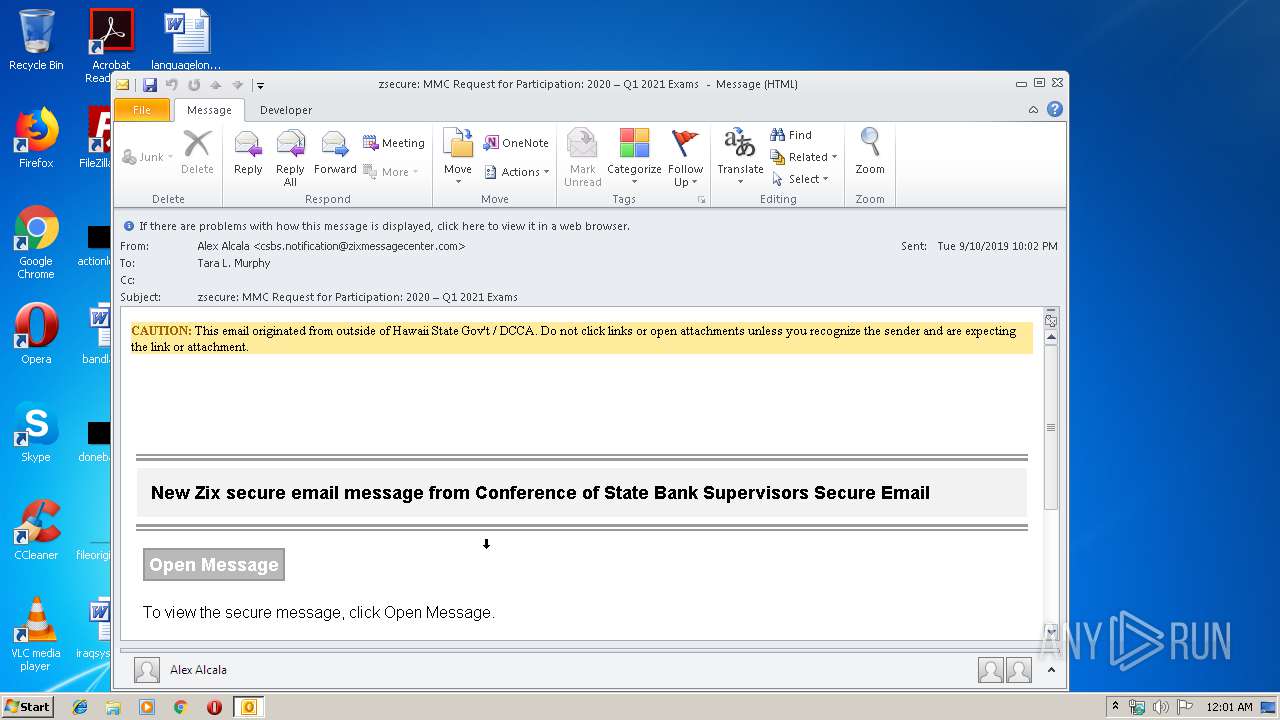
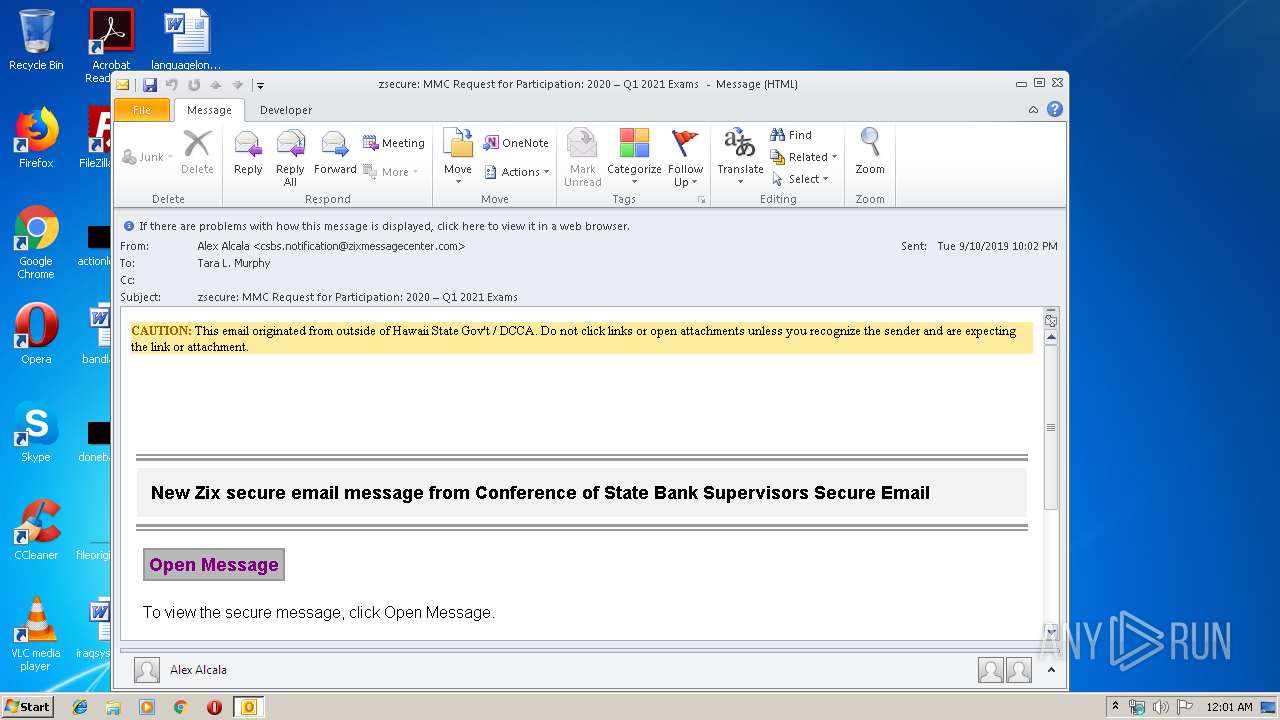
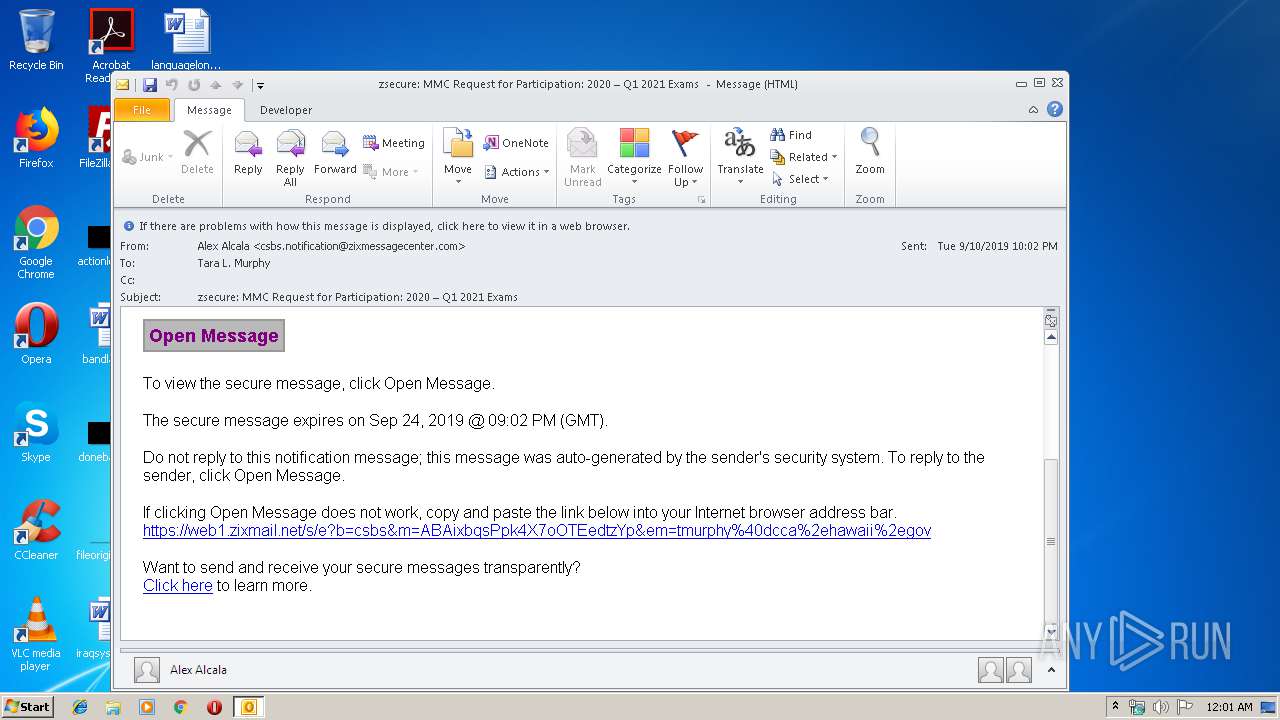
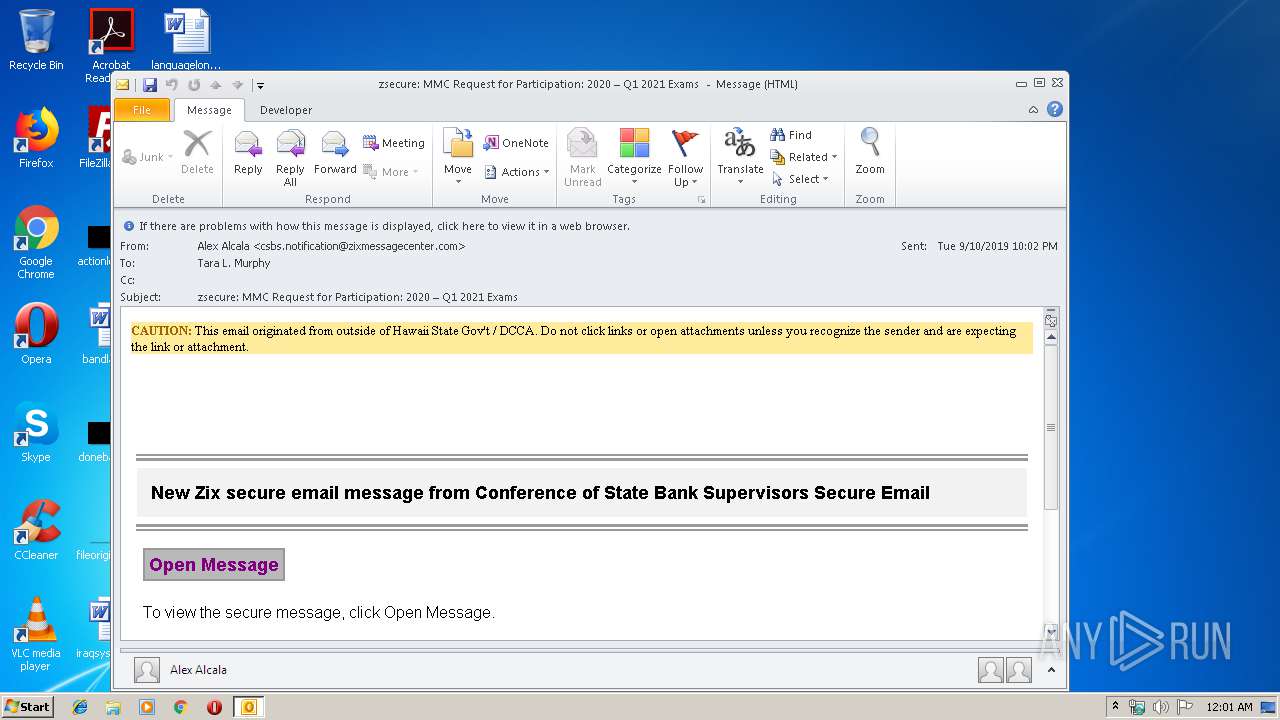
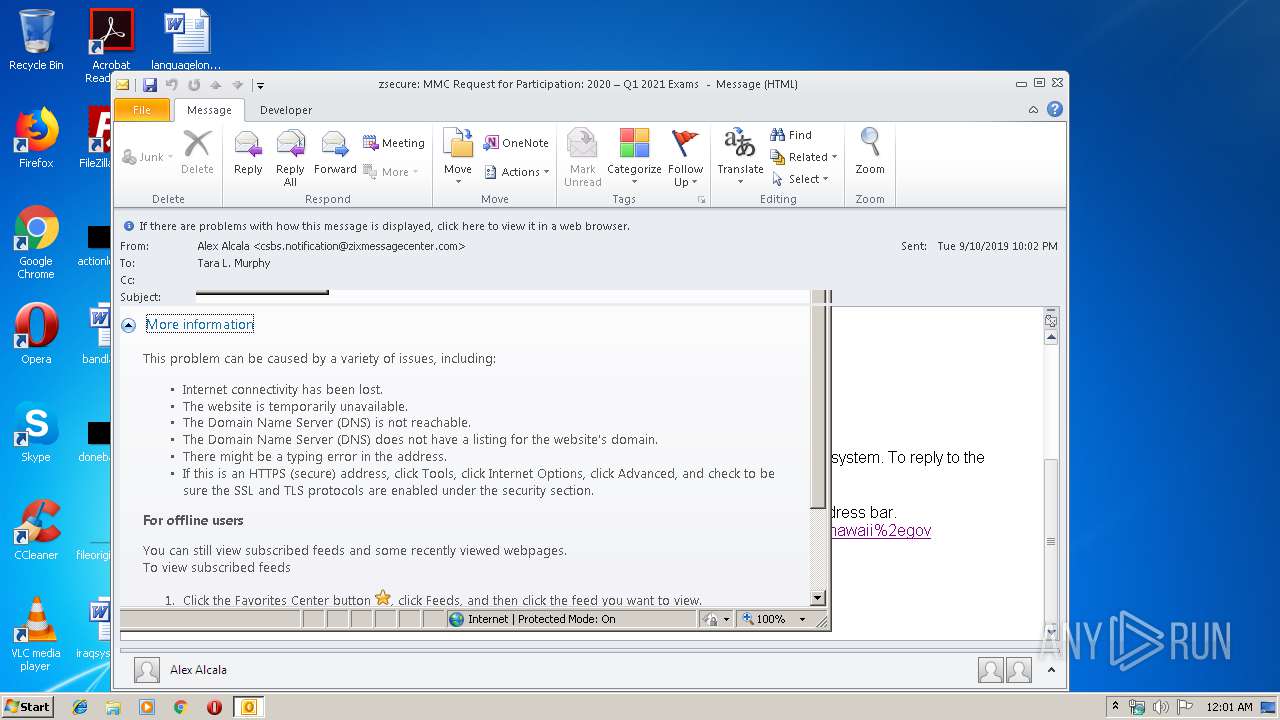
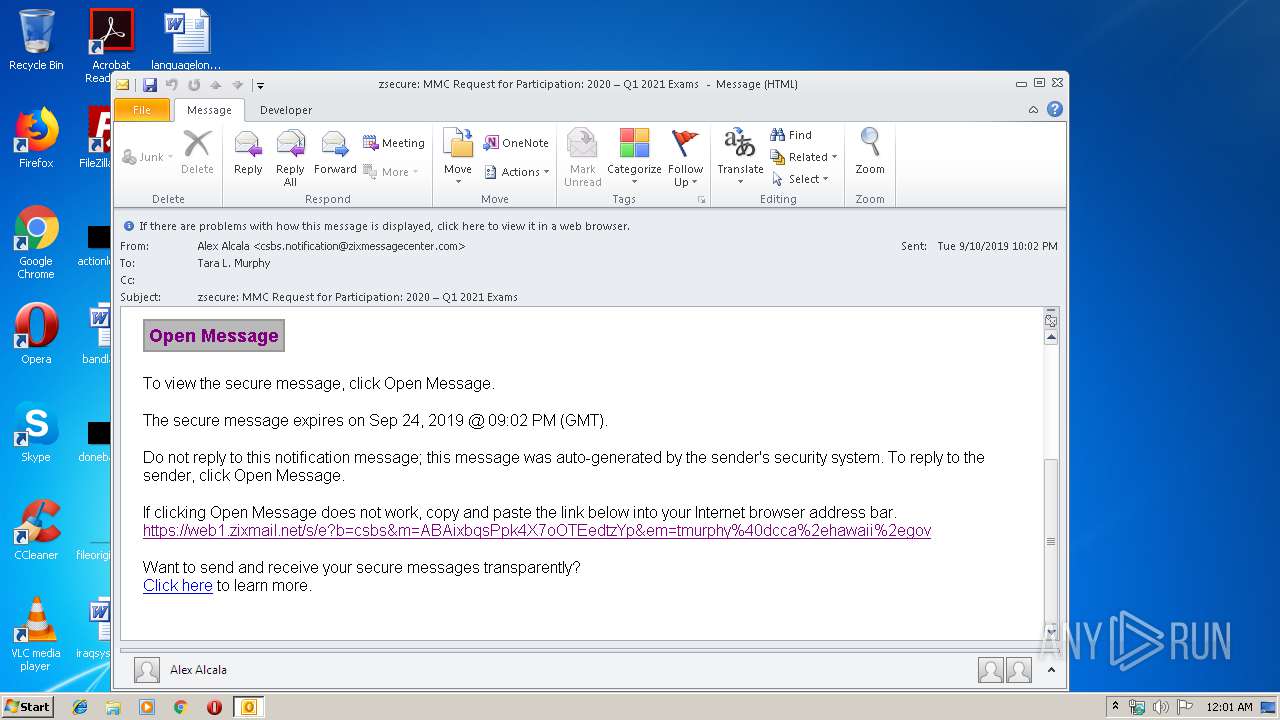
| File name: | zsecure MMC Request for Participation 2020 Q1 2021 Exams .msg |
| Full analysis: | https://app.any.run/tasks/06b7315b-af65-4a53-adda-59a2e460ace8 |
| Verdict: | Malicious activity |
| Analysis date: | September 10, 2019, 23:00:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 4D3B8D03556CDFE79C477202D58C6ED7 |
| SHA1: | 135FD0BE65F1765848B5B7461E47174B96282845 |
| SHA256: | 246B6B00402C5ACCFB56C1495E247A11809F29D6562B12BE2F8BA498317AFDE4 |
| SSDEEP: | 1536:YuWxWJrCx0c8hBgqo1UNunW7WJQkveGKf/GKVSIov6:Y4rCx0c8hBfYrQkvJKfuKVS1 |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2756)
SUSPICIOUS
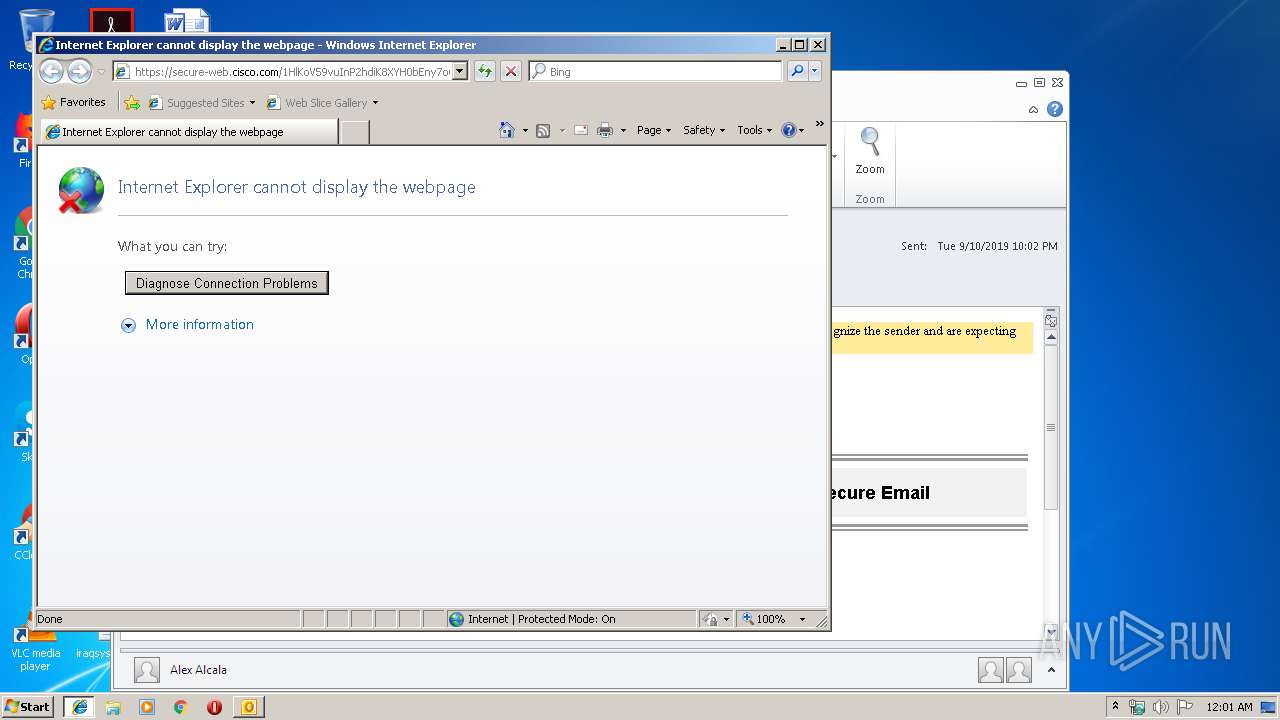
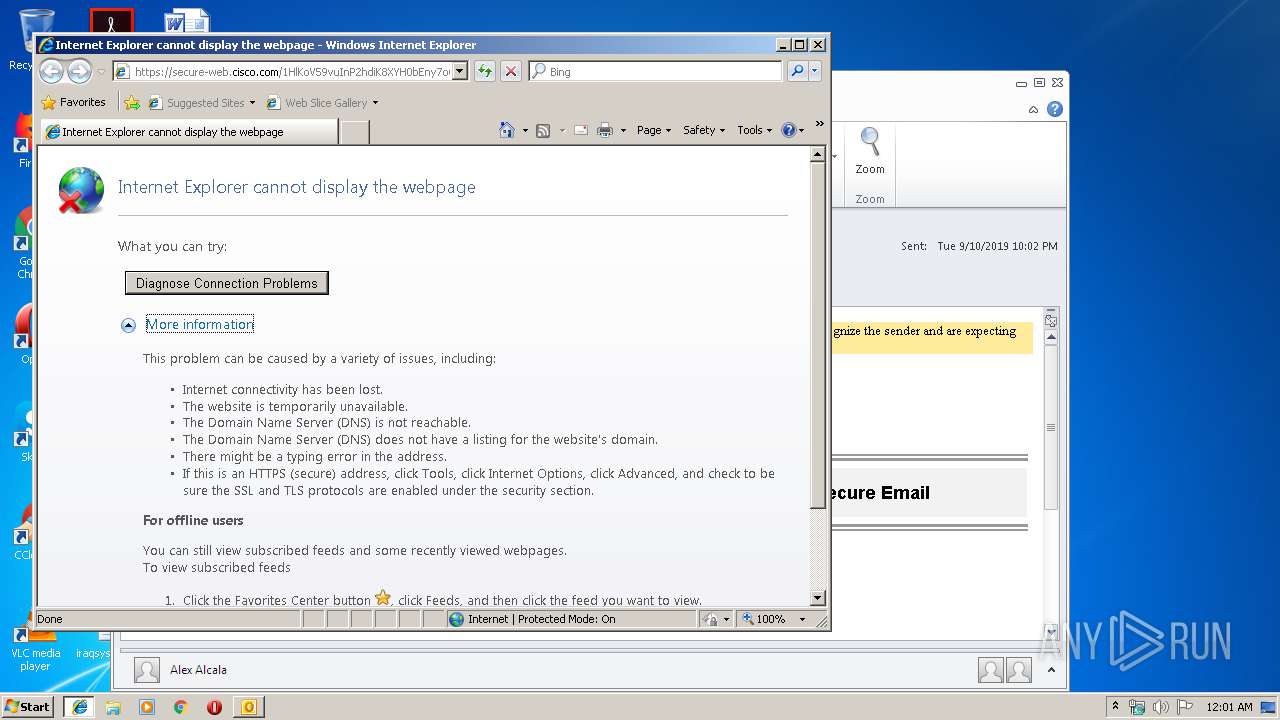
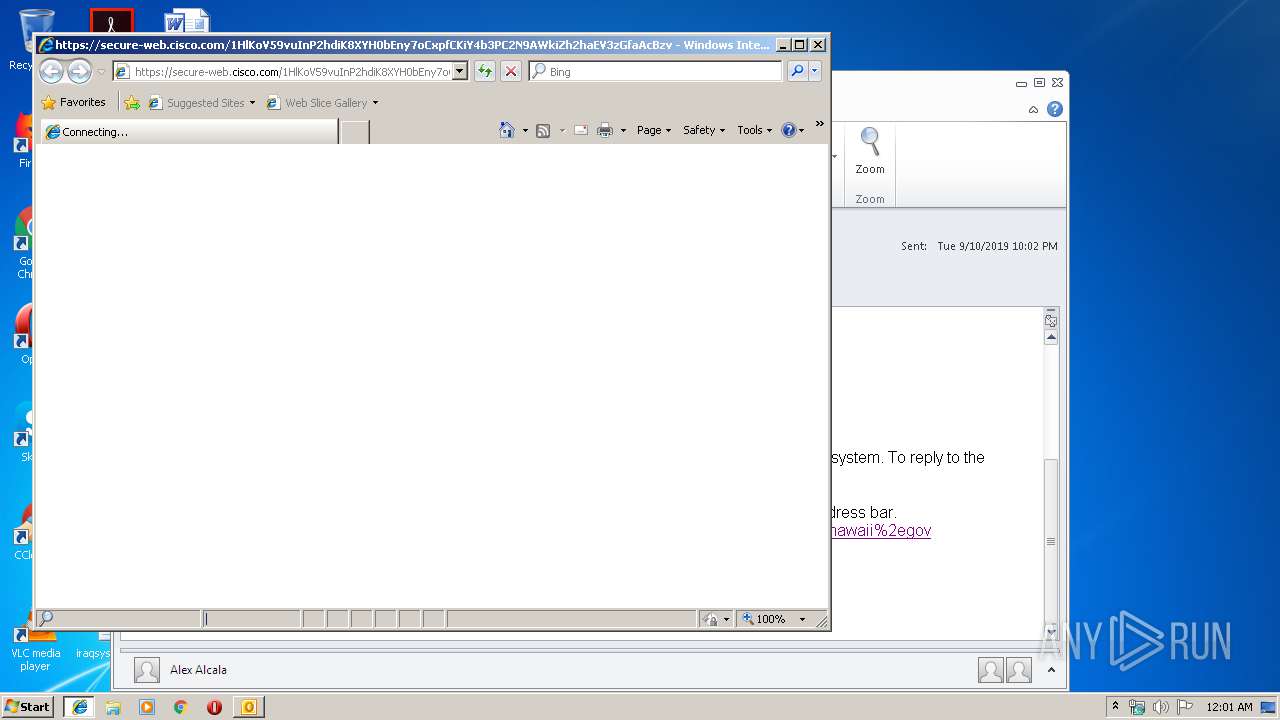
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2756)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2756)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2756)
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3824)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2756)
Application launched itself
- iexplore.exe (PID: 704)
- iexplore.exe (PID: 2860)
- iexplore.exe (PID: 3548)
Changes internet zones settings
- iexplore.exe (PID: 704)
- iexplore.exe (PID: 3548)
- iexplore.exe (PID: 2860)
Reads Internet Cache Settings
- iexplore.exe (PID: 504)
- iexplore.exe (PID: 3532)
- iexplore.exe (PID: 2308)
- iexplore.exe (PID: 3548)
Reads internet explorer settings
- iexplore.exe (PID: 3532)
- iexplore.exe (PID: 504)
- iexplore.exe (PID: 2308)
Creates files in the user directory
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3824)
- iexplore.exe (PID: 2308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
41
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 504 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:704 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
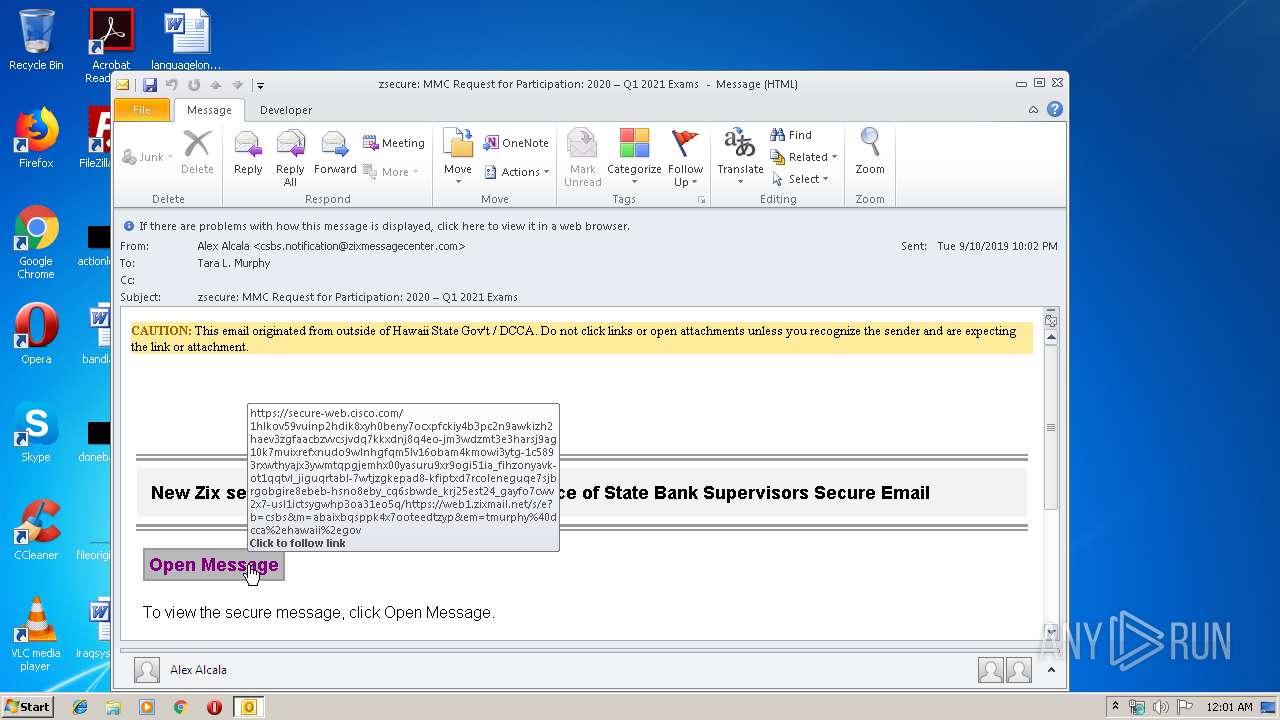
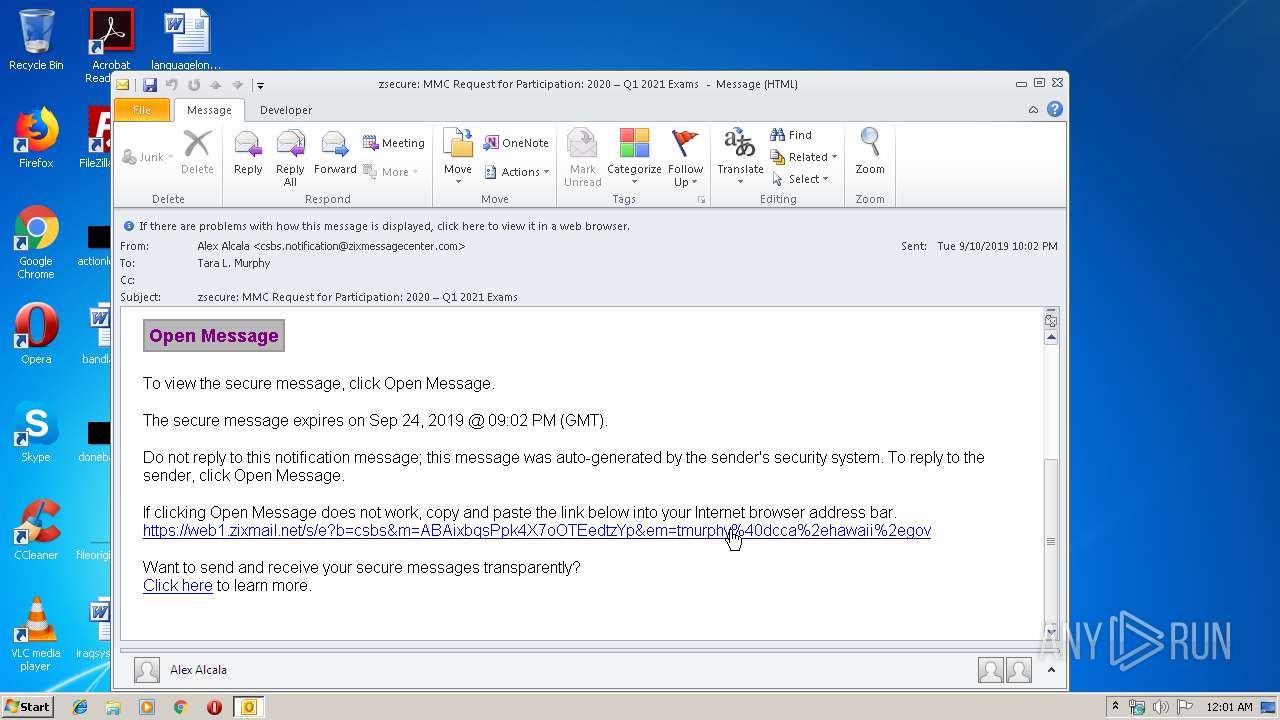
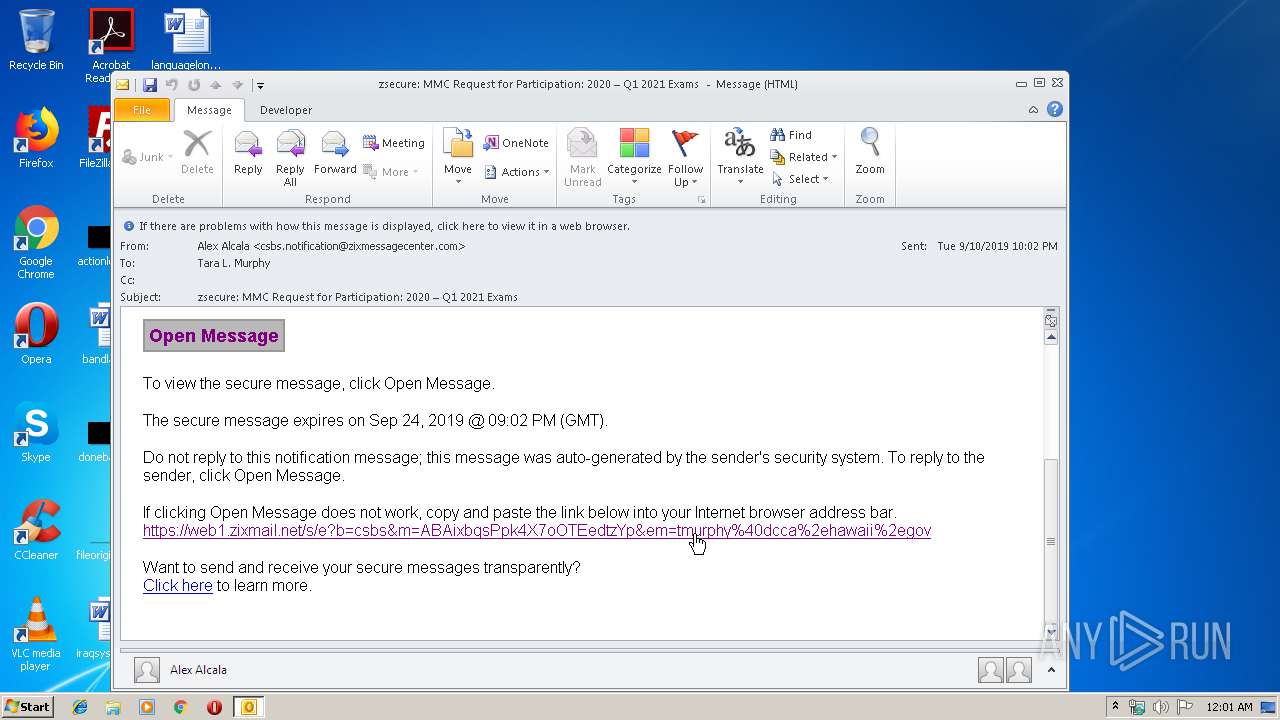
| 704 | "C:\Program Files\Internet Explorer\iexplore.exe" https://secure-web.cisco.com/1HlKoV59vuInP2hdiK8XYH0bEny7oCxpfCKiY4b3PC2N9AWkiZh2haEV3zGfaAcBzvVcsJVdq7kkxdNJ8Q4eO-Jm3WdZMT3E3hArsj9ag10K7muIXreFxnUDo9wlnHGFQm5lV16obam4KMowi3YTG-1c5893rXWThYAJX3yWmTqpGjEMHx00yASUru9xR9OGI51IA_FiHZoNYaVk-Ot1QqtVL_JIgUqrtaBL-7wTJZgkEPAd8-KFIpTXD7rcOleNEgUQe7SjBRGobgIre8ebEB-Hsno8eBY_CQ6SBWDE_KrJ25EsT24_GAyFO7CWv2x7-UsL1ictSygWhP3oA31Eo5Q/https%3A%2F%2Fweb1.zixmail.net%2Fs%2Fe%3Fb%3Dcsbs%26m%3DABAixbqsPpk4X7oOTEedtzYp%26em%3Dtmurphy%2540dcca%252ehawaii%252egov | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2308 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3548 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2756 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\zsecure MMC Request for Participation 2020 Q1 2021 Exams .msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2860 | "C:\Program Files\Internet Explorer\iexplore.exe" https://secure-web.cisco.com/1HlKoV59vuInP2hdiK8XYH0bEny7oCxpfCKiY4b3PC2N9AWkiZh2haEV3zGfaAcBzvVcsJVdq7kkxdNJ8Q4eO-Jm3WdZMT3E3hArsj9ag10K7muIXreFxnUDo9wlnHGFQm5lV16obam4KMowi3YTG-1c5893rXWThYAJX3yWmTqpGjEMHx00yASUru9xR9OGI51IA_FiHZoNYaVk-Ot1QqtVL_JIgUqrtaBL-7wTJZgkEPAd8-KFIpTXD7rcOleNEgUQe7SjBRGobgIre8ebEB-Hsno8eBY_CQ6SBWDE_KrJ25EsT24_GAyFO7CWv2x7-UsL1ictSygWhP3oA31Eo5Q/https%3A%2F%2Fweb1.zixmail.net%2Fs%2Fe%3Fb%3Dcsbs%26m%3DABAixbqsPpk4X7oOTEedtzYp%26em%3Dtmurphy%2540dcca%252ehawaii%252egov | C:\Program Files\Internet Explorer\iexplore.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3532 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2860 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
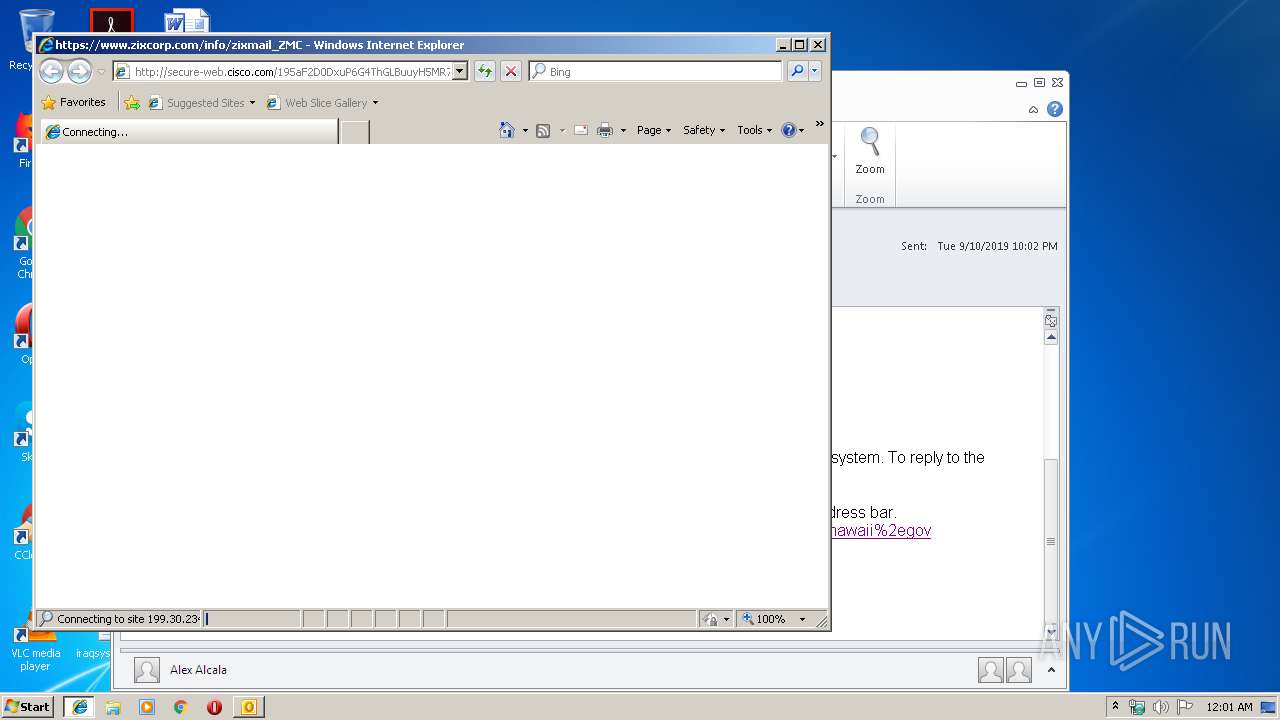
| 3548 | "C:\Program Files\Internet Explorer\iexplore.exe" http://secure-web.cisco.com/195aF2D0DxuP6G4ThGLBuuyH5MR7ZJ5r_-_FaEiAcAurXh5L_vLJ0PF9UXO6ENRSIBKFhMlGXbKIaFfgb99QQFbAeqwJRF6H1NdLr7JmI6Os6Czu18JsQ36KSihb7RBVmgbKI9DRuA_O2UfNn0sNigz1RgKkCn5FH_49e5-r-JW7S-Z9DBjWkPuDC3nW9WK4SQbXmpneYTzN--4gHWPnNGzNYXYAyPBK2z2zR2FlK5WsobyRzG7EBjUFU0GLUnH2BlQDbMpvuiKvl-0B7iPV9xaTHRUsY1vTBEi8Z-rKg6UyjWdvNH6D_6hzFnC9uQ4obSMeWpVy7rcPBfGgOv3GwDQ/http%3A%2F%2Fwww.zixcorp.com%2Finfo%2Fzixmail_ZMC | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3824 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
Total events
2 360
Read events
1 796
Write events
541
Delete events
23
Modification events
| (PID) Process: | (2756) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2756) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2756) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | gc! |
Value: 67632100C40A0000010000000000000000000000 | |||
| (PID) Process: | (2756) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: C40A0000B2DB7D9D2B68D50100000000 | |||
| (PID) Process: | (2756) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2756) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220210560 | |||
| (PID) Process: | (2756) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2756) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2756) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2756) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1328218133 | |||
Executable files
0
Suspicious files
8
Text files
75
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2756 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR9BE7.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 704 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 704 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 504 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabB8E5.tmp | — | |
MD5:— | SHA256:— | |||
| 504 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarB8E6.tmp | — | |
MD5:— | SHA256:— | |||
| 504 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabB8F6.tmp | — | |
MD5:— | SHA256:— | |||
| 504 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarB907.tmp | — | |
MD5:— | SHA256:— | |||
| 504 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabB9B4.tmp | — | |
MD5:— | SHA256:— | |||
| 504 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarB9B5.tmp | — | |
MD5:— | SHA256:— | |||
| 2756 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
37
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2756 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2308 | iexplore.exe | GET | 302 | 184.94.240.100:80 | http://secure-web.cisco.com/195aF2D0DxuP6G4ThGLBuuyH5MR7ZJ5r_-_FaEiAcAurXh5L_vLJ0PF9UXO6ENRSIBKFhMlGXbKIaFfgb99QQFbAeqwJRF6H1NdLr7JmI6Os6Czu18JsQ36KSihb7RBVmgbKI9DRuA_O2UfNn0sNigz1RgKkCn5FH_49e5-r-JW7S-Z9DBjWkPuDC3nW9WK4SQbXmpneYTzN--4gHWPnNGzNYXYAyPBK2z2zR2FlK5WsobyRzG7EBjUFU0GLUnH2BlQDbMpvuiKvl-0B7iPV9xaTHRUsY1vTBEi8Z-rKg6UyjWdvNH6D_6hzFnC9uQ4obSMeWpVy7rcPBfGgOv3GwDQ/http%3A%2F%2Fwww.zixcorp.com%2Finfo%2Fzixmail_ZMC | US | — | — | whitelisted |
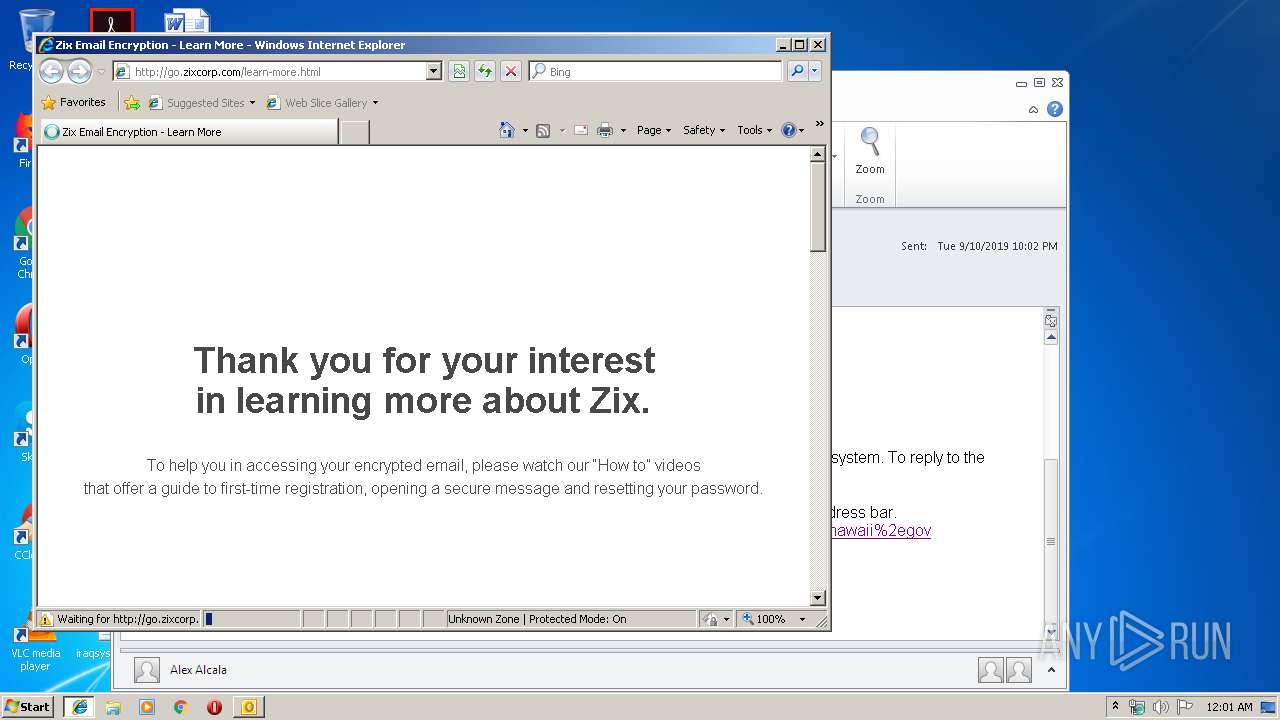
2308 | iexplore.exe | GET | 200 | 199.15.213.30:80 | http://go.zixcorp.com/rs/406-QBF-138/images/Zix_Logo_Blue_small.png | US | image | 20.6 Kb | malicious |
2308 | iexplore.exe | GET | 200 | 216.58.207.42:80 | http://fonts.googleapis.com/css?family=Raleway | US | text | 162 b | whitelisted |
2308 | iexplore.exe | GET | 200 | 199.15.213.30:80 | http://go.zixcorp.com/learn-more.html | US | html | 6.39 Kb | malicious |
2308 | iexplore.exe | GET | 200 | 199.15.213.30:80 | http://go.zixcorp.com/rs/406-QBF-138/images/Learn%20More%20-%20Open%20Email.png | US | image | 42.0 Kb | malicious |
2308 | iexplore.exe | GET | 200 | 199.15.213.30:80 | http://go.zixcorp.com/rs/406-QBF-138/images/Learn%20More%20-%20Register%20Email.png | US | image | 45.6 Kb | malicious |
2308 | iexplore.exe | GET | 200 | 172.217.21.194:80 | http://www.googleadservices.com/pagead/conversion.js | US | text | 9.14 Kb | whitelisted |
2308 | iexplore.exe | GET | 200 | 172.217.22.35:80 | http://www.gstatic.com/wcm/loader.js | US | text | 323 b | whitelisted |
2308 | iexplore.exe | GET | 200 | 104.111.251.133:80 | http://munchkin.marketo.net//munchkin.js | NL | text | 752 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2308 | iexplore.exe | 216.58.210.10:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2756 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
704 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
504 | iexplore.exe | 63.71.15.50:443 | web1.zixmail.net | Zix Corporation | US | suspicious |
504 | iexplore.exe | 13.107.4.50:80 | www.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
3532 | iexplore.exe | 63.71.15.50:443 | web1.zixmail.net | Zix Corporation | US | suspicious |
2308 | iexplore.exe | 184.94.240.100:80 | secure-web.cisco.com | Cisco Systems Ironport Division | US | suspicious |
2308 | iexplore.exe | 199.30.234.249:80 | www.zixcorp.com | Zix Corporation | US | suspicious |
— | — | 199.15.213.30:80 | go.zixcorp.com | MARKETO | US | unknown |
2308 | iexplore.exe | 45.33.24.119:443 | placehold.it | Linode, LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
secure-web.cisco.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
web1.zixmail.net |
| whitelisted |
www.zixcorp.com |
| suspicious |
go.zixcorp.com |
| malicious |
ajax.googleapis.com |
| whitelisted |
d12ulf131zb0yj.cloudfront.net |
| shared |
fonts.googleapis.com |
| whitelisted |