| File name: | gdbprosetup.exe |
| Full analysis: | https://app.any.run/tasks/67c6c5ec-2459-4fd8-8f48-450256d6048a |
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2025, 19:56:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | ABBF9439C25699EB16179752C6AED97C |
| SHA1: | 5198F18A783D380FE4DA67B4BD55CA6936B6C012 |
| SHA256: | 24692CB15444F050994D55A185C47BEAE58966953D325B9DDFBA080A93540C95 |
| SSDEEP: | 98304:g92flm4DCcrsJHszoBklYOfmUGEjxpUsMlpCTrGNE/4q9+5TIdYQ+qwmDOAyXr2K:B833VD4VYRYqJaNG1BGw6P5JTGCTRY |
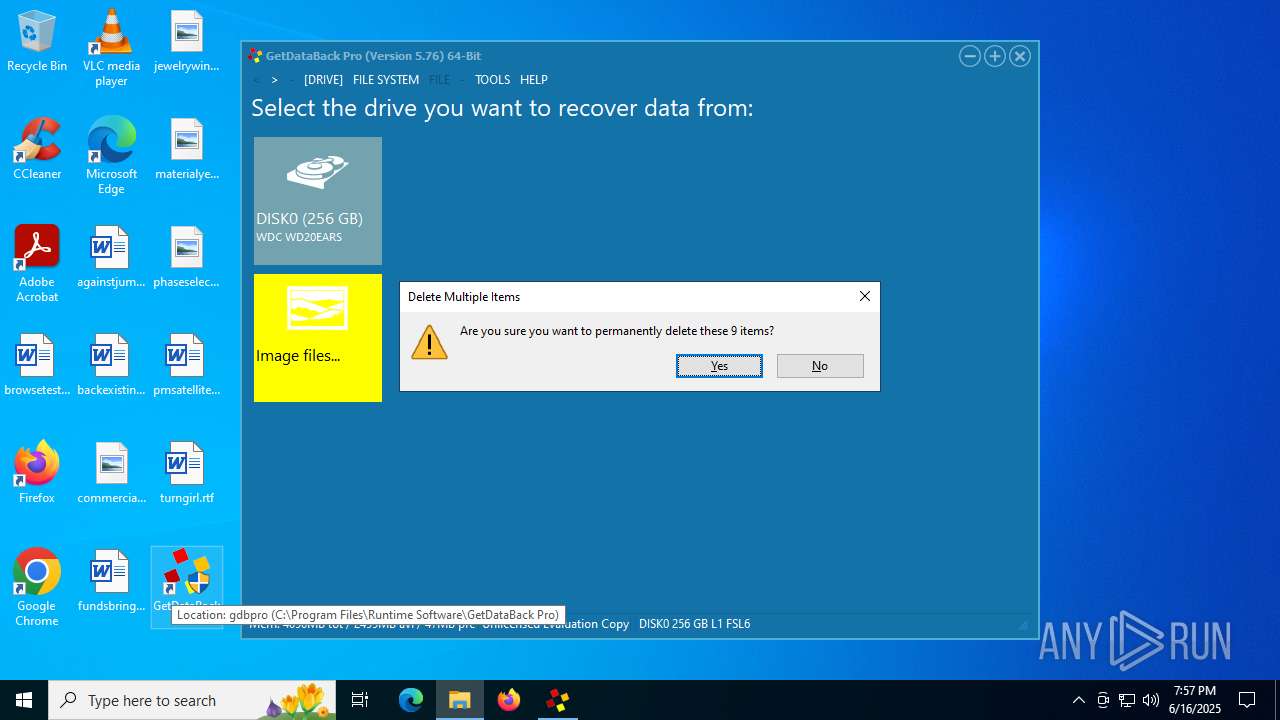
MALICIOUS
Executing a file with an untrusted certificate
- gdbprosetup.exe (PID: 3540)
- gdbpro.exe (PID: 6540)
SUSPICIOUS
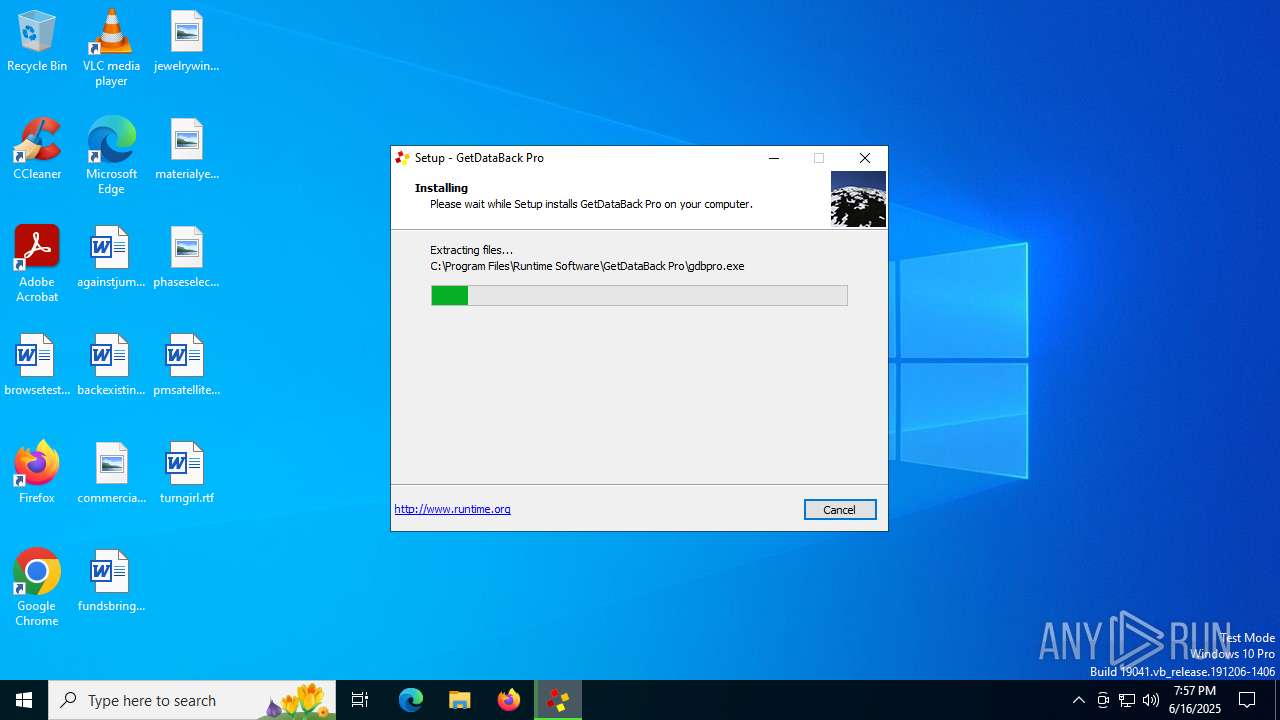
Executable content was dropped or overwritten
- gdbprosetup.tmp (PID: 6388)
- gdbprosetup.exe (PID: 3540)
Reads security settings of Internet Explorer
- gdbprosetup.tmp (PID: 6584)
INFO
Reads the computer name
- gdbprosetup.tmp (PID: 6584)
- gdbpro.exe (PID: 6540)
Create files in a temporary directory
- gdbprosetup.exe (PID: 3540)
Detects InnoSetup installer (YARA)
- gdbprosetup.exe (PID: 3540)
- gdbprosetup.tmp (PID: 6584)
- gdbprosetup.exe (PID: 2668)
- gdbprosetup.tmp (PID: 6388)
Checks supported languages
- gdbprosetup.exe (PID: 3540)
- gdbprosetup.tmp (PID: 6584)
- gdbpro.exe (PID: 6540)
Process checks computer location settings
- gdbprosetup.tmp (PID: 6584)
Creates files in the program directory
- gdbprosetup.tmp (PID: 6388)
The sample compiled with german language support
- gdbprosetup.tmp (PID: 6388)
Compiled with Borland Delphi (YARA)
- gdbprosetup.tmp (PID: 6584)
- gdbprosetup.tmp (PID: 6388)
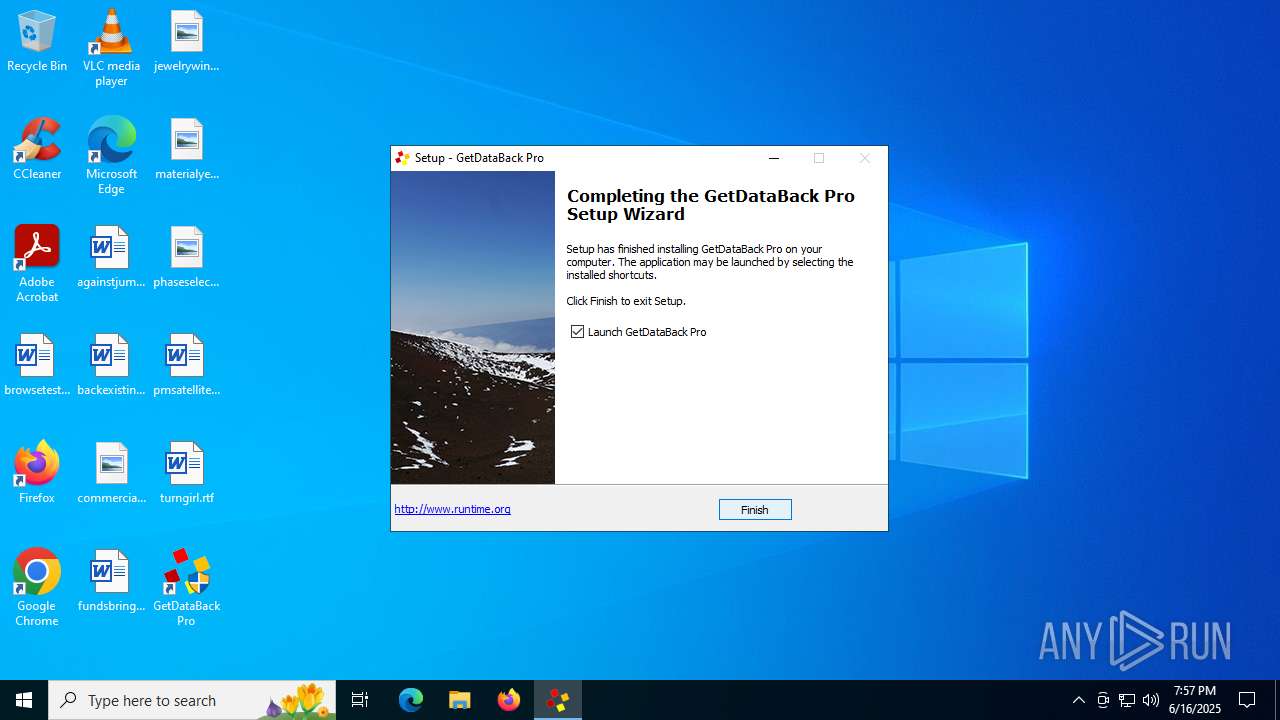
Creates a software uninstall entry
- gdbprosetup.tmp (PID: 6388)
The sample compiled with english language support
- gdbprosetup.tmp (PID: 6388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (81.5) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.5) |
| .exe | | | Win32 Executable (generic) (3.3) |
| .exe | | | Win16/32 Executable Delphi generic (1.5) |
| .exe | | | Generic Win/DOS Executable (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 41472 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaa98 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
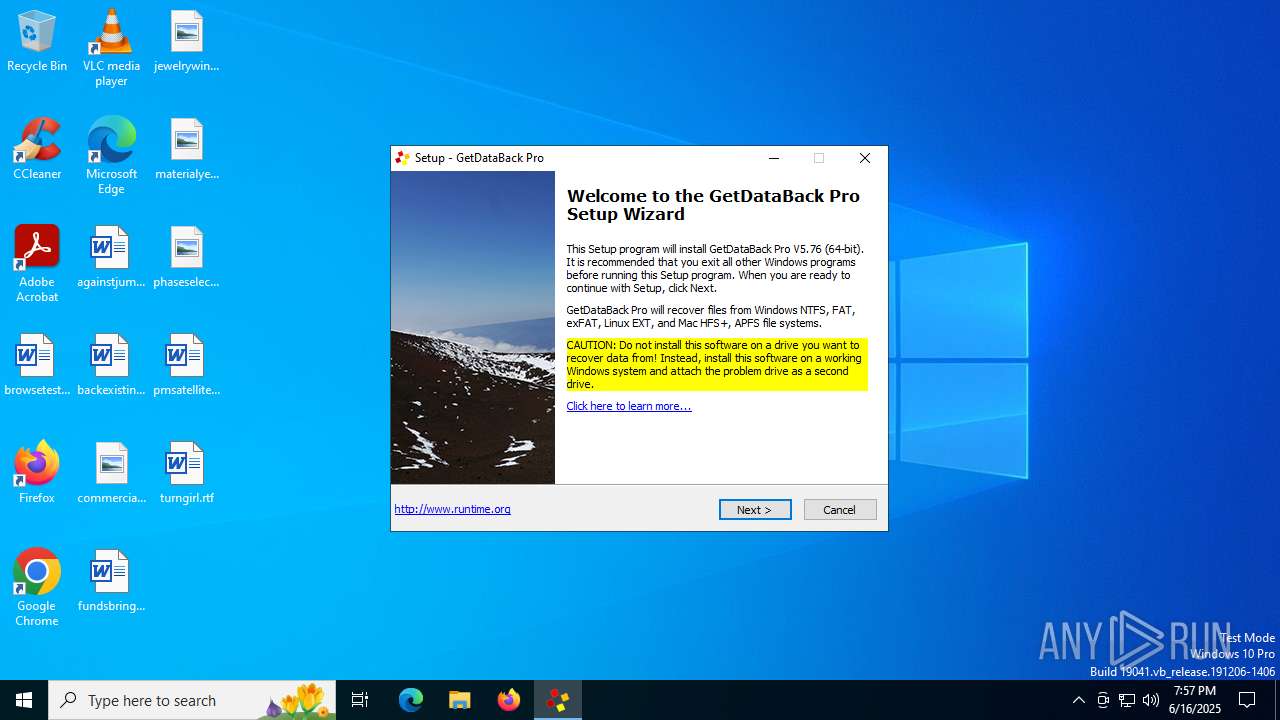
| FileVersionNumber: | 5.76.0.0 |
| ProductVersionNumber: | 5.76.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
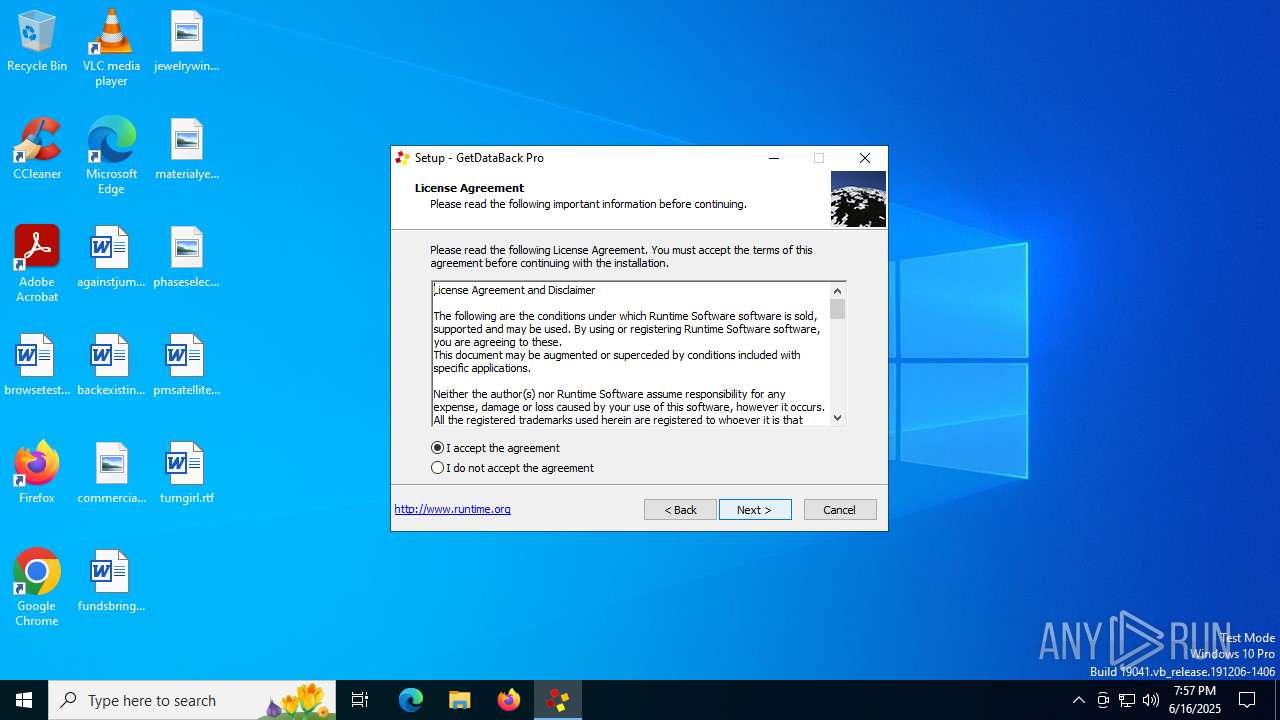
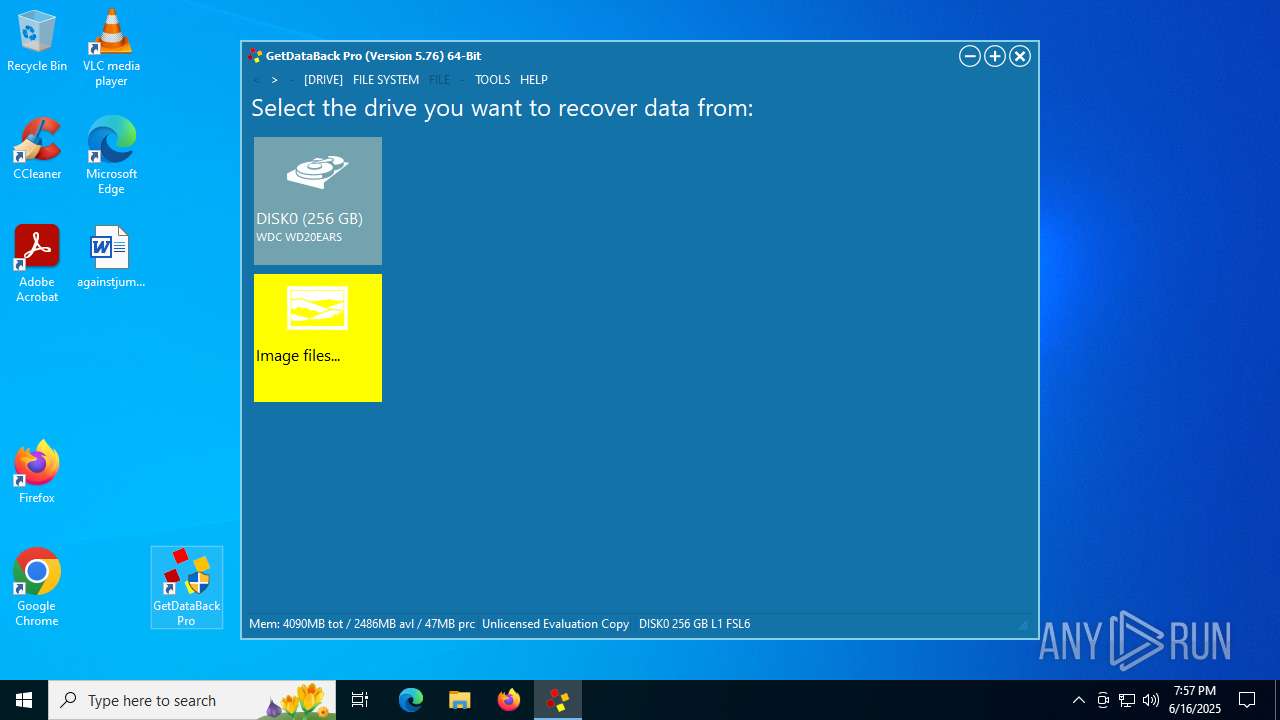
| CompanyName: | Runtime Software, LLC |
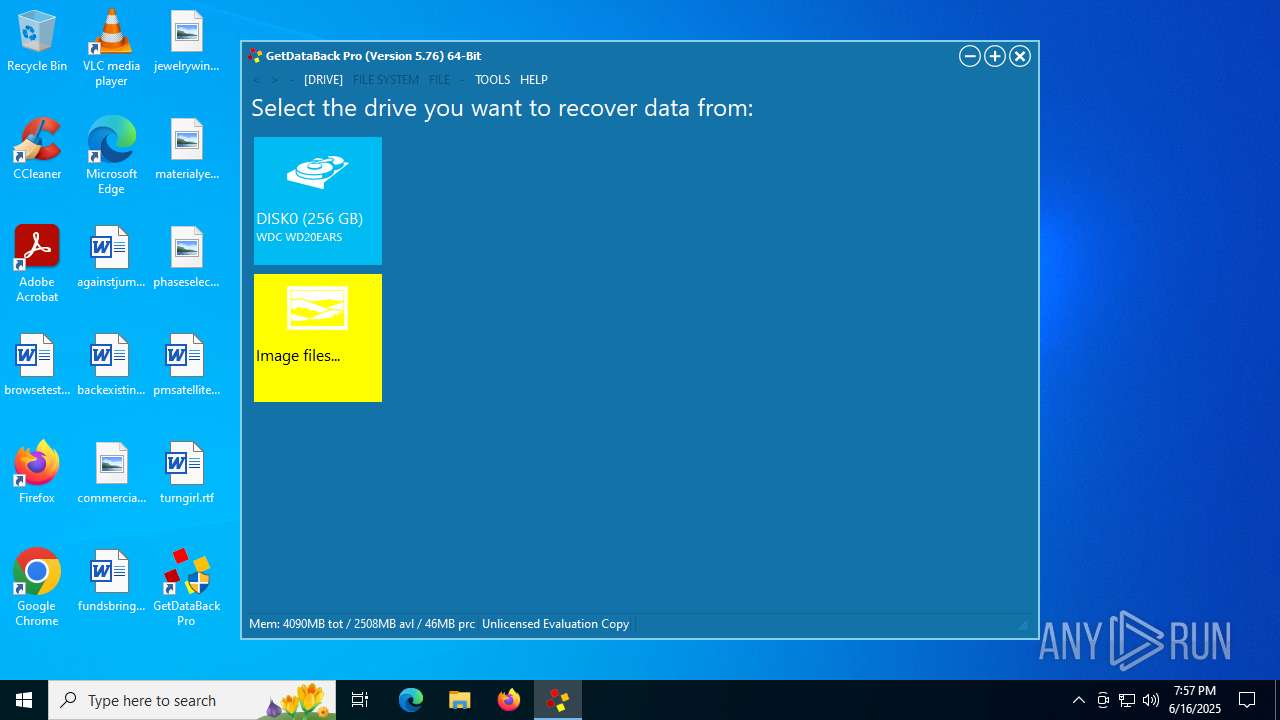
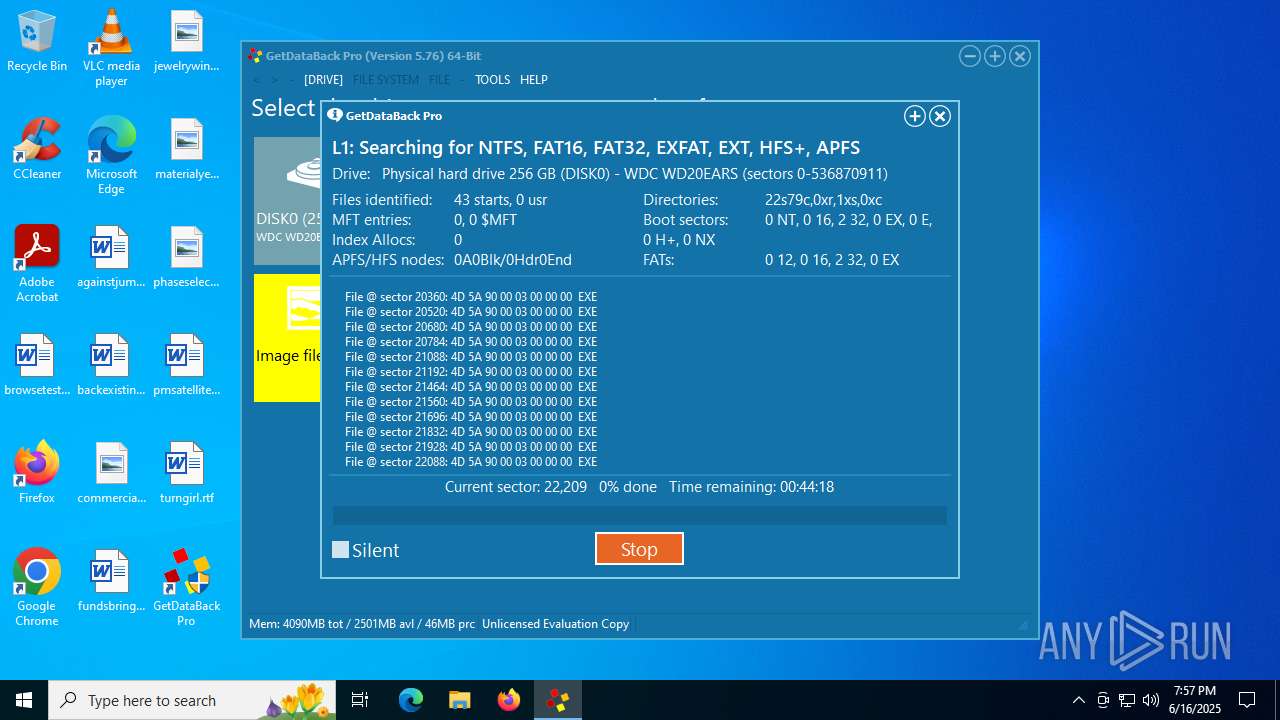
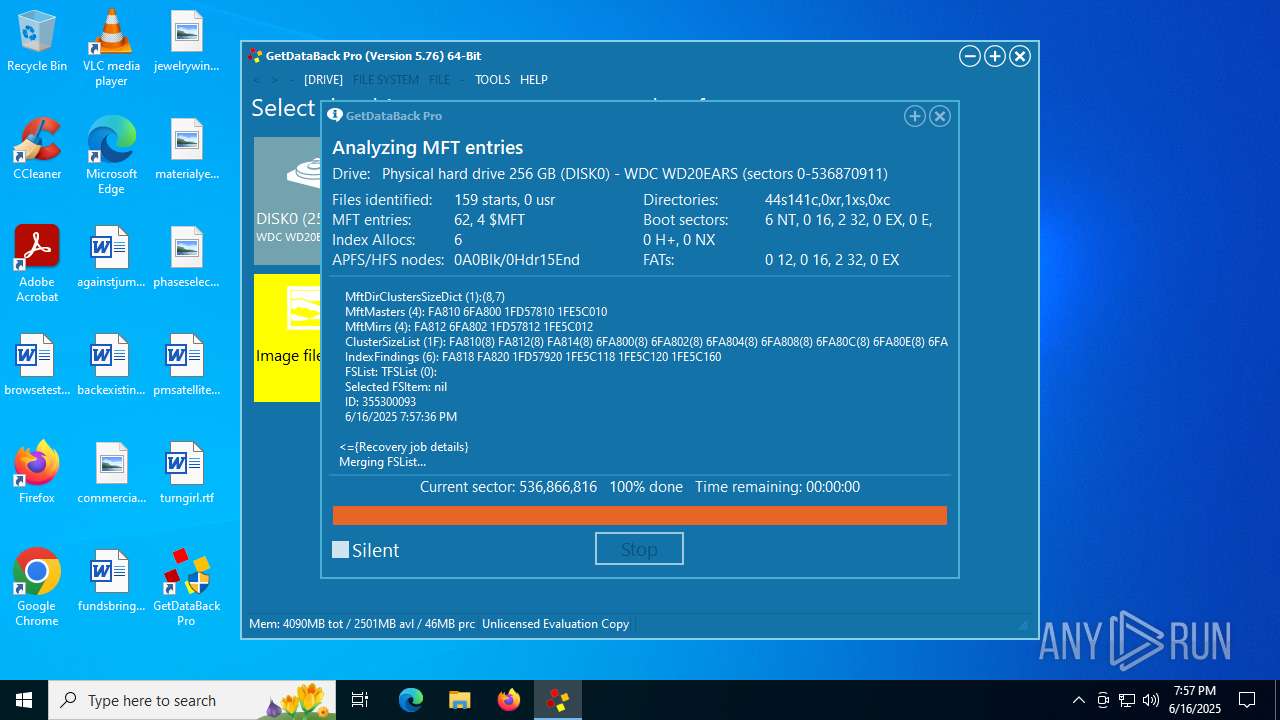
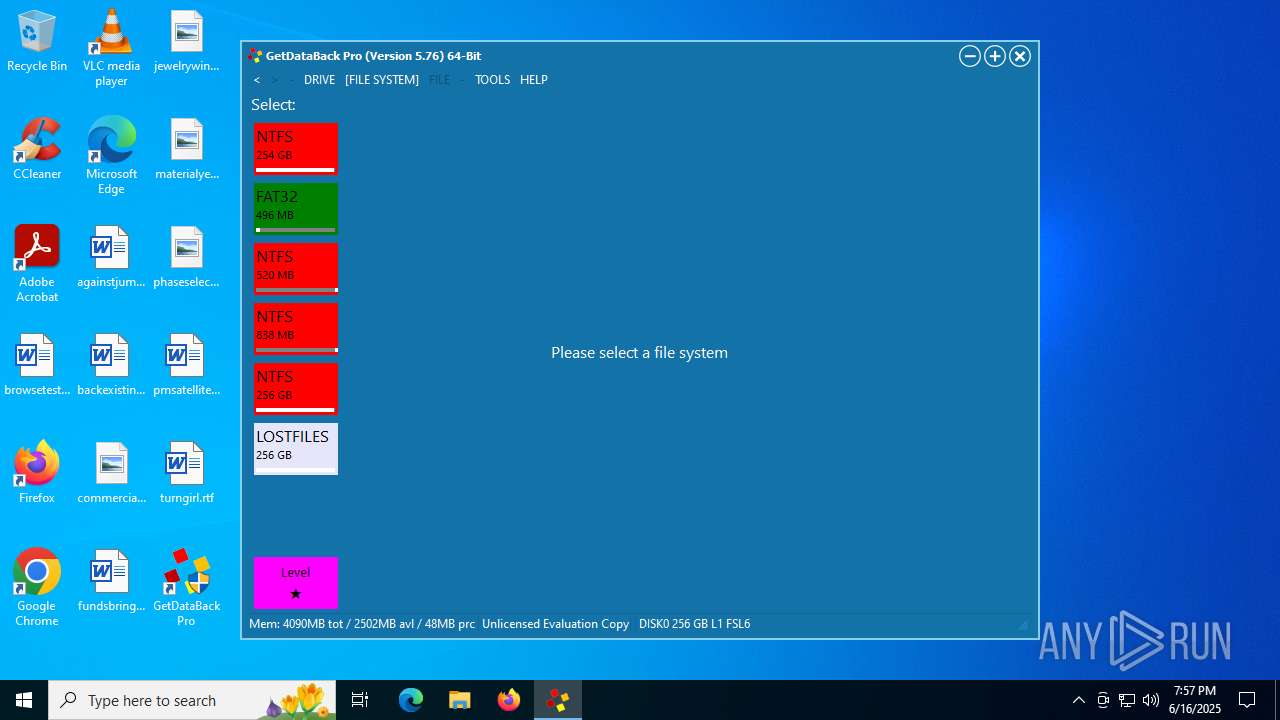
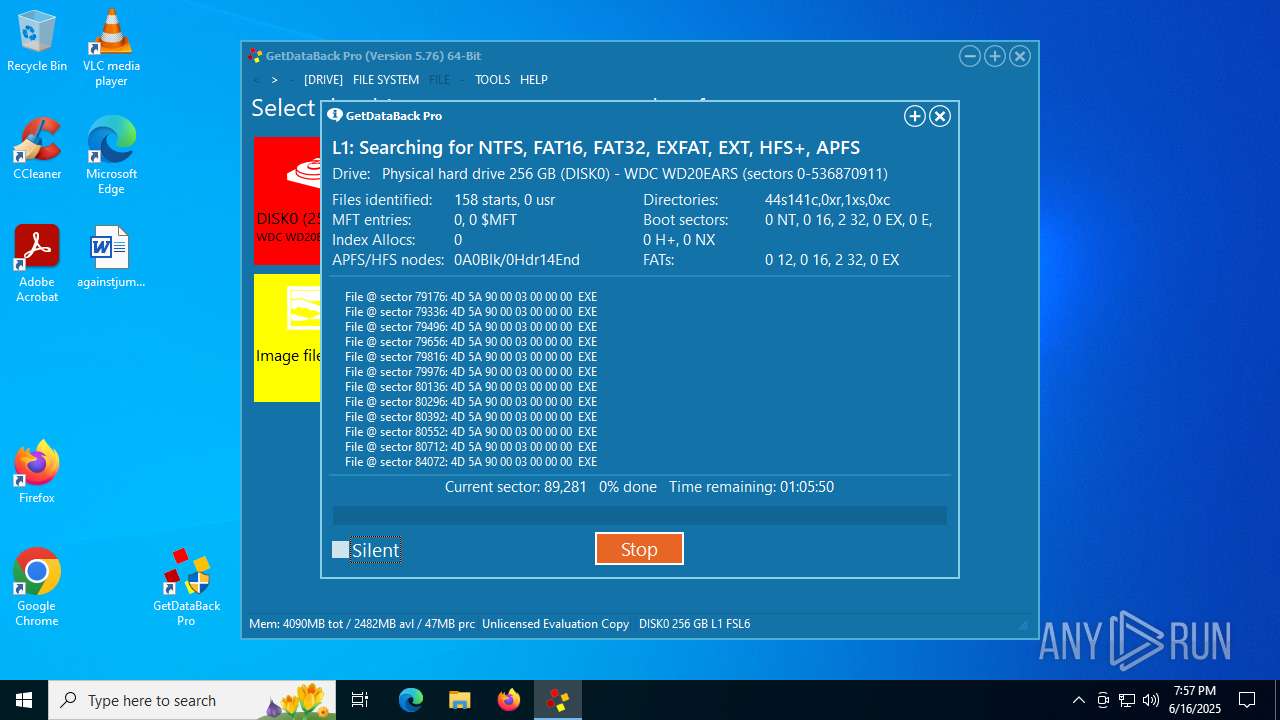
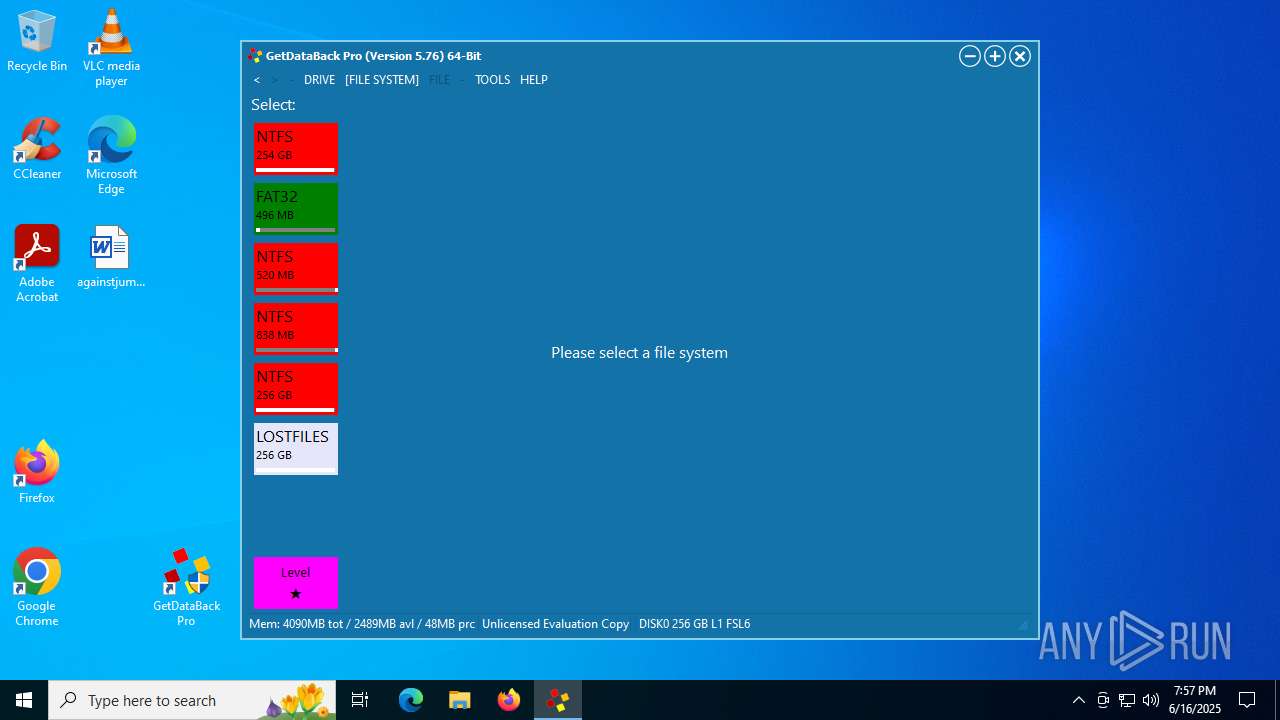
| FileDescription: | Recover Data from NTFS, FAT, exFAT, EXT, HFS+, and APFS |
| FileVersion: | 5.76 |
| LegalCopyright: | Runtime Software, LLC |
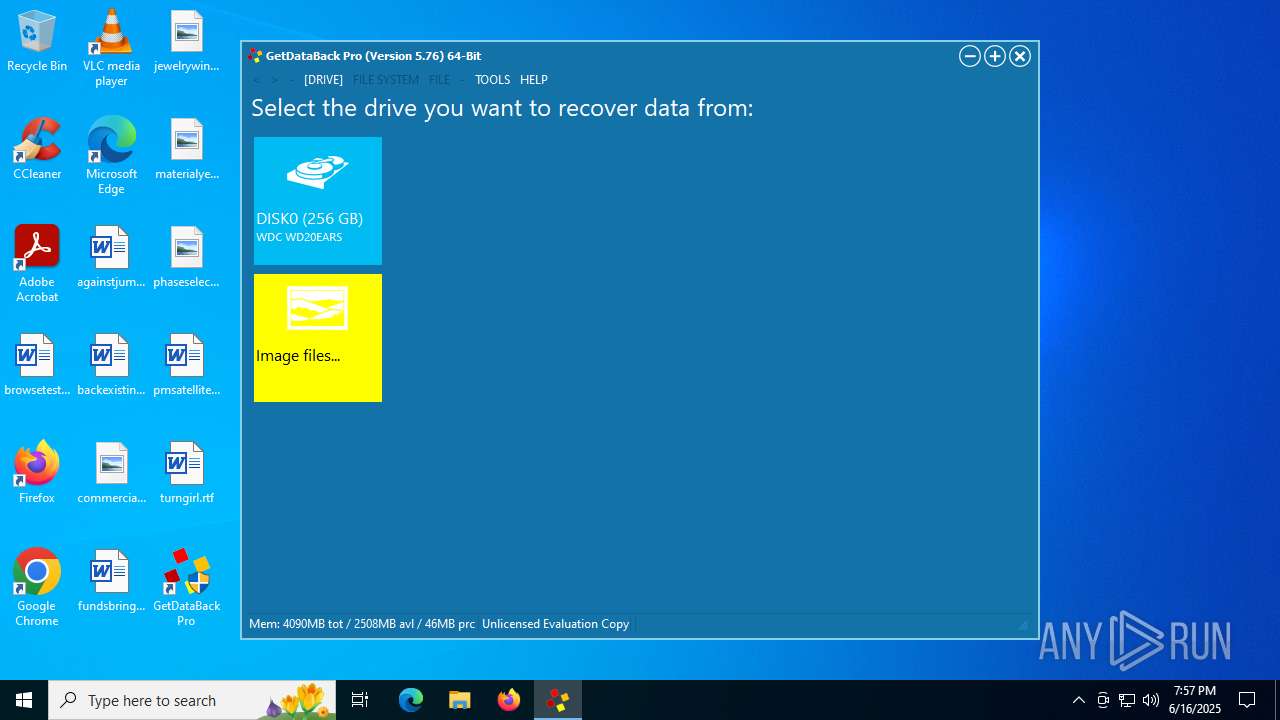
| ProductName: | GetDataBack Pro Data Recovery |
| ProductVersion: | 5.76 |
Total processes
141
Monitored processes
6
Malicious processes
1
Suspicious processes
2
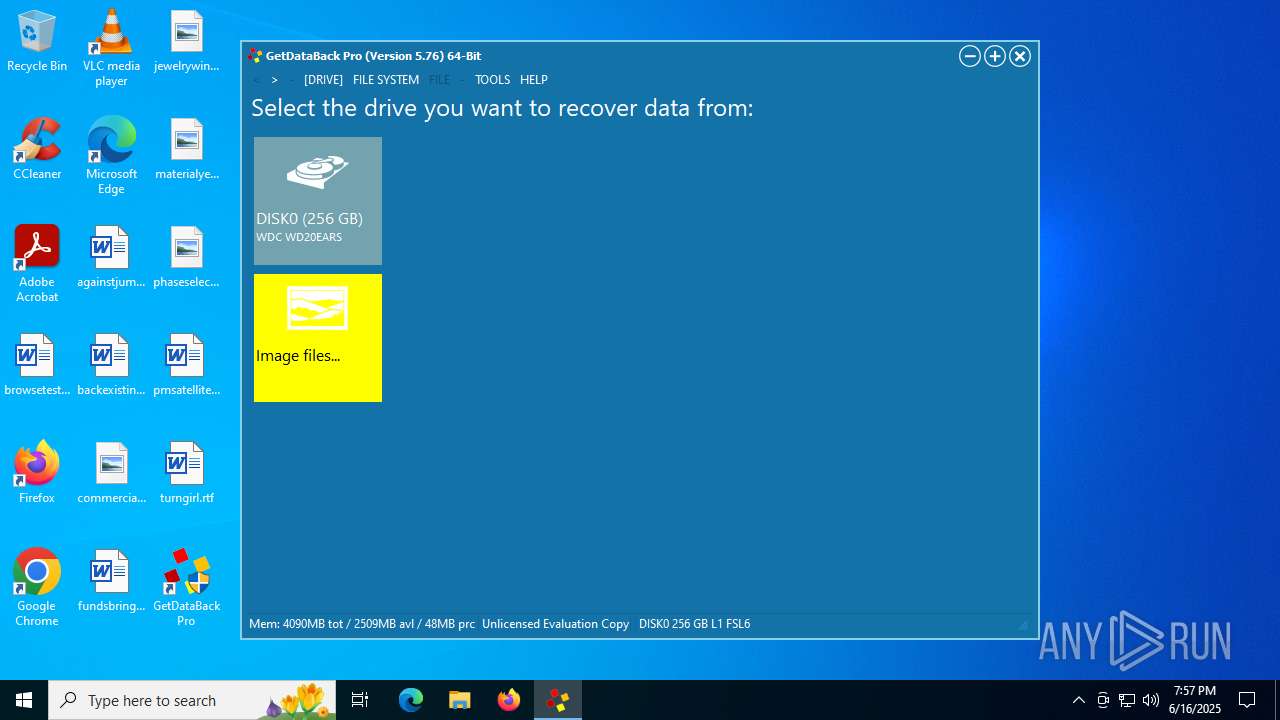
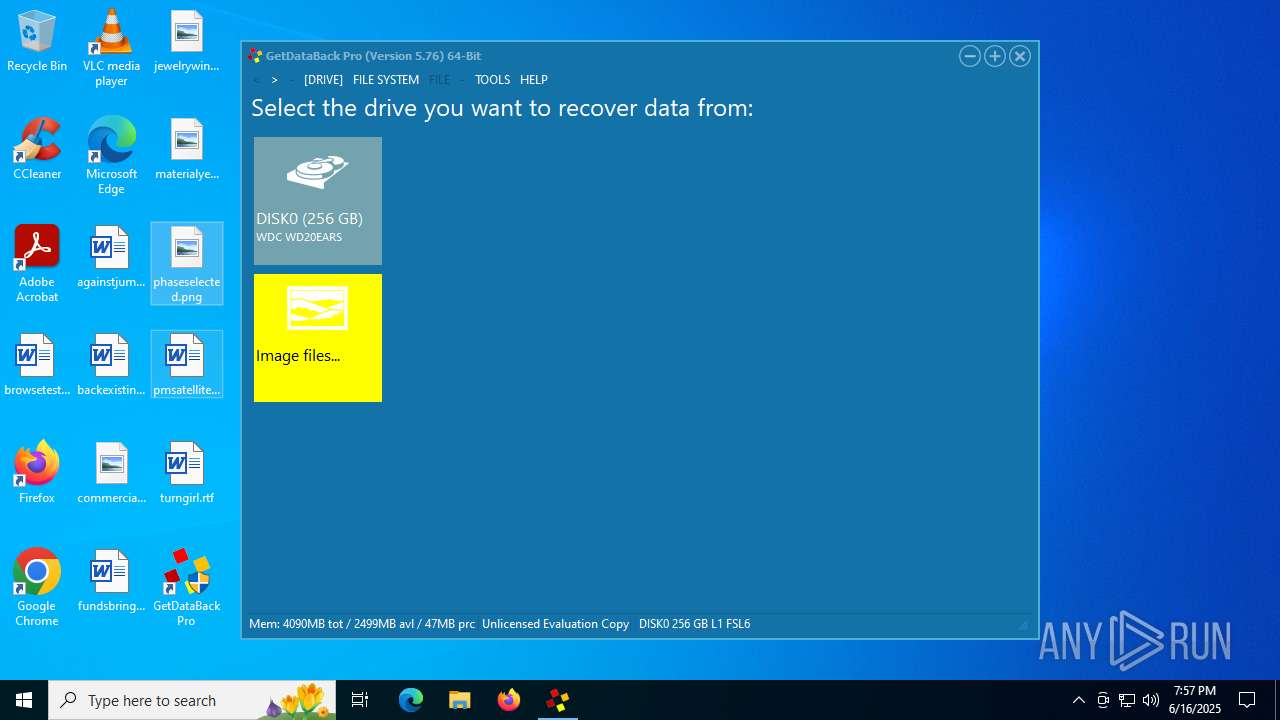
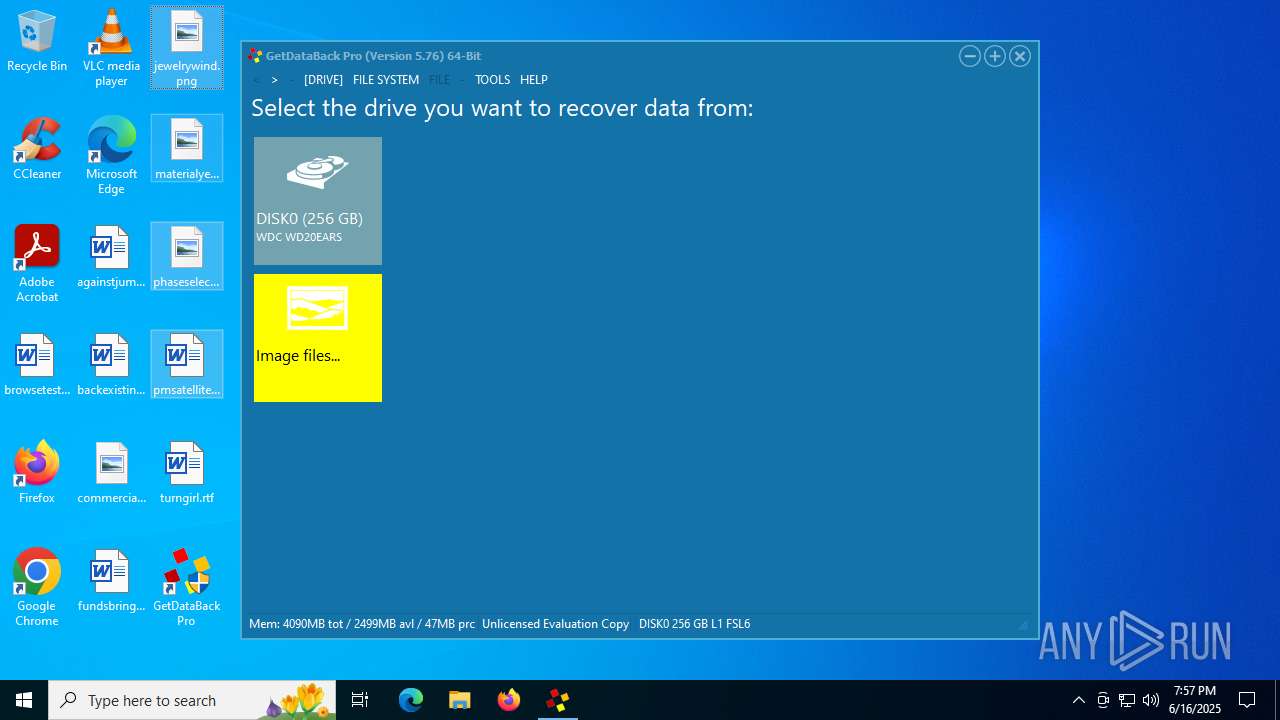
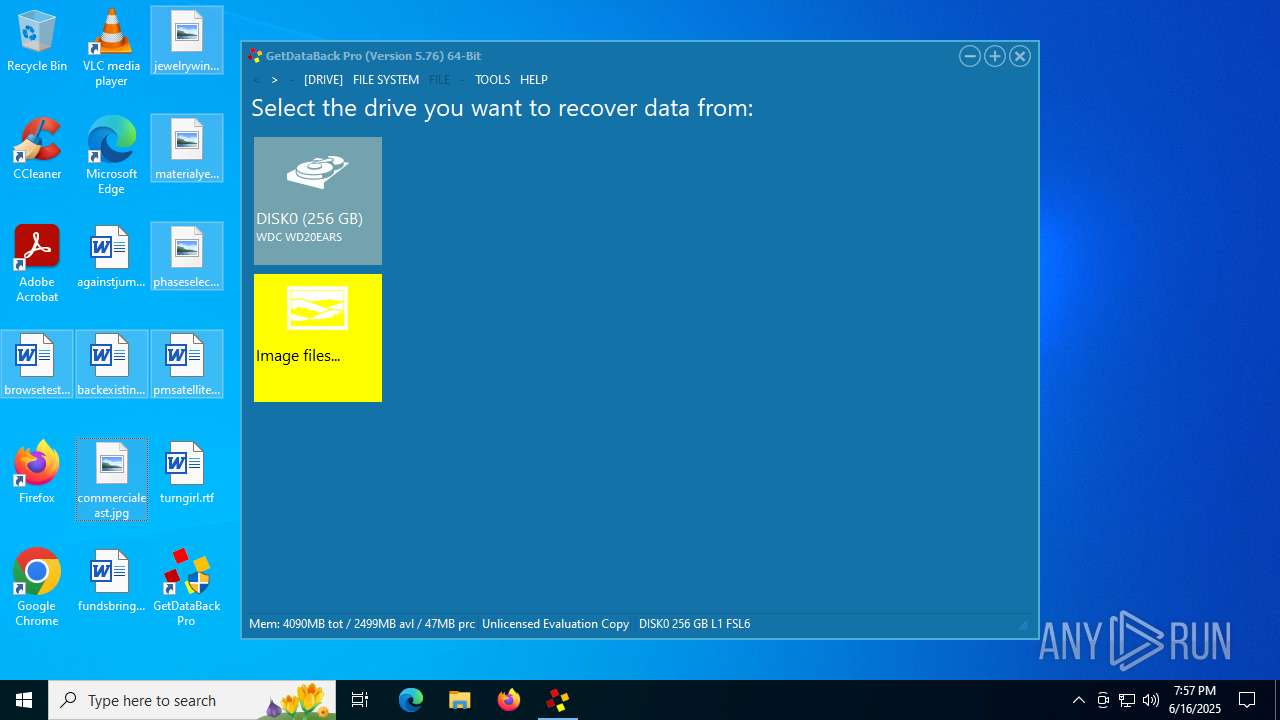
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 592 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2668 | "C:\Users\admin\AppData\Local\Temp\gdbprosetup.exe" /SPAWNWND=$6030E /NOTIFYWND=$70374 | C:\Users\admin\AppData\Local\Temp\gdbprosetup.exe | gdbprosetup.tmp | ||||||||||||
User: admin Company: Runtime Software, LLC Integrity Level: HIGH Description: Recover Data from NTFS, FAT, exFAT, EXT, HFS+, and APFS Exit code: 0 Version: 5.76 | |||||||||||||||
| 3540 | "C:\Users\admin\AppData\Local\Temp\gdbprosetup.exe" | C:\Users\admin\AppData\Local\Temp\gdbprosetup.exe | explorer.exe | ||||||||||||
User: admin Company: Runtime Software, LLC Integrity Level: MEDIUM Description: Recover Data from NTFS, FAT, exFAT, EXT, HFS+, and APFS Exit code: 0 Version: 5.76 Modules
| |||||||||||||||
| 6388 | "C:\Users\admin\AppData\Local\Temp\is-90LH2.tmp\gdbprosetup.tmp" /SL5="$1402EA,15923499,207360,C:\Users\admin\AppData\Local\Temp\gdbprosetup.exe" /SPAWNWND=$6030E /NOTIFYWND=$70374 | C:\Users\admin\AppData\Local\Temp\is-90LH2.tmp\gdbprosetup.tmp | — | gdbprosetup.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 6540 | "C:\Program Files\Runtime Software\GetDataBack Pro\gdbpro.exe" | C:\Program Files\Runtime Software\GetDataBack Pro\gdbpro.exe | gdbprosetup.tmp | ||||||||||||
User: admin Company: Runtime Software, LLC Integrity Level: HIGH Description: GetDataBack Pro Version: 5.7.6.0 Modules
| |||||||||||||||
| 6584 | "C:\Users\admin\AppData\Local\Temp\is-IRS30.tmp\gdbprosetup.tmp" /SL5="$70374,15923499,207360,C:\Users\admin\AppData\Local\Temp\gdbprosetup.exe" | C:\Users\admin\AppData\Local\Temp\is-IRS30.tmp\gdbprosetup.tmp | — | gdbprosetup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
Total events
736
Read events
700
Write events
36
Delete events
0
Modification events
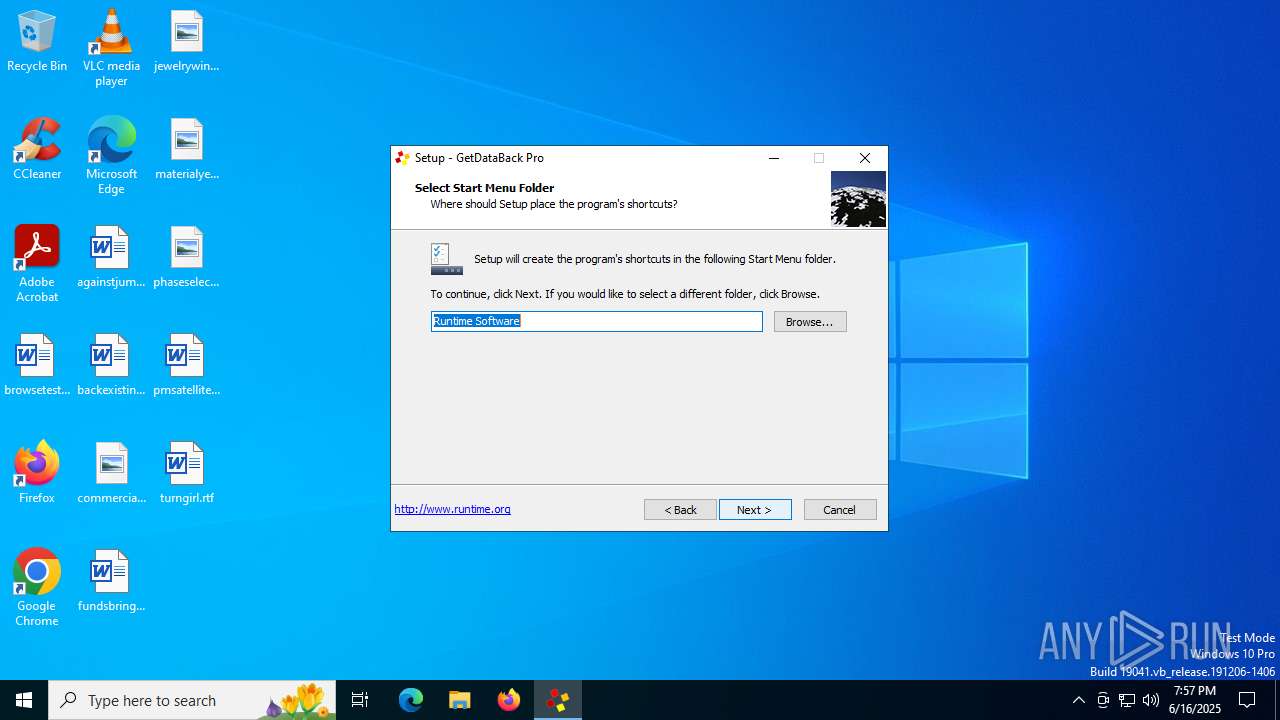
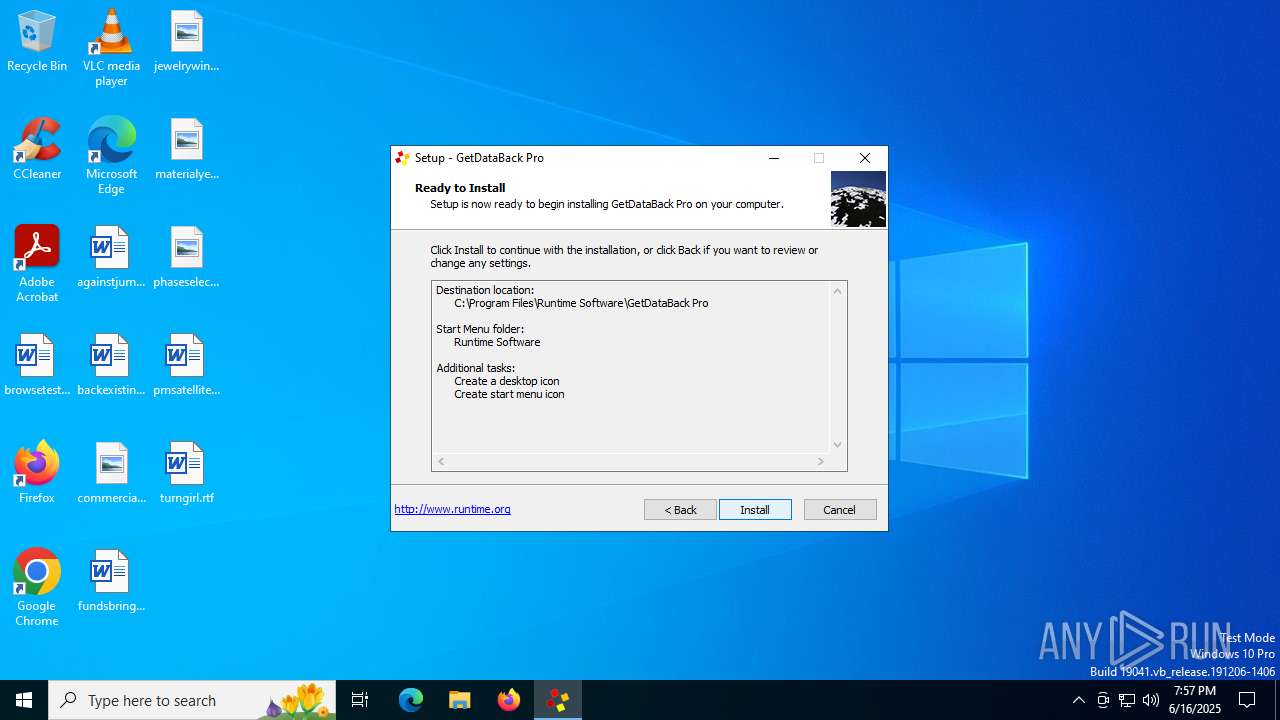
| (PID) Process: | (6388) gdbprosetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Runtime Software\GetDataBackPro |
| Operation: | write | Name: | InstallDir |
Value: C:\Program Files\Runtime Software\GetDataBack Pro | |||
| (PID) Process: | (6388) gdbprosetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Runtime Software\GetDataBackPro |
| Operation: | write | Name: | InstalledBy |
Value: gdbpro | |||
| (PID) Process: | (6388) gdbprosetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Runtime Software\GetDataBackPro |
| Operation: | write | Name: | Language |
Value: | |||
| (PID) Process: | (6388) gdbprosetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Runtime Software\GetDataBackPro |
| Operation: | write | Name: | Version |
Value: 5.76 | |||
| (PID) Process: | (6388) gdbprosetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Runtime Software\GetDataBackPro\License |
| Operation: | write | Name: | Date |
Value: | |||
| (PID) Process: | (6388) gdbprosetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Runtime Software\GetDataBackPro\License |
| Operation: | write | Name: | Key |
Value: | |||
| (PID) Process: | (6388) gdbprosetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Runtime Software\GetDataBackPro\License |
| Operation: | write | Name: | Name |
Value: | |||
| (PID) Process: | (6388) gdbprosetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Runtime Software\GetDataBackPro\Options |
| Operation: | write | Name: | DefaultRecoverDir |
Value: | |||
| (PID) Process: | (6388) gdbprosetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Runtime Software\GetDataBackPro\Options |
| Operation: | write | Name: | DefaultTempDir |
Value: | |||
| (PID) Process: | (6388) gdbprosetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Runtime Software\GetDataBackPro\Options |
| Operation: | write | Name: | DiskExplorerPath |
Value: | |||
Executable files
12
Suspicious files
0
Text files
0
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6388 | gdbprosetup.tmp | C:\Program Files\Runtime Software\GetDataBack Pro\unins000.dat | dat | |
MD5:1842BE8CECE340569877BAF72AB4958B | SHA256:B756DA597FA2B572EE6333E456FF4214E272ED31A778313B3A51EFF9654BFAEF | |||
| 6388 | gdbprosetup.tmp | C:\Program Files\Runtime Software\GetDataBack Pro\unins000.exe | executable | |
MD5:677415DB06E76A48A3A539B622C9519B | SHA256:EF7577DD518A9615AC58D43256021ED3BCCEB2CBD86E4FEA5AB7E4E90577DDBD | |||
| 6388 | gdbprosetup.tmp | C:\Program Files\Runtime Software\GetDataBack Pro\is-JOIIG.tmp | executable | |
MD5:677415DB06E76A48A3A539B622C9519B | SHA256:EF7577DD518A9615AC58D43256021ED3BCCEB2CBD86E4FEA5AB7E4E90577DDBD | |||
| 3540 | gdbprosetup.exe | C:\Users\admin\AppData\Local\Temp\is-IRS30.tmp\gdbprosetup.tmp | executable | |
MD5:1C14D349E32731381193267BDB30BA16 | SHA256:7A5A1362D7F2A751F392A2A1E5586FC5353D5327C2AB688B3622E84CD2545EBA | |||
| 6388 | gdbprosetup.tmp | C:\Program Files\Runtime Software\GetDataBack Pro\is-PM6UU.tmp | executable | |
MD5:7E549ABE834E46A800097808261E4D45 | SHA256:DCA11E7F73FA7B3B8905F5AF5473968BC8A6825931648C6B798CE1F170CF6095 | |||
| 6388 | gdbprosetup.tmp | C:\Users\admin\AppData\Local\Temp\is-LNHS8.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 6388 | gdbprosetup.tmp | C:\Program Files\Runtime Software\GetDataBack Pro\is-P8CT4.tmp | executable | |
MD5:DA6EC984BF76A57CC7A77074B8626438 | SHA256:1FC4298B89FCC2396336350766FEF13BE10135DF03ADCCB2B183E366C3E52FFC | |||
| 6388 | gdbprosetup.tmp | C:\Program Files\Runtime Software\GetDataBack Pro\is-8A9FE.tmp | jdbg | |
MD5:B4A617E865D72F09A3D24A18E0D20221 | SHA256:00428DFD7A3D5BB4EAECBD305317CD2F08A9797A2FB4AF0A74363A4C83B6B793 | |||
| 6388 | gdbprosetup.tmp | C:\Program Files\Runtime Software\GetDataBack Pro\gdbpro.jdbg | jdbg | |
MD5:B4A617E865D72F09A3D24A18E0D20221 | SHA256:00428DFD7A3D5BB4EAECBD305317CD2F08A9797A2FB4AF0A74363A4C83B6B793 | |||
| 6388 | gdbprosetup.tmp | C:\Program Files\Runtime Software\GetDataBack Pro\wpdecodejp64.dll | executable | |
MD5:78B09B212E737A079B0FEEE0AF437D9C | SHA256:E21414F726465AD518546AA744D3E11892E63A9FDDE1D9D2A6F4369DFC1816D3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
21
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1096 | SIHClient.exe | GET | 200 | 104.85.1.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1096 | SIHClient.exe | GET | 200 | 104.85.1.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3944 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3800 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1096 | SIHClient.exe | 20.12.23.50:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1096 | SIHClient.exe | 104.85.1.163:80 | www.microsoft.com | AKAMAI-AS | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
gdbpro.exe | kpkndx |