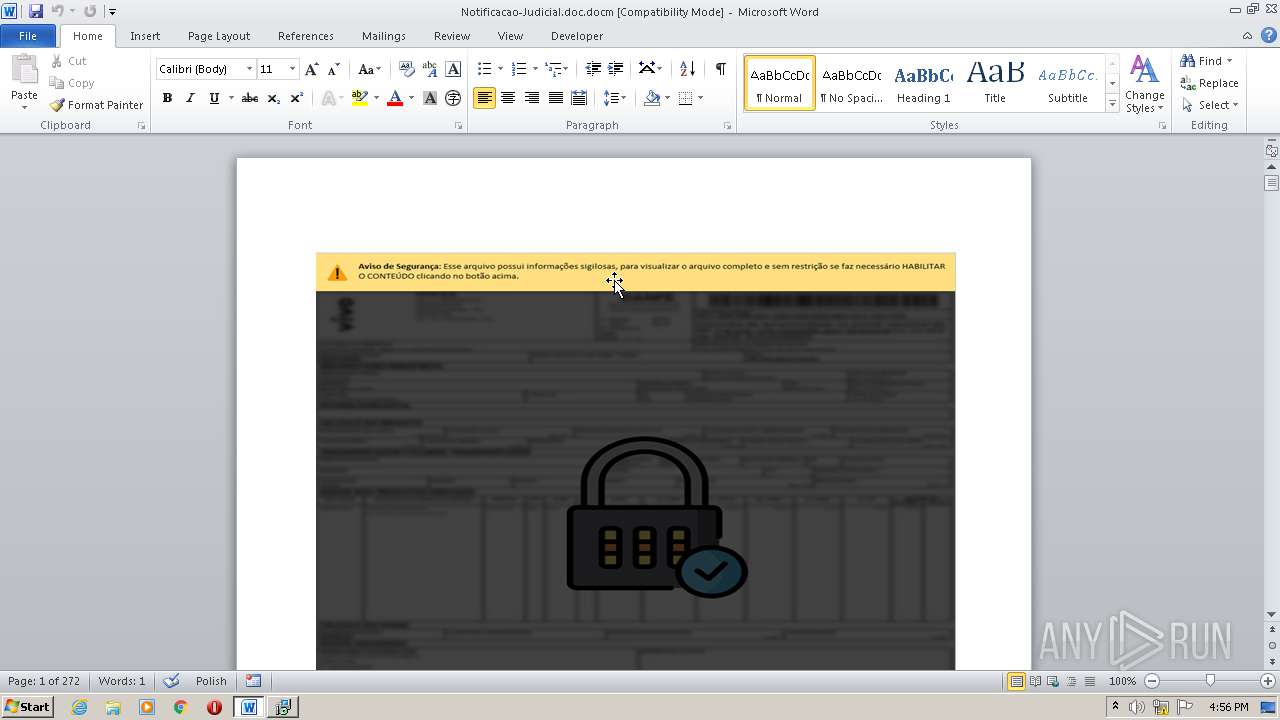
| download: | Notificacao-Judicial.doc |
| Full analysis: | https://app.any.run/tasks/c9ab2f54-84de-4bdd-bd98-48574afc5bc3 |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2020, 16:55:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | Microsoft OOXML |
| MD5: | CD929CCBA2C3615256DCBF4EA0EF8062 |
| SHA1: | 8F09A937DDC15F5522788718A9483B48557A287A |
| SHA256: | 24A67ECE50933155FABEDCCF7DF8B32E1C4D45636EFEB720383D8C5DEACE76DB |
| SSDEEP: | 12288:gcpZjPu8VQrLkwO8tFACyhSPHTqXjvgn4mZa0mYE8xLnIGqG+yMdosgr:gkc8VZwjazGTWjvXmM0mYh5IGFXsgr |
MALICIOUS
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 2472)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2472)
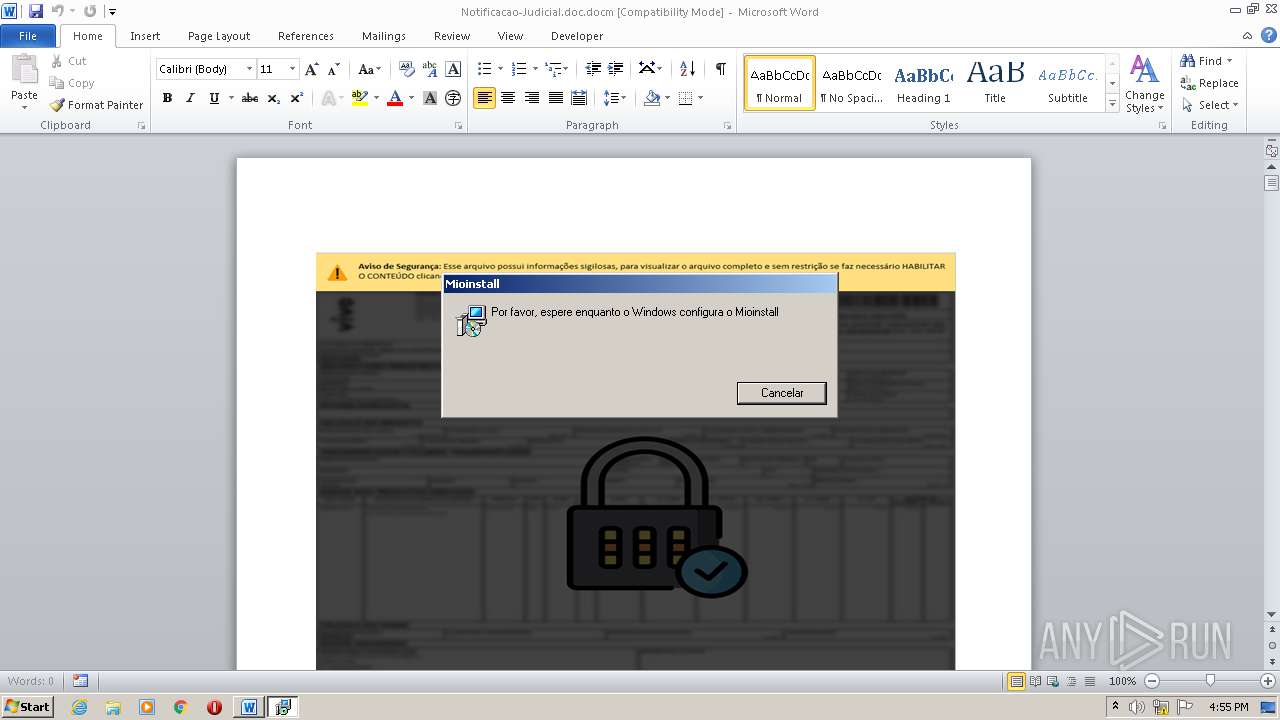
Application was dropped or rewritten from another process
- ms.exe (PID: 2800)
SUSPICIOUS
Creates files in the program directory
- WINWORD.EXE (PID: 2472)
Drops a file that was compiled in debug mode
- WINWORD.EXE (PID: 2472)
- msiexec.exe (PID: 3720)
Executed as Windows Service
- vssvc.exe (PID: 3644)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3720)
- ms.exe (PID: 2800)
Creates a directory in Program Files
- msiexec.exe (PID: 3720)
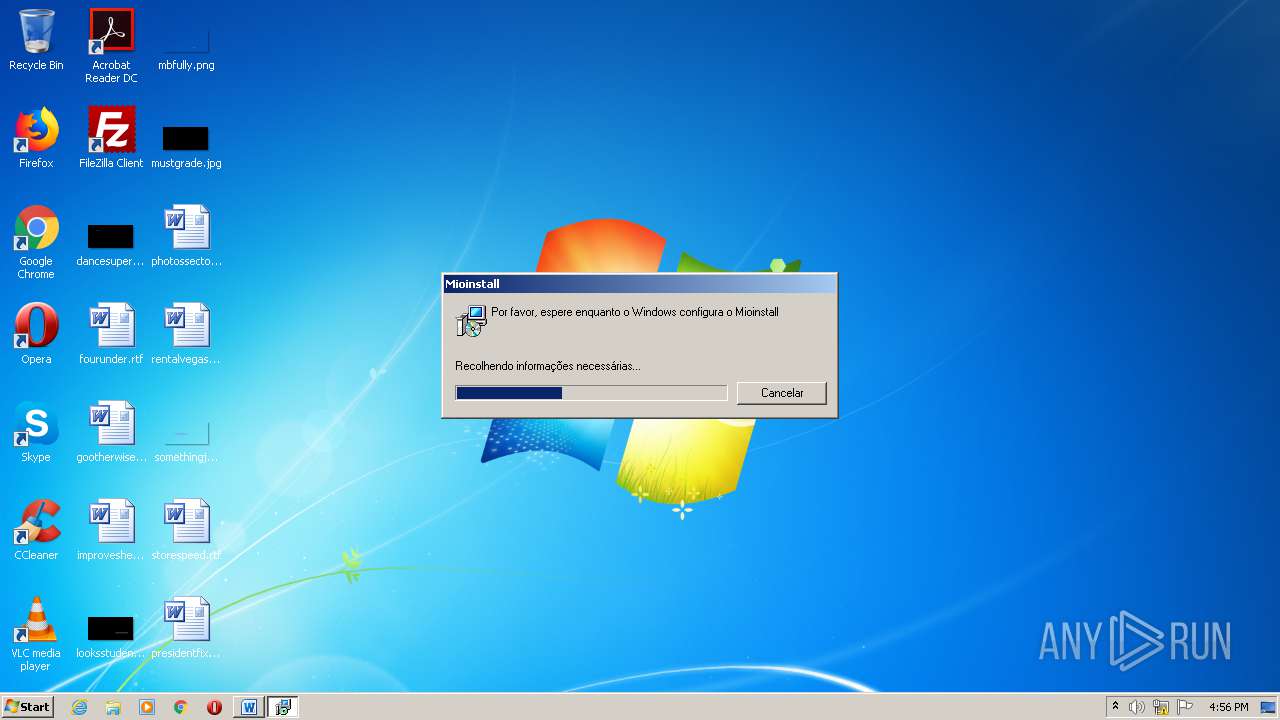
Starts Microsoft Installer
- ms.exe (PID: 2800)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2472)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3644)
Creates files in the user directory
- WINWORD.EXE (PID: 2472)
Creates a software uninstall entry
- msiexec.exe (PID: 3720)
Searches for installed software
- msiexec.exe (PID: 3720)
Application launched itself
- msiexec.exe (PID: 3720)
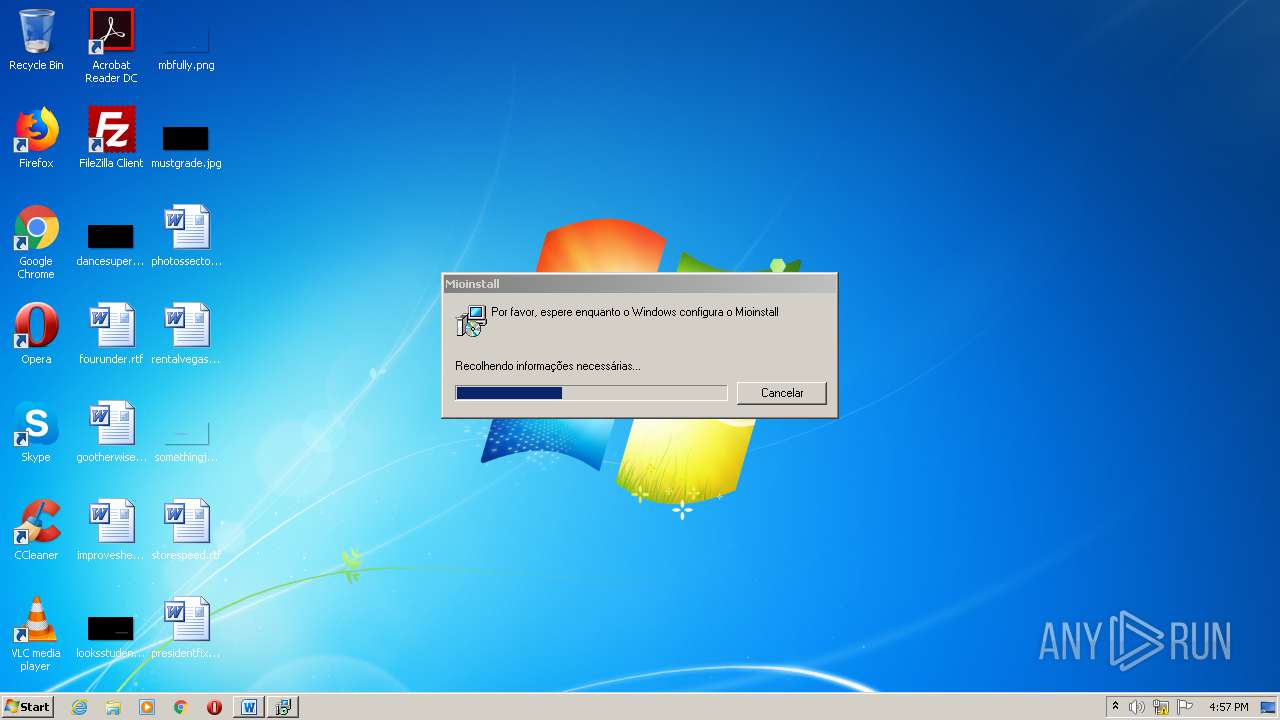
Manual execution by user
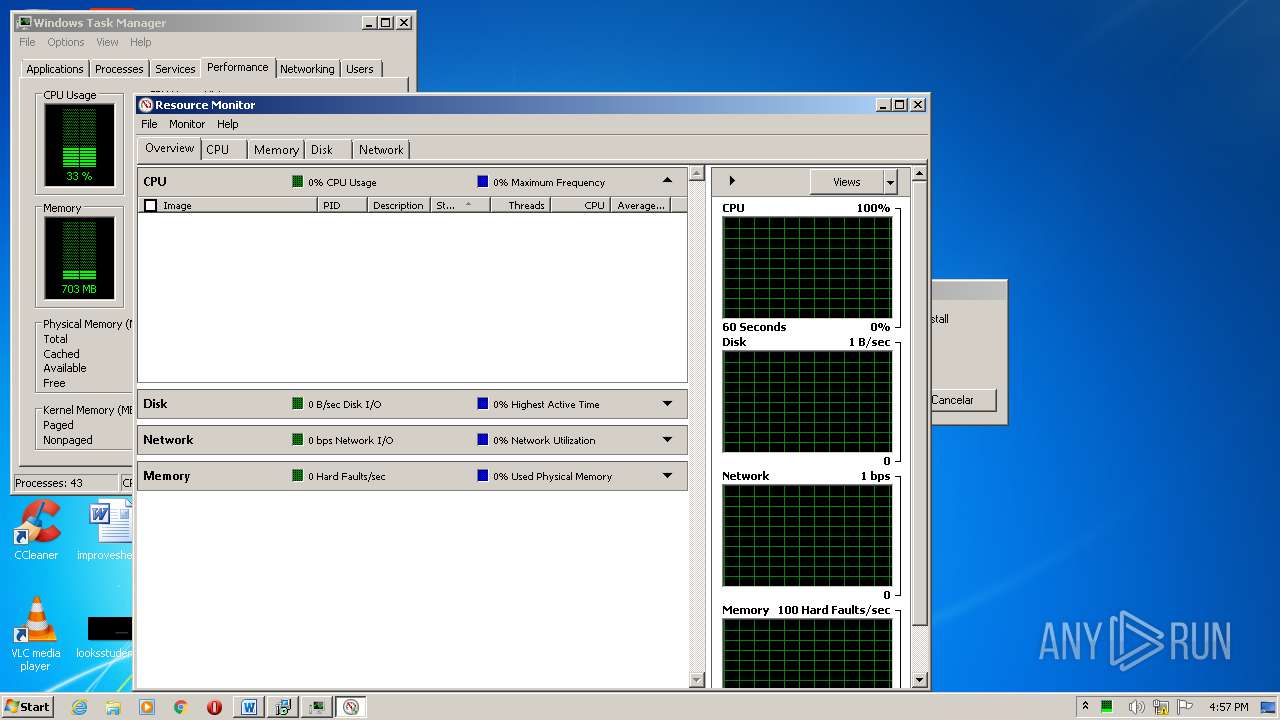
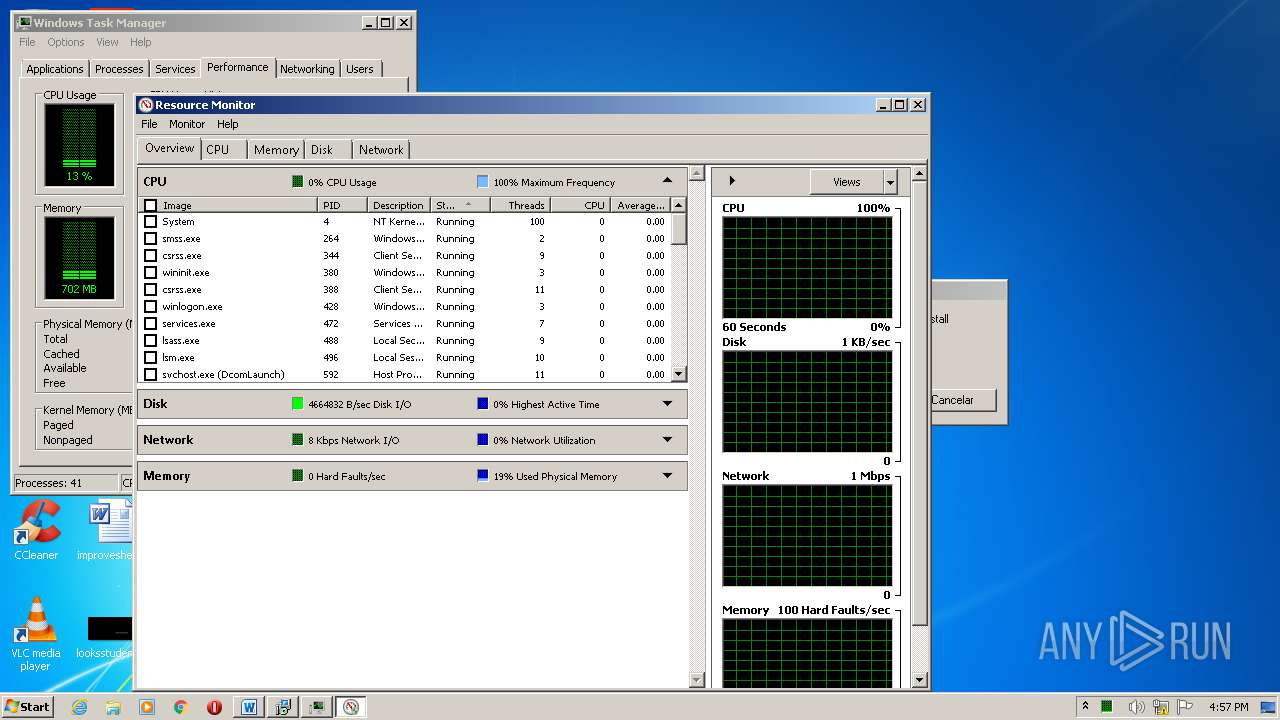
- taskmgr.exe (PID: 1992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0xa1fe8fa1 |
| ZipCompressedSize: | 430 |
| ZipUncompressedSize: | 1768 |
| ZipFileName: | [Content_Types].xml |
Total processes
49
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
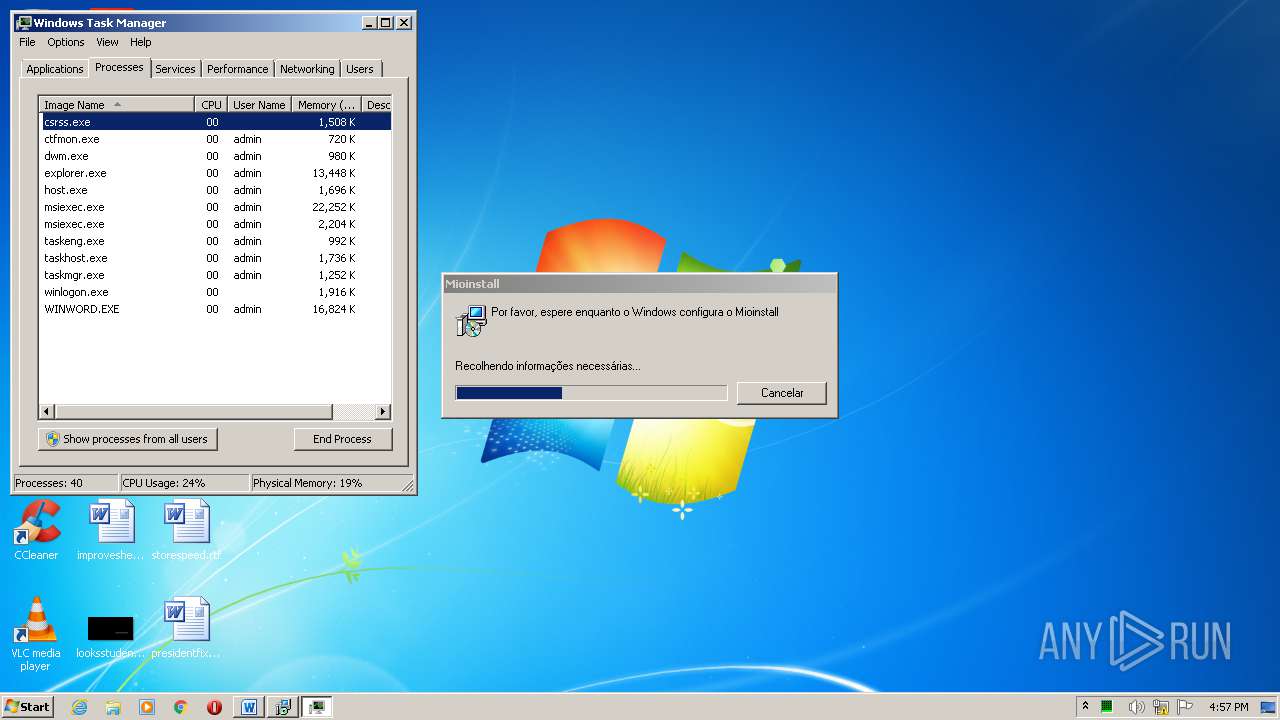
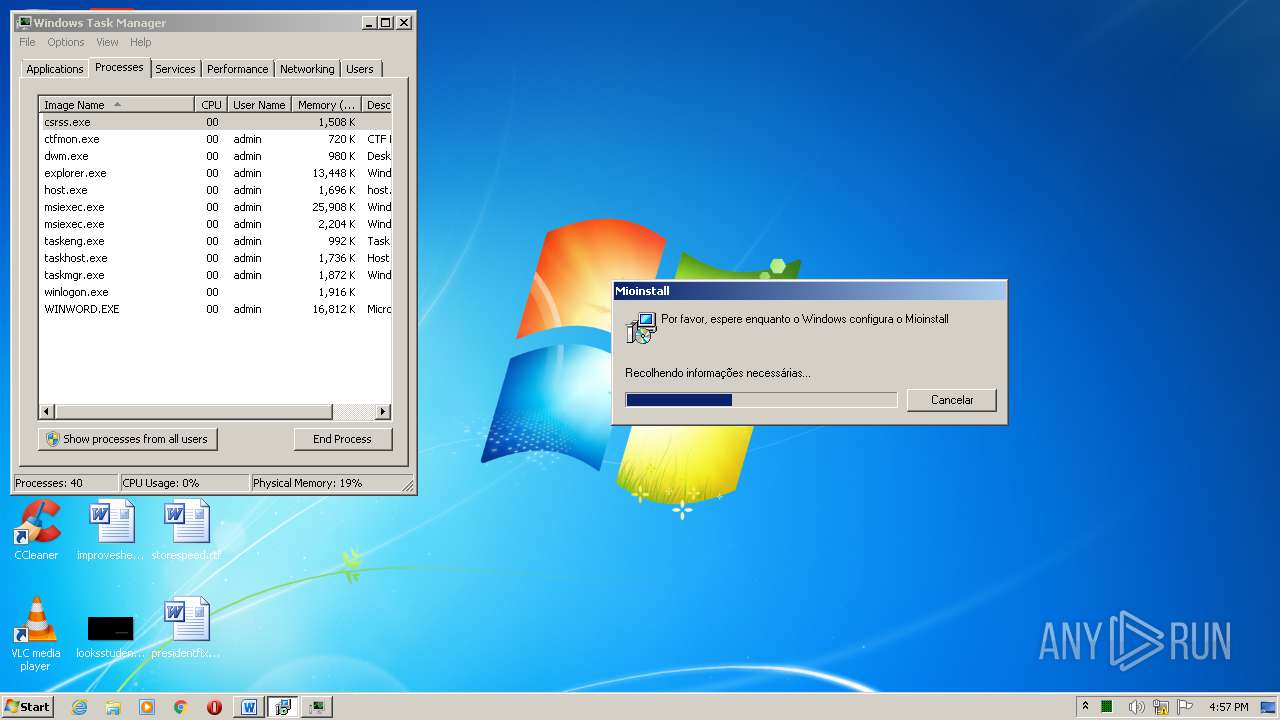
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1496 | C:\Windows\system32\MsiExec.exe -Embedding 52A78129A81BB65F0F4D15324205B7A1 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1992 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2472 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Notificacao-Judicial.doc.docm" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2800 | C:\ProgramData\Memsys\ms.exe | C:\ProgramData\Memsys\ms.exe | WINWORD.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3644 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3720 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
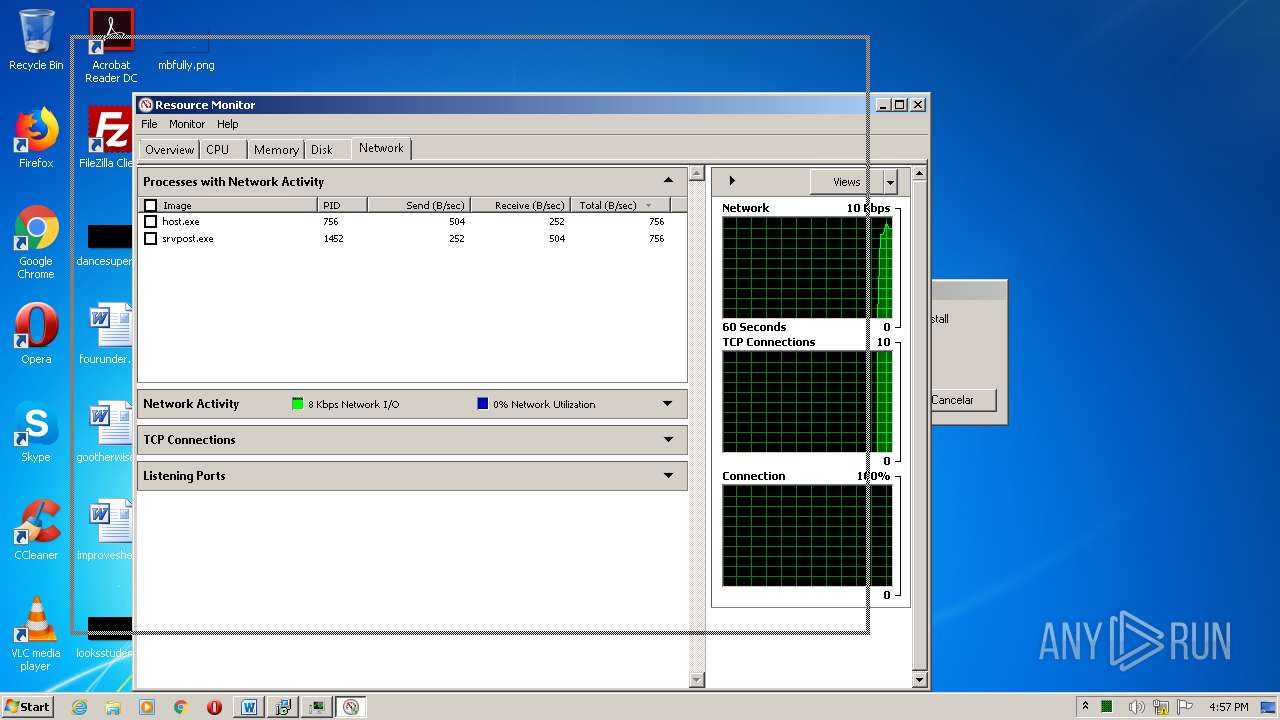
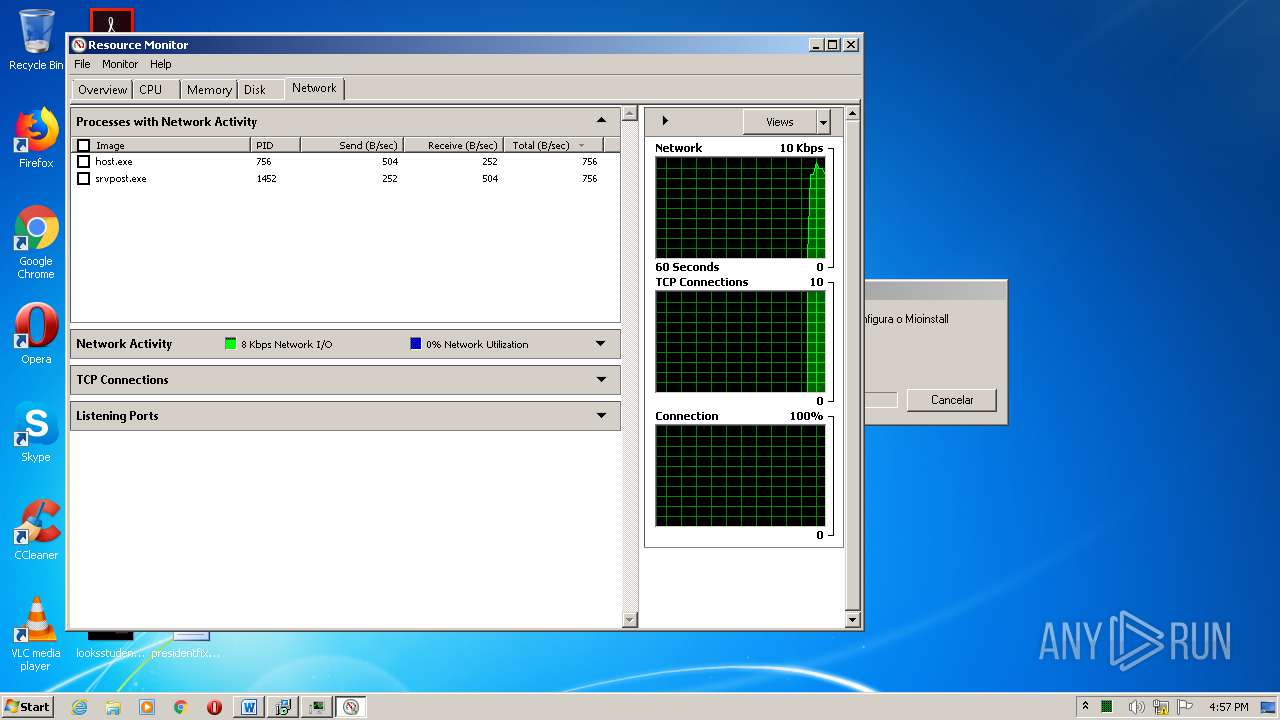
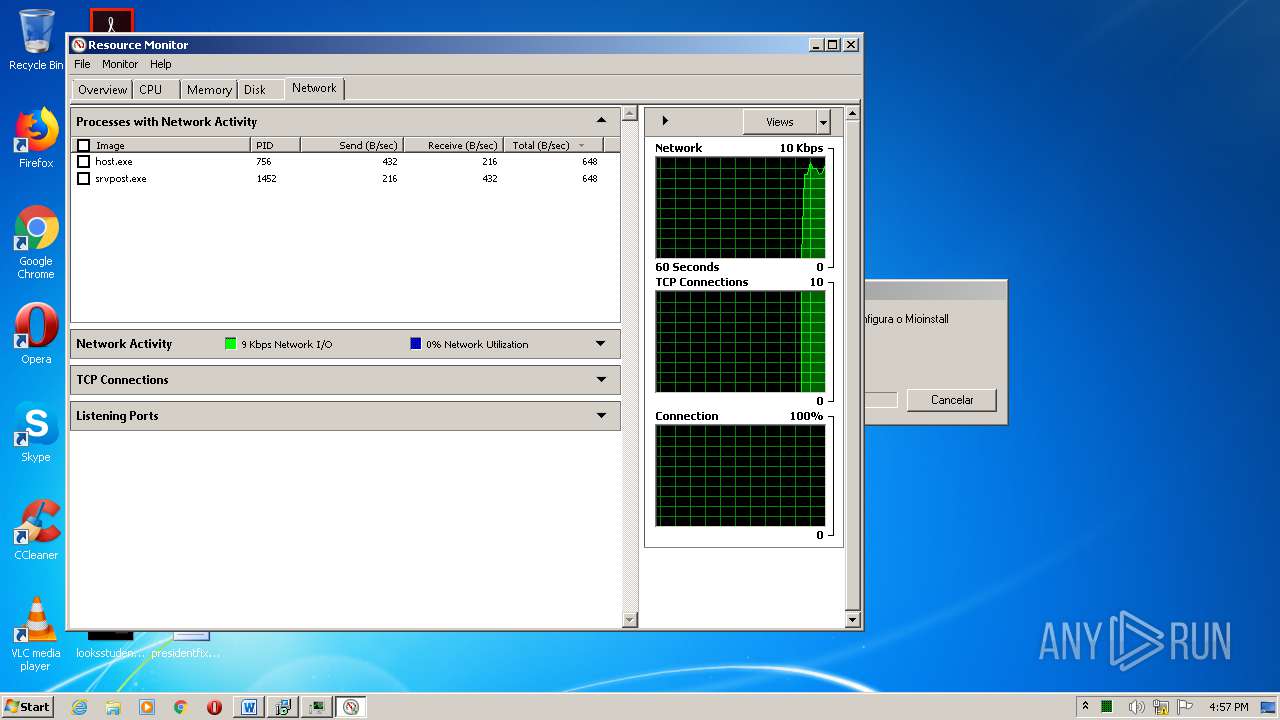
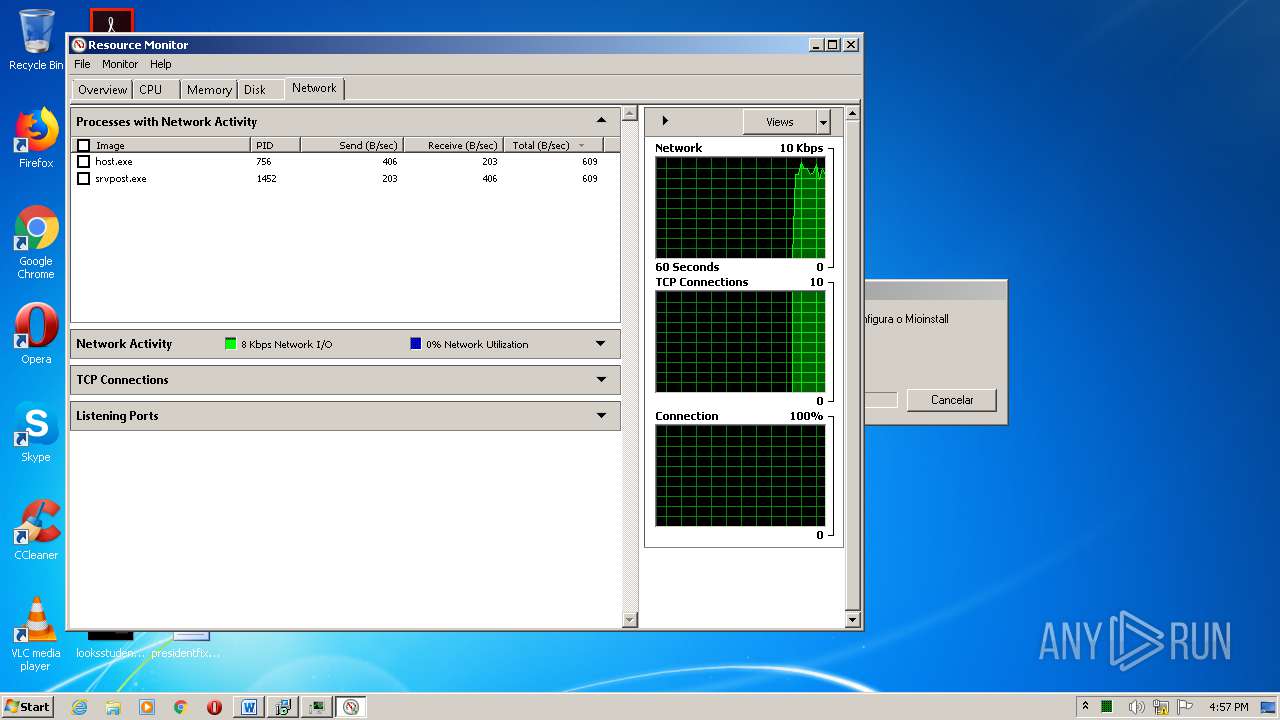
| 3784 | "C:\Windows\System32\perfmon.exe" /res | C:\Windows\System32\perfmon.exe | taskmgr.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Resource and Performance Monitor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3848 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\Public\Documents\HDSKUDHS.msi" | C:\Windows\System32\msiexec.exe | — | ms.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 281
Read events
1 437
Write events
747
Delete events
97
Modification events
| (PID) Process: | (2472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 9t" |
Value: 39742200A8090000010000000000000000000000 | |||
| (PID) Process: | (2472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2472) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
5
Suspicious files
5
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2472 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD099.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2472 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\msoD935.tmp | — | |
MD5:— | SHA256:— | |||
| 3720 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3720 | msiexec.exe | C:\Windows\Installer\MSI21C6.tmp | — | |
MD5:— | SHA256:— | |||
| 3720 | msiexec.exe | C:\Windows\Installer\MSI22B2.tmp | — | |
MD5:— | SHA256:— | |||
| 3720 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF8B07CF25C8634BD4.TMP | — | |
MD5:— | SHA256:— | |||
| 3644 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 3720 | msiexec.exe | C:\Windows\Installer\MSI23AE.tmp | — | |
MD5:— | SHA256:— | |||
| 3720 | msiexec.exe | C:\Config.Msi\191a28.rbs | — | |
MD5:— | SHA256:— | |||
| 3720 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFC8A673268429B0D3.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
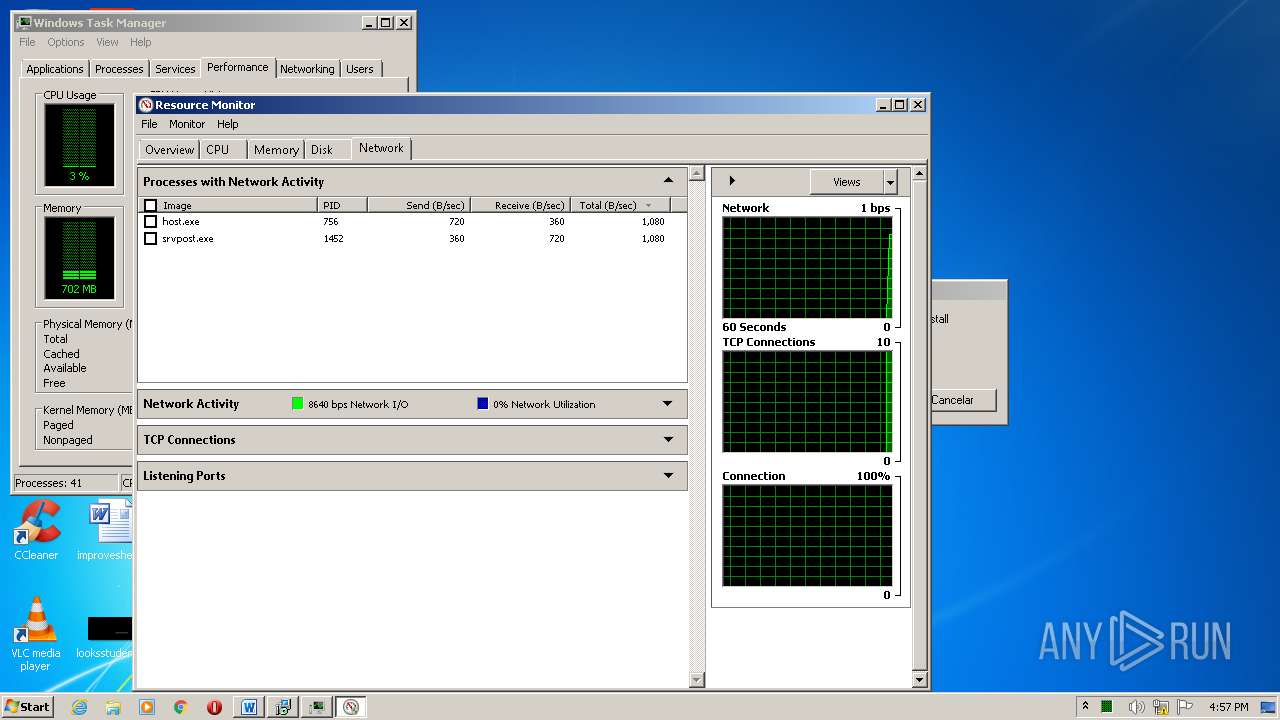
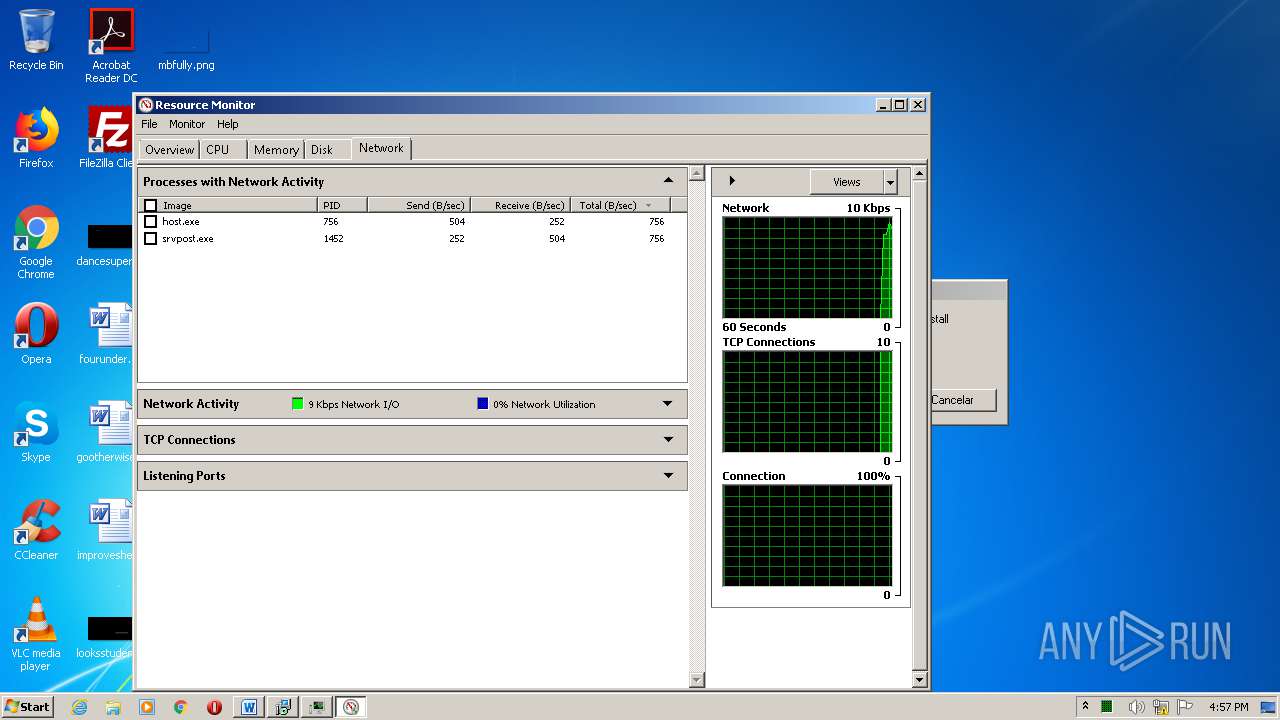
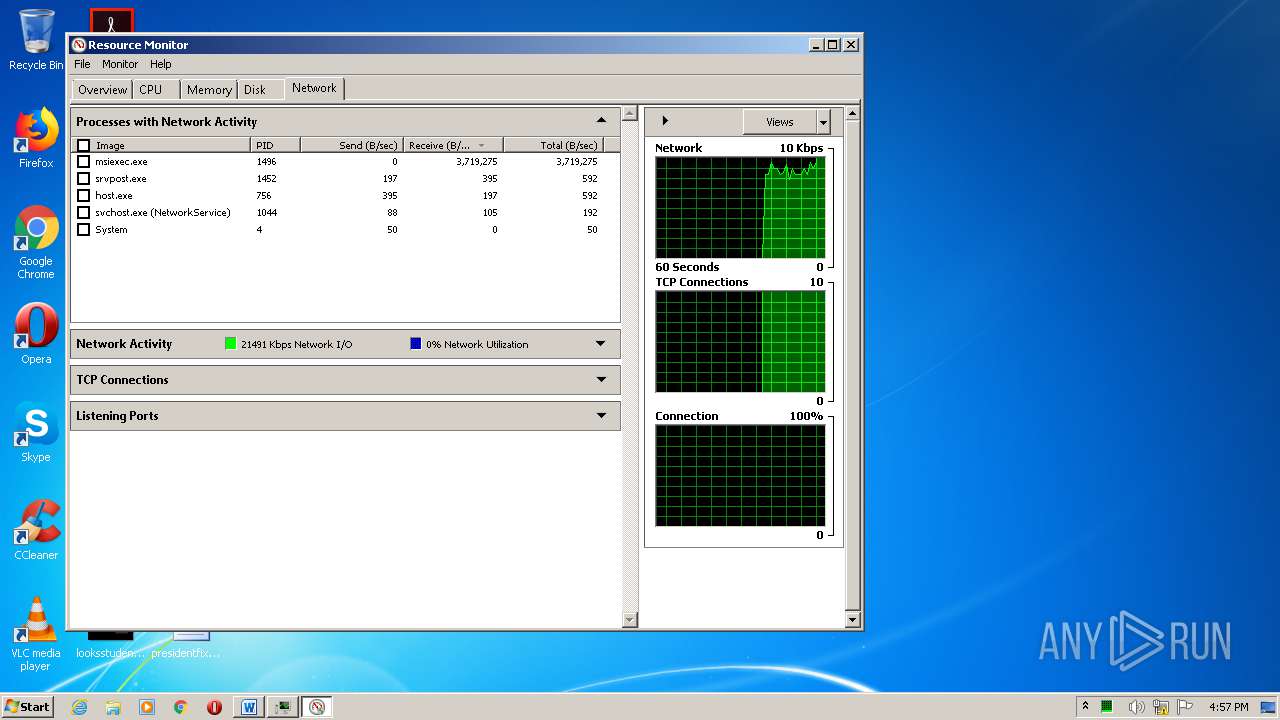
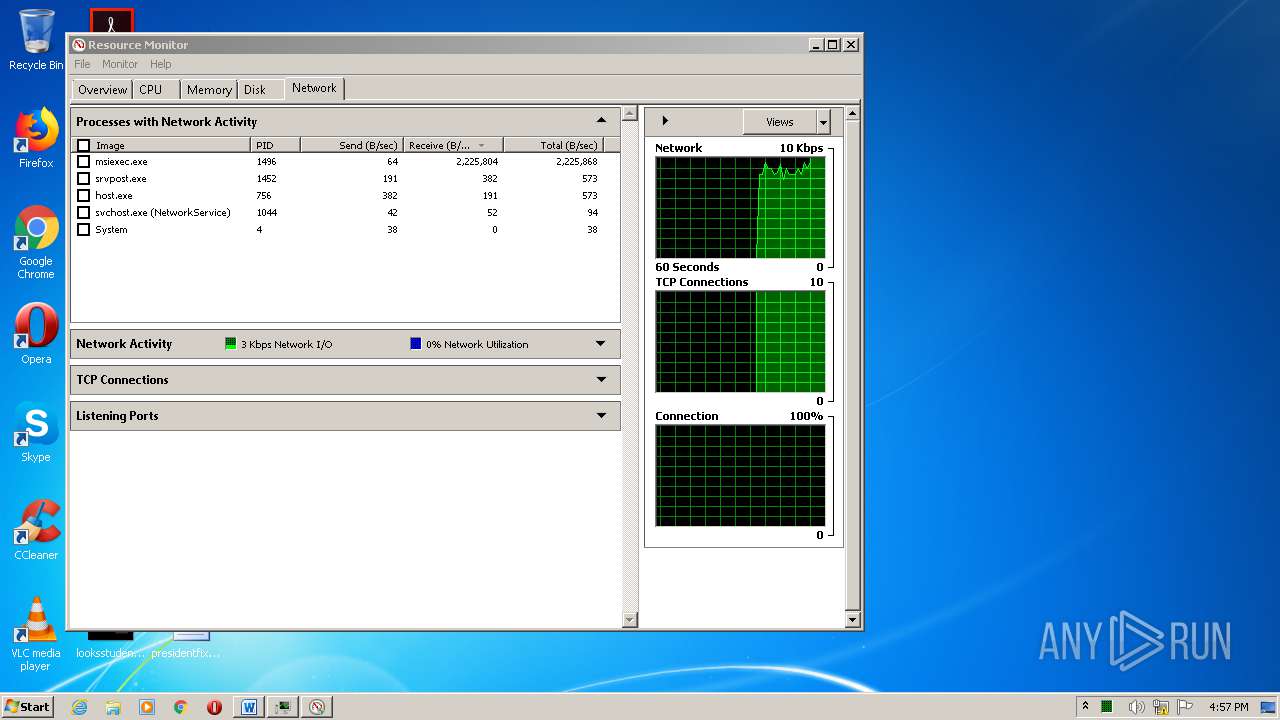
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
7
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
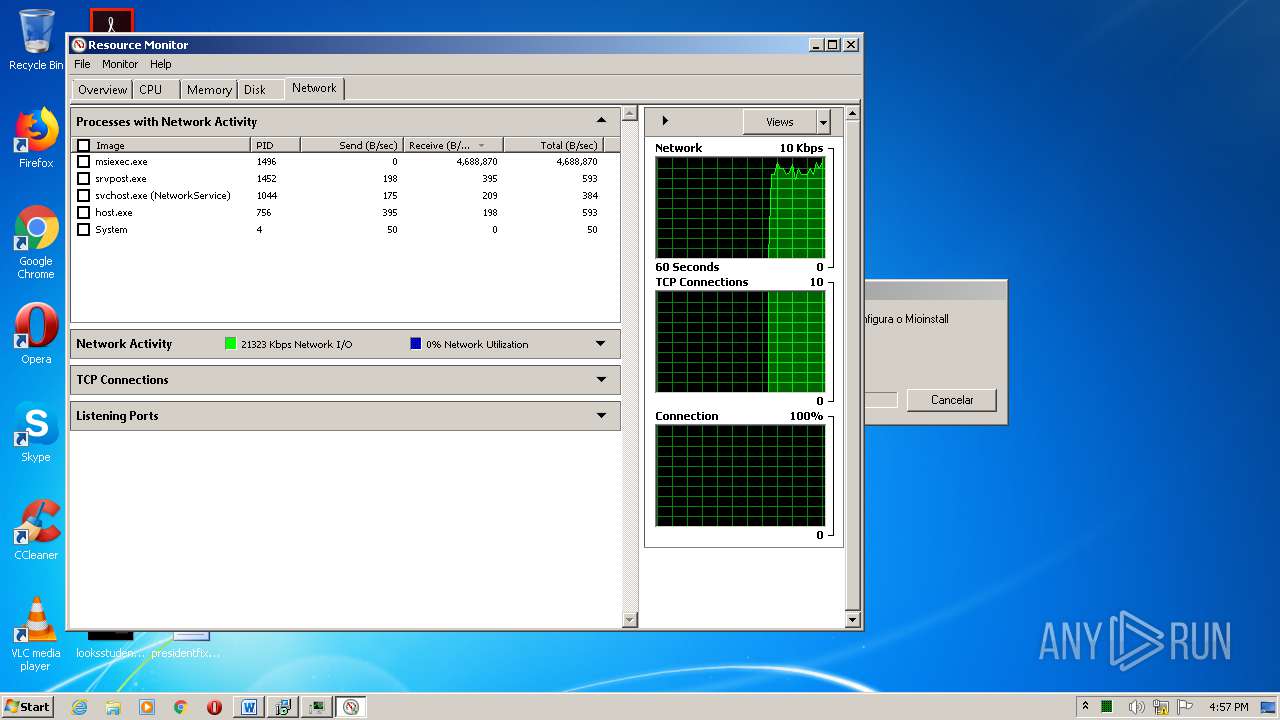
1496 | MsiExec.exe | GET | 200 | 51.81.68.207:80 | http://mymodulop2pcar.servehttp.com/xx.zip | GB | compressed | 29.7 Mb | suspicious |
1496 | MsiExec.exe | GET | 200 | 45.15.24.61:80 | http://java-update.online/Bv3wF1uHKG/counter.php | unknown | text | 26 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
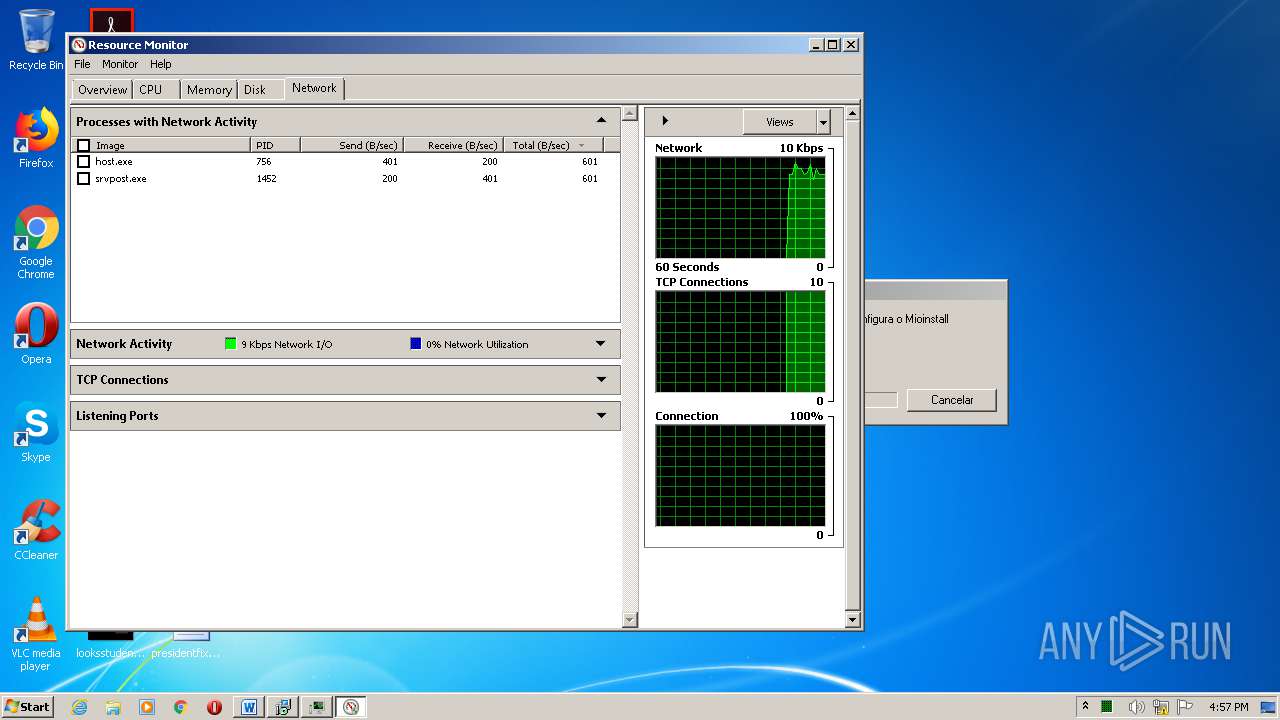
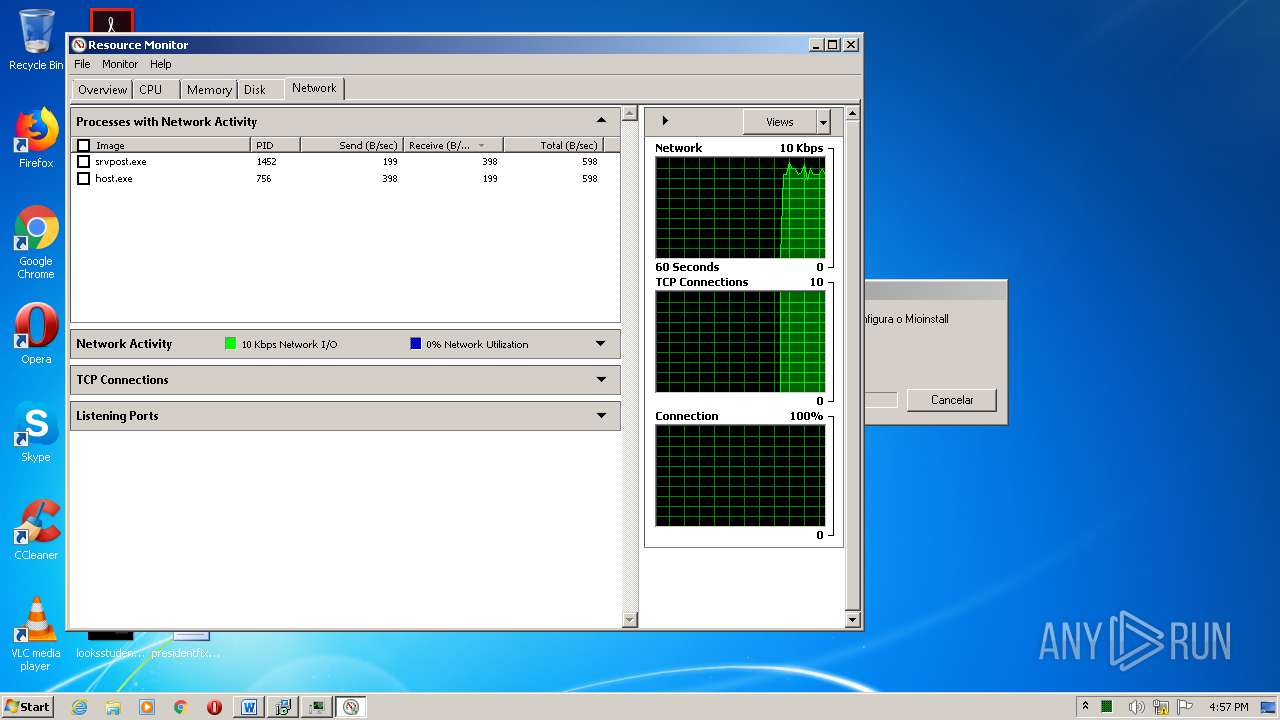
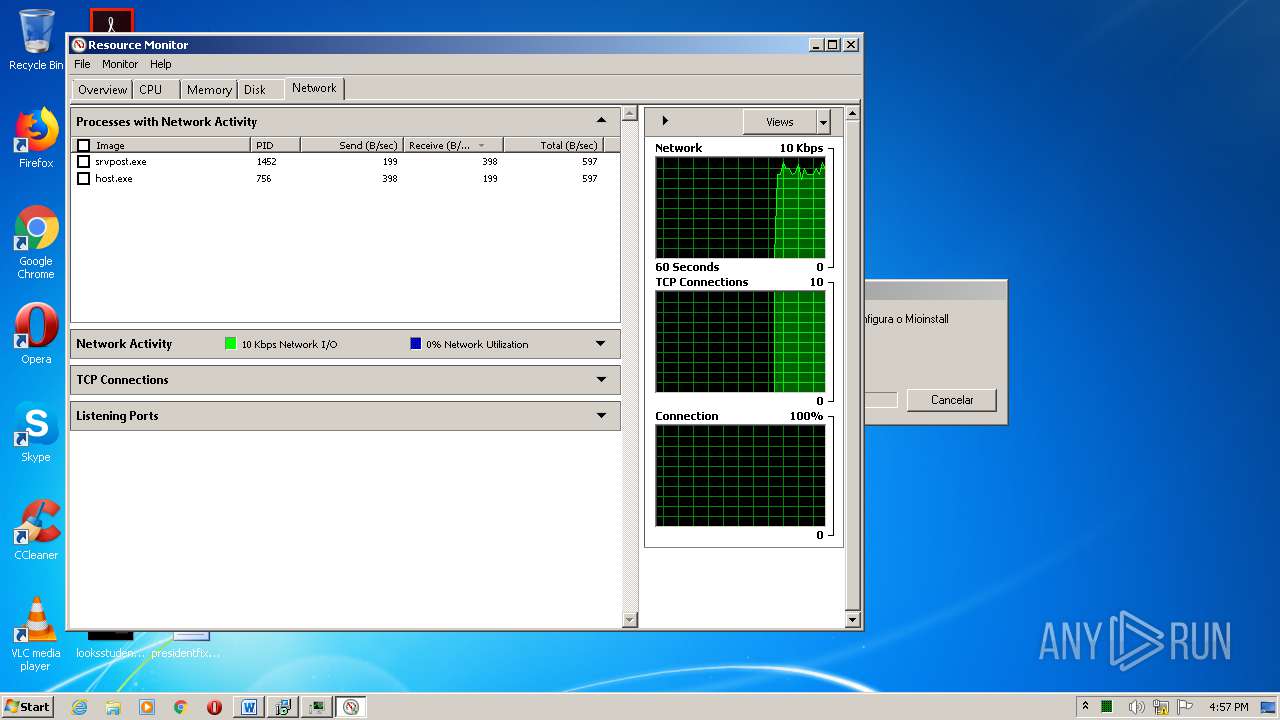
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1496 | MsiExec.exe | 51.81.68.207:80 | mymodulop2pcar.servehttp.com | — | GB | suspicious |
1496 | MsiExec.exe | 45.15.24.61:80 | java-update.online | — | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mymodulop2pcar.servehttp.com |
| suspicious |
207.68.81.51.in-addr.arpa |
| unknown |
2.100.168.192.in-addr.arpa |
| whitelisted |
java-update.online |
| malicious |
61.24.15.45.in-addr.arpa |
| unknown |
252.0.0.224.in-addr.arpa |
| unknown |
3.0.0.0.1.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.2.0.f.f.ip6.arpa |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.servehttp .com |
1496 | MsiExec.exe | Potentially Bad Traffic | ET INFO HTTP Connection To DDNS Domain Servehttp.com |
1496 | MsiExec.exe | A Network Trojan was detected | MALWARE [PTsecurity] VBS.Loader.Gen |