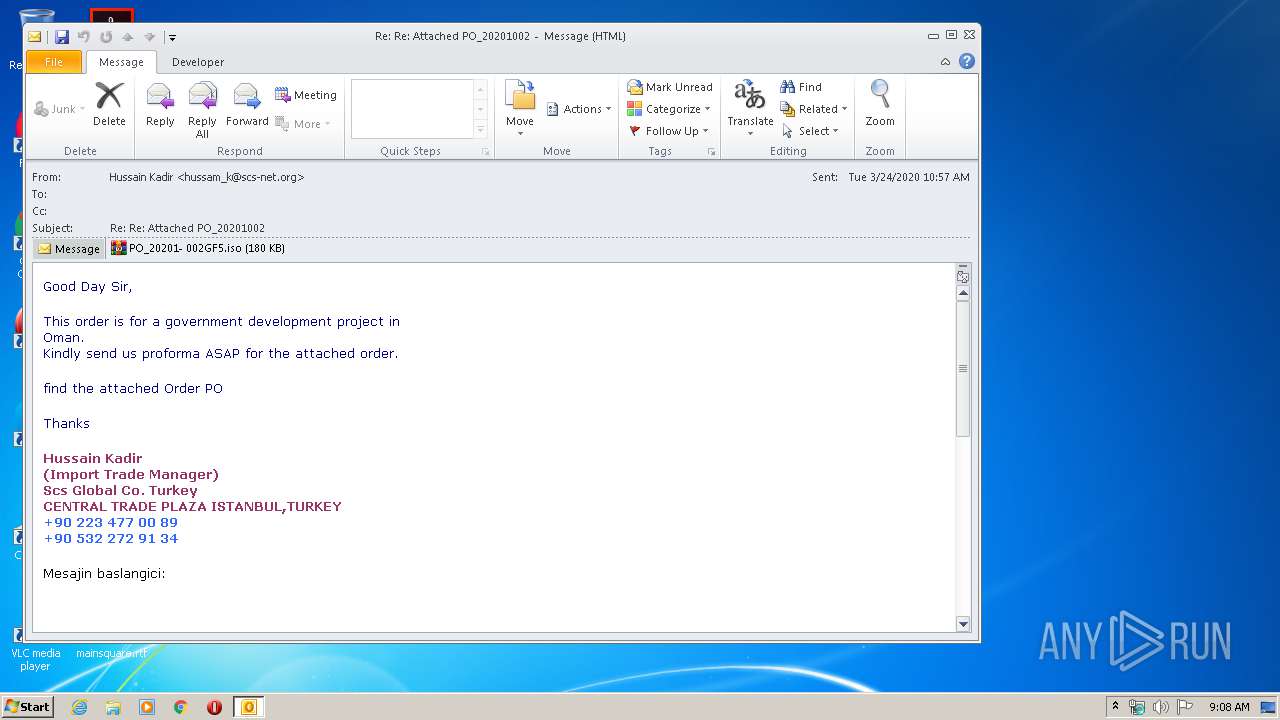
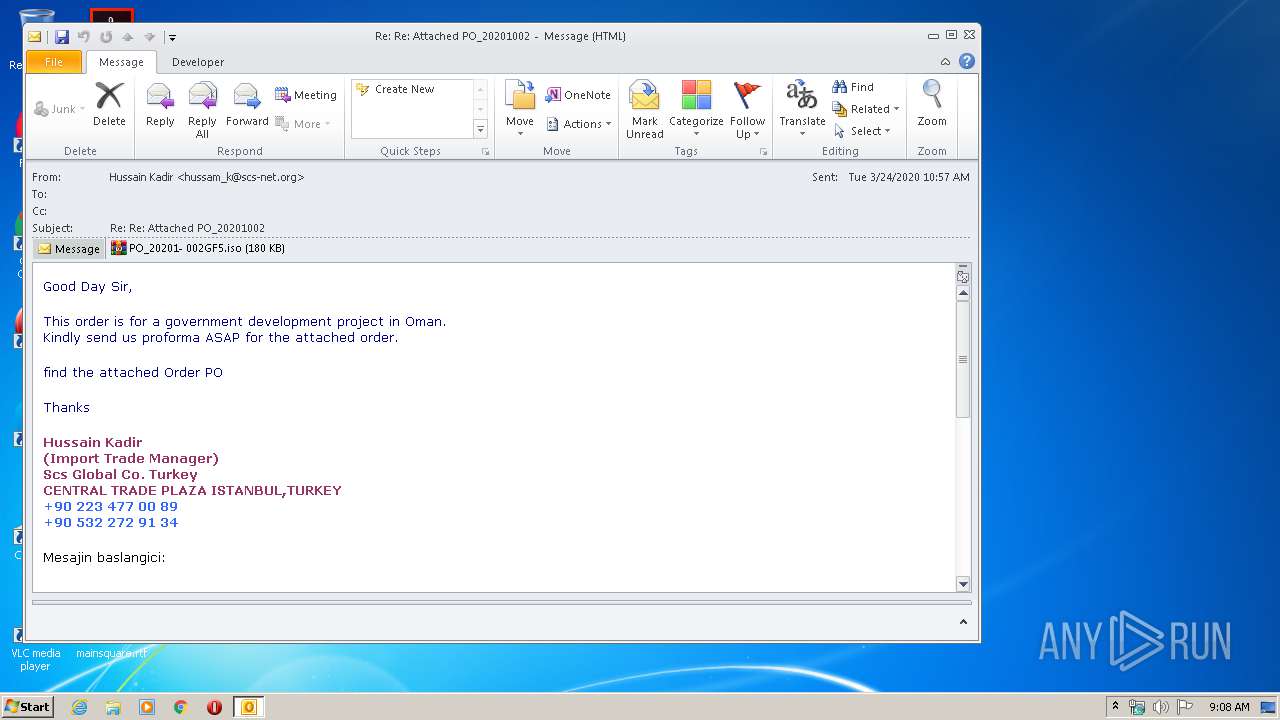
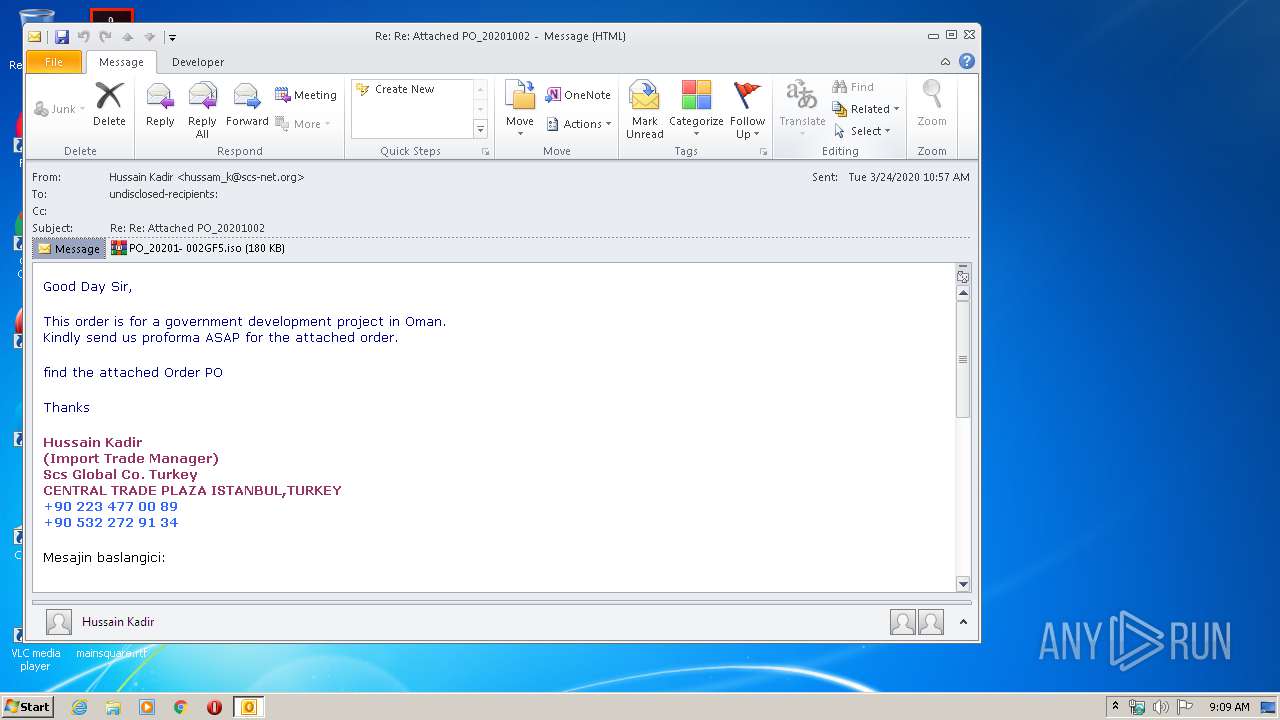
| File name: | 3fcd0cae-14e0-4245-da87-08d7d260c16c219e8e00-5909-9766-d12f-e6a7666b7525.eml |
| Full analysis: | https://app.any.run/tasks/16332ebd-a5ac-4616-a134-9a97340a5e75 |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 08:08:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with CRLF line terminators |
| MD5: | EE24513C50AEFE30E13177C6ACB381A6 |
| SHA1: | 0D33C8F25ADCA50A16AF906AEB3FA2FB16A386EC |
| SHA256: | 24CF4491A1245D09B56B3DAEF4EB34CCAEFA194A970C66C219157EEAA9F93278 |
| SSDEEP: | 1536:nuU8WQrqABGWtbWZ1SBYX7liRxKaYdMWgp3mYkQb2M8TkRo:nu8Qrq8GkmHX5i4SVWkb2M83 |
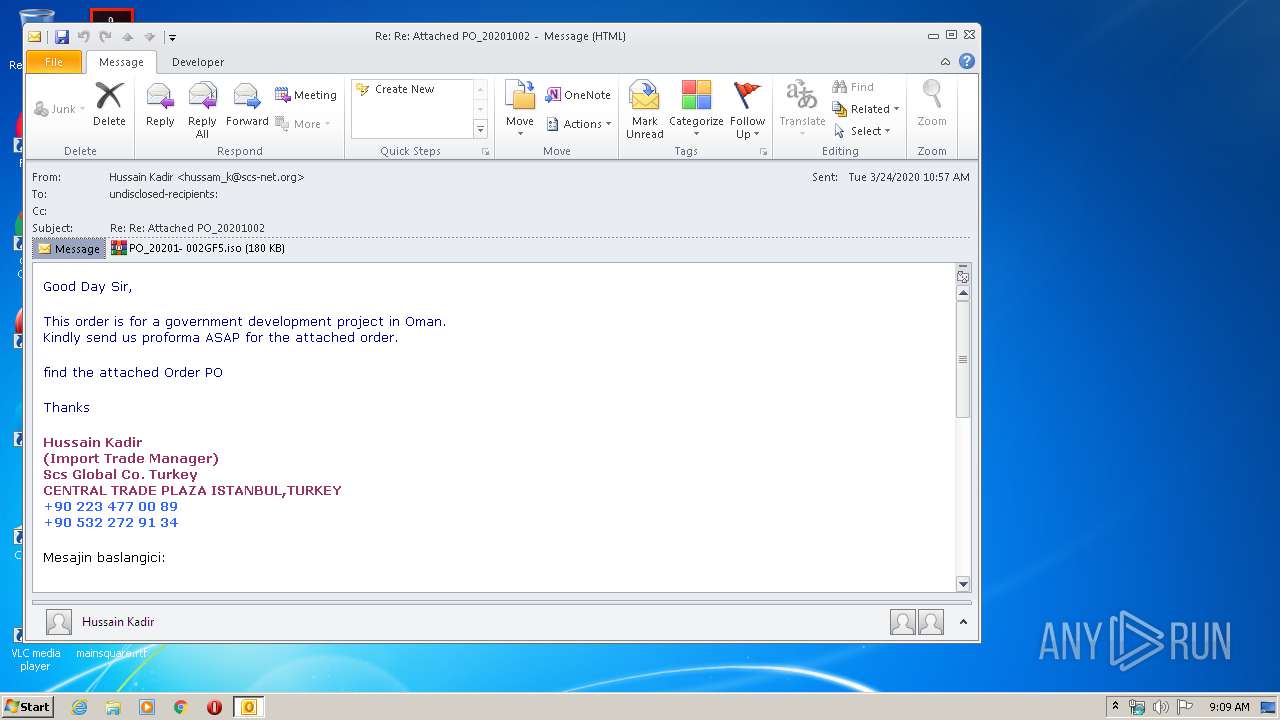
MALICIOUS
Application was dropped or rewritten from another process
- PO_20201- 002GF5.exe (PID: 2612)
- PO_20201- 002GF5.exe (PID: 2904)
Changes settings of System certificates
- RegAsm.exe (PID: 1196)
SUSPICIOUS
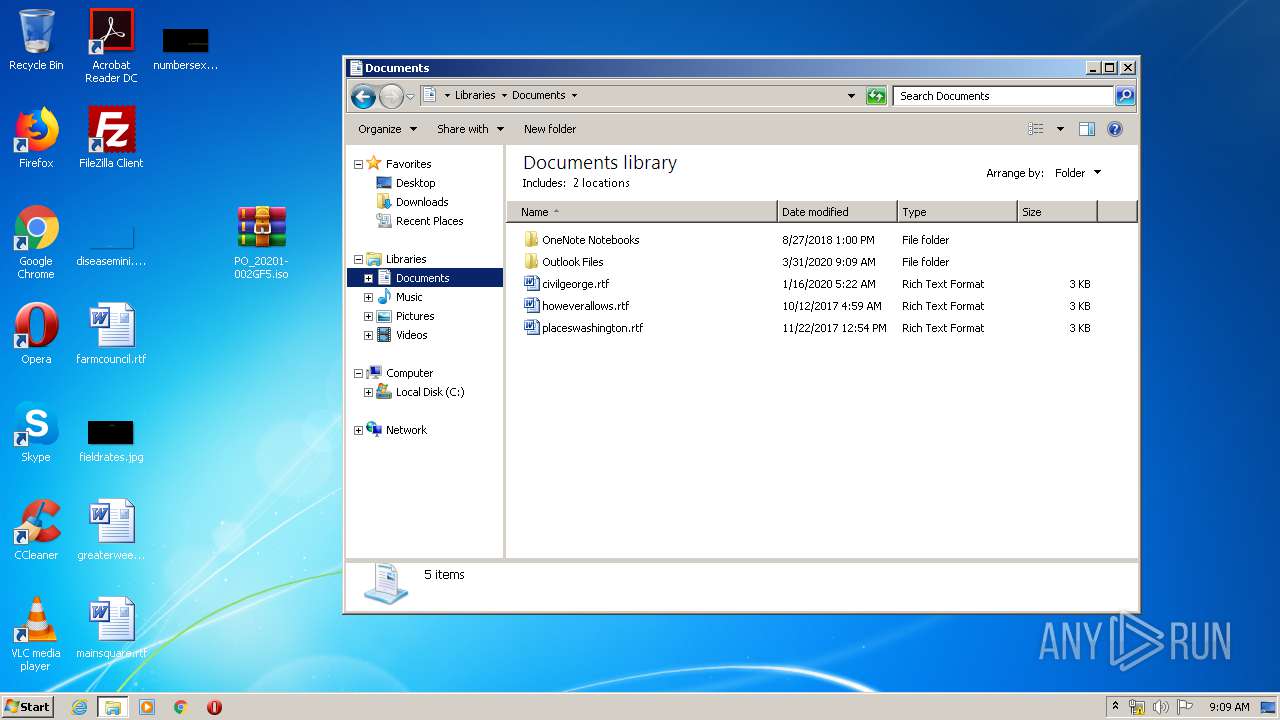
Creates files in the user directory
- OUTLOOK.EXE (PID: 304)
- RegAsm.exe (PID: 1196)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 304)
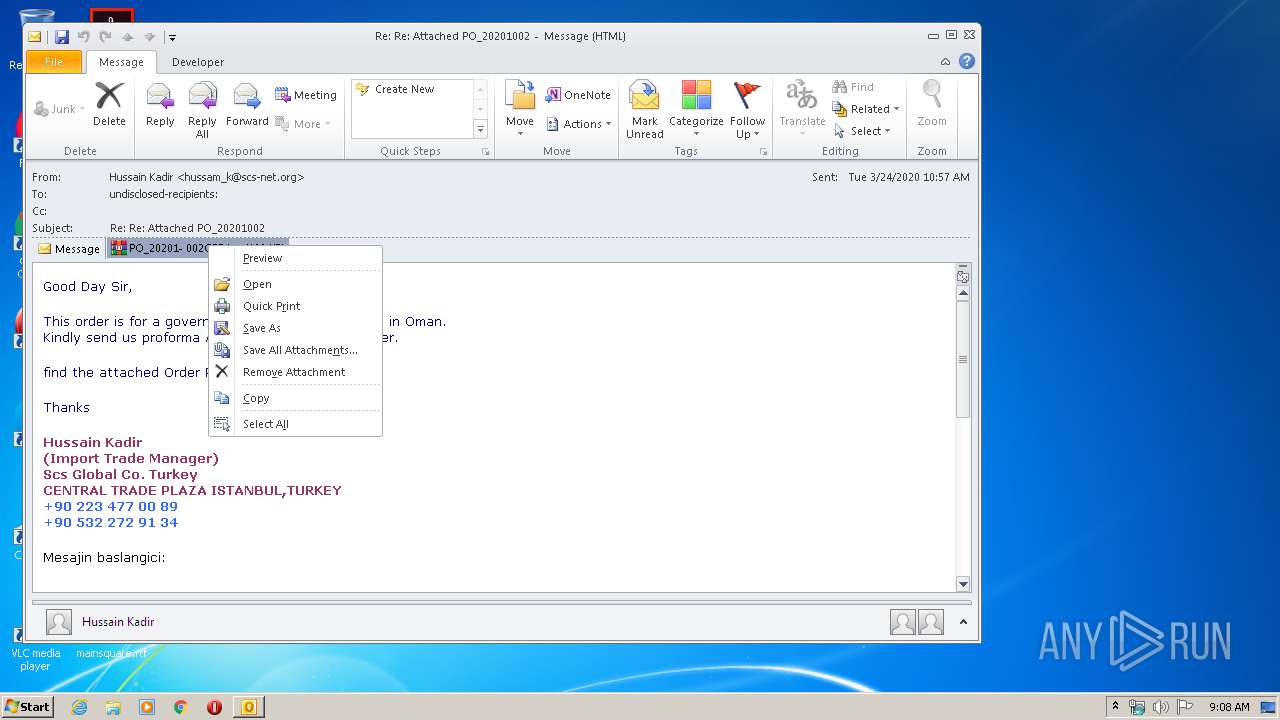
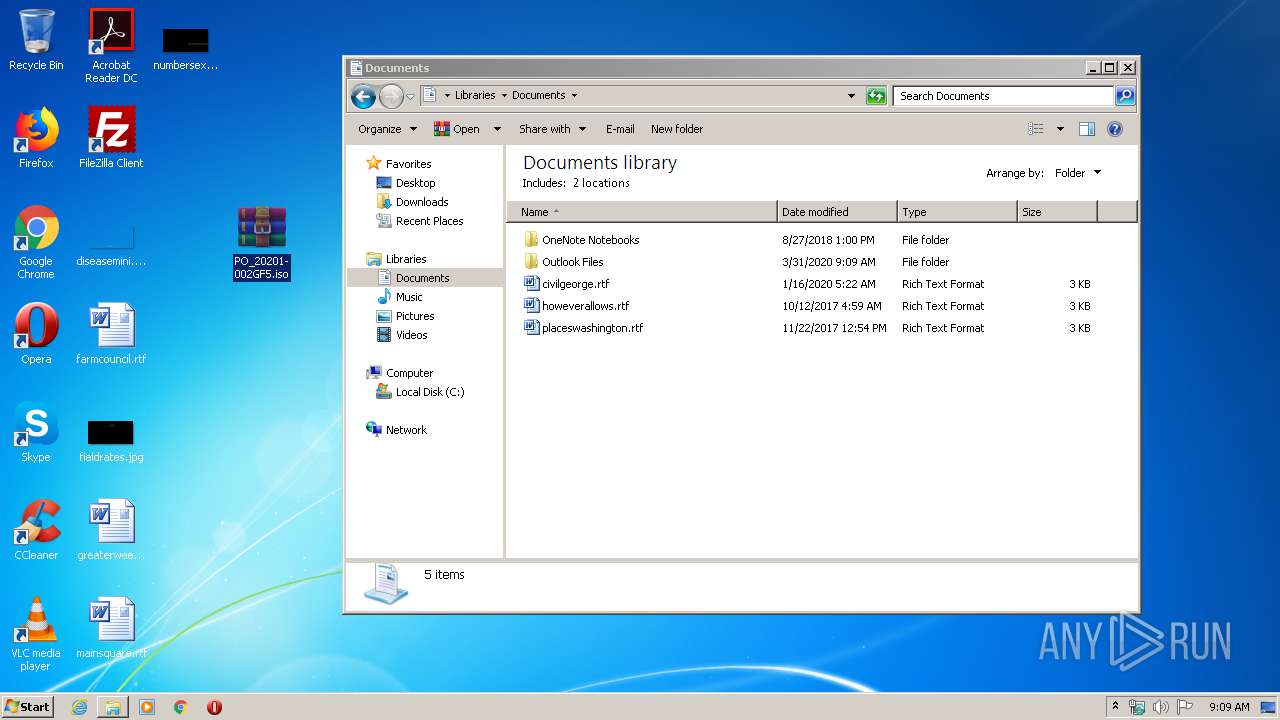
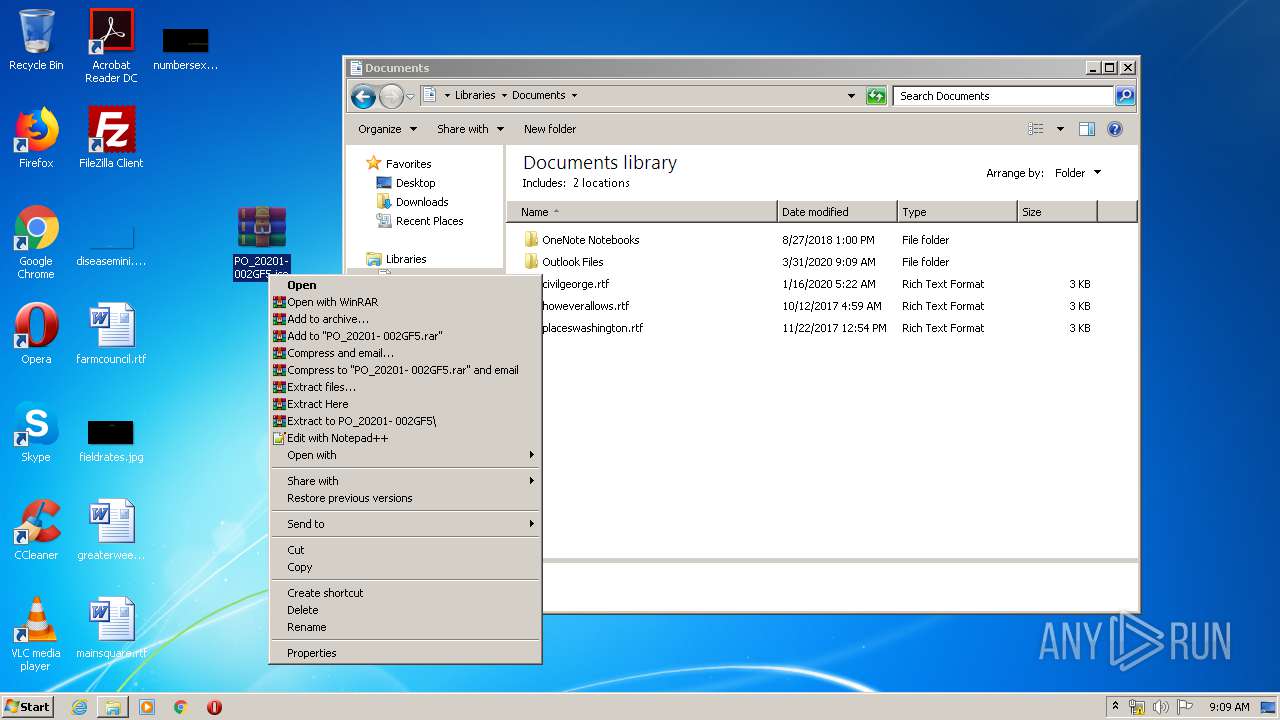
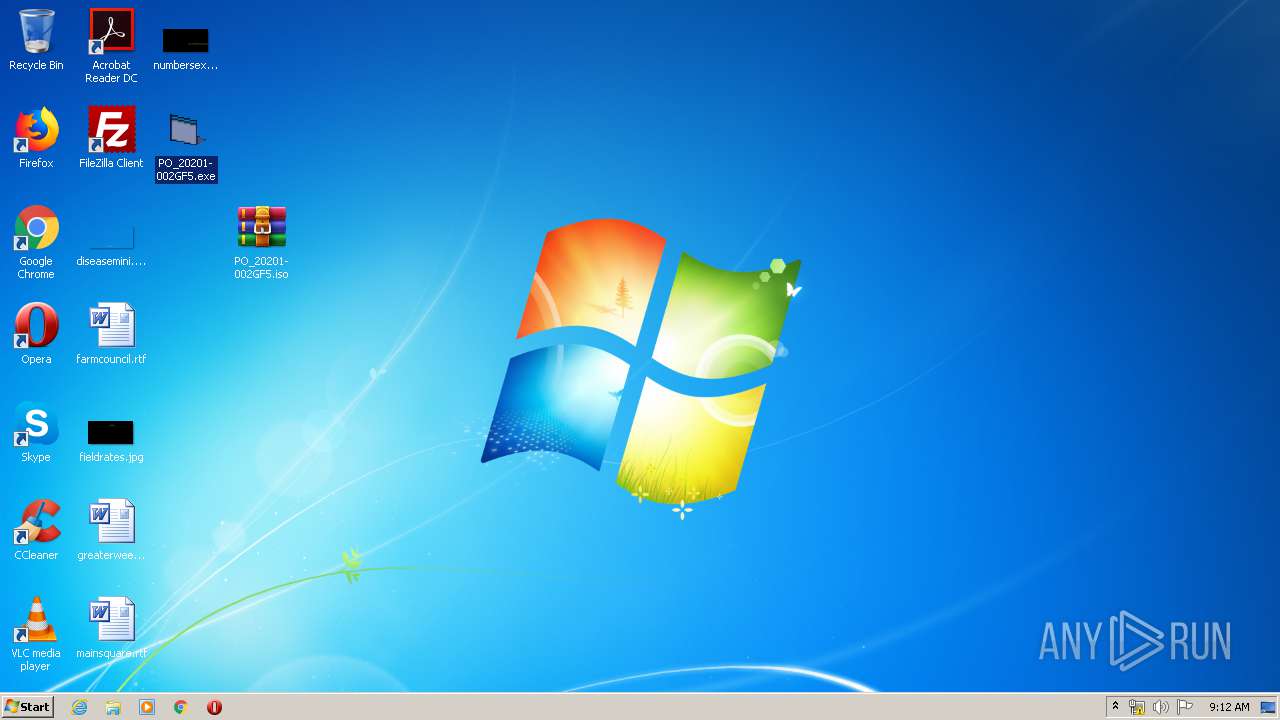
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3732)
Adds / modifies Windows certificates
- RegAsm.exe (PID: 1196)
INFO
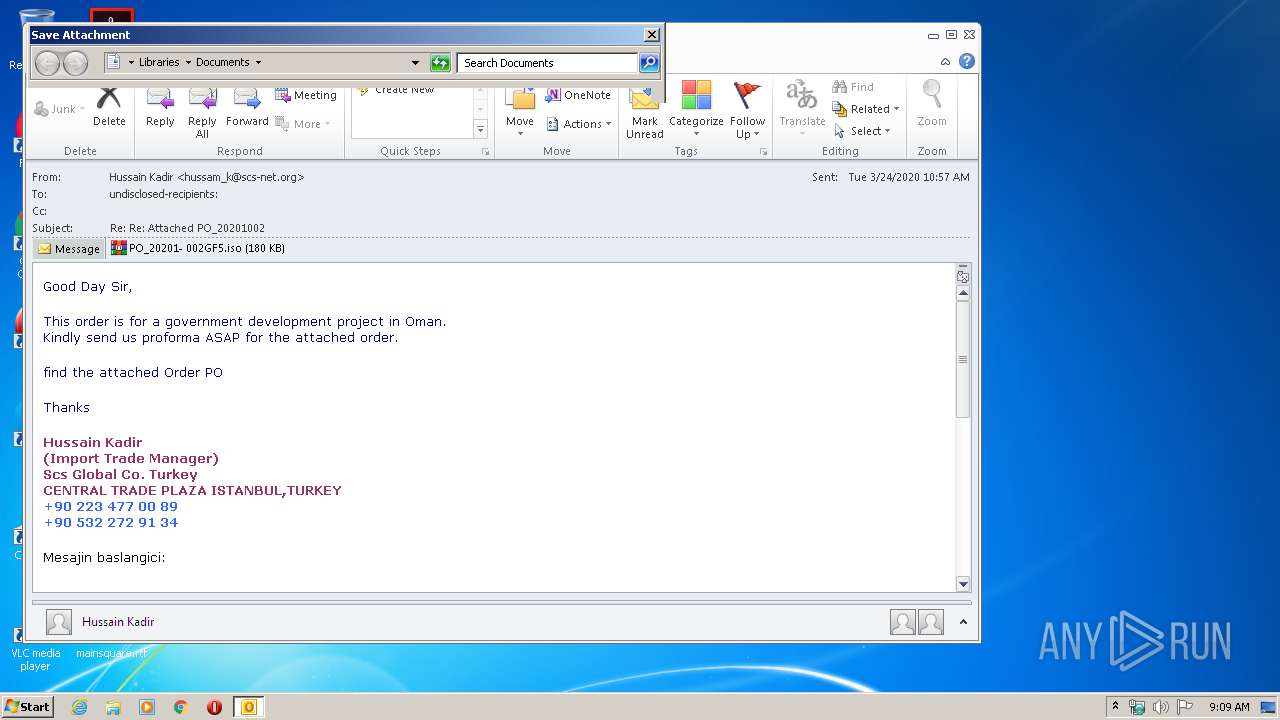
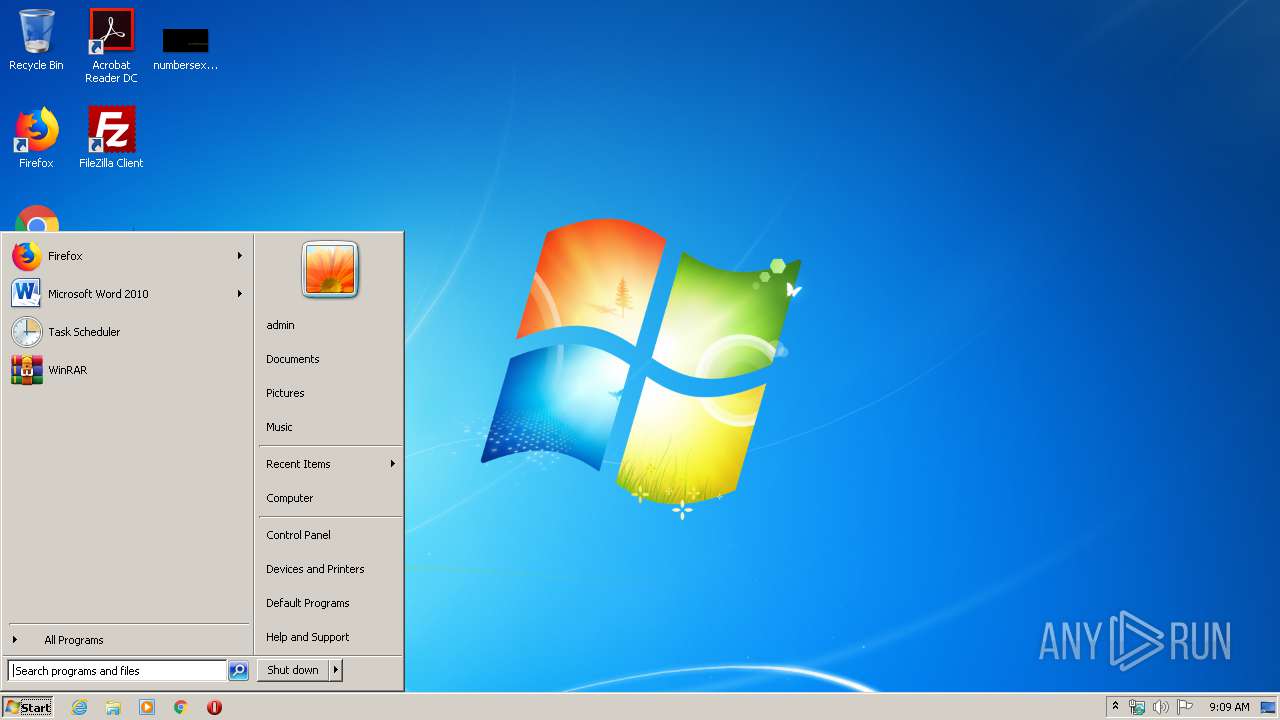
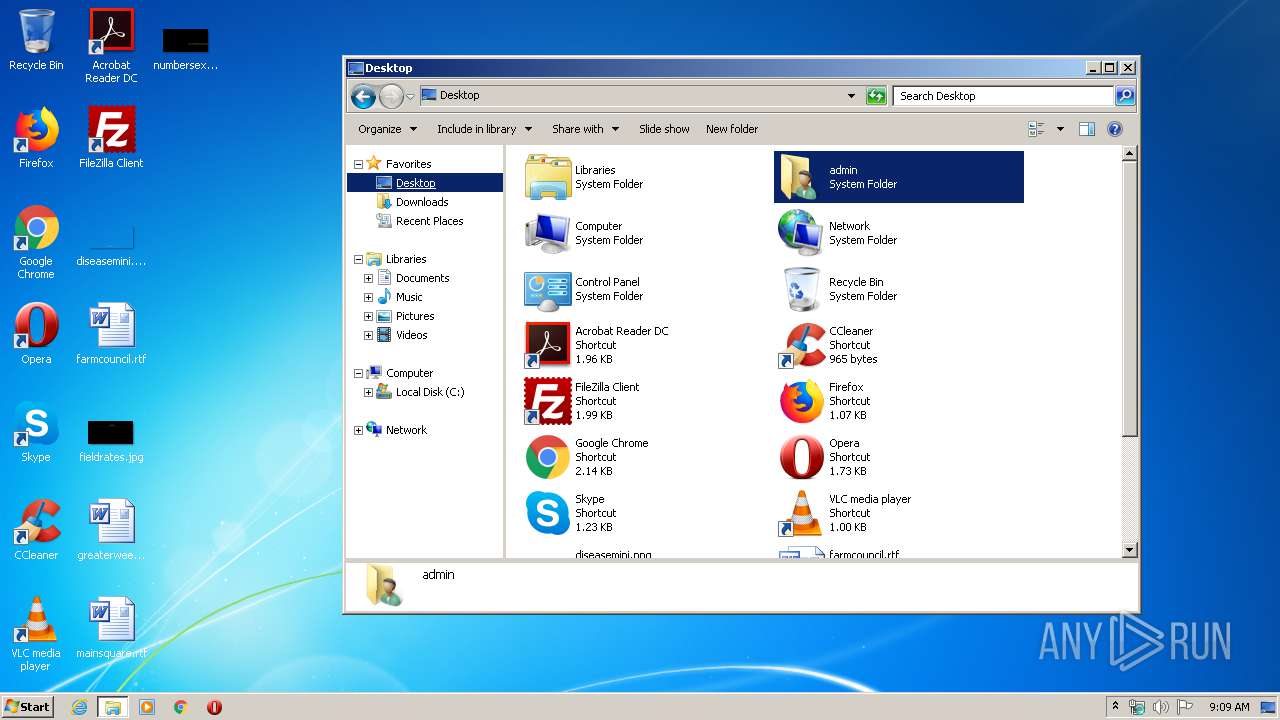
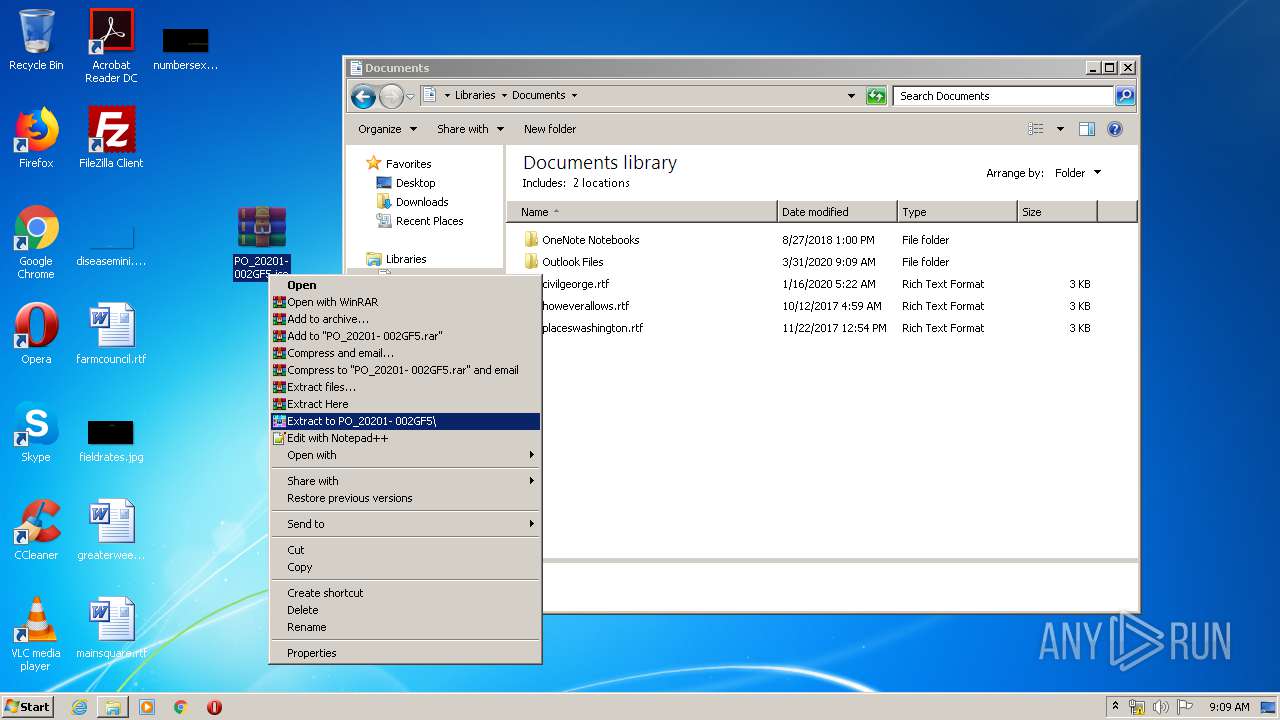
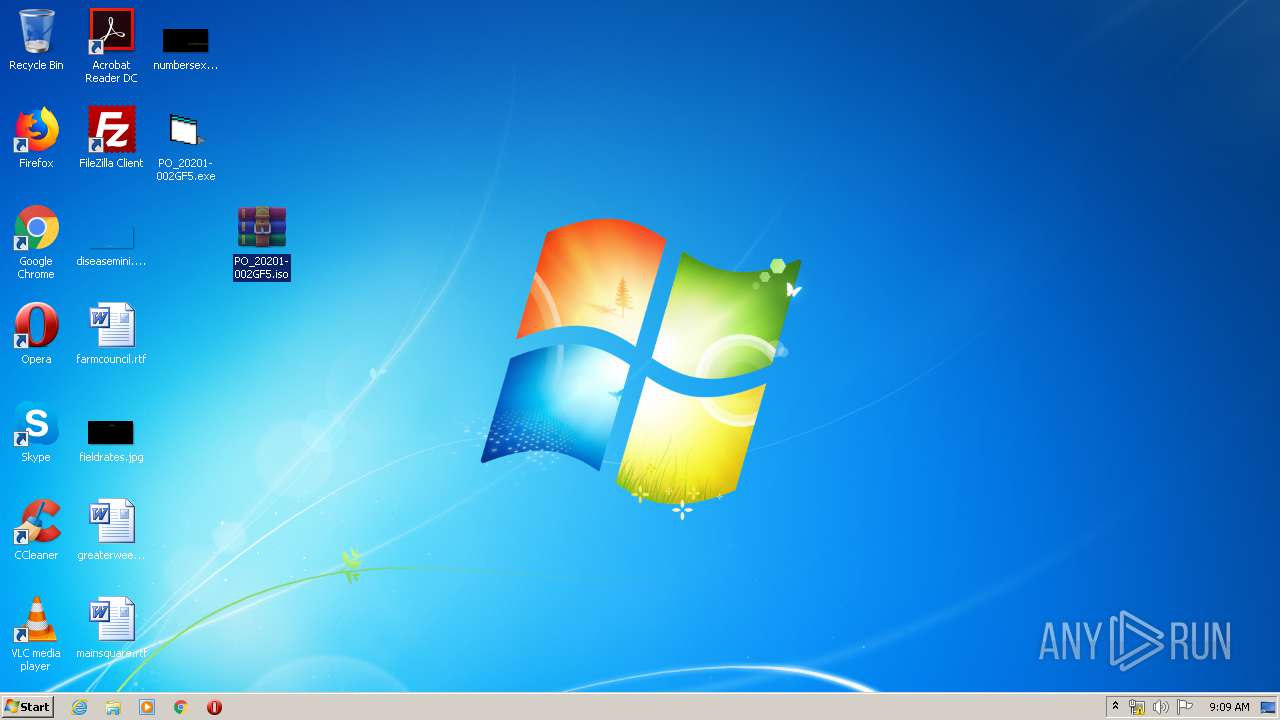
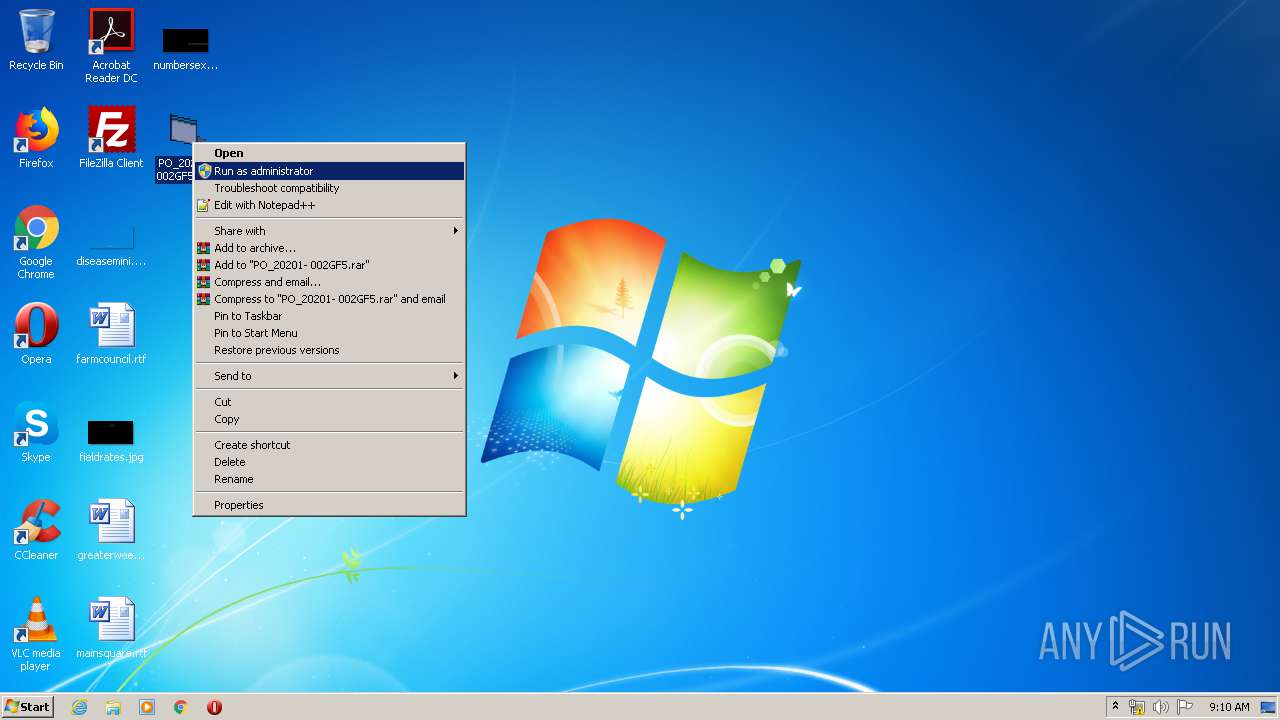
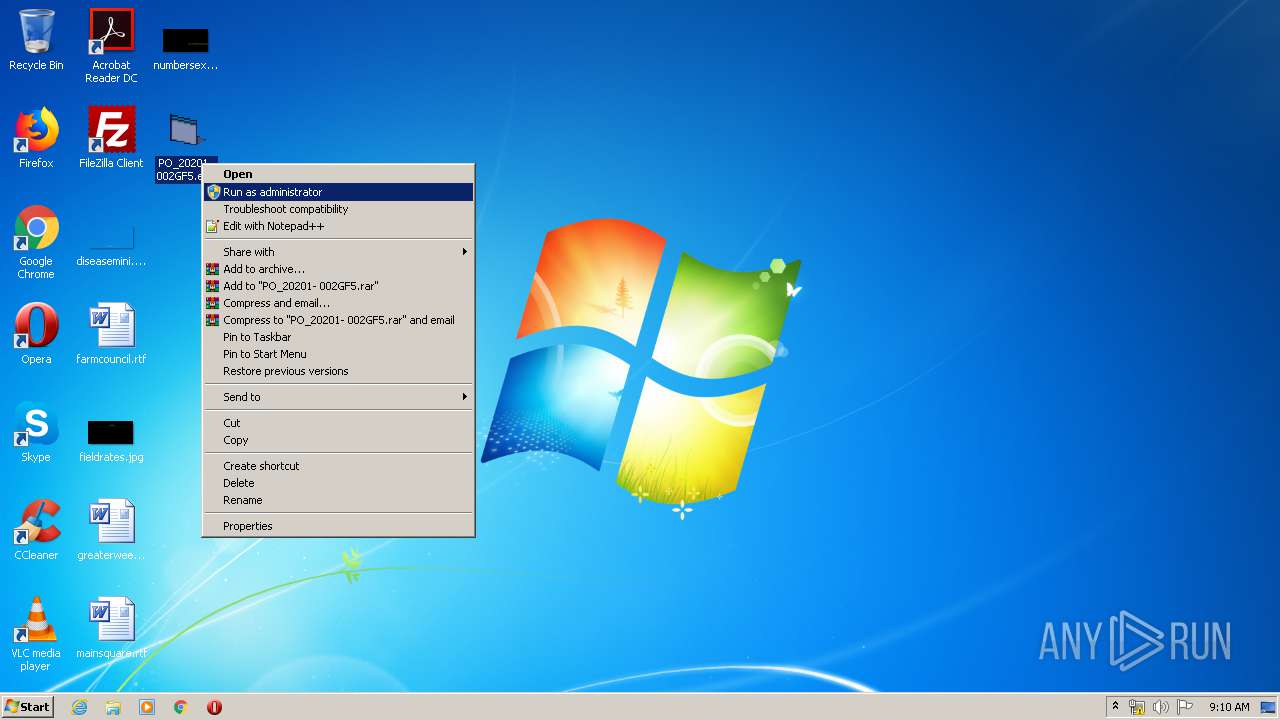
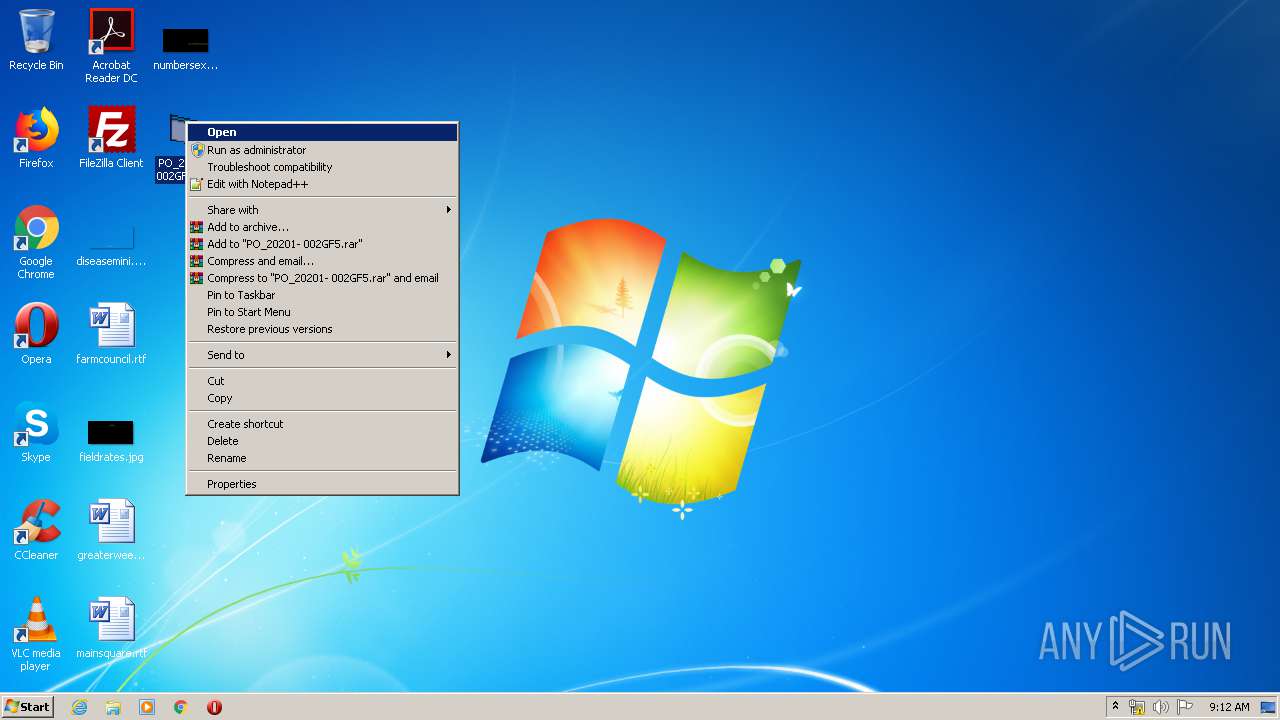
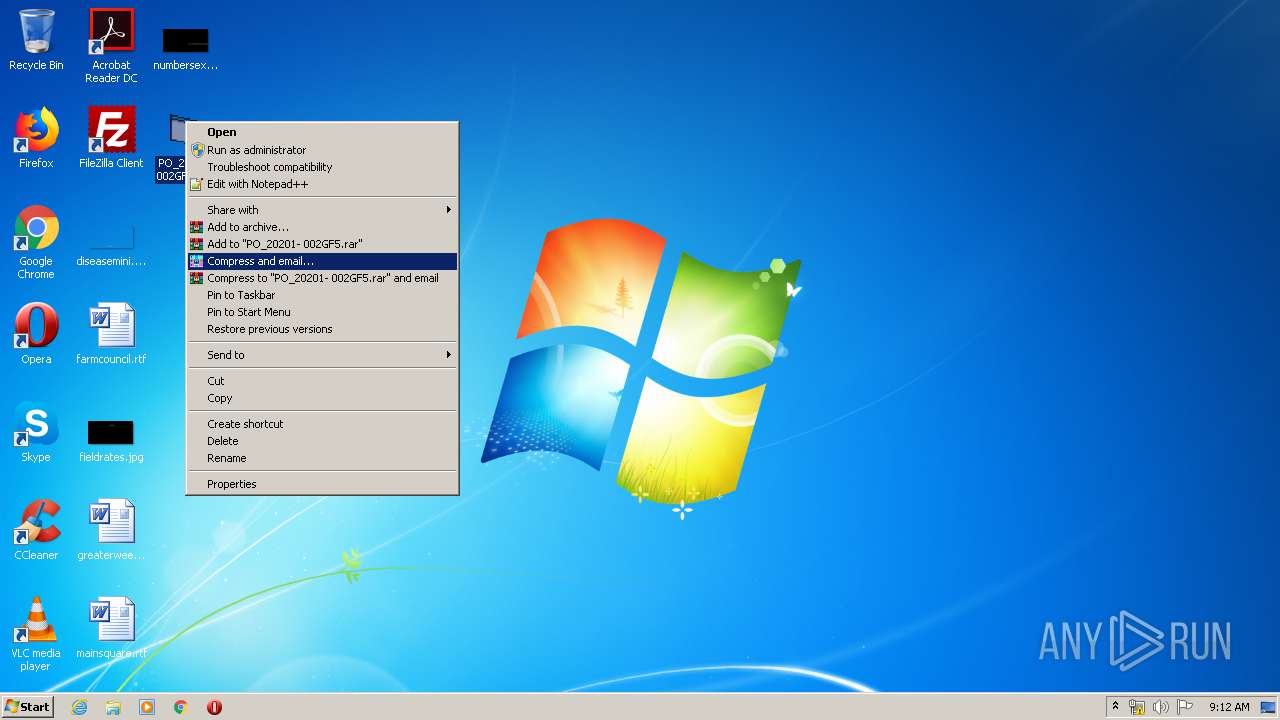
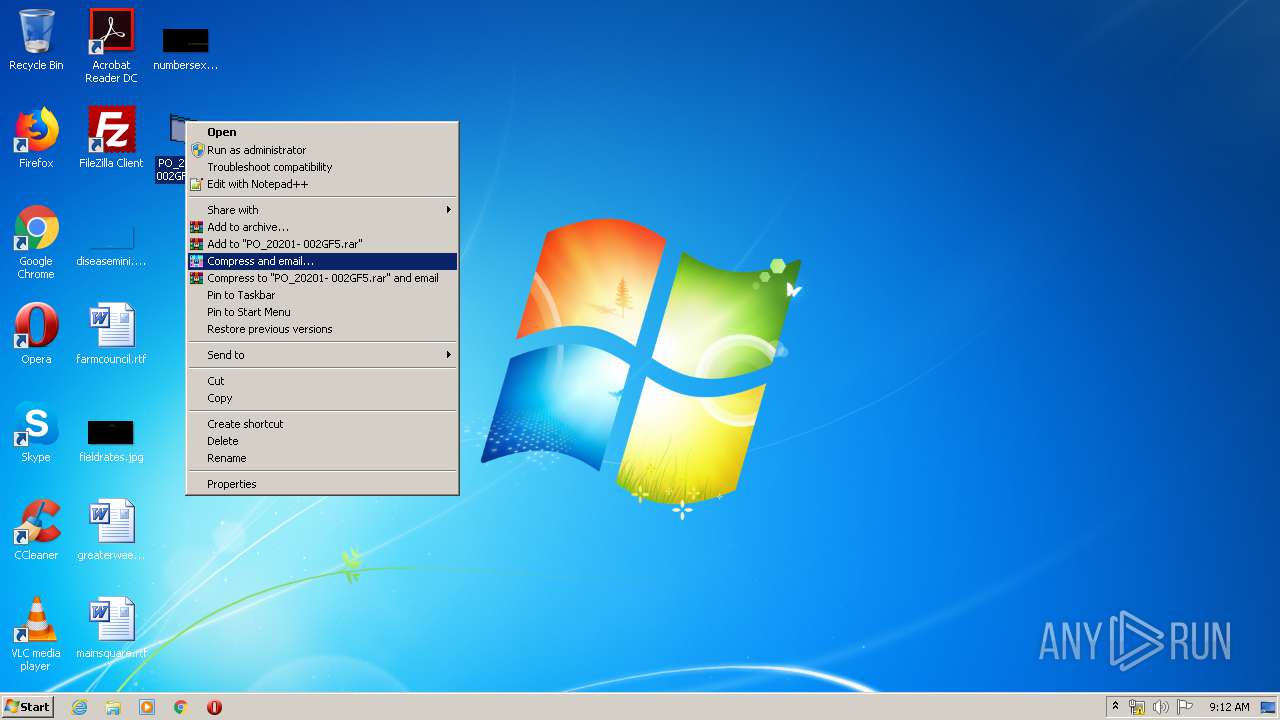
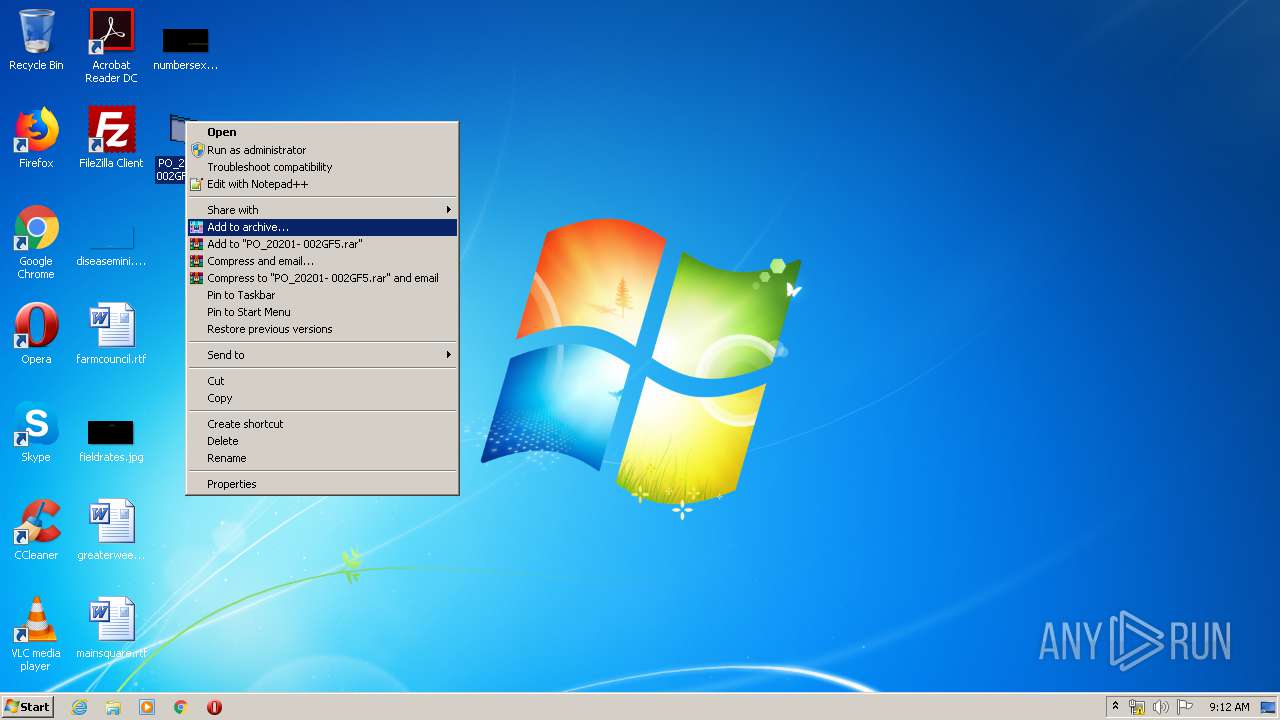
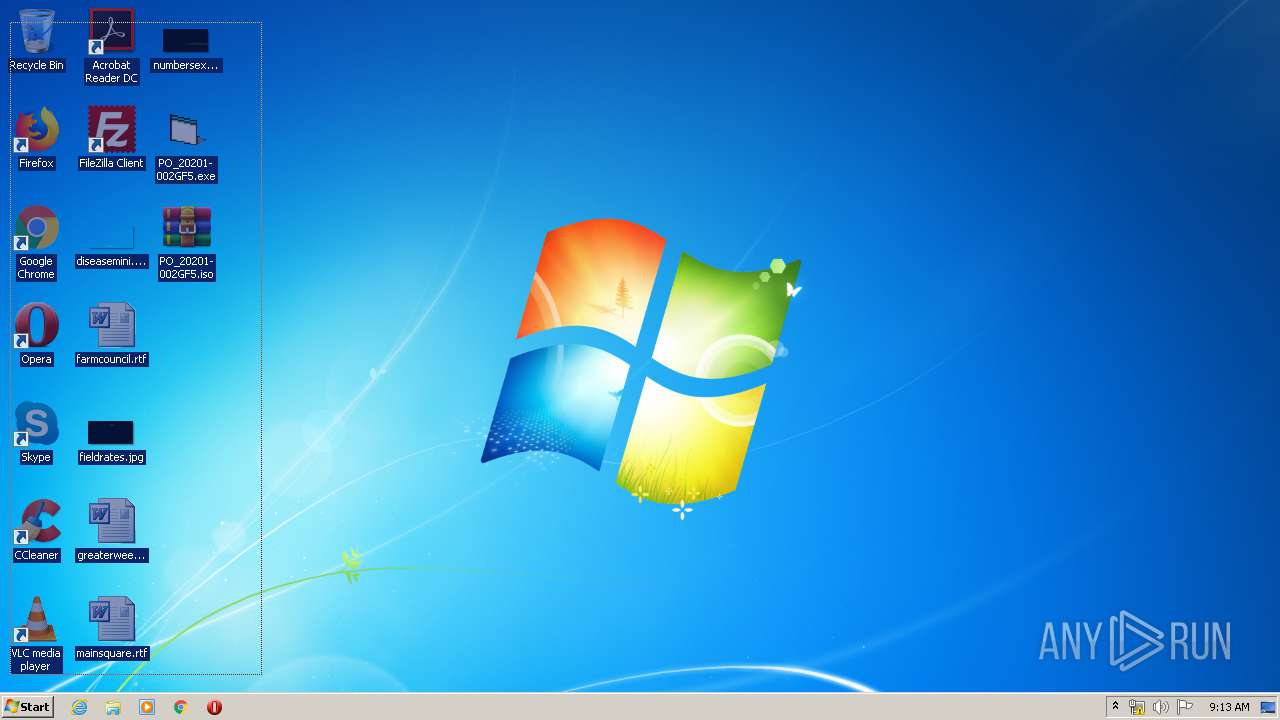
Manual execution by user
- WinRAR.exe (PID: 3732)
- PO_20201- 002GF5.exe (PID: 2612)
- PO_20201- 002GF5.exe (PID: 2904)
Reads settings of System Certificates
- RegAsm.exe (PID: 1196)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 304)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
56
Monitored processes
6
Malicious processes
3
Suspicious processes
0
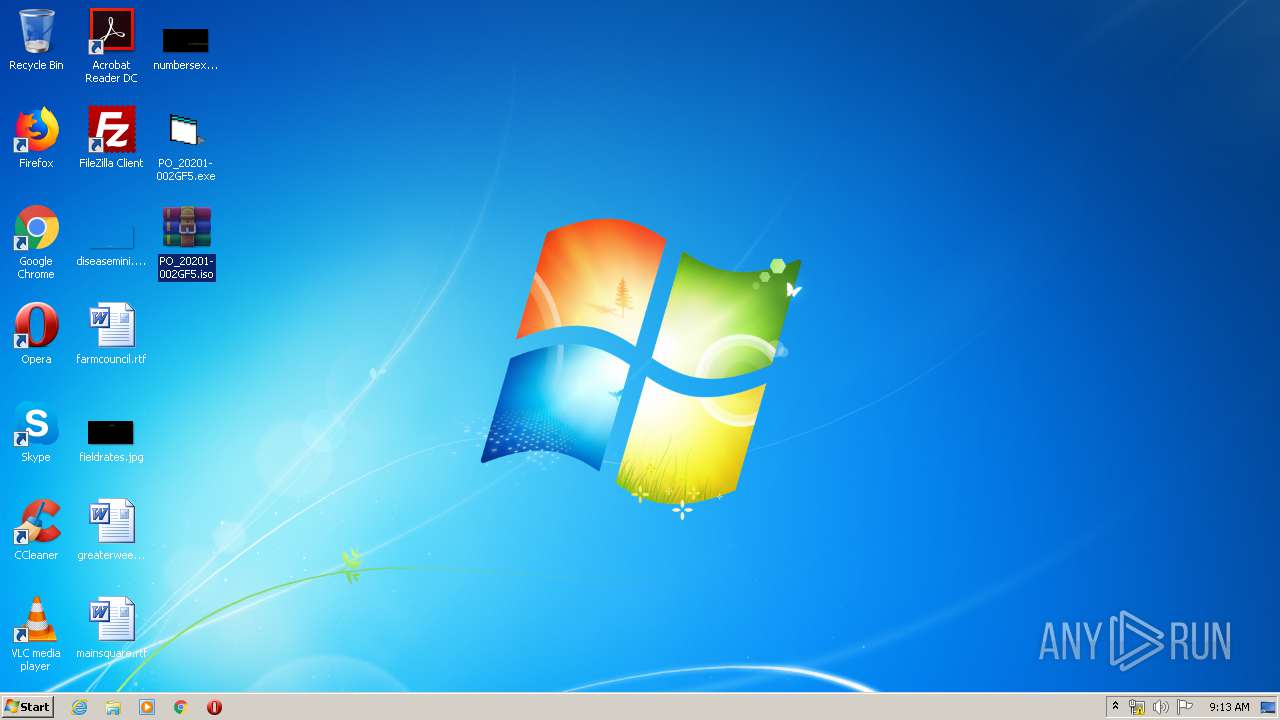
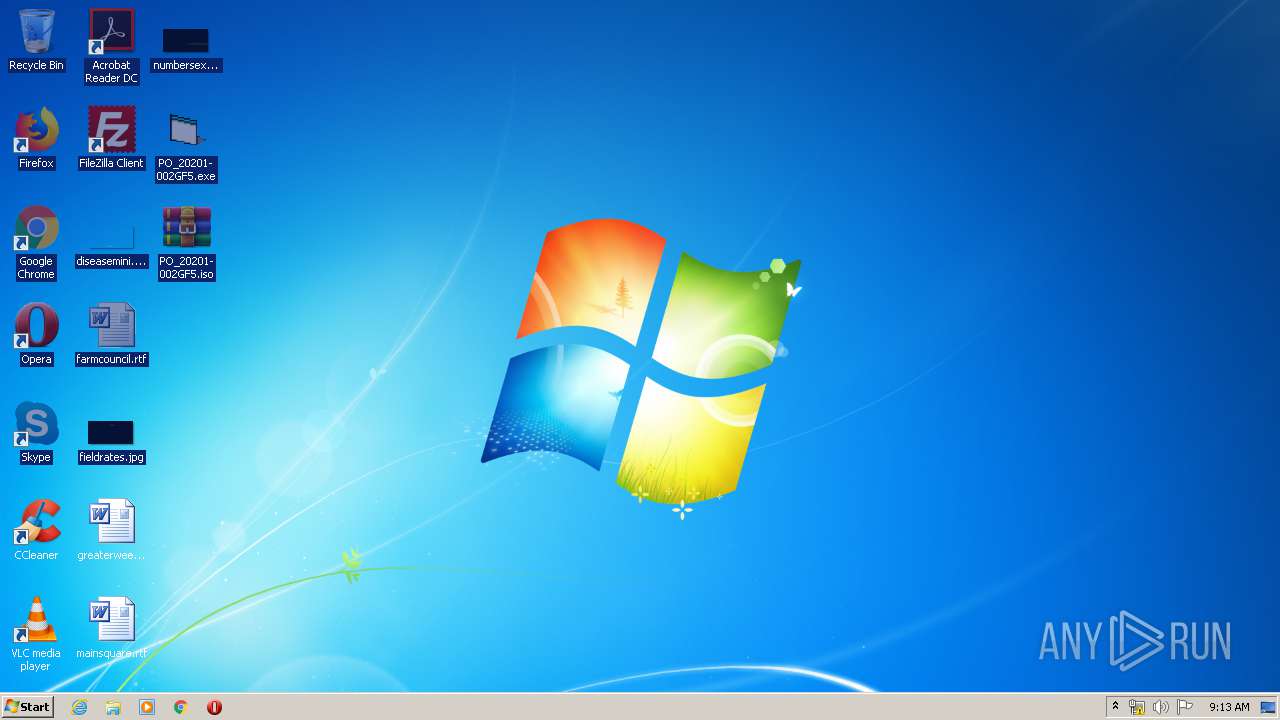
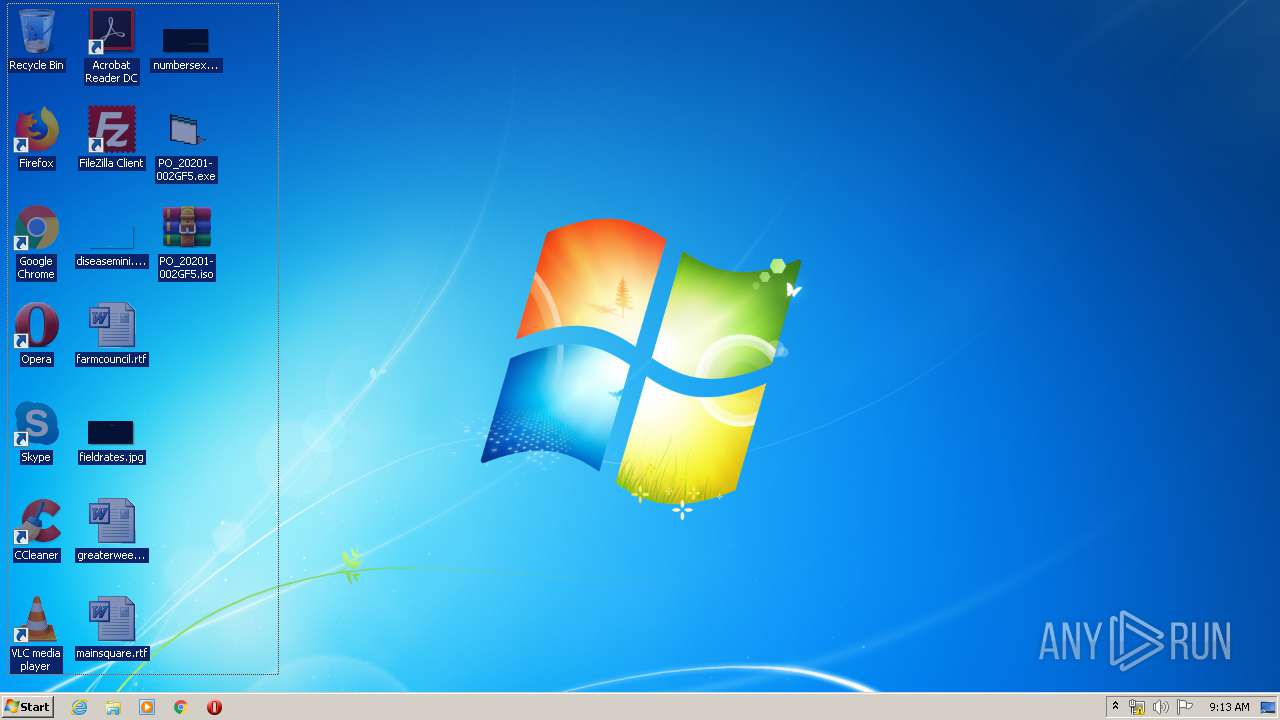
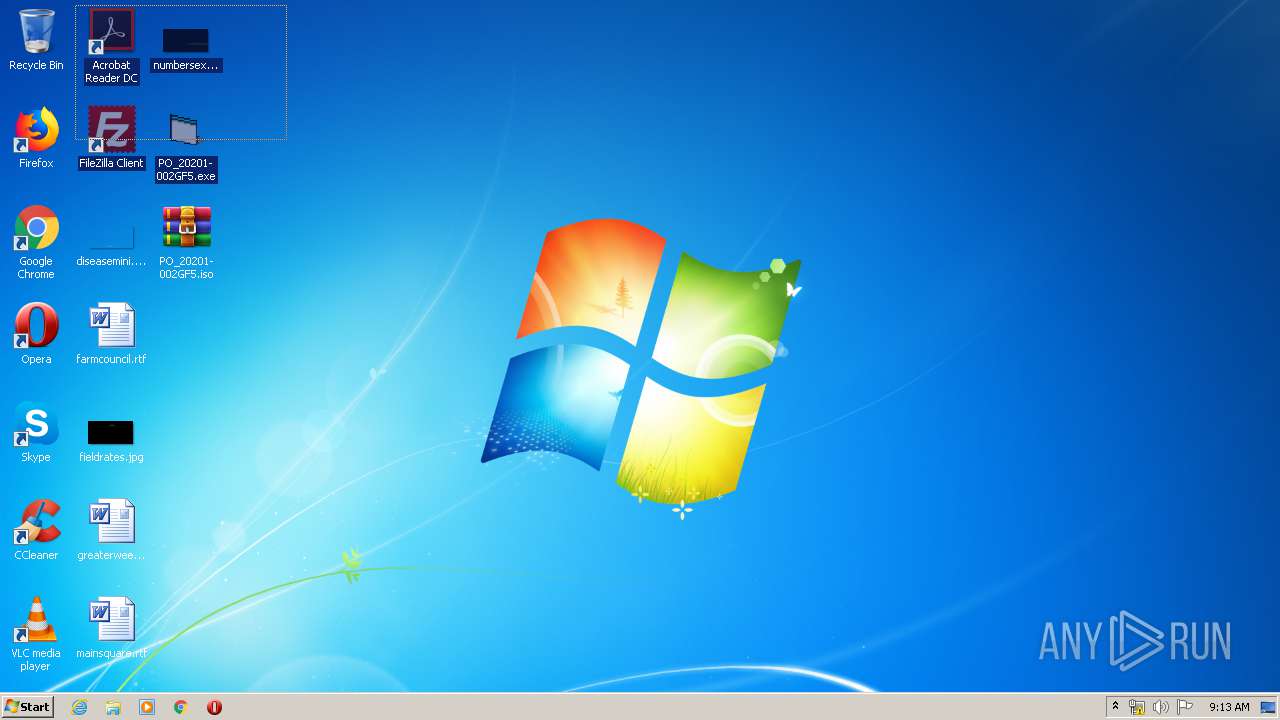
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\3fcd0cae-14e0-4245-da87-08d7d260c16c219e8e00-5909-9766-d12f-e6a7666b7525.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 1196 | "C:\Users\admin\Desktop\PO_20201- 002GF5.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | PO_20201- 002GF5.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2208 | "C:\Users\admin\Desktop\PO_20201- 002GF5.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | PO_20201- 002GF5.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2612 | "C:\Users\admin\Desktop\PO_20201- 002GF5.exe" | C:\Users\admin\Desktop\PO_20201- 002GF5.exe | explorer.exe | ||||||||||||
User: admin Company: SMARt Integrity Level: HIGH Description: AALNDINGES Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2904 | "C:\Users\admin\Desktop\PO_20201- 002GF5.exe" | C:\Users\admin\Desktop\PO_20201- 002GF5.exe | explorer.exe | ||||||||||||
User: admin Company: SMARt Integrity Level: HIGH Description: AALNDINGES Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3732 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\PO_20201- 002GF5.iso" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
3 634
Read events
1 772
Write events
1 839
Delete events
23
Modification events
| (PID) Process: | (304) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (304) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (304) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (304) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (304) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (304) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (304) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (304) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (304) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (304) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
1
Suspicious files
9
Text files
28
Unknown types
4
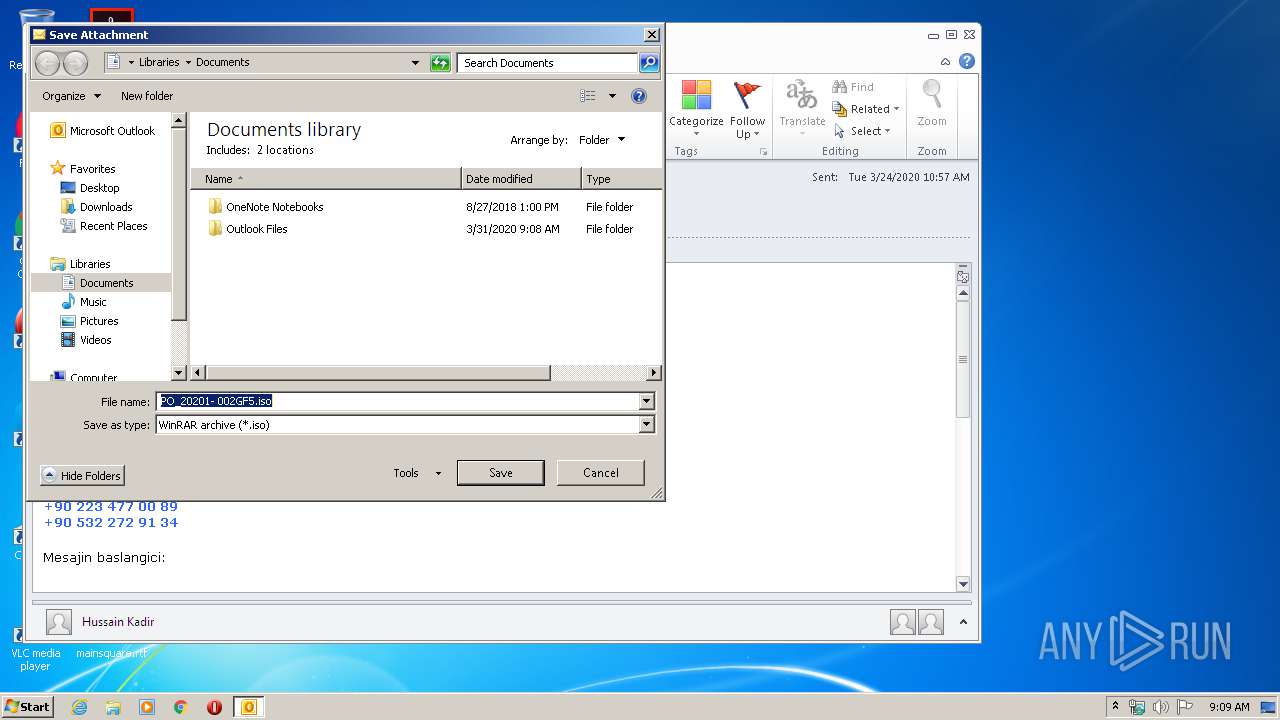
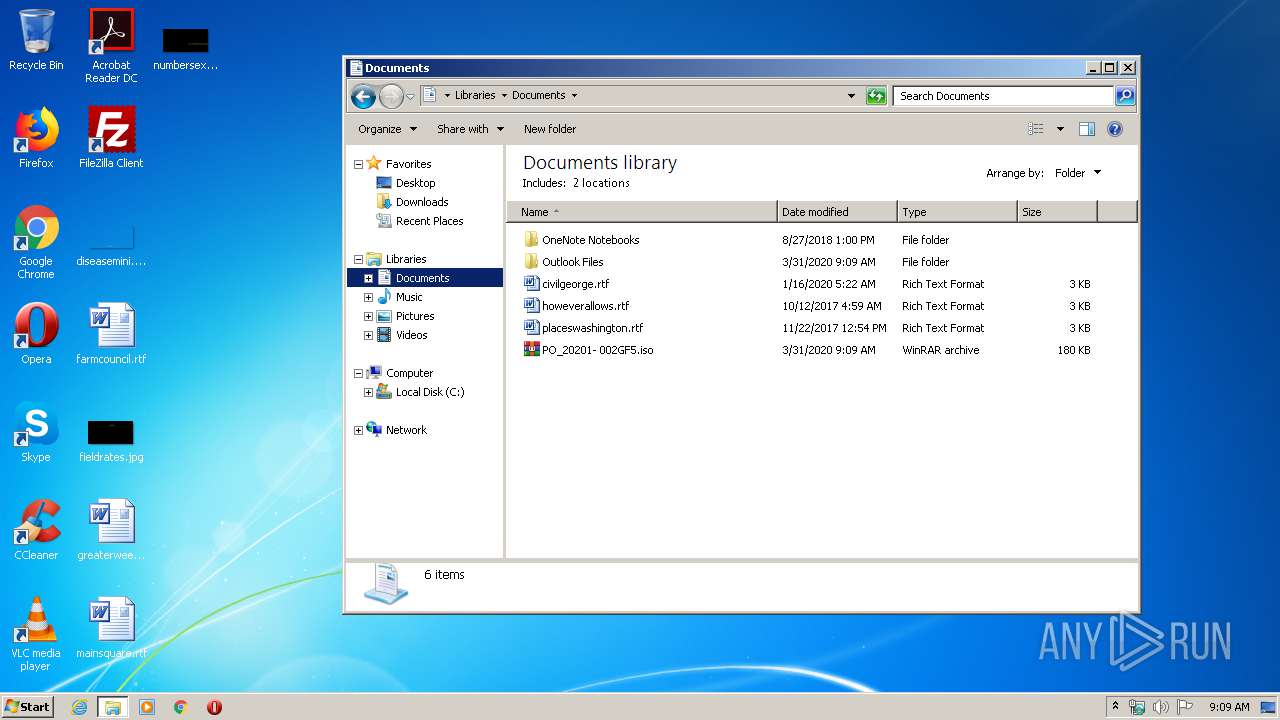
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 304 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR6B64.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 304 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp6DC7.tmp | — | |
MD5:— | SHA256:— | |||
| 304 | OUTLOOK.EXE | C:\Users\admin\Documents\PO_20201- 002GF5.iso\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 304 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~WRD0000.tmp | — | |
MD5:— | SHA256:— | |||
| 304 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{AD5F9557-4F67-4617-8202-1C8E0716D9BC}.tmp | — | |
MD5:— | SHA256:— | |||
| 304 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Outlook\NoMail.srs | srs | |
MD5:— | SHA256:— | |||
| 304 | OUTLOOK.EXE | C:\Users\admin\Documents\PO_20201- 002GF5.iso | compressed | |
MD5:— | SHA256:— | |||
| 1196 | RegAsm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | der | |
MD5:— | SHA256:— | |||
| 304 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\TZN3GBIP\PO_20201- 002GF5.iso | compressed | |
MD5:— | SHA256:— | |||
| 1196 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\CabFADE.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
5
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
304 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
1196 | RegAsm.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1196 | RegAsm.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDL%2FQslYWVuogIAAAAAXGdc | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
304 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
1196 | RegAsm.exe | 216.58.207.78:443 | drive.google.com | Google Inc. | US | whitelisted |
2208 | RegAsm.exe | 216.58.207.78:443 | drive.google.com | Google Inc. | US | whitelisted |
1196 | RegAsm.exe | 172.217.23.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
drive.google.com |
| shared |
ocsp.pki.goog |
| whitelisted |