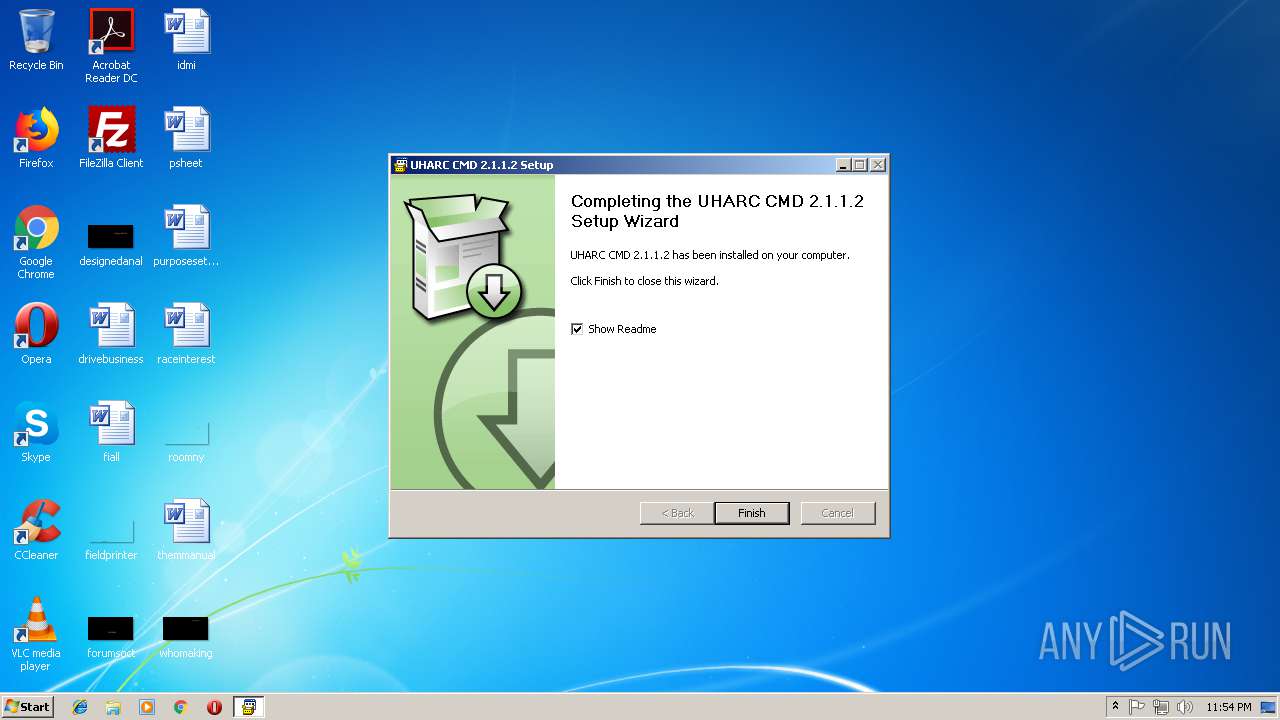
| File name: | uharc-cmd-install.exe |
| Full analysis: | https://app.any.run/tasks/8ab9ca52-c67d-4be1-ae78-8cc344f8ca9c |
| Verdict: | Malicious activity |
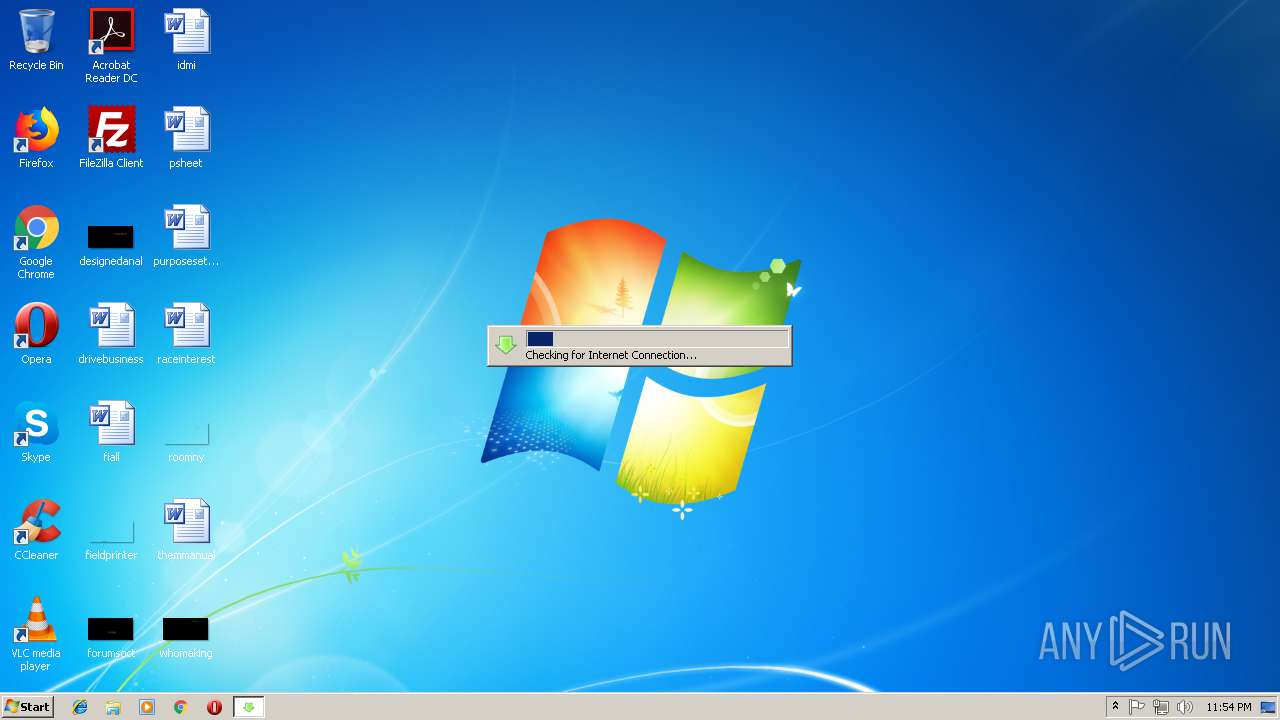
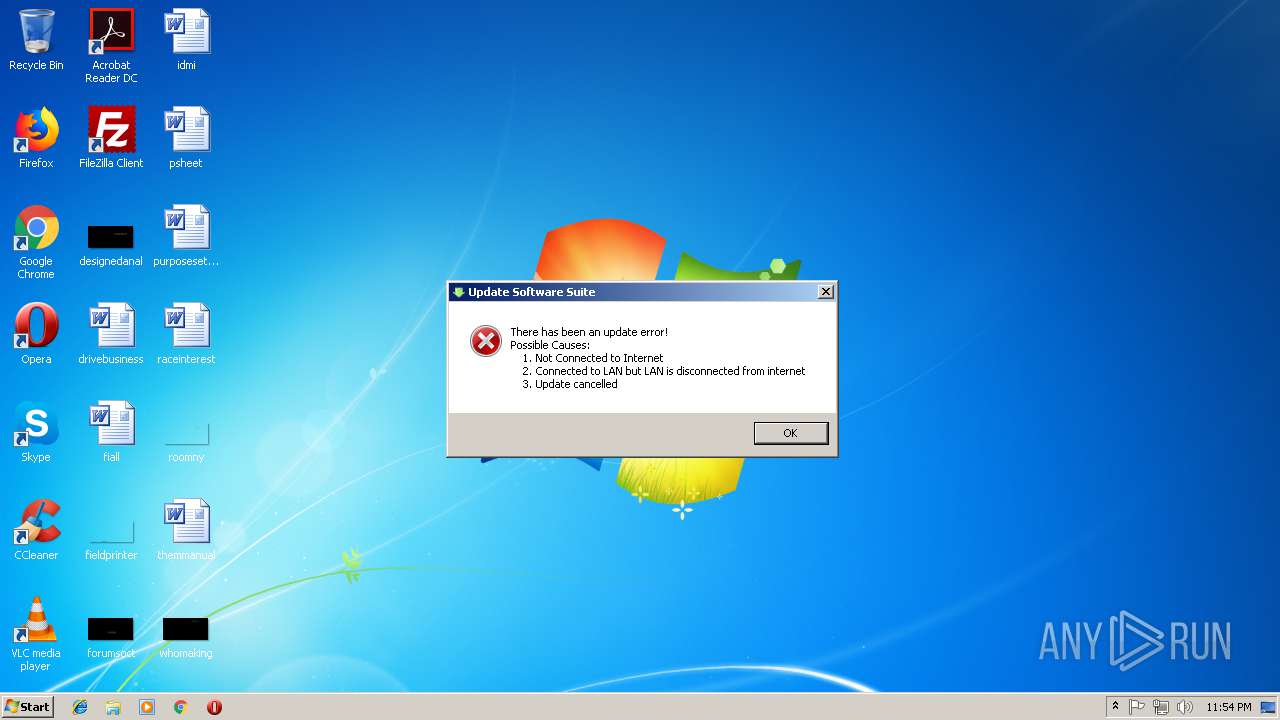
| Analysis date: | September 11, 2018, 22:53:51 |
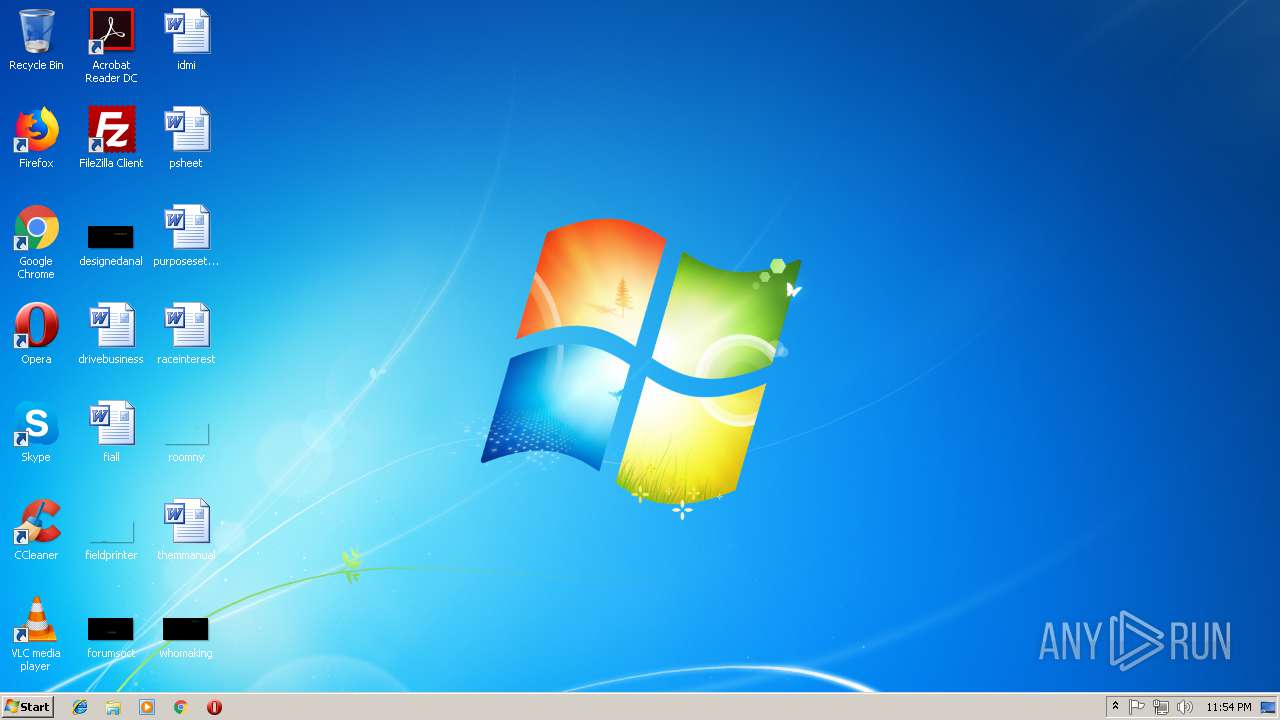
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
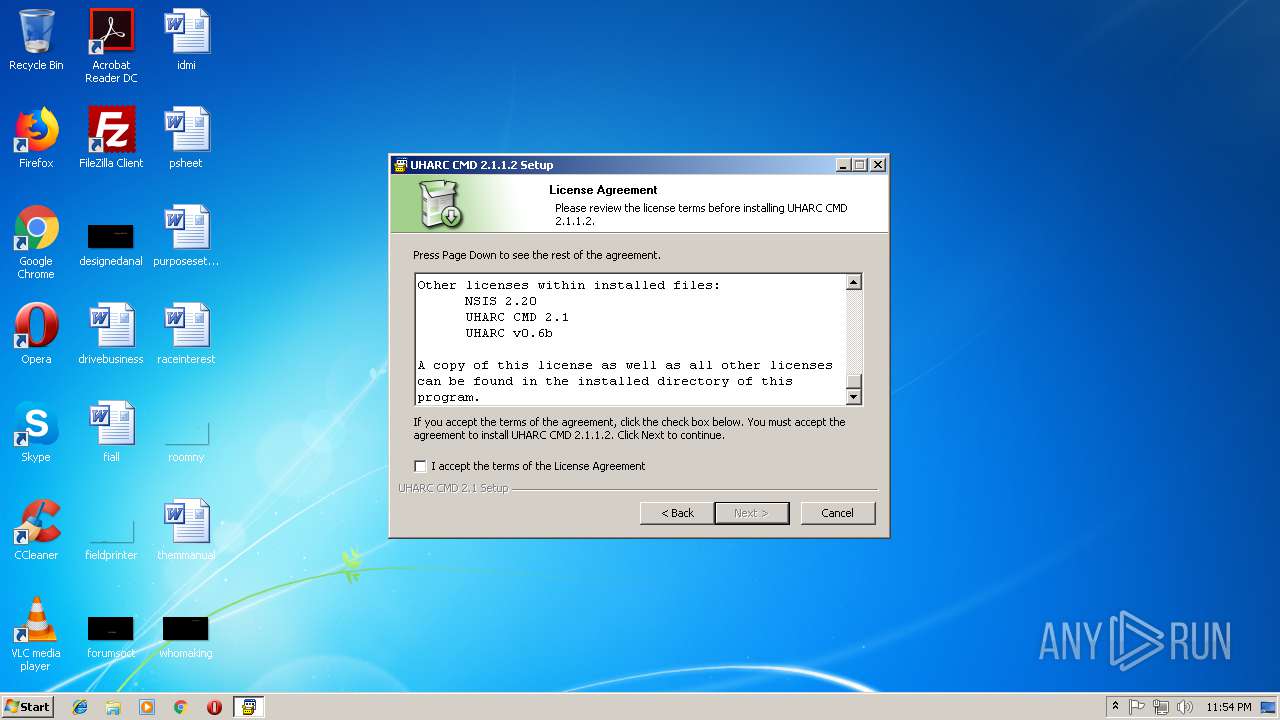
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | D96590E15007750187A77077192073B7 |
| SHA1: | 341698FEC91174CEA6786DC6692C8CDDD3AFF95B |
| SHA256: | 24C16F37D16FCC9BA5942242CF1E6A904591698387B4A1688F7CFEE1E012726C |
| SSDEEP: | 49152:SCT8eBy530PbGlABhI4J1rGNsP252ye2ZoXCBcgFUBgDib77V:SCvio7II1zO529woXCWgRD477V |
MALICIOUS
Loads dropped or rewritten executable
- uharc-cmd-install.exe (PID: 3324)
- update.exe (PID: 3684)
- settings.exe (PID: 1360)
- update.exe (PID: 3672)
Application was dropped or rewritten from another process
- update.exe (PID: 3684)
- settings.exe (PID: 1348)
- settings.exe (PID: 1360)
- update.exe (PID: 3672)
SUSPICIOUS
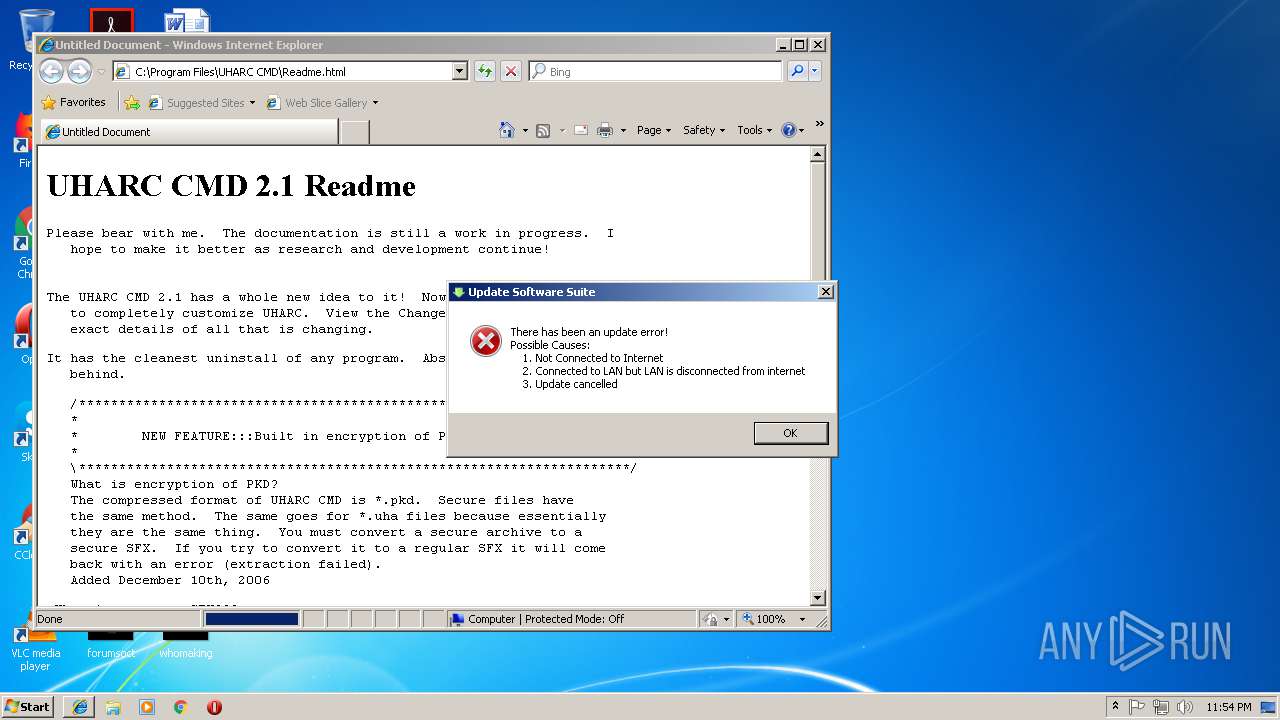
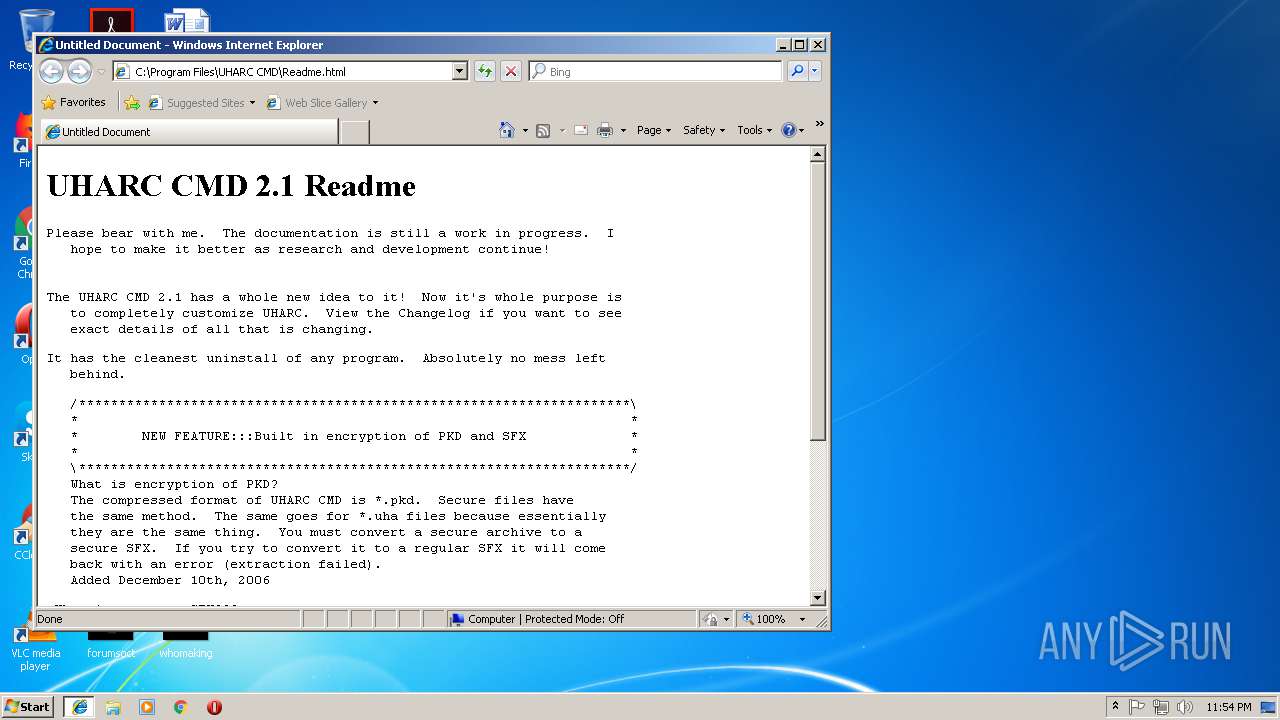
Starts Internet Explorer
- uharc-cmd-install.exe (PID: 3324)
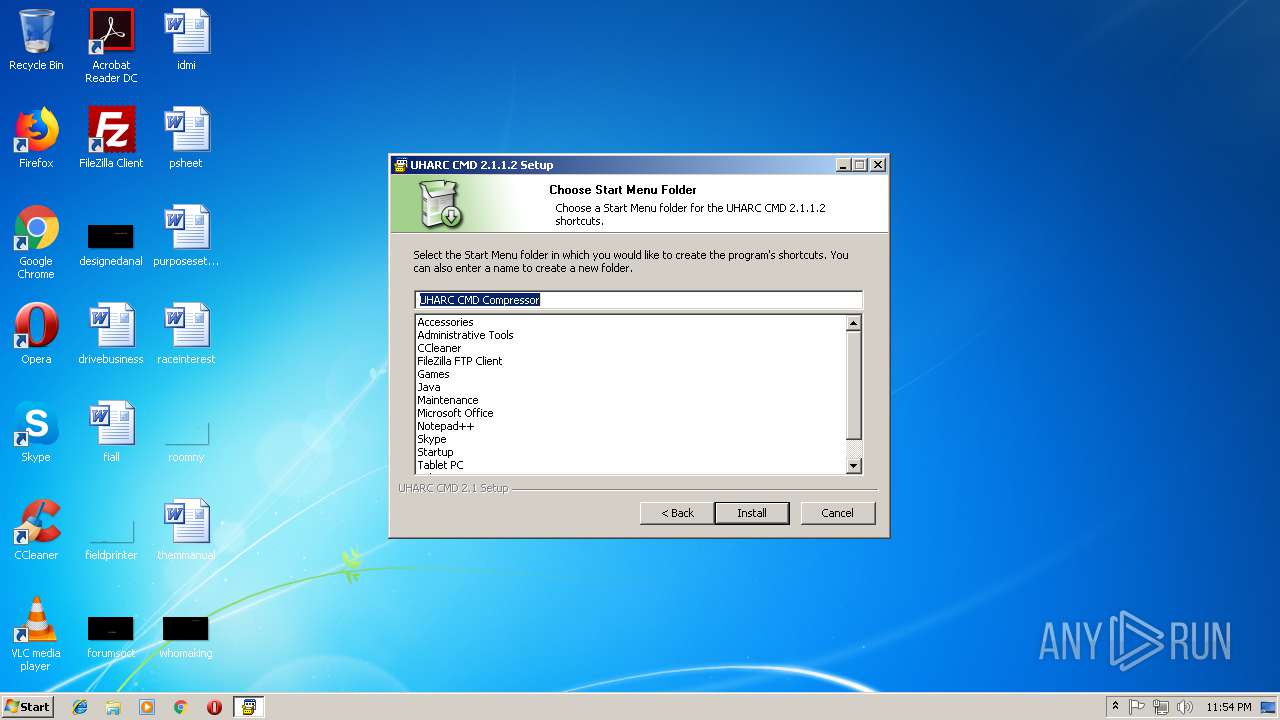
Modifies the open verb of a shell class
- uharc-cmd-install.exe (PID: 3324)
Creates a software uninstall entry
- uharc-cmd-install.exe (PID: 3324)
Executable content was dropped or overwritten
- uharc-cmd-install.exe (PID: 3324)
- update.exe (PID: 3684)
- settings.exe (PID: 1360)
- update.exe (PID: 3672)
Creates files in the program directory
- uharc-cmd-install.exe (PID: 3324)
Check for Java to be installed
- iexplore.exe (PID: 1364)
INFO
Application launched itself
- iexplore.exe (PID: 1364)
Changes internet zones settings
- iexplore.exe (PID: 1364)
Reads internet explorer settings
- iexplore.exe (PID: 3464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:06:06 23:41:54+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
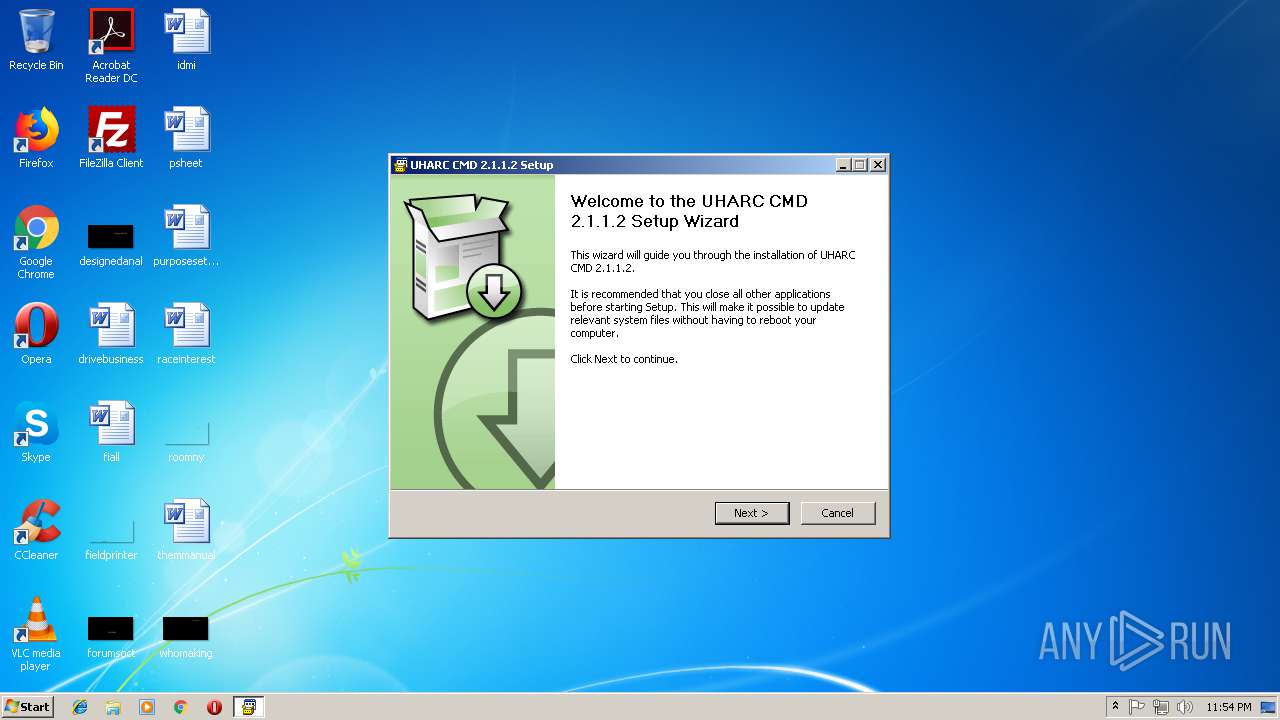
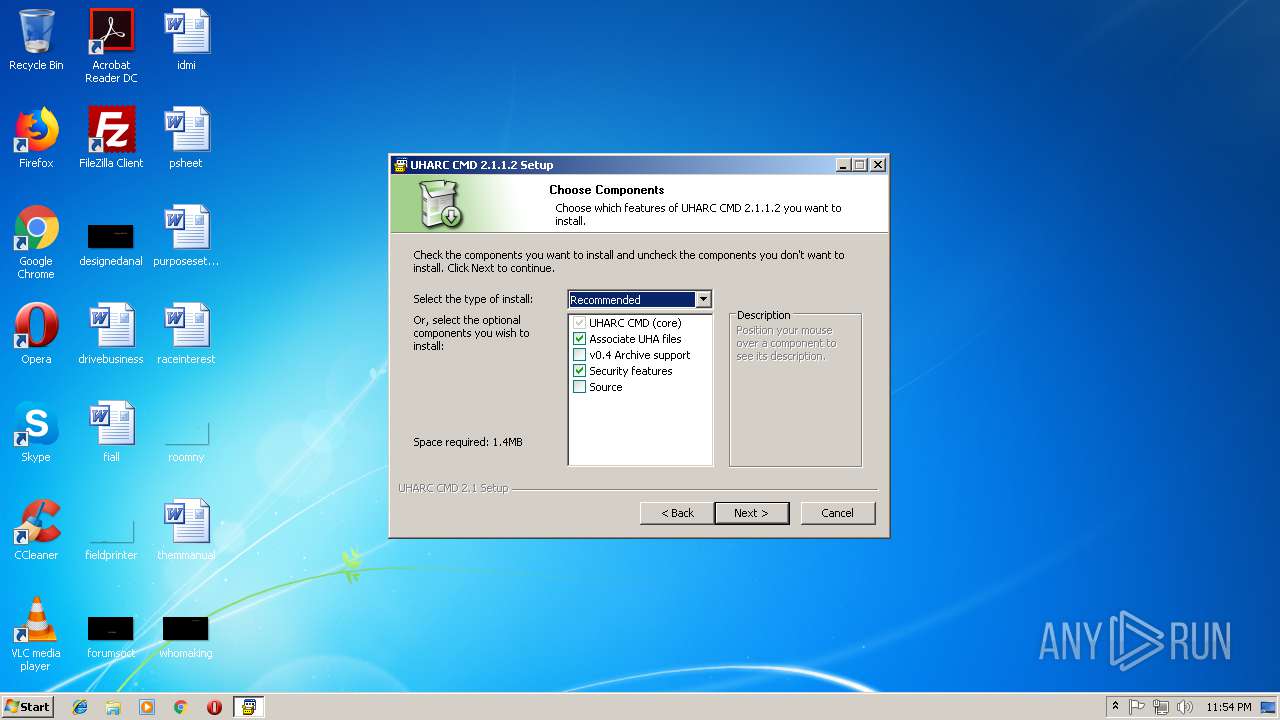
| FileVersionNumber: | 2.1.1.2 |
| ProductVersionNumber: | 2.1.1.2 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
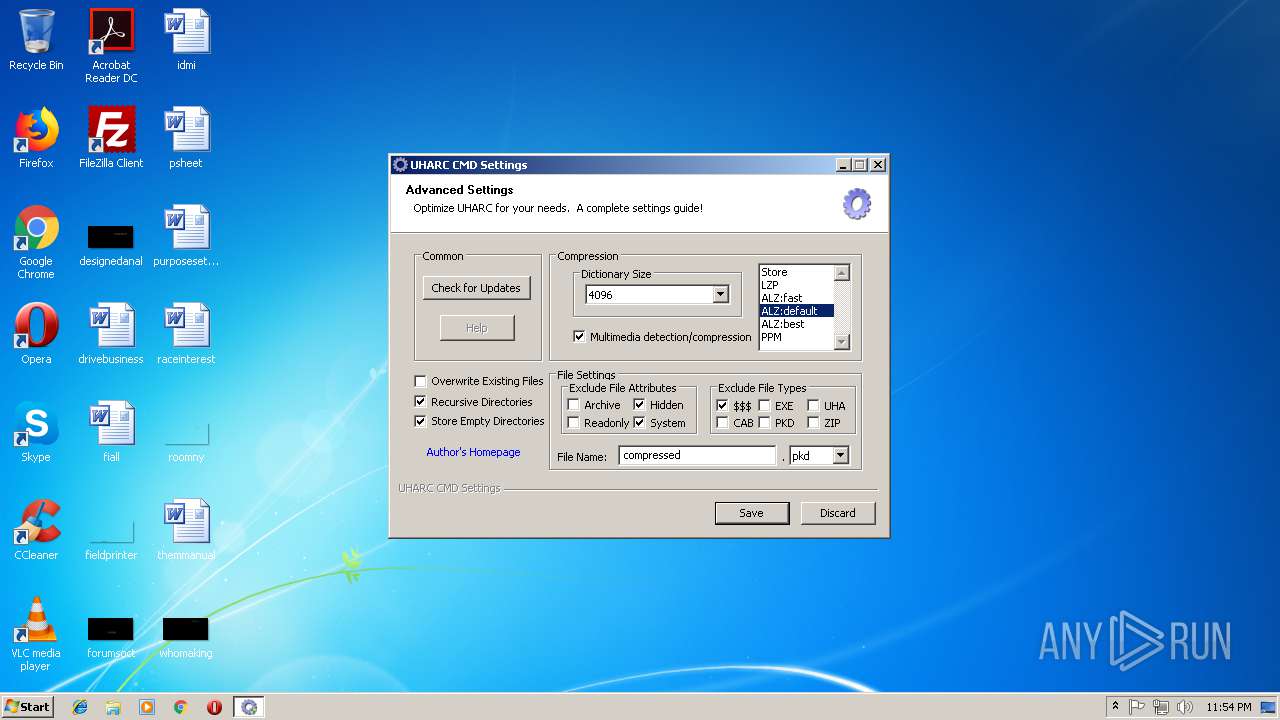
| Comments: | A commandline compressor rebuilt for the Windows GUI |
| CompanyName: | By Sam Gleske |
| FileDescription: | UHARC CMD Installer |
| FileVersion: | 2.1.1.2 |
| InternalName: | uharc |
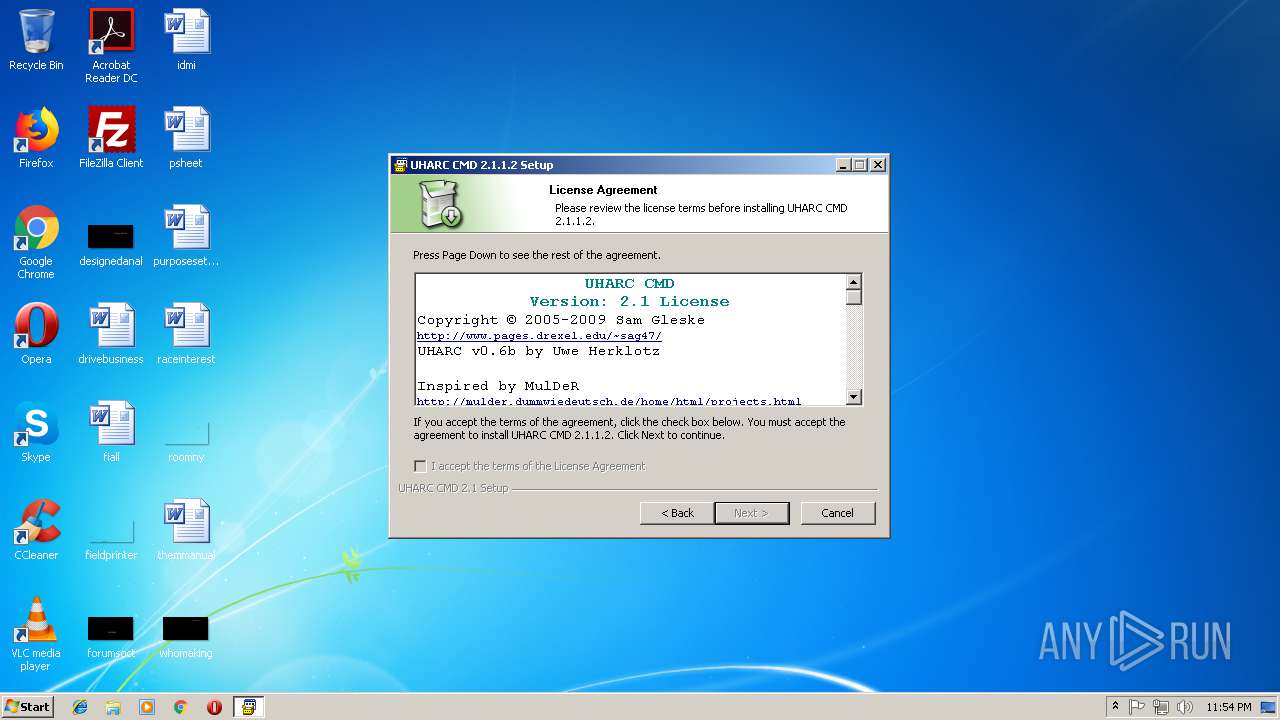
| LegalCopyright: | © Sam Gleske |
| LegalTrademarks: | All shell edits are copyrighted to Sam Gleske |
| OriginalFileName: | uharc-cmd-install.exe |
| ProductName: | UHARC CMD 2.1.1.2 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Jun-2009 21:41:54 |
| Detected languages: |
|
| Comments: | A commandline compressor rebuilt for the Windows GUI |
| CompanyName: | By Sam Gleske |
| FileDescription: | UHARC CMD Installer |
| FileVersion: | 2.1.1.2 |
| InternalName: | uharc |
| LegalCopyright: | © Sam Gleske |
| LegalTrademarks: | All shell edits are copyrighted to Sam Gleske |
| OriginalFilename: | uharc-cmd-install.exe |
| ProductName: | UHARC CMD 2.1.1.2 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 06-Jun-2009 21:41:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A5A | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4177 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18163 |
.data | 0x00009000 | 0x0001AF98 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70903 |
.ndata | 0x00024000 | 0x0000A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002E000 | 0x000037E8 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.0055 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10609 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.23843 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 1.33371 | 1384 | UNKNOWN | English - United States | RT_ICON |
4 | 3.48487 | 744 | UNKNOWN | English - United States | RT_ICON |
5 | 3.50101 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.77728 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.70992 | 344 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.67385 | 512 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
109 | 2.70146 | 212 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
48
Monitored processes
8
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
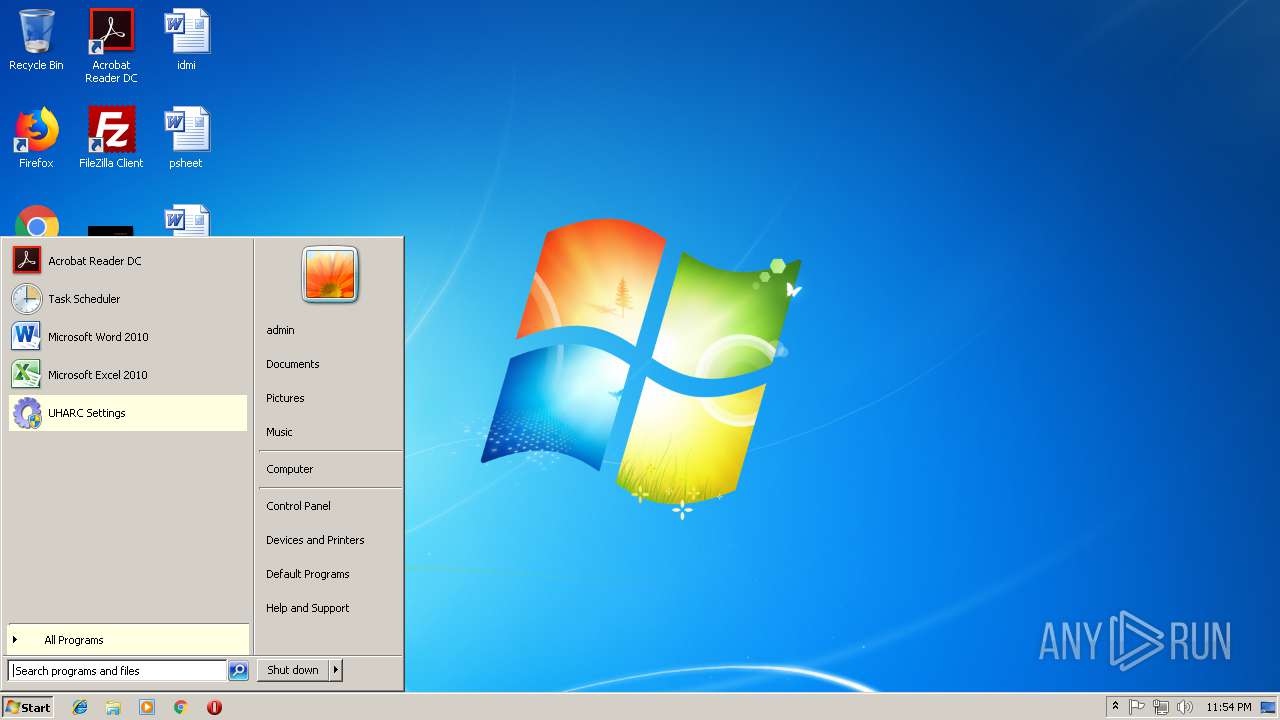
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
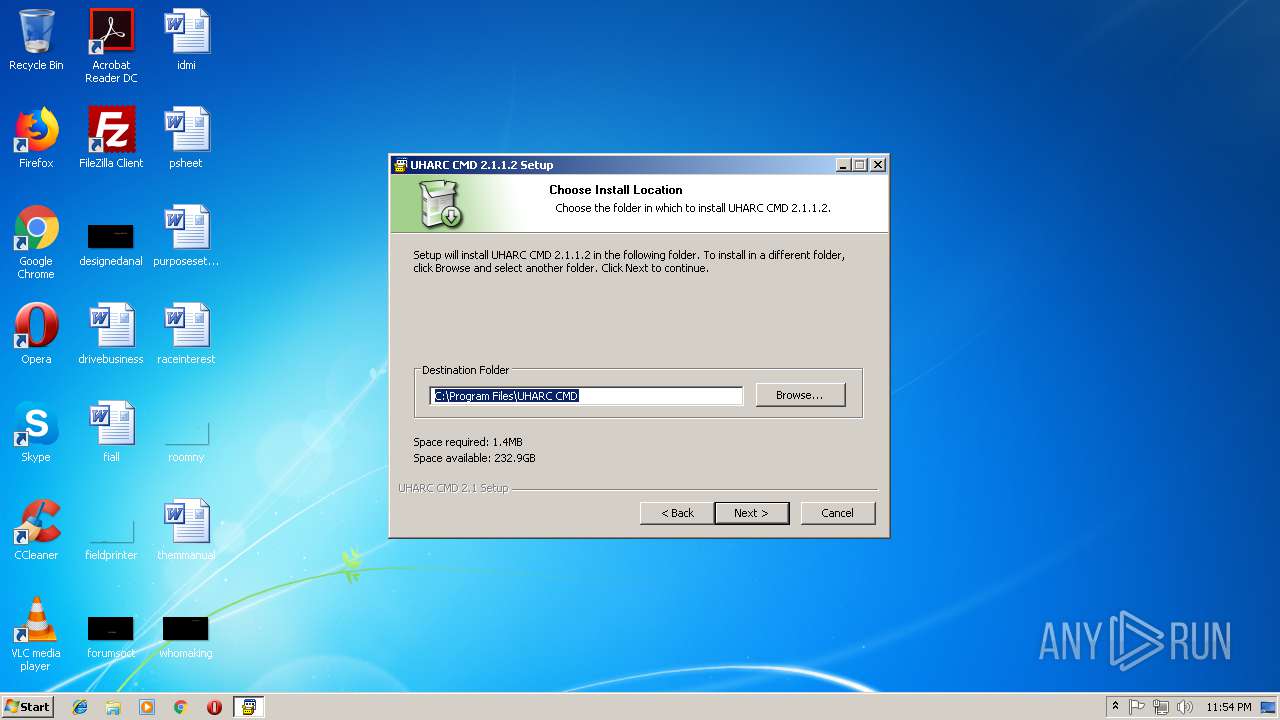
| 1348 | "C:\Program Files\UHARC CMD\settings.exe" | C:\Program Files\UHARC CMD\settings.exe | — | explorer.exe | |||||||||||
User: admin Company: By Sam Gleske Integrity Level: MEDIUM Description: UHARC CMD Settings Exit code: 3221226540 Version: 2.1 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\UHARC CMD\settings.exe" | C:\Program Files\UHARC CMD\settings.exe | explorer.exe | ||||||||||||
User: admin Company: By Sam Gleske Integrity Level: HIGH Description: UHARC CMD Settings Exit code: 0 Version: 2.1 Modules
| |||||||||||||||
| 1364 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | uharc-cmd-install.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1968 | "C:\Users\admin\AppData\Local\Temp\uharc-cmd-install.exe" | C:\Users\admin\AppData\Local\Temp\uharc-cmd-install.exe | — | explorer.exe | |||||||||||
User: admin Company: By Sam Gleske Integrity Level: MEDIUM Description: UHARC CMD Installer Exit code: 3221226540 Version: 2.1.1.2 Modules
| |||||||||||||||
| 3324 | "C:\Users\admin\AppData\Local\Temp\uharc-cmd-install.exe" | C:\Users\admin\AppData\Local\Temp\uharc-cmd-install.exe | explorer.exe | ||||||||||||
User: admin Company: By Sam Gleske Integrity Level: HIGH Description: UHARC CMD Installer Exit code: 0 Version: 2.1.1.2 Modules
| |||||||||||||||
| 3464 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1364 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3672 | "C:\Program Files\UHARC CMD\update.exe" SW_SHOWNORMAL | C:\Program Files\UHARC CMD\update.exe | settings.exe | ||||||||||||
User: admin Company: By Sam Gleske Integrity Level: HIGH Description: Update Software Exit code: 2 Version: 1.0 Modules
| |||||||||||||||
| 3684 | "C:\Program Files\UHARC CMD\update.exe" SW_SHOWNORMAL | C:\Program Files\UHARC CMD\update.exe | uharc-cmd-install.exe | ||||||||||||
User: admin Company: By Sam Gleske Integrity Level: HIGH Description: Update Software Exit code: 2 Version: 1.0 Modules
| |||||||||||||||
Total events
899
Read events
748
Write events
149
Delete events
2
Modification events
| (PID) Process: | (3324) uharc-cmd-install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\*\shell\uharccomp |
| Operation: | write | Name: | |
Value: Compress with UHARC | |||
| (PID) Process: | (3324) uharc-cmd-install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\*\shell\uharccomp\command |
| Operation: | write | Name: | |
Value: "C:\Program Files\UHARC CMD\bin\uharc.exe" a -aeH+S+ -ed+ -m2 -md4096 -mm+ -op -y- -r+ "compressed.pkd" !*.$$ | |||
| (PID) Process: | (3324) uharc-cmd-install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.$$ |
| Operation: | write | Name: | |
Value: UHARC.Compress | |||
| (PID) Process: | (3324) uharc-cmd-install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.pkd |
| Operation: | write | Name: | |
Value: UHARC.CMD | |||
| (PID) Process: | (3324) uharc-cmd-install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Directory\shell\uharccomp |
| Operation: | write | Name: | |
Value: Compress with UHARC | |||
| (PID) Process: | (3324) uharc-cmd-install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Directory\shell\uharccomp\command |
| Operation: | write | Name: | |
Value: "C:\Program Files\UHARC CMD\bin\uharc.exe" a -aeH+S+ -ed+ -m2 -md4096 -mm+ -op -y- -r+ "compressed.pkd" !*.$$ | |||
| (PID) Process: | (3324) uharc-cmd-install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\UHARC.CMD |
| Operation: | write | Name: | |
Value: Compressed UHARC file | |||
| (PID) Process: | (3324) uharc-cmd-install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\UHARC.CMD\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Program Files\UHARC CMD\icons\uharc.ico | |||
| (PID) Process: | (3324) uharc-cmd-install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\UHARC.CMD\shell\open3 |
| Operation: | write | Name: | |
Value: Decompress files here... | |||
| (PID) Process: | (3324) uharc-cmd-install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\UHARC.CMD\shell\open3\command |
| Operation: | write | Name: | |
Value: "C:\Program Files\UHARC CMD\bin\uharc.exe" x "%1" | |||
Executable files
27
Suspicious files
3
Text files
136
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3324 | uharc-cmd-install.exe | C:\Program Files\UHARC CMD\uharc.htm | html | |
MD5:— | SHA256:— | |||
| 3324 | uharc-cmd-install.exe | C:\Program Files\UHARC CMD\UHARC_license.txt | text | |
MD5:— | SHA256:— | |||
| 3324 | uharc-cmd-install.exe | C:\Users\admin\AppData\Local\Temp\nspA8C7.tmp\splash.bmp | image | |
MD5:— | SHA256:— | |||
| 3324 | uharc-cmd-install.exe | C:\Users\admin\AppData\Local\Temp\nspA8C7.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 3324 | uharc-cmd-install.exe | C:\Users\admin\AppData\Local\Temp\nspA8C7.tmp\modern-header.bmp | image | |
MD5:— | SHA256:— | |||
| 3324 | uharc-cmd-install.exe | C:\Users\admin\AppData\Local\Temp\nspA8C7.tmp\modern-wizard.bmp | image | |
MD5:— | SHA256:— | |||
| 3324 | uharc-cmd-install.exe | C:\Program Files\UHARC CMD\uharc_v0.6.htm | html | |
MD5:— | SHA256:— | |||
| 3324 | uharc-cmd-install.exe | C:\Program Files\UHARC CMD\NSIS_license.txt | text | |
MD5:— | SHA256:— | |||
| 3324 | uharc-cmd-install.exe | C:\Program Files\UHARC CMD\license.txt | text | |
MD5:— | SHA256:— | |||
| 3324 | uharc-cmd-install.exe | C:\Program Files\UHARC CMD\update.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
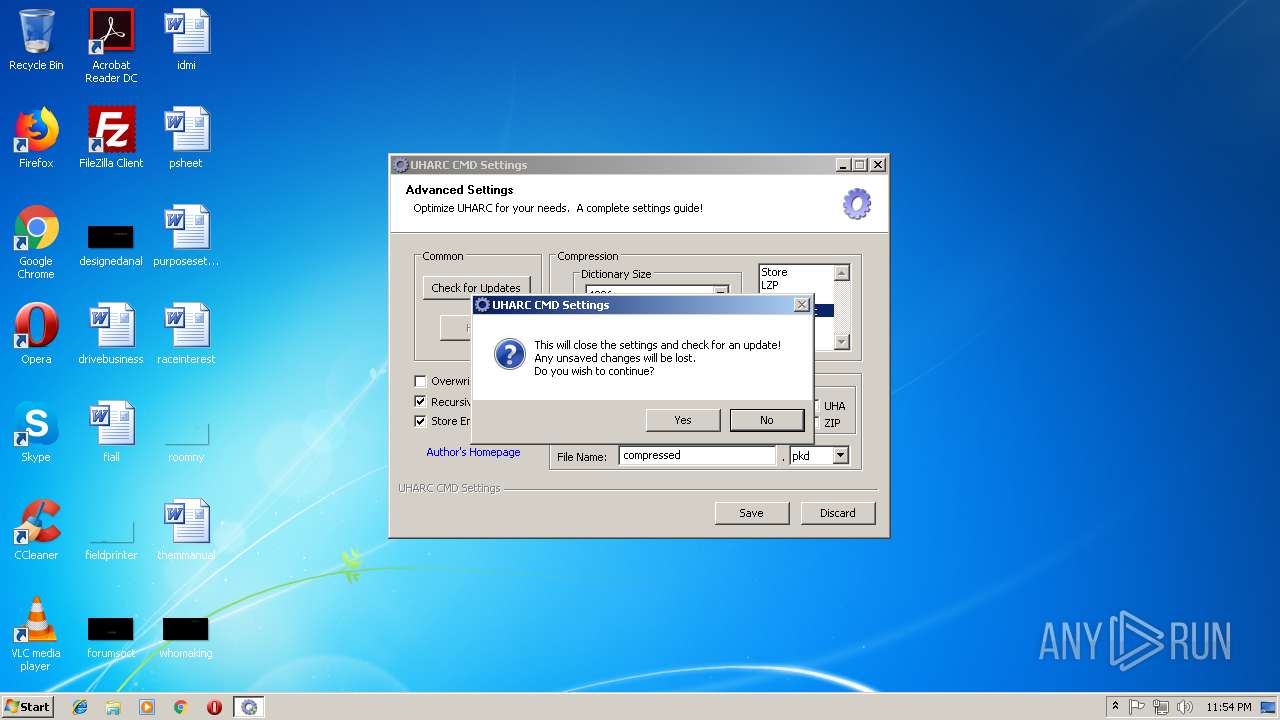
3684 | update.exe | GET | 404 | 144.118.24.33:80 | http://www.pages.drexel.edu/~sag47/uharc/version.ini | US | html | 222 b | suspicious |
1364 | iexplore.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | — | — | whitelisted |
3672 | update.exe | GET | 404 | 144.118.24.33:80 | http://www.pages.drexel.edu/~sag47/uharc/version.ini | US | html | 222 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3684 | update.exe | 144.118.24.33:80 | www.pages.drexel.edu | Drexel University | US | suspicious |
1364 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3672 | update.exe | 144.118.24.33:80 | www.pages.drexel.edu | Drexel University | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.pages.drexel.edu |
| suspicious |
www.bing.com |
| whitelisted |
Threats
2 ETPRO signatures available at the full report