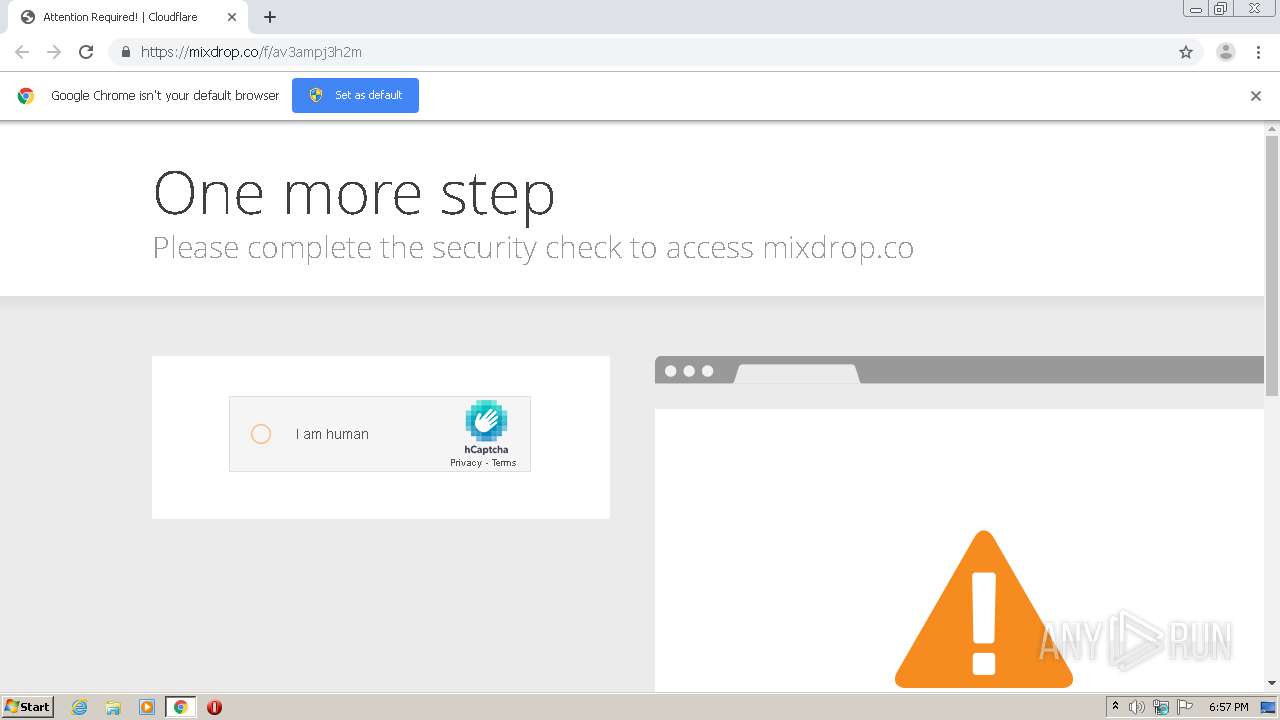
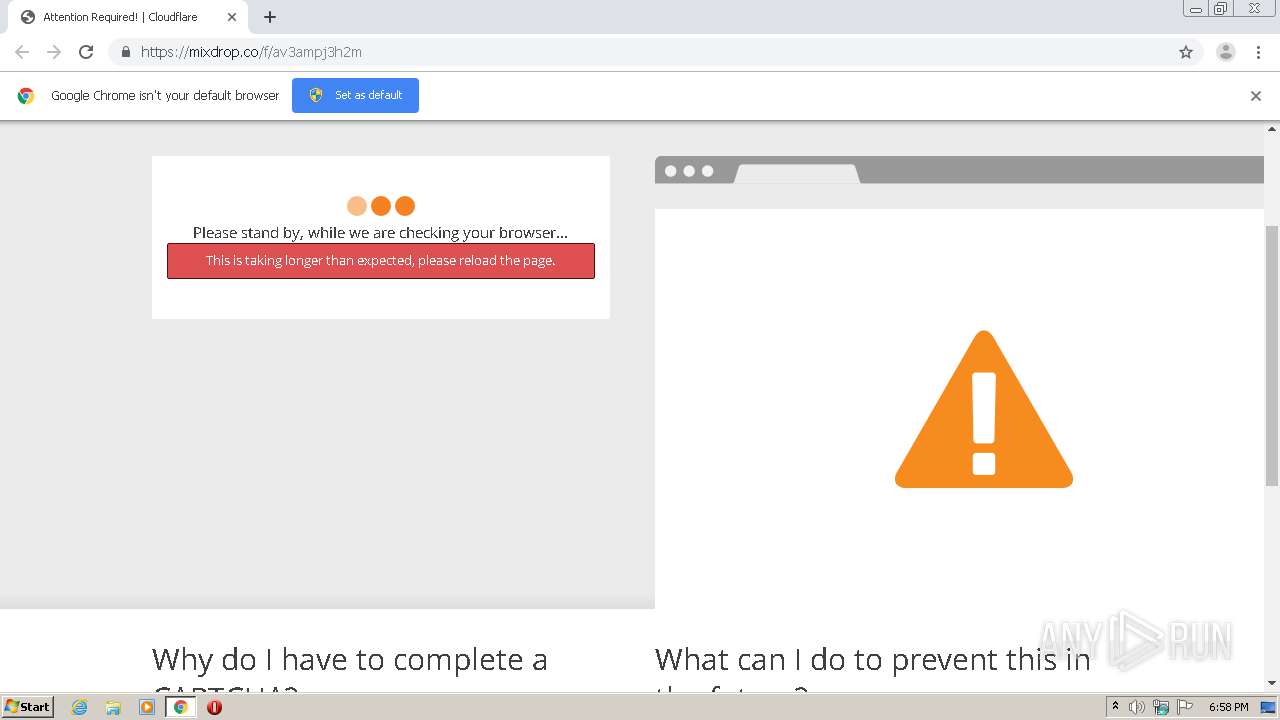
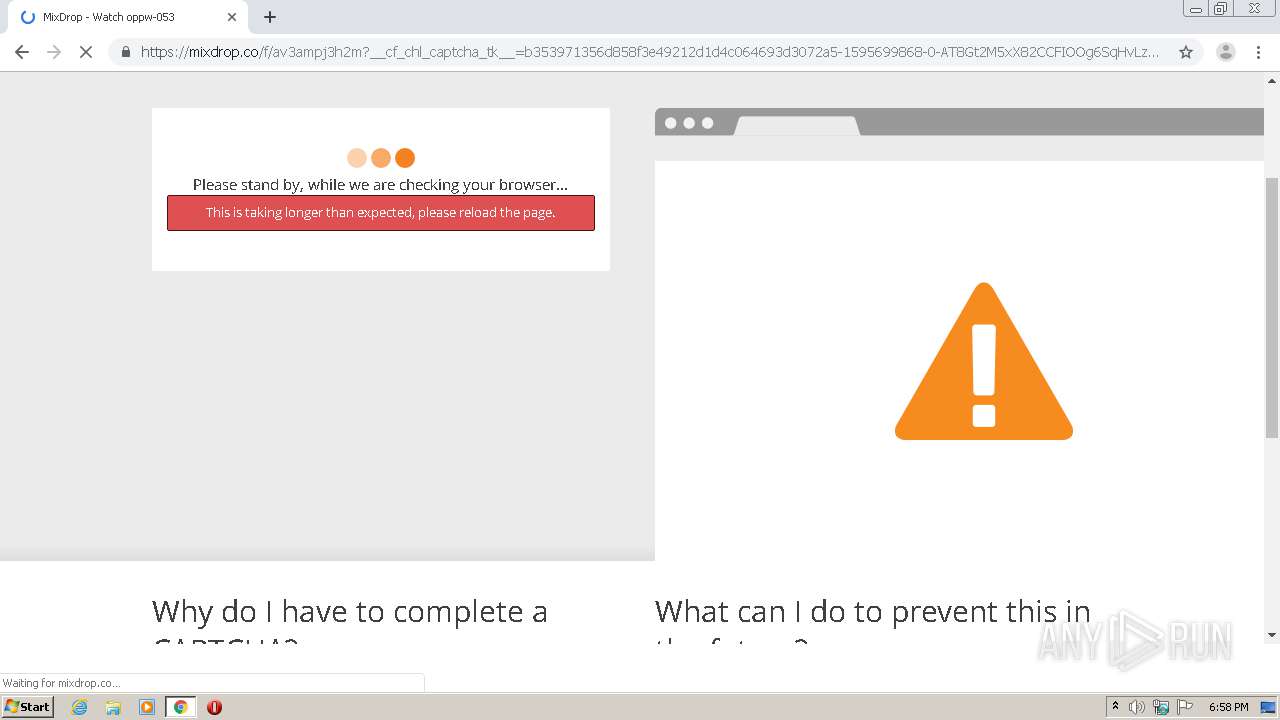
| URL: | http://mixdrop.co/f/av3ampj3h2m |
| Full analysis: | https://app.any.run/tasks/ca61a852-dea8-4805-9c7f-18c888675492 |
| Verdict: | No threats detected |
| Analysis date: | July 25, 2020, 17:57:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 576C4DDC3E94CFA58D923DBBE785835B |
| SHA1: | 96AB5BAA19D65B40ABC39C8705F740E8339EC672 |
| SHA256: | 2488C089CA76D048093EFFAC2C976BFDFBAE5DCCC76D39516383C437A6E94C90 |
| SSDEEP: | 3:N1KTiKhjPWFIn:C/PWFI |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2260)
Reads settings of System Certificates
- chrome.exe (PID: 1140)
Reads the hosts file
- chrome.exe (PID: 2260)
- chrome.exe (PID: 1140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
25
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,18322248527978286511,14183466479826211649,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=11643005525337443015 --mojo-platform-channel-handle=1652 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=ppapi --field-trial-handle=996,18322248527978286511,14183466479826211649,131072 --enable-features=PasswordImport --ppapi-flash-args --lang=en-US --device-scale-factor=1 --ppapi-antialiased-text-enabled=0 --ppapi-subpixel-rendering-setting=0 --service-request-channel-token=1211515127498551023 --mojo-platform-channel-handle=2988 --ignored=" --type=renderer " /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,18322248527978286511,14183466479826211649,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7771786828888306349 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2420 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,18322248527978286511,14183466479826211649,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16341007963860746940 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3040 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,18322248527978286511,14183466479826211649,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18375741161363851430 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3116 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2252 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,18322248527978286511,14183466479826211649,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9786827922249158505 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,18322248527978286511,14183466479826211649,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=13862193504169724229 --mojo-platform-channel-handle=3784 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,18322248527978286511,14183466479826211649,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5047760272079931615 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4320 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,18322248527978286511,14183466479826211649,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1994663734466910287 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3388 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
393
Read events
304
Write events
84
Delete events
5
Modification events
| (PID) Process: | (2260) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2260) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2260) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2260) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2260) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1736) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2260-13240173465803750 |
Value: 259 | |||
| (PID) Process: | (2260) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2260) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2260) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2260) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
54
Text files
93
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\32c10352-d6ca-443d-a7f4-1f87b7c29033.tmp | — | |
MD5:— | SHA256:— | |||
| 2260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFde36b.TMP | text | |
MD5:— | SHA256:— | |||
| 2260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFde38a.TMP | text | |
MD5:— | SHA256:— | |||
| 2260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2260 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
55
DNS requests
37
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1140 | chrome.exe | GET | 301 | 172.64.143.30:80 | http://mixdrop.co/f/av3ampj3h2m | US | — | — | shared |
1140 | chrome.exe | GET | 204 | 35.201.117.228:80 | http://dexchangeinc.com/jump/next.php?stamat=m%7C%2CgYhO6N2arB1dQO0dEdHP3xP.3df%2C2t5FkDDYpjxJXsMWHSh7wAJn9ZfM3gzHzUDUzVBr_s81qwRaP-33NhcG-h9T0kFh5seLN_BelPMQzYCZ6IYfYA%2C%2C&cbrandom=0.14677684317001094&cbtitle=&cbiframe=0&cbWidth=1280&cbHeight=620&cbdescription=&cbkeywords=&cbref= | US | — | — | whitelisted |
1140 | chrome.exe | GET | 303 | 107.23.28.17:80 | http://ps.popcash.net/ad/ad?p=262415&w=543028&t=6c29e1920322a899&r=&s=1280,720,1.23,1574.4,885.6,1&v=&m=&vw=1272&vh=636 | US | html | 69 b | shared |
1140 | chrome.exe | GET | 200 | 139.45.195.81:80 | http://graizoah.com/afu.php?zoneid=3412407 | US | html | 9.00 Kb | suspicious |
1140 | chrome.exe | POST | 204 | 139.45.195.81:80 | http://graizoah.com/?z=3412407 | US | compressed | 9.00 Kb | suspicious |
1140 | chrome.exe | GET | 200 | 35.201.90.210:80 | http://www.dexpredict.com/jump/next.php?r=2740971 | US | html | 2.57 Kb | malicious |
1140 | chrome.exe | GET | 200 | 107.23.28.17:80 | http://ps.popcash.net/go/262415/543028/&s=1280,720,1.23,1574.4,885.6,1&v=&m= | US | html | 300 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1140 | chrome.exe | 172.217.17.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1140 | chrome.exe | 216.58.214.13:443 | accounts.google.com | Google Inc. | US | suspicious |
1140 | chrome.exe | 104.18.26.20:443 | assets.hcaptcha.com | Cloudflare Inc | US | malicious |
1140 | chrome.exe | 172.217.168.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1140 | chrome.exe | 104.18.27.20:443 | hcaptcha.com | Cloudflare Inc | US | malicious |
1140 | chrome.exe | 172.217.17.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
1140 | chrome.exe | 172.217.168.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1140 | chrome.exe | 172.217.0.72:443 | www.googletagmanager.com | Google Inc. | US | unknown |
1140 | chrome.exe | 209.197.3.24:443 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
1140 | chrome.exe | 8.247.210.249:443 | cdn.runative-syndicate.com | Level 3 Communications, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mixdrop.co |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
hcaptcha.com |
| whitelisted |
assets.hcaptcha.com |
| whitelisted |
clients1.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
imgs.hcaptcha.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
code.jquery.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1140 | chrome.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 15 |
1140 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |