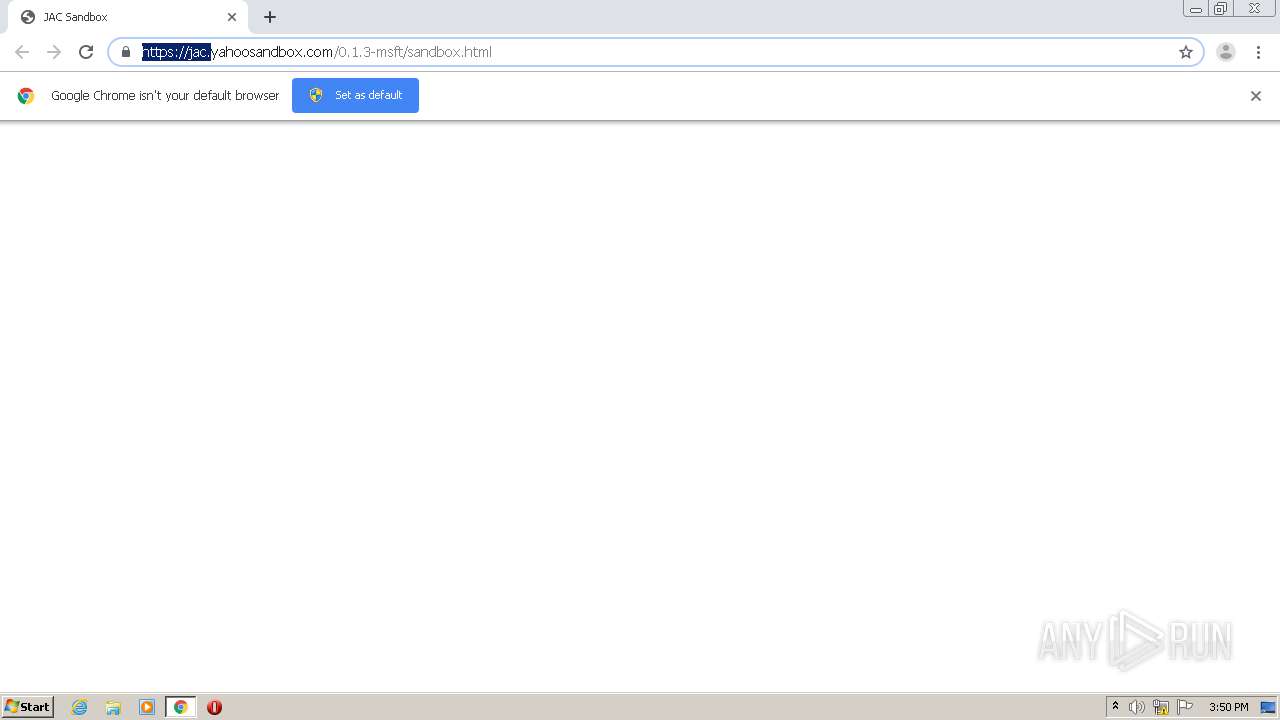
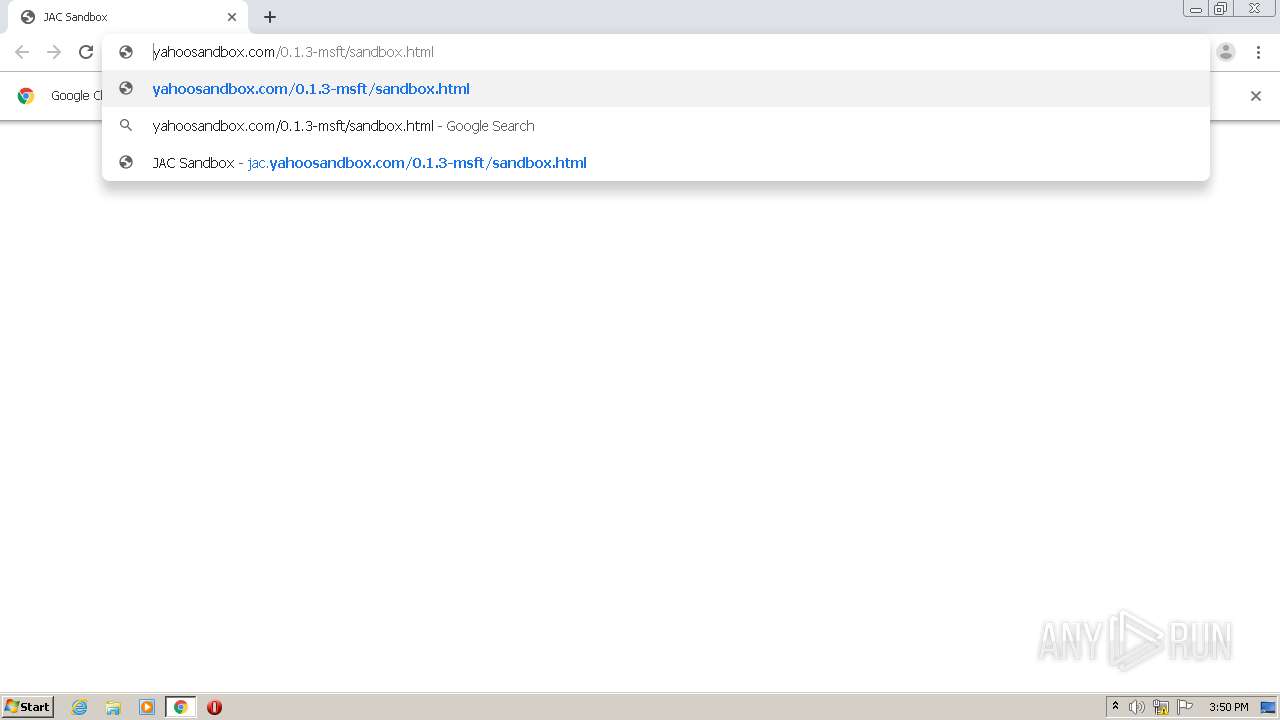
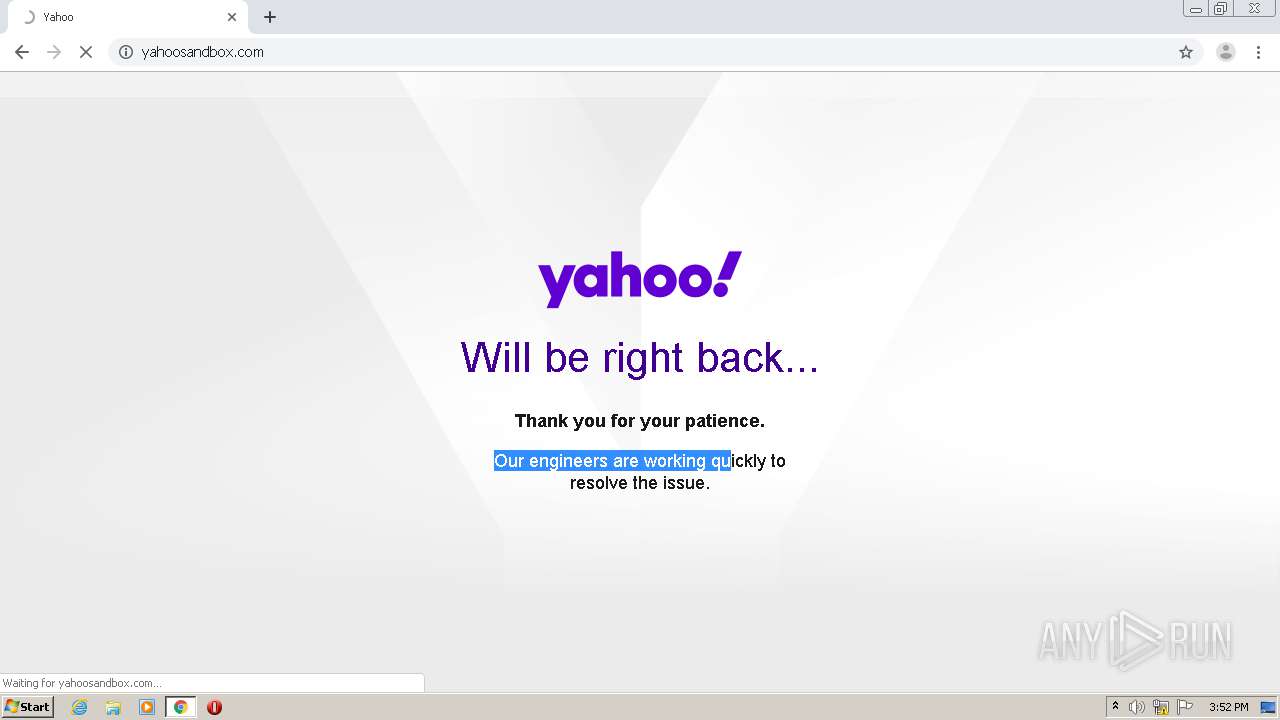
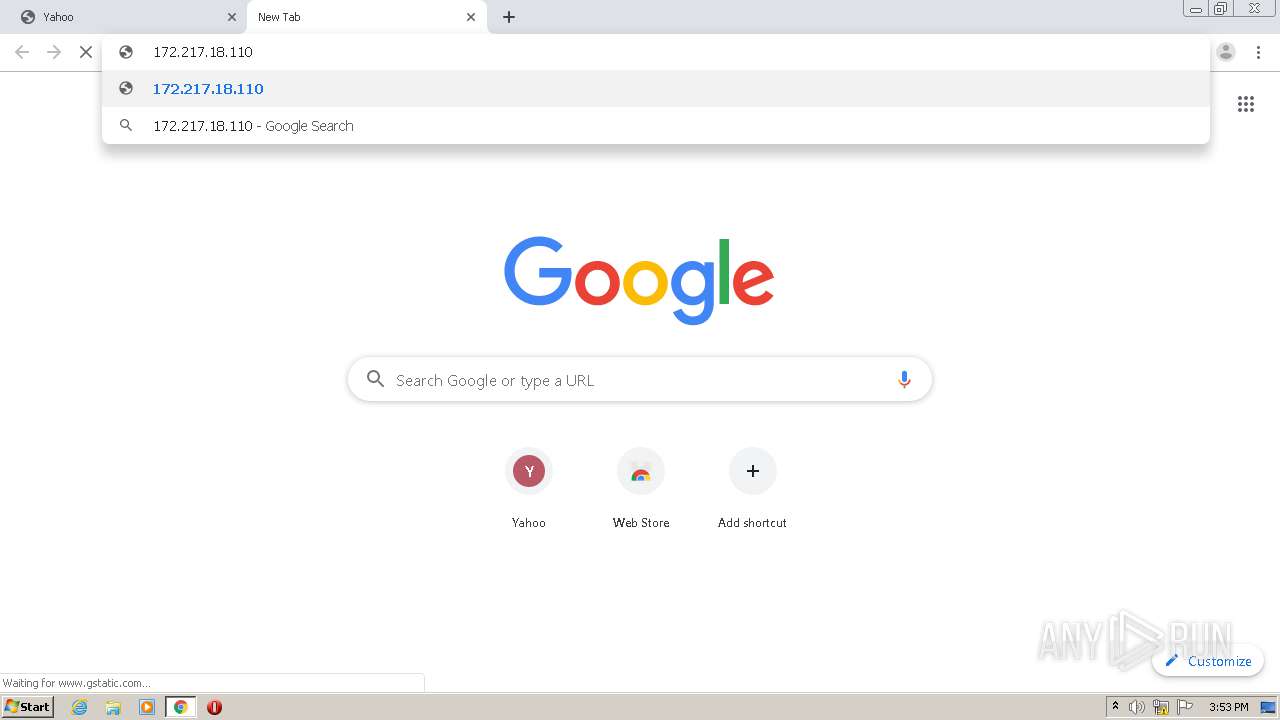
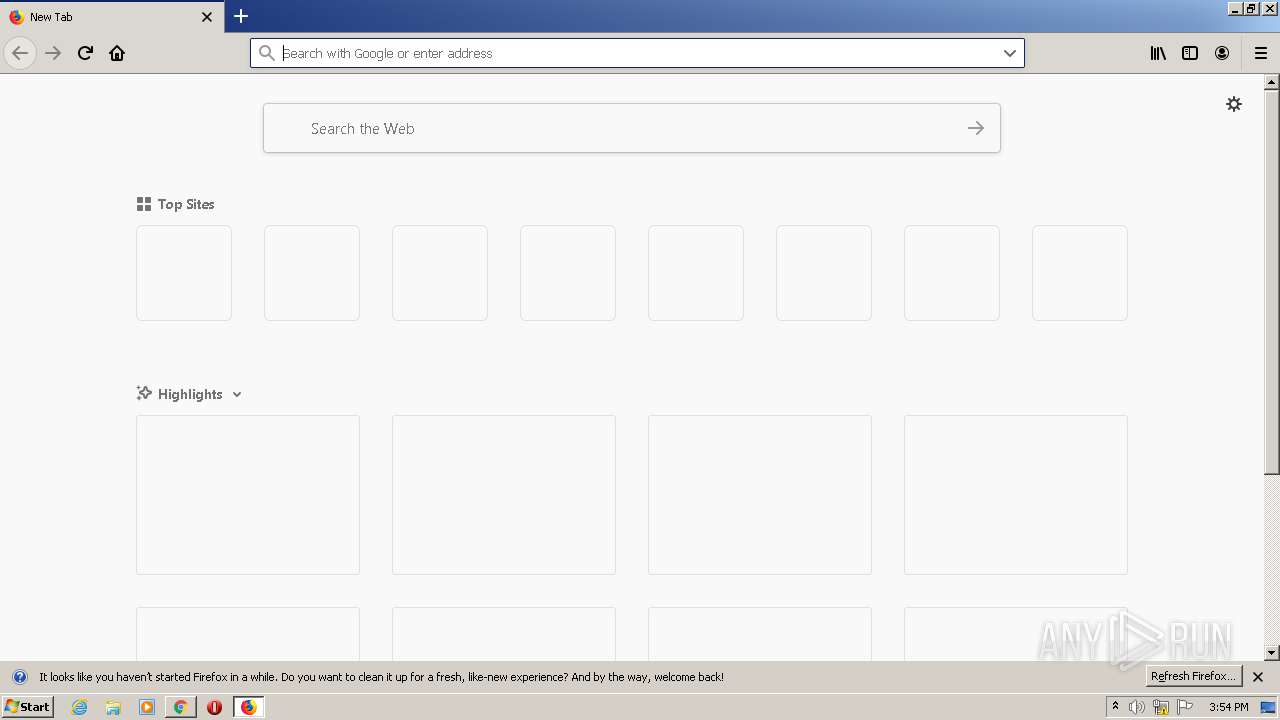
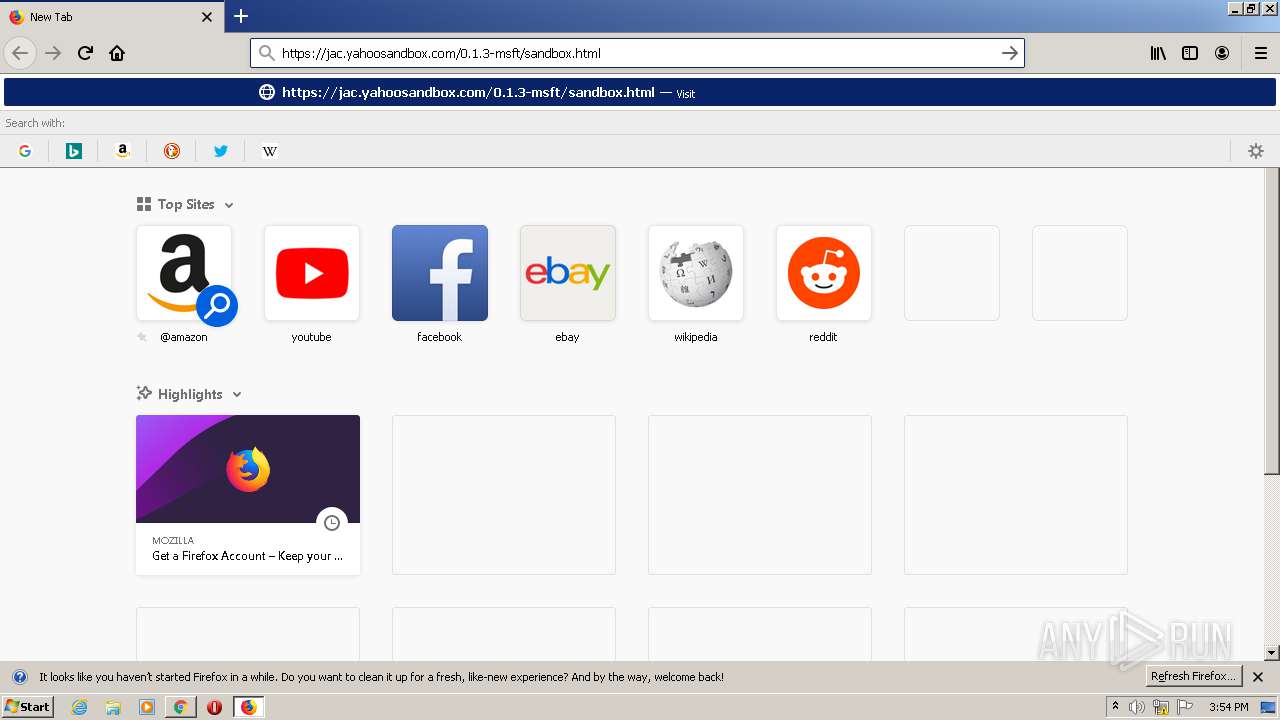
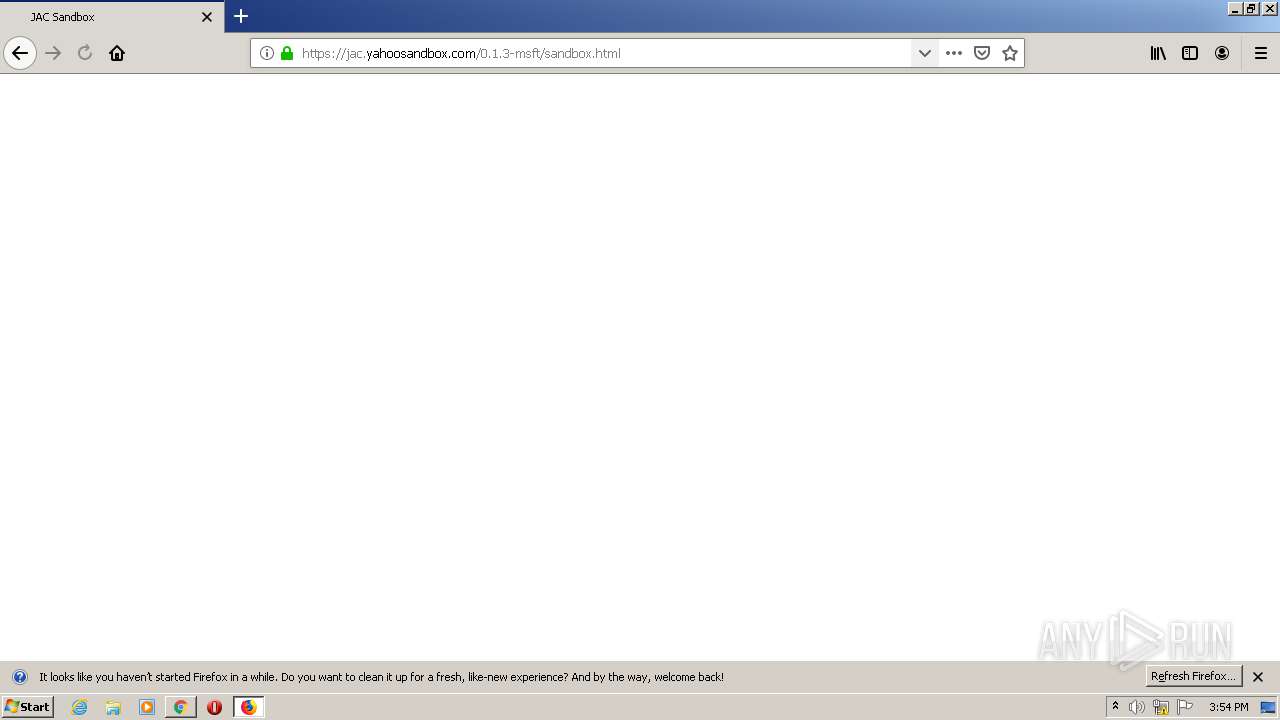
| URL: | https://jac.yahoosandbox.com/0.1.3-msft/sandbox.html |
| Full analysis: | https://app.any.run/tasks/09ccebe4-c54f-4a54-a2b5-7e9e340e3b30 |
| Verdict: | Malicious activity |
| Analysis date: | October 07, 2020, 14:50:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CD1CDD3847C59F48FF4F4D3FB1D9F57E |
| SHA1: | 7EA4E0E35568B47D0B89504D6A73525DB0704D96 |
| SHA256: | 24B8EDEFE4C77D49DC80E861476808FEC6840146661CA5DA9034FFF9154B30AD |
| SSDEEP: | 3:N81L1NNBmLG13kKdLNG:21ZXvG |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 3512)
INFO
Application launched itself
- chrome.exe (PID: 3268)
- firefox.exe (PID: 616)
- firefox.exe (PID: 3512)
Creates files in the user directory
- opera.exe (PID: 1356)
- firefox.exe (PID: 3512)
Reads settings of System Certificates
- chrome.exe (PID: 3080)
Manual execution by user
- firefox.exe (PID: 616)
- opera.exe (PID: 1356)
Reads the hosts file
- chrome.exe (PID: 3080)
- chrome.exe (PID: 3268)
Reads Internet Cache Settings
- firefox.exe (PID: 3512)
Reads CPU info
- firefox.exe (PID: 3512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
27
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1356 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 1364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,11168459753982281865,12447449458490739739,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6322734425752893864 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=984,11168459753982281865,12447449458490739739,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9510619298241591235 --mojo-platform-channel-handle=1028 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1668 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3512.13.1643514381\1661273332" -childID 2 -isForBrowser -prefsHandle 2760 -prefMapHandle 2764 -prefsLen 5996 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3512 "\\.\pipe\gecko-crash-server-pipe.3512" 2776 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=984,11168459753982281865,12447449458490739739,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3267061272048008010 --mojo-platform-channel-handle=3496 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6cdba9d0,0x6cdba9e0,0x6cdba9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3512.3.650501868\1501825577" -childID 1 -isForBrowser -prefsHandle 1724 -prefMapHandle 1644 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3512 "\\.\pipe\gecko-crash-server-pipe.3512" 1744 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,11168459753982281865,12447449458490739739,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=991420993828912837 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3024 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,11168459753982281865,12447449458490739739,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16457274183242430227 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 489
Read events
1 344
Write events
141
Delete events
4
Modification events
| (PID) Process: | (3404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3268-13246555831448875 |
Value: 259 | |||
| (PID) Process: | (3268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (3268) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
90
Text files
128
Unknown types
46
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F7DD5B8-CC4.pma | — | |
MD5:— | SHA256:— | |||
| 3268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7684c229-55f4-46d3-8042-a72583d585f3.tmp | — | |
MD5:— | SHA256:— | |||
| 3268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1ab1fc.TMP | text | |
MD5:— | SHA256:— | |||
| 3268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF1ab2c7.TMP | text | |
MD5:— | SHA256:— | |||
| 3268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
61
DNS requests
90
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3080 | chrome.exe | GET | 200 | 98.136.103.23:80 | http://yahoosandbox.com/ | US | html | 1.66 Kb | malicious |
3080 | chrome.exe | POST | 204 | 76.13.32.152:80 | http://csp.yahoo.com/beacon/csp?src=redirect | US | — | — | shared |
3080 | chrome.exe | POST | 204 | 76.13.32.152:80 | http://csp.yahoo.com/beacon/csp?src=redirect | US | — | — | shared |
3080 | chrome.exe | POST | 204 | 76.13.32.152:80 | http://csp.yahoo.com/beacon/csp?src=redirect | US | — | — | shared |
3080 | chrome.exe | POST | 204 | 76.13.32.152:80 | http://csp.yahoo.com/beacon/csp?src=redirect | US | — | — | shared |
3080 | chrome.exe | GET | 200 | 98.136.103.23:80 | http://yahoosandbox.com/ | US | html | 1.66 Kb | malicious |
3080 | chrome.exe | POST | 204 | 76.13.32.152:80 | http://csp.yahoo.com/beacon/csp?src=redirect | US | — | — | shared |
3080 | chrome.exe | POST | 204 | 76.13.32.152:80 | http://csp.yahoo.com/beacon/csp?src=redirect | US | — | — | shared |
1356 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
3512 | firefox.exe | POST | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3080 | chrome.exe | 87.248.118.23:443 | jac.yahoosandbox.com | Yahoo! UK Services Limited | GB | malicious |
3080 | chrome.exe | 172.217.16.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
3080 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3080 | chrome.exe | 172.217.21.196:443 | www.google.com | Google Inc. | US | whitelisted |
3080 | chrome.exe | 98.136.103.23:80 | yahoosandbox.com | Yahoo | US | whitelisted |
3080 | chrome.exe | 212.82.100.150:80 | yahoosandbox.com | Yahoo! UK Services Limited | CH | shared |
3080 | chrome.exe | 76.13.32.152:80 | csp.yahoo.com | Yahoo! | US | unknown |
3080 | chrome.exe | 172.217.16.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3080 | chrome.exe | 216.58.207.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3080 | chrome.exe | 216.58.210.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
jac.yahoosandbox.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
yahoosandbox.com |
| malicious |
s.yimg.com |
| shared |
csp.yahoo.com |
| shared |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |