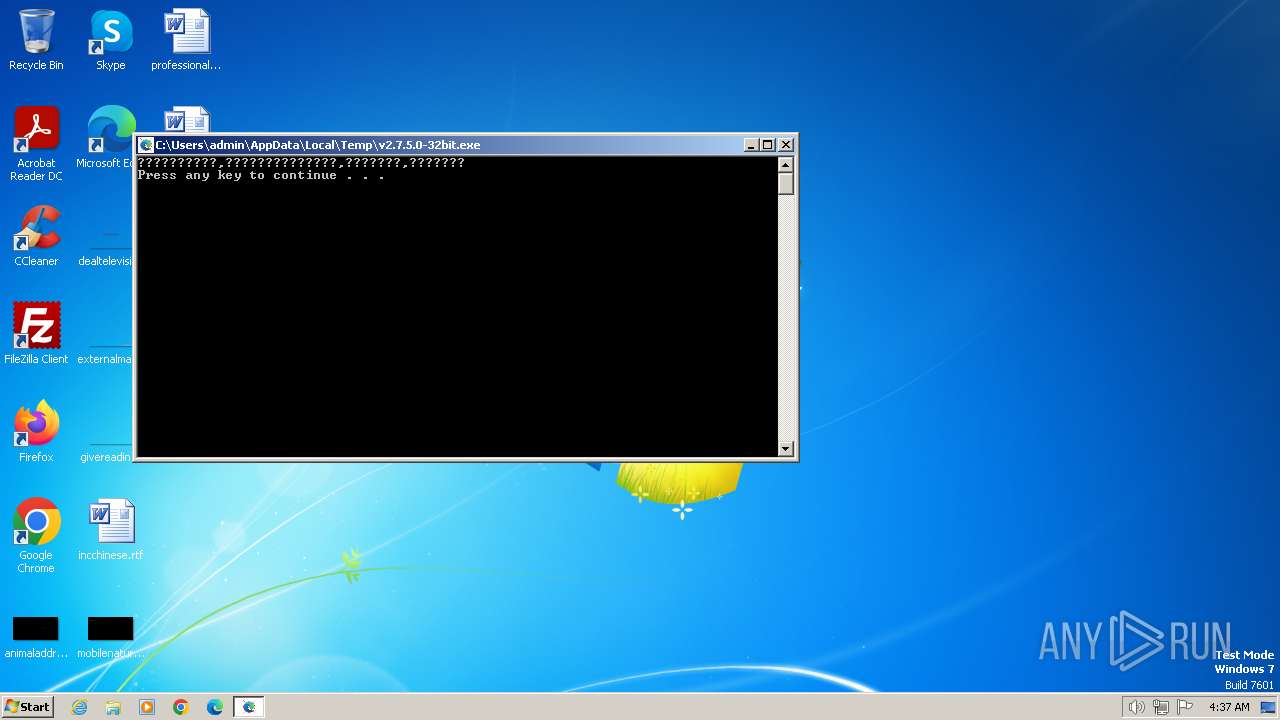
| File name: | v2.7.5.0-32bit.exe |
| Full analysis: | https://app.any.run/tasks/5fe0488d-caea-42f1-9053-d50ac1d586b7 |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2024, 03:37:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 56EBDCE1E8C10DADEE32F9988A1D4C23 |
| SHA1: | 8C3988AFEB2FDF08213F900E75466B85747C7BAC |
| SHA256: | 24F823D6CC0109878A28FF1245331FA0E871D4EABF08EFD18DDF54E51F598655 |
| SSDEEP: | 6144:2u7ARtymmAHnEFB0kmxATEZvpDKIZBrZ7hQbjVVHM:2u7hmZH3kmeKh+IZBrZ7huR2 |
MALICIOUS
Drops the executable file immediately after the start
- v2.7.5.0-32bit.exe (PID: 4044)
- setup.exe (PID: 712)
Actions looks like stealing of personal data
- setup.exe (PID: 712)
SUSPICIOUS
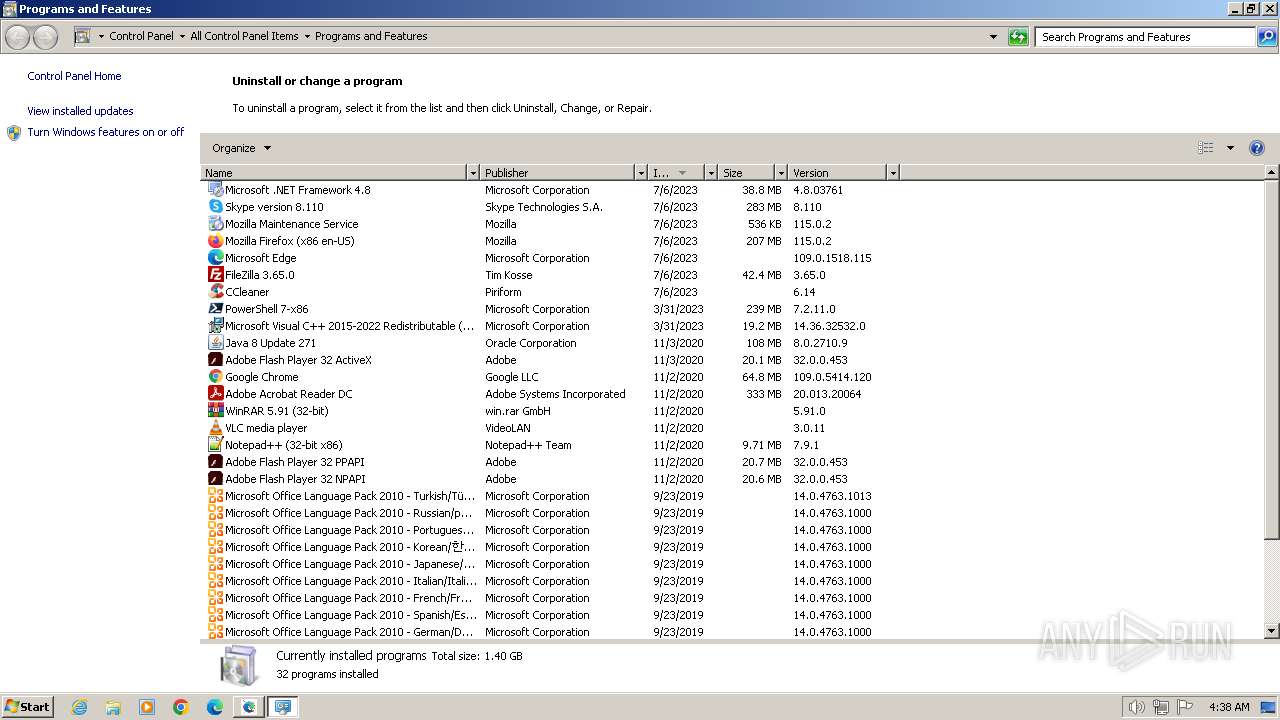
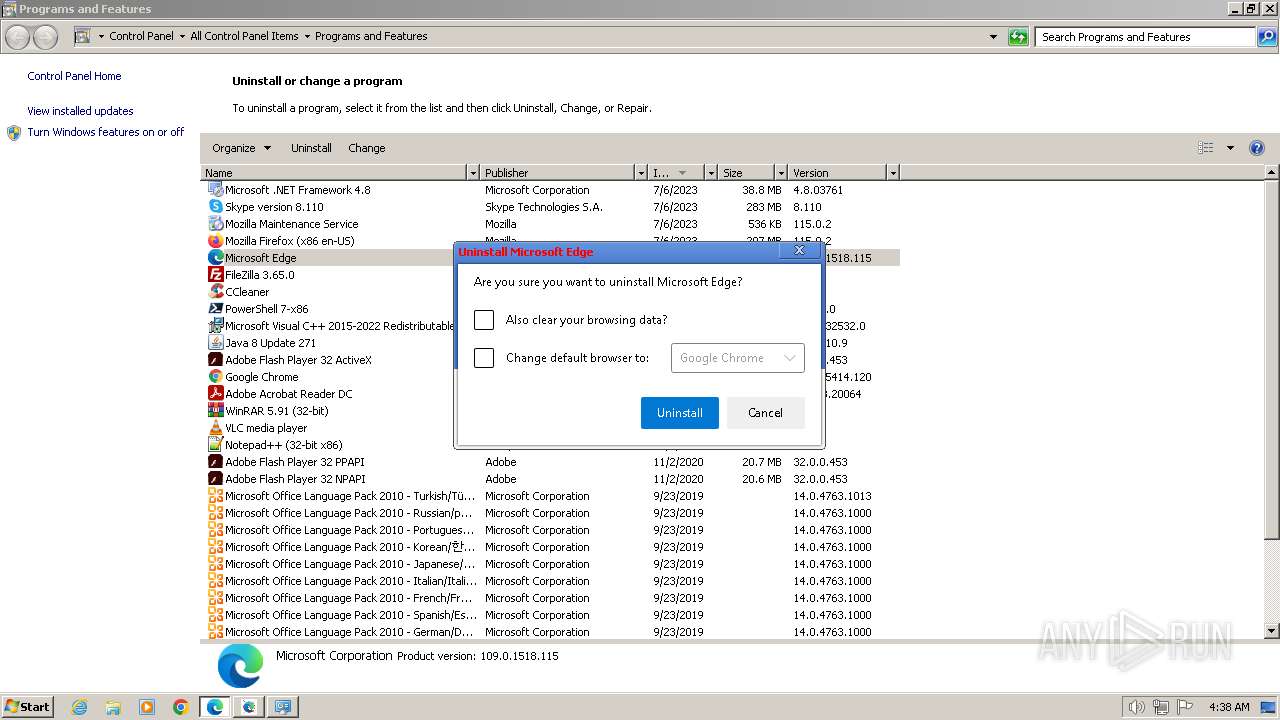
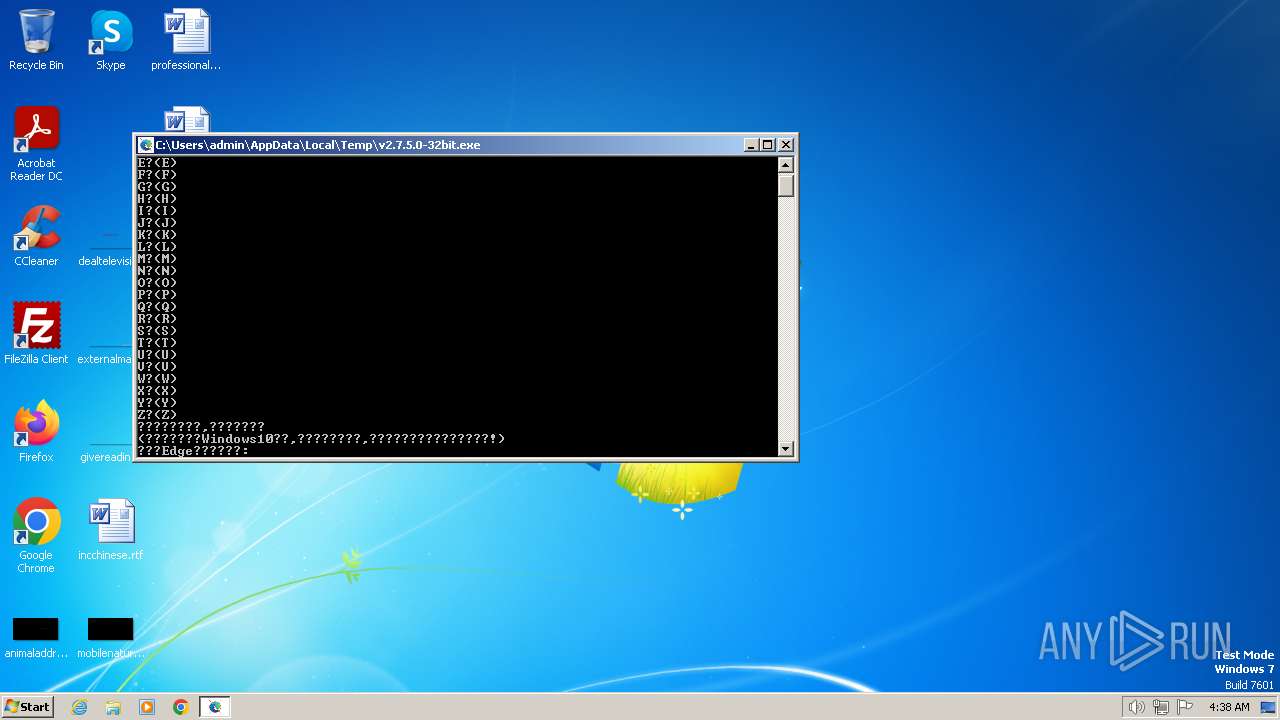
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 2896)
Starts CMD.EXE for commands execution
- v2.7.5.0-32bit.exe (PID: 4044)
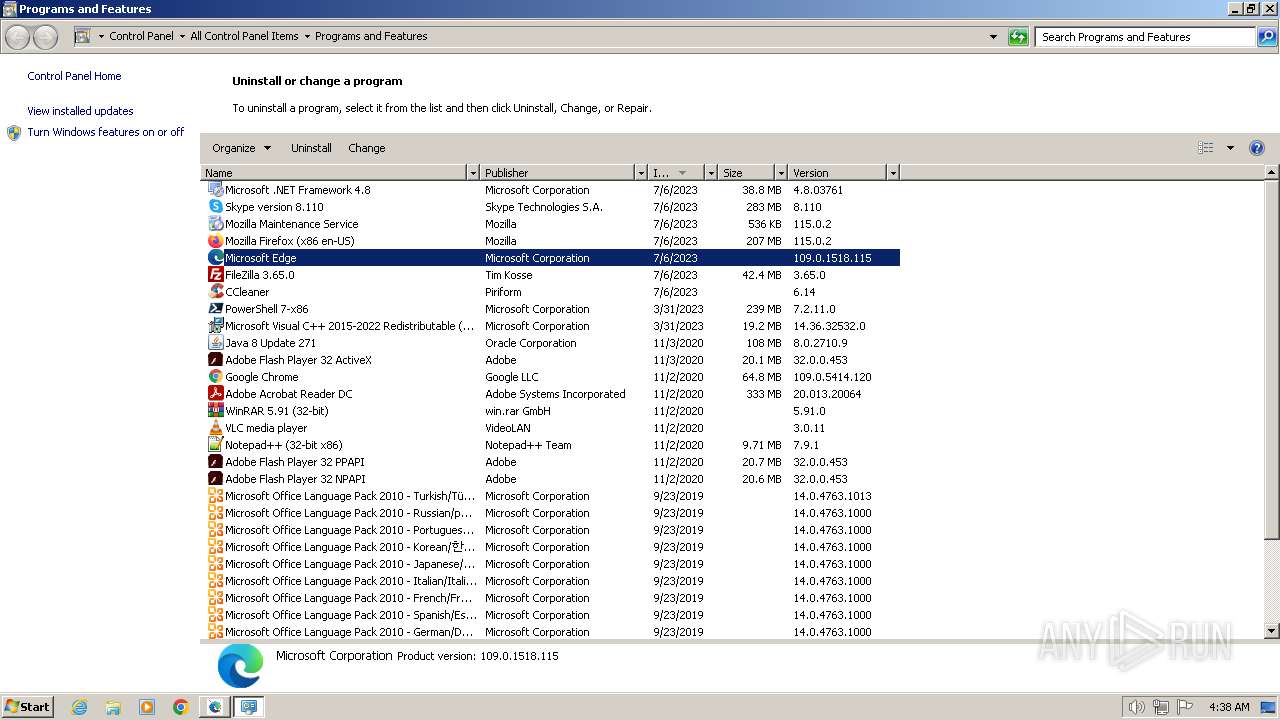
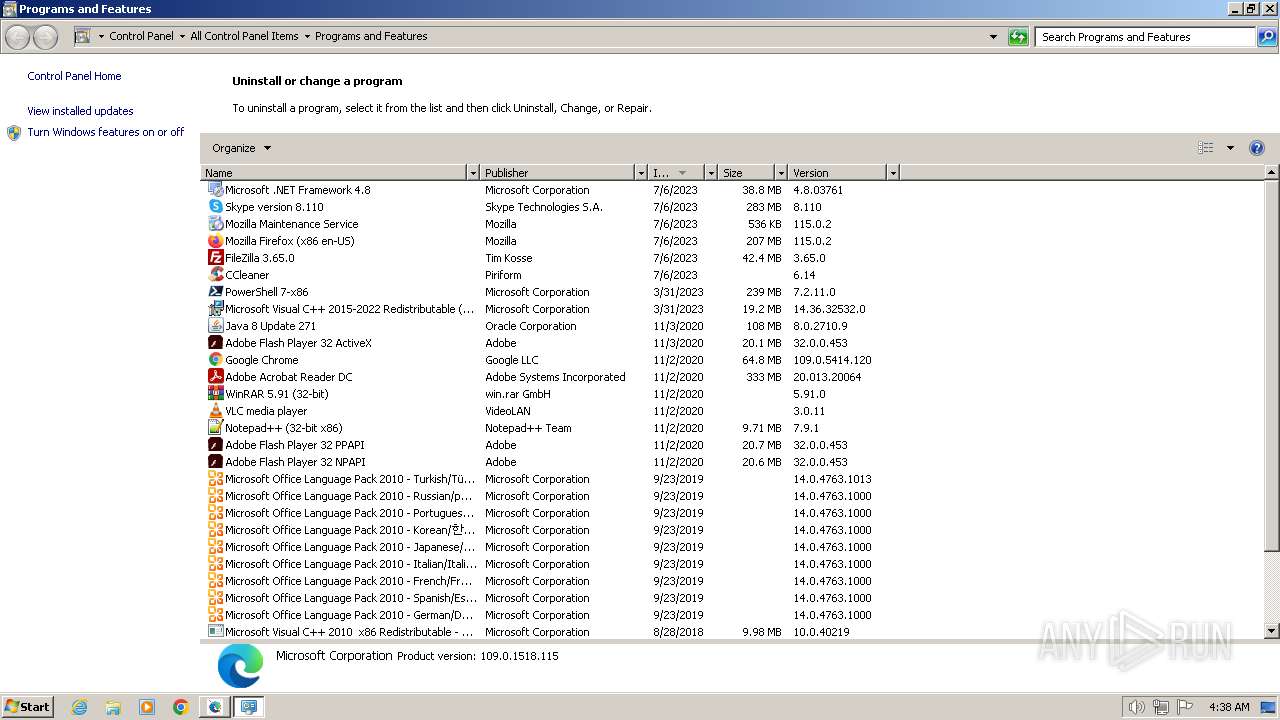
Creates a software uninstall entry
- reg.exe (PID: 2000)
- reg.exe (PID: 3308)
- reg.exe (PID: 2596)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2896)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2896)
Executing commands from a ".bat" file
- v2.7.5.0-32bit.exe (PID: 4044)
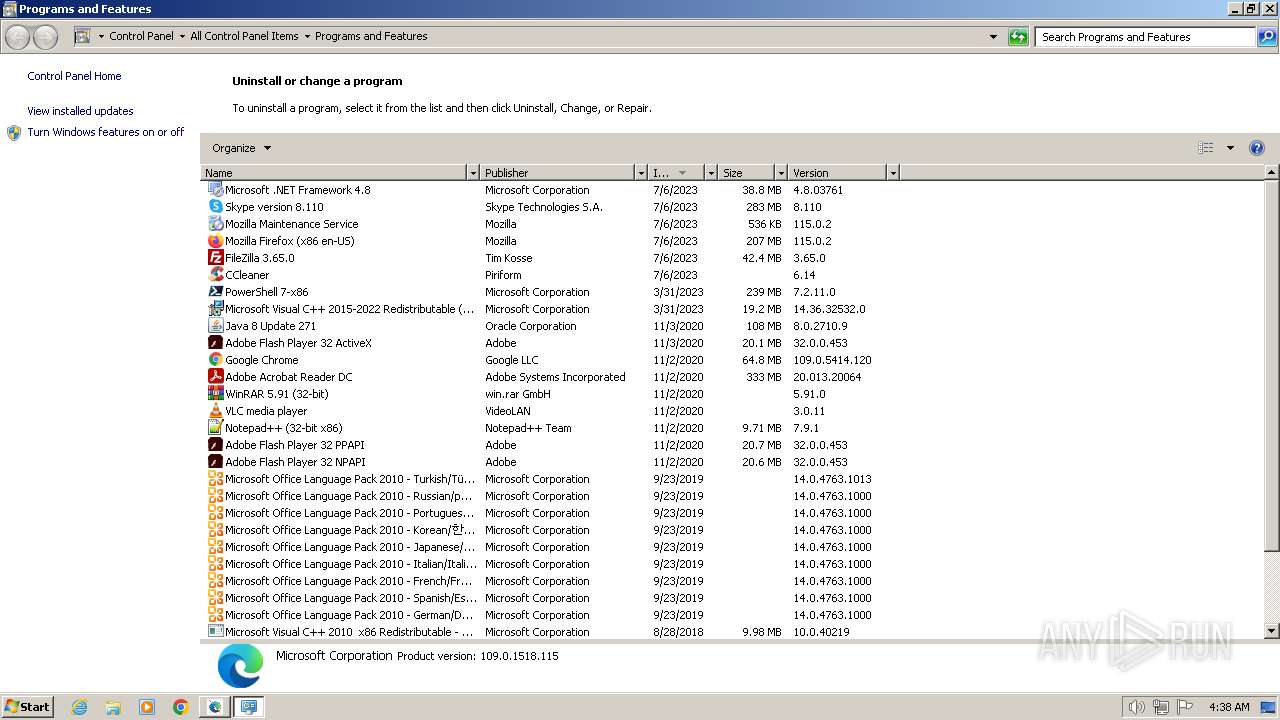
Searches for installed software
- reg.exe (PID: 2596)
- reg.exe (PID: 3308)
- dllhost.exe (PID: 2248)
- reg.exe (PID: 2000)
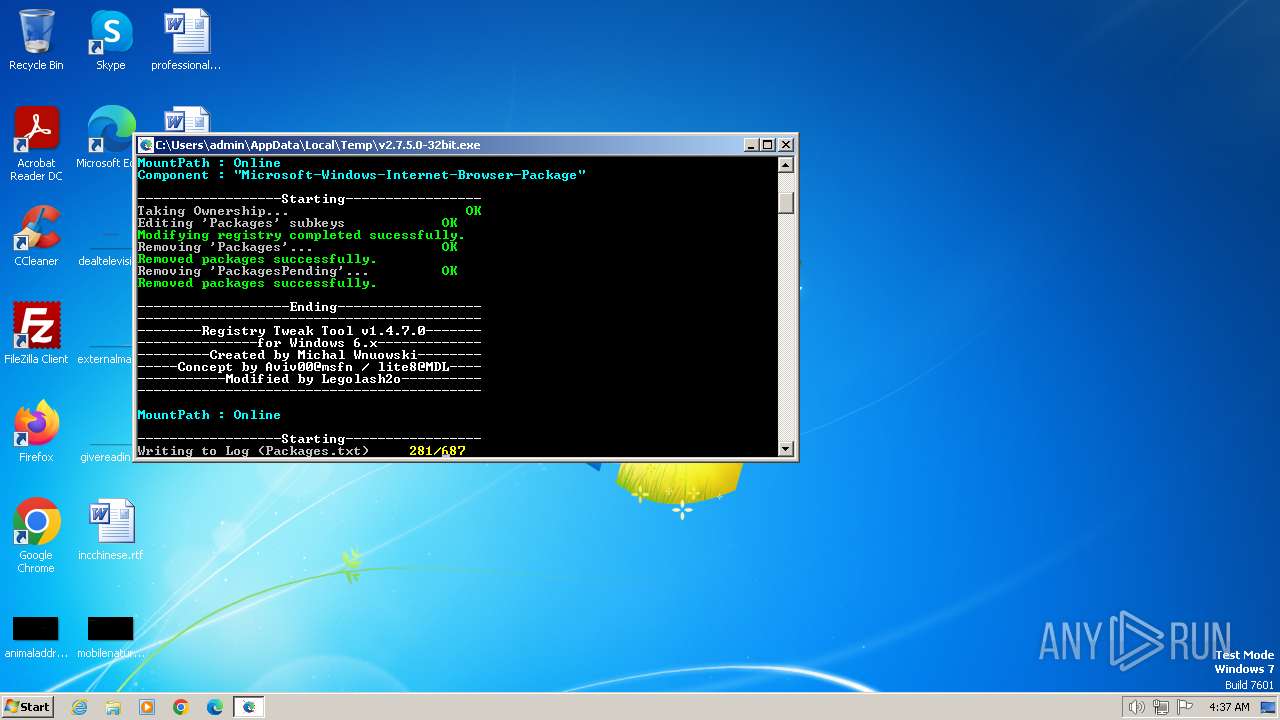
The executable file from the user directory is run by the CMD process
- install_wim_tweak.exe (PID: 3072)
- install_wim_tweak.exe (PID: 3324)
- install_wim_tweak.exe (PID: 1644)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 2896)
Process drops legitimate windows executable
- setup.exe (PID: 712)
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 2896)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 2896)
INFO
Create files in a temporary directory
- v2.7.5.0-32bit.exe (PID: 4044)
- install_wim_tweak.exe (PID: 1644)
- install_wim_tweak.exe (PID: 3324)
- setup.exe (PID: 712)
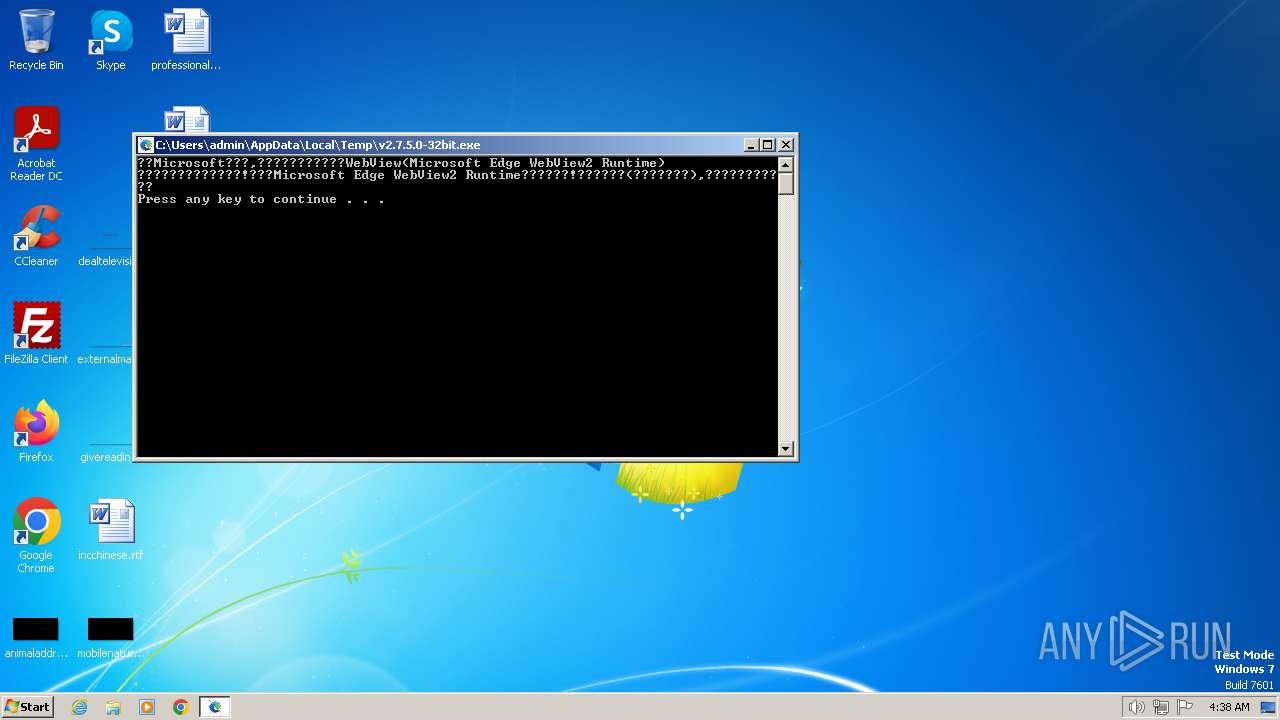
Checks supported languages
- v2.7.5.0-32bit.exe (PID: 4044)
- install_wim_tweak.exe (PID: 1644)
- install_wim_tweak.exe (PID: 3072)
- install_wim_tweak.exe (PID: 3324)
- setup.exe (PID: 712)
Reads the computer name
- install_wim_tweak.exe (PID: 1644)
- install_wim_tweak.exe (PID: 3072)
- install_wim_tweak.exe (PID: 3324)
- setup.exe (PID: 712)
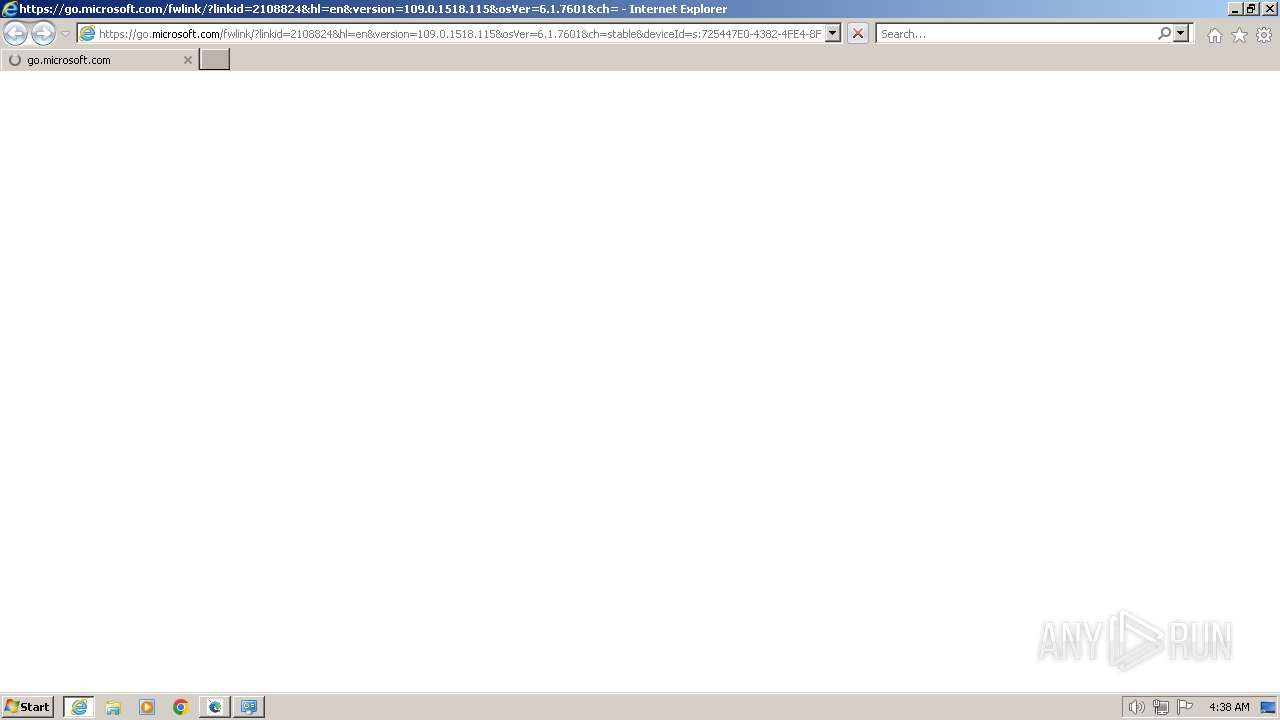
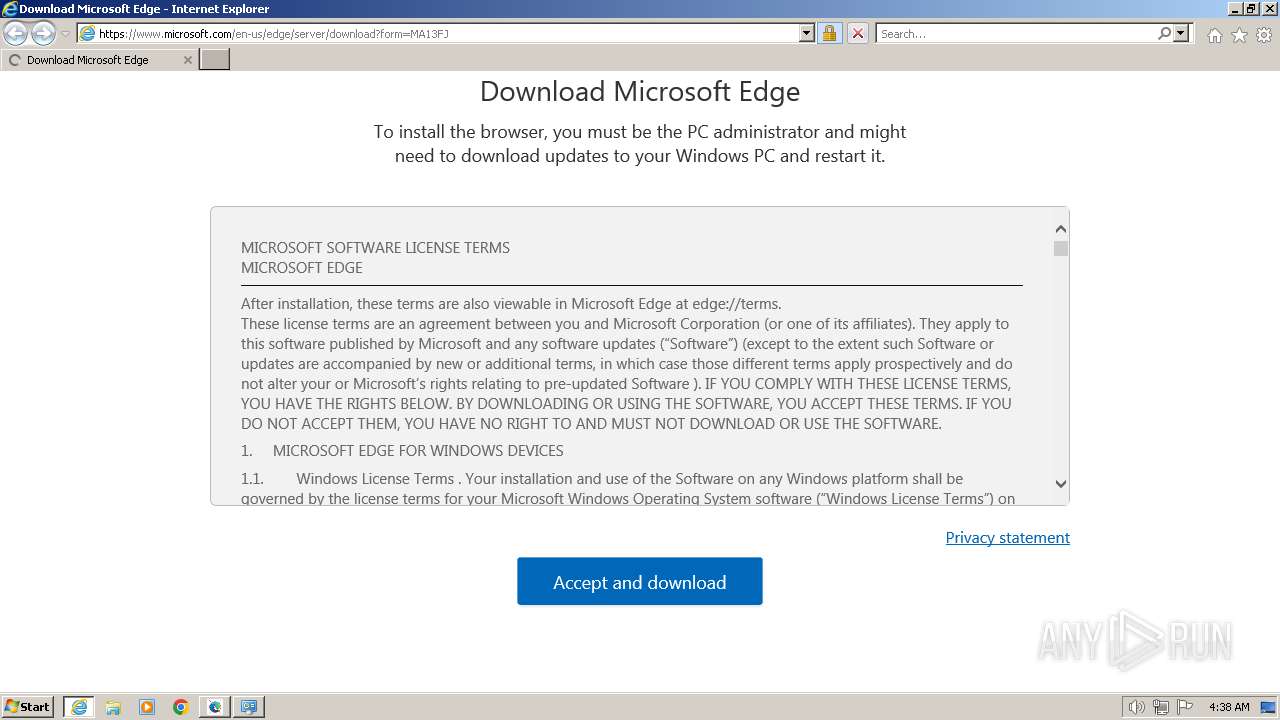
Application launched itself
- msedge.exe (PID: 2568)
- iexplore.exe (PID: 2556)
- msedge.exe (PID: 1624)
Reads the machine GUID from the registry
- setup.exe (PID: 712)
Manual execution by a user
- iexplore.exe (PID: 2556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.1) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.5) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:19 11:27:31+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 106496 |
| InitializedDataSize: | 45056 |
| UninitializedDataSize: | 110592 |
| EntryPoint: | 0x34f70 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileVersion: | 2.7.5.0(32位系统版) |
| ProductVersion: | 2.7.5.0(32位系统版) |
| ProductName: | 2.7.5.0(32位系统版)Microsoft Edge卸载工具 |
| OriginalFileName: | Microsoft Edge卸载工具 |
| FileDescription: | 一款简单好用的Microsoft Edge卸载工具 |
Total processes
94
Monitored processes
48
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xf8,0x6ba2f598,0x6ba2f5a8,0x6ba2f5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 712 | "C:\Program Files\Microsoft\Edge\Application\109.0.1518.115\Installer\setup.exe" --uninstall --msedge --channel=stable --system-level --verbose-logging | C:\Program Files\Microsoft\Edge\Application\109.0.1518.115\Installer\setup.exe | dllhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Installer Exit code: 19 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 748 | taskkill /f /t /im MicrosoftEdgeUpdate.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 796 | taskkill /t /f backgroundTaskHost.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 956 | taskkill /t /f /im widgets.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1584 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1252 --field-trial-handle=1428,i,17436484288542998420,10071271364950053426,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1624 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --suspend-background-mode | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1644 | C:\Users\admin\AppData\Local\Temp\1F2B.tmp/install_wim_tweak.exe /o /l | C:\Users\admin\AppData\Local\Temp\1F2B.tmp\install_wim_tweak.exe | — | cmd.exe | |||||||||||
User: admin Company: Modified by Legolash2o Integrity Level: HIGH Description: win6.x_registry_tweak Exit code: 0 Version: 1.4.7.0 Modules
| |||||||||||||||
| 1656 | taskkill /f /t /im msedge.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1696 | takeown /f "y\Program Files\WindowsApps\DeletedAllUserPackages\Microsoft.WindowsFeedbackHub_1.2201.61.0_neutral_split.scale-125_8wekyb3d8bbwe\Assets\Images\EdgeLogo.scale-125.png" | C:\Windows\System32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
24 443
Read events
24 129
Write events
128
Delete events
186
Modification events
| (PID) Process: | (2000) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Microsoft Edge Update |
| Operation: | write | Name: | NoRemove |
Value: 0 | |||
| (PID) Process: | (2596) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Microsoft EdgeWebView |
| Operation: | write | Name: | NoRemove |
Value: 0 | |||
| (PID) Process: | (3308) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Microsoft Edge |
| Operation: | write | Name: | NoRemove |
Value: 0 | |||
| (PID) Process: | (1624) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1624) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1624) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1624) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1624) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1624) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1624) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
2
Suspicious files
12
Text files
21
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4044 | v2.7.5.0-32bit.exe | C:\Users\admin\AppData\Local\Temp\1F2B.tmp\1F2C.tmp\1F2D.bat | text | |
MD5:— | SHA256:— | |||
| 4044 | v2.7.5.0-32bit.exe | C:\Users\admin\AppData\Local\Temp\1F2B.tmp\install_wim_tweak.exe | executable | |
MD5:— | SHA256:— | |||
| 1644 | install_wim_tweak.exe | C:\Users\admin\AppData\Local\Temp\Packages.txt | text | |
MD5:— | SHA256:— | |||
| 3324 | install_wim_tweak.exe | C:\Users\admin\AppData\Local\Temp\Packages.txt | text | |
MD5:— | SHA256:— | |||
| 1624 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\settings.dat | binary | |
MD5:— | SHA256:— | |||
| 2632 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\CrashpadMetrics.pma | binary | |
MD5:— | SHA256:— | |||
| 1624 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Variations | binary | |
MD5:— | SHA256:— | |||
| 1624 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\958f5a67-b68b-4204-b948-a0e241419585.tmp | — | |
MD5:— | SHA256:— | |||
| 1624 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF18625e.TMP | binary | |
MD5:— | SHA256:— | |||
| 1624 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
27
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3048 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?80db9c8c50c110d9 | unknown | — | — | unknown |
3048 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
3048 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?afc5c8919c0c2a29 | unknown | — | — | unknown |
3048 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | unknown |
3048 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
2556 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?799d03254737cc91 | unknown | — | — | unknown |
2556 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?753a240a9c2686f2 | unknown | — | — | unknown |
2556 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3048 | iexplore.exe | 184.30.17.189:443 | go.microsoft.com | AKAMAI-AS | DE | unknown |
3048 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3048 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3048 | iexplore.exe | 184.30.21.171:443 | www.microsoft.com | AKAMAI-AS | DE | unknown |
3048 | iexplore.exe | 152.199.19.160:443 | ajax.aspnetcdn.com | EDGECAST | US | whitelisted |
3048 | iexplore.exe | 13.107.246.60:443 | edgestatic.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2556 | iexplore.exe | 13.107.246.60:443 | edgestatic.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ajax.aspnetcdn.com |
| whitelisted |
edgestatic.azureedge.net |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |