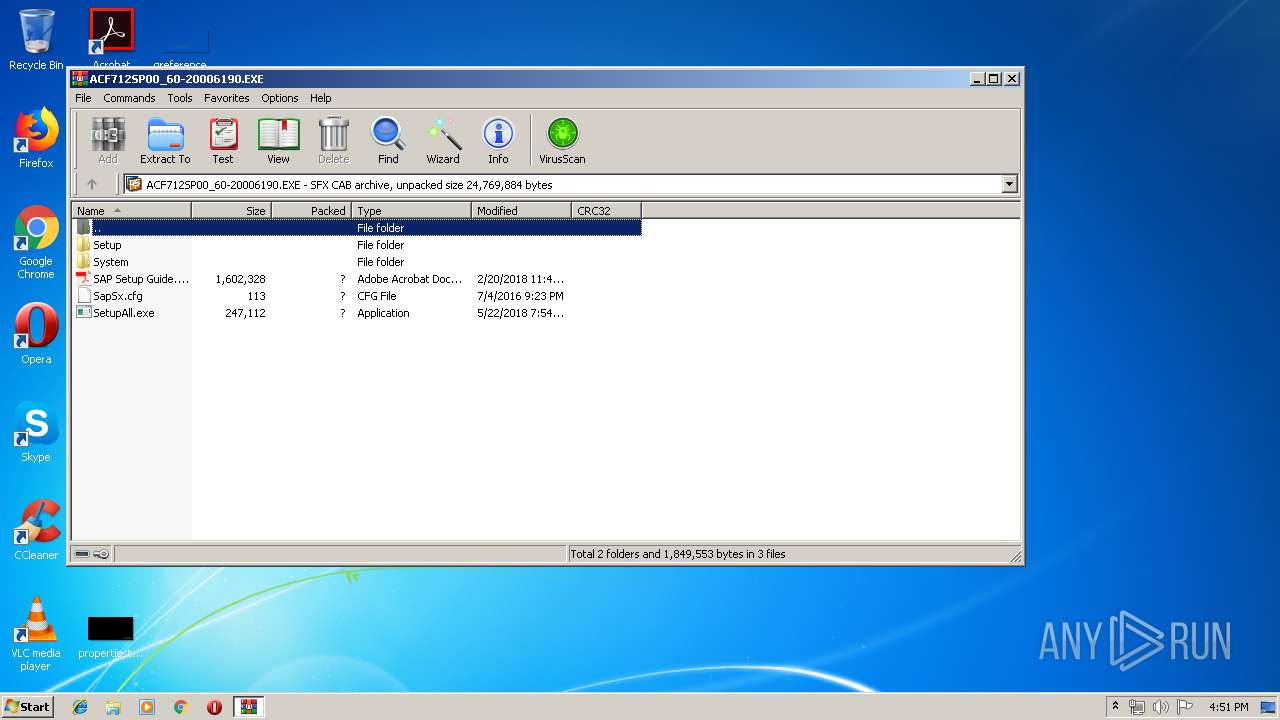
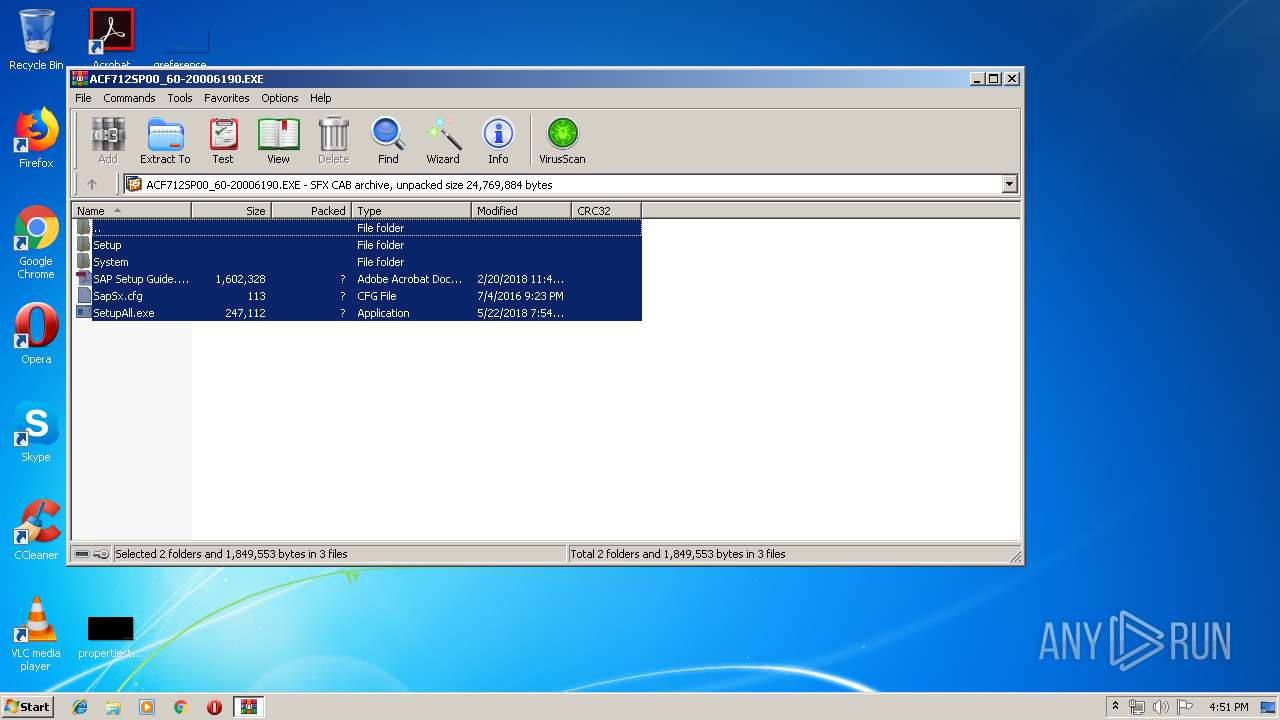
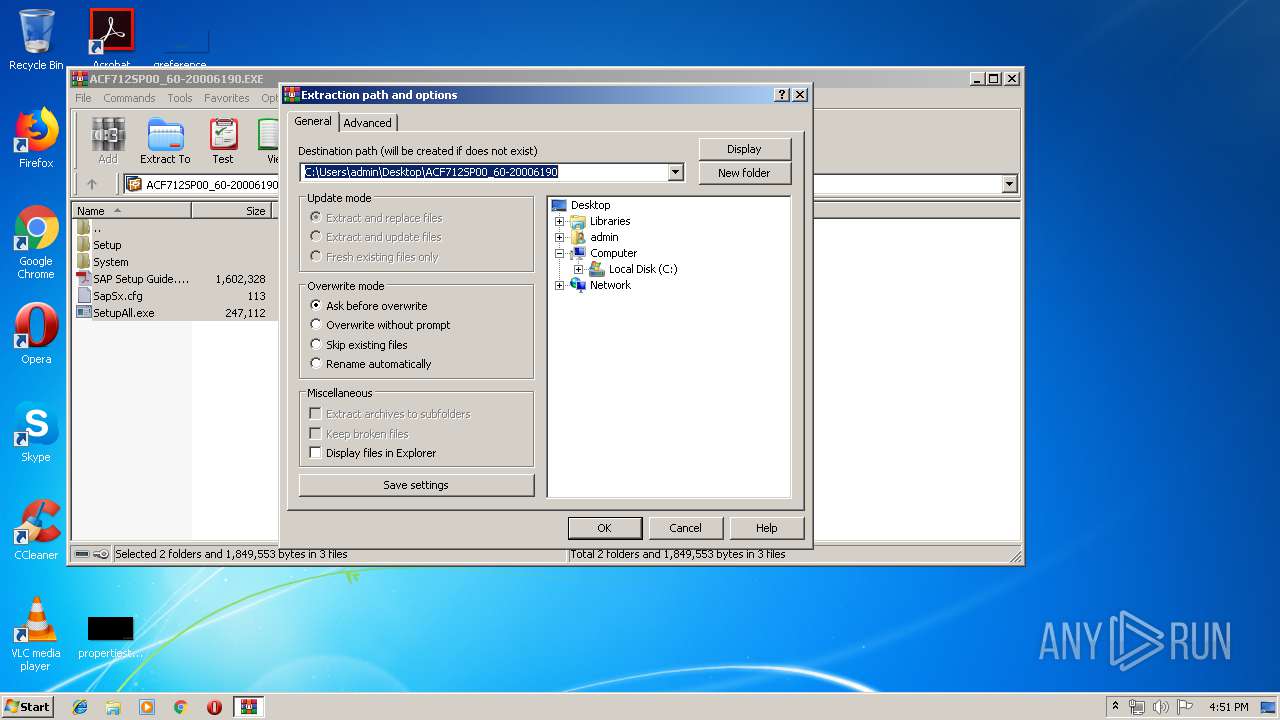
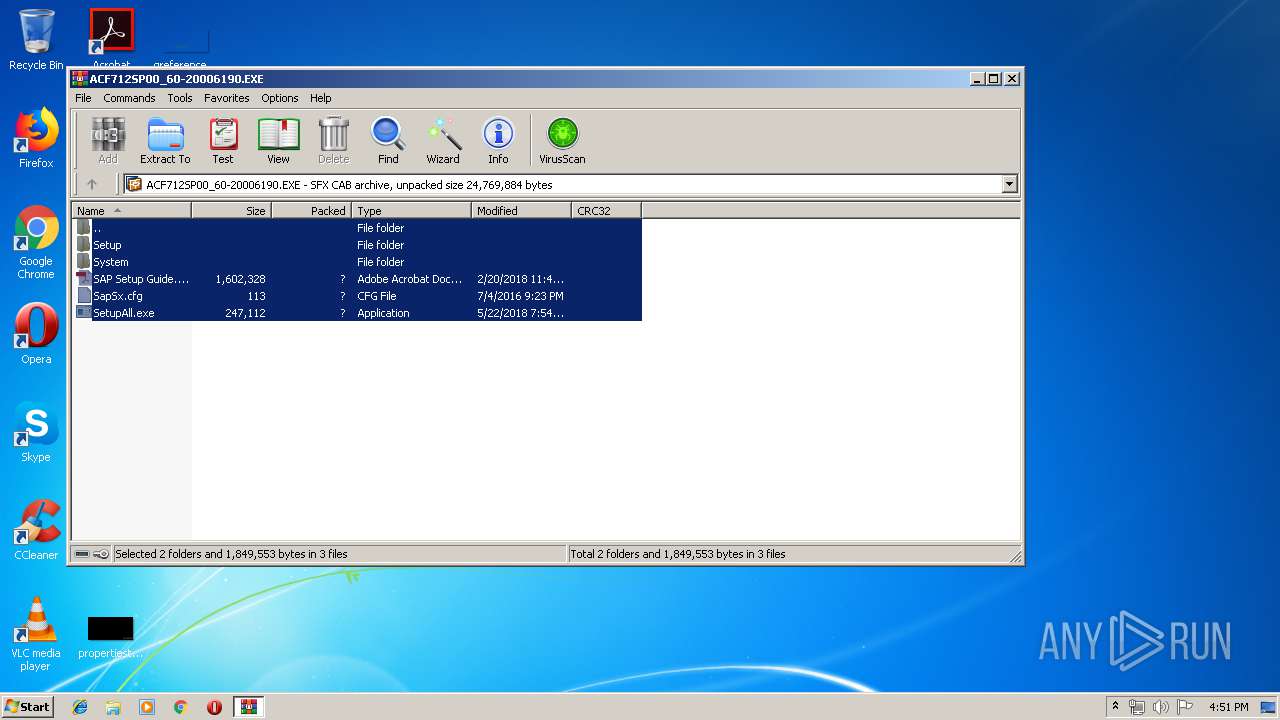
| File name: | ACF712SP00_60-20006190.EXE |
| Full analysis: | https://app.any.run/tasks/b4a7f929-b134-4027-a36d-b54405e7e893 |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2019, 15:50:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3DA53DF8F5D9BC94885FC2C9647C3EDA |
| SHA1: | 27D4A114DB27FEA33226F246D0F5EB0037344DF4 |
| SHA256: | 24B8BF40A93C8A29D36815EA93669BE5229FA9A5446FD4E09DB4B4B20DB13F15 |
| SSDEEP: | 196608:ax0rzfhZFDkWO5UF7/+zq/A3xmpdZovu0KZqCfd6Pnc7eY6PgIVkNYs/QS0:aafhZFy2biqogLvZH2n9PgIVkNYo0 |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 1876)
- WerFault.exe (PID: 3232)
- explorer.exe (PID: 128)
- csrss.exe (PID: 400)
- svchost.exe (PID: 852)
- csrss.exe (PID: 344)
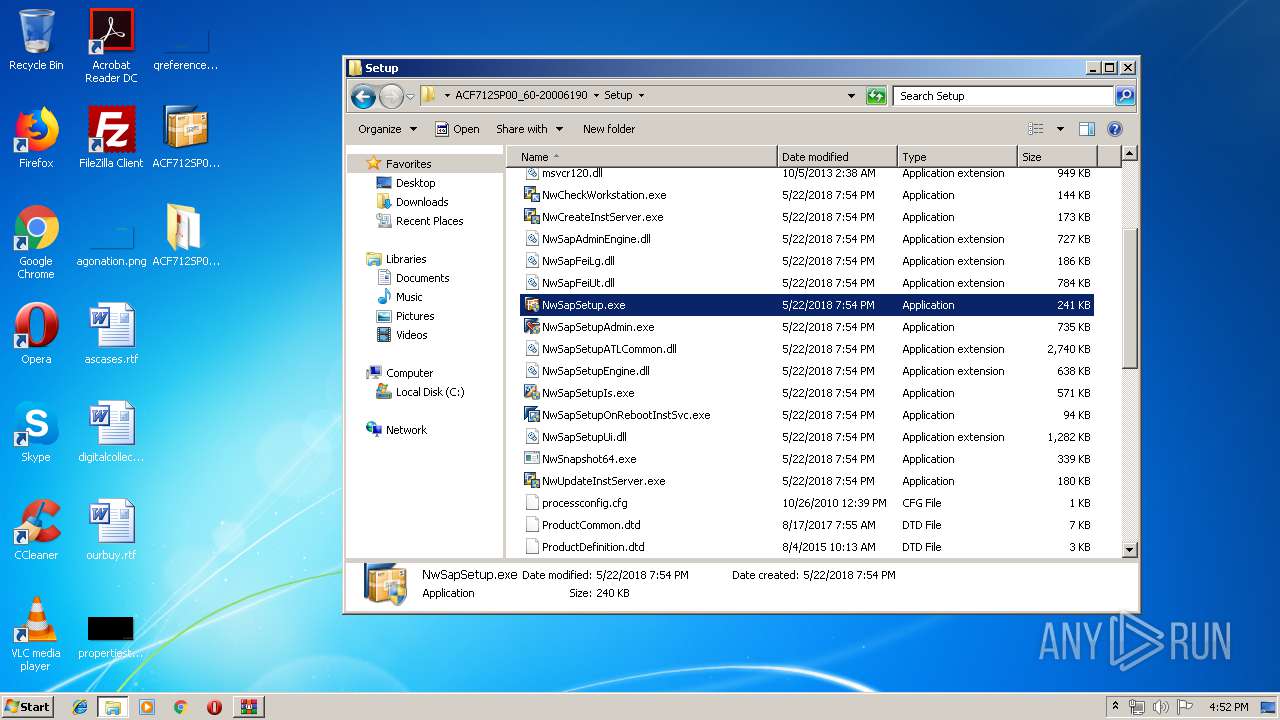
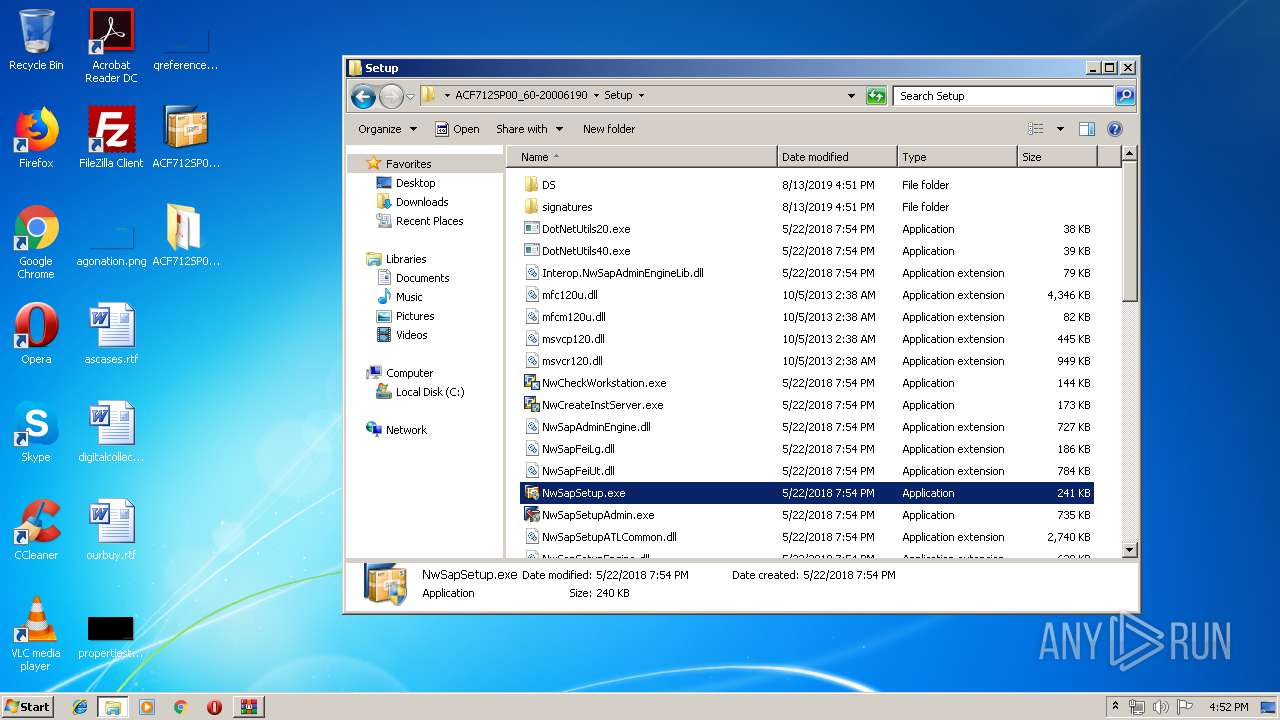
- NwSapSetup.exe (PID: 3560)
- svchost.exe (PID: 824)
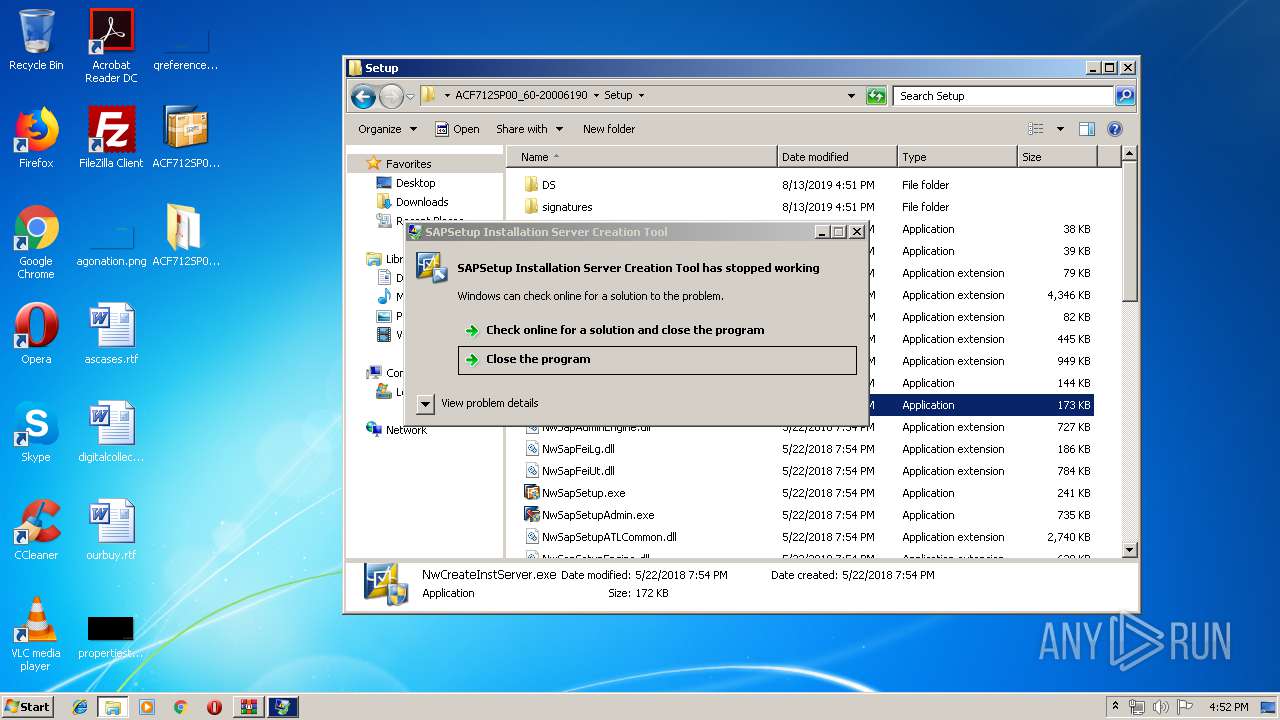
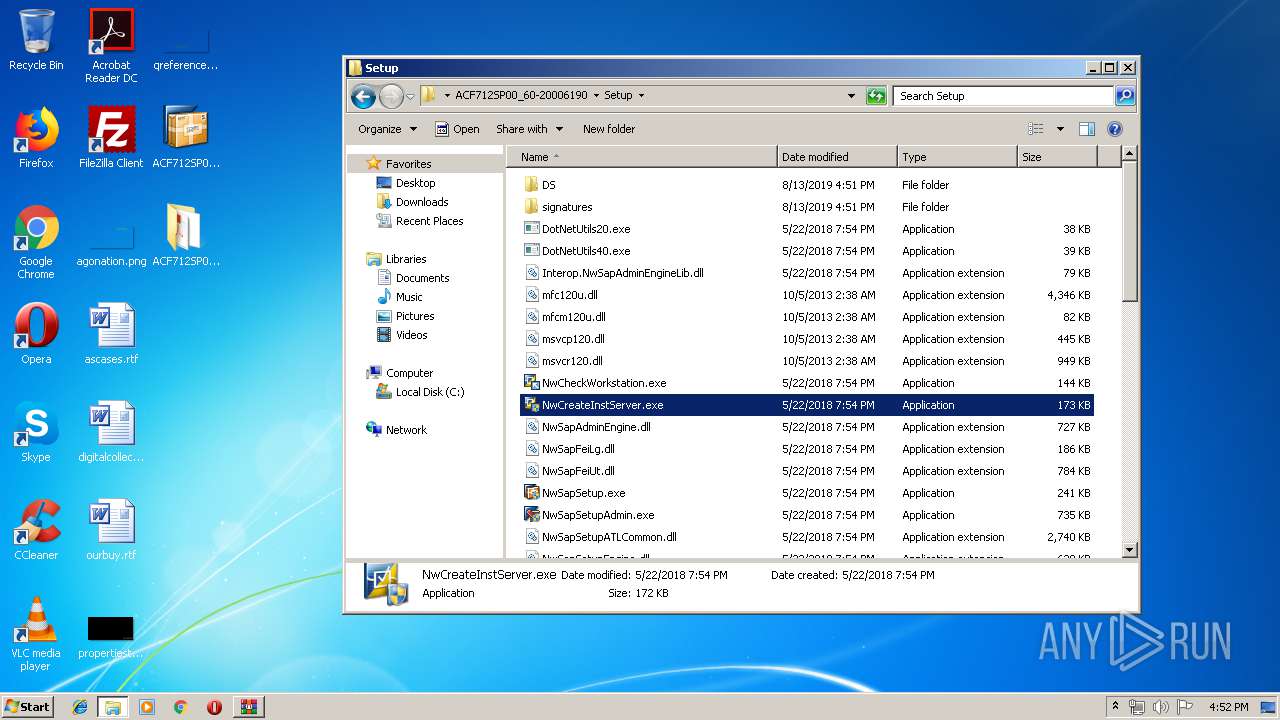
- NwCreateInstServer.exe (PID: 3248)
- WerFault.exe (PID: 1508)
- sdiagnhost.exe (PID: 3596)
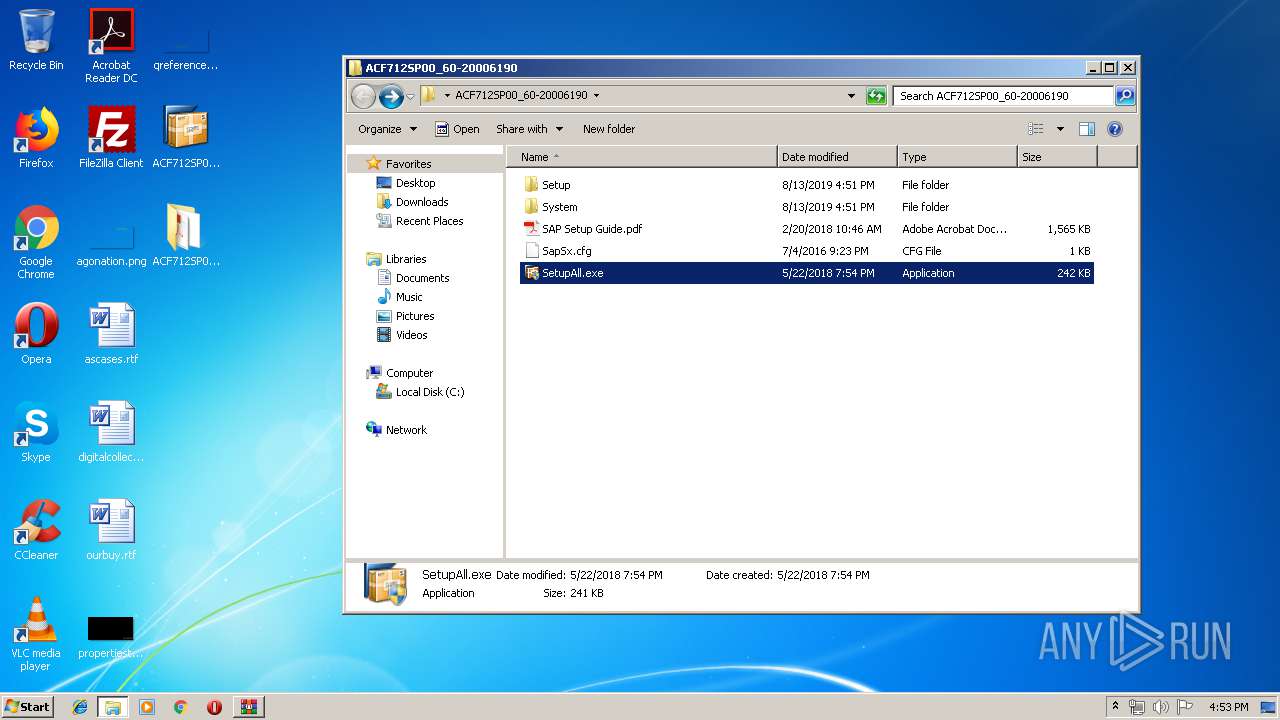
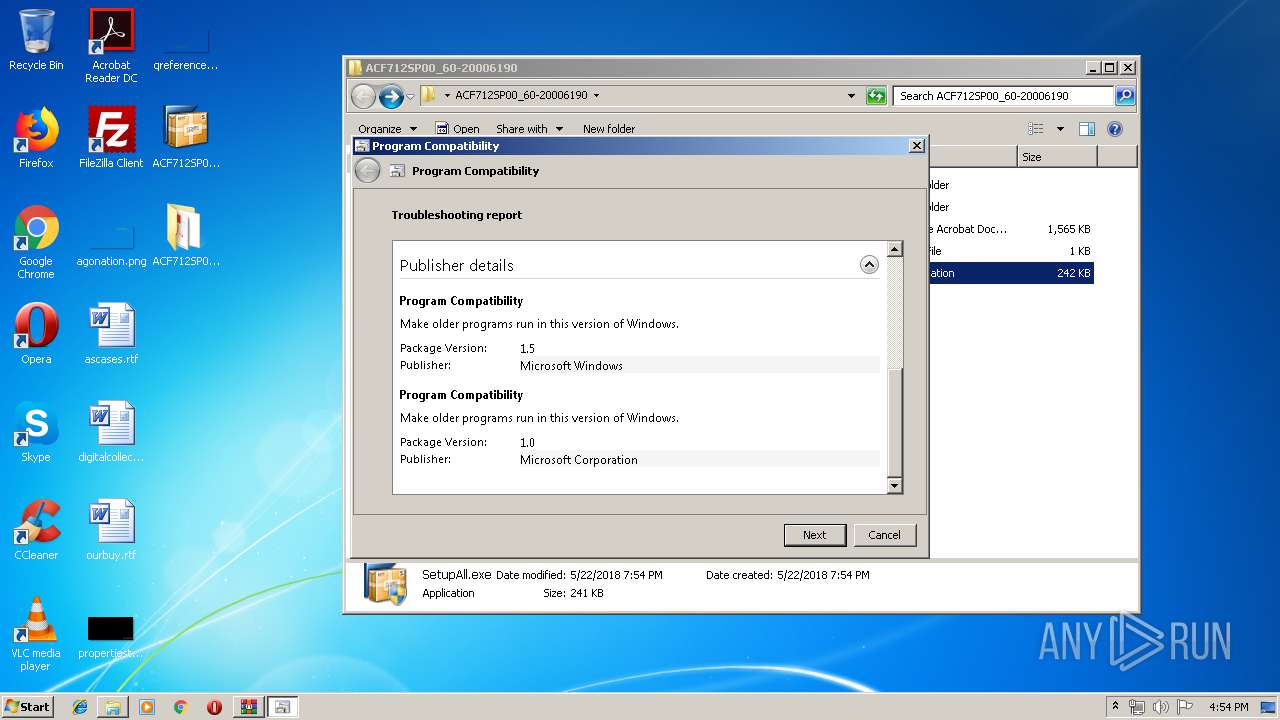
Application was dropped or rewritten from another process
- NwCreateInstServer.exe (PID: 3008)
- NwCreateInstServer.exe (PID: 3248)
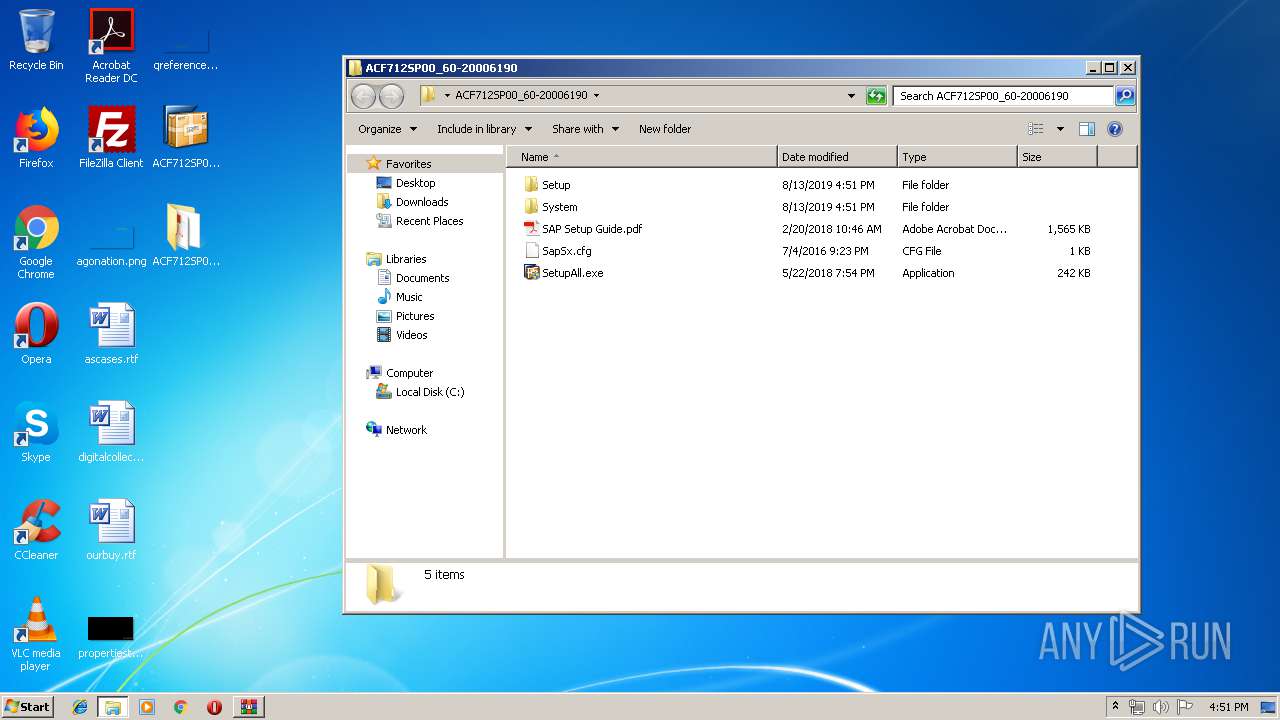
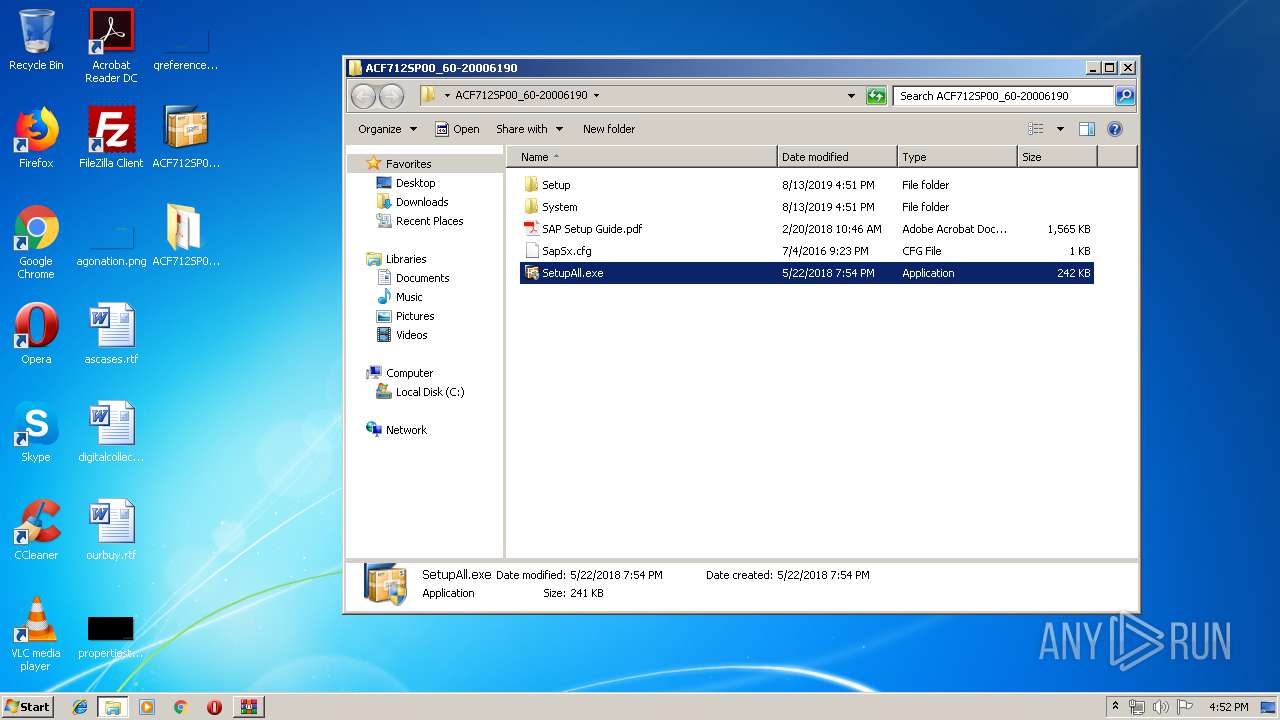
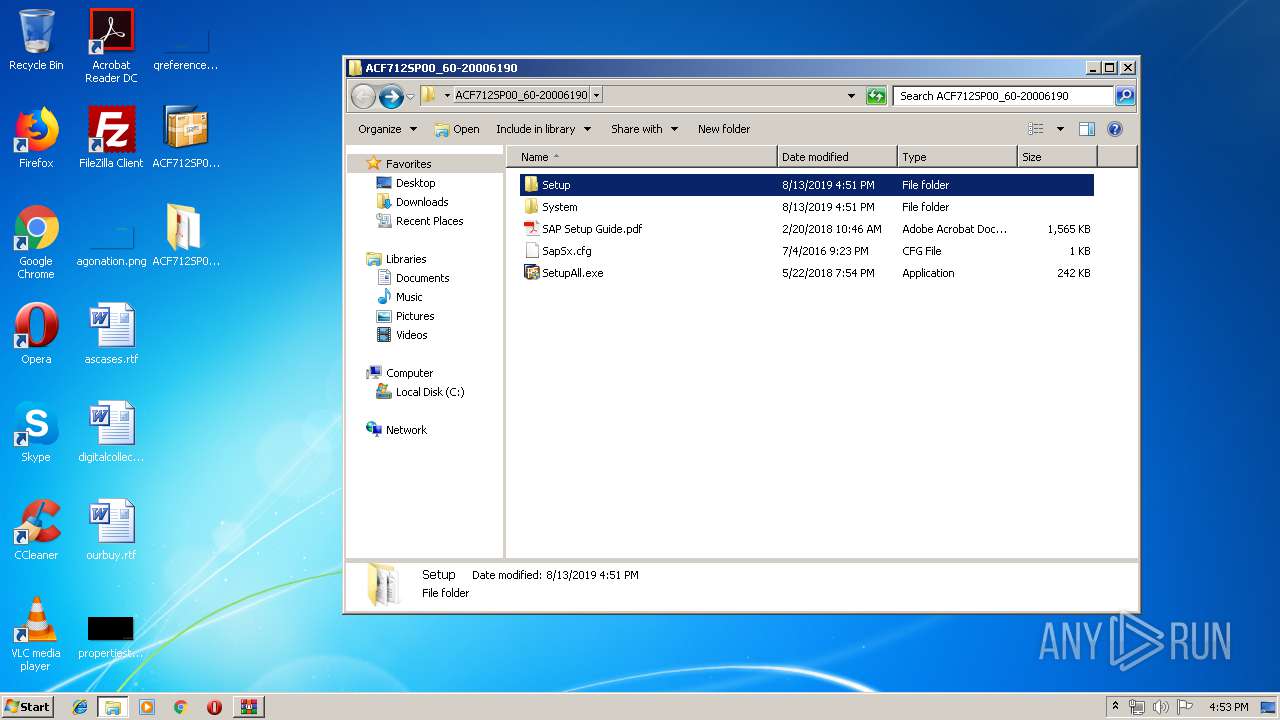
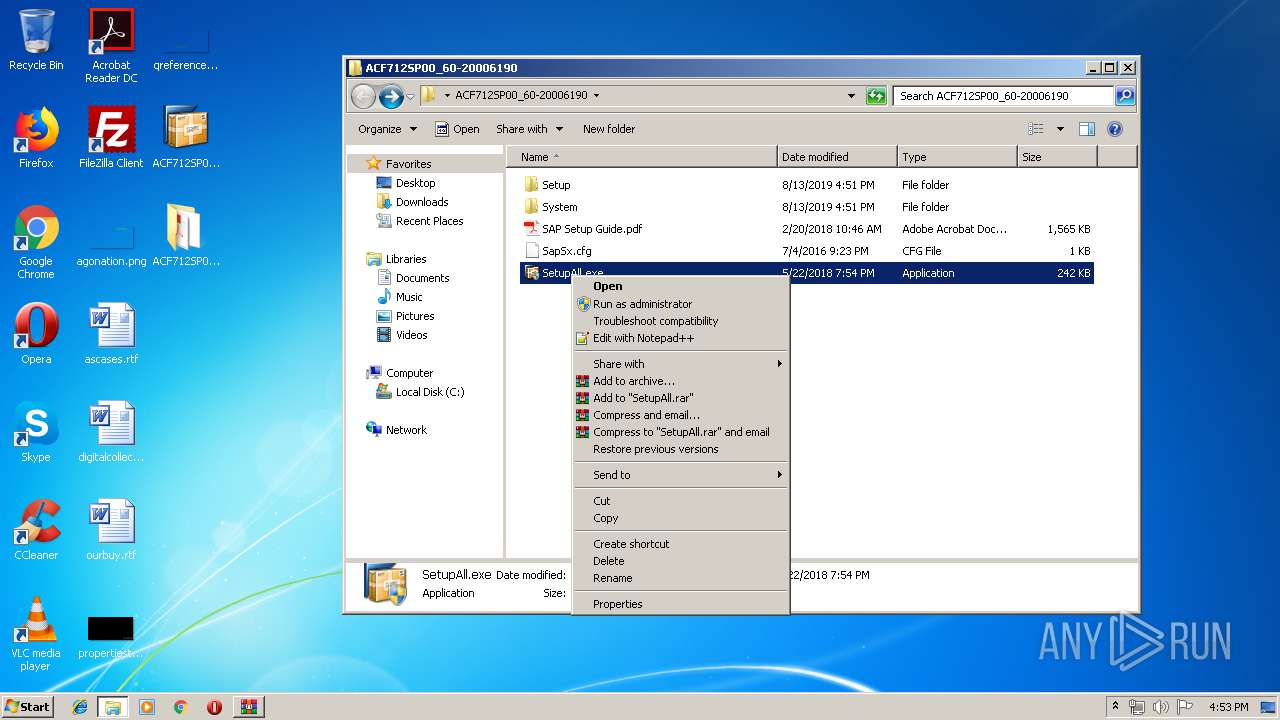
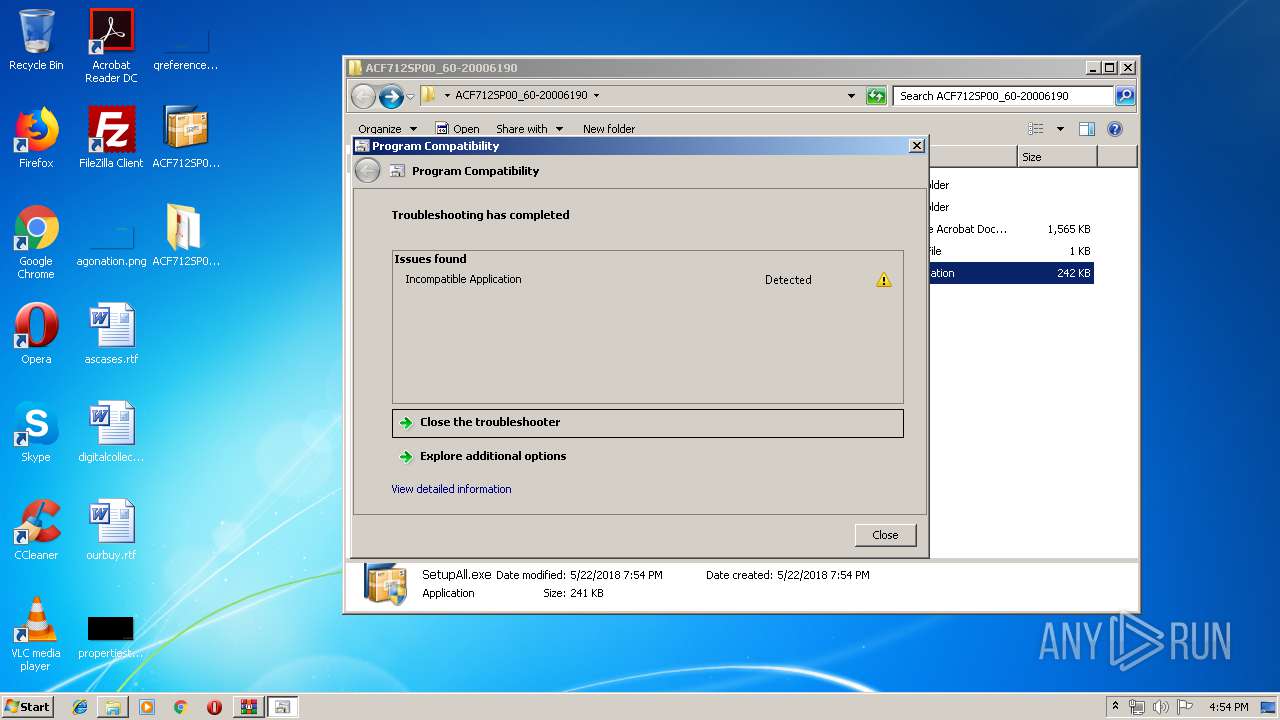
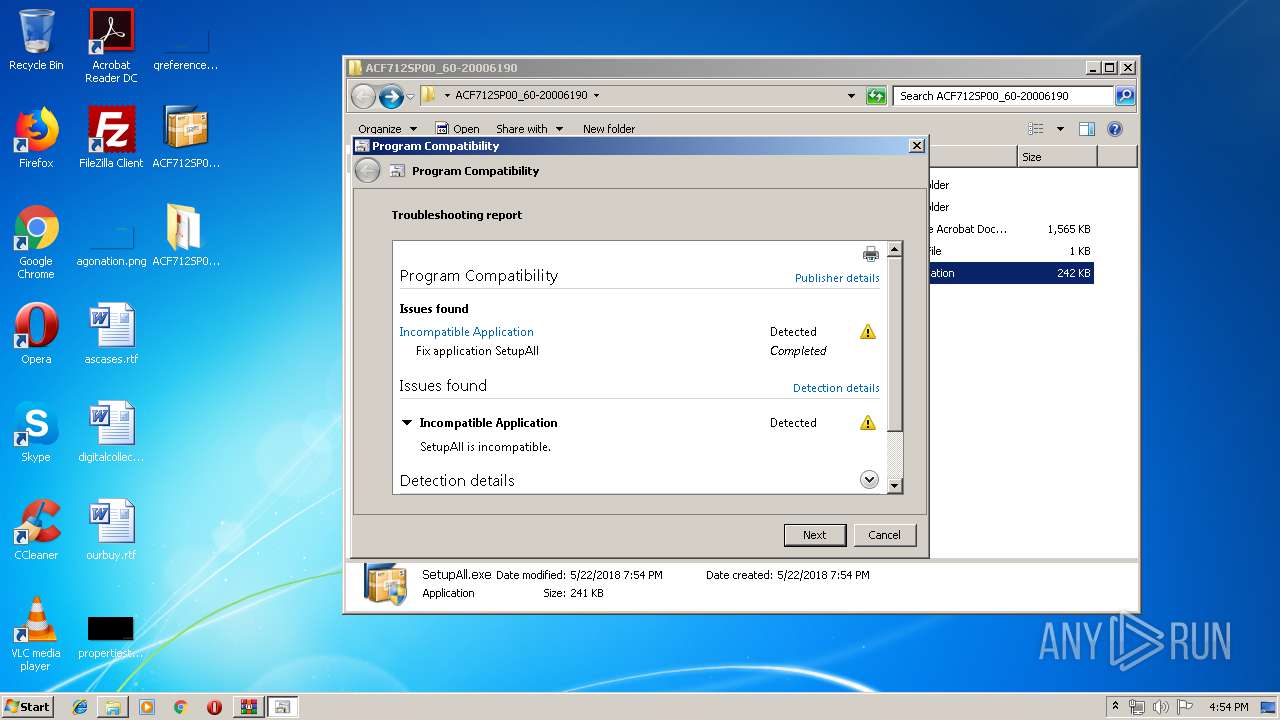
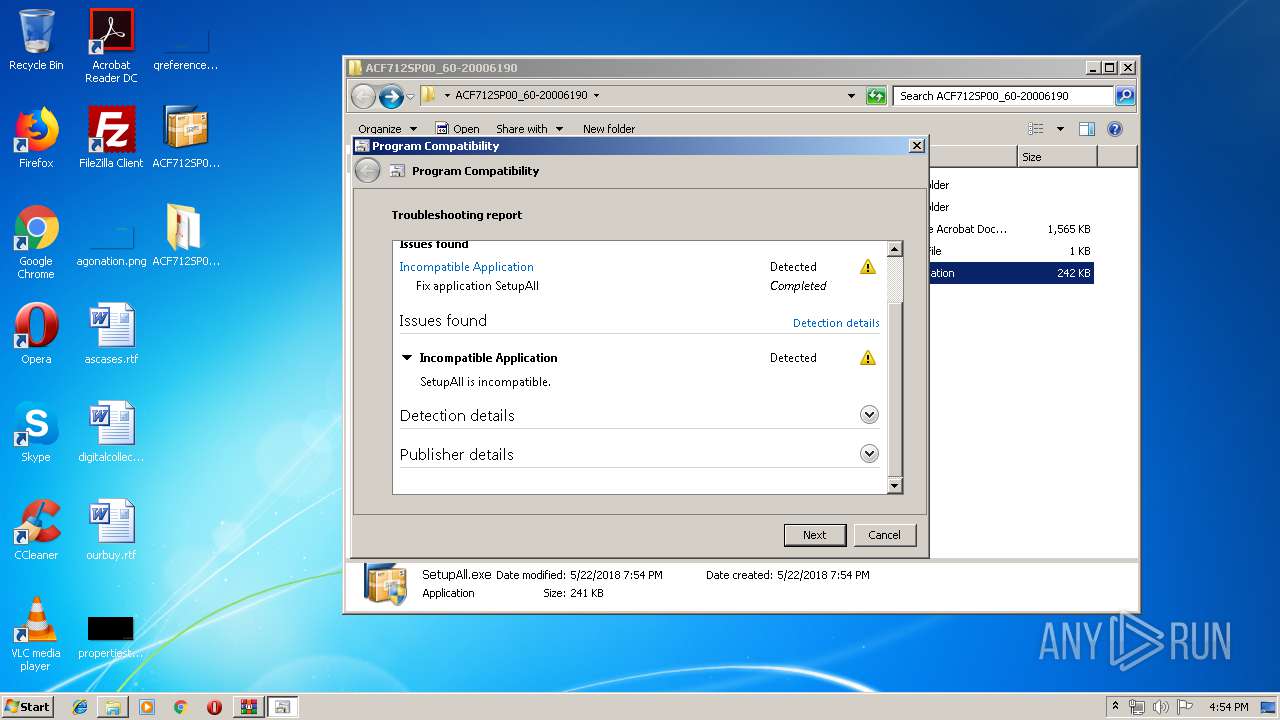
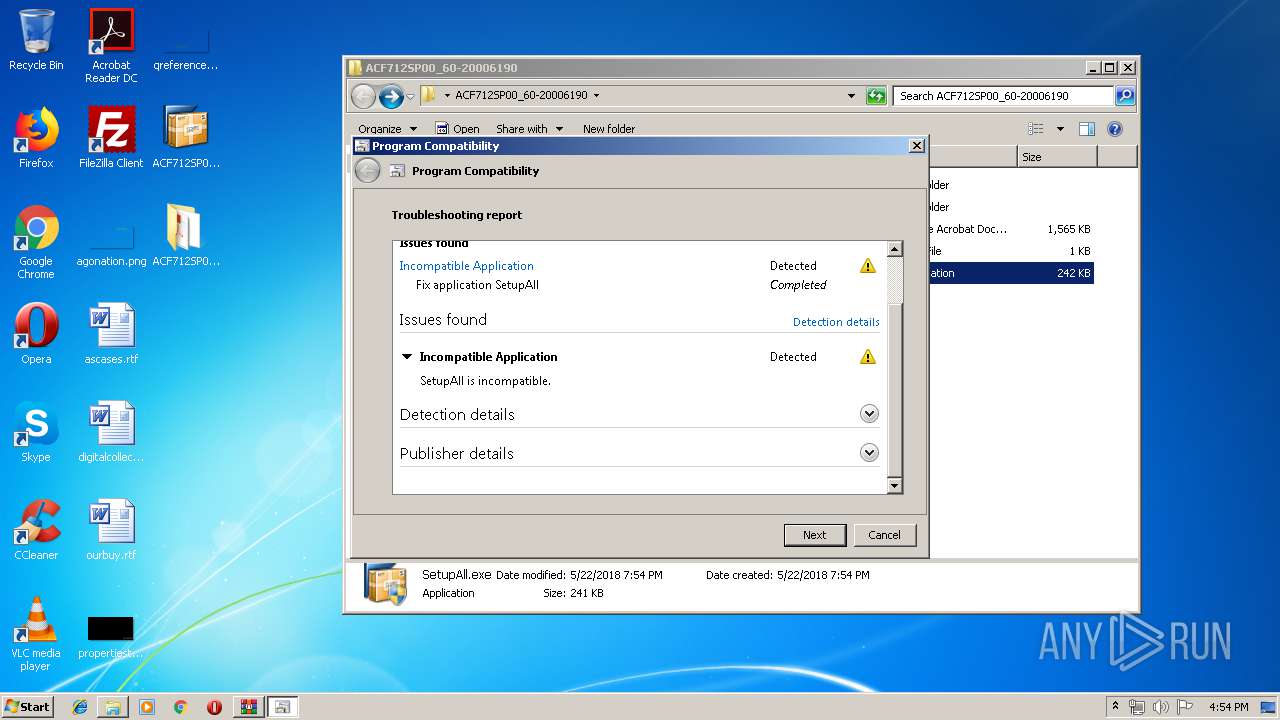
- SetupAll.exe (PID: 2588)
- SetupAll.exe (PID: 1480)
- NwSapSetup.exe (PID: 2488)
- NwSapSetup.exe (PID: 3560)
- SetupAll.exe (PID: 3016)
- SetupAll.exe (PID: 2436)
- SetupAll.exe (PID: 2848)
Starts Visual C# compiler
- sdiagnhost.exe (PID: 3596)
- sdiagnhost.exe (PID: 1684)
Loads the Task Scheduler COM API
- rundll32.exe (PID: 3612)
SUSPICIOUS
Creates files in the program directory
- WerFault.exe (PID: 3232)
- WerFault.exe (PID: 1508)
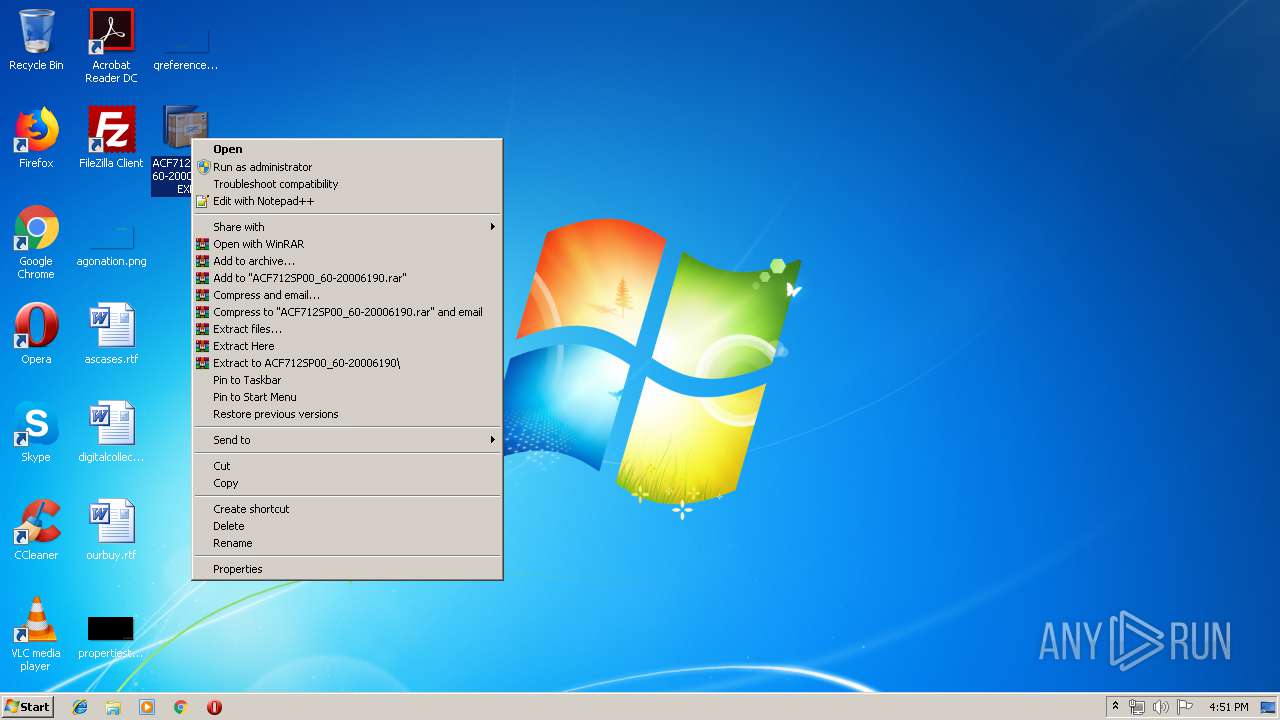
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3804)
- msdt.exe (PID: 2468)
Executed via COM
- sdiagnhost.exe (PID: 3596)
- sdiagnhost.exe (PID: 1684)
Uses RUNDLL32.EXE to load library
- msdt.exe (PID: 2468)
Creates files in the Windows directory
- svchost.exe (PID: 852)
Executed via Task Scheduler
- SetupAll.exe (PID: 2848)
- SetupAll.exe (PID: 2436)
Reads Internet Cache Settings
- msdt.exe (PID: 2468)
- explorer.exe (PID: 128)
Searches for installed software
- svchost.exe (PID: 824)
Reads internet explorer settings
- msdt.exe (PID: 2468)
INFO
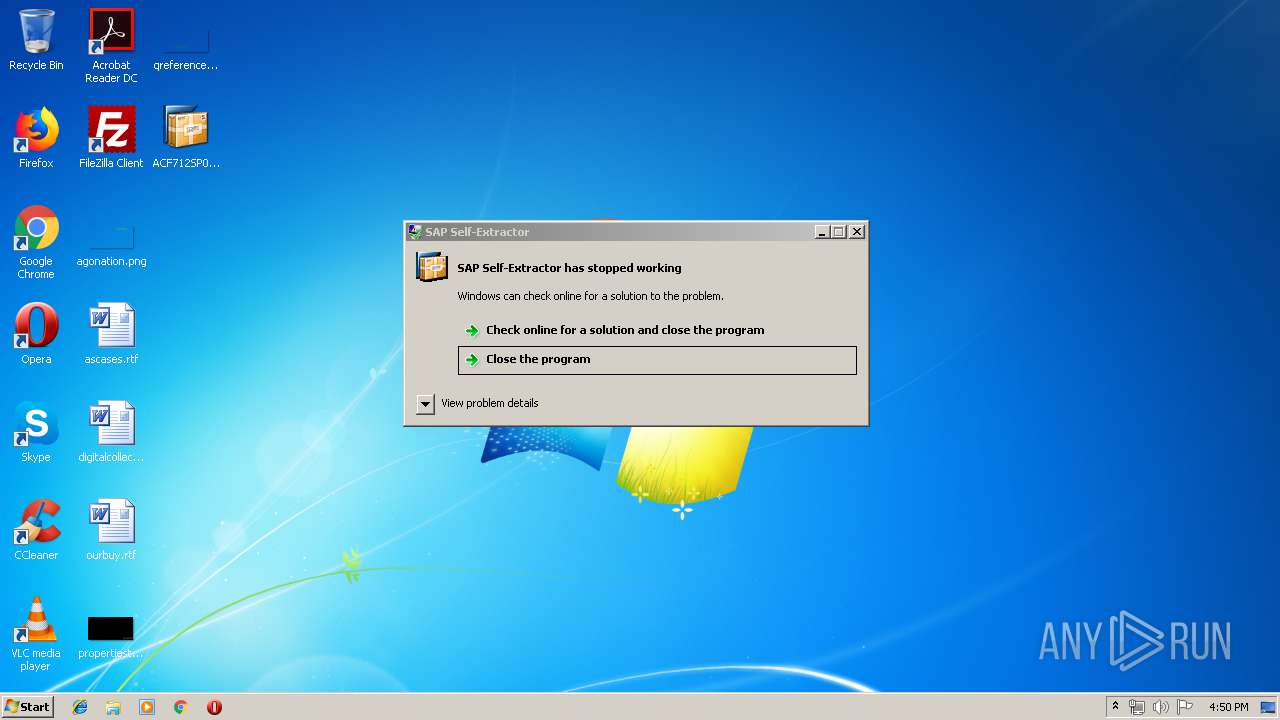
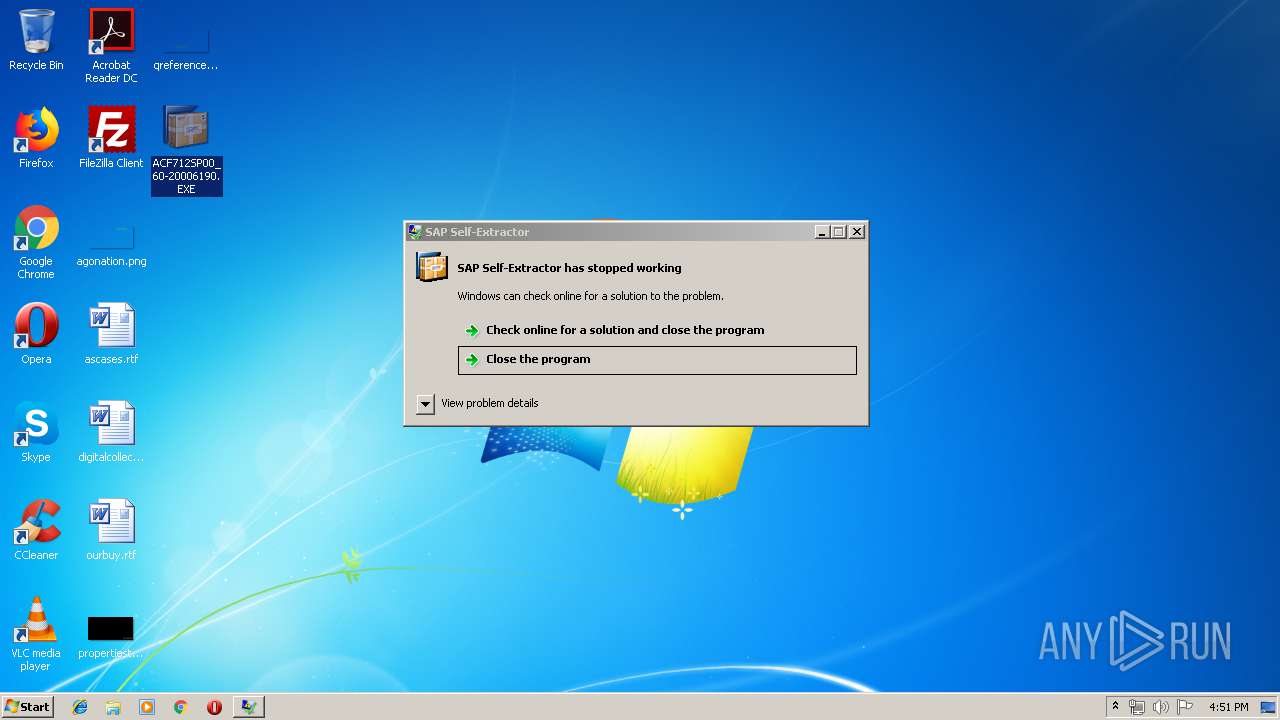
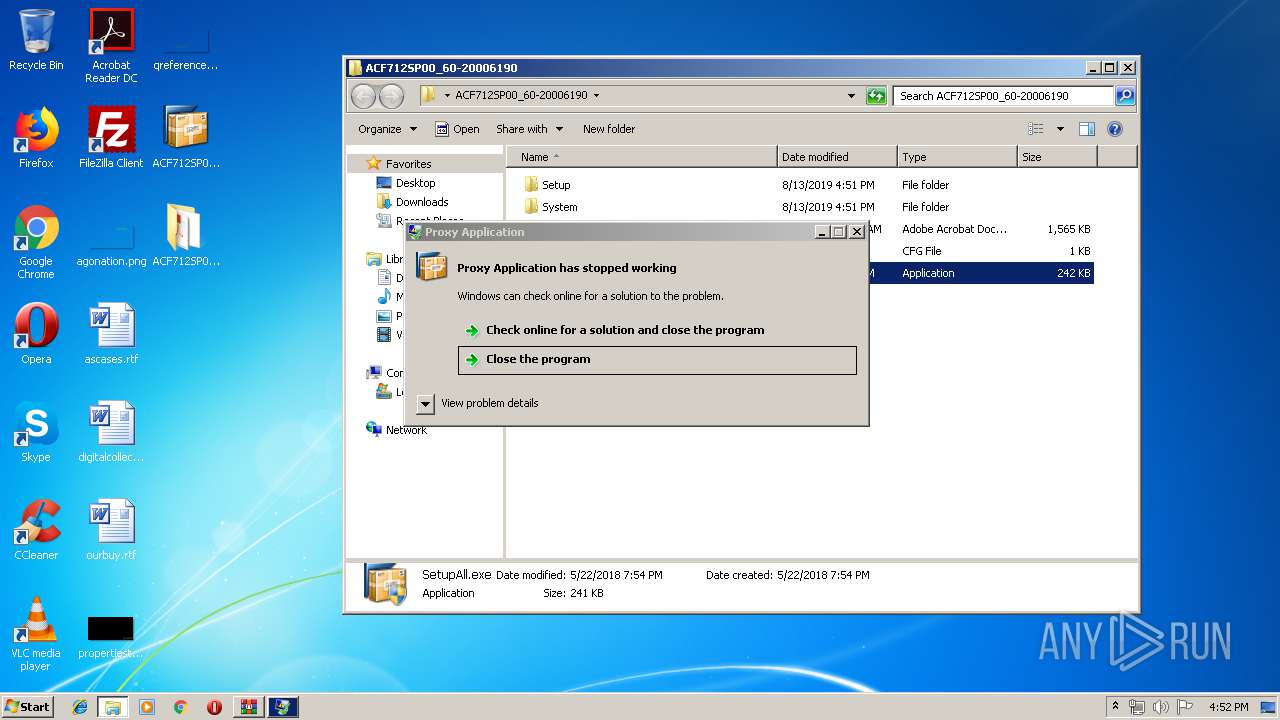
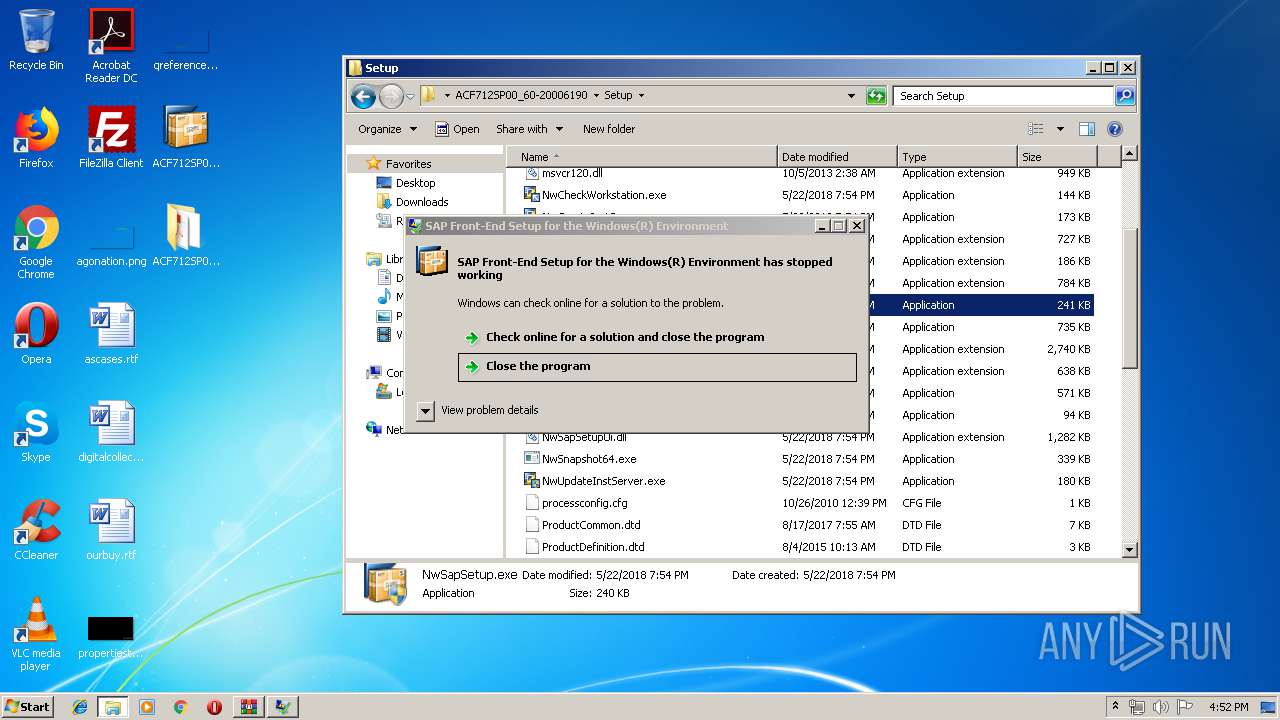
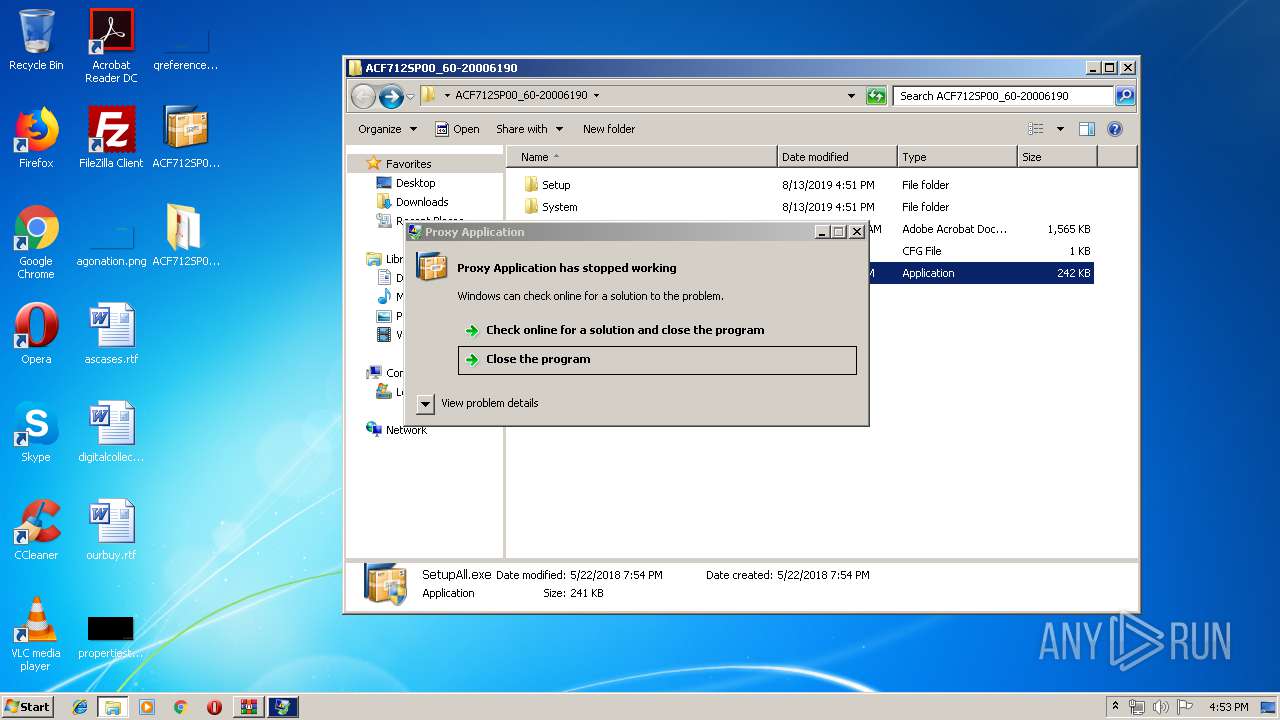
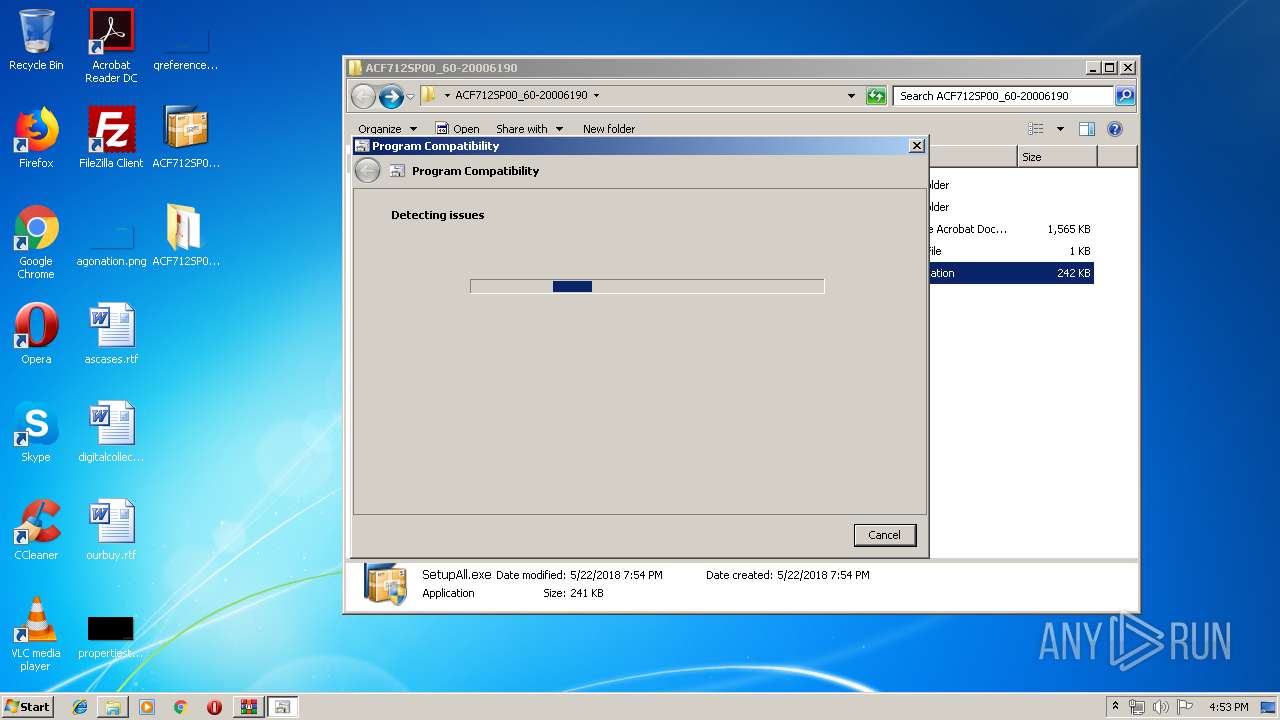
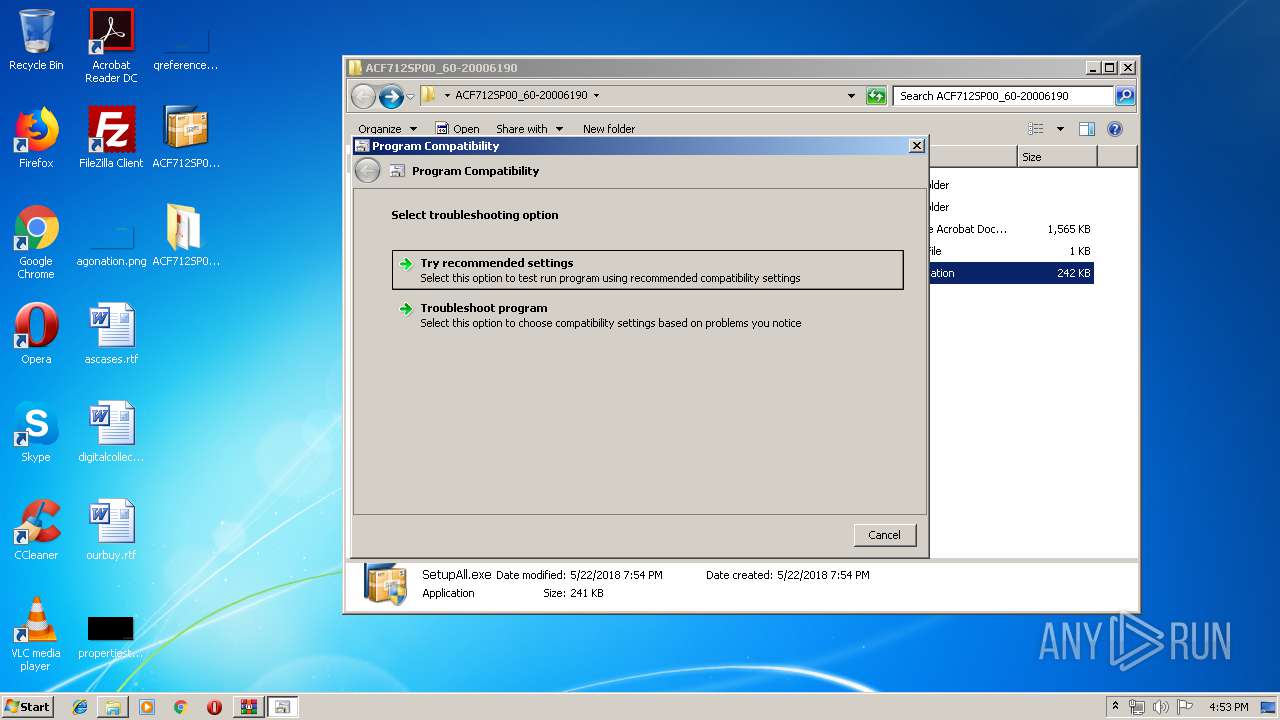
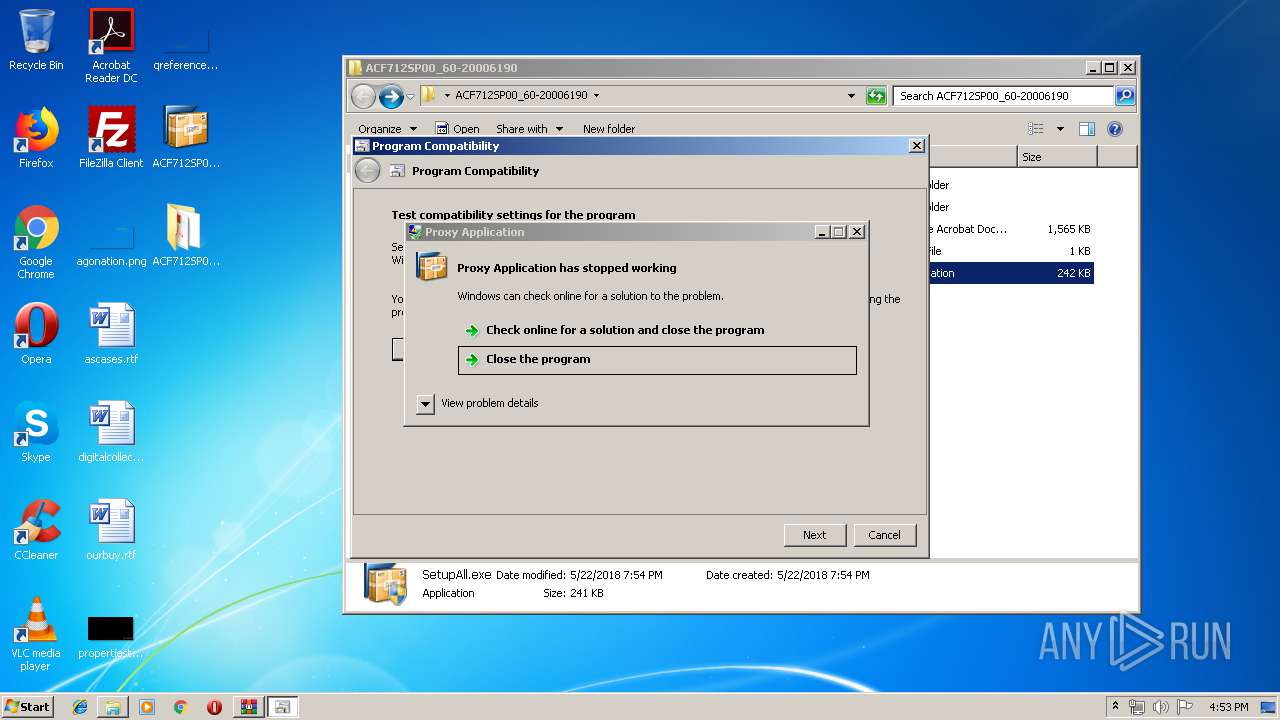
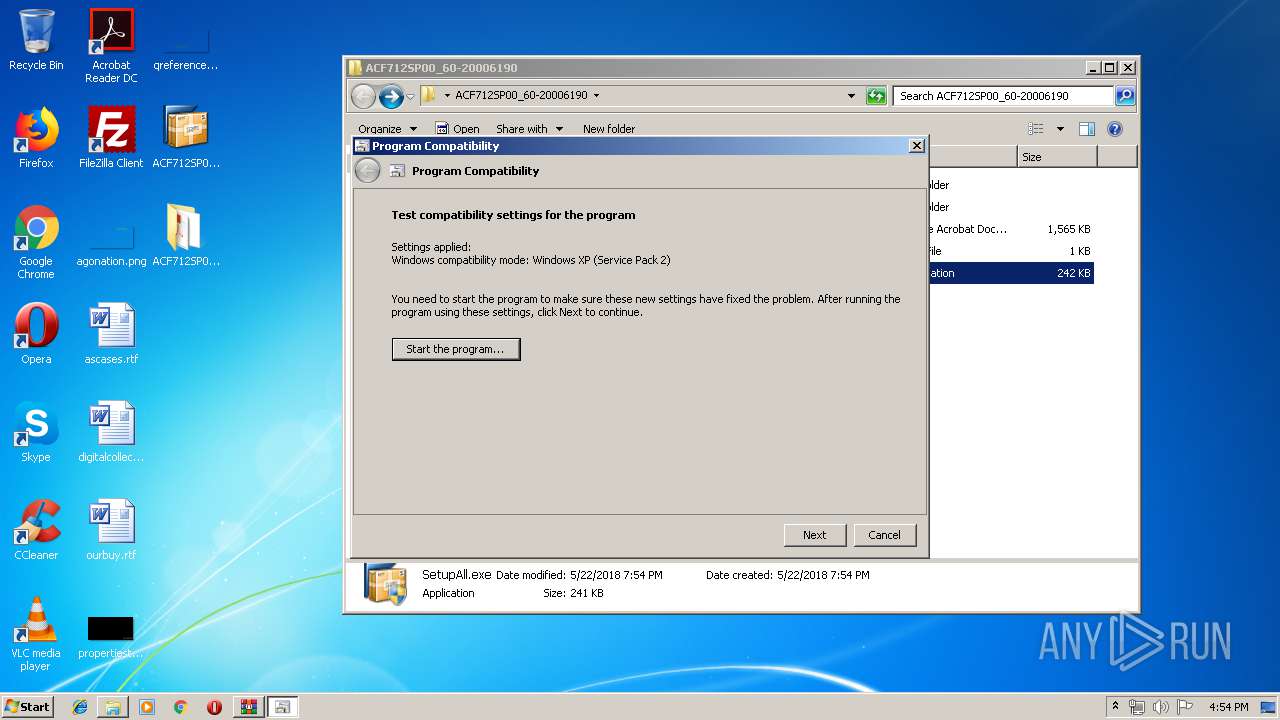
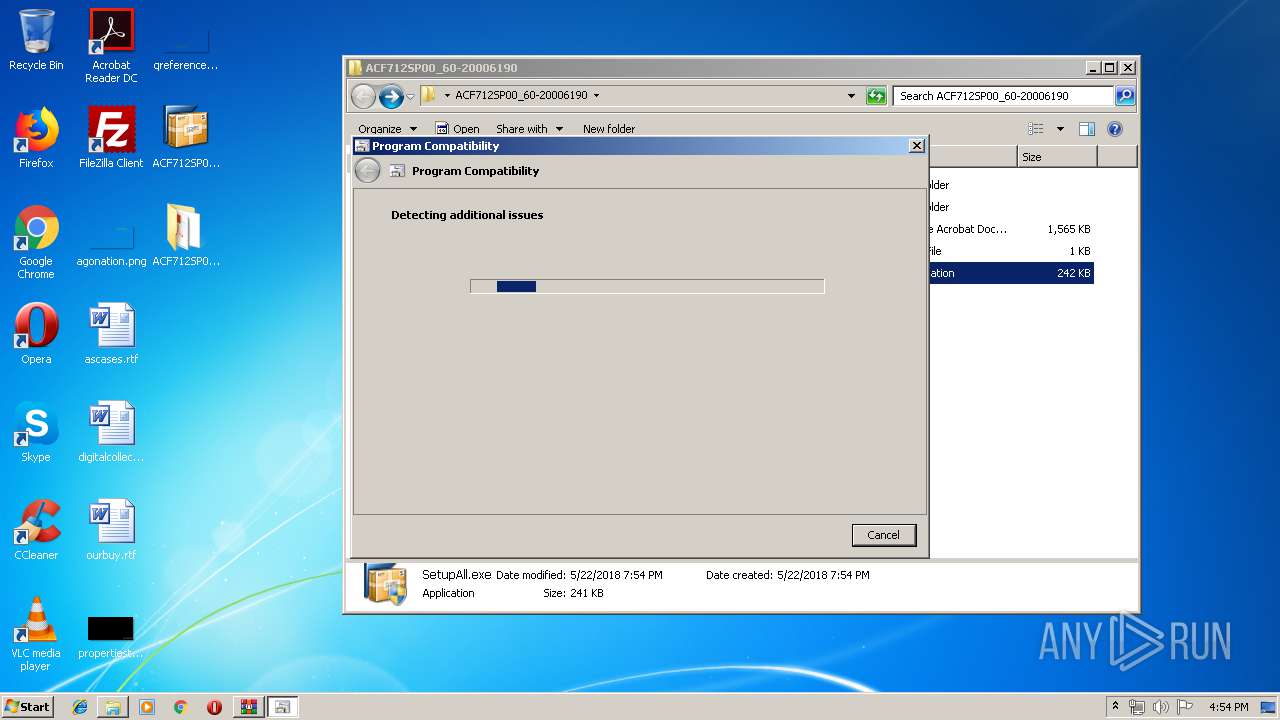
Application was crashed
- ACF712SP00_60-20006190.EXE (PID: 3748)
- ACF712SP00_60-20006190.EXE (PID: 3392)
- NwSapSetup.exe (PID: 3560)
- SetupAll.exe (PID: 1480)
- NwCreateInstServer.exe (PID: 3248)
- SetupAll.exe (PID: 3016)
- SetupAll.exe (PID: 2436)
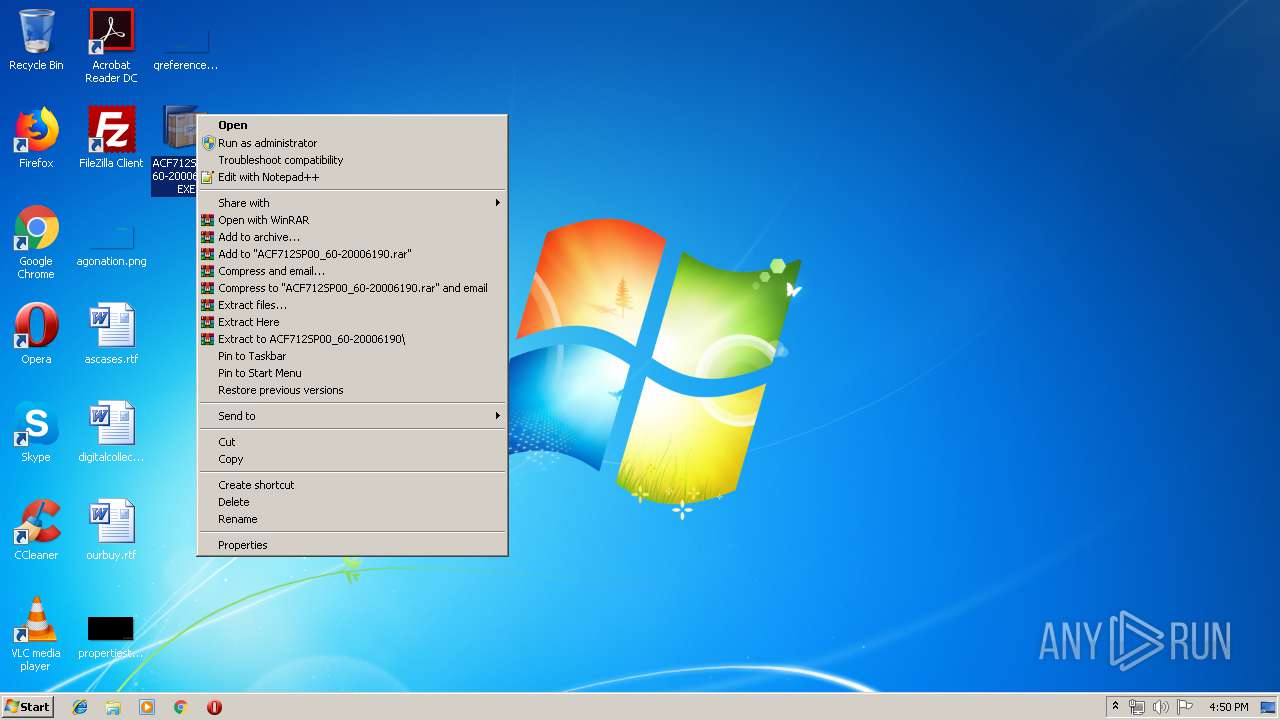
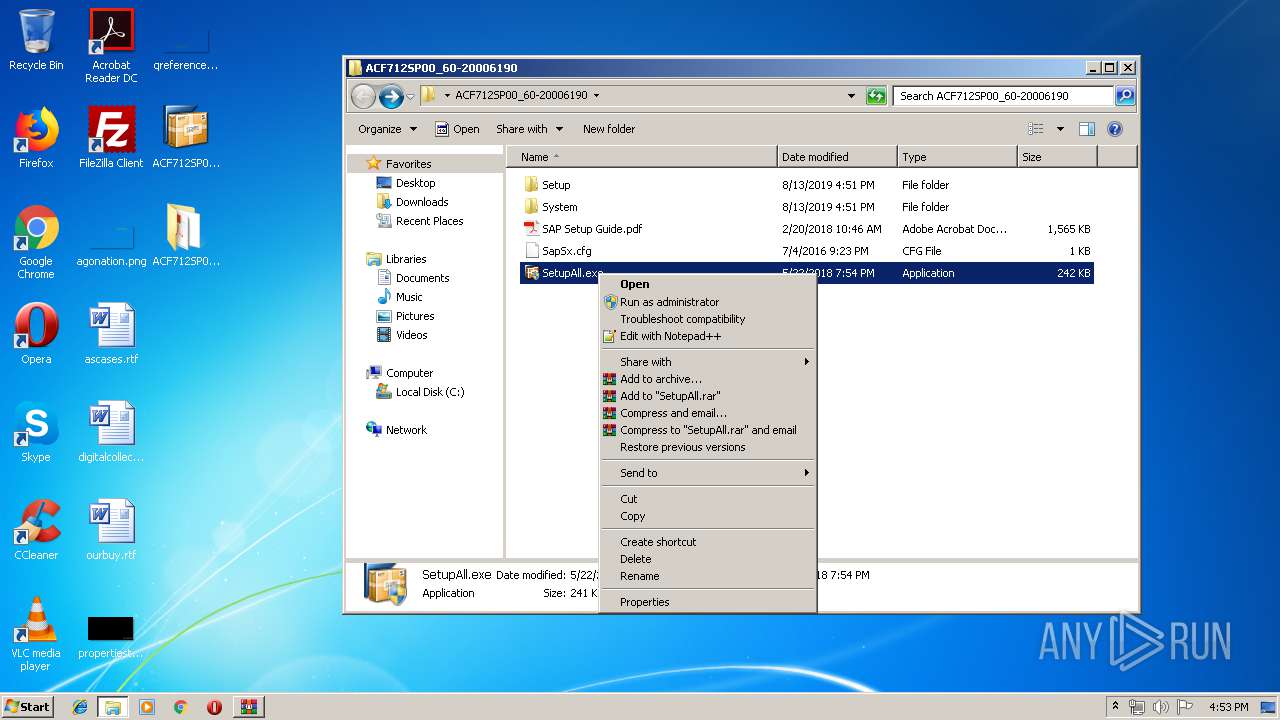
Manual execution by user
- ACF712SP00_60-20006190.EXE (PID: 3748)
- WinRAR.exe (PID: 3804)
- SetupAll.exe (PID: 2588)
- SetupAll.exe (PID: 1480)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3804)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:05:22 19:11:49+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 534016 |
| InitializedDataSize: | 232960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4bdb8 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.0.95.0 |
| ProductVersionNumber: | 9.0.95.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | SAP SE |
| FileDescription: | SAP Self-Extractor |
| FileVersion: | 9, 0, 95, 0 |
| InternalName: | SAP Self-Extractor |
| LegalCopyright: | Copyright (C)2001-2017 SAP SE |
| Copyright: | Copyright (C)2001-2017 SAP SE |
| LegalTrademarks: | - |
| OriginalFileName: | SapSx.exe |
| PrivateBuild: | - |
| ProductName: | SAP Front-End Setup for the Windows(R) Environment |
| ProductVersion: | 9, 0, 95, 0 |
| SpecialBuild: | Unicode Build |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-May-2018 17:11:49 |
| Detected languages: |
|
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | SAP SE |
| FileDescription: | SAP Self-Extractor |
| FileVersion: | 9, 0, 95, 0 |
| InternalName: | SAP Self-Extractor |
| LegalCopyright: | Copyright (C)2001-2017 SAP SE |
| Copyright: | Copyright (C)2001-2017 SAP SE |
| LegalTrademarks: | - |
| OriginalFilename: | SapSx.exe |
| PrivateBuild: | - |
| ProductName: | SAP Front-End Setup for the Windows(R) Environment |
| ProductVersion: | 9, 0, 95, 0 |
| SpecialBuild: | Unicode Build |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 22-May-2018 17:11:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00082558 | 0x00082600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.5234 |
.rdata | 0x00084000 | 0x0002004C | 0x00020200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.35275 |
.data | 0x000A5000 | 0x00008DC8 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.73472 |
.tls | 0x000AE000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x000AF000 | 0x0000CA08 | 0x0000CC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.59202 |
.reloc | 0x000BC000 | 0x00007C70 | 0x00007E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.56481 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.24837 | 948 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.29282 | 744 | Latin 1 / Western European | German - Germany | RT_ICON |
3 | 3.5546 | 296 | Latin 1 / Western European | German - Germany | RT_ICON |
4 | 5.98053 | 3752 | Latin 1 / Western European | German - Germany | RT_ICON |
5 | 6.1098 | 2216 | Latin 1 / Western European | German - Germany | RT_ICON |
6 | 4.08587 | 1384 | Latin 1 / Western European | German - Germany | RT_ICON |
7 | 2.12805 | 78 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 6.27499 | 3240 | Latin 1 / Western European | German - Germany | RT_ICON |
9 | 5.44703 | 1128 | Latin 1 / Western European | German - Germany | RT_ICON |
100 | 3.28591 | 376 | Latin 1 / Western European | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
Cabinet.dll |
KERNEL32.dll |
NETAPI32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
VERSION.dll |
Total processes
95
Monitored processes
35
Malicious processes
13
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 344 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,12288,512 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=winsrv:ConServerDllInitialization,2 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\System32\csrss.exe | — | ctfmon.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 400 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,12288,512 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=winsrv:ConServerDllInitialization,2 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\System32\csrss.exe | — | — | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 824 | C:\Windows\System32\svchost.exe -k LocalSystemNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 852 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1432 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES1DFE.tmp" "c:\Users\admin\AppData\Local\Temp\CSC1DEE.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 1480 | "C:\Users\admin\Desktop\ACF712SP00_60-20006190\SetupAll.exe" | C:\Users\admin\Desktop\ACF712SP00_60-20006190\SetupAll.exe | explorer.exe | ||||||||||||
User: admin Company: SAP SE Integrity Level: HIGH Description: Proxy Application Exit code: 3221225477 Version: 2018, 0, 95, 0 Modules
| |||||||||||||||
| 1496 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\xyxe0wtk.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 1508 | C:\Windows\system32\WerFault.exe -u -p 3248 -s 180 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1684 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 978
Read events
4 644
Write events
333
Delete events
1
Modification events
| (PID) Process: | (128) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (852) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 4 | |||
| (PID) Process: | (852) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 3 | |||
| (PID) Process: | (128) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\Qrfxgbc\NPS712FC00_60-20006190.RKR |
Value: 00000000010000000000000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF7093F1E8EE51D50100000000 | |||
| (PID) Process: | (128) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000001D00000025000000B4920C00090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101 | |||
| (PID) Process: | (3804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3804) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\ACF712SP00_60-20006190.EXE | |||
| (PID) Process: | (3804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
Executable files
44
Suspicious files
10
Text files
60
Unknown types
11
Dropped files
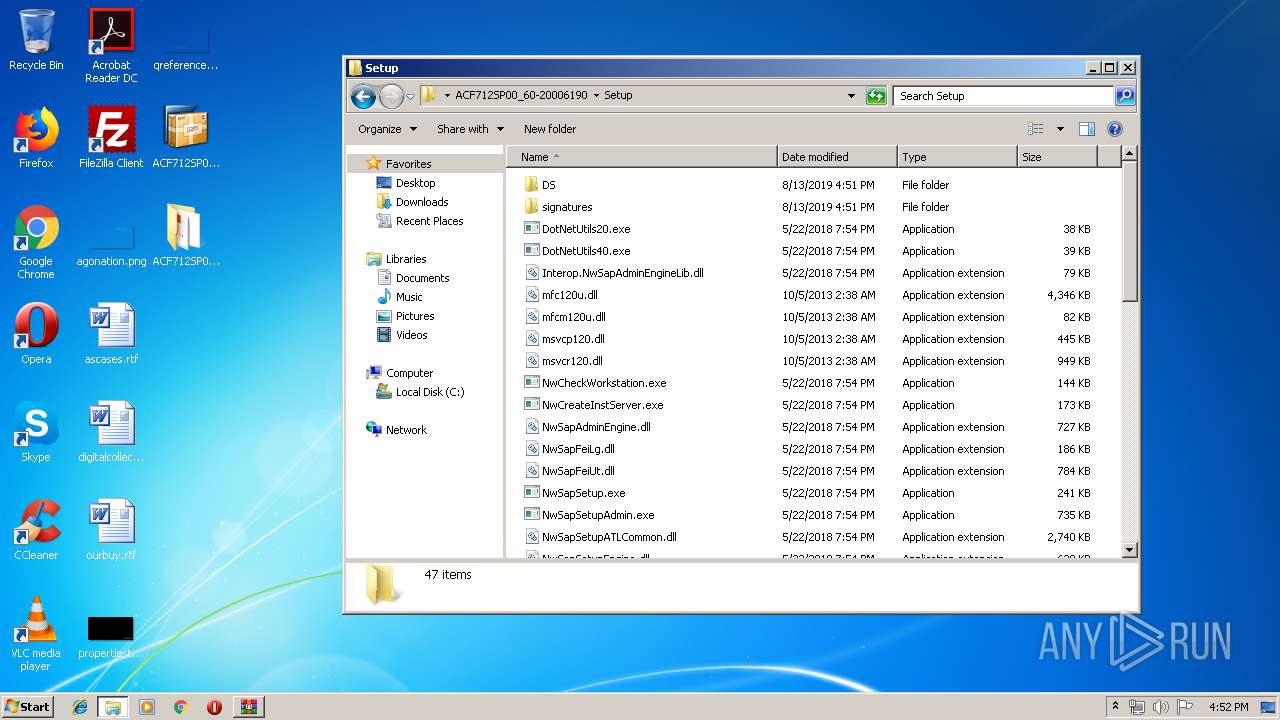
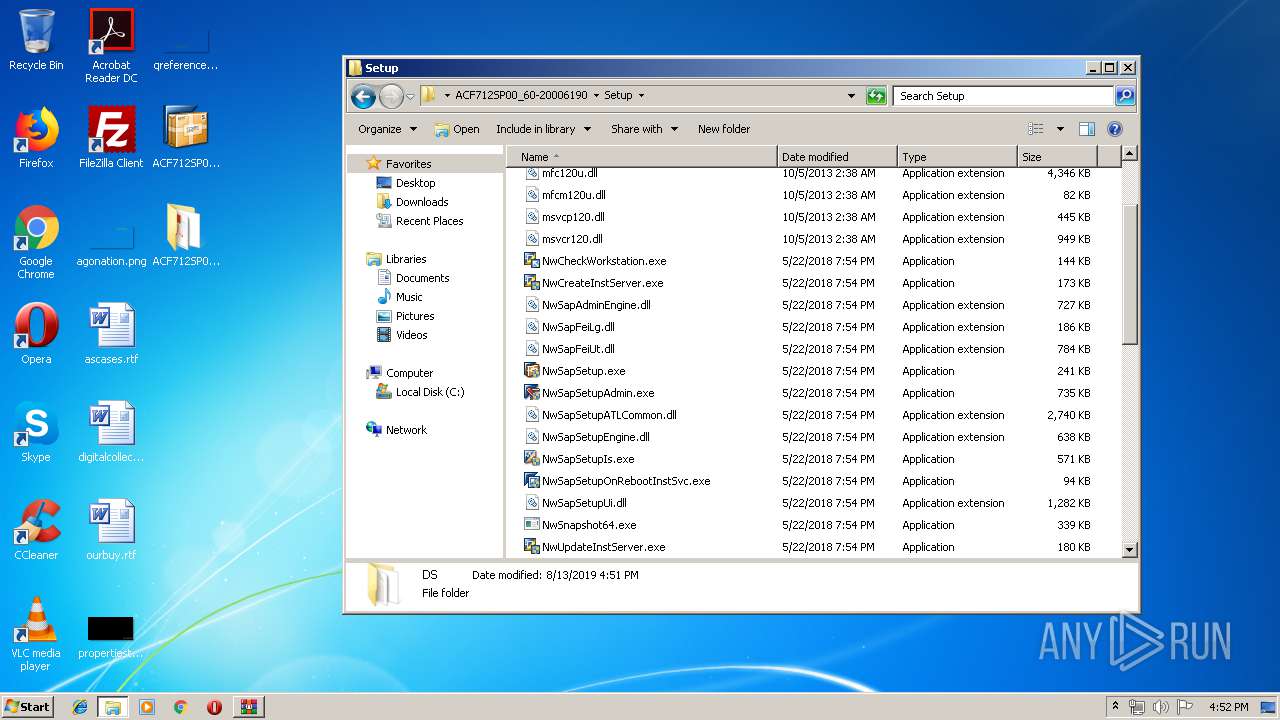
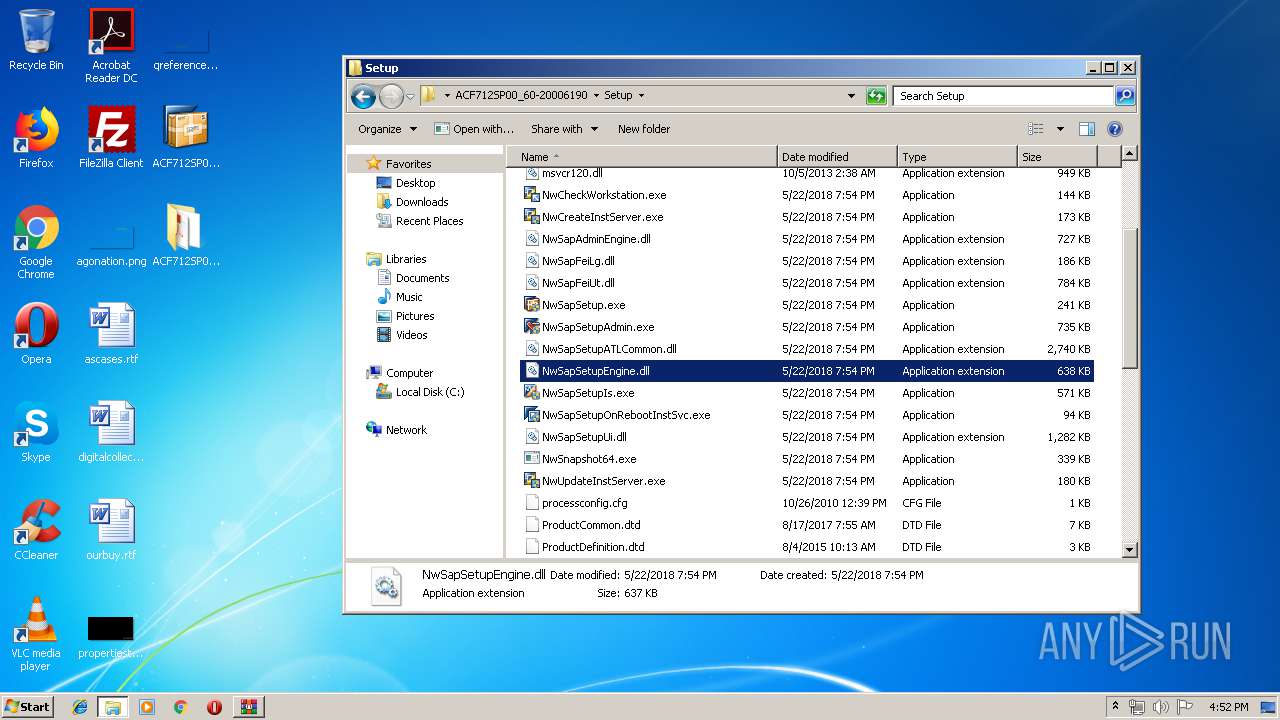
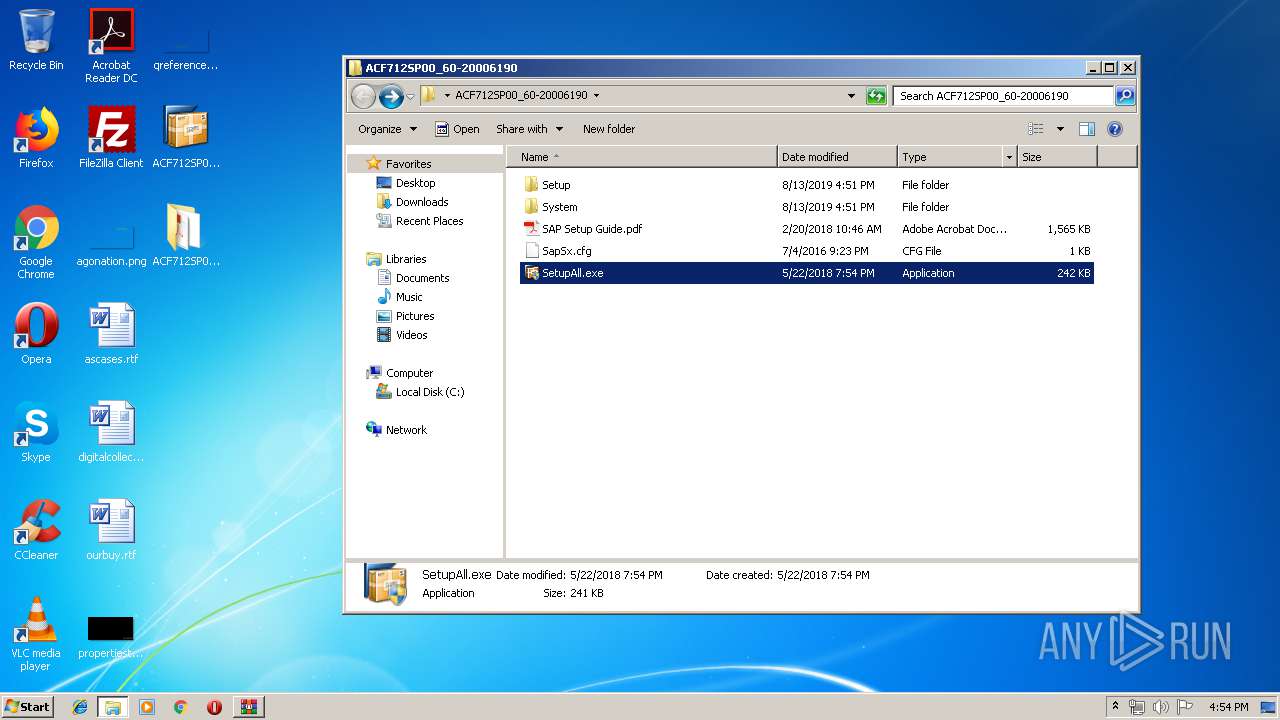
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 852 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
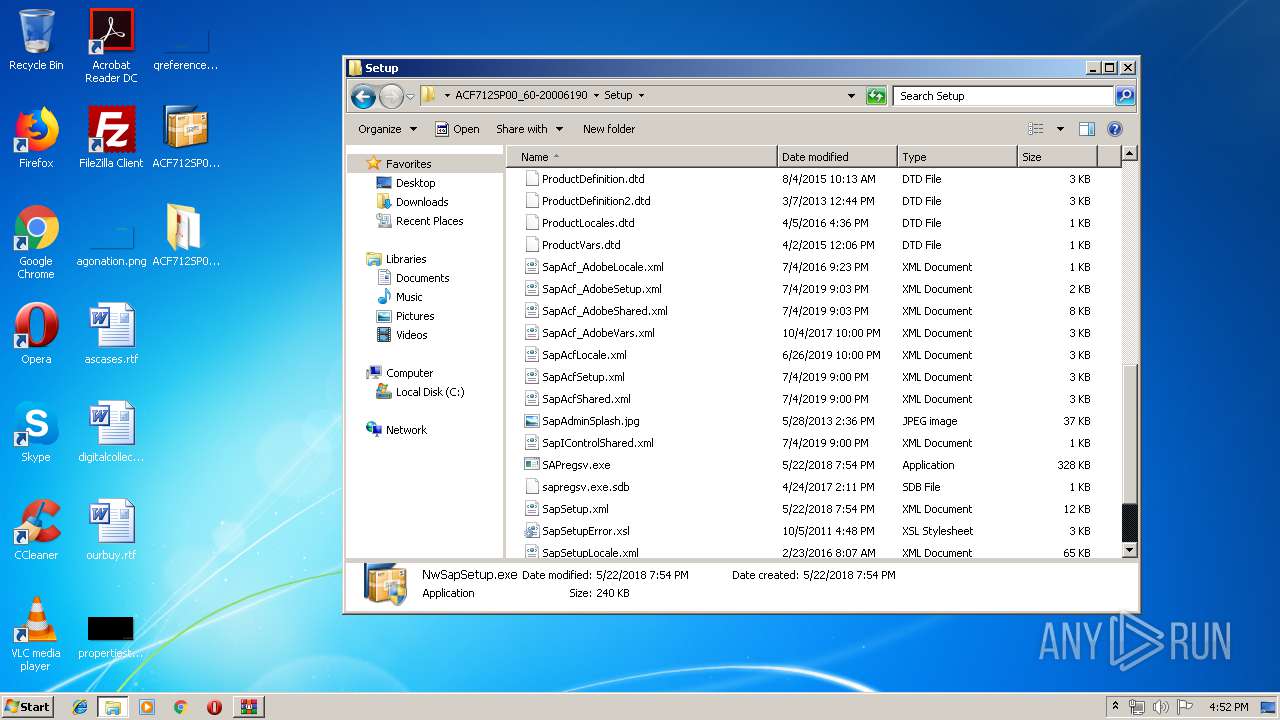
| 3804 | WinRAR.exe | C:\Users\admin\Desktop\ACF712SP00_60-20006190\Setup\DotNetUtils20.exe | executable | |
MD5:— | SHA256:— | |||
| 3804 | WinRAR.exe | C:\Users\admin\Desktop\ACF712SP00_60-20006190\SAP Setup Guide.pdf | ||
MD5:— | SHA256:— | |||
| 3804 | WinRAR.exe | C:\Users\admin\Desktop\ACF712SP00_60-20006190\SetupAll.exe | executable | |
MD5:— | SHA256:— | |||
| 3804 | WinRAR.exe | C:\Users\admin\Desktop\ACF712SP00_60-20006190\SapSx.cfg | text | |
MD5:— | SHA256:— | |||
| 3804 | WinRAR.exe | C:\Users\admin\Desktop\ACF712SP00_60-20006190\Setup\DotNetUtils40.exe | executable | |
MD5:— | SHA256:— | |||
| 3804 | WinRAR.exe | C:\Users\admin\Desktop\ACF712SP00_60-20006190\Setup\Interop.NwSapAdminEngineLib.dll | executable | |
MD5:— | SHA256:— | |||
| 3804 | WinRAR.exe | C:\Users\admin\Desktop\ACF712SP00_60-20006190\Setup\NwSapSetupAdmin.exe | executable | |
MD5:— | SHA256:— | |||
| 3804 | WinRAR.exe | C:\Users\admin\Desktop\ACF712SP00_60-20006190\Setup\NwSapFeiLg.dll | executable | |
MD5:— | SHA256:— | |||
| 3804 | WinRAR.exe | C:\Users\admin\Desktop\ACF712SP00_60-20006190\Setup\NwCreateInstServer.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|