| download: | cmslitesetup.exe |
| Full analysis: | https://app.any.run/tasks/f18b78c3-2425-42f9-b38d-428cc0a5f14b |
| Verdict: | Malicious activity |
| Analysis date: | September 25, 2019, 12:51:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | C29DDFCEA6D248F3C19A190D0CFE8908 |
| SHA1: | 3271D554FF5CD21FCFDF15E214007E0F74AB847D |
| SHA256: | 24F3557C13F824B70A1C1771F134583C5DB9C865B132E99A5A7F755148407866 |
| SSDEEP: | 196608:XCWRV2TiQmzEGNDDbGgxQeBu2VA8Ni12LCfTGAgrK2Te/:y46iQmwGNDbzQeBzq4p5zs/ |
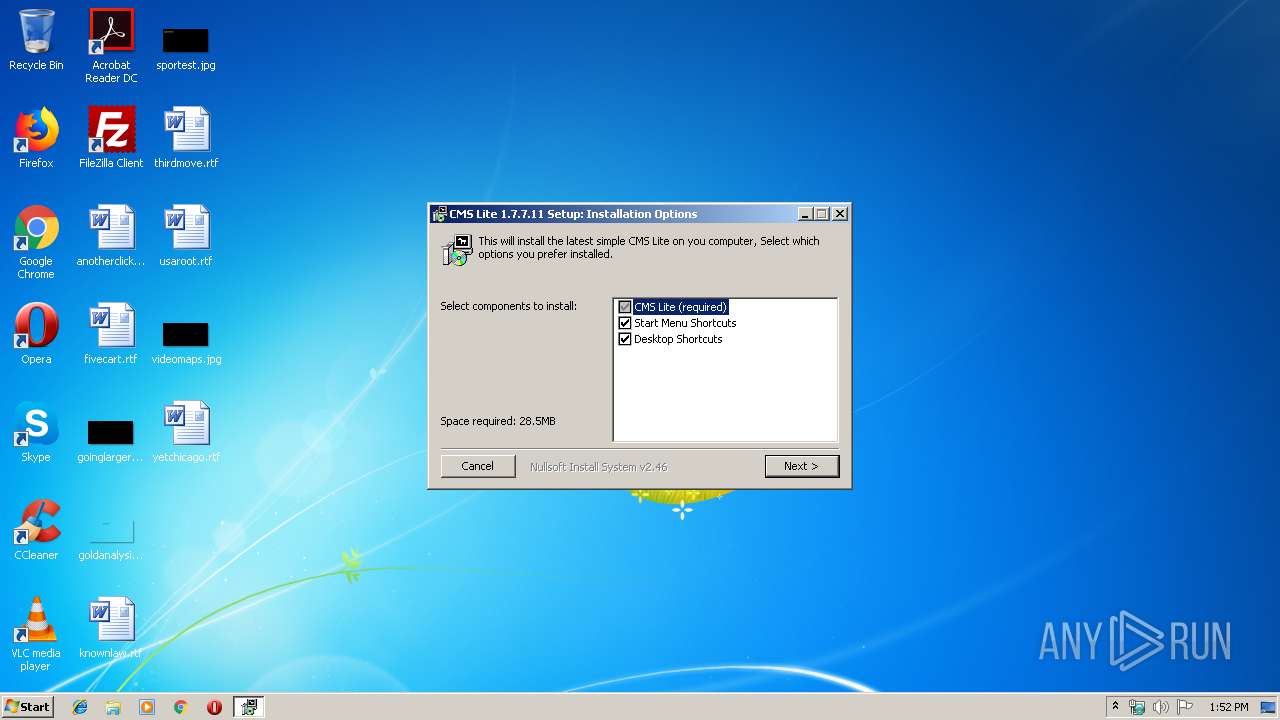
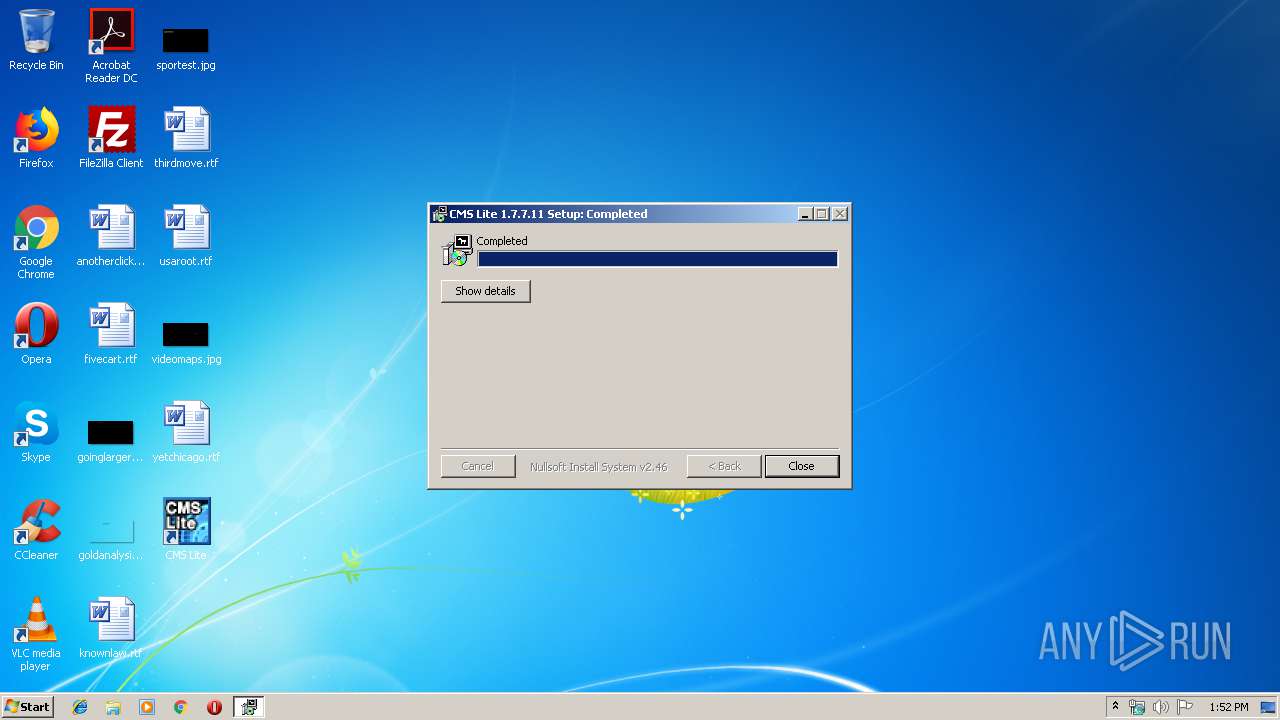
MALICIOUS
Application was dropped or rewritten from another process
- SMS.exe (PID: 3236)
Loads dropped or rewritten executable
- SMS.exe (PID: 3236)
SUSPICIOUS
Creates files in the user directory
- cmslitesetup.exe (PID: 1660)
Executable content was dropped or overwritten
- cmslitesetup.exe (PID: 1660)
Creates a software uninstall entry
- cmslitesetup.exe (PID: 1660)
Creates files in the program directory
- cmslitesetup.exe (PID: 1660)
INFO
Manual execution by user
- SMS.exe (PID: 3236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:52+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30fa |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:52 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005C4C | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44011 |
.rdata | 0x00007000 | 0x0000129C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04684 |
.data | 0x00009000 | 0x00025C58 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.801 |
.ndata | 0x0002F000 | 0x00008000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00037000 | 0x00002C90 | 0x00002E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.70777 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21482 | 958 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.6935 | 316 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.62276 | 196 | UNKNOWN | English - United States | RT_DIALOG |
110 | 3.22336 | 872 | UNKNOWN | English - United States | RT_BITMAP |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
203 | 2.54013 | 304 | UNKNOWN | English - United States | RT_DIALOG |
204 | 2.66176 | 296 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
40
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1660 | "C:\Users\admin\AppData\Local\Temp\cmslitesetup.exe" | C:\Users\admin\AppData\Local\Temp\cmslitesetup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
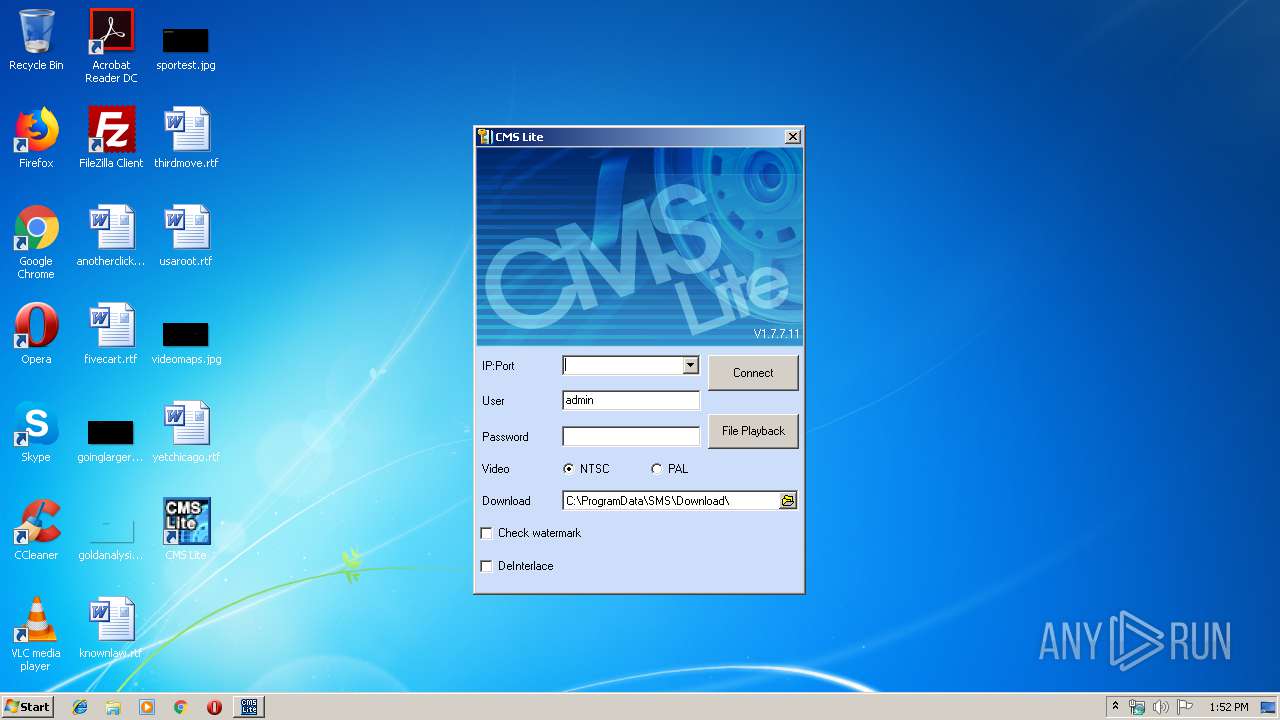
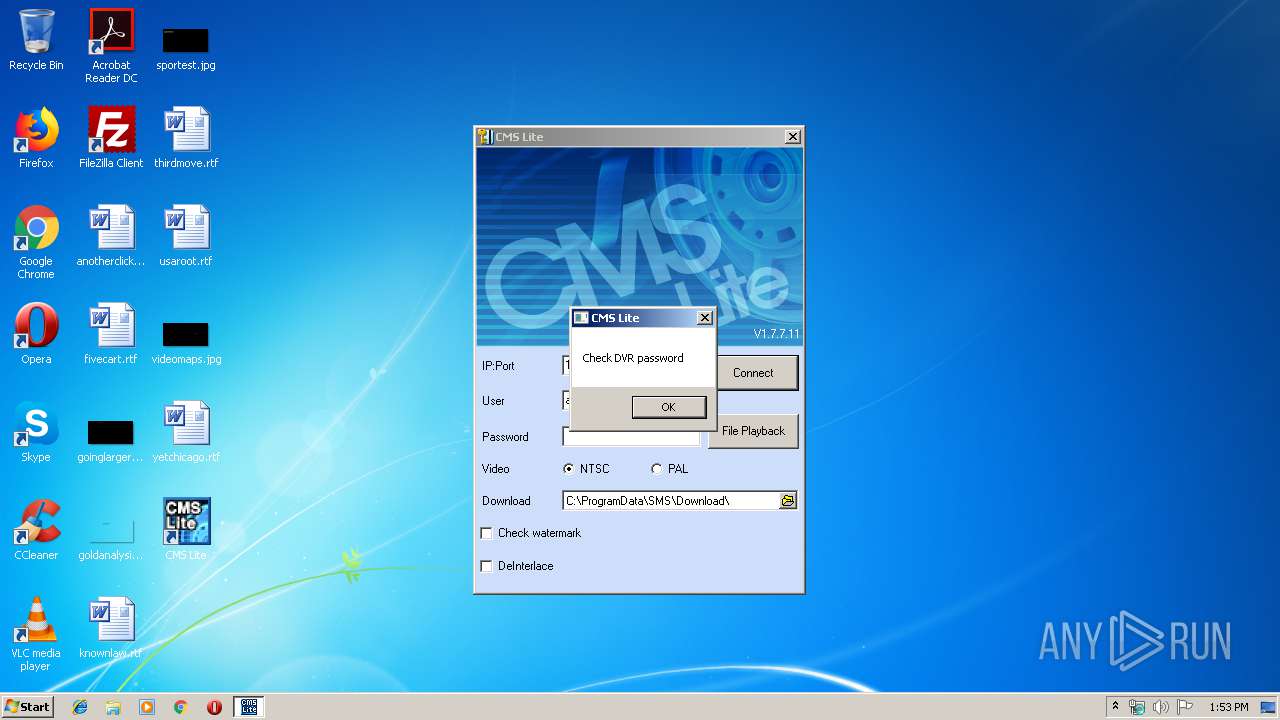
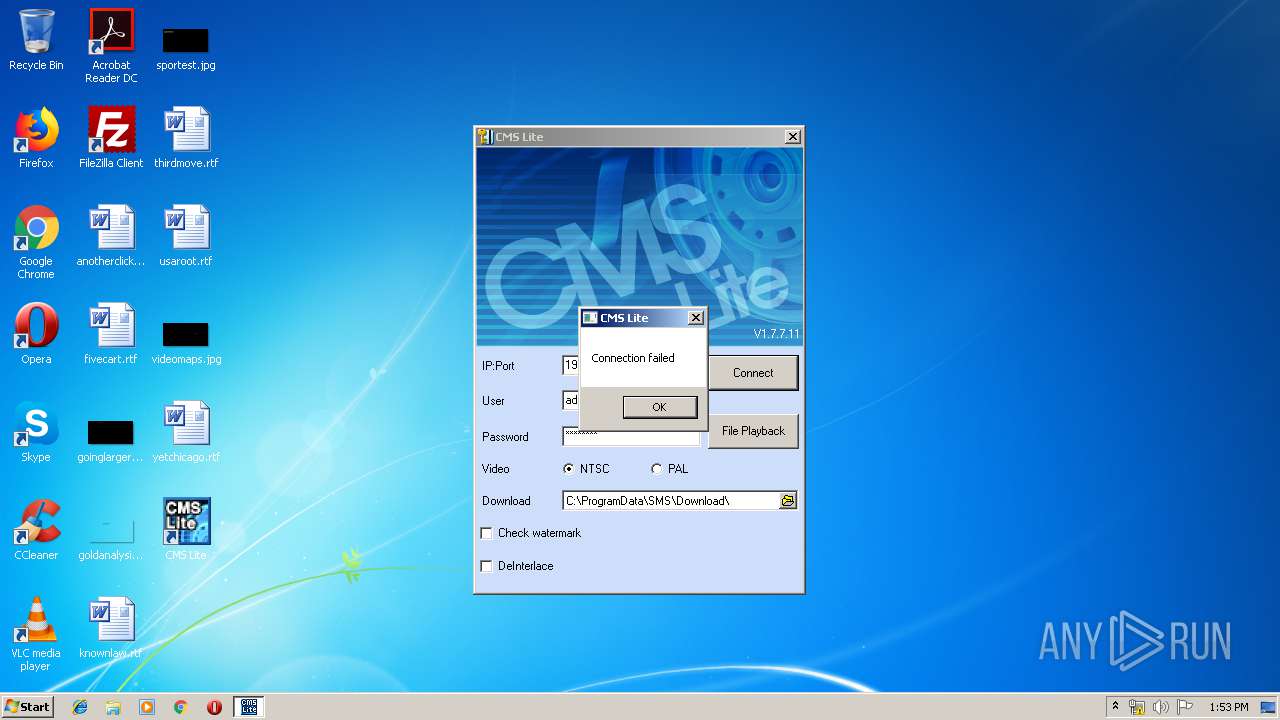
| 3236 | "C:\Program Files\CMS Lite\SMS.exe" | C:\Program Files\CMS Lite\SMS.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.7.7.11 Modules
| |||||||||||||||
| 3676 | "C:\Users\admin\AppData\Local\Temp\cmslitesetup.exe" | C:\Users\admin\AppData\Local\Temp\cmslitesetup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
424
Read events
388
Write events
36
Delete events
0
Modification events
| (PID) Process: | (1660) cmslitesetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\PINETRON\SMS\SYSTEM |
| Operation: | write | Name: | OEM |
Value: 0 | |||
| (PID) Process: | (1660) cmslitesetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\PINETRON\SMS\SYSTEM |
| Operation: | write | Name: | AUD |
Value: 0 | |||
| (PID) Process: | (1660) cmslitesetup.exe | Key: | HKEY_CURRENT_USER\Software\PINETRON\SMS\SYSTEM |
| Operation: | write | Name: | AUD |
Value: 0 | |||
| (PID) Process: | (1660) cmslitesetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\PINETRON\SMS\SYSTEM |
| Operation: | write | Name: | TITLE1 |
Value: CMS Lite | |||
| (PID) Process: | (1660) cmslitesetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\PINETRON\SMS\SYSTEM |
| Operation: | write | Name: | TITLE2 |
Value: CMS Lite | |||
| (PID) Process: | (1660) cmslitesetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\PINETRON\SMS\SYSTEM |
| Operation: | write | Name: | TITLE3 |
Value: Connect DVR | |||
| (PID) Process: | (1660) cmslitesetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\PINETRON\SMS\SYSTEM |
| Operation: | write | Name: | CMODE |
Value: 0 | |||
| (PID) Process: | (1660) cmslitesetup.exe | Key: | HKEY_CURRENT_USER\Software\PINETRON\SMS\SYSTEM |
| Operation: | write | Name: | CMODE |
Value: 0 | |||
| (PID) Process: | (1660) cmslitesetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SMS |
| Operation: | write | Name: | DisplayName |
Value: SMS (remove only) | |||
| (PID) Process: | (1660) cmslitesetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SMS |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\CMS Lite\uninstall.exe" | |||
Executable files
5
Suspicious files
0
Text files
16
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
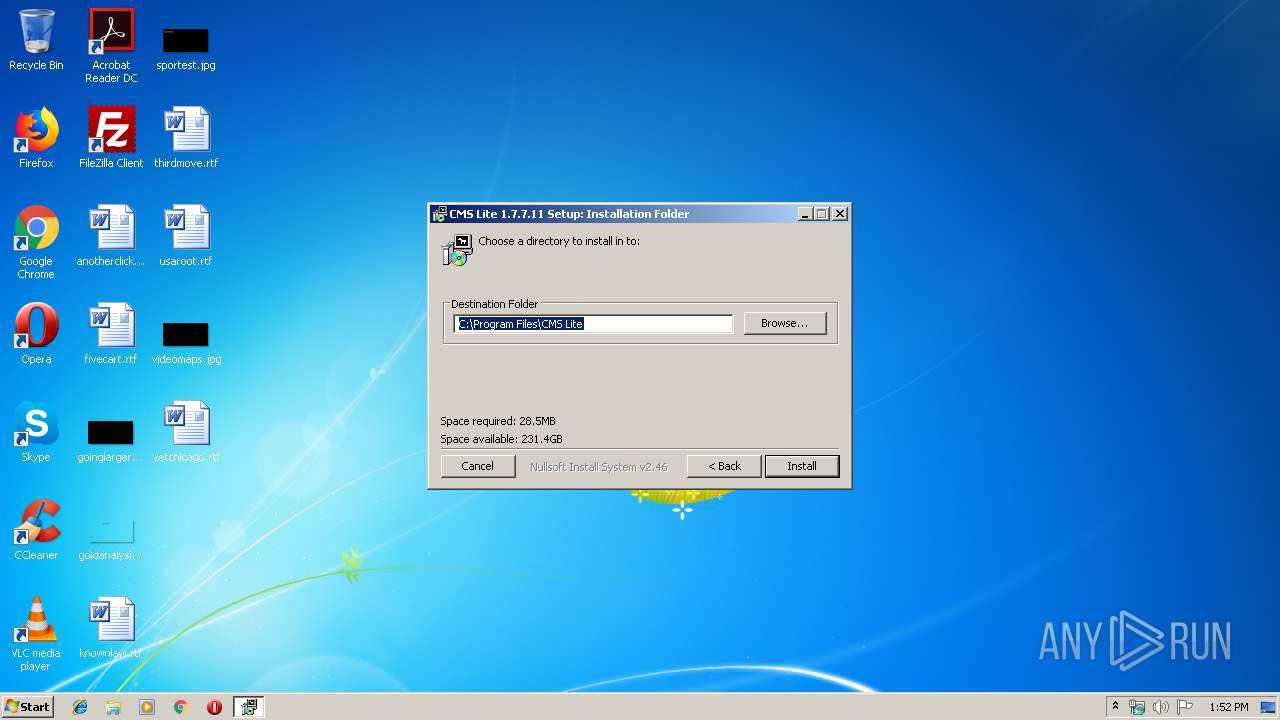
| 1660 | cmslitesetup.exe | C:\Program Files\CMS Lite\AviConverter.exe | executable | |
MD5:— | SHA256:— | |||
| 1660 | cmslitesetup.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\CMS Lite\Uninstall.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1660 | cmslitesetup.exe | C:\Program Files\CMS Lite\uninstall.exe | executable | |
MD5:— | SHA256:— | |||
| 1660 | cmslitesetup.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\CMS Lite\AVI Converter.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3236 | SMS.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\PdvrServer.INI | text | |
MD5:— | SHA256:— | |||
| 1660 | cmslitesetup.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\CMS Lite\CMS Lite.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1660 | cmslitesetup.exe | C:\Program Files\CMS Lite\SysInfo.dll | text | |
MD5:— | SHA256:— | |||
| 1660 | cmslitesetup.exe | C:\Program Files\CMS Lite\PdvrServer.dll | executable | |
MD5:— | SHA256:— | |||
| 1660 | cmslitesetup.exe | C:\Program Files\CMS Lite\SMS.exe | executable | |
MD5:— | SHA256:— | |||
| 1660 | cmslitesetup.exe | C:\Users\admin\Desktop\CMS Lite.lnk | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
SMS.exe | PdvrParser.axfile loading |
SMS.exe | Create Filter From Dll |
SMS.exe | Parent Handle 001100DE |