| download: | InPixio_PhotoClip_DE_FT.exe |
| Full analysis: | https://app.any.run/tasks/df91e1bb-e1ae-4093-b03d-ae45a0a2b81b |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 12:26:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 42D80ECE5BC0784439E72CC667602982 |
| SHA1: | DAE8F0B27DB4C1D0935B6B2DF4B42E50C1623F77 |
| SHA256: | 24882ECD190A7AD5CDED69D0E9A5BDED31D234F728A6A15273F5A895B66D00EF |
| SSDEEP: | 49152:q4BHIXzo5m4c8YN3Uhg9RBNTe1/QZ8AqCqkwMTqe138aTnVzIic5sRTRtX/asd2v:bJIb4fYRdhde1/4ute138ap016NRNrMv |
MALICIOUS
Loads dropped or rewritten executable
- InPixio_PhotoClip_DE_FT.exe (PID: 928)
- inPixioPhotoClip9.exe (PID: 3952)
Application was dropped or rewritten from another process
- inPixioPhotoClip9.exe (PID: 3952)
- Setup.exe (PID: 3788)
Changes settings of System certificates
- inPixioPhotoClip9.exe (PID: 3952)
SUSPICIOUS
Creates files in the user directory
- Setup.exe (PID: 3788)
- inPixioPhotoClip9.exe (PID: 3952)
Creates a software uninstall entry
- Setup.exe (PID: 3788)
Creates files in the program directory
- Setup.exe (PID: 3788)
Reads the Windows organization settings
- Setup.exe (PID: 3788)
Adds / modifies Windows certificates
- inPixioPhotoClip9.exe (PID: 3952)
Reads Windows owner or organization settings
- Setup.exe (PID: 3788)
Executable content was dropped or overwritten
- InPixio_PhotoClip_DE_FT.exe (PID: 928)
- Setup.exe (PID: 3788)
Changes IE settings (feature browser emulation)
- Setup.exe (PID: 3788)
INFO
Reads settings of System Certificates
- inPixioPhotoClip9.exe (PID: 3952)
Dropped object may contain Bitcoin addresses
- Setup.exe (PID: 3788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:14 10:09:36+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 568832 |
| InitializedDataSize: | 1307136 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x75126 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.0.0.0 |
| ProductVersionNumber: | 9.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build, Special build |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductName: | inPixio Photo Clip |
| ProductVersion: | 9.0.0 |
| Comments: | inPixio Photo Clip |
| FileDescription: | inPixio Photo Clip |
| InternalName: | Setup.exe |
| OriginalFileName: | Setup.exe |
| FileVersion: | 9.0.0.0 |
| CompanyName: | inPixio |
| LegalCopyright: | Copyright © inPixio 2019 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Feb-2019 09:09:36 |
| Detected languages: |
|
| Debug artifacts: |
|
| ProductName: | inPixio Photo Clip |
| ProductVersion: | 9.0.0 |
| Comments: | inPixio Photo Clip |
| FileDescription: | inPixio Photo Clip |
| InternalName: | Setup.exe |
| OriginalFilename: | Setup.exe |
| FileVersion: | 9.0.0.0 |
| CompanyName: | inPixio |
| LegalCopyright: | Copyright © inPixio 2019 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 14-Feb-2019 09:09:36 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008AC32 | 0x0008AE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59781 |
.rdata | 0x0008C000 | 0x000220FA | 0x00022200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.58331 |
.data | 0x000AF000 | 0x000299E8 | 0x00002E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.77531 |
.rsrc | 0x000D9000 | 0x00112FF8 | 0x00113000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.77455 |
.reloc | 0x001EC000 | 0x000070F4 | 0x00007200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.76524 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.41067 | 1334 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 3.37186 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.04226 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 4.88238 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.49498 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 3.50283 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 4.82636 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 5.07024 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 3.16151 | 554 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.14743 | 552 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
DIRPACN.dll (delay-loaded) |
GDI32.dll |
KERNEL32.dll |
MSIMG32.dll |
SETUPAPI.dll |
SHELL32.dll |
SHLWAPI.dll |
Total processes
39
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 928 | "C:\Users\admin\AppData\Local\Temp\InPixio_PhotoClip_DE_FT.exe" | C:\Users\admin\AppData\Local\Temp\InPixio_PhotoClip_DE_FT.exe | explorer.exe | ||||||||||||
User: admin Company: inPixio Integrity Level: HIGH Description: inPixio Photo Clip Exit code: 0 Version: 9.0.0.0 Modules
| |||||||||||||||
| 1136 | "C:\Users\admin\AppData\Local\Temp\InPixio_PhotoClip_DE_FT.exe" | C:\Users\admin\AppData\Local\Temp\InPixio_PhotoClip_DE_FT.exe | — | explorer.exe | |||||||||||
User: admin Company: inPixio Integrity Level: MEDIUM Description: inPixio Photo Clip Exit code: 3221226540 Version: 9.0.0.0 Modules
| |||||||||||||||
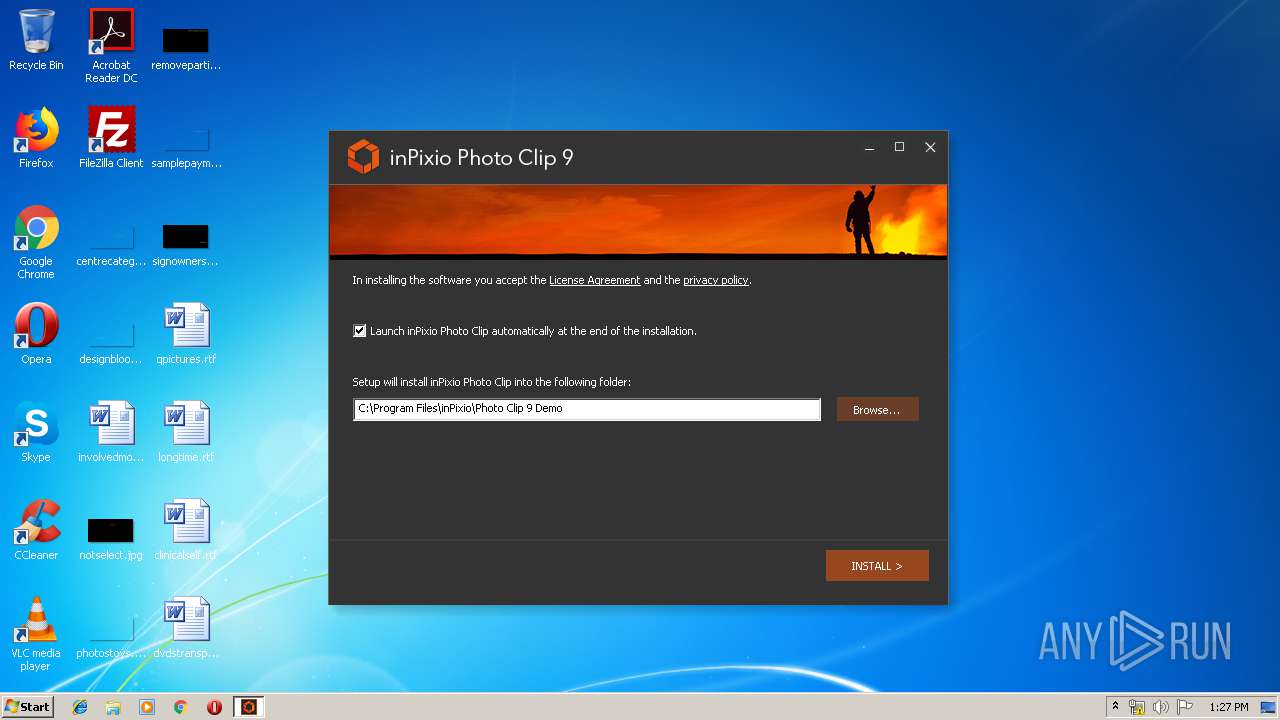
| 3788 | "C:\Users\admin\AppData\Local\Temp\{38bda697-0675-403f-9798-C8257F870CB5}\{7B28E39C-883C-4f49-ABFB-5D16796F2DD9}\Setup.exe" /DIR:"C:\Program Files\inPixio\Photo Clip 9 Demo" /L:2057 | C:\Users\admin\AppData\Local\Temp\{38bda697-0675-403f-9798-C8257F870CB5}\{7B28E39C-883C-4f49-ABFB-5D16796F2DD9}\Setup.exe | InPixio_PhotoClip_DE_FT.exe | ||||||||||||
User: admin Company: Avanquest Software Integrity Level: HIGH Description: inPixio Photo Clip Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3952 | "C:\Program Files\inPixio\Photo Clip 9 Demo\inPixioPhotoClip9.exe" | C:\Program Files\inPixio\Photo Clip 9 Demo\inPixioPhotoClip9.exe | InPixio_PhotoClip_DE_FT.exe | ||||||||||||
User: admin Company: Avanquest Software Integrity Level: HIGH Description: inPixio Photo Clip Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
805
Read events
703
Write events
102
Delete events
0
Modification events
| (PID) Process: | (928) InPixio_PhotoClip_DE_FT.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\InPixio_PhotoClip_DE_FT_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (928) InPixio_PhotoClip_DE_FT.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\InPixio_PhotoClip_DE_FT_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (928) InPixio_PhotoClip_DE_FT.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\InPixio_PhotoClip_DE_FT_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (928) InPixio_PhotoClip_DE_FT.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\InPixio_PhotoClip_DE_FT_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (928) InPixio_PhotoClip_DE_FT.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\InPixio_PhotoClip_DE_FT_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (928) InPixio_PhotoClip_DE_FT.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\InPixio_PhotoClip_DE_FT_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (928) InPixio_PhotoClip_DE_FT.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\InPixio_PhotoClip_DE_FT_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (928) InPixio_PhotoClip_DE_FT.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\InPixio_PhotoClip_DE_FT_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (928) InPixio_PhotoClip_DE_FT.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\InPixio_PhotoClip_DE_FT_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (928) InPixio_PhotoClip_DE_FT.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\InPixio_PhotoClip_DE_FT_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
7
Suspicious files
16
Text files
35
Unknown types
39
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 928 | InPixio_PhotoClip_DE_FT.exe | C:\Users\admin\AppData\Local\Temp\{38bda697-0675-403f-9798-C8257F870CB5}\Neutral.001 | — | |
MD5:— | SHA256:— | |||
| 928 | InPixio_PhotoClip_DE_FT.exe | C:\Users\admin\AppData\Local\Temp\{38bda697-0675-403f-9798-C8257F870CB5}\English.001 | — | |
MD5:— | SHA256:— | |||
| 928 | InPixio_PhotoClip_DE_FT.exe | C:\Users\admin\AppData\Local\Temp\{38bda697-0675-403f-9798-C8257F870CB5}\NewUI.tmp | — | |
MD5:— | SHA256:— | |||
| 928 | InPixio_PhotoClip_DE_FT.exe | C:\Users\admin\AppData\Local\Temp\{38bda697-0675-403f-9798-C8257F870CB5}\English.lng | executable | |
MD5:— | SHA256:— | |||
| 928 | InPixio_PhotoClip_DE_FT.exe | C:\Users\admin\AppData\Local\Temp\{38bda697-0675-403f-9798-C8257F870CB5}\setup.cfg | text | |
MD5:— | SHA256:— | |||
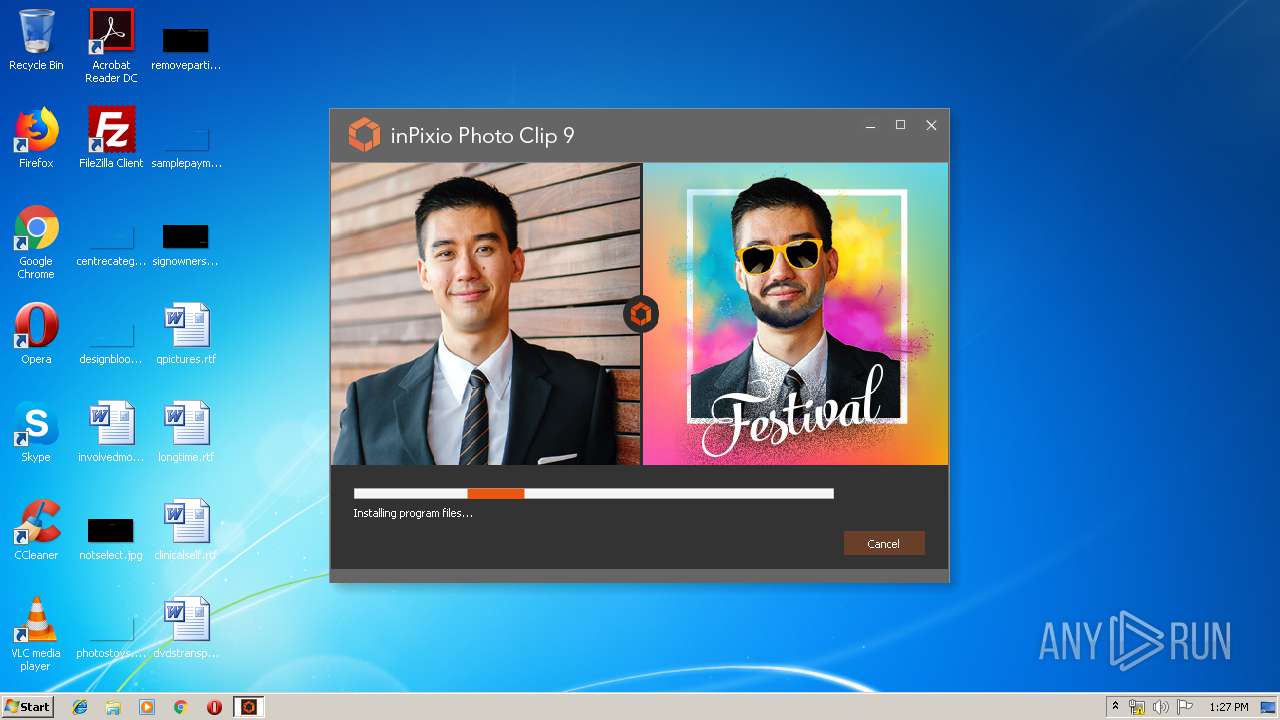
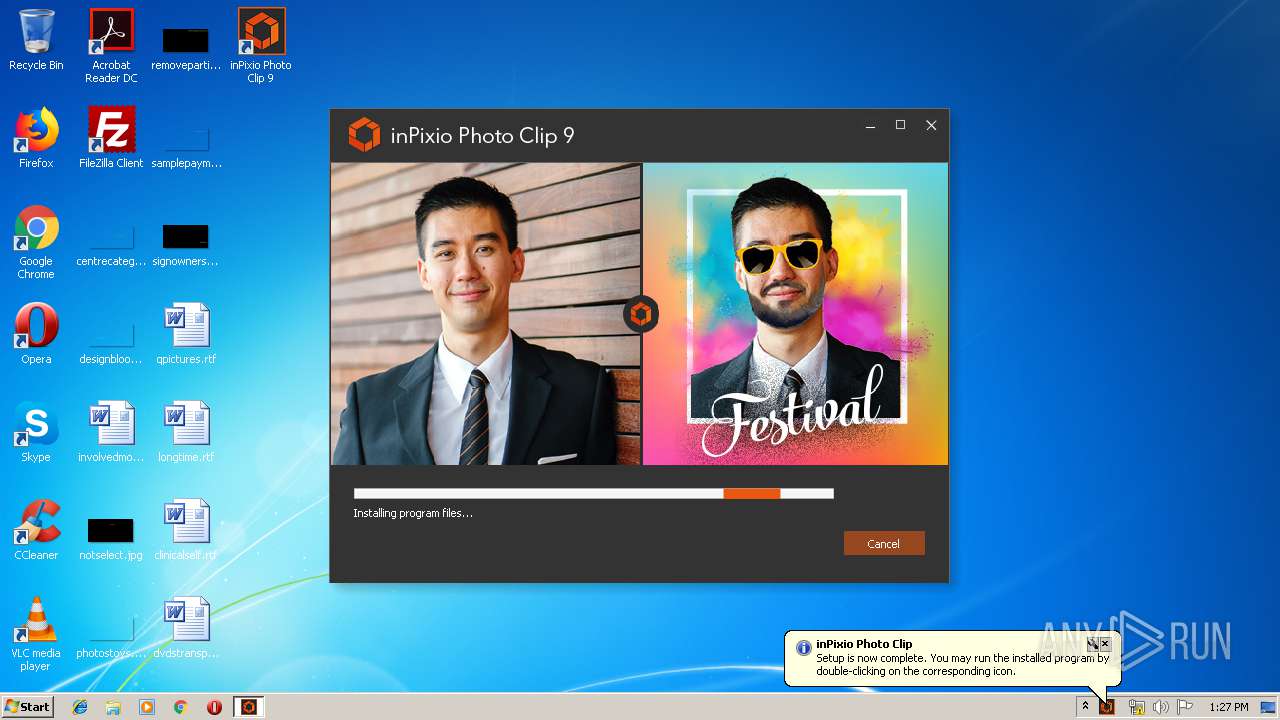
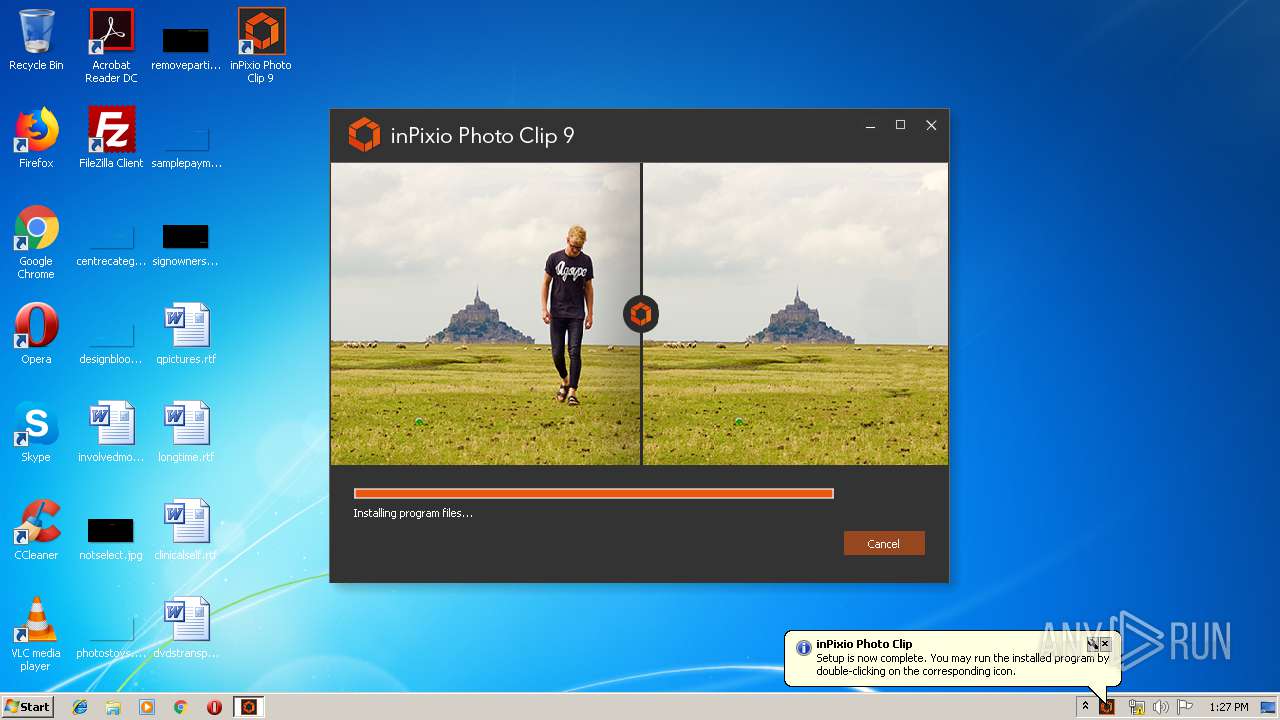
| 928 | InPixio_PhotoClip_DE_FT.exe | C:\Users\admin\AppData\Local\Temp\{38bda697-0675-403f-9798-C8257F870CB5}\Trial_BackgroundProgressBar Photo Clip 9.png | image | |
MD5:— | SHA256:— | |||
| 928 | InPixio_PhotoClip_DE_FT.exe | C:\Users\admin\AppData\Local\Temp\{38bda697-0675-403f-9798-C8257F870CB5}\PackImages\ProgressBar1.jpg | image | |
MD5:— | SHA256:— | |||
| 928 | InPixio_PhotoClip_DE_FT.exe | C:\Users\admin\AppData\Local\Temp\{38bda697-0675-403f-9798-C8257F870CB5}\PackImages\ProgressBar3.jpg | image | |
MD5:— | SHA256:— | |||
| 928 | InPixio_PhotoClip_DE_FT.exe | C:\Users\admin\AppData\Local\Temp\{38bda697-0675-403f-9798-C8257F870CB5}\PackImages\ProgressBar2.jpg | image | |
MD5:— | SHA256:— | |||
| 928 | InPixio_PhotoClip_DE_FT.exe | C:\Users\admin\AppData\Local\Temp\{38bda697-0675-403f-9798-C8257F870CB5}\PackImages\ProgressBar4.jpg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
13
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3788 | Setup.exe | POST | 302 | 217.195.25.241:80 | http://webtools.avanquest.com/redirect.cfm?redirectId=inpixio/IPC_INPIXIO_EN_FT_POST_INSTALL.htm | FR | text | 96 b | malicious |
3952 | inPixioPhotoClip9.exe | GET | 200 | 217.195.25.238:80 | http://web.avanquest.com/iframe/Inpixio/EN/images/Header_Image_Photo_Clip_7.png | FR | image | 4.89 Kb | malicious |
3952 | inPixioPhotoClip9.exe | GET | 302 | 217.195.25.241:80 | http://webtools.avanquest.com/redirect.cfm?redirectId=inpixio/IPC_INPIXIO_EN_IF_FT.htm | FR | text | 96 b | malicious |
3952 | inPixioPhotoClip9.exe | GET | 200 | 217.195.25.238:80 | http://web.avanquest.com/iframe/Inpixio/EN/IPC_INPIXIO_EN_VTUTO.cfm | FR | html | 5.89 Kb | malicious |
3952 | inPixioPhotoClip9.exe | GET | 200 | 2.16.186.26:80 | http://embed.wistia.com/deliveries/c3943df6b34ad174f3c0c7b5522be48618ad176f/file.mp4 | unknown | m4v | 4.45 Mb | whitelisted |
3952 | inPixioPhotoClip9.exe | GET | 304 | 217.195.25.238:80 | http://web.avanquest.com/iframe/Inpixio/EN/images/logo_INP.png | FR | image | 967 b | malicious |
3952 | inPixioPhotoClip9.exe | GET | 304 | 217.195.25.238:80 | http://web.avanquest.com/iframe/Inpixio/EN/images/Header_Image_Photo_Clip_7.png | FR | html | 5.89 Kb | malicious |
3952 | inPixioPhotoClip9.exe | GET | 304 | 2.16.186.26:80 | http://embed.wistia.com/deliveries/c3943df6b34ad174f3c0c7b5522be48618ad176f/file.mp4 | unknown | m4v | 4.45 Mb | whitelisted |
3952 | inPixioPhotoClip9.exe | GET | 304 | 217.195.25.238:80 | http://web.avanquest.com/iframe/Inpixio/EN/images/hp.jpg | FR | image | 967 b | malicious |
3952 | inPixioPhotoClip9.exe | GET | 304 | 217.195.25.238:80 | http://web.avanquest.com/iframe/Inpixio/EN/images/next-btn.png | FR | html | 5.89 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3788 | Setup.exe | 217.195.25.241:80 | webtools.avanquest.com | SPIE Cloud Services SAS | FR | malicious |
3952 | inPixioPhotoClip9.exe | 217.195.25.241:80 | webtools.avanquest.com | SPIE Cloud Services SAS | FR | malicious |
3952 | inPixioPhotoClip9.exe | 217.195.25.238:80 | web.avanquest.com | SPIE Cloud Services SAS | FR | unknown |
3952 | inPixioPhotoClip9.exe | 216.58.205.234:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3952 | inPixioPhotoClip9.exe | 172.217.18.3:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3952 | inPixioPhotoClip9.exe | 2.16.186.26:80 | embed.wistia.com | Akamai International B.V. | — | whitelisted |
3952 | inPixioPhotoClip9.exe | 216.58.205.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3952 | inPixioPhotoClip9.exe | 66.102.1.157:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
3952 | inPixioPhotoClip9.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
928 | InPixio_PhotoClip_DE_FT.exe | 23.212.224.236:80 | www.microsoft.com | Akamai Technologies, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
webtools.avanquest.com |
| unknown |
web.avanquest.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
embed.wistia.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
www.google.com |
| malicious |
www.google.pl |
| whitelisted |