 | fbsetup.exe | C:\Users\admin\AppData\Local\Temp\{CD59C0FB-86A8-45F0-97F3-9907475AE97F}\.ba\1036\mbapreq.wxl | xml | |
MD5:AA32A059AADD42431F7837CB1BE7257F | SHA256:88E7DDACD6B714D94D5322876BD50051479B7A0C686DC2E9EB06B3B7A0BC06C9 | |||
| 4048 | fbsetup.exe | C:\Users\admin\AppData\Local\Temp\{CD59C0FB-86A8-45F0-97F3-9907475AE97F}\.ba\1032\mbapreq.wxl | xml | |
MD5:074D5921AF07E6126049CB45814246ED | SHA256:B8E90E20EDF110AAAAEA54FBC8533872831777BE5589E380CFDD17E1F93147B5 | |||
| 4048 | fbsetup.exe | C:\Users\admin\AppData\Local\Temp\{CD59C0FB-86A8-45F0-97F3-9907475AE97F}\.ba\1060\mbapreq.wxl | xml | |
MD5:5836F0C655BDD97093F68AAF69AB2BAB | SHA256:C015247D022BDC108B4FFCAE89CB55D1E313034D7E6EED18744C1BB55F108F8C | |||
| 4048 | fbsetup.exe | C:\Users\admin\AppData\Local\Temp\{CD59C0FB-86A8-45F0-97F3-9907475AE97F}\.ba\1045\mbapreq.wxl | xml | |
MD5:96ACAAA5AEF7798E9048BAFF4C3FA8D3 | SHA256:F4AA983E39FB29C95E3306082F034B3A43E1D26489C997B8E6697B6A3B2F9F3C | |||
| 4048 | fbsetup.exe | C:\Users\admin\AppData\Local\Temp\{CD59C0FB-86A8-45F0-97F3-9907475AE97F}\.ba\1046\mbapreq.wxl | xml | |
MD5:BD39ADB6B872163FD2D570028E9F3213 | SHA256:ECB5C22E6C2423CAF07AEBE69F4FAF22450164EEE9587B64EF45A2D7F658CA15 | |||
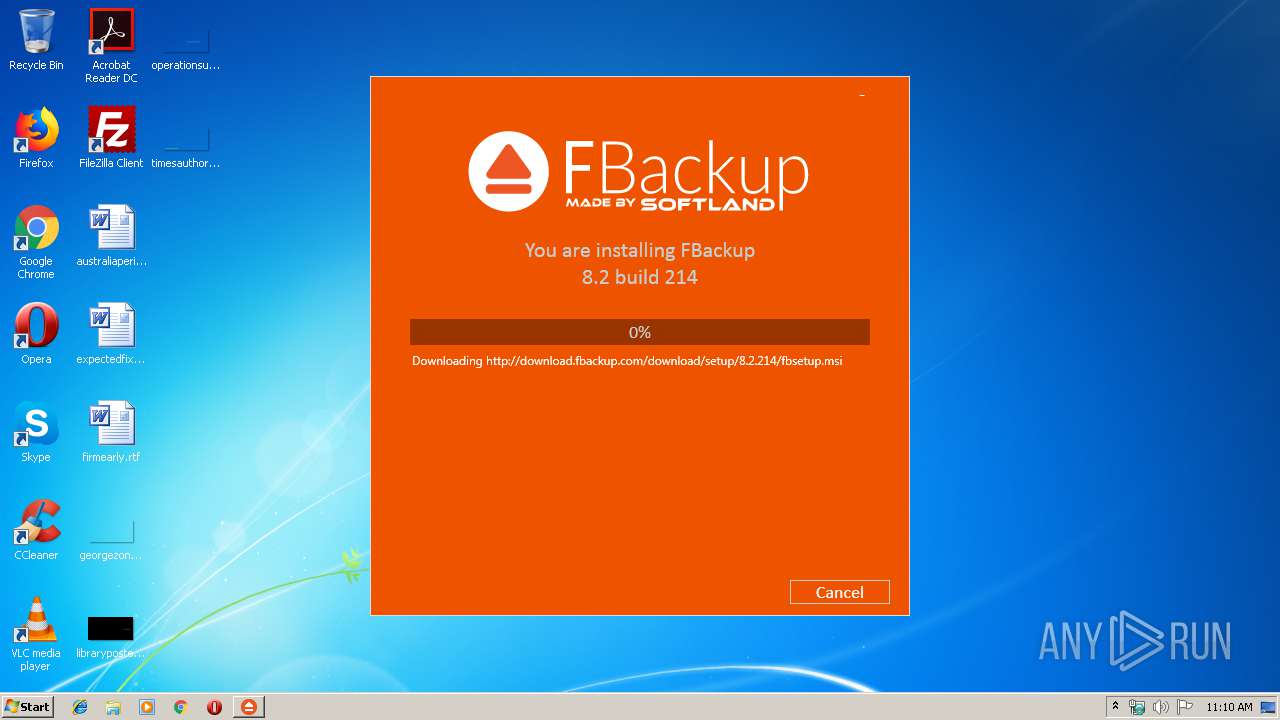
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4048 | fbsetup.exe | HEAD | — | 151.139.239.32:80 | http://download.fbackup.com/download/setup/8.2.214/fbsetup.msi | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4048 | fbsetup.exe | 206.221.191.155:443 | secure.backup4all.com | Choopa, LLC | US | unknown |
4048 | fbsetup.exe | 151.139.239.32:80 | download.fbackup.com | netDNA | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
secure.backup4all.com |
| unknown |
download.fbackup.com |
| malicious |