| File name: | RuckZuck.exe |
| Full analysis: | https://app.any.run/tasks/4c3a9602-430c-447d-a6e2-73b32826baf5 |
| Verdict: | Malicious activity |
| Analysis date: | December 26, 2024, 20:43:11 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 981DA0EE9844D7162660EF9C3D60CB1E |
| SHA1: | D717E9C85C8666554C57672468B33979A131EC5D |
| SHA256: | 24BEBCA72D6CD5E03EF67AFFBF7328A58A928DD58371DCEF8287A3AC69F534C2 |
| SSDEEP: | 49152:LL1PAe8RLZ/2yCgLWb75NHb1HNj/7CcuAk0K8jbjSpxRyCOZsYEt+6e8N5/JpxKU:LLVT8RLZ/Mbzxl/7wAk0K0XSRDdYgeC9 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- RuckZuck.exe (PID: 1300)
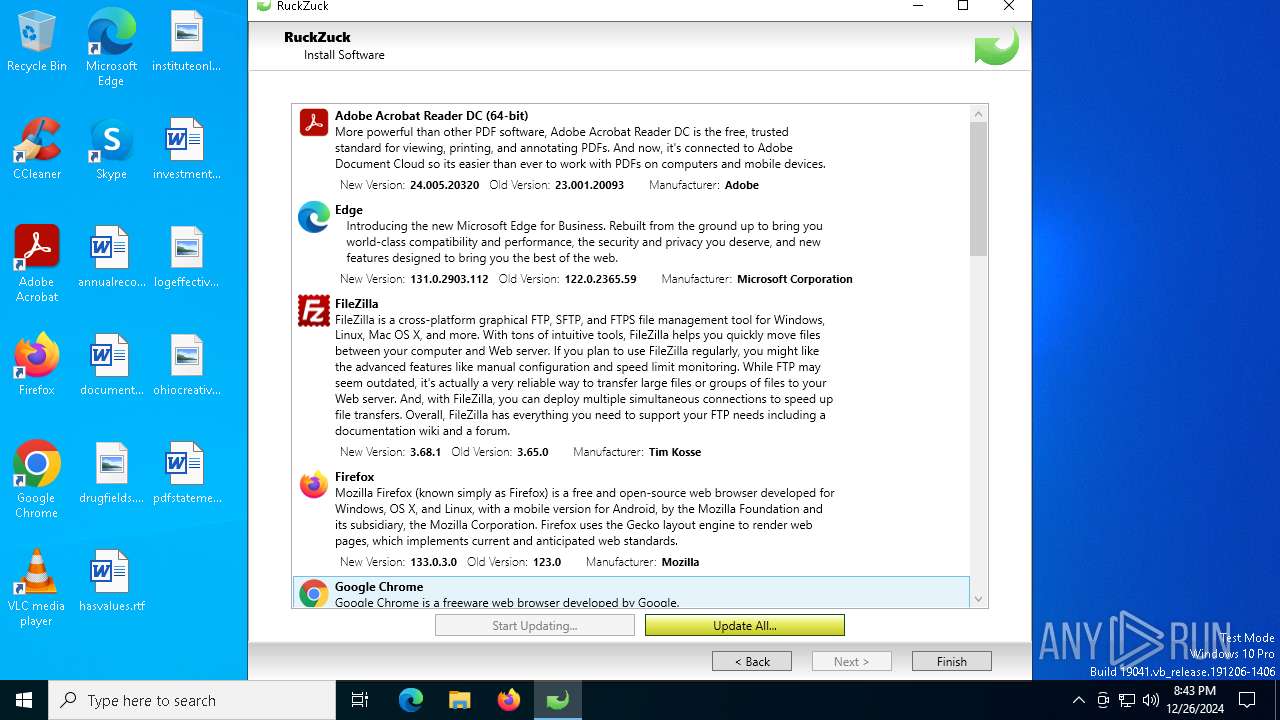
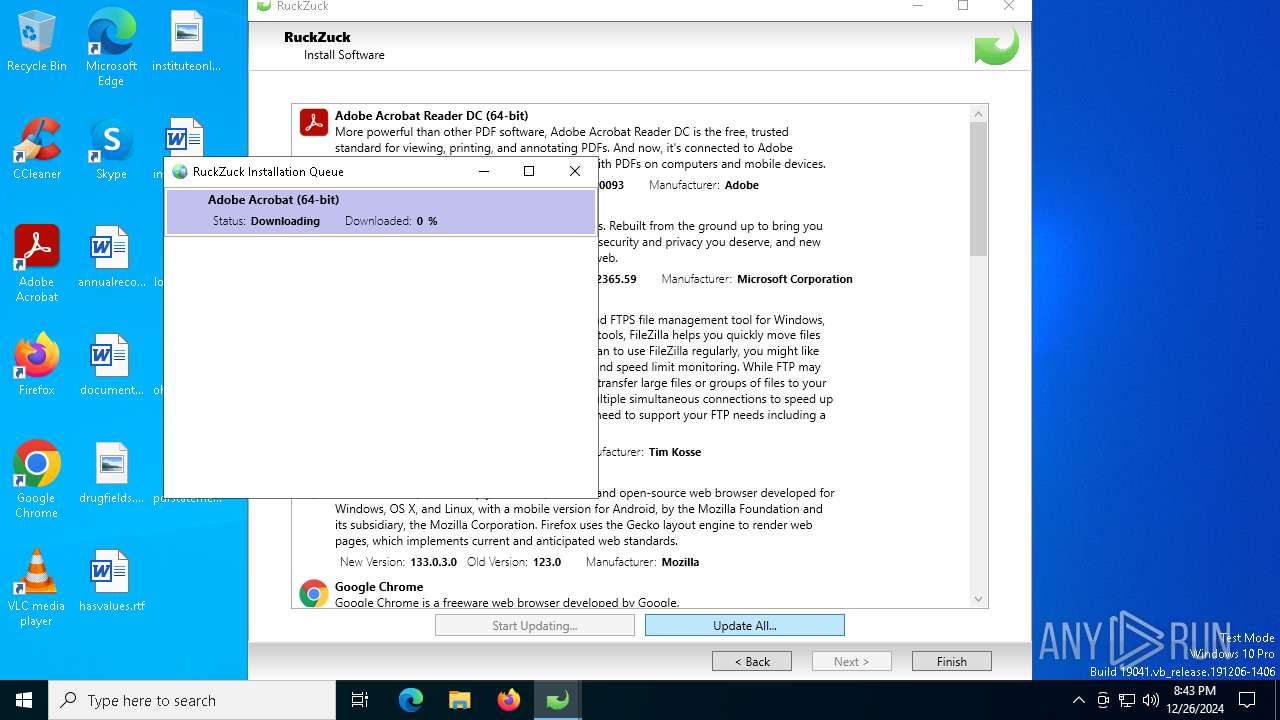
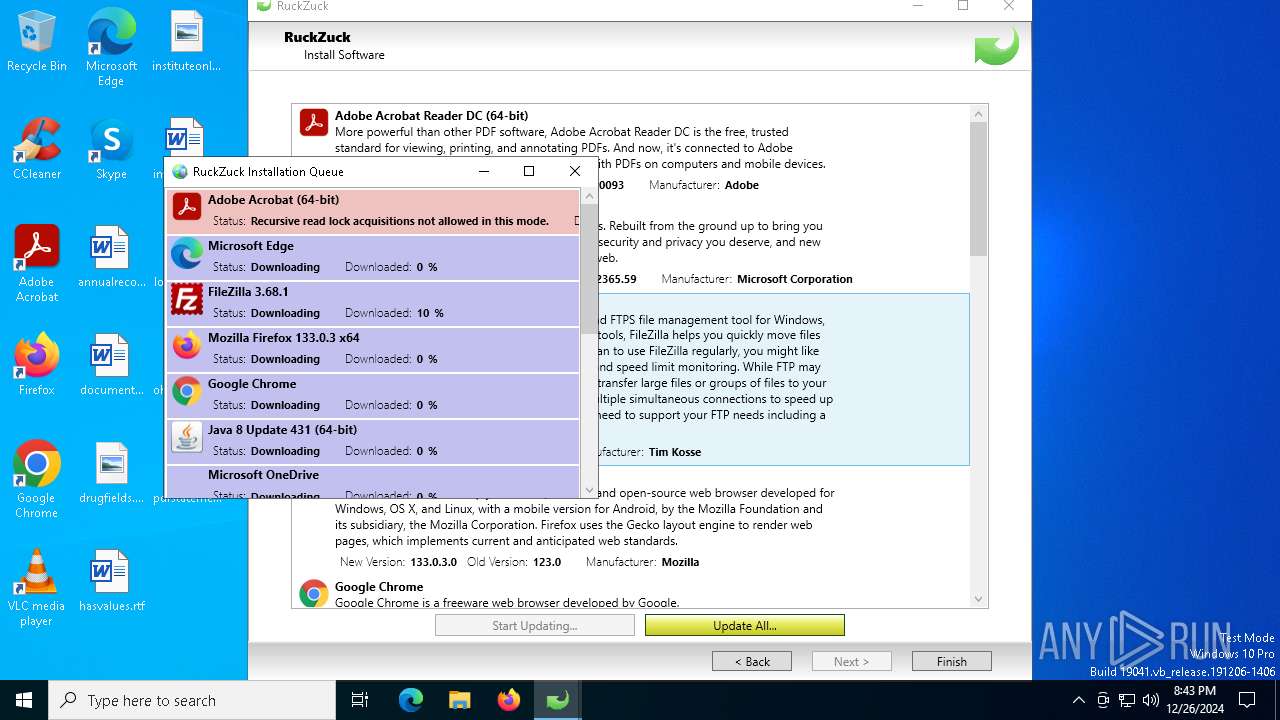
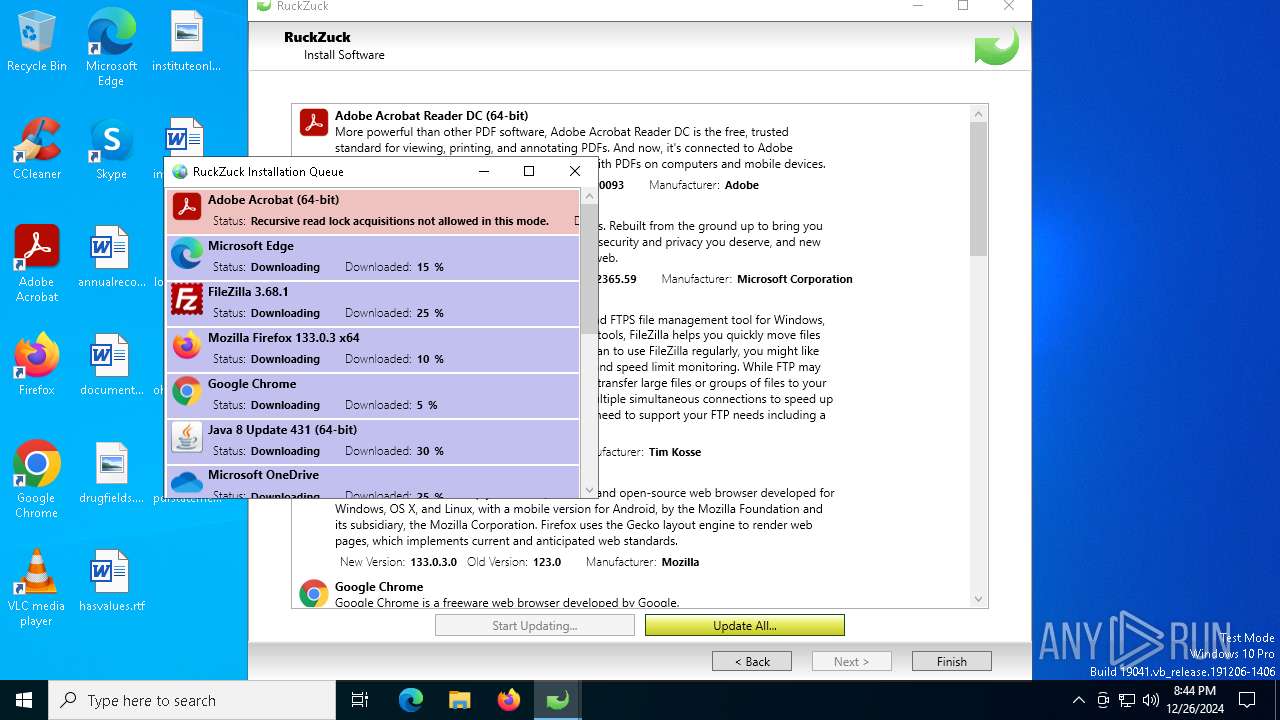
Searches for installed software
- RuckZuck.exe (PID: 1300)
Checks Windows Trust Settings
- RuckZuck.exe (PID: 1300)
Gets or sets the security protocol (POWERSHELL)
- RuckZuck.exe (PID: 1300)
Checks a user's role membership (POWERSHELL)
- RuckZuck.exe (PID: 1300)
INFO
Creates files or folders in the user directory
- RuckZuck.exe (PID: 1300)
Checks proxy server information
- RuckZuck.exe (PID: 1300)
Reads the machine GUID from the registry
- RuckZuck.exe (PID: 1300)
Reads the computer name
- RuckZuck.exe (PID: 1300)
Checks supported languages
- RuckZuck.exe (PID: 1300)
Confuser has been detected (YARA)
- RuckZuck.exe (PID: 1300)
Create files in a temporary directory
- RuckZuck.exe (PID: 1300)
Reads the software policy settings
- RuckZuck.exe (PID: 1300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:03:24 10:33:16+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 1396224 |
| InitializedDataSize: | 14336 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x156dee |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.7.3.5 |
| ProductVersionNumber: | 1.7.3.5 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
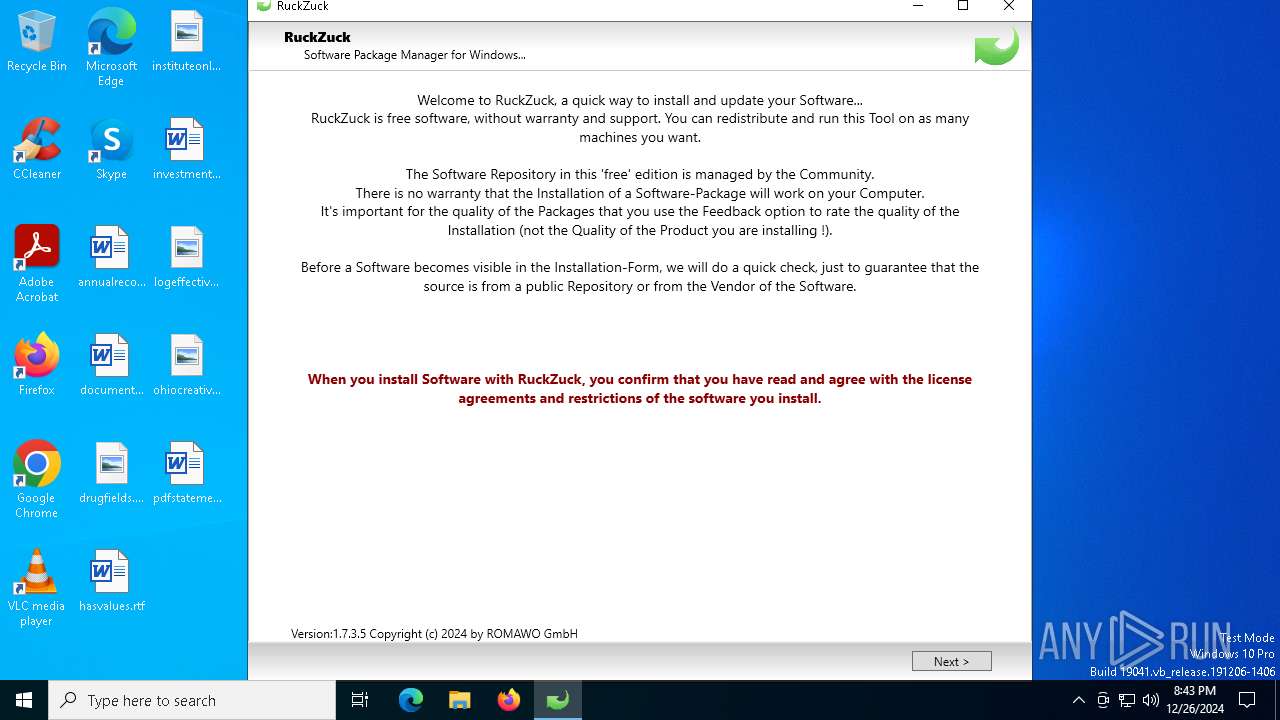
| Comments: | Software Package Manager for Windows |
| CompanyName: | ROMAWO GmbH |
| FileDescription: | RuckZuck |
| FileVersion: | 1.7.3.5 |
| InternalName: | RuckZuck.exe |
| LegalCopyright: | Copyright © 2024 by ROMAWO GmbH |
| LegalTrademarks: | - |
| OriginalFileName: | RuckZuck.exe |
| ProductName: | RuckZuck |
| ProductVersion: | 1.7.3.5 |
| AssemblyVersion: | 1.7.3.20795 |
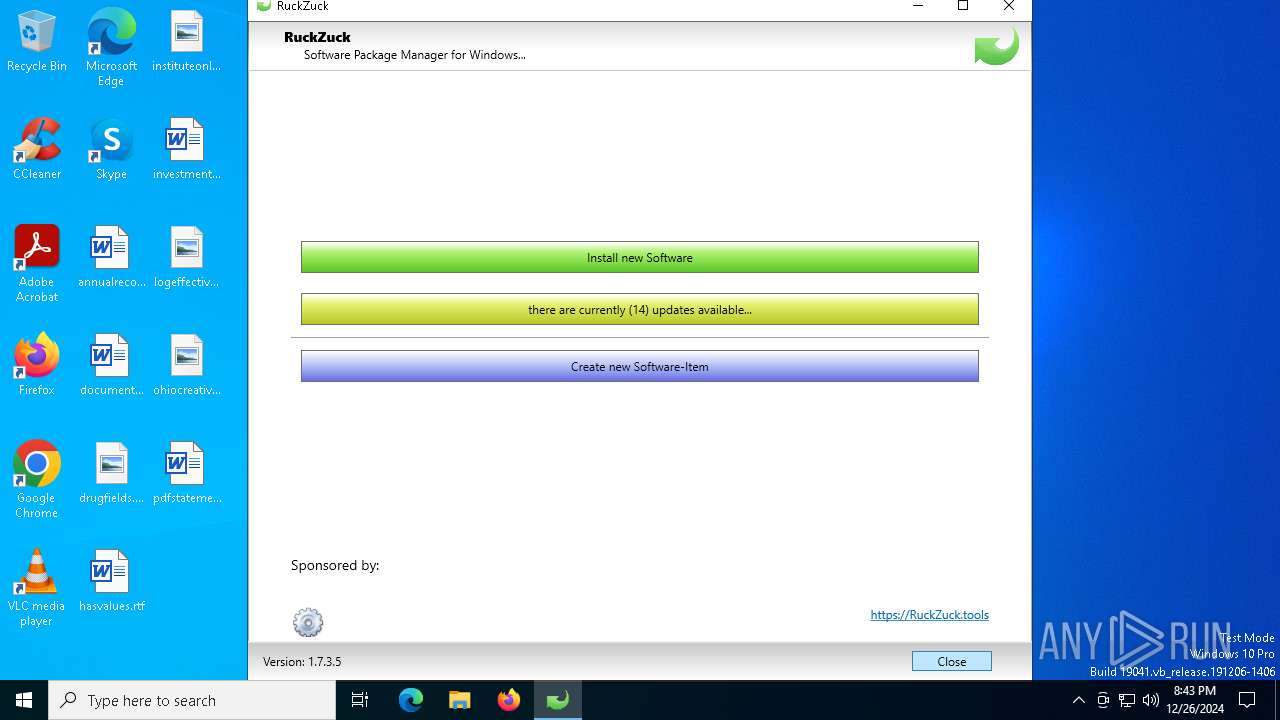
Total processes
128
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
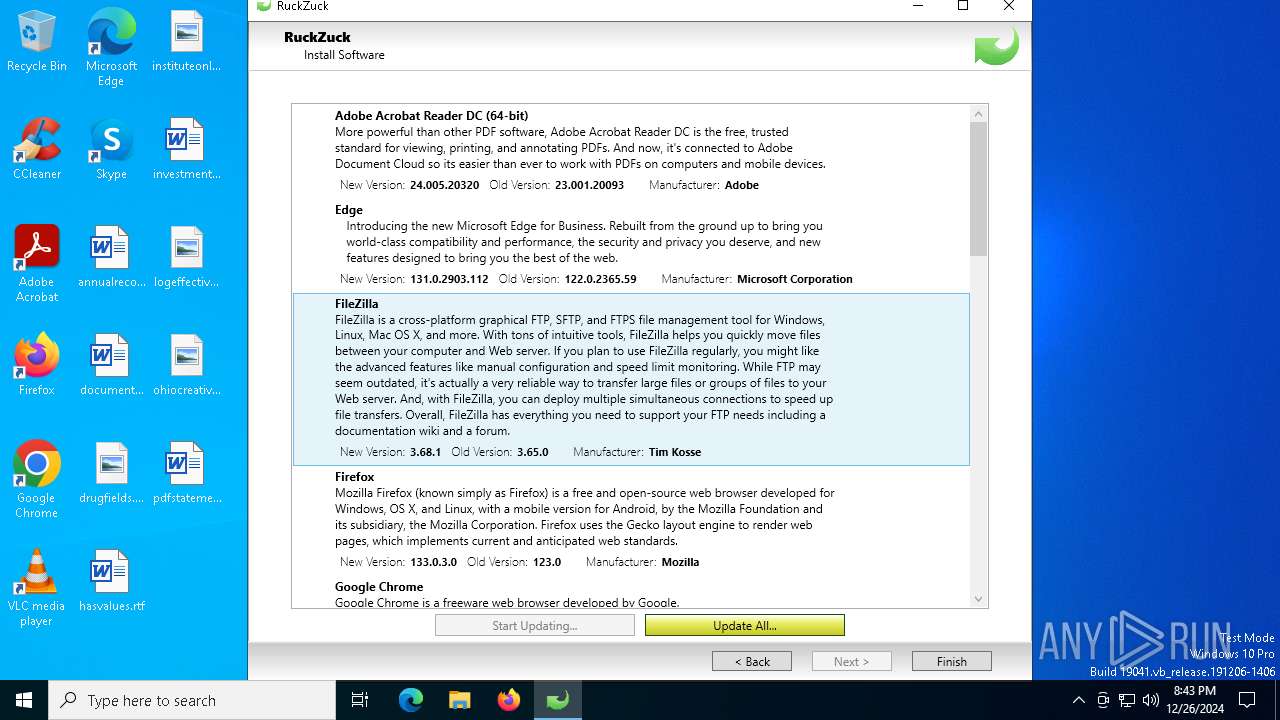
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1300 | "C:\Users\admin\AppData\Local\Temp\RuckZuck.exe" | C:\Users\admin\AppData\Local\Temp\RuckZuck.exe | explorer.exe | ||||||||||||
User: admin Company: ROMAWO GmbH Integrity Level: HIGH Description: RuckZuck Version: 1.7.3.5 Modules
| |||||||||||||||
| 4976 | "C:\Users\admin\AppData\Local\Temp\RuckZuck.exe" | C:\Users\admin\AppData\Local\Temp\RuckZuck.exe | — | explorer.exe | |||||||||||
User: admin Company: ROMAWO GmbH Integrity Level: MEDIUM Description: RuckZuck Exit code: 3221226540 Version: 1.7.3.5 Modules
| |||||||||||||||
Total events
8 342
Read events
8 325
Write events
17
Delete events
0
Modification events
| (PID) Process: | (1300) RuckZuck.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1300) RuckZuck.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1300) RuckZuck.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1300) RuckZuck.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RuckZuck_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1300) RuckZuck.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RuckZuck_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1300) RuckZuck.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RuckZuck_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1300) RuckZuck.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RuckZuck_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1300) RuckZuck.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RuckZuck_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (1300) RuckZuck.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RuckZuck_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1300) RuckZuck.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RuckZuck_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
1
Suspicious files
6
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1300 | RuckZuck.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:6D47FDACE81573F5CBF21BEFD05DF5D9 | SHA256:8A88D44ACF9E54E3889FD2359B60156E152C7A1F447EF07549CD8DAD08CF7F4E | |||
| 1300 | RuckZuck.exe | C:\Users\admin\AppData\Local\ROMAWO_GmbH\RuckZuck.exe_Url_mnnkqobmo4g1syo2fb1glqpybf0ynfgf\1.7.3.20795\rrex5lx3.newcfg | xml | |
MD5:2B6FE5A5027B38CD99D49CC300F43A9C | SHA256:D6580AD140B2C96F360EE164B9A88E06F6BA83DB3DF05DC90D908F0467DDADF6 | |||
| 1300 | RuckZuck.exe | C:\Users\admin\AppData\Local\ROMAWO_GmbH\RuckZuck.exe_Url_mnnkqobmo4g1syo2fb1glqpybf0ynfgf\1.7.3.20795\user.config | xml | |
MD5:A71B2875CB982F979BB5140665C8E712 | SHA256:343789C61269549DEFC214994BE390833DB47815A063E35436B104E7E4424A8F | |||
| 1300 | RuckZuck.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8EC9B1D0ABBD7F98B401D425828828CE_5BCA9560D578FC4FE46BB9B726ABAF78 | binary | |
MD5:4141F229A8A7C3CF024BC58ED1AB2D2F | SHA256:794E07CC58252BC98377549A11CA4FCB5D8789D05CFE47C74EAA7026C9892C6A | |||
| 1300 | RuckZuck.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:468C4460F6A0CB486D6A952276B386C1 | SHA256:12E57D6B9F093C8D43BA27B2AB47C18CF26F0E315BCDEA90C166785B0852BA97 | |||
| 1300 | RuckZuck.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8EC9B1D0ABBD7F98B401D425828828CE_5BCA9560D578FC4FE46BB9B726ABAF78 | binary | |
MD5:967458A835D73DCA66D8E64BDDCDF172 | SHA256:56C5624A588808C0C6E473D819BC4ED876F575032E8F77690ECE31FDA7DD68FE | |||
| 1300 | RuckZuck.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:6B2D9C71B34F97024A816291CA26B330 | SHA256:9FB5DD6968D5A7AB97540ABDFBB81125C785DB2BD0E21C794F1DECD86B77198C | |||
| 1300 | RuckZuck.exe | C:\Users\admin\AppData\Local\ROMAWO_GmbH\RuckZuck.exe_Url_mnnkqobmo4g1syo2fb1glqpybf0ynfgf\1.7.3.20795\oxhnmv2t.newcfg | xml | |
MD5:A71B2875CB982F979BB5140665C8E712 | SHA256:343789C61269549DEFC214994BE390833DB47815A063E35436B104E7E4424A8F | |||
| 1300 | RuckZuck.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ieo3mxps.5lp.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1300 | RuckZuck.exe | C:\Users\admin\AppData\Local\ROMAWO_GmbH\RuckZuck.exe_Url_mnnkqobmo4g1syo2fb1glqpybf0ynfgf\1.7.3.20795\flcdt3l0.newcfg | xml | |
MD5:0B2DA9986D80C83EC2EEBAA53C7C14AA | SHA256:886AEF87EB55A58D872644E858C4FFA6F1C2B6B7446983414D9BC9EAA63DCC1D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
60
DNS requests
35
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1300 | RuckZuck.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1300 | RuckZuck.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAIV84c7pFZCWDdWGehqSnk%3D | unknown | — | — | whitelisted |
1300 | RuckZuck.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
7076 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1016 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 2.23.209.149:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cdn.ruckzuck.tools |
| unknown |
go.microsoft.com |
| whitelisted |
ruckzuck.tools |
| unknown |
msedge.sf.dl.delivery.mp.microsoft.com |
| unknown |